Ranter
Join devRant
Do all the things like
++ or -- rants, post your own rants, comment on others' rants and build your customized dev avatar
Sign Up
Pipeless API

From the creators of devRant, Pipeless lets you power real-time personalized recommendations and activity feeds using a simple API
Learn More
Comments
-
 Root772337yI am so incredibly surprised you survived that.
Root772337yI am so incredibly surprised you survived that.
Spying on and fucking with the XO? And taking credit for it in front of both him and the sysadmin? AND burning classified documents to dvd?
Holy crap.
But you absolutely proved the network was shit in order to force the responsible party to make it better, so. I would have let you off (and punished the sydadmin severely), but the average person would be livid and blame you for everything. (Including the sysadmin being terrible because people are useless, illogical pieces of shit.)
Holy crap you got lucky. -
@Root I was surprised too, but hey, that's young foolishness for you :)
The fact is, besides the sysad, none understood the severity of the problem. I had to pull some Hollywood-like stunts to MAKE them understand. Besides, with the security the way it was, I seriously doubt anyone had any idea what to do. The major problem was, that was a network in a military academy. I've seen much better security on much less prestigious and funded places.
Frankly, it was just... embarrassing. Truly embarrassing. What I did was just some monkeys-with-machine-guns exploitation. Nothing barred me. No separate networks for critical areas, no actual security on the PCs, NOTHING.
Can you imagine such a place as being security-conscious, security-aware, security-ANYTHING?
While it was fun, it was just my IPSec puberty. And I got an ideal playground for that :P -
 Albatross277yI started a new job a while ago, and naturally I immediately began an audit of all the servers on the network. I found mostly what I expected: a couple of Server 2003s and a bunch of 2008s and up, but then I RDPed into a server with a distinct lack of documentation and was greeted by the Windows 2000 login screen. Not SERVER 2000, just Windows 2000. If I find something running on NT 4 I'm fucking done.
Albatross277yI started a new job a while ago, and naturally I immediately began an audit of all the servers on the network. I found mostly what I expected: a couple of Server 2003s and a bunch of 2008s and up, but then I RDPed into a server with a distinct lack of documentation and was greeted by the Windows 2000 login screen. Not SERVER 2000, just Windows 2000. If I find something running on NT 4 I'm fucking done. -
@Albatross Ouch, that sounds a bit chaotic in and on itself. I mean, you have, say, 4 types of OSes to look after, 2 of which are unsupported, at 2020 Windows 2008 and Windows 7 will be unsupported...
Sounds like a ticking bomb. -
 Albatross277y@bladedemon Oh, definitely. I've got the entire spectrum from 2000 to 2016 to work with, plus homebrewed applications and ancient third-party software. But, a sysadmin's gotta have work to do, right?
Albatross277y@bladedemon Oh, definitely. I've got the entire spectrum from 2000 to 2016 to work with, plus homebrewed applications and ancient third-party software. But, a sysadmin's gotta have work to do, right?
Related Rants

 Did you say security?
Did you say security?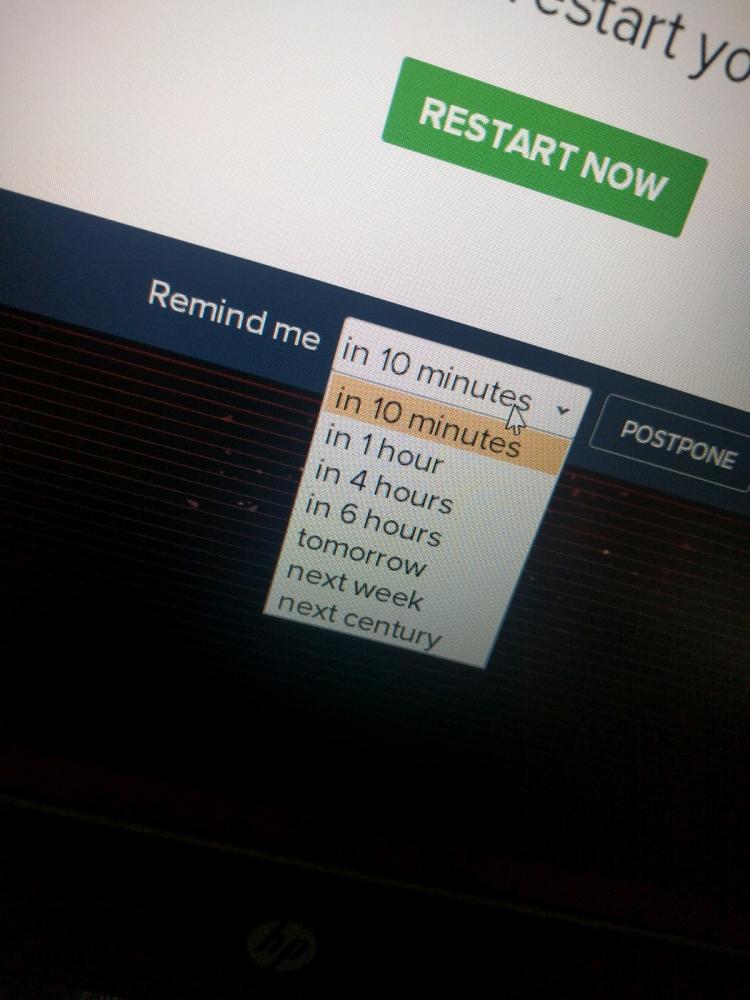 10 points for next century option.
