Ranter
Join devRant
Do all the things like
++ or -- rants, post your own rants, comment on others' rants and build your customized dev avatar
Sign Up
Pipeless API

From the creators of devRant, Pipeless lets you power real-time personalized recommendations and activity feeds using a simple API
Learn More
Comments
-
Fail2ban is a brilliant tool. Once properly configured I just copy the config file over to my new server with the appropriate version and all works fine with minor additional confirmation. In fact I have created a shell script to do it for me as the steps are always the same.
-
Meeh.. Setting root pw to a hash digest of some random data [for recovery measures] and using ssh keys for BAU is good enough 😁
-
Just don't have SSH open to the world. All my VMs use an ansible script to establish their firewalls. One server has OpenVPN and the others only have port 22 open on the private network they share.
You can find my ansible roles here:
https://github.com/sumdog/bee2 -
 bahua124696y@Teknas
bahua124696y@Teknas
"Safe enough," is extremely relative. It's much, much harder to brute force than password authentication, but it's still possible. There is no such thing as a 100% secure solution, but SSH restricted to pubkey auth is pretty dang close.
Related Rants

 Did you say security?
Did you say security?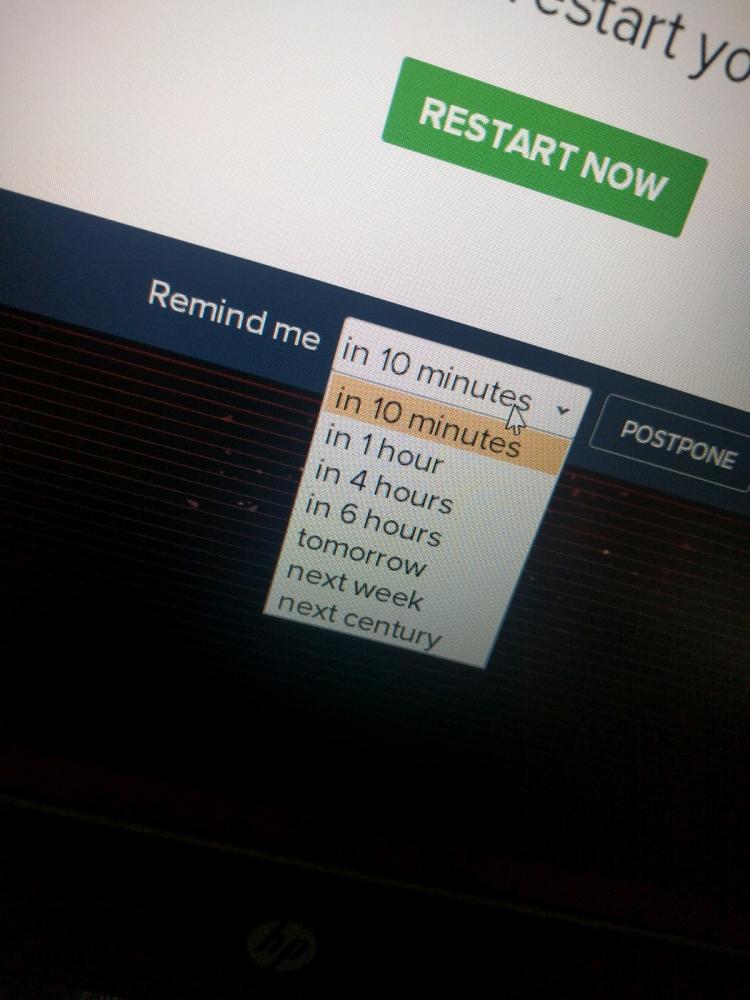 10 points for next century option.
10 points for next century option.
If you want to install, configure, and dedicate resources to fail2ban, knock yourself out, but putting these options in your sshd_config alone will save you mountains of headache:
PermitRootLogin no
PasswordAuthentication no
random
fail2ban
ssh
security