Join devRant
Do all the things like
++ or -- rants, post your own rants, comment on others' rants and build your customized dev avatar
Sign Up
Pipeless API

From the creators of devRant, Pipeless lets you power real-time personalized recommendations and activity feeds using a simple API
Learn More
Search - "hidden files"
-
A scammer called me today. They were saying that harmful files were moved to my computer and they needed to remove them. I don't think they are ever going to call me again.
S = scammer; M = me;
S: this is tech support we need access to your computer because we detected harmful files and need to remove them.
M: oh my! Hold on, let me go to my computer now. How can you access it?
S: we can just use RDP and delete the files. They are in a hidden folder that is encrypted so this Is the only way.
M: oh ok I believe you. Hm... it looks like my son only allows certain IP addresses to access our computers.. I don't know how to disable this so can you just email me your IP address?
S: Sure...
He then sends me his actual IP address... it doesn't even look like a proxy or VPN.
M: oh my I forgot that you need my password to login. It's really long and complicated... can I just email it to you?
S: Sure!!
I then tell him to hold on I have to find it that my "son" stored it somewhere.
At this time I'm taking a photo of my bare ass and attaching it to the email. I then say in the email "Please note what my job title is in my signature.. I just sent the FBI your name, phone number, email, and IP address. Please enjoy my bare ass, you'll see a lot of it in prison."23 -
How to hide your important files from people without making Hidden folders
1. Go to Desktop and create a new folder
2. Name the folder Internet Explorer
3. Change the folder icon to Internet Explorer
4. Keep it in a corner of the desktop
Now, no one will open internet explorer :D10 -
@Devintrix , congrats and happy lifes with your wife. this joke is for you :)
Dear Tech Support:
Last year I upgraded from Girlfriend 7.0 to Wife 1.0 and noticed that the new program began running unexpected child processing that took up a lot of space and valuable resources.
In addition, Wife 1.0 installs itself into all other programs and launches during system initialization, where it monitors all other system activity. Applications such as PokerNight 10.3, Drunken Boys Night 2.5 and Monday Night football 5.0 no longer run, crashing the system whenever selected.
I cannot seem to keep Wife 1.0 in the background while attempting to run some of my other favorite applications. I am thinking about going back to Girlfriend 7.0, but un-install does not work on this program.
Can you help me please?
Thanks,
Joe
——————————————————–
Dear Joe:
This is a very common problem men complain about but is mostly due to a primary misconception. Many people upgrade from Girlfriend 7.0 to Wife 1.0 with the idea that Wife 1.0 is merely a “UTILITIES & ENTERTAINMENT” program. Wife 1.0 is an OPERATING SYSTEM and designed by its creator to run everything.
It is unlikely you would be able to purge Wife 1.0 and still convert back to Girlfriend 7.0. Hidden operating files within your system would cause Girlfriend 7.0 to emulate Wife 1.0 so nothing is gained.
It is impossible to un-install, delete, or purge the program files from the system once installed. You cannot go back to Girlfriend 7.0 because Wife 1.0 is not designed to do this. Some have tried to install Girlfriend 8.0 or Wife 2.0 but end up with more problems than the original system.
I recommend you keep Wife 1.0 and just deal with the situation. Having Wife 1.0 installed myself, I might also suggest you read the entire section regarding General Partnership Faults (GPFs). You must assume all responsibility for faults and problems that might occur, regardless of their cause. The best course of action will be to enter the command C:\APOLOGIZE. The system will run smoothly as long as you take the blame for all the GPFs.
Wife 1.0 is a great program, but very high maintenance. Consider buying additional software to improve the performance of Wife 1.0. I recommend Flowers 2.1, Jewelry 2.2, and Chocolates 5.0.
Do not, under any circumstances, install Secretary With Short Skirt 3.3. This is not a supported application for Wife 1.0 and is likely to cause irreversible damage to the operating system.
Best of luck,
Tech Support11 -
Somehow I feel like I personally owe Linus for git.
17:50 Colleague whispers "fuck" and the entire project we've worked on for the last half year responds with 404.
17:55 A quick diagnosis shows that she wrote "rm - rf ../" instead of "./" when she threw out her staging dir an thereby deleted everything.
17:58 git pull, everything is back.
18:15 everything is configured and we're up and running again.
**Alternative Timeline without Version control **
17:58 We start looking through Backup folders
18:20 We're fairly confident to have found the most up to date Backup in /var/backup/newback/v2/june/new/released/ and start copying back into the project directory.
19:30 Some files are missing we start patching shit up.
19:40 I realize how much work went down the drain and start strangling my colleague. The Api seems to do the most important things again.
20:00 My colleagues dead body is hidden and I'm 80% confident that the tasks depending on us should run.
Next day: They didn't run. Every nightly build failed, nobody can do anything useful.
A week later : Shits starting to work again, all lost files are replaced. Replacement for dead colleague still missing though.
