Ranter
Join devRant
Do all the things like
++ or -- rants, post your own rants, comment on others' rants and build your customized dev avatar
Sign Up
Pipeless API

From the creators of devRant, Pipeless lets you power real-time personalized recommendations and activity feeds using a simple API
Learn More
Comments
-
You are correct (not that I am a qualified expert in the field, but I know how to read). It has been proven that one really strong password is more secure than coming up with a new one every X months.
It makes sense too. Of course, if your password is compromised and you never change it it gives people with rotten intentions more time to exploit it, but on the contrary a single good password is much less likely to be cracked by brute force.
Either way 2-phase verification with a strong passord should be enough! -
At work, I agree.
Personally, I have my stuff scripted to reset most passwords weekly -
A while back some co-workers and I discovered a loophole on our domain policy. When changing our password we can't use the last 10 passwords. However there is no time frame limit on passwords. Hypothetically one could change their password 10 times on the 90 day mandate, take 15 minutes and change their password 10 times and then change it right back to the original. How's that for security 🤣
Hypothetically of course 😏 -
IIRC several reputable security consultancy companies have found a connection between more onerous password policies and poor security practices.
Most seem to assume it is a "if you only have a hammer" type problem. -
My last job we had to update our password every 60 days. The downside is we didn't use our password at all. We had a smart card and pin the log in, and had to remember our password just so we could change it again in 2 months.
-
 C0D4644185yI deal with 45 days + MFA 🤷♂️
C0D4644185yI deal with 45 days + MFA 🤷♂️
Bastards probably want my eye and finger print scanned too at some point. -
 beleg30915yOr write them on a piece of paper and stick it on the corner of the screen ;-)
beleg30915yOr write them on a piece of paper and stick it on the corner of the screen ;-)
But seriously, I guess if there is an expiration policy, there should also be policies to control the conditions you mentioned, like enforcing a minimum password strength. Statistically, after all, changing password periodically will reduces the chance and also the effect of a possible breach, of course if you don't just give away your password every time :) -
 C0D4644185y@beleg even "last 5 passwords can't be used" can be defeated just by having:
C0D4644185y@beleg even "last 5 passwords can't be used" can be defeated just by having:
1) password
2) password2
3) password3
... you get the idea.
@OneOrZero same problem here, we have min length, characters, same password, ect, but you just append something and away you go 😅 -
 beleg30915y@C0D4 The other end can generate hashes for a neighborhood of similarity of your new password and check them against your old one.
beleg30915y@C0D4 The other end can generate hashes for a neighborhood of similarity of your new password and check them against your old one. -
 Voxera108835yIt was proven more than 20 years ago that enforced password change, at least manual change, is detrimental for just those reasons.
Voxera108835yIt was proven more than 20 years ago that enforced password change, at least manual change, is detrimental for just those reasons.
One long strong password that you do not use anywhere else is better.
The reason is that the old limit was calculated on the time to brute force the password at the time.
Today you would have to change at least weekly to come close to avoid brute force and that is just not practical or possible for 99.999 % of users ;)
On the other hand, local passwords on servers for admin should be changed regularly and preferably stored in an access portal to where you use your own password to checkout the current one.
Then you could change the passwords every hour AND use long randomly generated ones.
That way an intruder would have to break in quite deep before they can hack the password store.
And brute forcing any passwords you might find would be all but impossible.
We currently use a 90 day change + MFA but the limit will most likely go away since the security department has acknowledged that its a bad practice. -
 Voxera108835y@iiii well the combination of Mfa makes it good enough in most cases, but removing it will be a quality of life also :)
Voxera108835y@iiii well the combination of Mfa makes it good enough in most cases, but removing it will be a quality of life also :) -
 kleopi8475yif i can figure out your password is
kleopi8475yif i can figure out your password is
password12 i can guess it may be password13 next month,.
theres no security in that.
in fact if you know the password is changed regularly you can brute force for 8 letters+index instead of 10 letters in this case, vastly reducing the search space.
more rules reduce it further.
also dictionary attacks are very effective in this case -
 hjk10156195yI think the best is to have it rotate so they don't exist indefinitely but not so often it becomes a hassle (resulting in weak passwords), yearly should do it. There might be a leak somewhere on an old harddrive it something; this increases the chance it is worthless. Second password manager is mandatory. Third passwords should be at least 12 characters long.
hjk10156195yI think the best is to have it rotate so they don't exist indefinitely but not so often it becomes a hassle (resulting in weak passwords), yearly should do it. There might be a leak somewhere on an old harddrive it something; this increases the chance it is worthless. Second password manager is mandatory. Third passwords should be at least 12 characters long.
And last enforce 2fa/mfa are much as possible.
Related Rants

 Did you say security?
Did you say security?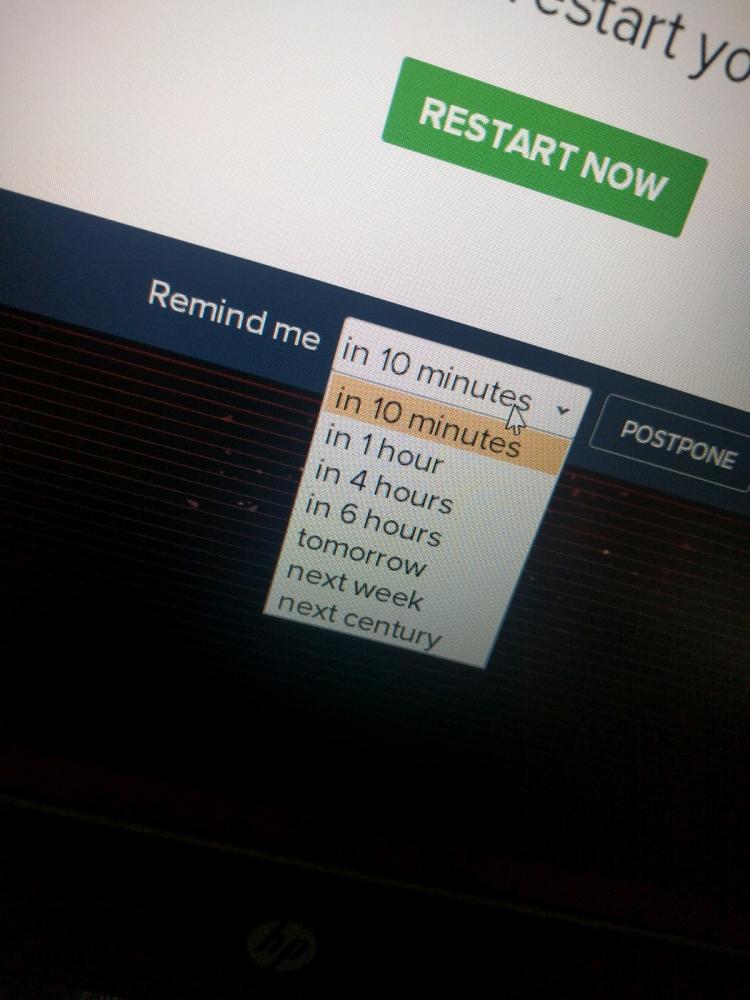 10 points for next century option.
10 points for next century option.
My argument: Password change policies (every 3, 6 moths, etc.) are a detriment to security because users will either come up with simple, throw-away passwords (knowing they will need to change them soon anyways) or use the same password anyways with a few variations.
Discuss.
rant
policy
password
security