Ranter
Join devRant
Do all the things like
++ or -- rants, post your own rants, comment on others' rants and build your customized dev avatar
Sign Up
Pipeless API

From the creators of devRant, Pipeless lets you power real-time personalized recommendations and activity feeds using a simple API
Learn More
Comments
-
With pub/priv keys the advantage is that your private key stays on your pc and you can prove your identity without sending credentials over a network
And essentially, what you're describing is that the username is just an extension of the password, which I can kinda agree with if the username is secret.
Some sites have both an username and a display name -
@alexbrooklyn can you explain me more about this? I always thought both email and password are sent to the server (or atleast some hash that gets generated after first successful login) .So this IS kind of sending credentials over the network, right? Like i said, if someone has both of my public and private key( username - password in this case), they can forever login because the system has generated a hash for them after first login attempt.
And yes , i am precisely describing username being an extension to password. More than that , i am describing a way to make every platform handle an extra layer of security by relying only partially on the common key ( the email in this example). But i did thought that i wanted username to be public instead of being a secret. Is there any problem in that logic?
Also yes display name is used in sites like github, twitter etc, but isn't that just a gimmicky public info? i thought it had nothing to do with security except makein user search easy -
@TitanLannister Username != public key, password != private key; while they appear equal at daily use, they are not the same in a cryptographic sense.
When using a (cryptographic) key pair to log in, the private key never leaves my system, but a answers challenges anyone can create or verify with my public key. As a consequence, the other party (the one who wants to check my identity) will just need the public key, but never the private one. -
About using an "email id" (do you mean email address?) as a "secondary" secret:
This would either be leaked the same way as the password or (in case of the email address) is public knowledge.
When you said one currently 'just' needs the username and password: Where do I get the last one from? If I get the password, wouldn't it be trivial to get the "email id", too?
A better choice would be following: You use a cryptographic key pair and place it on a separate hardware device. To log in, a challenge is generated by the website and answered by the (USB?) device, ideally in a way that is unique for each domain (e.g. site a.com cannot create a challenge b.com).
This is (in short) the already existing U2F protocol. Many sites (like Google, Github, Gitlab, Dropbox) support it already. -
I needed to read the rant twice to get what was meant.
username, password, email and then somehow mixed up with public/private keys?!
But @sbiewald explained what supposedly was meant already.
Related Rants

 Did you say security?
Did you say security?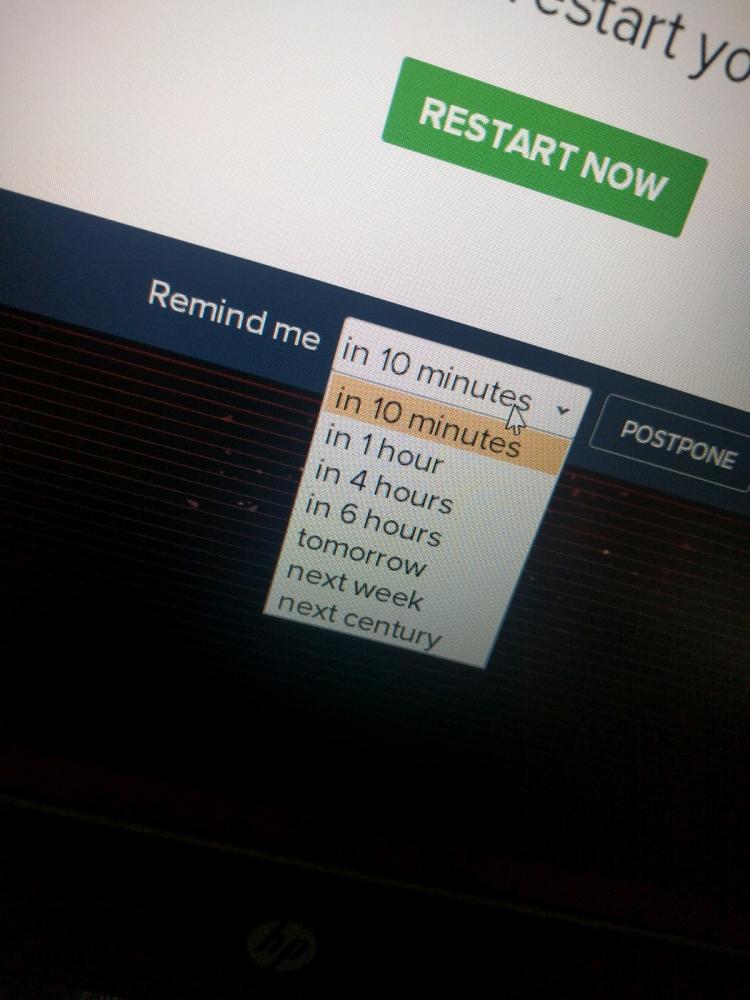 10 points for next century option.
10 points for next century option.
#justAthought
I was reading about public and private keys yesterday, and i had a thought: don't you think the concept of "username" is being so badly misused?
It can act as a great firewall, but we are just misusing it as an alternative to "login via email", because we are now so dumb to remember our email.
You might think of my rant as being going back in time, but think about this: my profile shows the name titanlannister. if someone got access to my password, he/she can immediately take over my complete identity because devrant allows us to login via username/password combo.
Now think of this: my username shows titanlannister. Anyone of you can write a post and mention me via @titanlannister, and this system will notify me. However even if you get my password, you are unable to hack into my profile, because my profile is only accessible via my email id/password combo, which you still don't know.
This, I would call as Platform Public Key which adds a kind of semi firewall over default public/private key combination .
What do you think?
question
security