Ranter
Join devRant
Do all the things like
++ or -- rants, post your own rants, comment on others' rants and build your customized dev avatar
Sign Up
Pipeless API

From the creators of devRant, Pipeless lets you power real-time personalized recommendations and activity feeds using a simple API
Learn More
Comments
-
 donkulator3992359dUnless you build it all yourself, down to the OS level, you have to trust someone. And even if you did build it all yourself, the person you're talking to has to trust you.
donkulator3992359dUnless you build it all yourself, down to the OS level, you have to trust someone. And even if you did build it all yourself, the person you're talking to has to trust you. -
 Grumm1967359dExactly what @donkulator said.
Grumm1967359dExactly what @donkulator said.
At what point will you gain the trust of the users to use it ?
In these cases, I like to give Apple as a great example. The whole OS is closed source. They claim that they don't store personal data, yet later on it was proven that it was not true. They tracked every single bit of information.
So who can guaranty that your system does not have a backdoor ? Maybe the FBI has given you 30m $ so they can have a sneak-peek to the messages... -
 azuredivay1224359d@donkulator im aware everything from OS to ISP to CISCO Hardware/Network Switches can be backdoored
azuredivay1224359d@donkulator im aware everything from OS to ISP to CISCO Hardware/Network Switches can be backdoored
But that's also the case for the other "secure" software on the market so we'd be on the same field there no? unless they're building their own Linux server images but that only closes 1 possible backdoor, they're not re-creating their own network infra after all
@Grumm im not worried about the users part, since that part isnt provable, But I'm curious about the system-design
for how in-depth the secure messaging platforms go, it made me wonder if it's at all needed? keeping things in-memory and encrypting should put me at par with what others offer -
 donkulator3992359d@azuredivay Ensuring the OS keeps things in memory only and never writes them to a swap file is non-trivial, especially if it's a VM.
donkulator3992359d@azuredivay Ensuring the OS keeps things in memory only and never writes them to a swap file is non-trivial, especially if it's a VM. -
 azuredivay1224359d@donkulator ofc not a VM, im talking about a server on a rack in a Data Centre, or a self-operated static-IP server in your home
azuredivay1224359d@donkulator ofc not a VM, im talking about a server on a rack in a Data Centre, or a self-operated static-IP server in your home
there's 0 cloud involvement in any of this -
 jestdotty6770359d@azuredivay Intel management software is sus af
jestdotty6770359d@azuredivay Intel management software is sus af
amd has a similar thing
https://en.wikipedia.org/wiki/...
also I remember they were trying to fuck kernels and put DRM in them, you know about how DRM software historically acts like a virus and even bricked PCs on occassion. you will own nothing and you will be happy
-
 jestdotty6770359dI want the avoid man in middle attack explained in dumber terms
jestdotty6770359dI want the avoid man in middle attack explained in dumber terms
cuz I was gonna write a client like this
the reason why security is hard is if people know you're famous for security other people will be very interested in compromising your security. the best security is through obscurity. don't be popular, don't have anything people want, don't use anything that's popular. if there's a will there's a way, it's just a matter of time. just stay out of places where there's will -
 Grumm1967359d@jestdotty If you want to remove the man in middle attack, well you then only need to propose a service where you drive person A to the house of person B and let them talk in person.
Grumm1967359d@jestdotty If you want to remove the man in middle attack, well you then only need to propose a service where you drive person A to the house of person B and let them talk in person.
Anything over a cable or signal can be tapped into and listen too.
this is an issue since they started using a telegraph... -
 devRancid662359d"to avoid mitm" this was solved years ago with TLS
devRancid662359d"to avoid mitm" this was solved years ago with TLS
And to actually avoid anyone else reading it, regardless of server backdoors or hypothetical mitm: end-to-end encrypted messages -
 electrineer28547359dWhose communication do you want to secure? The communication between you and your server? Your solution sounds fine for that.
electrineer28547359dWhose communication do you want to secure? The communication between you and your server? Your solution sounds fine for that. -
 azuredivay1224358d@jestdotty true, the more ur stationary, the easier you are to find and target
azuredivay1224358d@jestdotty true, the more ur stationary, the easier you are to find and target
Thats why i go with random public IPs and ports being shared for this talk and not a 1-stop domain ppl can find
@Grumm even with certificate fingerprint verification? coz the solution assumes broadcasting the fingerprint pre-communication and only continuing it till the fingerprints match, u add a daily/hourly rotation and u also block possible bruteforcing
@electrineer yep, since both users communicate to-from the server, no direct U2U involved
rudamentary tech but theoretically secure enough -
 Grumm1967358d@azuredivay Sure, but who will moderate it ?
