Join devRant
Do all the things like
++ or -- rants, post your own rants, comment on others' rants and build your customized dev avatar
Sign Up
Pipeless API

From the creators of devRant, Pipeless lets you power real-time personalized recommendations and activity feeds using a simple API
Learn More
Search - "data breach"
-
In may this year, the new mass surveillance law in the Netherlands went into effect. Loads of people were against it with the arguments that everyone's privacy was not protected well enough, data gathered through dragnet surveillance might not be discarded quickly after the target data was filtered out and the dragnet surveillance wouldn't be that 'targeted'.
They were put into the 'paranoid' corner mostly and to assure enough support/votes, it was promised that:
- dragnet surveillance would be done as targeted as possible.
- target data would be filtered out soon and data of non-targets would be discarded automatically by systems designed for that (which would have to be out in place ASAP).
- data of non-targets would NOT be analyzed as that would be a major privacy breach.
- dragnet surveillance could only be done if enough proof would be delivered and if the urgency could justify the actions.
A month ago it was already revealed that there has been a relatively (in this context) high amount of cases where special measures (dragnet surveillance/non-target hacking to get to targets and so on) were used when/while there wasn't enough proof or the measures did not justify the urgency.
Privacy activists were anything but happy but this could be improved and the guarantees which were given to assure privacy of innocent people were in place according to the politicians... we'll see how this goes..
Today it was revealed that:
-there are no systems in place for automatic data discarding (data of innocent civilians) and there are hardly any protocols for how to handle not-needed or non-target data.
- in real life, the 'as targeted dragnet as possible' isn't really as targeted as possible. There aren't any/much checks in place to assure that the dragnets are aimed as targeted as possible.
- there isn't really any data filtering which filters out non-targers, mostly everything is analyzed.
Dear Dutch government and intelligence agency; not so kindly to fuck yourself.
Hardly any of the promised checks which made that this law could go through are actually in place (yet).
Fuck you.28 -
haveibeenpwned: MASSIVE SECURITY BREACH AT COMPANY X, MILLIONS OF RECORDS EXPOSED AND SOLD, YOUR DATA IS AT RISK, please change your password!
Company X website: Hey your password expired! Please change it. Everything's fine, wanna buy premium? The sun is shining. Great day.1 -
I realize I've ranted about this before, but...
Fuck APIs.
First the fact that external services can throw back 500 errors or timeouts when their maintainer did a drunk deploy (but you properly handled that using caching, workers, retry handlers, etc, right? RIGHT?)...
Then the fact that they all speak a variety of languages and dialects (Oh fuck why does that endpoint return a JSON object with int keys instead of a simple array... wait the params are separated with pipe characters? And the other endpoint uses SOAP? Fuck I need to write another wrapper class around the client...)
But the worst thing: It makes developers live in this happy imaginary universe where "malicious" is not a word.
"I found this cloud service which checks our code style" — hmm ok, they seem trustworthy. Hope they don't sell our code, but whatever.
"And look at this thing, it automatically makes database backups, just have to connect to it to DigitalOcean" — uhhh wait...
"And I just built this API client which sends these forms to be OCR processed" — Fuck... stop it... there are bank accounts numbers on those forms... Where's that API even located? What company?
* read their privacy policy *
"We can not guarantee the safety of your personal data, use at your own risk [...] we are located in Russia".
I fucking hate these millennial devs who literally fail to get their head out of the cloud.
Somehow they think it's easier to write all these NodeJS handlers and layers around some API, which probably just calls ImageMagick + Tesseract on the other side.
If I wasn't so fucking exhausted, I'd chop of their heads... but they're like hydra, you seal one privacy breach and another is waiting to be merged, these kids just keep spewing their crap into easy packages, they keep deploying shitty heroku apps... ugh.
😖8 -
Oh fuck and boy Jesus, how on earth is this still a thing 😦
MD fucking 5 is not a fucking “secure” crypto algorithm.
This site has 14 million breached accounts with fucking MD5 hashes.
I think I’ve had to much internet for today.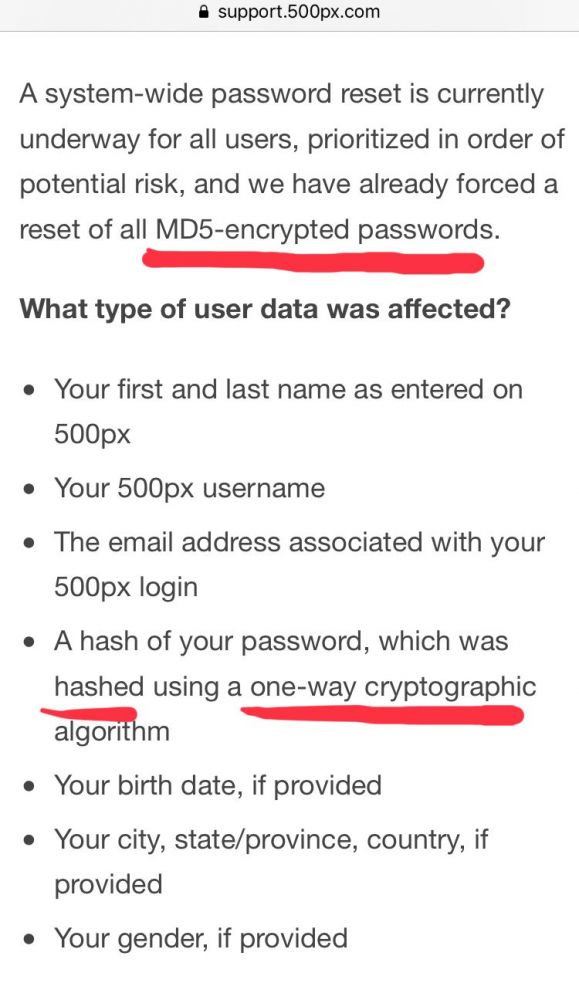 17
17 -
No, MD5 hash is not a safe way to store our users' passwords. I don't care if its been written in the past and still works. I've demonstrated how easy it is to reverse engineer and rainbow attack. I've told you your own password for the site! Now please let me fix it before someone else forces you to. We're too busy with other projects right now? Oh, ok then, I'll just be quiet and ignore our poor security. Whilst I'm busy getting on with my other work, could you figure out what we're gonna do with the tatters of our client's business (in which our company owns a stake) in the aftermath of the attack?7
-
My client is trying to force me to sign an ethics agreement that would allow them to sue me if found in breach of it. At the same time they are scraping eBay's data without their consent and refuse to sign the licence agreement. Apparently they don't understand irony.2
-
Omg, when does the Stupid stop? New Zealand just passed a law that empowers immigration officials to compel travellers to unlock their devices. Otherwise, you pay a hefty fine. They are also allowed to copy the data and do God knows what with.
