Ranter
Join devRant
Do all the things like
++ or -- rants, post your own rants, comment on others' rants and build your customized dev avatar
Sign Up
Pipeless API

From the creators of devRant, Pipeless lets you power real-time personalized recommendations and activity feeds using a simple API
Learn More
Comments
-
Jesus Christ dude you're a fucking terrible co worker.
I feel sorry for your co workers. -
 shine9367yOK. I don't think you people get it. The moral of the story is "don't fucking leave your machine unattended - ever!"
shine9367yOK. I don't think you people get it. The moral of the story is "don't fucking leave your machine unattended - ever!"
Inside the office, it's a prank. Outside, it's serious.
Now, I might have sabotaged my colleagues coding skills / reputation (something that can be re-earned). Imagine the sabotage if the code-base of the application leaked outside the company.
The email - I did not send it.
I admit that I went overboard with the facebook stuff.
This one, imagine the impact of the situation if this exact same scenario happened outside of the office environment. The code-base that runs the application is just sitting there for anyone to take and consume.
I only inverted some conditional symbols on one file. In the wrong hands, that is definitely not what is going to happen.
And no, I'm not bragging / boasting. I'm just showing a lesson to people who leave their machines unattended and the implications of it. -
So everyone should be paranoid, have trust issues and fear sabotage at his company. Lovely atmosphere.
I'd suggest you to rethink your attitude, locking the station of your COWORKER would "teach" them in a friendly way. -
 C0D4644187yDoing this, unless in a controlled manner where the code won’t touch prod without checks and bounds being in place is fucking idiotic.
C0D4644187yDoing this, unless in a controlled manner where the code won’t touch prod without checks and bounds being in place is fucking idiotic.
I get you’re trying to prove a point, But you had plenty of opportunity to correct your malicious change. I can only hope that if statement didn’t mess with financials or critical systems. -
 shine9367y@Alice You're right. I'm an asshole.
shine9367y@Alice You're right. I'm an asshole.
I'm an asshole for considering that scenario outside the office atmosphere - in a coffee shop, on the subway, in a pub.
I'm not saying that it was the perfect of lessons to give anyone but that must have taught at least that one person to never leave their machine unattended even if it was in the office.
What I've learnt the hard way has always stuck around with me forever. I hope it does for them too.
I wouldn't mind if that happened in the office environment because we are still in control. We know what went wrong, where and how to fix it.
I don't know what would happen if the exact same scenario happened in a coffee shop where a lot of crackers already lurk for such opportunities. Ransomware, DDoS, attack from the inside, request flood, a full-blown data breach.
Let's talk about sabotage and fucking the company over then. At that point, it just wouldn't be me sabotaging the company. -
@shine Nobody with a brain (as in programmers that work with computers for a living) leaves their laptop/computer unattended in a public setting (like a library, coffee shop, ect).
The office is supposed to be a safe area that you can step away for 30 seconds without a cunt fucking everything up. -
 shine9367y@Stuxnet That's the problem. I've worked out of co-working spaces and I've seen many people leave their machines unlocked in open spaces. To those people, I've also politely explained what would happen if someone had access to their account.
shine9367y@Stuxnet That's the problem. I've worked out of co-working spaces and I've seen many people leave their machines unlocked in open spaces. To those people, I've also politely explained what would happen if someone had access to their account.
And they'd lock their machines for the rest of the day, but the next day, it'd just go back to the same old.
I know for a fact that a person who got their resignation and a hate email almost sent to the entire company never leaves his machine unlocked anymore.
I've learnt a lot of things the hard way and those have stuck with me so far. I don't remember someone advising me against doing something and me following it the next day forth.
It's not like my organization doesn't have any security policies against such stuff. Or not conducting regular awareness sessions for these security policies. It's just that people ignore the important parts unless they come face-to-face with the hard truth of what could actually happen if they did. -
 shine9367y@rantalicious For me, I value security (even if it is in a safe environment) with utmost priority. And I cannot just sit around seeing all the machines in the office just stay open when everyone's gone out for lunch.
shine9367y@rantalicious For me, I value security (even if it is in a safe environment) with utmost priority. And I cannot just sit around seeing all the machines in the office just stay open when everyone's gone out for lunch.
It takes one person who gets access to the office to eliminate that company for good. And I cannot sit around and regret that I could've prevented it only if there was a way that everyone would have locked their systems when they went out for lunch.
Like I said earlier, it's not like we don't have policies or awareness sessions for all of this. It's just that people tend to ignore the hard truths until it hits them in the face.
Well, that's what I'm doing on a more lower level with minimal damage, but enough to convey the point across. -
 shine9367y@BoomRaccoon Locking the station would do no good inside the office. And besides the person would just think naturally that the machine timed out and went to sleep. They wouldn't even consider the hard truth of their machines being compromised. What I'd be more bothered about is what happens outside the office. These pranks are just tastes of what could so many times multiplied if it were to happen outside.
shine9367y@BoomRaccoon Locking the station would do no good inside the office. And besides the person would just think naturally that the machine timed out and went to sleep. They wouldn't even consider the hard truth of their machines being compromised. What I'd be more bothered about is what happens outside the office. These pranks are just tastes of what could so many times multiplied if it were to happen outside.
This damage is from within your organization, that's nothing compared to what you could get from the outside. You could probably debug your way through a prank like this one.
Tell me how you'd navigate through a DDoS. Or an attack from the inside - when your application is the actual attacker.
How would you handle a ransomware attack or a data breach?