It's moments like this that make you really appreciate the luxurys we have nowadays...5 -
How to hide your important files from people without making Hidden folders
1. Go to Desktop and create a new folder
2. Name the folder Internet Explorer
3. Change the folder icon to Internet Explorer
4. Keep it in a corner of the desktop
Now, no one will open internet explorer :D5 -
One comment from @Fast-Nop made me remember something I had promised myself not to. Specifically the USB thing.
So there I was, Lieutenant Jr at a warship (not the one my previous rants refer to), my main duties as navigation officer, and secondary (and unofficial) tech support and all-around "computer guy".
Those of you who don't know what horrors this demonic brand pertains to, I envy you. But I digress. In the ship, we had Ethernet cabling and switches, but no DHCP, no server, not a thing. My proposition was shot down by the CO within 2 minutes. Yet, we had a curious "network". As my fellow... colleagues had invented, we had something akin to token ring, but instead of tokens, we had low-rank personnel running around with USB sticks, and as for "rings", well, anyone could snatch up a USB-carrier and load his data and instructions to the "token". What on earth could go wrong with that system?
What indeed.
We got 1 USB infected with a malware from a nearby ship - I still don't know how. Said malware did the following observable actions(yes, I did some malware analysis - As I said before, I am not paid enough):
- Move the contents on any writeable media to a folder with empty (or space) name on that medium. Windows didn't show that folder, so it became "invisible" - linux/mac showed it just fine
- It created a shortcut on the root folder of said medium, right to the malware. Executing the shortcut executed the malware and opened a new window with the "hidden" folder.
Childishly simple, right? If only you knew. If only you knew the horrors, the loss of faith in humanity (which is really bad when you have access to munitions, explosives and heavy weaponry).
People executed the malware ON PURPOSE. Some actually DISABLED their AV to "access their files". I ran amok for an entire WEEK to try to keep this contained. But... I underestimated the USB-token-ring-whatever protocol's speed and the strength of a user's stupidity. PCs that I cleaned got infected AGAIN within HOURS.
I had to address the CO to order total shutdown, USB and PC turnover to me. I spent the most fun weekend cleaning 20-30 PCs and 9 USBs. What fun!
What fun, morons. Now I'll have nightmares of those days again.9 -
Actual rant time. And oh boy, is it pissy.
If you've read my posts, you've caught glimpses of this struggle. And it's come to quite a head.
First off, let it be known that WINDOWS Boot Manager ate GRUB, not the other way around. Windows was the instigator here. And when I reinstalled GRUB, Windows threw a tantrum and won't boot anymore. I went through every obvious fix, everything tech support would ever think of, before I called them. I just got this laptop this week, so it must be in warranty, right? Wrong. The reseller only accepts it unopened, and the manufacturer only covers hardware issues. I found this after screaming past a pretty idiotic 'customer representative' ("Thank you for answering basic questions. Thank you for your patience. Thank you for repeating obvious information I didn't catch the first three times you said it. Thank you for letting me follow my script." For real. Are you tech support, or emotional support? You sound like a middle school counselor.) to an xkcd-shibboleth type 'advanced support'. All of this only to be told, "No, you can't fix it yourself, because we won't give you the license key YOU already bought with the computer." And we already know there's no way Microsoft is going to swoop in and save the day. It's their product that's so faulty in the first place. (Debian is perfectly fine.)
So I found a hidden partition with a single file called 'Image' and I'm currently researching how to reverse-engineer WIM and SWM files to basically replicate Dell's manufacturing process because they won't take it back even to do a simple factory reset and send it right back.
What the fuck, Dell.
As for you, Microsoft, you're going to make it so difficult to use your shit product that I have to choose between an arduous, dangerous, and likely illegal process to reclaim what I ALREADY BOUGHT, or just _not use_ a license key? (Which, there's no penalty for that.) Why am I going so far out of my way to legitimize myself to you, when you're probably selling backdoors and private data of mine anyway? Why do I owe you anything?
Oh, right. Because I couldn't get Fallout 3 to run in Wine. Because the game industry follows money, not common sense. Because you marketed upon idiocy and cheapness and won a global share.
Fuck you. Fuck everything. Gah.
VS Code is pretty good, though.20 -
How to hide your important files from people without making Hidden folders?
1. Go to Desktop and create a new folder
2. Name the folder Internet Explorer
3. Change the folder icon to Internet Explorer
4. Keep it in a corner of the desktop
Now, no one will open internet explorer 😂7 -
How to hide your important files from people without making Hidden folders
1. Go to Desktop and create anew folder
2. Name the folder Internet Explorer
3. Change the folder icon to Internet Explorer
4. Keep it in a corner of the desktop
Now, no one will open internet explorer :D
Comment your ideas...16 -
Yes. Please. Stop putting hidden files in my home directory. It's not the place for it.