The horrible invasion of privacy aside, it also brings with it some legal hurdles. What if you are making a presentation or report to an investor or someone you have a fiduciary obligation with. You are carrying IP bound by several NDA's and other funding red tape that would end your life if it got out. Are you in breach if the data gets copied by the gov officials? Worse yet you have zero control over what they do afterwards.
I don't think any of this inspires investor confidence.
Government needs to stop touching things!7 -
Paranoid Developers - It's a long one
Backstory: I was a freelance web developer when I managed to land a place on a cyber security program with who I consider to be the world leaders in the field (details deliberately withheld; who's paranoid now?). Other than the basic security practices of web dev, my experience with Cyber was limited to the OU introduction course, so I was wholly unprepared for the level of, occasionally hysterical, paranoia that my fellow cohort seemed to perpetually live in. The following is a collection of stories from several of these people, because if I only wrote about one they would accuse me of providing too much data allowing an attacker to aggregate and steal their identity. They do use devrant so if you're reading this, know that I love you and that something is wrong with you.
That time when...
He wrote a social media network with end-to-end encryption before it was cool.
He wrote custom 64kb encryption for his academic HDD.
He removed the 3 HDD from his desktop and stored them in a safe, whenever he left the house.
He set up a pfsense virtualbox with a firewall policy to block the port the student monitoring software used (effectively rendering it useless and definitely in breach of the IT policy).
He used only hashes of passwords as passwords (which isn't actually good).
He kept a drill on the desk ready to destroy his HDD at a moments notice.
He started developing a device to drill through his HDD when he pushed a button. May or may not have finished it.
He set up a new email account for each individual online service.
He hosted a website from his own home server so he didn't have to host the files elsewhere (which is just awful for home network security).
He unplugged the home router and began scanning his devices and manually searching through the process list when his music stopped playing on the laptop several times (turns out he had a wobbly spacebar and the shaking washing machine provided enough jittering for a button press).
He brought his own privacy screen to work (remember, this is a security place, with like background checks and all sorts).
He gave his C programming coursework (a simple messaging program) 2048 bit encryption, which was not required.
He wrote a custom encryption for his other C programming coursework as well as writing out the enigma encryption because there was no library, again not required.
He bought a burner phone to visit the capital city.
He bought a burner phone whenever he left his hometown come to think of it.
He bought a smartphone online, wiped it and installed new firmware (it was Chinese; I'm not saying anything about the Chinese, you're the one thinking it).
He bought a smartphone and installed Kali Linux NetHunter so he could test WiFi networks he connected to before using them on his personal device.
(You might be noticing it's all he's. Maybe it is, maybe it isn't).
He ate a sim card.
He brought a balaclava to pentesting training (it was pretty meme).
He printed out his source code as a manual read-only method.
He made a rule on his academic email to block incoming mail from the academic body (to be fair this is a good spam policy).
He withdraws money from a different cashpoint everytime to avoid patterns in his behaviour (the irony).
He reported someone for hacking the centre's network when they built their own website for practice using XAMMP.
I'm going to stop there. I could tell you so many more stories about these guys, some about them being paranoid and some about the stupid antics Cyber Security and Information Assurance students get up to. Well done for making it this far. Hope you enjoyed it. 26
26 -
The public seems to be worried a lot on the Facebook "data breach" yet doesn't bat an eye on a bigger website that has already been selling private data for more than a decade.
Google9 -
Being responsible for a massive breach of personal & financial data.
Seriously, that crap scares me way more than any amount of downtime does.1 -
---WiFi Vision: X-Ray Vision using ambient WiFi signals now possible---
“X-Ray Vision” using WiFi signals isn’t new, though previous methods required knowledge of specific WiFi transmitter placements and connection to the network in question. These limitations made WiFi vision an unlikely security breach, until now.
Cybersecurity researchers at the University of California and University of Chicago have succeeded in detecting the presence and movement of human targets using only ambient WiFi signals and a smartphone.
The researchers designed and implemented a 2-step attack: the 1st step uses statistical data mining from standard off-the-shelf smartphone WiFi detection to “sniff” out WiFi transmitter placements. The 2nd step involves placement of a WiFi sniffer to continuously monitor WiFi transmissions.
Three proposed defenses to the WiFi vision attack are Geofencing, WiFi rate limiting, and signal obfuscation.
