Join devRant
Do all the things like
++ or -- rants, post your own rants, comment on others' rants and build your customized dev avatar
Sign Up
Pipeless API

From the creators of devRant, Pipeless lets you power real-time personalized recommendations and activity feeds using a simple API
Learn More
Search - "passwords"
-
My school.
We have free WiFi access, but you need to login into your personal student account to use it.
Turns out, SQL Injection works.
It gets worse.
Table name "schueler".
SELECT *
Well.
Got all data on all students.
Name, address, phone number, passwords in plain.
I reported it using an anonymous email. Partially fixed. Standard quotes now get eacaped. Still, passwords are now MD5.47 -
Creating a new account is always fun...
"This Is My Secure Password" <-- Sorry, no spaces allowed.
"ThisIsMySecurePassword" <-- Sorry, Passwords must include a number
"ThisIsMySecurePassword1" <-- Sorry, Passwords must include a special character
"ThisIsMySecurePassword 1" <-- Sorry, no spaces allowed
"ThisIsMySecurePassword%1" <-- Sorry, the % character is not allowed
"ThisIsMySecurePassword_1" <-- Sorry, passwords must be shorter than 16 characters
"Fuck" <-- Sorry, passwords must longer than 6 characters
"Fuck_it" <-- Sorry, passwords can't contain bad language
"Password_1" <-- Accepted.24 -
I was reviewing one dev's work. It was in PHP. He used MD5 for password hashing. I told him to use to password_hash function as MD5 is not secure...
He said no we can't get a password from MD5 hashed string. It's one way hashing...
So I asked him to take couple of passwords from the users table and try to decode those in any online MD5 decoder and call me after that if he still thinks MD5 is secure.
I have not got any call from him since.18 -
Hope it's not a repost but this is brilliant... although putting it up in my office wouldnt change anything. Password123 was there before me and it'll be there after me.
 8
8 -
"I really love the new $3k Fortigate firewall switch you bought for the office after our chat about security but it doesn't change the fact that you can access any computer in the company using Password123" - me13
-
What the actual fuck? Person (or people!) who devised this password policy, you are an idiot (or idiots - all of you). You are stupid and insane and have no idea about security or user experience.
 14
14 -
Me: *enters password on phone (long PIN)*
Person next to me is looking at my phone WHILE I enter my password, and as I look at him, he doesn't even turn away and even has the nerve to say:
"Wow, why do you have such a long password!"
Μy answer: "Because of security reasons."
What I actually wanted to say:
"Because of pieces of SHIT like you who can't keep their eyes to themselves, even when PASSWORDS are involved, you FUCK! Guess why everytime I enter a password in public, I have to dim my screen and turn my screen sideways? Because of fuckheads like you, not knowing shit about privacy and security! Fuck you!"7 -
Mistyping one character wrong in a password and hitting backspace until I am sure I’ve deleted the entire Wikipedia.
Then starting all over again.3 -
PM: We need security on signup, the password entry should contain "A capital letter, 2 numbers, a symbol, an inspiring message, a spell, a gang sign, a hieroglyph and the blood of a virgin."
ME: 8
8 -
Way to many...
- Passwords stored in plain text on the year 2014
- Not supporting HTTPS because to expensive
- Hidden admin URLS
- Databases available all over the internet
- Client Side validation
- IoT5 -
Guy: I don't trust password managers
Me: so how do you remember passwords?
Guy: oh, I just keep them in a note in the iPhone notes app/iCloud.7 -
Just went skydiving. Realized I probably should have left behind all my clients' site admin passwords in case my chute didn't open. Turns out I'm still alive so no harm done.8
-
!rant
IDE or text editors ?
I tbh use notepad++ to work on text files and encrypted files for passwords lol 22
22 -
My dad believes in hiding his passwords in plain sight
He puts them all in a
readme.txt sitting next to the Canon printer exe file. 😂2 -
Writing customer passwords fulltext into the prod database because "it's easier to associate them with the user"2
-
A ecom website which sales premium gold product from 50k to 170k INR.
database : mysql
all passwords and user ID's are saved in plain text.23 -
'Incorrect password.'
"I must've forgotten the password. Let me change it".
'Old and new passwords cannot be same'
o_O 14
14 -
Today FileZilla saved my life by storing all site connection passwords in base64
Without it we'd have lost access to an old production server 👌6 -
Gets email from work
"New password policy introduced from next month
Passwords will have to include:
- a capital
- a lower case
- a number
- a symbol
- be at least 8 characters
Passwords will be be changed every 60 days with a new password not previously used"
Everyone starts moaning, there I am laughing as I'm in Linux and off their domain controller, and my windows laptop is a BYOD laptop and they don't want it on the domain :D27 -
My insurance company sending me the payment slip by post with my username and password to the online account for easy access. How sweet of them. 10/10 customer satisfaction.
I see your "Storing passwords in plain text". I raise you to "sending passwords via post in plain text". 17
17 -
!!pointless story
Bug report comes in from a coworker. "Cloudinary uploads aren't working. I can't sign up new customers."
"I'll look into it" I say.
I go to one of our sites, and lo! No Cloudinary image loads. Well that can't be good.
I check out mobile app -- our only customer-facing platform. None of the images load! Multiple "Oops!" snackbars from 500 errors on every screen / after every action.
"None of our Cloudinary images load, even in the mobile app," I report.
Nobody seems to notice, but they're probably busy.
I go to log into the Cloudinary site, and realize I don't have the credentials.
"What are the Cloudinary credentials, @ceo?" I ask.
I'm met with more silence. I use this opportunity to look through the logs, try different URLs/transforms directly. Oddly, everything seems fine except on our site.
I check Slack again, and see nothing's changed, so I set about trying to guess the credentials.
Let's see... the ceo is basically illiterate when it come to tech, so it's probably not his email. It's a startup, and custom emails for things cost money, and haven't been a thing here forever, so it's probably oen of the CTO's email aliases. he likes dots and full names so that narrows it down. Now for the password.... his are always crappy (so they're "easy to remember") and usually have the abbreviated company name in them. He also likes adding numbers, generally two-digit numbers, and has a thing for 7s and 9s. Mix in some caps, spaces, order...
Took me a few minutes, but I managed to figured it out.
"Nevermind, I guessed them." I reported.
After getting into Cloudinary, I couldn't find anything amiss. Everything looked great. No outage warnings, metrics looked fine, images all loaded. Ex-cto didn't revoke payment or cancel the account.
I checked our app; everything started loading -- albeit slowly.
I checked the aforementioned site; after a few minutes, everything loaded there, too.
Not sure what else to do, and with everything appearing to work, I said "Fixed!" and closed the issue.
About 20 minutes later, the original person said "thanks" -- never did hear anything from the ceo. I've heard him chatting away in the other room the entire time.
Regardless, good thing for crappy passwords, eh?15 -
My school stores everyone's username and passwords (including admins) in plain text on a Windows 2007 server that they remote desktop into.8
-
!security
(Less a rant; more just annoyance)
The codebase at work has a public-facing admin login page. It isn't linked anywhere, so you must know the url to log in. It doesn't rate-limit you, or prevent attempts after `n` failures.
The passwords aren't stored in cleartext, thankfully. But reality isn't too much better: they're salted with an arbitrary string and MD5'd. The salt is pretty easy to guess. It's literally the company name + "Admin" 🙄
Admin passwords are also stored (hashed) in the seeds.rb file; fortunately on a private repo. (Depressingly, the database creds are stored in plain text in their own config file, but that's another project for another day.)
