Ranter
Join devRant
Do all the things like
++ or -- rants, post your own rants, comment on others' rants and build your customized dev avatar
Sign Up
Pipeless API

From the creators of devRant, Pipeless lets you power real-time personalized recommendations and activity feeds using a simple API
Learn More
Comments
-
 Kimmax106839yPassword authentication is obsolete.
Kimmax106839yPassword authentication is obsolete.
Enroll your publickey instead.
If you really really really need pass auth, add Googles 2FA PAM module to the mix and setup the user as proper sudoer. Nooo, User bla ALL NOPASSWD is not a proper use of sudo rights.
Keep your privatekey safe stored and encrypted with a passphrase and you should be good to go.
Bonus points for using a VPN to the host and make SSH listen there only.
Also: Fail2Ban. -
 rayanon13579yYeah, like @Kimmax said disable password based auth on your servers. Lesser attack surface on the server. Use only SSH keys to login. And setup Fail2ban.
rayanon13579yYeah, like @Kimmax said disable password based auth on your servers. Lesser attack surface on the server. Use only SSH keys to login. And setup Fail2ban. -
@Kimmax You are of course right, but since I hadn't used ssh myself at all I didn't think about that yet. Good to keep in mind though.
Also fail2ban is practically the same as denyhosts right? (from what I've read) -
 Linux429879y@LucaScorpion
Linux429879y@LucaScorpion
Fail2ban is more flexible. You can for exemple set up automatic "complains", so fail2ban send a email to the abuse Contact of the IP range
Related Rants

 Did you say security?
Did you say security?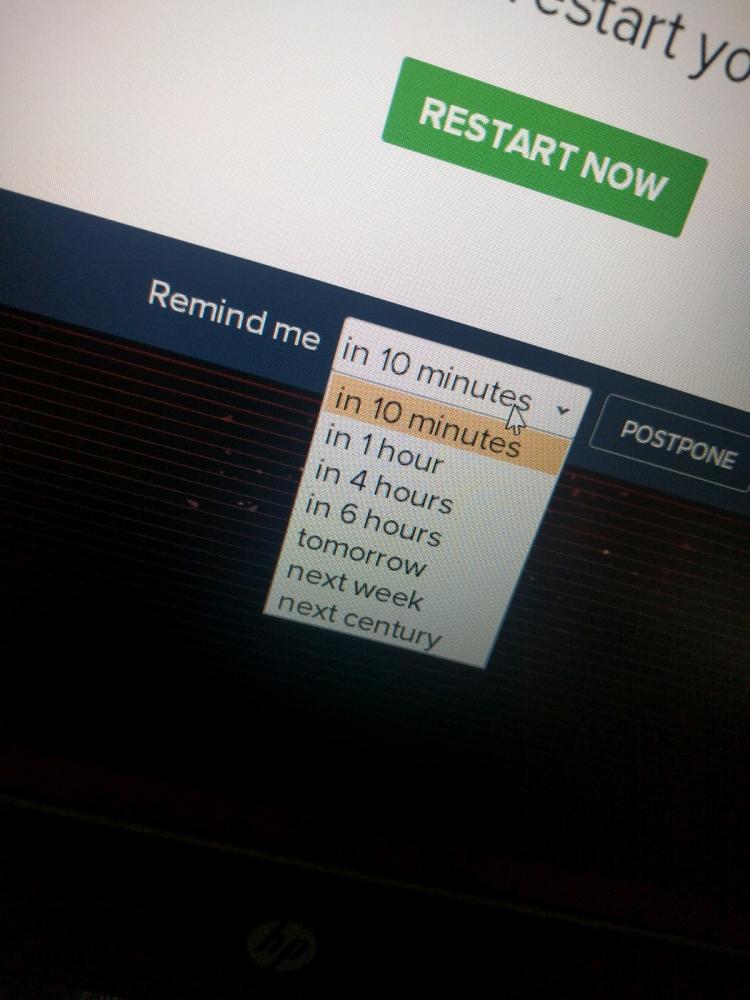 10 points for next century option.
10 points for next century option.
I set up unRAID on my server this weekend, and only just checked my logs to see if anything weird was happening. Turns out 2 IPs have been trying to brute-force the SSH password all weekend. I quickly installed the DenyHosts plugin and reminded myself to always use a strong password, which luckily I did.
A bit later now, and one of the 2 gave up, the other one keeps trying but of course the connection is refused. Just keep trying buddy :P
undefined
unraid
ssh
security
strong passwords