Geofencing, or reducing the spatial range of WiFi devices, is a great defense against the attack. For its advantages, however, geofencing is impractical and unlikely to be adopted by most, as the simplest geofencing tactic would also heavily degrade WiFi connectivity.
WiFi rate limiting is effective against the 2nd step attack, but not against the 1st step attack. This is a simple defense to implement, but because of the ubiquity of IoT devices, it is unlikely to be widely adopted as it would reduce the usability of such devices.
Signal obfuscation adds noise to WiFi signals, effectively neutralizing the attack. This is the most user-friendly of all proposed defenses, with minimal impact to user WiFi devices. The biggest drawback to this tactic is the increased bandwidth of WiFi consumption, though compared to the downsides of the other mentioned defenses, signal obfuscation remains the most likely to be widely adopted and optimized for this kind of attack.
For more info, please see journal article linked below.
https://arxiv.org/pdf/...9 -
Watch out for these fucking bug bounty idiots.
Some time back I got an email from one shortly after making a website live. Didn't find anything major and just ran a simple tool that can suggest security improvements simply loading the landing page for the site.
Might be useful for some people but not so much for me.
It's the same kind of security tool you can search for, run it and it mostly just checks things like HTTP headers. A harmless surface test. Was nice, polite and didn't demand anything but linked to their profile where you can give them some rep on a system that gamifies security bug hunting.
It's rendering services without being asked like when someone washes your windscreen while stopped at traffic but no demands and no real harm done. Spammed.
I had another one recently though that was a total disgrace.
"I'm a web security Analyst. My Job is to do penetration testing in websites to make them secure."
"While testing your site I found some critical vulnerabilities (bugs) in your site which need to be mitigated."
"If you have a bug bounty program, kindly let me know where I should report those issues."
"Waiting for response."
It immediately stands out that this person is asking for pay before disclosing vulnerabilities but this ends up being stupid on so many other levels.
The second thing that stands out is that he says he's doing a penetration test. This is illegal in most major countries. Even attempting to penetrate a system without consent is illegal.
In many cases if it's trivial or safe no harm no foul but in this case I take a look at what he's sending and he's really trying to hack the site. Sending all kinds of junk data and sending things to try to inject that if they did get through could cause damage or provide sensitive data such as trying SQL injects to get user data.
It doesn't matter the intent it's breaking criminal law and when there's the potential for damages that's serious.
It cannot be understated how unprofessional this is. Irrespective of intent, being a self proclaimed "whitehat" or "ethical hacker" if they test this on a site and some of the commands they sent my way had worked then that would have been a data breach.
These weren't commands to see if something was possible, they were commands to extract data. If some random person from Pakistan extracts sensitive data then that's a breach that has to be reported and disclosed to users with the potential for fines and other consequences.
The sad thing is looking at the logs he's doing it all manually. Copying and pasting extremely specific snippets into all the input boxes of hacked with nothing to do with the stack in use. He can't get that many hits that way.4 -
A new breach has just been confirmed about 10 minutes ago. CHECK YOUR EMAILS AND PASSWORDS!!!
Details at: https://troyhunt.com/the-773-millio...
CHECK YOUR EMAILS AND PASSWORDS AT haveibeenpwned.com TO CHECK FOR WHETHER YOU WERE COMPROMISED.9 -
This has been here for years already but with the recent data breach scandles which also highlights how they profit from me, u'd think they would cancel this small amount which is wronggfully charged to start with....
I've even tried ccontacting them about it... for years.... and they don't respond.... EVER...
So much for listening to users... clearly they don't... 4
4 -
I’m LOLing at the audacity of one of our vendors.
We contract with a vendor to build and maintain a website. Our network security team noticed there was a security breach of the vendor’s website. Our team saw that malicious users gained access to our Google Search console by completing a challenge that was issued to the vendor’s site.
At first, the vendor tried to convince us that their site wasn’t comprised and it was the Google search Console that was compromised. Nah dude. Our Search Console got compromised via the website you maintain for us. Luckily our network team was able to remove the malicious users from our search console.
That vendor site accepts credit card payments and displays the user’s contact info like address, email, and phone. The vendor uses keys that are tied to our payment gateway. So now my employer is demanding a full incident report from the vendor because their dropping the ball could have compromised our users’ data and we might be responsible for PCI issues.
And the vendor tried to shit on us even more. The vendor also generates vanity urls for our users. My employer decided to temporarily redirect users to our main site (non vendor) because users already received those links and in order to not lose revenue. The vendor’s solution is to build a service that will redirect their vanity urls to our main site. And they wanted to charge us $5000 usd for this. We already pay them $1000 a month already.
WTAF we are not stupid. Our network service team said we could make the argument that they do this without extra charge because it falls in the scope of our contract with them. Our network team also said that we could terminate the contract because the security breach means they didn’t render the service they were contracted to do. Guess it’s time for us to get our lawyer’s take on this.
So now it looks like my stakeholders want me to rebuild all of this in house. I already have a lot on my plate, but I’m going to be open to their requests because we are still in the debrief phase.2 -
Just saw this:
Add comma's to your passwords to mess with the csv file they will be dumped in after a data breach9 -
"Using MD5" !? What year are we in again?
NOTICE OF DATA BREACH
Dear Yahoo User,
We are writing to inform you about a data security issue that may involve your Yahoo account information. We have taken steps to secure your account and are working closely with law enforcement.
...
What Information Was Involved?
The stolen user account information may have included names, email addresses, telephone numbers, dates of birth, hashed passwords (using MD5)2 -
I am doing some freelance work for a client who is thankfully mindful about security. I found out that they are so strict with their access because they had a huge data breach last year.