https://0x46.net/thoughts/2019/...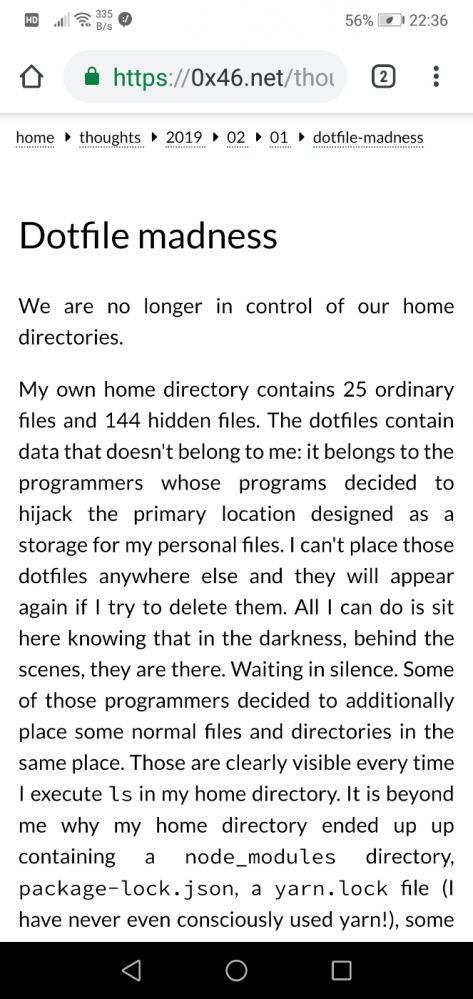 15
15 -
TL;DR I'm fucking sick and tired of Devs cutting corners on security! Things can't be simply hidden a bit; security needs to be integral to your entire process and solution. Please learn from my story and be one of the good guys!
As I mentioned before my company used plain text passwords in a legacy app (was not allowed to fix it) and that we finally moved away from it. A big win! However not the end of our issues.
Those Idiot still use hardcoded passwords in code. A practice that almost resulted in a leak of the DB admin password when we had to publish a repo for deployment purposes. Luckily I didn't search and there is something like BFG repo cleaner.
I have tried to remedy this by providing a nice library to handle all kinds of config (easy config injection) and a default json file that is always ignored by git. Although this helped a lot they still remain idiots.
The first project in another language and boom hardcoded password. Dev said I'll just remove before going live. First of all I don't believe him. Second of all I asked from history? "No a commit will be good enough..."
Last week we had to fix a leak of copyrighted contend.
How did this happen you ask? Well the secure upload field was not used because they thought that the normal one was good enough. "It's fine as long the URL to the file is not published. Besides now we can also use it to upload files that need to be published here"
This is so fucking stupid on so many levels. NEVER MIX SECURE AND INSECURE CONTENT it is confusing and hard to maintain. Hiding behind a URL that thousands of people have access to is also not going to work. We have the proof now...
Will they learn? Maybe for a short while but I remain sceptic. I hope a few DevrRanters do!7 -
How to hide your important files from people without making Hidden folders
1. Go to Desktop and create a new folder
2. Name the folder Internet Explorer
3. Change the folder icon to Internet Explorer.
4.Done8 -
I just ran a batch rename script in the console. What's so bad about this? I forgot that I had closed the previous console, which caused Win+4 to open a new one at the default location. Which is my home folder.
"Desktop"? Nah, you mean "file4.png". "Downloads"? No, that's "file6.png". "rclonesync-V2-master"? That's "file19.png" now.
Luckily I was able to restore it all, except for one folder, containing unreadable files with names like "data_0". I hope I didn't need that. And luckily it skipped all hidden files and folders.3 -
How you can hide your important files from people without making Hidden folders...
1. Go to Desktop and create a new folder
2. Name the folder Internet Explorer
3. Change the folder icon to Internet Explorer
4. Keep it in a corner of the desktop
Now, no one will open internet explorer 4
4 -
TL;DR; I unfucked a micro sd used by a nintendo switch with one command: fsck
I had noticed that the nintendo switch displayed way more storage usage then it should. I didn't mind at first, but at some point I couldn't download any games. When I checked I saw some ridiculous storage usage.
According to the system, all games summed up ~20Gb, but >100Gb was in use? Sounds retarded, so I did the following:
* Plugged it into laptop
* Spend one our searching for a way to to access this seemingly unknown filesystem
* Find out this filesystem is actually exFAT
* Find out that 2/3 sd adapters suck
* check filesystem with dust (A visually more pleasing version of du)
* Find 20Gb of files, nothing hidden or whatever
* run fsck
* "File system contains some errors want me to fix then?"
* "Sure"
* check usage
* 17%
As for the reason why this happened in the first place, my guess is that the switch labels the whole segment of the card as used before downloading a game and it something goes wrong, it shits itself.
Anyways, fsck is a pretty useful command. 1
1 -
I think I'm already blind. Or the liquor ate a chunk of my brain cells.
I just realized that devRant web version has different accent colours based on avatar's bg colour.
Earlier I realized I have disabled show hidden files feature on my file manager and thought there was no .htaccess file. 7
7 -
So this was going to be a comment but damn!!!!