Those are more serious issues that needs to be addressed than some random guy going around playing such random pranks only to prove a more serious point. -
 shine9367y@C0D4 Honestly, I didn't expect the code to reach production. Of course, we had our checks and bounds. It's just that it was a hot-fix had the exception to bypass all of those checks.
shine9367y@C0D4 Honestly, I didn't expect the code to reach production. Of course, we had our checks and bounds. It's just that it was a hot-fix had the exception to bypass all of those checks.
- I honestly thought it would be caught by the developer themselves when they ran their unit test suite.
- then there was peer review (for all pull-requests) that was bypassed by the hot-fix policy.
- there was an integration test suite that too was again bypassed by the hot-fix policy.
- there were also multiple environment deployments and manual application smoke tests that were supposed to be conducted all of which was bypassed by the hot-fix policy.
And no, this didn't affect critical systems. It was just a campaign thing that didn't work as expected. Some people who were supposed to get rewards probably lost their chances. -
 taglia5667y@shine yes, you are an asshole. You pretend to be the "good guy" just by saying "but if he did that outside of the company", but he fucking didn't.
taglia5667y@shine yes, you are an asshole. You pretend to be the "good guy" just by saying "but if he did that outside of the company", but he fucking didn't.
He was INSIDE the office, in a protected environment (if strangers wanders randomly in your office, then there are even bigger problems, but I don't think this is the case).
I ALWAYS lock my machine when I'm not at home/office. You know what? I don't even leave my laptop "alone" with strangers. But in office? Yeah, sometimes I don't lock the machine because, who would steal my code? my co-workers? my boss?
You are not a "good guy", nor a "good co-worker". You are just a moron, and you are lucky no one discovered you. If I wad your boss, I'd have directly fired you. As co-worker, I'd surely have lost mine because I'd have punched you in the face. -
 taglia5667yAnd the "I didn't thought it would have ended up in production" is not an excuse.
taglia5667yAnd the "I didn't thought it would have ended up in production" is not an excuse.
When it happened, you had the possibility to tell the truth and admit your mistake.
But hey! Why doing that? Why someone would deliberately risks its own salary to admit he was a prick?
Let's skip the responsibilities and let everybody blame an innocent.
Bravo. -
Should've just used fakeupdate.net.
Touching code even just by removing a semicolon is too rough to be considered a prank. -
 shine9367y@taglia Wait, you're blowing it out of proportion. While I agree with your first comment, I do not full agree with your second comment.
shine9367y@taglia Wait, you're blowing it out of proportion. While I agree with your first comment, I do not full agree with your second comment.
When I said I didn't put in a commit with my name in it, that didn't mean I didn't own up to what I did. And it would be futile to just let the poor developer take the blame and fall for something they didn't do. My point was to show one impact of leaving your machine unattended. And if they didn't see that point, then everything I did would go to waste.
At first, the developer thought it was a coding error that they made because it went into a commit signed by them.They'd just hate themselves for being a bad developer.
But no, I went up to them and explained what had happened and asked them whether they saw the impact of their seemingly harmless / inconspicuous actions. Then they saw my point.
Related Rants

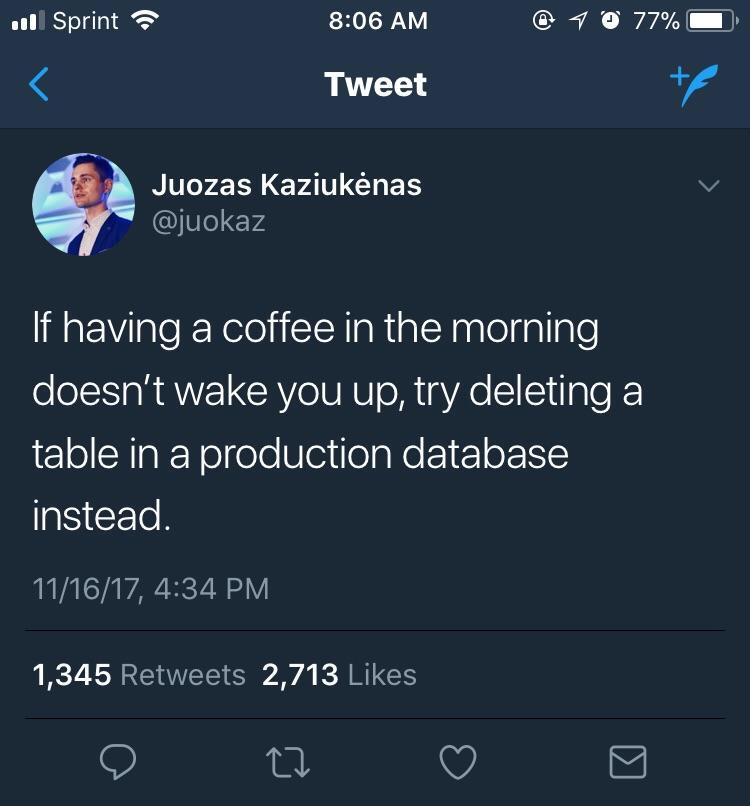 Oh sh*t
Oh sh*t It changed my life, really. 😁
It changed my life, really. 😁
A co-worker left their IDE open (and went away) with some code they were working on. There were some condition checks that were made. I simply inverted those checks and left them. Apparently, it was some bug-fix that had to go in soon. So, there was no test run to catch those issues. I hoped that even if it missed peer review, it'd be caught by the test suite. Since there was no test suite run, the code went straight into production and broke the remainder of the application that was working fine.
Of course, no one traced it back to me then because it was checked into version control by the developer and they had to take the blame / fall for the error.
Now, in hindsight, I think I should've owned up to those sins and should've left a commit there saying "Committed when <developer> wasn't at their desk leaving their IDE open" signed by <my-name>. Alas, I don't work there anymore.
rant
mess
code
production
wk37
deploy