Today I was given access to their repo for connecting to their AS400. In the docker file the username and password were included and were the same for dev and prod. They also are performing no sql injection prevention. They are just joining strings together.1 -
developer makes a "missed-a-semicolon"-kind of mistake that brings your non-production infrastructure down.
manager goes crazy. rallies the whole team into a meeting to find "whom to hold accountable for this stupid mistake" ( read : whom should I blame? ).
spend 1-hour to investigate the problem. send out another developer to fix the problem.
... continue digging ...
( with every step in the software development lifecycle handbook; the only step missing was to pull the handbook itself out )
finds that the developer followed the development process well ( no hoops jumped ).
the error was missed during the code review because the reviewer didn't actually "review" the code, but reported that they had "reviewed and merged" the code
get asked why we're all spending time trying to fix a problem that occurred in a non-production environment. apparently, now it is about figuring out the root cause so that it doesn't happen in production.
we're ALL now staring at the SAME pull request. now the manager is suddenly more mad because the developer used brackets to indicate the pseudo-path where the change occurred.
"WHY WOULD YOU WASTE 30-SECONDS PUTTING ALL THOSE BRACES? YOU'RE ALREADY ON A BRANCH!"
PS : the reason I didn't quote any of the manager's words until the end was because they were screaming all along, so, I'd have to type in ALL CAPS-case. I'm a CAPS-case-hater by-default ( except for the singular use of "I" ( eye; indicating myself ) )
WTF? I mean, walk your temper off first ( I don't mean literally, right now; for now, consider it a figure of speech. I wish I could ask you to do it literally; but no, I'm not that much of a sadist just yet ). Then come back and decide what you actually want to be pissed about. Then think more; about whether you want to kill everyone else's productivity by rallying the entire team ( OK, I'm exaggerating, it's a small team of 4 people; excluding the manager ) to look at an issue that happened in a non-production environment.
At the end of the week, you're still going to come back and say we're behind schedule because we didn't get any work done.
Well, here's 4 hours of our time consumed away by you.
This manager also has a habit of saying, "getting on X's case". Even if it is a discussion ( and not a debate ). What is that supposed to mean? Did X commit such a grave crime that they need to be condemned to hell?
I miss my old organization where there was a strict no-blame policy. Their strategy was, "OK, we have an issue, let's fix it and move on."
I've gotten involved ( not caused it ) in even bigger issues ( like an almost-data-breach ) and nobody ever pointed a finger at another person.
Even though we all knew who caused the issue. Some even went beyond and defended the person. Like, "Them. No, that's not possible. They won't do such dumb mistakes. They're very thorough with their work."
No one even talked about the person behind their back either ( at least I wasn't involved in any such conversation ). Even later, after the whole issue had settled down. I don't think people brought it up later either ( though it was kind of a hush-hush need-to-know event )
Now I realize the other unsaid-advantage of the no-blame policy. You don't lose 4 hours of your so-called "quarantine productivity". We're already short on productivity. Please don't add anymore. 🙏10 -
!Rant
The new bill passed the house for ISP to be able to sell data. This get me ticked off. I already ausme that ISP did it under the table. Doesn't make it right. Now it legal for them to breach our privacy. At what leave do i need to run my own internet just to feel safe. VPN can sell the data, ISP can sell data about you. I spend my life teaching how to protect people online and now I can't even say they are safe at home from someone with wrong intention. A quote comes to mind.
"Dear lord I need to see some change, because the man in the mirror is wearing a mask"
I shouldn't have to feel every time. I boot my PC, that I need to remind my self that what I'm doing now is being sold so someone can lable me. When will the common man learn to protect their privacy online; And where is the line in the sand?
It not all bad, this event has given me the itch to code. Just to spin some heads I'm going to make a script to make random Google query across the widest array of topics, so my profile is full of contradiction.
The few who read this have a nice day!6 -
Part 1: https://devrant.com/rants/4298172/...
So we get this guy in a meeting and he is now saying "we can't have application accounts because that violates our standard of knowing who accessed what data - the application account anonamizes the user behind the app account data transaction and authorization"
And so i remind him that since it's an application account, no one is going to see the data in transit (for reference this account is for CI/CD), so the identity that accessed that data really is only the app account and no one else.
This man has the audacity to come back with "oh well then thats fine, i cant think of a bunch of other app account ideas where the data is then shown to non-approved individuals"
We have controls in place to make sure this doesnt happen, and his grand example that he illustrates is "Well what if someone created an app account to pull github repo data and then display that in a web interface to unauthorized users"
...
M******* why wouldnt you JUST USE GITHUB??? WHO WOULD BUILD A SEPARATE APPLICATION FOR THAT???
I swear I have sunk more time into this than it would have costed me to mop up from a whole data breach. I know there are situations where you could potentially expose data to the wrong users, but that's the same issue with User Accounts (see my first rant with the GDrive example). In addition, the proposed alternative is "just dont use CI/CD"!!!
I'm getting pretty pissed off at this whole "My compliance is worth more than real security" bullshit. -
Can't really say it's the most pissed off I've been probably at mild annoyance. So for the last two years I've been stressing that in order to do my job efficiently. I need handovers and documentation. It's a ball ache I know but definitely needed.
Well after not being listened too for the last two years we now are getting a documentation process. Why? Because a lack of documentation was the leading cause to a data breach.
