Ranter
Join devRant
Do all the things like
++ or -- rants, post your own rants, comment on others' rants and build your customized dev avatar
Sign Up
Pipeless API

From the creators of devRant, Pipeless lets you power real-time personalized recommendations and activity feeds using a simple API
Learn More
Comments
-
There is Keepass which runs locally. It doesn’t have security questions, which is good.
As you have realized, security question are nothing more than less secure passwords. -
yes you're boned.
there are multiple ways to unlock a database though, a password being one of them. You can also just use a File as the encryption key. But the thing is, as an attacker youll never know, what the owner of the database used, because you need to choose, when decrypting.
Another security (and identity) related website called keybase uses a paper key, that they want you to write down, so if you forget your password, you can use the paper key to recover your login. The paper key consists out of like 15 or so words.
And also on a nother topic: every online password manager is a security vulnerability. -
 Hazarth92052yI also use KeePass. I have it both on my Phone and Computer and have them synced using syncthing. So far it's the best setup I could make...
Hazarth92052yI also use KeePass. I have it both on my Phone and Computer and have them synced using syncthing. So far it's the best setup I could make...
KeePass also includes browser and android auto-full integration and a built-in secure password generator. (depending on the frontend you use, technically KeePass is just the secure base and open source, so people can easily extend it) So you should consider implementing something similar, make it open source or consider some sort of plugin system to compete
Honestly your security intuition is pretty solid. It's not exactly novel as far as I can say, passphrases are generally recommended these days as alternatives to passwords (fuck websites that have an *upper limit* on password length....)
KeePass also supports hardware keys like UbiKey or similar, at least KeePassXC for linux does, but I assume most ports will :D -
Update: I have indeed decided to completely remove the security questions system in favor of a multiple passphrase system
-
 hjk10156302yIf you are going to go KeePass I can highly recommend KeePassXC. That is a better implementation of it.
hjk10156302yIf you are going to go KeePass I can highly recommend KeePassXC. That is a better implementation of it.
Security questions are like WPS flawed by concept and undermines security. If you dare worried about the forgetting of the master password (which is weird to be honest). Get some hardware and back it up.
I have a separate database that holds a Yubikey secret. I use a passphrase in combination with my Yubikey to unlock my normal database.
So you need my database, passphrase and my Yubikey to get too it.
Or you need to have my special backup usb stick and my backup passphrase. To eliminate the Yubikey requirement. -
@hjk101 The original goal was to make one for my parents, who will not be backing up their passwords anywhere and still use poor password practices in the first place.
The question for them is "if I cannot reset my password with email, what happens if I forget it?" and the answer of "all your shit is gone" is unacceptable.
I'm trying to find a balance between secure and easy to use. I think that allowing unlimited passphrases (think: maybe my mother can remember 1-2 and my father can remember a similar amount) is a good compromise because between two people and four passphrases, there's a good chance you can get access.
Later on, I can support other means of entry too. Such as a file, biometrics, etc. The cool part of my design is that you can add or remove methods of entry at any point. -
 hjk10156302y@AlgoRythm there are two things of importance here.
hjk10156302y@AlgoRythm there are two things of importance here.
1. It's there any chance of them losing access to their email?
2. Are there any accounts/services that can't be reset using password reset via email?
It's they can be trusted nor to delete the password database or change the master password and they trust you. You can also keep the master password in your database and set your email as recovery for their mail. That does mean that are at risk of you are at risk but seems less likely.
Also the ease of use is becoming a lot more important than the whole offline stuff. Then just go with the best online password service.
As a last resort you can write your own, that auto backs it up and allows for a reset via email + sms.
Related Rants

 Did you say security?
