Ranter
Join devRant
Do all the things like
++ or -- rants, post your own rants, comment on others' rants and build your customized dev avatar
Sign Up
Pipeless API

From the creators of devRant, Pipeless lets you power real-time personalized recommendations and activity feeds using a simple API
Learn More
Comments
-
 wowotek57297yoh and also i got the wordpress hosting on that website so i also run the WPscan on them. and don't find anythting interestinf (for me atleast)
wowotek57297yoh and also i got the wordpress hosting on that website so i also run the WPscan on them. and don't find anythting interestinf (for me atleast) -
 2erXre524687yoh interesting task, that kind of work is very satisfying 😀
2erXre524687yoh interesting task, that kind of work is very satisfying 😀
ping
traceroute
try sql injection on the page
javascript injections
portscan for os fingerprinting
webserver scan for webserver fingerprinting
inspect cookies
try out nessus vulnerability scanner
get hands on with metasploit
and and and -
 2erXre524687ythink like an attacker: where are interfaces, how are they exposed, how are they protected, is there input validation...
2erXre524687ythink like an attacker: where are interfaces, how are they exposed, how are they protected, is there input validation... -
 Condor315487yI can't provide any precise information regarding how to do the pentest without the ability to recreate the target here or having explicit permission from the owner to conduct a pentest directly on their system. In both cases I'd have to do it for you which.. meh, I don't really feel like doing and it'd be cheating. The problem is that pentesting is a skill, a science, an art of its own. The only thing that all targets have in common is that you'll want to extract as much information as you can (reconnaissance) and based on that try to recreate the system locally to see what works and what doesn't. When you have a working attack, that's when you can fire shots on your target.
Condor315487yI can't provide any precise information regarding how to do the pentest without the ability to recreate the target here or having explicit permission from the owner to conduct a pentest directly on their system. In both cases I'd have to do it for you which.. meh, I don't really feel like doing and it'd be cheating. The problem is that pentesting is a skill, a science, an art of its own. The only thing that all targets have in common is that you'll want to extract as much information as you can (reconnaissance) and based on that try to recreate the system locally to see what works and what doesn't. When you have a working attack, that's when you can fire shots on your target.
Footprinting, not sure what you mean by that.. determining attack surface? OS fingerprinting (use p0f for that)? Scanning means port scanning and identifying services. You can use nmap for seeing what ports are open, but I tend to prefer ncat so that I can program in and randomize sleep timers between probing of each port to avoid tripping an IDS, and to select only the ports that I'm interested in (80, 443, 25, 993, etc etc). From there on out I like to use telnet to communicate with servers. You'll have to have a good understanding of the protocols that the servers speak because in telnet you'll be speaking it too. Enumeration, probably also part of the reconnaissance process. Information gathering, as much as you can. Gaining access, that's the actual exploitation. Try to upload a shell or in any way exploit one of their services to gain a shell under its user. This can be done by injecting certain data to the web server in case of the Apache Struts vulnerability for example (jexboss is a good tool for exploiting that). For different servers there's different vulnerabilities. Once you know the service and its version, you can look it up in the Exploit-DB. Once you've got shell access, you can try to use a kernel exploit to root the server. -
 wowotek57297y@Condor no i don't ask you to do my work. i just need the explaination which you did VERY GOOD (i wish i could ++ 11 times). i was very lost i don't understand a thing; which is which, what is this, and why is that? and so on and so forth. since this is the first meeting and he only gave subject syllabus
wowotek57297y@Condor no i don't ask you to do my work. i just need the explaination which you did VERY GOOD (i wish i could ++ 11 times). i was very lost i don't understand a thing; which is which, what is this, and why is that? and so on and so forth. since this is the first meeting and he only gave subject syllabus
so apparently i found this server don't Cipher its SSL (i don't understand actually, but the terminal said so). and i can access telnet via port 22 and it stop doing anything after:
...
Escape Character ^]
OpenSSH
|
...
as soon as i enter something it said Wrong Protocol-- or something like that, im in bed now -- and then disconnect.
my target was to connect to the server via SSH which the mentor said it possible. as soon as i got there i can figure out my exploits. but now i am running around in circles in reconnaissance and enumerating. -
 Condor315487y@wowotek ooh, SSH? If you've got the keys to login to the server, just do it that way. Otherwise you'll be looking to bruteforce your way in, which is difficult. Servers on the internet get their sshd bruteforced all the time, but with little success. And when the server doesn't accept passwords (which the server notifies you of but the many hekorman who probe these servers on the internet don't know how to use apparently 🙃), it's impossible. So yeah.. ideally you'd have keys. Then you can login and go ahead with the rooting process, or maybe the keys are already authorized to login as root to begin with. Not sure how that'd be a pentest though 🤔 I mean SSH is something that's used all the time by sysadmins to login to their remote servers... There's no hackery involved in that 🤨
Condor315487y@wowotek ooh, SSH? If you've got the keys to login to the server, just do it that way. Otherwise you'll be looking to bruteforce your way in, which is difficult. Servers on the internet get their sshd bruteforced all the time, but with little success. And when the server doesn't accept passwords (which the server notifies you of but the many hekorman who probe these servers on the internet don't know how to use apparently 🙃), it's impossible. So yeah.. ideally you'd have keys. Then you can login and go ahead with the rooting process, or maybe the keys are already authorized to login as root to begin with. Not sure how that'd be a pentest though 🤔 I mean SSH is something that's used all the time by sysadmins to login to their remote servers... There's no hackery involved in that 🤨 -
 wowotek57297y@Condor it's actually hidden in the first place since the port are missing and it's routed from subdomain. so that (maybe) what mentor said it's possible; i forgot to mention that this server are built for pentest training and assignments. so they said it is easy, but i still don't get where is the easy part -_-. i am no tester just plain developer want to riddle around in networking, but when i do the recon and enum i know there are a lot of security holes there. but i don't know how to exploit them.