Windows is seriously about making life harder for power users now, every fucking update lately is moving more easy to change things and fucking hiding them inside hidden menus or stupid links that don’t make sense. I mean fuck I just want to turn on dual screen with my laptop (because for some bizarre reason, just showing the desktop on the plugged in monitor is so hard to do automatically, especially since I just plugged a hdmi cable in) and the fucker was gone with nothing but a “detect screens” button before it would use an external screen.
Fuck I’m so close to pulling the plug on windows, but Linux just doesn’t sell me for daily use (yet... it’s getting there though)
The fucking forced updates (yes I consider a random bsod due to a system interrupt, then as it reboots magically has updates awaiting... a forced update) are starting to get to me, the fucking thing half crashing and not responding due to a network transfer of files (the fucker was 5GB)
If it wasn’t for my gaming needs and someone can show me a very good alternative to MS Visio (I haven’t really found one yet) then I would swap over and just adjust to the not so great (imo) desktop environments.5 -
EoS1: This is the continuation of my previous rant, "The Ballad of The Six Witchers and The Undocumented Java Tool". Catch the first part here: https://devrant.com/rants/5009817/...
The Undocumented Java Tool, created by Those Who Came Before to fight the great battles of the past, is a swift beast. It reaches systems unknown and impacts many processes, unbeknownst even to said processes' masters. All from within it's lair, a foggy Windows Server swamp of moldy data streams and boggy flows.
One of The Six Witchers, the Wild One, scouted ahead to map the input and output data streams of the Unmapped Data Swamp. Accompanied only by his animal familiars, NetCat and WireShark.
Two others, bold and adventurous, raised their decompiling blades against the Undocumented Java Tool beast itself, to uncover it's data processing secrets.
Another of the witchers, of dark complexion and smooth speak, followed the data upstream to find where the fuck the limited excel sheets that feeds The Beast comes from, since it's handlers only know that "every other day a new one appears on this shared active directory location". WTF do people often have NPC-levels of unawareness about their own fucking jobs?!?!
The other witchers left to tend to the Burn-Rate Bonfire, for The Sprint is dark and full of terrors, and some bigwigs always manage to shoehorn their whims/unrelated stories into a otherwise lean sprint.
At the dawn of the new year, the witchers reconvened. "The Beast breathes a currency conversion API" - said The Wild One - "And it's claws and fangs strike mostly at two independent JIRA clusters, sometimes upserting issues. It uses a company-deprecated API to send emails. We're in deep shit."
"I've found The Source of Fucking Excel Sheets" - said the smooth witcher - "It is The Temple of Cash-Flow, where the priests weave the Tapestry of Transactions. Our Fucking Excel Sheets are but a snapshot of the latest updates on the balance of some billing accounts. I spoke with one of the priestesses, and she told me that The Oracle (DB) would be able to provide us with The Data directly, if we were to learn the way of the ODBC and the Query"
"We stroke at the beast" - said the bold and adventurous witchers, now deserving of the bragging rights to be called The Butchers of Jarfile - "It is actually fewer than twenty classes and modules. Most are API-drivers. And less than 40% of the code is ever even fucking used! We found fucking JIRA API tokens and URIs hard-coded. And it is all synchronous and monolithic - no wonder it takes almost 20 hours to run a single fucking excel sheet".
Together, the witchers figured out that each new billing account were morphed by The Beast into a new JIRA issue, if none was open yet for it. Transactions were used to update the outstanding balance on the issues regarding the billing accounts. The currency conversion API was used too often, and it's purpose was only to give a rough estimate of the total balance in each Jira issue in USD, since each issue could have transactions in several currencies. The Beast would consume the Excel sheet, do some cryptic transformations on it, and for each resulting line access the currency API and upsert a JIRA issue. The secrets of those transformations were still hidden from the witchers. When and why would The Beast send emails, was still a mistery.
As the Witchers Council approached an end and all were armed with knowledge and information, they decided on the next steps.
The Wild Witcher, known in every tavern in the land and by the sea, would create a connector to The Red Port of Redis, where every currency conversion is already updated by other processes and can be quickly retrieved inside the VPC. The Greenhorn Witcher is to follow him and build an offline process to update balances in JIRA issues.
The Butchers of Jarfile were to build The Juggler, an automation that should be able to receive a parquet file with an insertion plan and asynchronously update the JIRA API with scores of concurrent requests.
The Smooth Witcher, proud of his new lead, was to build The Oracle Watch, an order that would guard the Oracle (DB) at the Temple of Cash-Flow and report every qualifying transaction to parquet files in AWS S3. The Data would then be pushed to cross The Event Bridge into The Cluster of Sparks and Storms.
This Witcher Who Writes is to ride the Elephant of Hadoop into The Cluster of Sparks an Storms, to weave the signs of Map and Reduce and with speed and precision transform The Data into The Insertion Plan.