Did you say security?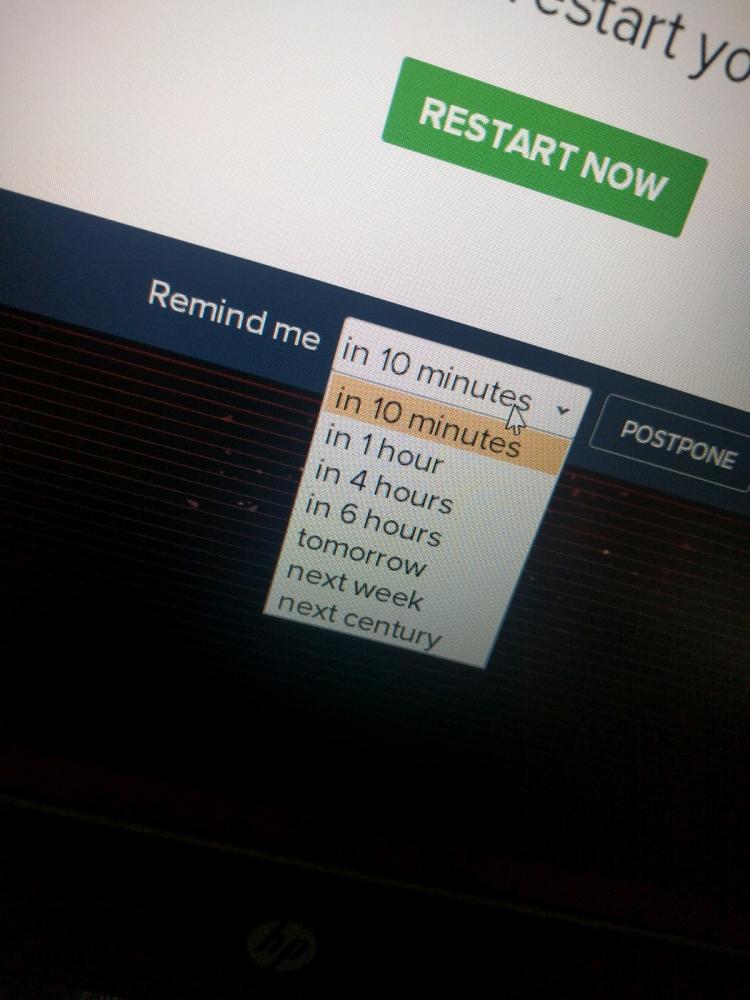 10 points for next century option.
10 points for next century option.
I’m working on a new app I’m pretty excited about.
I’m taking a slightly novel (maybe 🥲) approach to an offline password manager. I’m not saying that online password managers are unreliable, I’m just saying the idea of giving a corporation all of my passwords gives me goosebumps.
Originally, I was going to make a simple “file encrypted via password” sort of thing just to get the job done. But I’ve decided to put some elbow grease into it, actually.
The elephant in the room is what happens if you forget your password? If you use the password as the encryption key, you’re boned. Nothing you can do except set up a brute-forcer and hope your CPU is stronger than your password was.
Not to mention, if you want to change your password, the entire data file will need to be re-encrypted. Not a bad thing in reality, but definitely kinda annoying.
So actually, I came up with a design that allows you to use security questions in addition to a password.
But as I was trying to come up with “good” security questions, I realized there is virtually no such thing. 99% of security question answers are one or two words long and come from data sets that have relatively small pools of answers. The name of your first crush? That’s easy, just try every common name in your country. Same thing with pet names. Ice cream flavors. Favorite fruits. Childhood cartoons. These all have data sets in the thousands at most. An old XP machine could run through all the permutations over lunch.
So instead I’ve come up with these ideas. In order from least good to most good:
1) [thinking to remove this] You can remove the question from the security question. It’s your responsibility to remember it and it displays only as “Question #1”. Maybe you can write it down or something.
2) there are 5 questions and you need to get 4 of them right. This does increase the possible permutations, but still does little against questions with simple answers. Plus, it could almost be easier to remember your password at this point.
All this made me think “why try to fix a broken system when you can improve a working system”
So instead,
3) I’ve branded my passwords as “passphrases” instead. This is because instead of a single, short, complex word, my program encourages entire sentences. Since the ability to brute force a password decreases exponentially as length increases, and it is easier to remember a phrase rather than a complicated amalgamation or letters number and symbols, a passphrase should be preferred. Sprinkling in the occasional symbol to prevent dictionary attacks will make them totally uncrackable.
In addition? You can have an unlimited number of passphrases. Forgot one? No biggie. Use your backup passphrases, then remind yourself what your original passphrase was after you log in.
All this accomplished on a system that runs entirely locally is, in my opinion, interesting. Probably it has been done before, and almost certainly it has been done better than what I will be able to make, but I’m happy I was able to think up a design I am proud of.
rant
security
encryption