wowotek57297y@Condor it's actually hidden in the first place since the port are missing and it's routed from subdomain. so that (maybe) what mentor said it's possible; i forgot to mention that this server are built for pentest training and assignments. so they said it is easy, but i still don't get where is the easy part -_-. i am no tester just plain developer want to riddle around in networking, but when i do the recon and enum i know there are a lot of security holes there. but i don't know how to exploit them.
are the telnet thing are crucial? can i exploit that? -
 Condor315487y@wowotek telnet is mostly what I'd use for determining what server is running there. Every server speaks their protocols ever so slightly differently. Many servers do introduce themselves in telnet just by saying what they are though. For example, my mail server here is Postfix. Normally it'd also say that it's running on Ubuntu but I've told the server to omit that during its setup.
Condor315487y@wowotek telnet is mostly what I'd use for determining what server is running there. Every server speaks their protocols ever so slightly differently. Many servers do introduce themselves in telnet just by saying what they are though. For example, my mail server here is Postfix. Normally it'd also say that it's running on Ubuntu but I've told the server to omit that during its setup.
The server machine being routed doesn't really matter as long as you can reach it. If it's something that's built for pentesting, maybe it's running Metasploitable? That's a distribution that's designed to be vulnerable.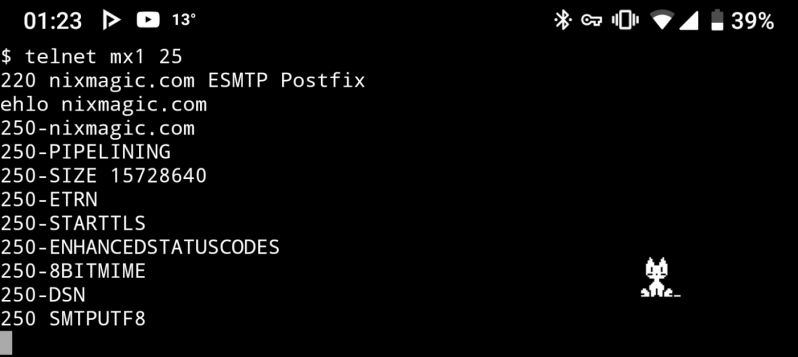
-
 Condor315487y@wowotek Try logging into the server via ssh. Also check what other ports are open and if they're exploitable.. and if it's Metasploitable, just look for something generic that can exploit something in that distribution and that way you may be able to wing it. Anyway, OpenSSH 7.4 is pretty generic, most distributions have that. Look for more info that can uniquely identify this one. And for every service that you find the version for, look it up in the Exploit-DB. And be sure to also ask the teacher for more help if you need it. For me it's been a while since I've done this sort of thing.. so yeah.
Condor315487y@wowotek Try logging into the server via ssh. Also check what other ports are open and if they're exploitable.. and if it's Metasploitable, just look for something generic that can exploit something in that distribution and that way you may be able to wing it. Anyway, OpenSSH 7.4 is pretty generic, most distributions have that. Look for more info that can uniquely identify this one. And for every service that you find the version for, look it up in the Exploit-DB. And be sure to also ask the teacher for more help if you need it. For me it's been a while since I've done this sort of thing.. so yeah. -
 wowotek57297y@xzvf well, i already sent the report to my lecturer. so this is assignment no more. can you teach me just a little bit more? i really interested in this topic.
wowotek57297y@xzvf well, i already sent the report to my lecturer. so this is assignment no more. can you teach me just a little bit more? i really interested in this topic.
originally the lecturer only gave me the website. and start from there.
Related Rants


 Someone's going to get a surprise tonight 🤣
Someone's going to get a surprise tonight 🤣 Last night I was exploring the feasibility of cracking the WPA2 key of my own router at home. I set out on a l...
Last night I was exploring the feasibility of cracking the WPA2 key of my own router at home. I set out on a l...
got first assignment on my first meet on Network Security. it require to pentest one unsecured specified website. yet they don't tell me shit about anything just try it.
i need to :
1. Footprint
2. Scanning
3. Enumeration
4. Gaining Access (previledges raising?) (bonus)
suppose : <target-website> is x
i've done this:
1. whois x
2. got the ipaddress via :
host x
3. nmap -F ip.of.x
my head is already spinning, i need to know what BASICLY each of what i've done. i only get that 'whois' get the information about that domain, 'host' is used to know the target ip address and nmap to find what are the open ports. i don't know what else should i do. need help :(
question
pentest