Yeah I've been stressing that scenario for the last two years. But no one gave a damn until it happened. -
I can't believe companies fucking do this! If your users PIIs gets fucking leaked or the security is breached in any god-damned way it's YOUR FUCKING JOB to let the affected users know! 57 million users got affected! What the fucking fuck? I think they should pass proper laws where companies have to tell the victims about breaches, especially when it's at a such a huge scale. I get it that it's wasn't under Uber but some third party; but even so Uber should have talked about the level of security in their SLAs and maybe performed regular audits.
This is ridiculous!
https://darkreading.com/attacks-bre...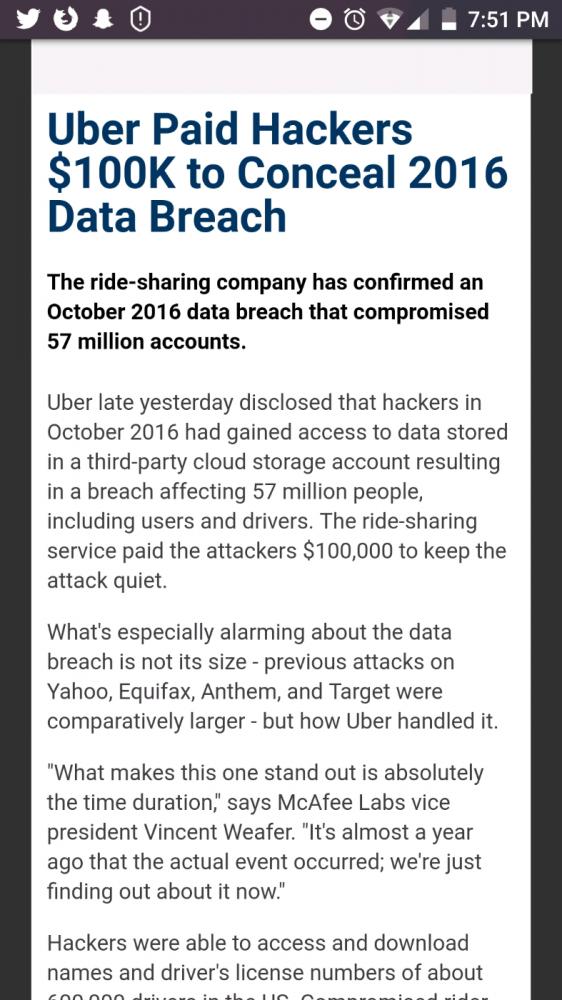 5
5 -
How is it possible my netflix password got hacked when I never used it anywhere else and it's randomly generated? I saw some weird logins with random subtitles. Google password manager told me it's in some data breach, how do I find out from where? Haveibeenpwned didn't find anything. 😐6
-
HOW I CAUGHT MY CHEATING PARTNER WITH THE HELP OF SOLACE CYBER WORKSTATIONS
Solace Cyber Workstations is a tool designed to help individuals find important information about their partner's online activities without causing any disruption or breach of privacy. This software works by gathering data that is publicly available, allowing users to understand more about their partner's digital presence. It can include social media profiles, public posts, and other online interactions, making it a comprehensive solution for those seeking clarity in their relationships. Using Solace Cyber Workstations is simple and user-friendly. The interface guides users step-by-step through the process of retrieving information. There are no complicated setups or technical skills needed. Once the user inputs the relevant details, the tool quickly navigates the internet to compile the necessary data, ensuring a seamless and efficient process. This ease of use supports individuals in their quest for knowledge about their partner's online life. One of the key features of Solace Cyber Workstations is its commitment to non-intrusiveness. The tool respects privacy and ensures that all information collected is taken from public sources. This means that users can learn more about their partner without violating their privacy or crossing any ethical boundaries. Users can feel comfortable knowing they are not engaging in any harmful or invasive practices while seeking information. Moreover, Solace Cyber Workstations are particularly useful for individuals looking to enhance trust and communication in their relationships. By using this tool, users can clarify any doubts they may have about their partner's online presence. Understanding their partner’s online interactions can lead to more open discussions and strengthen the bond between both individuals, ultimately fostering a healthier environment for the relationship. In conclusion, Solace Cyber Workstations provides a reliable and respectful way to learn about a partner's online life. Its user-friendly interface and non-intrusive methods make it an ideal choice for those who want to ensure transparency while maintaining ethical standards. By utilizing this tool, users can promote understanding and trust in their relationships, which is essential for long-term success. Send a W h a t s A pp D M via: +1 2 4 0 7 4 3 7 6 8 9
Thanks.9 -
My email address appeared in a new data breach at gravatar. I thought that's exactly gravatar's purpose, to make my email address publicly known and provide an additional profile picture?
 1
1 -
!rant
This is fucking how you do it!
Ticketmaster UK had a "data security incident" where they don't really know if any data was actually leaked/stolen/"accessed by an unknown third-party" — their response:
1. Disable the compromised service across their platforms
2. Send a mail to any customer that may have been affected (I got one in Danish because I had only interacted with them through a Danish subsidiary)
2b. All notified customers have their passwords reset and must go through the "Forgot password" process; the _temporary_ password they sent me was even pretty nicely random looking: ";~e&+oVX1RQOA`BNe4"
3. Do forensics and security reviews to understand how the data was compromised
3b. Take contact to relevant authorities, credit card companies, and banks
4. Establish a dedicated website (https://security.ticketmaster.co.uk/...) to explain the incident and answer customer questions
5. "We are offering impacted customers a free 12 month identity monitoring service with a leading provider. To request this service please visit [this page]"
EDIT: As mentioned and sourced in the first comment, the breach was apparently noticed by a banking provider and reported to Ticketmaster on the 12th of April and later to Mastercard on the 19th of April.
