Ranter
Join devRant
Do all the things like
++ or -- rants, post your own rants, comment on others' rants and build your customized dev avatar
Sign Up
Pipeless API

From the creators of devRant, Pipeless lets you power real-time personalized recommendations and activity feeds using a simple API
Learn More
Comments
-
 jchw10958yThis is why I'm glad for cloud-init and the widespread ability to provision VMs with key auth only by default. Probably still wise to set up fail2ban, but at least you can start secure from the get go.
jchw10958yThis is why I'm glad for cloud-init and the widespread ability to provision VMs with key auth only by default. Probably still wise to set up fail2ban, but at least you can start secure from the get go. -
I can set it up later, no need a configtest, enough iptables for the moment, default hot words in spam filter is OK, no need of any other logs than systemctl's...
-
 sinisas3198yYou should also allow ssh only from your ip. If you are using control panel of a sort, aws/cloud you should have some security group settings where you can add your ip.
sinisas3198yYou should also allow ssh only from your ip. If you are using control panel of a sort, aws/cloud you should have some security group settings where you can add your ip. -
 cr782708yI once saw some outgoing connection to an ip in china from my vps, the pid using it was the sshd process. That was at about 2 am. Activated the provider firewall, restarted a few times, installed fail2ban, installed logwatch and disabled ssh root logins (yeah ik i was stupid back then). Now when somebody logs in to the server, a web request gets sent immediately which sends a push notification to my phone. Secure now. I still get a few thousand failed logins per day. And no, this server isn't big or something, it's just a private dev server...
cr782708yI once saw some outgoing connection to an ip in china from my vps, the pid using it was the sshd process. That was at about 2 am. Activated the provider firewall, restarted a few times, installed fail2ban, installed logwatch and disabled ssh root logins (yeah ik i was stupid back then). Now when somebody logs in to the server, a web request gets sent immediately which sends a push notification to my phone. Secure now. I still get a few thousand failed logins per day. And no, this server isn't big or something, it's just a private dev server... -
 AllenII16148yAnd here i was saying I'll set up a VPS just to get some practice working with them and nobody's gonna bother my negligible corner of the world wide web.
AllenII16148yAnd here i was saying I'll set up a VPS just to get some practice working with them and nobody's gonna bother my negligible corner of the world wide web. -
 SHA-25614368yChanged to key only authentication on my server and changed the SSH port..my logs are silent since then...might add port knocking for extra security...
SHA-25614368yChanged to key only authentication on my server and changed the SSH port..my logs are silent since then...might add port knocking for extra security...
Related Rants

 Did you say security?
Did you say security?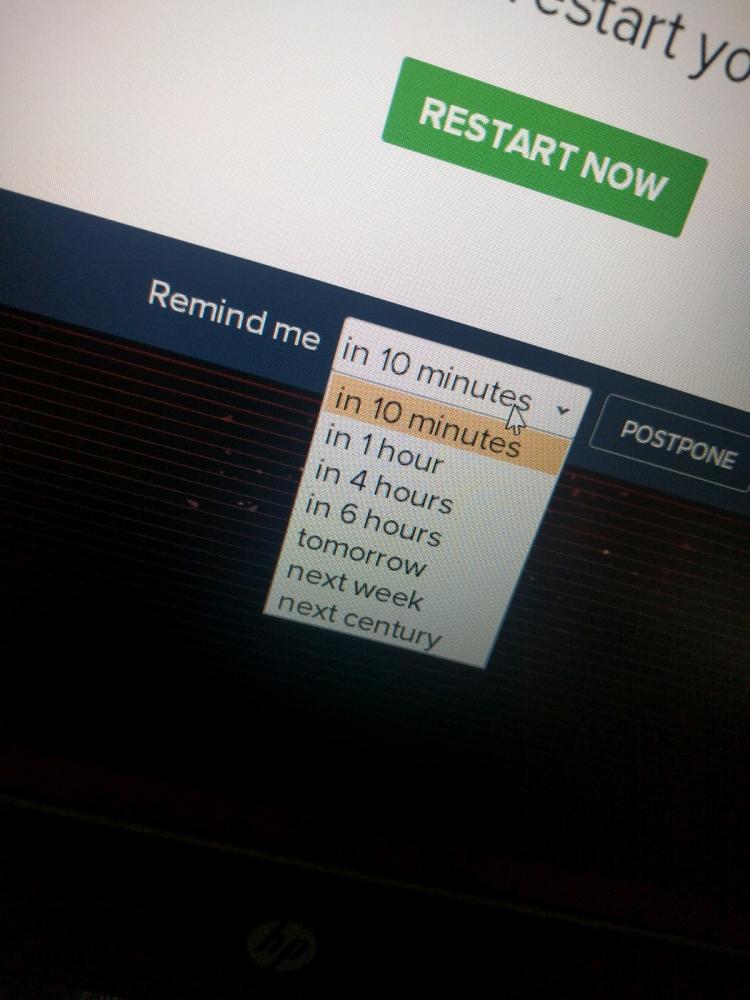 10 points for next century option.
10 points for next century option.
Funny story about the first time two of my servers got hacked. The fun part is how I noticed it.
So I purchased two new vps's for proxy server goals and thought like 'I can setup fail2ban tomorrow, I'll be fine.'
Next day I wanted to install NginX so I ran the command and it said that port 80 was already in use!
I was sitting there like no that's not possible I didn't install any server software yet. So I thought 'this can't be possible' but I ran 'pidof apache2' just to confirm. It actually returned a PID! It was a barebones Debian install so I was sure it was not installed yet by ME. Checked the auth logs and noticed that an IP address had done a huge brute force attack and managed to gain root access. Simply reinstalled debian and I put fail2ban on it RIGHT AWAY.
Checked about two seconds later if anyone tried to login again (iptables -L and keep in mind that fail2ban's default config needs six failed attempts within I think five minutes to ban an ip) and I already saw that around 8-10 addresses were banned.
Was pretty shaken up but damn I learned my lesson!
undefined
wk55
security
servers
hacked
server