I'm going to rip out all of the authentication cruft and replace it with a proper bcrypt approach, temporary lockouts, rate limiting, and maybe with some clientside hashing, too, for added transport security.
But it's friday, so I must unfortunately wait. :<13 -
No, MD5 hash is not a safe way to store our users' passwords. I don't care if its been written in the past and still works. I've demonstrated how easy it is to reverse engineer and rainbow attack. I've told you your own password for the site! Now please let me fix it before someone else forces you to. We're too busy with other projects right now? Oh, ok then, I'll just be quiet and ignore our poor security. Whilst I'm busy getting on with my other work, could you figure out what we're gonna do with the tatters of our client's business (in which our company owns a stake) in the aftermath of the attack?7
-
Pure evil and geniusness, this is a must read for JavaScript developers and security enthusiasts !
https://hackernoon.com/im-harvestin... 9
9 -
left a company over 3 years ago because they wanted me to dumb my code down so that the other devs could understand it. they wouldn't allow me to use classes in my code lol. anyway, 3+ years later figured I would try to log in to some of the admin panels... passwords still the same. MySQL dbs... passwords the same... cpanel... passwords the same. smh. even if I still worked there the passwords should be changed every so often. top notch security right there. funniest part is they don't even do backups or use VCS for the code. sad sad company. glad I'm no longer there. my personal projects have more security, redundancy and fail over lol4
-
Girlfriend: There are so many passwords to remember, man. What's my amazon password, baby?
Me: Just use a password manager?
Girlfriend: That sort of thing exists?12 -
Wtf is this? Austrian telecom company admits storing all passwords in clear text saying they are too secure to be hacked....
Read here:
https://twitter.com/tmobileat/...9 -
I used to work in a call center for a local hospital.
One night, all of our lines are swamped. Literally no time for a break between phone calls, +15 minute wait times. I answer the next call:
Me: "Its a marvelous Monday at AskIT, how may I help you?"
Doctor: "This is Dr. [Noone Care]. I need you to fix my password now."
Me: "Absolutely! You should be able to enter a new password now."
Doctor: "MY HANDS ARE NOT FOR PASSWORDS, MY HANDS ARE FOR SURGERY!"
😩 So glad I don't work for doctors anymore. Oh and the best part is, he had selected the general phone queue, rather than the doctor queue (~3 minute wait time instead).7 -
Bank forces me to change my password. Figured I'd use Safari's strong password generation. Submit. Password changed.
Go to log in with new password. Password not saved because I had previously told Safari not to save this site's password.
Okay… so the strong password you JUST generated and submitted without showing me is now my banking password but neither of us knows what it is?
Fucking brilliant. I mean at least let me fucking copy it so I can store it in my password manager. The most hilarious thing is the message that appeared on the generated password saying my password would be available from Safari preferences. Yup, nope. Nothing there except a note saying no passwords will be stored for this site.
This is the state of Apple in 2018, folks. Fucking sad.16 -
I used PHPMailer to send emails to a client's website user. SMTP host is smtp.gmail.com.
web was hosted on Bluehost. I found out that mailer was not working. I enabled verbose output and to my surprise I found out that Bluehost was intercepting my mail and responding with
220-We do not authorize the use of this system to transport unsolicited, 220 and/or bulk e-mail
when i was explicitly using smtp.gmail.com. Not only they were intercepting but also They were trying my credentials against its own smtp server and then showing me that authentication failed.
When i contacted chat they asked me to tell last 4 characters of Bluehost account password to verify ownership.
Dude do they have passwords in plaintext.🤔5 -
I started using Keepass and changed all my passwords to auto generated passwords. Somehow, my PC crashed before I saved the database. That was the day, where I lost access to my primary email address.5
-
- Guys, today the security auditors are coming, don't forget to remove your sticky notes with passwords. And for God's sake wear the badges for a least a day!
-
Relying on Chrome to remember all my passwords. I have no idea any more what passwords I have chosen for several important sites. Don't even want to think about what happens the day I switch PC or reset that cache somehow.10
-
Security rant ahead - you have been warned.
It never fails to amuse and irritate me that, despite being in the 2019 supposed information age, people still don't understand or care about their security.
I've travelled to a lot of ports and a lot of countries, but, at EVERY port, without fail, there will be at least one wifi that:
- Has default name/password that has been cracked already (Thomson/SpeedTouch/Netfaster etc)
- Has a phone number as password (reduces crack time to 15-30 mins)
- Someone, to this day, has plain old WEP
I am not talking about cafeteria/store wifi but home networks. WTF people?! I can check my email (through VPN, of course) but it still bugs me. I have relented to try and snoop around the network - I can get carried away, which is bad. Still...
The speed is great though :P9 -
Today Comcast told me my account password over the phone... Fucking Comcast stores passwords in plaintext.8
-
Notice :
Citizens are advised to store all their passwords into either text files or Google Keep, OneNote, Evernote so that it would come in handy whenever you forget the Password.
Please share this among your family and friends.
Have a nice day :)11 -
I have bank accounts with 5 different banks.
I HAVE TO use 4-5 different government websites.
Every fucking place: you cannot use these "~-/;^"(some others too) symbols in your password.
Are you freaking fucking kidding me!! And all of them have a limit of 12or15 characters.
If this wasn't mind numbingly stupid enough, they fucking go ahead and force you to change password every fucking month or two.
THIS IS NOT SECURITY. YOU SHOULDN'T FORCE SOMEONE TO LIMIT THERE PASSWORDS TO:
- CERTAIN CHARACTERS
- A 15 CHARACTER SIZE LIMIT
- THRN OVERTHAT, FORCE TO CHANGE PASSWPRDS PERIODICALLY.
ALL THE 5 MAJOR FUCKING BANKS IN INDIA.
FUUUUUCCCCKKKKK YOUU 🖕11 -
This “Caps lock is on” feature when typing in passwords was probably very angrily added by a developer after several failed log in attempts.11
-
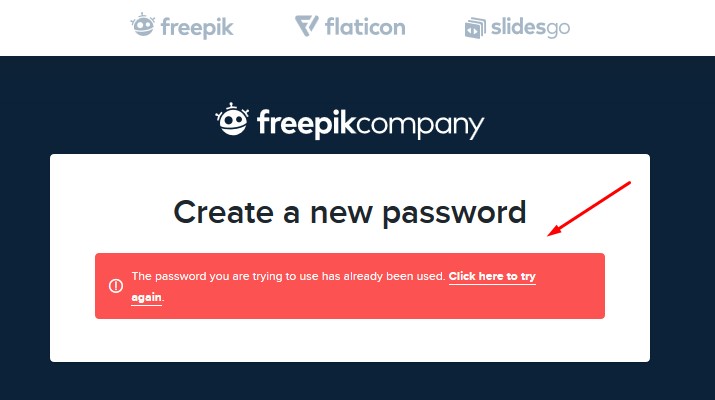
Anyone ever entered a password and it keeps saying wrong password, so you decide to reset the fucking password and now the problem is ....the systems/website tells you that you can't reset the password to your current password or a password you are already using... like okay what the fuck!!!!!.....2
-
Boy, sure wish I knew about this before putting all of my passwords into lastpass. This looks way more secure. Handwriting in English is pretty much as good as encryption.
 9
9 -
when you work for a place that has plain text passwords in the db. lol
I asked head of department if he knew what salting/hashing passwords was and he said no.... is this real life?19 -
Storing passwords in plain text.
To be fair, it was a feature requested by the client, but still...