Ticketmaster's internal investigation found no evidence of breach (which makes sense, as it wasn't an internal breach), but when Mastercard issued an alert to banks about it on the 21st of June, Ticketmaster followed up by finding the actual breach and disabling the breached third party service on the 23rd of June.
I still think they did the right thing in the right way...2 -
recently noticed that Github is warning some users that their password has been compromised in a data breach by "HaveIBeenPwned". what is this about?8
-
Prank idea: call a colleague's phone and if they don't have your number (you'll notice by the way they talk), they won't know it's you. Then try to convince them they've somehow created a data breach and you have access to their company's source code... 😈
Oh, and if they do have your number just say you accidentally called the wrong person. -
This is why you keep production data separate -- and out of the hands of developers: http://businessinsider.com/uber-emp...3
-
Recovering Investment Losses with GearHead Engineers Cyber Security Services
In today’s increasingly digital financial landscape, investors face growing threats from cybercriminals targeting everything from brokerage accounts to blockchain-based assets. For individuals and businesses alike, falling victim to a cyberattack or financial scam can be devastating. Fortunately, firms like GearHead Engineers, known for their advanced cybersecurity services, are stepping in to help investors recover losses and, more importantly, prevent future breaches.
The Rise of Cyber-Investment Threats
As digital platforms have become the norm for managing investments, they’ve also become a prime target for hackers. Common threats include:
* Phishing scams that trick users into revealing login credentials.
* Ransomware attacks on financial firms.
* Malware that siphons personal and financial data.
* DeFi and cryptocurrency hacks exploiting insecure smart contracts or user wallets.
The financial implications can be enormous, especially when assets are stolen, trading accounts are compromised, or confidential investment strategies are exposed.
GearHead Engineers: A Cybersecurity Partner for Investors
GearHead Engineers specializes in protecting financial data, systems, and transactions with comprehensive cybersecurity strategies tailored to modern digital investment environments. Their services include:
* Threat Detection & Response: 24/7 monitoring of systems to identify unusual activity before it becomes a serious threat.
* Incident Forensics: In the event of a breach, GearHead Engineers conduct thorough investigations to trace the source, identify vulnerabilities, and assist in recovery efforts.
* Asset Recovery Support: While not a financial firm, GearHead can coordinate with law enforcement and digital forensics specialists to trace stolen digital assets, especially in cryptocurrency-related incidents.
* Security Audits & Penetration Testing: Preemptive testing of platforms and networks to find and fix security holes before hackers do.
* Cyber Insurance Advisory: Guidance on cyber insurance coverage and how to maximize your protection and potential reimbursement in case of a loss.
Real-World Application: Turning Loss into Learning
Clients who’ve suffered financial loss due to cyber incidents often find that working with cybersecurity experts like GearHead Engineers is a turning point. Not only can the firm help assess whether any funds are recoverable (especially in crypto and digital asset cases), but it also strengthens the client's defense moving forward.
By implementing robust firewalls, multi-factor authentication, encryption, and behavioral analytics, GearHead Engineers empowers investors to take control of their digital financial security.
Conclusion: Proactive Security is Smart Investment Strategy
Recovering from a cyberattack is never easy, but it’s possible—especially with the right partners. GearHead Engineers brings a unique blend of technical expertise and practical support to help victims of cyber fraud bounce back and secure their future. For investors, engaging in strong cybersecurity isn’t just risk management—it’s a smart investment in itself.4 -
Approx. 24 hours ago I proceeded to use MEGA NZ to download a file It's something I've done before. I have an account with them.
This is part of the email I received from MEGA NZ following the dowload: "
zemenwambuis2015@gmail.com
YOUR MEGA ACCOUNT HAS BEEN LOCKED FOR YOUR SAFETY; WE SUSPECT THAT YOU ARE USING THE SAME PASSWORD FOR YOUR MEGA ACCOUNT AS FOR OTHER SERVICES, AND THAT AT LEAST ONE OF THESE OTHER SERVICES HAS SUFFERED A DATA BREACH.
While MEGA remains secure, many big players have suffered a data breach (e.g. yahoo.com, dropbox.com, linkedin.com, adobe.com, myspace.com, tumblr.com, last.fm, snapchat.com, ashleymadison.com - check haveibeenpwned.com/PwnedWebsites for details), exposing millions of users who have used the same password on multiple services to credential stuffers (https://en.wikipedia.org/wiki/...). Your password leaked and is now being used by bad actors to log into your accounts, including, but not limited to, your MEGA account.
To unlock your MEGA account, please follow the link below. You will be required to change your account password - please use a strong password that you have not used anywhere else. We also recommend you change the passwords you have used on other services to strong, unique passwords. Do not ever reuse a password.
Verify my email
Didn’t work? Copy the link below into your web browser:
https://mega.nz//...
To prevent this from happening in the future, use a strong and unique password. Please also make sure you do not lose your password, otherwise you will lose access to your data; MEGA strongly recommends the use of a password manager. For more info on best security practices see: https://mega.nz/security
Best regards,
— Team MEGA
Mega Limited 2020."
Who in their right mind is going to believe something like that that's worded so poorly.
Can anybody shed some light on this latest bit of MEGA's fuckery?
