Ranter
Join devRant
Do all the things like
++ or -- rants, post your own rants, comment on others' rants and build your customized dev avatar
Sign Up
Pipeless API

From the creators of devRant, Pipeless lets you power real-time personalized recommendations and activity feeds using a simple API
Learn More
Comments
-
 possum15385y@ilechuks73 Not my problem anymore (and something evil in me hopes so), I've had it with that mfing bs in that mfing company and quit next month
possum15385y@ilechuks73 Not my problem anymore (and something evil in me hopes so), I've had it with that mfing bs in that mfing company and quit next month -
Depending on where you're at, you can anonymously report this lol. It's illegal in maaaany places to deliberately tell an employee to ignore data safety measures.
I'll add that I implore you to have these orders from your manager signed in writing and have a lawyer advise you on how to properly handle this situation privately.
If, when you quit, the company wants to blame you for something going wrong, you'll want proof they told you to stand down. This can get REALLY ugly for you if you're not careful. -
 kiki374865yIdk, with that logic a nice, fat collective lawsuit should be just what this company needs. So much business value.
kiki374865yIdk, with that logic a nice, fat collective lawsuit should be just what this company needs. So much business value. -
Legible passwords may actually be a good thing when compensating the reduced entropy by increasing the length.
Everyone knows https://xkcd.com/936/ by now.
If the user will probably not use a password manager or click on a link to enter the password or token, chaining random syllables or words is better than chaining random glyphs.
Calculation of count of possible passwords is the same as with glyphs for chains of randomly chosen items (syllables or words):
<Amount of possible items> raised to the power of <count of chosen items>. -
@Oktokolo stop sharing this. This has been proven to not be that much better (dictionaries attacks).
Password managers or nothing, specially for business accounts. -
@possum
Step 1: papertrail!
Step 2: leak the info to customers.
We'll see if the absence of security does not hold any value... -
@react-guy
A dictionary attack on a random sequence of syllables or words is equivalent to a bruteforce attack on a random sequence of glyphs.
You trade increased length for legibility - thats all.
The mentioned formula works regardless, whether the items are glyphs, syllables or letters - it is only about the amount of possible items and how many are randomly chosen. -
@Oktokolo yet you are more likely to keep using the same password everywhere, which is actually much more dangerous than a weak password.
I am actually switching to login-through-email on most of my services. Users won't follow best practices anyway. -
@Oktokolo enforcing password characters reduces their entropy though. They take more "volume" but less "density" since the domain of each digit in the password is shortened to a smaller set.
If I'm going to pen-test a site and try to brute passwords, I'm going to find out all of the parameters of the password entry to make the search set smaller.
That's why enforcing certain symbols does NOT increase entropy and can even work against the security of your application.
For example, if I only enforce that A and B are used in passwords, that's 1 bit of entropy each.
Alternatively, if I allow any byte value (I know, that isn't common either), that's 8 bits per digit.
That means the password AAAAA in the first scheme has 5 bits of entropy, whereas in the second scheme it has 40. That's a huge difference. -
@react-guy
I am writing about randomly generated passwords here.
Also: Why would it be more likely to use the same password everywhere, when passwords in general become easier to remember?
Login-through-email also works. But please still allow simple very long passwords for us few, who actually do use a password manager.
Scenarios where legible passwords really shine:
- Device login.
- Password manager master password.
- Any token that might have to be entered by hand (like when doing actual two-factor authentication which doesn't use the same device for both factors).
Related Rants


 Conversation with my Boss
B: Are u a hacker?
M: No
B: We need a hacker?
M: Why?
B: Because X department w...
Conversation with my Boss
B: Are u a hacker?
M: No
B: We need a hacker?
M: Why?
B: Because X department w... When your boss wants it done now but you're on vacation
When your boss wants it done now but you're on vacation
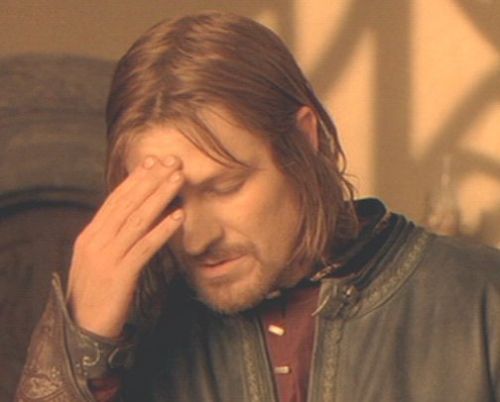
In other news, I have been forbidden by my boss to implement any security or performance improvements into the company infrastructure as this holds no business value. Furthermore, passwords are not to be a random alphanumeric+special-chars string but something legible.
rant
boss