At least encrypt it man.6 -
Wrost security fix ever seen?
encode that passwords in base64 is safe enough.
And keep the password.txt accessible from internet it's safe because nobody know that it exists...6 -
Recently, one of our passwords was accidently published on a public page for a few minutes before it was noticed and removed. Unfortunately, this password opens nearly every locked account so it's a pretty big deal.
Management was informed of this mistake and told that we should change the passwords as well as implement a few other protocols to make sure this doesn't happen again including things like unique passwords, more secure passwords, using a password manager, etc.
Their response? It wasn't online long, probably no one saw it. There will be no changes in how we handle ours or our clients' secure passwords.6 -
Unencrypted, plain text passwords stored in SQL, from lowest role all the way up through Admin. In the same system, they had a "backdoor" password that would log in any user...
-
Tesco.com, you deep pool of creamy baby shit. I've tried to reset my password three times already. My new password has way more entropy than your mathematically impaired rules command, but apparently using password managers is bad practice. It should be about having at least one special character, not EXACTLY one. I've got lots of uppercase characters, not PRECISELY one.4
-
Are there any website or public list that shame companies and websites for sending passwords in plaintext whenever we tend to reset the password?6
-
My trusty password manager, so I dont have to remember those shitty passwords. (its however being rebuilt after a failed firmware upgrade who bricked it).
 6
6 -
Our sysadmin just wrote our new work account passwords on our office whiteboard, visible to everyone... Now that's how you create chaos2
-
The "Change Password" function autofilled the old password. Dev told be it didn't matter because "if you set the field type to password you can't see it".4
-
former boss wrote three cyber-defense books. had his "collections" team sending plaintext passwords to high-side clients over unsecured email4
-
Best decisions:
- Switching to Linux entirely
- Learning how to use the shell
Worst decisions:
- Using Windows 8
- Hardcoded passwords (I built a small thing for myself, don't judge)3 -
Never ever have a tab open on production server database. Changed all users passwords by mistake. Thought was my test database.2
-
So, I just learned that all clients connected with TeamViewer to the same server share all their clipboards to everybody. I now have a lot of passwords that I shouldn't have.
-
If($password = $password2) {
//login
}
Keep in mind that password is the salted and hashed input and password2 is the Salter and hashed pw in the database...
Who needs passwords am I right?8 -
New password cannot be one of your four previous passwords.
Password must conatin upper and lower case characters, at least two numbers and two special characters
Password cannot contain five or more consecutive letters of username.
Password cannot include any _illegal patterns_.
Locked out of your system? Drive over to HQ and ask the admins to reset your password in person.6 -
Finally did the switch to Firefox and migrated my passwords to a proper password manager. Bye chrome!14
-
When your client wants you to store password in plain text and it makes your life easier but it still feels really wrong12
-
Password policy for a big water company site in Spain.
Translation: Between 6 and 10 characters (only letters and numbers, no spaces)
In guess they have a VARCHAR(10) password field in their db?!? 2
2 -
If we compare this list with last year’s list, nothing much has changed. The top three worst passwords of last year were ‘123456’, ‘password’, and ‘123456789’. Source : Splashdata
Top 10 worst passwords in 2019 below:
1. 123456
2. 123456789
3. qwerty
4. password
5. 1234567
6. 12345678
7. 12345
8. iloveyou
9. 111111
10. 12312314 -
Client from a big company requested that all sensible data should be encrypted, passwords included.
We agreed that was OK, and that we were already saving the hashes for the passwords.
The reply was "Hashes should be encrypted too"4 -
Found an article on medium, which does make one think about the security of fetching things from npm and somebody "checking" the source on github.
“I’m harvesting credit card numbers and passwords from your site. Here’s how.” @D__Gilbertson https://hackernoon.com/im-harvestin... 3
3 -
Tldr; make sure what you study is relevant to the field and you enjoy it otherwise don't waste your time.
BTW: devrant is awesome it gets me through the day.
So I am almost 3/4ths through a master's in cs and I am contemplating why I went to school in the first place/dropping out.
My program is basically an extension of the bs I got from the same school meaning we learn very general cs topics. There is only one ai class for example.
I had a junior developer position before I even got my bs so now that I am this far along and looking at job openings I'm wondering what why and how my school is able to get away with teaching us this shit.
After all my schooling I learnt more on my own and through Google. I have little to show for my school work other than a degree that says I did a bunch of busy work. And the specific things that I did learn I will never ever remember. Seriously. Who here knows what a MIB and OID are and have actually used them?
I wish I tried harder to get into a school like Berkeley but just looking at their applications is depressing. I always had issues with school and they expect my to have the grades, extra curriculars and other shit. I'll build you a robot or make you a website but I'm not doing that nonsense.
And then there's Google and apple and all these big tech companies expecting me to have written full Enterprise software and know every single algorithm and programming language because everyone uses something different. Sure I wish I had experience in all 50 languages that are popular right now but I don't. And I'm not gonna learn it from school that's for damn sure.
Who here actually went to a good school and can say it helped them in the real world? How many employers actually care about school over actual experience?
Who knows how to burn a school down and get away with it? Or at least make teachers with Phds stop reading off slides all lecture. I know how to fucking read for fucks sake. Not too mention they use shitty software made in 2003 that's no longer supported. And I could go on about the teacher last quarter who graded the midterm on final day while he flirted with the 3 girls in class. And I could go on and on and on but I feel like I need to start being productive so I don't waste away.
Just so done.7 -
Updating code for big client.
Find that they are not encrypting passwords in the database and are not sanitizing user input from forms.
Do not trust the user!2 -
Reset 65 passwords today already, a new personal best for one day! No idea why the reset password button is so hard for clients to use, aghh!3
-
Fucking hell with the password fields.
Why in the fucking hell you can't tell me what's the max characters count? Why I have to deal with auto-truncated passwords after the fact?
Go eat exquisite shit, peasant punks, pussy cutters.2 -
I wonder how many decades it will take until employees stop to fucking stick their passwords to the computer screen at their station. It is a complete fucking nightmare if you are responsible for the network!
Can we bring back the guillotine? But it must be stub!
Those nitwits shall suffer!19 -
“Password length mustn't exceed seventeen characters.”
Why? Why do some Web sites still have this rule? It's 2018. We should be using passwords of at least twenty-four characters. This is crap.15 -
A new breach has just been confirmed about 10 minutes ago. CHECK YOUR EMAILS AND PASSWORDS!!!
Details at: https://troyhunt.com/the-773-millio...
CHECK YOUR EMAILS AND PASSWORDS AT haveibeenpwned.com TO CHECK FOR WHETHER YOU WERE COMPROMISED.9 -
When you forget your password, go to change it and get greeted with:
"Your new password cannot be the same as your current password!"1 -
A few years ago I found a public AWS S3 bucket owned by a fortune 500 company containing a database dump backup with all of their users unsalted md5 hashed passwords.
I didn't report it because I don't want to get sued or charged. I don't know whether it's still public or not.6 -
I'm sick of the tyranny of websites who say your password must include at least one shady character, one special agent, and a number of other filthy things. Only makes your passwords impossible to remember, hard to type, and not a bit more secure.
"mynameisronalddumpandimanorangehairedorangutan" is a million times more secure than "P4$$word".13 -
Why the fuck would you allow special characters in your passwords, when some of them are considered "potentially dangerous!" can't even login ffs!
 6
6 -
Microsoft seriously hates security, first they do enforce an numer, upper and lowercase combined with a special character.
But then they allow no passwords longer than 16 characters....