Thank you very much.4 -
HOW TO REOVER LOST OR STOLEN BITCOIN, ETH AND OTHER CRYPTO ASSETS; VISIT CYBER CONSTABLE INTELLIGENCE
On January 2, 2025, at precisely 3 AM, Bet365 was hit by a devastating cyber-attack. Our website was infiltrated by a sophisticated virus that granted cybercriminals access to sensitive customer data. In the span of a few hours, £2,500,000 was stolen from our customers’ accounts. The attack was swift and covert, and by the time we realized what had happened, a significant amount of funds had already been siphoned off. As soon as we discovered the breach, my team and I worked tirelessly to secure our platform and protect our customers. We immediately launched an internal investigation and found that the virus had allowed unauthorized withdrawals from a number of accounts. This was a critical situation, and we knew we needed immediate help to recover the stolen funds and prevent any further damage. That's when we turned to Cyber Constable Intelligence. Their reputation for successfully recovering stolen funds in cybercrime cases made them the ideal partner for this challenge. The team at Cyber Constable Intelligence responded immediately, quickly analyzing the virus and the methods used by the hackers. Within hours, they were able to trace the movement of the stolen funds and identify the cybercriminals responsible for the attack. Cyber Constable Intelligence acted swiftly, working around the clock to coordinate with financial institutions and law enforcement. They used their advanced investigative tools and global network to track and recover the £2,500,000 stolen from our customers. Thanks to their relentless efforts, within just three days, we had recovered the full amount. By January 5, 2025, only three days after the attack, we were able to reimburse all affected customers and restore the funds to their accounts. This quick recovery was crucial in reassuring our customers and restoring their trust in Bet365. Additionally, Cyber Constable Intelligence helped us bolster our security measures, ensuring that we are now better protected against future threats. This experience was a stark reminder of the constant risks in the digital world. However, thanks to Cyber Constable Intelligence, we were able to act quickly, recover the stolen funds, and ensure that our platform remains a safe and secure place for our customers. Moving forward, we are more committed than ever to maintaining the highest standards of security to protect both our business and our users.
Reach out to their Info below
WhatsApp: 1 252378-7611
Website info; www cyberconstableintelligence com
Email Info cyberconstable@coolsite net1 -
Hire a Trusted Company for Recovery of Lost Bitcoin — CryptoChain Global Track
The rapid growth of the cryptocurrency industry has created both opportunity and risk. While digital assets like Bitcoin offer financial freedom, privacy, and accessibility, they also attract cybercriminals who exploit unsuspecting users. From investment scams to phishing attacks, hacked wallets to fraudulent trading platforms, Bitcoin holders around the world are increasingly falling victim to schemes that result in serious financial loss. When this happens, finding a reliable, professional recovery service becomes a critical step forward.
CryptoChain Global Track is a trusted and recognized name in the field of cryptocurrency recovery. The company is known for helping individuals and businesses who have lost Bitcoin due to scams, unauthorized access, or transactional errors. Backed by a team of skilled blockchain analysts, ethical hackers, and forensic investigators, CryptoChain Global Track offers a lifeline to those who thought their assets were gone forever.
Unlike many services that overpromise and underdeliver, CryptoChain Global Track works with complete transparency and professionalism. Their recovery process begins with a detailed analysis of the client’s situation. This includes examining the blockchain data, wallet transactions, and any communication or documentation related to the scam or loss. Using advanced tools, the team can trace the movement of Bitcoin through multiple wallets and platforms, even if the funds have been moved through mixing services or converted into other cryptocurrencies.
The company's success is rooted in its deep understanding of blockchain networks and how digital criminals operate. Their technical capabilities allow them to identify patterns, pinpoint destination wallets, and in many cases, work directly with exchanges or law enforcement to flag suspicious accounts. Every case is approached with careful investigation, guided by facts and real-time data—not assumptions or generic solutions.
Trust is a key part of any recovery process, especially when dealing with sensitive financial matters. CryptoChain Global Track treats every case with discretion and ensures that clients remain informed throughout the investigation. From initial assessment to asset tracking and follow-up actions, communication is clear and consistent. Clients are not charged upfront for empty promises—they receive honest evaluations and tailored solutions based on the nature of their case.
Beyond technical expertise, CryptoChain Global Track is also committed to client support and education. Many Bitcoin losses occur because of a lack of awareness about threats in the crypto space. The company takes time to educate its clients about how the breach or scam occurred and provides practical advice to help them avoid similar situations in the future. This commitment to both recovery and prevention makes the service holistic and genuinely helpful.
A trusted solution is available—and it starts by connecting with a team that understands how to fight back against crypto fraud with skill and determination.6 -
HOW TO HIRE A GENUINE CRYPTO RECOVERY SERVICE CONTACT SPARTAN TECH GROUP RETRIEVAL
All the time, I had believed in networking, but I never knew that a local crypto meetup would save me from financial disaster. Discussion at the event ranged from trading strategies to security tips, but one name cropped up repeatedly that sounded impressive: SPARTAN TECH GROUP RETRIEVAL. Many spoke about how that service had rescued them from lost wallets, forgotten passwords, and even cyber-attacks. I filed that away mentally but never thought I'd find myself in that position. That changed just weeks later. One morning, I went into my Bitcoin wallet and saw suspicious activity. My heart sank as I realized that $180,000 in crypto was on the line. Someone had access, and if I didn't act fast, I'd lose everything. Panic set in, and I scrambled to figure out how it happened: had I clicked a phishing link, was my private key compromised? No matter the cause, I needed help. And fast. That's when I remembered the crypto meetup. I scrolled through my notes and found SPARTAN TECH GROUP RETRIEVAL's name. With no time to waste, I sent a reply-my anxious and desperate words spilling into one frenetic sentence. They responded very fast and professionally. They immediately initiated an investigation into my wallet's transaction history and security logs. They were able to trace the breach and lock it, trying not to be late in recovering the stolen money. Then they worked around the clock for several days, coordinating tracking on the blockchain, forensic data recovery, and reinforcements of security. I barely slept, but at each and every stage, they kept reassuring me. Then came that call I was praying for: They had recovered my funds. Speechless. Relieved. Grateful. But SPARTAN TECH GROUP RETRIEVAL didn't just stop with the recovery, teaching me means of security practices, helped fortify the defense around my wallet, and making sure this does not happen again. I consider it one of the best I have done so far-attending that crypto meet-up. I might never have heard of SPARTAN TECH GROUP RETRIEVAL if it had not been that night, or the outcome worse. Now I do my best to spread the word. For a reason is their reputation preceding them, and personally I can vouch for their expertise, efficiency, and reliability.
