Ranter
Join devRant
Do all the things like
++ or -- rants, post your own rants, comment on others' rants and build your customized dev avatar
Sign Up
Pipeless API

From the creators of devRant, Pipeless lets you power real-time personalized recommendations and activity feeds using a simple API
Learn More
Comments
-
"The core problem with passwords is that they reside on a server."
That's so empty I don't know what it means... -
Depends on context.
On Windows this is a huge problem: While the cleartext password of the logged in user (from console or RDP) is not stored in a persistent database, it is in memory for the length of a session.
This means, if a Windows server administrated with RDP is compromised (e.g. with malware), the user account is as well. As sessions are commonly done with network wide credentials, it may hurt the whole network.
The emotet malware does this: It waits on a server / workstation for a domain administrator to log on and uses his credentials to compromoise the network.
For web applications there is a similar issue: in case a hacker can execute arbitrary code, as the web application takes the password unhashed from the user before comparing it to the stored hash. -
I think the 'expert' still draws the wrong conclusion:
The problem is that the same passwords are used for multiple resources. -
 bahua124725y@sbiewald
bahua124725y@sbiewald
Sure, but when the server has a bad security design, hacking it gets you everybody's credentials, regardless of how good or bad the discipline is of each user.
Related Rants

 Did you say security?
Did you say security?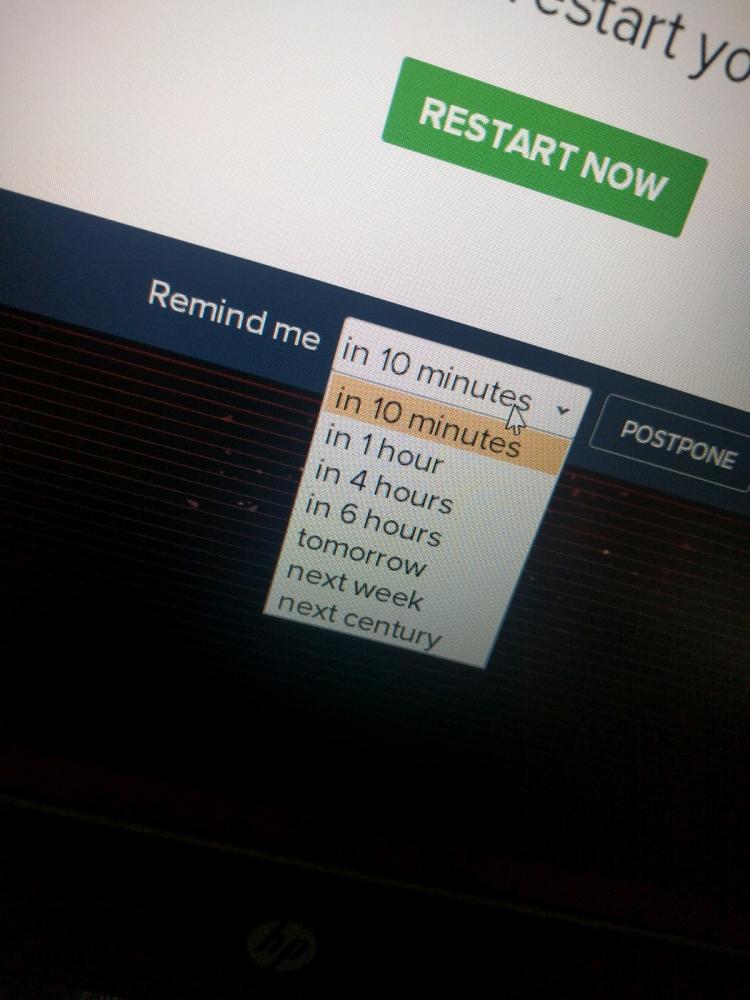 10 points for next century option.
10 points for next century option.
Expert: "The core problem with passwords is that they reside on a server."
I suppose that's true, but only if you're a complete moron. Store a hash of a password, and users can authenticate against it with a password that doesn't get logged. This is technology that's been around for over fifty years. If you're storing passwords on a server, you deserve whatever trouble you get.
rant
security
hacks
passwords
best practices