However, how exactly is The Data to be transformed is not yet known.
Will the Witchers be able to build The Data's New Path? Will they figure out the mysterious transformation? Will they discover the Undocumented Java Tool's secrets on notifying customers and aggregating data?
This story is still afoot. Only the future will tell, and I will keep you posted.6 -
Github 101 (many of these things pertain to other places, but Github is what I'll focus on)
- Even the best still get their shit closed - PRs, issues, whatever. It's a part of the process; learn from it and move on.
- Not every maintainer is nice. Not every maintainer wants X feature. Not every maintainer will give you the time of day. You will never change this, so don't take it personally.
- Asking questions is okay. The trackers aren't just for bug reports/feature requests/PRs. Some maintainers will point you toward StackOverflow but that's usually code for "I don't have time to help you", not "you did something wrong".
- If you open an issue (or ask a question) and it receives a response and then it's closed, don't be upset - that's just how that works. An open issue means something actionable can still happen. If your question has been answered or issue has been resolved, the issue being closed helps maintainers keep things un-cluttered. It's not a middle finger to the face.
- Further, on especially noisy or popular repositories, locking the issue might happen when it's closed. Again, while it might feel like it, it's not a middle finger. It just prevents certain types of wrongdoing from the less... courteous or common-sense-having users.
- Never assume anything about who you're talking to, ever. Even recently, I made this mistake when correcting someone about calling what I thought was "powerpc" just "power". I told them "hey, it's called powerpc by the way" and they (kindly) let me know it's "power" and why, and also that they're on the Power team. Needless to say, they had the authority in that situation. Some people aren't as nice, but the best way to avoid heated discussion is....
- ... don't assume malice. Often I've come across what I perceived to be a rude or pushy comment. Sometimes, it feels as though the person is demanding something. As a native English speaker, I naturally tried to read between the lines as English speakers love to tuck away hidden meanings and emotions into finely crafted sentences. However, in many cases, it turns out that the other person didn't speak English well enough at all and that the easiest and most accurate way for them to convey something was bluntly and directly in English (since, of course, that's the easiest way). Cultures differ, priorities differ, patience tolerances differ. We're all people after all - so don't assume someone is being mean or is trying to start a fight. Insinuating such might actually make things worse.
- Please, PLEASE, search issues first before you open a new one. Explaining why one of my packages will not be re-written as an ESM module is almost muscle memory at this point.
- If you put in the effort, so will I (as a maintainer). Oftentimes, when you're opening an issue on a repository, the owner hasn't looked at the code in a while. If you give them a lot of hints as to how to solve a problem or answer your question, you're going to make them super, duper happy. Provide stack traces, reproduction cases, links to the source code - even open a PR if you can. I can respond to issues and approve PRs from anywhere, but can't always investigate an issue on a computer as readily. This is especially true when filing bugs - if you don't help me solve it, it simply won't be solved.
- [warning: controversial] Emojis dillute your content. It's not often I see it, but sometimes I see someone use emojis every few words to "accent" the word before it. It's annoying, counterproductive, and makes you look like an idiot. It also makes me want to help you way less.
- Github's code search is awful. If you're really looking for something, clone (--depth=1) the repository into /tmp or something and [rip]grep it yourself. Believe me, it will save you time looking for things that clearly exist but don't show up in the search results (or is buried behind an ocean of test files).
- Thanking a maintainer goes a very long way in making connections, especially when you're interacting somewhat heavily with a repository. It almost never happens and having talked with several very famous OSSers about this in the past it really makes our week when it happens. If you ever feel as though you're being noisy or anxious about interacting with a repository, remember that ending your comment with a quick "btw thanks for a cool repo, it's really helpful" always sets things off on a Good Note.
- If you open an issue or a PR, don't close it if it doesn't receive attention. It's really annoying, causes ambiguity in licensing, and doesn't solve anything. It also makes you look overdramatic. OSS is by and large supported by peoples' free time. Life gets in the way a LOT, especially right now, so it's not unusual for an issue (or even a PR) to go untouched for a few weeks, months, or (in some cases) a year or so. If it's urgent, fork :)
I'll leave it at that. I hear about a lot of people too anxious to contribute or interact on Github, but it really isn't so bad!4 -
Our team talking with a Mr. KnowItAll...
Mr. KIA: What concerns me about this huge system transference is that the devs won't give us the JS scripts files decompiled.
Mr. KIA again: I'm also concerned about Win XP end of support...
Us seeing each other: WTF is going on?!? Where are the hidden funny cameras...
A tip:
If you wanna pretend you know it all...you'll fail...
A humble dev never get humilliated1 -
In This Rant: A mildly satisfying piece of mind story.
Using code to prove yourself right is a hell of a drug.
A few weeks ago I whipped up a tiny program that downloads configs from hardware we manage. Since the vendor's API documentation is hidden behind a pay wall, my method of extraction is different. It results in bigger files, but testing showed it to still be valid.
