Details
-
Aboutjust a guy that loves pizza rolls and programming
-
SkillsLearning HTML, CSS, and JavaScript.
Joined devRant on 11/13/2016
Join devRant
Do all the things like
++ or -- rants, post your own rants, comment on others' rants and build your customized dev avatar
Sign Up
Pipeless API

From the creators of devRant, Pipeless lets you power real-time personalized recommendations and activity feeds using a simple API
Learn More
-
*random person stars my repo on Github*
Me: Fuck yes give me those stars!
*checks user's profile, has starred 40k repositories*
Me: Take that star back you whore.8 -
Dev: Microsoft is shit
VS Code: (ಥ⌣ಥ)
Dev: Oh not you dear! You're not like the other guys
VS Code: (。◕‿◕。)45 -
It's 4 A.M and I just remembered what I did wrong, this happens every freaking time 😐
What the hell brain !
I need some sleep ! 5
5 -
someone did xss on one of my websites.
i didnt bother to secure anything on the website because i was marketing to dumb kids.
¯\_(ツ)_/¯3 -
School has default router username and password. And it's not just a shitty tp-link router. It runs linux.
Made a simple reverse shell and I have a fully functional linux computer. Not really a hack, but it's sad.
Soon to get to the school server!3 -
My first unintentional "hack" was in middle school, I had been programming for a couple years already and I was really bored.
My school had blocked facebook, twitter and so on because most students are lazy and think everything revolves around their "descrete" cleavage picture's likes. Any way, I thought most would be naive and desperate enough to fall into a "Facebook unblocked" app at the desktop, the program was fairly simple just a mimicking FB page done on C# ASP that saved user and passwords in an encrypted file.
I distributed it in around 5 computers and by the end of the month I had over 60 accounts, and what did I do? I used it to post a gay relationship between two of my friends on fb (one had a gf), it was dumb but boy did I laughed, after that I erased everything as it didn't seem so important. 3
3 -
Decompiled a .exe from a program that was written in Visual Basic 6.
Got a public server IP, username and Password that was hardcoded in the program.
Found out it was a SQL Server. I've now got full access to the server.
I want to tell the company about this, but I'm afraid I might get sued. Any advice?12 -
I realized hacking was about being smart when at 14 i hacked into someones computer by guessing his password on the 2nd try.
The dude loved computers more than me and watched matrix all the time.
So i typed “neo”9 -
What's the downside of having a "high tech" classroom with Bose speakers and a mid tier PC you say?
Hackers
So back in highschool we used to have these fancy "corporate" classrooms with speakers, PC and projector setup (plus really comfy chairs). Classrooms were organized in triads next to each other so we usually knew when classes where taking place next to us.
One day I decided to fuck around with teachers, I waited until he/she started class and I remotely blasted music or porn sounds on the third empty classroom and waited until the angry teacher rushed to the classroom then...silence...nothing but an empty classroom.
One day one of the teachers was so pissed because I orchestrated a Vivaldi concert with the 3 classrooms he rushed into ours and took a friend of mine who he had a personal grudge against, I kinda felt bad but not so much after my mate told me that was genius and that we should do it again. 12
12 -
Hacking/attack experiences...
I'm, for obvious reasons, only going to talk about the attacks I went through and the *legal* ones I did 😅 😜
Let's first get some things clear/funny facts:
I've been doing offensive security since I was 14-15. Defensive since the age of 16-17. I'm getting close to 23 now, for the record.
First system ever hacked (metasploit exploit): Windows XP.
(To be clear, at home through a pentesting environment, all legal)
Easiest system ever hacked: Windows XP yet again.
Time it took me to crack/hack into today's OS's (remote + local exploits, don't remember which ones I used by the way):
Windows: XP - five seconds (damn, those metasploit exploits are powerful)
Windows Vista: Few minutes.
Windows 7: Few minutes.
Windows 10: Few minutes.
OSX (in general): 1 Hour (finding a good exploit took some time, got to root level easily aftewards. No, I do not remember how/what exactly, it's years and years ago)
Linux (Ubuntu): A month approx. Ended up using a Java applet through Firefox when that was still a thing. Literally had to click it manually xD
Linux: (RHEL based systems): Still not exploited, SELinux is powerful, motherfucker.
Keep in mind that I had a great pentesting setup back then 😊. I don't have nor do that anymore since I love defensive security more nowadays and simply don't have the time anymore.
Dealing with attacks and getting hacked.