After that they complain that "FuckMicrosoft!1" is a password they've seen to often, gee thanks for the brute force tips.
To add insult to injury the first displayed "tip" take a look at the attached image. rant password security security 101 security fail annoyance passwords passwords stupid practices microsoft13
rant password security security 101 security fail annoyance passwords passwords stupid practices microsoft13 -
This is why having strong and secure passwords are important. Your social media team must be ass BWW.
 1
1 -
For security reasons and to have stronger passwords, my organization enforces us to use '@123' at the end of the password!! Dumb motherfuckers!! :P2
-
Oh fuck, Germany wants to pull an Australia and force services-providers to disclose passwords, password-hashes,... to law enforcement.13
-
*logs in to pc*
- Your password will expire in 3 days. Consider changing it.
+ yeah sure...
*tries to change password*
- Your password must be different from your old 25 passwords
+ ....
+ What the fuck?!? I mean, really, what the fuck is this bullshit? You force me to use EXACTLY 8 char long passwords and this? Fuck you!5 -
That moment when you find out your school is using unsalted md5 passwords, and your school project requires using it too... FUCK4
-
Tl;dr stupid password requirements
Begin quote
Password must not contain any non-alphanumeric characters.
Your Password change was not accepted. Enter your current Password correctly following the rules for New Passwords. Please try again.
Passwords must be between 8 and 12 characters in length and MUST contain each of the following:
At least 1 lower case character (a-z)
At least 1 upper case character (A-Z)
At least 1 numeric digit (0-9)
But, MUST NOT contain:
more than five repeating characters in a row (e.g. 111111356 would not be valid, but 112233445 would be valid)
spaces or other special characters
NOTE: Your new password cannot be the same as any of your 10 previous passwords.
End quote
Are you fucking kidding me? Only (26+26+10)^8 through
(26+26+10)^12 different passwords to go through? It's like the oxygen wasters that built this website give zero fucks about security.
Why? This is the site that manages money and investments. Just allow passwords up to 64 characters, allow any ascii character and just fucking encod the characters to prevent any Injunction.4 -
A friend actually asked me this..
He is building an android app for selling his stuff and haven't used hashs for storing passwords.. 11
11 -
First of all how the fuck you are able to tell that MY password is one of many that have been stolen? How you are able to get those stolen passwords AND WHY YOU ARE EVEN ABLE TO COMPARE THEM?! Are you storing as plain text or just randomly salt all stolen passwords and chceck if they are in your base?
Now that is an INSTAdelete. 8
8 -
Why the Fuck is PayPal only allowing passwords up to 20 characters . Even the most useless websites aren't doing that (at least not visisible, maybe they shorten it in the backend).10
-
Security Horror Story:
A password authenticator which is case-insensitive and all special characters are treated as the same value. As a bonus, all passwords are truncated to 4 characters.2 -
Signed up for a driving class...
This is what i get in the mail shortly after.
Fucking fantastic guys! Saving passwords plaintext. Is it because of the government? 15
15 -
Interns built a user login portal. Password reset page takes user email from a GET parameter.
You can literally reset passwords if you know the emails 😂😂😂😂5 -
On chat today.
Dude: can you run a script for me? We don't have permission.
Me: what kind of script? Who wrote it?
Dude: posts screenshot of DML select/update statement he tried to run.
Me: I'm a DBA. We don't run DML for people.
Dude: Oh. Can you give me the password?
Me: examine script and notice he tried to run it on QA DB.
Me: No. We don't memorize passwords, and this is QA; you need to check the password out of the safe. You also need a change ticket to DevOps, and they will run it for you.
At that point I ended the discussion, because running anything in QA or Prod without a change ticket gets you fired. And I like my job. Really annoyed.3 -
More than 2 years ago I alerted management that the default password we use for client accounts (and two of the variations) were pwned in database breaches. Today we receive an all-staff email that management "has reason to believe this password may have been compromised" and that we needed to change it across the 1200+ accounts where it's being used (200+ clients, several accounts per client).
Is it unprofessional to send a few "I told you so" memes and gifs?7 -
These dimwits emailed my receipt for my dues (not shown) AND MY USERNAME AND PASSWORD in the same PLAINTEXT UNENCRYPTED email...
Off to go write a cranky email... 10
10 -
Today, this made me think: My bank limits the password I can choose to 16 chars, and only letters and numbers are allowed, no special chars. Meanwhile on Typeracer.com I was able to use 60 character password, including numbers, letters and special chars.9
-
"The password must have 7 or 8 characters (numbers and/or letters)”
says Movistar, the biggest ISP and telecom company in Spain ... I can't even. 6
6 -
Expert: "The core problem with passwords is that they reside on a server."
I suppose that's true, but only if you're a complete moron. Store a hash of a password, and users can authenticate against it with a password that doesn't get logged. This is technology that's been around for over fifty years. If you're storing passwords on a server, you deserve whatever trouble you get.6 -
Why is every company so BAD at working with spaces in passwords? Just trying to setup Hulu on my PS4, apparently I forgot my password? No, my password had a space in it. So maybe Hulu's just one of those companies that doesn't allow spaces in passwords? Wait no, I can log in with no problems on my Switch or PC with the space. It's just SPECIFICALLY the PS4 app that doesn't allow spaces. Cool cool cool.
Like, am I missing something? Is there some reason it's harder to hash than other characters? It's just an ASCII character, it's not like I'm copy/pasting in some fringe unicode shit. Some companies straight up ban it. Some like Amazon don't recognize it as a special character, while demanding I use a special character. Why is this so terrible?4 -
Our new COO has decided to migrate our passwords from to a new password manager (due to security concerns).
But now, nearly 75% of our passwords are just 'missing' and we don't have access anymore to our first password manager and it's been emptied out.
AFAIK, the COO still has all the passwords but not shared. He is not responding to my mails / team message from the past day.10 -
Storing DB credentials in a repo that were encrypted using functions... that are in the same repo (both encrypt and decrypt!)...2
-
Just saw this:
Add comma's to your passwords to mess with the csv file they will be dumped in after a data breach9 -
Clients r wankers. He wants to be able to send login details incl passwords in email to his clients when he adds them in the cms. The passwords are encrypted and generated on creation of a new user. Ive told him that sending credentials in email is shit and not secure. The stubborn bastard wont budge, so instead i've put explicit instructions to reset password once logged in with the credentials they send. Any other suggestions?3
-
I found a tool that saves passwords in plain text. Our client didn’t involve us in the decision process. They bought it. You did this to yourself... #1995 #fuckit1
-
“Passwords are like underwear. You shouldn’t leave them out where people can see them. You should change them regularly. And you shouldn’t loan them out to strangers.”24
-
I saved passwords to db hashed to SHA-1 with no salt... I left that company but I'm sure that application is still actively used today.2
-
Client: MY PASSWORD DOESN'T WORK
Me: our passwords are case-sensitive
Client: YES I USED CAPS LOCK1 -
Registering a new account for microsoft teams:
`Your password cannot contain a space, &# characters combination, or the following characters: < >`
Are they storing the passwords in plain text? Are they not sanitizing the input? Why the fuck would they care if I put motherfucking emojis in my password? What the fuck are you doing to the passwords, Microsoft? TELL ME.4 -
It amazes me how quickly give out their passwords. I ask for a person's user name and I swear at least 75% of the time they give me their password too!5
-
New way of storing passwords "securely":
1. Open word and write your passwords in plain text
2. Save that word document and open it in notepad
3. Delete a random character but remember which one and in which position & save
Now the document won't be accessible with word and to fix it you have to put back the character you deleted.10 -
Installs Nessus. Creates Admin account. Forgets to save the 32-char random password to a password manager and locks himself out. Installs Nessus...4
-
A lot of larger companies seem to be a happy about forcing employees to change their password every three months or so. They do it for security measures so that it is more difficult to break through the system, however most people end up making the worst passwords.