10 points for next century option.
Navy story continued.
And continuing from the arp poisoning and boredom, I started scanning the network...
So I found plenty of WinXP computers, even some Win2k servers (I shit you not, the year was 201X) I decided to play around with merasploit a bit. I mean, this had to be a secure net, right?
Like hell it was.
Among the select douchebags I arp poisoned was a senior officer that had a VERY high idea for himself, and also believed he was tech-savvy. Now that, is a combination that is the red cloth for assholes like me. But I had to be more careful, as news of the network outage leaked, and rumours of "that guy" went amok, but because the whole sysadmin thing was on the shoulders of one guy, none could track it to me in explicit way. Not that i cared, actually, when I am pissed I act with all the subtleness of an atom bomb on steroids.
So, after some scanning and arp poisoning (changing the source MAC address this time) I said...
"Let's try this common exploit, it supposedly shouldn't work, there have been notifications about it, I've read them." Oh boy, was I in for a treat. 12 meterpreter sessions. FUCKING 12. The academy's online printer had no authentication, so I took the liberty of printing a few pages of ASCII jolly rogers (cute stuff, I know, but I was still in ITSec puberty) and decided to fuck around with the other PCs. One thing I found out is that some professors' PCs had the extreme password of 1234. Serious security, that was. Had I known earlier, I could have skipped a TON of pointless memorising...
Anyway, I was running amok the entire network, the sysad never had a chance on that, and he seemed preoccupied with EVERYTHING ELSE besides monitoring the net, like fixing (replacing) the keyboard for the commander's secretary, so...
BTW, most PCs had antivirus, but SO out of date that I didn't even need to encode the payload or do any other trick. An LDAP server was open, and the hashed admin password was the name of his wife. Go figure.
I looked at a WinXP laptop with a weird name, and fired my trusty ms08_067 on it. Passowrd: "aaw". I seriously thought that Ophcrack was broken, but I confirmed it. WTF? I started looking into the files... nothing too suspicious... wait a min, this guy is supposed to work, why his browser is showing porn?
Looking at the ""Deleted"" files (hah!) I fount a TON of documents with "SECRET" in them. Curious...
Decided to download everything, like the asshole I am, and restart his PC, AND to leave him with another desktop wallpaper and a text message. Thinking that he took the hint, I told the sysadmin about the vulnerable PCs and went to class...
In the middle of the class (I think it was anti-air warfare or anti-submarine warfare) the sysad burst through the door shouting "Stop it, that's the second-in-command's PC!".
Stunned silence. Even the professor (who was an officer). God, that was awkward. So, to make things MORE awkward (like the asshole I am) I burned every document to a DVD and the next day I took the sysad and went to the second-in-command of the academy.
Surprisingly he took the whole thing in quite the easygoing fashion. I half-expected court martial or at least a good yelling, but no. Anyway, after our conversation I cornered the sysad and barraged him with some tons of security holes, needed upgrades and settings etc. I still don't know if he managed to patch everything (I left him a detailed report) because, as I've written before, budget constraints in the military are the stuff of nightmares. Still, after that, oddly, most people wouldn't even talk to me.
God, that was a nice period of my life, not having to pretend to be interested about sports and TV shows. It would be almost like a story from highschool (if our highschool had such things as a network back then - yes, I am old).
Your stories?
rant
navy story
security
passwords