Enter today. Interns at work downloaded a config to load onto a spare machine and it won't work.
"TheCapeGreek, your configs don't work"
I was confused since I tested the files when I built it and it worked. I am also currently fleshing out that download utility's features so the fear that I've been wasting the past 2 weeks on improvements is looming.
Last 15 minutes of the day and nothing else to do so I figured I might as well whip up a string comparer. The smaller file's content is scattered in the big file so a direct diff won't work.
Code it all, quick hardcoded proof of concept code, bit it got the job done. I was right, my bigger file is still correct!
Turns out the issue was with the machine they were configuring. They found this out before I finished my test code, so I'm off the hook already, but it was good to have piece of mind haha!1 -
I'm considering quitting a job I started a few weeks ago. I'll probably try to find other work first I suppose.
I'm UK based and this is the 6th programming/DevOps role I've had and I've never seen a team that is so utterly opposed to change. This is the largest company I've worked for in a full time capacity so someone please tell me if I'm going to see the same things at other companies of similar sizes (1000 employees). Or even tell me if I'm just being too opinionated and that I simply have different priorities than others I'm working with. The only upside so far is that at least 90% of the people I've been speaking to are very friendly and aren't outwardly toxic.
My first week, I explained during the daily stand up how I had been updating the readmes of a couple of code bases as I set them up locally, updated docker files to fix a few issues, made missing env files, and I didn't mention that I had also started a soon to be very long list of major problems in the code bases. 30 minutes later I get a call from the team lead saying he'd had complaints from another dev about the changes I'd spoke about making to their work. I was told to stash my changes for a few weeks at least and not to bother committing them.
Since then I've found out that even if I had wanted to, I wouldn't have been allowed to merge in my changes. Sprints are 2 weeks long, and are planned several sprints ahead. Trying to get any tickets planned in so far has been a brick wall, and it's clear management only cares about features.
Weirdly enough but not unsurprisingly I've heard loads of complaints about the slow turn around of the dev team to get out anything, be it bug fixes or features. It's weird because when I pointed out that there's currently no centralised logging or an error management platform like bugsnag, there was zero interest. I wrote a 4 page report on the benefits and how it would help the dev team to get away from fire fighting and these hidden issues they keep running into. But I was told that it would have to be planned for next year's work, as this year everything is already planned and there's no space in the budget for the roughly $20 a month a standard bugsnag plan would take.
The reason I even had time to write up such a report is because I get given work that takes 30 minutes and I'm seemingly expected to take several days to do it. I tried asking for more work at the start but I could tell the lead was busy and was frankly just annoyed that he was having to find me work within the narrow confines of what's planned for the sprint.
So I tried to keep busy with a load of code reviews and writing reports on road mapping out how we could improve various things. It's still not much to do though. And hey when I brought up actually implementing psr12 coding standards, there currently aren't any standards and the code bases even use a mix of spaces and tab indentation in the same file, I seemingly got a positive impression at the only senior developer meeting I've been to so far. However when I wrote up a confluence doc on setting up psr12 code sniffing in the various IDEs everyone uses, and mentioned it in a daily stand up, I once again got kickback and a talking to.
It's pretty clear that they'd like me to sit down, do my assigned work, and otherwise try to look busy. While continuing with their terrible practices.
After today I think I'll have to stop trying to do code reviews too as it's clear they don't actually want code to be reviewed. A junior dev who only started writing code last year had written probably the single worst pull request I've ever seen. However it's still a perfectly reasonable thing, they're junior and that's what code reviews are for. So I went through file by file and gently suggested a cleaner or safer way to achieve things, or in a couple of the worst cases I suggested that they bring up a refactor ticket to be made as the code base was trapping them in shocking practices. I'm talking html in strings being concatenated in a class. Database migrations that use hard coded IDs from production data. Database queries that again quote arbitrary production IDs. A mix of tabs and spaces in the same file. Indentation being way off. Etc, the list goes on.
Well of course I get massive kickback from that too, not just from the team lead who they complained to but the junior was incredibly rude and basically told me to shut up because this was how it was done in this code base. For the last 2 days it's been a bit of a back and forth of me at least trying to get the guy to fix the formatting issues, and my lead has messaged me multiple times asking if it can go through code review to QA yet. I don't know why they even bother with code reviews at this point.18 -
Any Windows Sysadmins here? I have a question for you - How do you do it?
I only very rarely have to do something that would fall under "Windows System Administration", but when I do... I usually find something either completely baffling, or something that makes me want to tear our my hair.
This time, I had a simple issue - Sis brought me her tablet laptop (You know, the kind of tablets that come with a bluetooth keyboard and so can "technically" be called a laptop) and an SD card stating that it doesn't work.
Plugging it in, it did work, only issue was that the card contained file from a different machine, and so all the ACLs were wrong.
I... Dealt with Windows ACLs before, so I went right to the usual combination of takeown and icacls to give the new system's user rights to work with the files already present. Takeown worked fine... But icacls? It got stuck on the first error it encountered and didn't go any further - very annoying.