Instead of forcing a very good password on them every year or two maybe, they all end up having passwords like: "Summer16", "Qwer1234", "London15".
I used to work for our national police, and this was the case there as well...7 -
Someone just guessed my 20+ character one time password on Microsoft 🤔 2 factor authentication and Geo IP checking are definitely good features.
Well, time to change all my passwords.8 -
Following on from my school having terrible passwords. Turns out they stored all our passwords in plain text somewhere - so some script kiddie (Do you even need to be a script kiddie to find this - probably not, but the guy who did this was a script kiddie) could just remote log me out twice, log in as me, be a twat, and have a conversation in Notepad.
 1
1 -
Passwords.. how do you guys manage yours? I'm one of those who often used the same semi weak password for nearly everything
I'm more than likely going to get a password manager but I have no idea which, do you use any?30 -
Password Rules are bullshit. I am the one to decide what password is safe for me. If even I can't remember my password it's not fucking safe. Morons.
 1
1 -
My university has a internal developed system, where everything is managed from e-mails, exams to personal data.
What I'd like most about it, they talk all day about Internet Security and store our passwords in plain text and if you press the "I've forgott my Password button", they even send your password unencrypted, plaintext via e-mail. (Hello Wiresharks)
I don't know how to feel about this, it just hurts :(1 -
Why are the MOST important passwords in my life (banks, financial, insurance) the LEAST secure (i.e. Max length 12, no special chars)
-
Scored another win as the family tech guy! I found out my wife's sister and her husband were storing all their passwords in a Excel spreadsheet. Long story short they are now using a password manager. 😁1
-
Soooo.. facebook got breached today, 50 million accounts compromised. I'm sure that will help their stock price.. 😂
Change your passwords, ladies and gents!11 -
Best password manager?
I usually use the post-it-jutsu art to save my passwords.
But I think that when you have too much passwords, there should be a better way to store your info.19 -
Finding out a service your school uses doesn't bother encrypting passwords is always fun, isn't it?7
-
Hacking is awesome and looks easy!!! And seems like even pentagon might have toooons of exploits and backdoors, and qwerty passwords !!
After watching Mr. Robot...4 -
Don't you just hate *silly* password restrictions? Surely there is a very limited number of possibile passwords
On top of this their "password prompt" says passwords are between 6 and 10 characters... 1
1 -
When you're guessing passwords and this time it took a bit longer... but it was still wrong...
Slow internet problems... -
Speaking of.. What in your opinion would be an appropriate way to warn someone about security problems, like db passwords in git?
I once came across dozens of extremely sensitive services' infra accesses: alibaba/aliexpress, natuonal observatories, gov institutions, telecomms, etc. I had dozens [if not hundreds] routers' and firewalls' credentials along with addresses. I tried one to confirm validity - it worked. I wanted to warn them but did not want to get in trouble.
If it were servers, I'd set a motd or append some warning messages in .profile. But not sure how to do it for non-server devices
what would you do? How would you warn them?
P.S. Deleting that record was a smart move, buddy ;)
p.P.S. Sorry, wrong category... Can't edit now :(6 -
Wow! This is a truly terrifying, yet fictional scenario. Malware by npm: https://hackernoon.com/im-harvestin...6
-
Short sad story:
The backend team in my company stores plain text passwords and I am making a view in the website to view all the users password in the system13 -
If you think walking on your parents while they're having sex is bad, hear(read) this:
Today I heard my mom asked my dad her email's password, and she's a doctor. Why and how can't you memorize your only password? I mean if she wasn't a doctor this situation would be more believable.9 -
Just had a very "OMG WTF!" kind of mini conversation with my co-founder, of a web dev startup.
Him: So what's LastPass then?
Me: It's a secure password management system.
Him: So let's use LastPass instead of Dropbox then. :-)
** quickly searches dropbox for passwords **
A little knowledge can be extremely dangerous if left unsupervised.
-
Goddamit I hate it when services advertise how they are about security and then deny me using random readable words with hyphens as passwords.2
-
Last year, my company has added the functionality for users to reset their passwords.
The company was then 5y old and already had to reset thousands of passwords. Oh well...1 -
I've been informed that through some level of recognition and certification, today is "Password Day," seemingly in an attempt to encourage people to have strong passwords. I will do my part and say that if you're not using a password manager, you have missed out on years of your life.9
-
When I see people using online tools to test the strength of their passwords I laugh at their stupidity 😭30
-
More emarassing than frustrating..But I was applying to a couple internal positions recently and decided to bring in a sample package to demonstrate some of what I had been working on in my current team. They seemed to like the example and the interview seemed to go well...A couple hours later one of the managers came by my cubicle and asked "is that the real password?" and pointed to a line in the code. Sure enough, I had left a plain text password in the script I had just handed out to 10 panelists at 2 interviews..proceeded to collect the packets back. In the future I'll be paying closer attention to what I include lol.
Still frustrated we keep the passwords in the script though >.> any suggestions for better storage of passwords and the like in Perl scripts?3 -
Every time I go home I have to switch all my passwords, because my little brother watches me type them and memorize them. Every damn time. I'm running out of passwords.12
-
I hate password restrictions that enforce all kind of limitations but then also limit you to a max of 16 ANSI characters ... i want passwords like this pѬѬasѪ"§§)("!编/)$=?!°&%)?§"$(§sw2
-
***ILLEGAL***
so its IPL(cricket) season in india, there is a OTT service called hotstar (its like netflix of india), the cricket streams exclusively on hotstar..
so a quick google search reveals literally thousands of emails & passwords, found a pastebin containing 500 emails&passwords ...but those are leaked last year most of passwords are changed & many of them enabled 2FA.. after looking through them we can find some passwords are similar to their emails , some contains birth year like 1975,1997 etc, some passwords end with 123 ..so after trying a few different versions of the passwords like
1) password123 -> password@123, password1234
2) passwordyear -> password@year
2) for passwords similar to emails, we can add 123 ,1234, @ etc
created a quick python script for sending login requests
so after like 30-40 mins of work, i have 7 working accounts
*for those who have basic idea of security practices you can skip this part
lessons learnt
1) enable 2FA
2) use strong passwords, if you change your password , new password should be very different from the old one
there are several thousands of leaked plaintext passwords for services like netflix,spotify, hulu etc, are easily available using simple google search,
after looking through & analysing thousands of them you can find many common passwords , common patterns
they may not be as obvious as password ,password123 but they are easily guessable.
mainly this is because these type of entertainment services are used by the average joe, they dont care about strong passwords, 2FA etc6 -
This is the kind of company that provides online ticket sales for one of the bigger cinemas in Italy. Yes, registration is unavoidable.
 1
1 -
Just found out today via Reddit that Wells Fargo, American Express (not personally confirmed), and Chase login passwords are NOT case sensitive!
I would check your bank too!2 -
It's gotten to the point where I am legitimately impressed when I can tell a service is hashing their passwords.
All of these unnecessary complications of "must not have more than 2 of the same character in a row" but "can't be more than 12 characters" requirements make me think that the passwords are being saved in plain text.
Amazon and Dropbox do it right - present the user with an input box and no requirements printed anywhere.8 -
Make all fancy Azure blob storage with SFTP connection through firewall with dedicated public IP.
