Ranter
Join devRant
Do all the things like
++ or -- rants, post your own rants, comment on others' rants and build your customized dev avatar
Sign Up
Pipeless API

From the creators of devRant, Pipeless lets you power real-time personalized recommendations and activity feeds using a simple API
Learn More
Comments
-
 stop65806y1. Wait until someone logs in and use pass-the hash?
stop65806y1. Wait until someone logs in and use pass-the hash?
2. No. New versions have new bugs that dont work on older releases. Usually the CVE Database saves programs and their version to document bugs. older versions have usually bugs that allow you getting SYSTEM rights. -
Networking attacks to gain access to other employees' accounts? And use them for scripts.
-
2012 (at least 2012R2) is still supported, even 2008 still is - so the customer can still fix it afterwards.
Are you sure with IIS 4.5? Wikipedia lists IIS 5 for Windows 2000, and I haven't found anything about IIS 4.5. -
If you get on one of the servers, wait for one admin to log in, or even purposely trigger a monitoring event.
As many persons login with domain admin credentials, you can now overtake the whole domain. -
 irene32736yKeylogger your own machine and call IT support for something that needs admin access to change. Grab their credentials from keylogger after change. Log into AD or whatever domain tool the IT person has to elevate one of the other user accounts. Use stolen user account to do admin things until you have a back door.
irene32736yKeylogger your own machine and call IT support for something that needs admin access to change. Grab their credentials from keylogger after change. Log into AD or whatever domain tool the IT person has to elevate one of the other user accounts. Use stolen user account to do admin things until you have a back door. -
@enigmamachine Pass-the-hash / -ticket works even for remote logon where the password is not necessarily transmitted to the workstation.
-
@R1100 (and @ any interested admin who didn't know about this)
To prevent logon with administrative credentials on non administrative machines, Microsoft has published a quite large list of recommendations.
https://docs.microsoft.com/en-gb/...
Related Rants

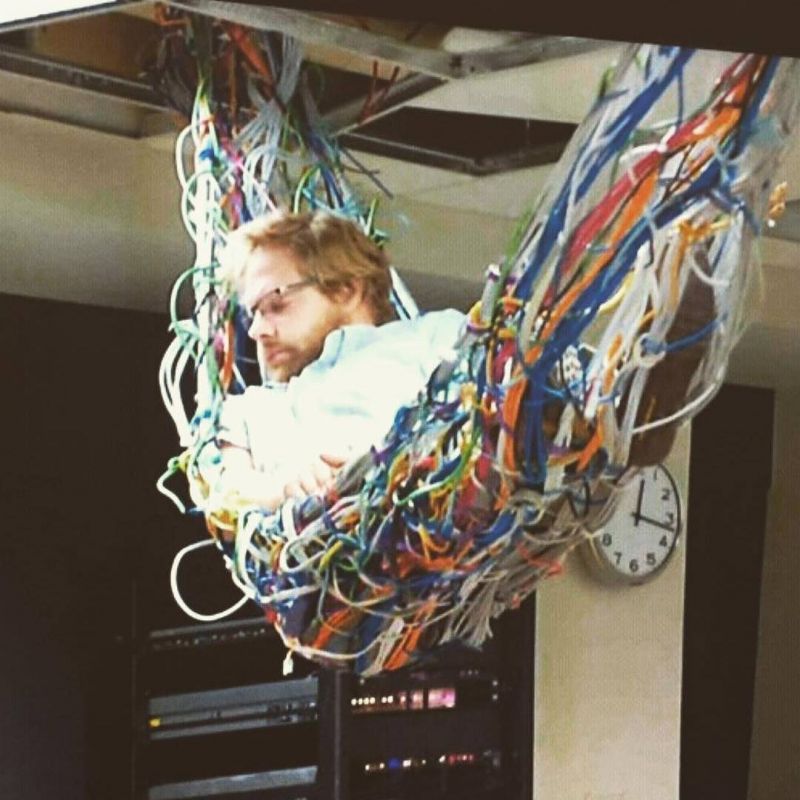 A sys admin in his natural environment.
A sys admin in his natural environment. Well... Erm...
Well... Erm...
I'm performing a pentest for my client.
So after scanning my client's network I understood they're using IIS 4.5 and windows server 2012 (or 2012 R2)
I know the systems are real old.
And there are known exploits for them.
The tricky part is I have to stay hidden and I only have my own credentials for logging in to the asp page. (Uploading a script is almost crossed cuz it will reveal my identity)
Also I have access to the local network with some of the other employees user/pass.
Any recommendation for exploiting and staying hidden at the same time ?
One more question : will exploits for newer versions work for the older ones necessarily?
rant
pentest
help
question
sysadmin
exploit