The issue was a found.000 folder (Something like lost+found folder from linux?) that was hidden by default, so I didn't spot it in the explorer.
Trying to take ownership of that folder... Worked for for files in there, safe for one - found.000\dir0000.chk$Txf; no idea what it is, and frankly neither do I care really.
Now... Me, coming from the Linux ecosystem, bang my head hard against the table whenever I get "Permission denied" as an administrator on the machine.
Most of the times... While doing something not very typical like... Rooting around (Hah... rooting... Get it?! I... Carry on) the Windows folder or system folders elsewhere. I can so-so understand why even administrators don't have access to those files.
But here, it was what I would consider a "common" situation, yet I was still told that my permissions were not high enough.
Seeing that it was my sister's PC, I didn't want to install anything that would let me gain system level permissions... So I got to writing a little forloop to skip the one hidden folder alltogether... That solved the problem.
My question is - Wtf? Why? How do you guys do this sort of stuff daily? I am so used to working as root and seeing no permission denied that situations like these make me loose my cool too fast too often...
Also - What would be the "optimal" way to go about this issue, aside for the forloop method?
The exact two commands I used and expected to work were:
takeown /F * /U user /S machine-name /R
icacls * /grant machine-name\user:F /T7 -
Teaching advanced IT topics like programming or system management has become much harder in only about five years, because many 20 year olds do not know how to effectively work with the file system. I don't blame them: the Microsoft Office applications nudge you strongly towards storing everything in the Cloud (saving files locally requires extra clicks), and on Windows, the folders C:\Users and C:\ are almost hidden in he respective dialogs (open file, save file). Same on macOS. Students also keep loosing files. This used to be an excuse for not doing the work; nowadays, you're able to find the files on their systems by using appropriate tools (e.g. `find`, installed with Git Bash on Windows). And don't get me started on touch-typing... hell, those kids were fast ten years ago with a proper keyboard! Now they're fast with their smartphone, but painstakingly slow on an actual keyboard.8
-
macOS' Finder says I have 24 files and directories in my home directory. 'ls -lah | wc -l' says I have 172. That's a lot to keep hidden from me. :)2
-
Maybe I should automate downloading these google spreadsheets... neat there's an api for it, lemme just check the npm (https://npmjs.com/package/...).
Unpacked Size
49.2 MB
Total Files
900
Uhhh... fuck no? How about no fucking way? The nerve of these guys! Can you imagine being so up your own ass!? That's like 2kb of shit I care about, and the rest is bloat. Might even have some spyware hidden in there for how much NSA pays them.3 -
Moving files is emotionally easier than copying and deleting files, and moving eliminates the risk of selecting the wrong files at the deletion part.
I have read that it is safer to manually copy and manually delete files rather than to move it, but copying and deleting has a hidden risk that was not mentioned: selecting the wrong files for deletion.
Moving files feels like moving an obstacle from one room to another. The deletion part of copying and deleting feels like destroying something, which is an added emotional barrier.
Technically, copying and deleting is safer, since there is no risk of source files being deleted without having been transferred as a result of a device disconnecting or the buggy media transfer protocol (MTP) failing to load the entire file list. However, on mass storage devices, this pretty much never happened to me, and on MTP, data loss can be avoided by not moving folders but opening the source folders and selecting all files and moving those out. This prevents a parent folder with incompletely loaded file listing from being deleted.
However, something that is not considered about copying and deleting is that the risk of selecting the wrong files in the deletion step exists. One might end up selecting files that were never copied.
Not only is moving straightforward and time-saving, but it has no emotional barrier and the risk of selecting the wrong files to delete from the source is eliminated, since a proper file manager like Nemo or Windows Explorer (mass storage only, not MTP) only deletes a moved file from the source after it has been properly transferred. The user does not need to pay attention to select the correct files to delete, since the file manager already did it.4 -
Front-end web development is like a fucking cancer to me right now
I need the following behavior from my development environment if I don't want the webdev experience to destroy my sanity and tempt me into suicide by making me waste my valuable lifetime configuring shit that is ultimately meaningless to the software I'm trying to create:
- I should be able to open the webpage in the browser at localhost:<some-port>
- the page should refresh immediately as I save my files
- I should be able to import node modules installed with npm without using a script tag linking to some CDN (for instance, I want to do a get request with axios instead of the fetch API)
- I should be able to do this without spending more than two minutes reading the documentation for a tool that would enable me to do it, ideally without ever coming even close to touching a configuration file
Right now I know about browser-sync and webpack, or webpack-dev-server or some such fucking shit fuck fucking fuck.
browser-sync seems to fulfill most of these needs, except that I can't seem to bring npm modules into my application and import them. Webpack seems to be able to do this, but at the cost of slowly throwing my life away reading documentation for over-complicated configuration files that do not aid me in actual software creation and therefore do not interest me and never will, all in the hope that I *may* at some point dig out enough shit to find how to do such a use case (i.e. seamless, smooth web development) that to me feels reasonably common and expected.