...to just find out that the webcameras you want to send stuff to the blob storage take in max 16 or 30 character passwords for sFTP. While the autogenerated passwords for SFTP in Azure are 32 characters long.
WHO THE HELL RESTRICTS PASSWORD LENGTH!? ASfjksdnfjksdjfnjksdakfadsnjkfjdsa10 -
First time programming for work... Man in the middle student password changes. Yep that's right I'm being asked to write a program that will change students passwords on their Google accounts and local domain while also keeping a decryptable format password in a database. Granted it's much better than not letting students change their passwords at all. Plus were doing it because it will let us fix their issues while their out of school so...8
-
About 5 years ago I worked at a small company developing websites and .NET applications.
They haven't changed any passwords which means, I still have access to ALL of their customers DNS setups.
Of course I wouldn't do anything.
But just the thought, that I could make an infinite loop, by redirecting the domains, is amazing.
Or redirecting them to a porn site.3 -
I'm going to praise 1Password here.
I hate creating and remembering passwords. Now I can login to everything just with a click of a button.3 -
This morning I just discovered all our repos are visible to everyone in the company... Not just the team that created them...
We store passwords and certs in our repos....25 -
“This value must be shorter than 20 characters in length.” … password field, bank website, 2016, wtf ¯\_(ツ)_/¯2
-
The dev before me stored all the emails and passwords as plain text in the database. This is not good. Not good at all.1
-
Boss hired a freelancer to work on a new reporting dashboard. Freelancer also built a backed. Boss wants me to work on fixing that backend. I check out the DB first only to find plaintext passwords. I threw up a little.2
-
Wow..just logged into my university admin page and noticed that the passwords are all sent case insensitive to the server...
Huh?2 -
Is there a good technical reason to not allow passwords to contain special characters? My isp does this and I need to know why.10
-
Opens the source code for an app I have to integrate with.
Finds: if($cryptPW == $dbPW)
What the shit?!?!!!!!
Learn to hash! Far out 😢4 -
What if...
Someone made a self hosted password manager, where you can put all your secure random passwords in?10 -
When you're arguing with a non-programmer, make sure they know that you're the one saving their passwords.
-
People, even on devrant, are complaining about having to change their Twitter passwords. A major security event is not the only occasion to change your password (for anything).
You should change your passwords for everything regularly. Like, once every month or two.
This is why password managers are brilliant.3 -
hashing passwords atm.
i have a java backend, should i look into bcrypt or just use a loop?
also how many times would you recommend i hash passwords?
and should i look into hardware acceleration?11 -
I save all my work relate passwords in a single text file on my computer. I always have it open too.
Too many systems, too many password requirements, expires too frequently.1 -
Overheard this on my way in this morning.
Head of IT: I had to hack a few of our routers because someone changed the passwords. -
To all websites requiring at least one upper case, one lower case, one number, one special character, 25 emoji and 49 unicorns in the password when signing up.
If you say something is required, then your regex BETTER be checking ONLY for those things. You should not have hidden requirements for passwords that users are supposed to dream about and know. Especially if it's a super time-sensitive thing that they should have opened 2 Fridays ago.
I had to pull my hair out for 20 minutes (that felt like an hour) before looking at their code and reading their regex. The regex was different from what the page said the requirements actually were. What were they even thinking? 😑
The rest of everything related to this organization uses an SSO system, why can't they just use it? Isn't the whole point of SSO to avoid a different login for every tiny part of the system?
I wonder what the other less technically inclined people using the system are doing right now. Sadly, I have no way of letting them know.
I sincerely hope the dev that made that website faces the same thing while picking a password for creating an account somewhere else and realizes what he/she did.
I really needed to let it out.
I feel much better now.
Time to take out the stress ball :)1 -
Has anybody been forced by a PM or someone else to send clients passwords via email?
How should I tell them it's not best practice even if they are insisting?4 -
Long time ago cleared chrome history. Had the clear passwords box checked... Fuck. Spent hours recovering passwords. Then switched to lastpass
-
On Facebook open day:
Graduate dev lady telling a story about how much responsibility they are given and how she broke the password reset button for hours when her task was to instruct old users with weak passwords to update them...
//my first post, so not sure if it's appropriate, but surely did this come as a shock5 -
When the school district decides to change the passwords to every school related account of every student in your grade. Right before you take an online quiz. (They do this every year for the sophomores to make them change their passwords but they usually do it the first day, not two weeks in) Couldn't even log into the school computers, the site to check our grades, anything. Nice job guys, purposely reset passwords in the middle of the day.
-
People who use weak passwords are the digital equivalent to anti-vaxxers. Not only are they putting themselves at risk, but they can effect everyone else who has a lick of common sense.2
-
It’s really easy to gain administrative access on unencrypted windows machines with a single usb. You know what’s also easy? Extracting admin passwords with mimikatz.
Edit: this was back in 5th grade2 -
https://devrant.com/rants/2366822/...
following rant I started oppening my files to build copy of have i been pwned service why twitter kept their passwords in plain text lol
...
people actually got 123456 passwords looking for my email in twitter database file 1
1 -
I recently went to an office to open up a demat account
Manager: so your login and password will be sent to you and then once you login you'll be prompted to change the password
Me: *that's a good idea except that you're sending me the password which could be intercepted* ok
Manager: you'll also be asked to set a security question...
Me: *good step*
Manager: ...which you'll need to answer every time you want to login
Me: *lol what? Maybe that's good but kinda seems unnecessary. Instead you guys could have added two factor authentication* cool
Manager: after every month you'll have to change your password
Me : *nice* that's good
Manager: so what you can do change the password to something and then change it back to what it was. Also to remember it keep it something on your number or some date
Me: what? But why? If you suggest users to change it back to what it was then what is the point of making them change the password in the first place?
Manager: it's so that you don't have to remember so many different passwords
Me: but you don't even need to remember passwords, you can just use softwares like Kaspersky key manager where you can generate a password and use it. Also it's a bad practice if you suggest people who come here to open an account with such methods.
Manager: nothing happens, I'm myself doing that since past several years.
Me: *what a fucking buffoon* no, sir. Trust me that way it gets much easier to get access to your system/account. Also you shouldn't keep your passwords written down like that (there were some password written down on their whiteboard)
Manager: ....ok...so yeah you need sign on these papers and you'll be done
Me:(looking at his face...) Umm..ok4 -
Hi everyone,
One question is constantly popping in my head and I keep fighting to figure out how to answer.
So here it is:
Are you for or agains a password manager to store all your passwords?
P.S.
I am using a paid password manager, but keep asking myself is it really worth it, and am I compromising all my passwords if someone is willing to spend some time and hack my vaults. On the other hand the convenience and benefit of having all passwords in one place and also using different strong passwords for each of my accounts protects me from a weak security implementation on any third party service I use, because I am not re-using the same password everywhere.12 -
Some interesting reads I came across yesterday:
- Github got DDOSd with 1.35Tbps via memcached
-- https://githubengineering.com/ddos-...
- Troy Hunt, the creator of https://haveibeenpwned.com/ released "Pwned Passwords" V2 and talks about his partnership with cloudflare, how he handles traffic, why he chose SHA1 for the passwords, how he together with a cloudflare engineer thought of a solution to anonymize password checks and more
-- https://troyhunt.com/ive-just-launc... 1
1 -
JetBlue still storing passwords in plain text, after 4 years
“JetBlue: The deadly sin of an otherwise great airline” https://medium.com/@sethillgard/...13 -
"Ideal" online banking:
1. Force users to change passwords often.
2. Implement possibility to login if forgot password.
3. Make it impossible to chage password if forgot one.5 -
Sites requiring a maximum password length, does it mean they store the passwords in clear text?