Grumm1967358d@azuredivay Sure, but who will moderate it ?
Let's say you make the most secure messenger app. And people use it for bad and illegal stuff...
You as company cannot control the content of the messages, nobody can ? Is it the best solution ? -
 azuredivay1224358d@Grumm thats the point!
azuredivay1224358d@Grumm thats the point!
I was curious reading the reports of "IRL bad people" being caught by security coz they used something simple like WhatsApp, or the backdoored Signal or Proton and wondered why go that route in the first place?
If real bad ppl didnt want to get caught, why not just use the "messages-in-memory" solution? -
 azuredivay1224357d@jestdotty yep, as long as the encryption algo itself isnt backdoored to be decryptable, with enough daily shuffling this should suffice (theoretically)
azuredivay1224357d@jestdotty yep, as long as the encryption algo itself isnt backdoored to be decryptable, with enough daily shuffling this should suffice (theoretically)
the only attack area then is actual server itself and if they get access, take a memory dump then go through it to find the chat content
with nothing in disk and no IP/logs, this greatly reduces their spying chances, compared to bent-over-backwards-for-CIA companies like Signal or Proton
Related Rants

 Did you say security?
Did you say security?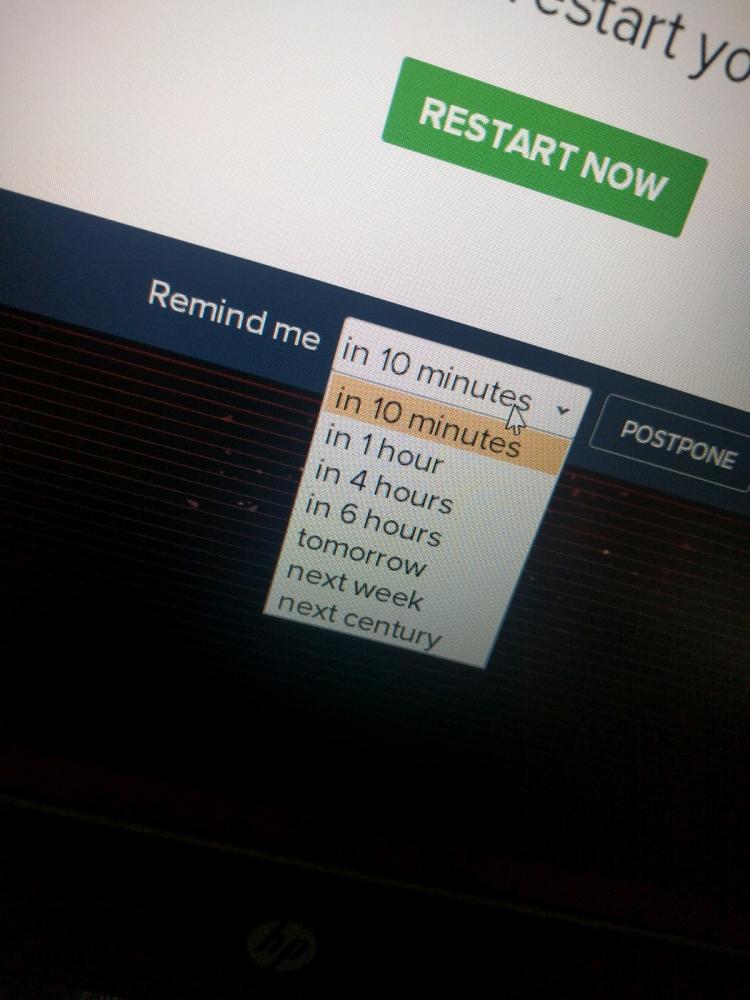 10 points for next century option.
10 points for next century option.
For someone not deep-into-security, can someone tell me why "encrypted"/"non-compromised" communication is hard?
Wouldn't a private server that holds conversation in-memory (imagine Dictionary holding U2U GUID-GUID list of 'msg' objs) suffice?
Incoming IP info is disregarded and nothing gets written on-disk ever
Need to erase everything? just reboot the server, it's all in memory anyway
To avoid man-in-the-middle, pre-handshake check cert integrity by exposing the certificate-fingerprint by another endpoint, if the fingerprints match, proceed to switch to websocket
Wouldn't this be wayyyy more secure for actual anti-establishment talks than all the fancy probably-backdoored software that exists today? .-.
Hell it's easy enough that someone could make it go live in a few days, keep it up accessible if you know the IP and port to communicate and close-and-delete when done
question
security