Is there some tool that enables me to do *seamless*, pleasurable web development without the hassles of over-complication and over-engineering? Is there some hidden command for webpack that allows me to run such simple shit without ever needing to edit some pointless configuration file?
Please, I beg of you, let me know.8 -
Assuming Mac: Alfred for OS such as searching and opening apps, using spaces to setup smart project areas, divvy app to quickly size and move around the windows, terminal shortcuts to open files in the OS or in an editor, transmit for hidden files and dragging between panes and server + occasional mounting for preprocessing, inbox-zero mentality, a properly setup google drive app so you don't email forked files back and fourth, beanstalk for deployment of larger stacks, surge.sh for targeted front-end sites, Ember CLI or brunch for build pipelines, CodePen for UI experiments outside of the project, slack instead of email, pick up the telephone and just call for clarification more often, stylus is easier to maintain then scss, hire designers that actually know what their job is if you can. For arduous WordPress administration, rightclick open in new tab for everything - or half your time will be pushing the back button, wp-migrate pro, and in general try to get out of WP when you can.
-
Stupid shell globbing! I always forget that * does not include hidden files, then get all surprised that a 1:1 copy doesn't work the same, ugh!
I need to learn to use rsync dir-from/ dir-to/ instead of rsync ./* dir-to/...3 -
Fucking dot files...
Written a deployment script to reduce the amount of another dude's fuck ups when updating code on the server. Apparently the website executable automatically generated TLS certificates (let's encrypt) and placed them into the local hidden folder.
There is a limit on how many certificates a single domain can generate so... The website is down...7 -
The whole windows server + ms sql server ordeal is the biggest fucking joke I've ever seen in my time being a dev.
The ms sql dashboard uses a hidden user to access files and stuffs, so I spent 1 hour trying to make the dashboard's explorer to find the database dump file, only to find out that the file need to be owned by the hidden user. So
I spent about 1 hour trying to set the correct owner of the dump file, but to no avail, the explorer still couldn't pick it up. Then I spent another hour to set the correct owner for the containing folder. Finally, a 6 years old answer on SO point out that I should just put the fucking .bak file in their default folder, and voilà, the fucking thing works like a charm.
I can't get why Microsoft has to go out of their way making permission management on their os so fucking convoluted. The fucking usernames are a fucking mess, you have to go through a bunch of form to change just the owner of a file (please don't start me up with that running some command on powershell bullshit, I would rather deal with bad GUI than a badly designed CLI)
If I were to being positive though, Microsoft is actually one of a few tech companies having a good technical decision of moving their shits over Linux. -
Visual Studio is a fucking shitheap of an IDE and everyone who worked on it should be fucking incinerated.
I've been trying to get Unity to build my game for about a fucking hour and a half now, only to realize that it was a warning from a script that was causing it to fall flat on it's face.
So I deleted the script because it was a shitty script anyways, not much was being lost here, and I started building the game, and lo and behold, it was actually fucking doing something.
I went to go get a drink, only to come back to see that this stupid fucking engine gave me yet ANOTHER error that wasn't even from a script anywhere in my game's files.
It was fucking Visual Studio. It didn't even give me that concise of a fucking error, just "this file doesn't exist" or whatever hypercomplex bullshit it spat out at me.
So, I took to google, and found that I should open the solution file hidden within the uncompleted build, and upon doing so Visual Studio told me it needed to install some more shit in order to do so.
I decided to let it do it's thing, and you wanna know what the real kicker is?
I started writing this rant when it was at 25%.
I had started talking to my friend about how absolutely fucking garbage and slow this IDE is at around the point where it started downloading. It took fifteen fucking minutes for it to get to 25%.
I could uninstall and reinstall both Destiny 2 and Killing Floor 2, twice, in the time takes for this shitty fucking program to install its tumor of an update onto my system.
FUCK Visual Studio.
Fuck the person who conceived the idea of it.
And fuck every single person who supports it.
Every single person that thinks this fucking anathema of an IDE was a good idea should be incinerated.12 -
I need some clarity with the situation below.
I have my API ready.
Let's say I have a route /reset/token,
I want to be able to serve a html file with css and all that once I've processed the token internally.
I've not worked with the whole stack before so I've never really served files based on conditions i.e if the token is valid serve x else serve y.html
Also, I'm pretty sure node.js isn't the best for serving files.
So I'm taking another approach with nginx which is to implement /reset/token to serve the static file with it's coupled js file to query the API. Seems standard to me but I have this feeling that a prefilled html would be more secure than one with exposed js.
Is this the right way? Should I worry about my API calls being exposed via the js fil ? Is obfuscation the only way to handle this ? Is this the way everyone does it cause somehow I don't see the key js files in most sites. How are they hidden if so? Or are they?
I'm confused and also nginx won't let me rewrite /reset/token to something else without changing the browser url field. How do I prevent that ?1
