Ranter
Join devRant
Do all the things like
++ or -- rants, post your own rants, comment on others' rants and build your customized dev avatar
Sign Up
Pipeless API

From the creators of devRant, Pipeless lets you power real-time personalized recommendations and activity feeds using a simple API
Learn More
Comments
-
 qwwerty11915y@iiii that would be a case of direct attack. But there are plenty of other scenarios, in which you can have the files stored remotely as backups, you did a `cat` on the file while logging output of the terminal and the passwords reamins in clear in the logfile, etc...
qwwerty11915y@iiii that would be a case of direct attack. But there are plenty of other scenarios, in which you can have the files stored remotely as backups, you did a `cat` on the file while logging output of the terminal and the passwords reamins in clear in the logfile, etc...
Feels like almost nobody asks "does it have to be stored in the plaintext" and everybody setttles for "config requires elevated access so good enough, it works anyway and i don't care." -
@iiii You can lean on a wall hacking away on your phone for hours on end without anyone caring in most cities.
-
@iiii If you know someone's address and wifi and have reason to believe that it's worth the effort you can just walk up to the house, join the WiFi from the street and place your backdoors.
Related Rants

 when your code is a mess but everything work out in the end
when your code is a mess but everything work out in the end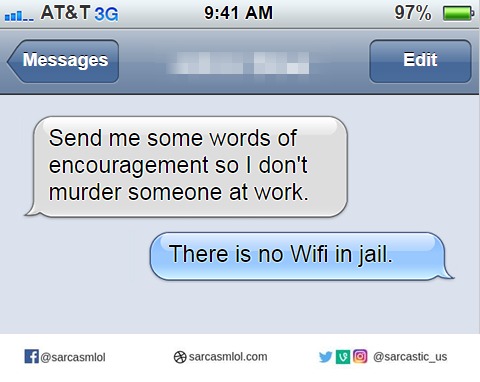 And that was enough encouragement
And that was enough encouragement When you keep getting +1s on a rant you posted a month ago.
When you keep getting +1s on a rant you posted a month ago.
Why is everybody using "wpa_passphrase" instead of "psk" in wpa_supplicant.conf is beyond me. You have an option to avoid plaintext passwords, the wpa_passphrase CLI tool even generates an entry for suppliant configuration, yet it seems nobody is using it.
rant
wifi
wpa