Or what would be a plausible explanation for this stupid requirement?4 -
2016 and the passwords were stored in plain text. I pointed it out, they said they'll use md5 instead :/
PS: Ended up fixing it for them with HMAC-SHA256 -
Am doing an online shop for some client as a side project. The client never requested a module enabling an admin user to manipulate listed products. Now this cheap genius wants to be able to login as a seller and manipulate whatever products they've listed. So I told the client it's not possible to do that because passwords are stored as hashes. Now, can you Guess who's storing clear text passwords ?
May shit never hits the fan.3 -
You know what's worse than having to come up with a new password every time you create an account? Forgetting your password every time you try to log in!
I swear, it's like my brain has a selective memory when it comes to passwords. I can remember every lyric to a song from 10 years ago, but I can't remember the password I created yesterday.
And don't even get me started on password manager software. You would think that having all of your passwords stored in one place would make things easier, but nope. I've forgotten my password for my password manager so many times that I'm starting to think I need a password manager for my password manager.
But seriously, why do we even need passwords in the first place? Why isn’t there an easier one stone kills all solution to all these password authentication nonsense?
I could remember when it was all letters, then forced to use letters + numbers…
then later forced to include symbols…
and then forced to make it lengthier…
and then solve puzzles after getting it right…
and after all the stress now we are forced to find nemo from a set of images.
I thought the misery would end there but nope. Now some platform forces 2FA like dude seriously?
For God’s sake we built self driving cars already! Why can’t one just exist without a password? Why do we always end up in a password cycle?
And please don’t say shit about oauth because if your password master (i.e: google) fucks you in the ass then all your oauth accounts are gone for good!
I'm currently having an existential crisis about the meaning of passwords in our modern society. Shit is crazy when I ponder about it I get worried.11 -
"We only permit non-restricted, non-offensive alpha-numeric passwords..."
Does ,wnW\M@Bb;v3F(xx offend you?5 -
My facebook password is so secure...I made it so complex to the degree that I couldn't recall anymore!!😂
Thx God my phone is still logged in !5 -
Why am I incapable of studying human languages that I can use to communicate with people I genuinely want to talk to, but will use all of my spare time to learn a new computer language that I’ll never use!?1
-
*breath in*
FUUUUUUUUUUCCCCCKKKKK.
OK.
There are many things one can complain about when it comes to windows. But I swear, the worst thing ever invented is this motherfucking "Windows Credential Manager". Basically I have a private and a buissness git account. I worked on a buissness project and pushed my changes. And when I looked in the repo it did commit under my private account. Ex fucking cuse me? Wtf? When pushing I logged in with my buissness account, why on earth did it push with my private account??
*3h of investigation*
Turns out this cunt fuck credential manager stored my private credentials and used them even tho I explicitly pushed with my buissness account. What goatfucker of a developer decided its a good idea to store user credentials without the users permission/without asking, and then uses the stored credentials instead of the one explicitly given??
I swear to god, if this piece of software would be a person, I would have thrown it him of my window(s).2 -
Don't password restrictions cause a reduction the possible passwords and reduce the search space if someone tried to try brute force?2
-
I changed my twitter password on web on the day they discovered the passwords in plaintext in their logs, and till today, I've not been logged out of the mobile client1
-
Who actually started the reign of mixed character passwords? because seriously it sucks to have an unnecessarily complex password! Like websites and apps requesting passwords to contain Upper/Lower case letter, numeric characters and symbols without considering the average user with low memory threshold (i.e; Me).
Let's push the complaint aside and return back to the actual reason a complex password is required.
Like we already know; Passwords are made complex so it can't be easily guessed by password crackers used by hackers and the primary reason behind adding symbols and numbers in a password is simply to create a stretch for possible outcome of guesses.
Now let's take a look into the logic behind a password cracker.
To hack a password,
1) The Password Cracker will usually lookup a dictionary of passwords (This point is very necessary for any possible outcome).
2) Attempts to login multiple times with list of passwords found (In most cases successful entries are found for passwords less than 8 chars).
3) If none was successful after the end of the dictionary, the cracker formulates each password on the dictionary to match popular standards of most website (i.e; First letter uppercase, a number at the end followed by a symbol. Thanks to those websites!)
4) If any password was successful, the cracker adds them to a new dictionary called a "pattern builder list" (This gives the cracker an upper edge on that specific platform because most websites forces a specific password pattern anyway)
In comparison:
>> Mygirlfriend98##
would be cracked faster compared to
>> iloveburberryihatepeanuts
Why?
Because the former is short and follows a popular pattern.
In reality, password crackers don't specifically care about Upper-Lowercase-Number-Symbol bullshit! They care more about the length of the password, the pattern of the password and formerly used entries (either from keyloggers or from previously hacked passwords).
So the need for requesting a humanly complex password is totally unnecessary because it's a bot that is being dealt with not another human.
My devrant password is a short story of *how I met first girlfriend* Goodluck to a password cracker!5 -
To the developer of jobomas.com (I sent this while I canceled my account):
Seriously, a platform that confirms my password in clear text in an email is a risk for my privacy and data.
One more story: I wanted to change gender to male and you asked me for my phone number, birthday etc. (required form fields)?
I should be able to decide myself what I want to share with you and what not!
This platform isn't even fully translated to english (Gender selection for example...).
Consider hiring a UX-Designer so I don't press cancel, when I want to cancel my account.... what a finish, sigh! 1
1 -
Logs in to client office 365.
Big recommendation at the top
"Disable password auto expiry, it's currently set to 90 days"
Why is this a recommendation? I suppose there's an argument that making a user change every now and again will weaken their passwords over time, but really?2 -
When a software improvement organization (cough Scrum.org) does this stupid crap with their passwords, causing us all to be pwned.
 2
2 -
Why the fuckin' hell does PayPal limit your password to 20 characters?!?
The length shouldn't matter if they hash and salt the passwords... sooooo...4 -
A list with usernames and passwords have to go from customer A to customer B, because customer A does not have the permission to set these login credentials to the productive system. Additionally, the users are technically unable to change their passwords (yes I know, it's a mess there). What should customer a do? Like except burn all my customers alive and punch them...
-
Why is it so fucking difficult to delete saved passwords from your Google account? I tried deleting all in Chrome, but as soon as I launched Chrome on another computer all the passwords synced down. And in the online console you can only delete them individually. Luckily I found a JS snippet that grabs all the button elements and clicks through them, but why does Google have to make this so difficult? Fucking hell.1
-
Yubikey: Worth it?
I'm a college student with way too many logins and offend reusing passwords. I also do password semantics research at the institution and know how useless they are.4 -
Serious biased question:
What's the newschool way of storing passwords now that everyone is against the known hashes?
