Join devRant
Do all the things like
++ or -- rants, post your own rants, comment on others' rants and build your customized dev avatar
Sign Up
Pipeless API

From the creators of devRant, Pipeless lets you power real-time personalized recommendations and activity feeds using a simple API
Learn More
Related Rants

 Did you say security?
Did you say security?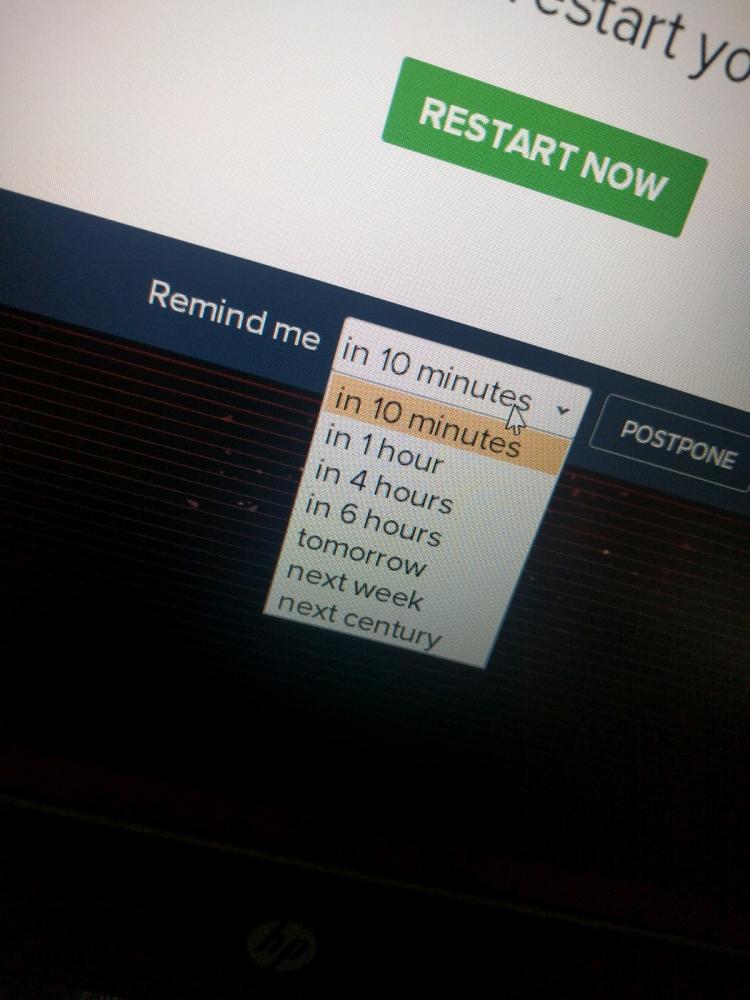 10 points for next century option.
10 points for next century option.
So just now I had to focus on a VM running in virt-manager.. common stuff, yeah. It uses a click of le mouse button to focus in, and Ctrl-Alt-L to release focus. Once focused, the VM is all there is. So focus, unfocus, important!
Except Mate also uses Ctrl-L to lock the screen. Now I actually don't know the password to my laptop. Autologin in lightdm and my management host can access both my account and the root account (while my other laptop uses fingerprint authentication to log in, but this one doesn't have it). Conveniently my laptop can also access the management host, provided a key from my password manager.. it makes more sense when you have a lot of laptops, servers and other such nuggets around. The workstations enter a centralized environment and have access to everything else on the network from there.
Point is, I don't know my password and currently this laptop is the only nugget that can actually get this password out of the password store.. but it was locked. You motherfucker for a lock screen! I ain't gonna restart lightdm, make it autologin again and lose all my work! No no no, we can do better. So I took my phone which can also access the management host, logged in as root on my laptop and just killed mate-screensaver instead. I knew that it was just an overlay after all, providing little "real" security. And I got back in!
Now this shows an important security problem. Lock screens obviously have it.. crash the lock screen somehow, you're in. Because behind that (quite literally) is your account, still logged in. Display managers have it too to some extent, since they run as root and can do autologin because root can switch user to anyone else on the system without authentication. You're not elevating privileges by logging in, you're actually dropping them. Just something to think about.. where are we just adding cosmetic layers and where are we actually solving security problems? But hey, at least it helped this time. Just kill the overlay and bingo bango, we're in!
rant
security