Keep in mind that I manage around 20 servers (including vps's and dedi's) so I get the usual amount of ssh brute force attacks (thanks for keeping me safe, CSF!) which is about 40-50K every hour. Those ip's automatically get blocked after three failed attempts within 5 minutes. No root login allowed + rsa key login with freaking strong passwords/passphrases.
linu.xxx/much-security.nl - All kinds of attacks, application attacks, brute force, DDoS sometimes but that is also mostly mitigated at provider level, to name a few. So, except for my own tests and a few ddos's on both those domains, nothing really threatening. (as in, nothing seems to have fucked anything up yet)
How did I discover that two of my servers were hacked through brute forcers while no brute force protection was in place yet? installed a barebones ubuntu server onto both. They only come with system-default applications. Tried installing Nginx next day, port 80 was already in use. I always run 'pidof apache2' to make sure it isn't running and thought I'd run that for fun while I knew I didn't install it and it didn't come with the distro. It was actually running. Checked the auth logs and saw succesful root logins - fuck me - reinstalled the servers and installed Fail2Ban. It bans any ip address which had three failed ssh logins within 5 minutes:
Enabled Fail2Ban -> checked iptables (iptables -L) literally two seconds later: 100+ banned ip addresses - holy fuck, no wonder I got hacked!
One other kind/type of attack I get regularly but if it doesn't get much worse, I'll deal with that :)
Dealing with different kinds of attacks:
Web app attacks: extensively testing everything for security vulns before releasing it into the open.
Network attacks: Nginx rate limiting/CSF rate limiting against SYN DDoS attacks for example.
System attacks: Anti brute force software (Fail2Ban or CSF), anti rootkit software, AppArmor or (which I prefer) SELinux which actually catches quite some web app attacks as well and REGULARLY UPDATING THE SERVERS/SOFTWARE.
So yah, hereby :P39 -
My school.
We have free WiFi access, but you need to login into your personal student account to use it.
Turns out, SQL Injection works.
It gets worse.
Table name "schueler".
SELECT *
Well.
Got all data on all students.
Name, address, phone number, passwords in plain.
I reported it using an anonymous email. Partially fixed. Standard quotes now get eacaped. Still, passwords are now MD5.47 -
I had a secondary Gmail account with a really nice short nickname (from the early invite/alpha days), forwarded to another of my mailboxes. It had a weak password, leaked as part of one of the many database leaks.
Eventually I noticed some dude in Brazil started using my Gmail, and he changed the password — but I still got a copy of everything he did through the forwarding rule. I caught him bragging to a friend on how he cracked hashes and stole and sold email accounts and user details in bulk.
He used my account as his main email account. Over the years I saw more and more personal details getting through. Eventually I received a mail with a plaintext password... which he also used for a PayPal account, coupled to a Mastercard.
I used a local website to send him a giant expensive bouquet of flowers with a box of chocolates, using his own PayPal and the default shipping address.
I included a card:
"Congratulations on acquiring my Gmail account, even if I'm 7 years late. Thanks for letting me be such an integral part of your life, for letting me know who you are, what you buy, how much you earn, who your family and friends are and where you live. I've surprised your mother with a cruise ticket as you mentioned on Facebook how sorry you were that you forgot her birthday and couldn't buy her a nice present. She seems like a lovely woman. I've also made a $1000 donation in your name to the EFF, to celebrate our distant friendship"31 -
I feel a bit bad.
My family left for the weekend sonim all alone at home.
I told everybody else not to bother me so could code.
Instead i went to buy soda,sandwich food, beer, papers and smokes (i quit smoking 6months ago ;)) and played video games for the last 2 days.7 -
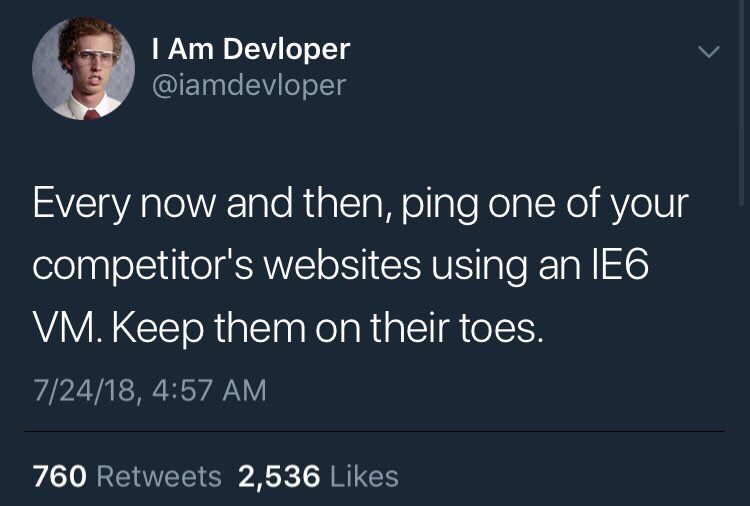
One of my teacher liked this tweet
I'm wondering if it is a hidden message for some of our teachers 🤔 8
8