Would prefer storing it in a good 'ol database tho pls.12 -
We should find a way to replace passwords: any password manager which I tried is inaccurate in identifying login forms and is too hard to use for non technical people older than 40 and convince people to not use some stupid name + birth year combination as their passwords is a frustrating uphill battle.11
-
client: "can you build out a staging server for us? here's all the code, everything you need"
me: "awesome, looking good, i have almost everything i need, just give me the credentials for the server, and I'll get started installing all the infrastructure"
client: "ok, try these!"
me: "doesn't work"
client: "this one?"
me: "doesn't work..."
client: "how about this one?"
me: "STILL NOT WORKING!!!"
imagine you want someone to do stuff on your server and you don't even know the root SSH password.... smh
why is this always a problem, use fucking 1password or something its 40 bucks a year, secure, and you can organize alllll your passwords. don't be a fucking boomer and write them on a piece of paper, or worse, apparently like my client, never know it or have it in the first place.5 -
Not dev per sé but annoys see he'll out of me on a monthly basis... 30 day password expiration, how does that make things more secure?! The thing that makes it worse is that I can't use any previous 28 passwords or anything too similar... Now I'm stuck with a 36 character password which I have to put in everytime my work machine decides to lock out... Which is less than a minute of not touching it.
What's that? No I can't turn around and answer a question because if I do I'll be taking 20mins off of my future career prospects as I'm working on leveling up my inevitable arthritis6 -
Got a new work laptop yesterday. Set it up, updated it, and went to bed. I woke up this morning to it not accepting my password. I had to blow it away in recovery and delete my old keychain. Great start to the morning.
-
A while back I was looking for a new job and was given an interview by one company who shall remain nameless. Before the interview, they asked me look through their current site, nothing unusual there, so I started browsing. Then I received an email with all the details I needed to access their production server. Apparently they wanted me to look through the code, unusual but I did so.
First thing all the passwords, including those belonging to members of the public were stored in plain text and many were still the default passwords which were based on the Id so were sequential.
I highlighted these issues at the interview and they then asked me to do a test, not the usual test though, they asked me to add some charts to their prod site. Needless to say that didn’t happen and I got another job elsewhere.1 -
Am I the only one not liking that shitty websites where you put almost no critical login information require insanely complicated password?
I don't want my complicated password ending up in a rainbow table because they store my passwords in text format...
There's only so much versions of passwords I can remember for trivial websites...24 -
can someone explain to me why some people think having a password with a maximum size of 14 is good enough and then have the audacity to force it onto users?!2
-
I lost the book that i store all my passwords on it
I almost had a heart attack and
I woke up from my dream2 -
Why is it so difficult to tell the people to not use the same passwords everywhere? I thought of a service which searches all leaked databases and predicts a password based on that as a warning for the user... Having the program told you that your password the user is likely to enter would be XY, because the adobe OR MySpace OR Dropbox passwords for the email OR username entered was that password could be a bit more aggressive but useful to let the users at least think of secure passwords.1
-
Took a long time to update to high sierra yesterday. Doesn't seem like much has changed, apart from some shinier icons. Oh and now having two different passwords for some reason?2
-
At work, how does your team store and share passwords to DBs, machines, other logins used by everyone (not linked to a specific person) or is needed by an app?6
-
Okay so if a company decides to use md5 for hashing passwords after a million users already registered how the hell will they transition to any other way of storing passwords. As they don't have plaintext to convert them into the new hashing function.12
-
Hey guys.
So, where do you guys store your passwords?
It's getting hard to keep track of so many logins and passwords now that I have the time to learn, try new stuff, meddle with VPS and shit and I can't keep track of everything.
Ps: must save somewhere online (or at least backups) and be multi platform (windows + Linux + Android9 -
Security issues I encountered:
- Passwords stored as plain text until last year.
- Sensitive data over http until last year.
- Webservice without user/pass authentication. -
A number of tech projects use mailman for their mailing lists. Yet, mailman sends passwords in plain text to their users, once a month. Wtf?2
-
Json host files of a whole server networks root server passwords under the webservers configs directory open to the public.
-
Anybody know of any enterprise software for password storage and sharing?
We have an issue where multiple people across different teams use the same accounts and need them to be able to access certain login information but not all login information.
I’m hoping for something free/open source but at this point I’m open to anything. Must have the ability to give users privileges.7 -
When the DBA restores the live db to staging and all your connections fail on passwords. Every fucking day!1
-
One of Biggest dev insecurity i think poor quality of user passwords. Users have not yet understood how to create secure passwords.2
-
The all too common passwords stored in clear text. When brought up with the developer they couldn't see the problem.
-
When after registration on some website you get your password, that you just set, send back to you in an email. Why the fuck do they store and transmit passwords in plain text.4
-
I'm hoping to eventually set up my own server where I can store files/passwords. Does anyone have experience with Sandstorm.io, Nextcloud, or ownCloud? Are there any other alternatives you would recommend?1
-
Not super ranty but what I’m interested in how passwords are managed in your organisation?
I feel dirty receiving passwords through slack and having a spreadsheet on a shared drive seems like madness.
I’ve worked at organisations before that have a single login to a password manager. However theoretically I still have access to that as no one would have changed the password.
Organisational password manager softwares are really expensive!14 -
I did an engineering quiz yesterday as a way of introducing a new database the school recently got access to. You had to sign up for the site.
- Passwords were max 20 characters (which is better than 10, but still, why???)
- You couldn't use special characters, but there was NO INDICATION ANYWHERE THAT THAT WAS THE CASE. It would just silently fail to log in. I had to open the browser console to figure out what wasn't working. FUCK -
i once changed all of the passwords of my main online accounts(google, apple, facebook, telegram, outlook) as they weren't changed for years.
i decided unique and long passwords for each of them.😎
immediately after changing the passwords, i forgot all of them. 😵fortunately, i was able to reset.
Has this ever happened to anyone?3 -
so i'm about to deploy admin application which doesn't have admins passwords hashed
after asking him, wtf dude?
he replied, no worries mate
fml5 -
Anybody heard of Clef - A new way to login? It's pretty coool! I've integrated it in one of my projects and it works like a charm..!
The best part being no need of any passwords or fingerprints or facial detection etc3 -
I’m harvesting credit card numbers and passwords from your site. Here’s how.
The state of npm is just 😢
https://hackernoon.com/im-harvestin...1 -
Nothing more secure than have 36 character length passwords mixing any kind of character in them and have them in a txt file inside my docs folder 🤯🤯🤫12
-
Am i overthinking too much or are passwords like this
S9L4dk1i6sy5
Insecure?
This is an example generated by some website where i have activated 2fa and need to generate app passwords to access it from clients
I've thought about it many times to ask them to make it more secure but everytime i think i'm overrracting17 -
"combination of upper and lower case letters, numbers and symbols"
Someone please change the devrant terms to encourage more secure passwords...
(Yes, I actually read* the terms and conditions)
* half of 7
7 -
What does devrant think about https://doppler.com/
Saw it on https://producthunt.com/posts/... today, and it seems interesting but I'm not sure what all to think of it, so I'm curious what the smarter than me members of devRant think.7 -
Anyone have the link to that rant where the individual is yelling about how maximum password lengths are retarded? I just really need to read that right now... the max password length on this site is 14 CAHRACTERS7
-
Started using Brave browser coz my bf wouldn’t shut up about it. Consumes much less memory than both chrome and firefox which is cool. Still haven’t figured out the in-built vpn yet. Cool i can import data from my firefox like my bookmarks and shit and I understand why I can’t import my saved passwords but damn i wish i could. I don’t know my passwords to anything anymore thanks to browsers beautifully saving my passwords and i am just frustrated having to go and copy passwords. This relationship with brave is clearly not going to last coz wtf2
-
Me just now:
> finishes adapting an app for my purposes in android studio
Time to export a signed apk!
> successfully locates the keystore I generated a year ago
> even remembers the passwords
Nice! Now I can finally close Android Studio!
One second after I close it:
Shit, I forgot to enable dark mode
> reopens android studio
(The dark mode normally becomes accessible through in-app purchases, but since I built the app from source those don't work)3