SPARTAN TECH GROUP RETRIEVAL CONTACT INFO:
Email: spartantech (@) cyber services . com OR support (@) spartantechgroupretrieval. org
Website : h t t p s : / / spartantechgroupretrieval. org
WhatsApp: +1 (971) 487 - 3538
Telegram: +1 (581) 286 - 8092 6
6 -
Building Fortresses, not Firewalls: Ethical Hacking Meets Software Development
In the digital age, security is no longer an afterthought; it's the bedrock upon which our online world rests. Yet, traditional security measures often resemble fortresses – imposing, but vulnerable to unseen cracks and tunnels. To truly safeguard our systems, we need to think like the enemy, like the nimble figures scaling those walls: ethical hackers.
Enter the exciting realm of DevSecOps, where ethical hacking practices are woven into the very fabric of the software development lifecycle (SDLC). This proactive approach is akin to building castles with security in mind, each brick meticulously laid to withstand even the most cunning siege.
Why Ethical Hacking in SDLC?
Imagine developing a critical piece of software, only to discover a gaping security hole after launch. The damage could be catastrophic, exposing sensitive data and eroding trust. Ethical hacking flips this script. By integrating penetration testing, vulnerability assessments, and threat modeling throughout the SDLC, we proactively hunt for weaknesses before they can be exploited.
Think of it as a friendly sparring match, where the ethical hacker throws their best punches to expose vulnerabilities, allowing the development team to fortify the software's defenses. This constant testing and refining leads to robust, secure systems that can withstand real-world attacks.
Benefits of DevSecOps:
1. Reduced Costs and Risks: Early detection and patching of vulnerabilities are far cheaper than dealing with a full-blown data breach.
2. Improved Software Quality: Security becomes an inherent part of the development process, leading to more reliable and trustworthy software.
3. Enhanced Brand Reputation: Demonstrating a proactive approach to security builds trust with customers and stakeholders.
Putting it into Practice:
Integrating ethical hacking into the SDLC requires a cultural shift. Developers, security professionals, and testers need to work together seamlessly, sharing knowledge and fostering a collaborative environment. Here are some key practices:
1. Threat Modeling: Identify potential threats and attack vectors early in the development process.
2. Static and Dynamic Code Analysis: Use automated tools to detect vulnerabilities in code.
3. Penetration Testing: Simulate real-world attacks to uncover hidden weaknesses.
4. Security Awareness Training: Educate developers and other stakeholders about security best practices.
Tools of the Trade:
A plethora of tools empowers ethical hackers and security professionals in their quest for a more secure digital world. Some popular options include:
1. Kali Linux: A distribution packed with security tools for penetration testing.
2. Burp Suite: A web application security testing platform.
3. Metasploit: A framework for developing and executing exploit code.
4. Wireshark: A network traffic analyzer for identifying suspicious activity.
The Future of Security:
As technology evolves, so too must our security practices. DevSecOps, with its embrace of ethical hacking, is at the forefront of this evolution. By building security into the very fabric of software development, we can create a safer, more resilient digital world for everyone.
Remember, in the ongoing battle against cyber threats, ethical hackers are not the enemy; they are our allies, the architects of digital fortresses that stand strong against the shadows. So, let's embrace DevSecOps, sharpen our ethical hacking skills, and build a future where security is not just an afterthought, but a fundamental principle.
I encourage you to explore the world of DevSecOps and ethical hacking. Whether you're a seasoned developer or just starting your journey, there's always more to learn and contribute. Together, we can build a more secure digital future, one line of code and one vulnerability patch at a time.
Do you have any questions about DevSecOps or ethical hacking? Share your thoughts and experiences in the comments below! -
RECLAIM YOUR LOST CRYPTOCURRENCY TODAY WITH TRUSTED EXPERTS - HIRE HACKATHON TECH SOLUTIONS
The sudden disappearance of your cryptocurrency holdings, whether due to a sophisticated cyberattack, a deceptive scam, or simply misplaced access credentials, can feel like a financial disaster. During these crucial times, HACKATHON TECH SOLUTIONS provides the ultimate solution for digital asset restoration, offering unmatched expertise in recovering Bitcoin, Ethereum, and a vast array of altcoins.What sets HACKATHON TECH SOLUTIONS unique from the rest is their elite team of blockchain forensic specialists, who combine cutting-edge technology with in-depth investigative methods. These experts utilize advanced cryptographic analysis to thoroughly trace transaction histories across decentralized ledgers, uncovering vulnerabilities and exploiting weaknesses in even the most complicated theft schemes. Their approach goes far beyond basic wallet recovery services, employing proprietary tools to navigate the often murky world of blockchain transactions.The recovery process begins with an in-depth consultation where clients provide essential information about the loss, including transaction records, wallet addresses, and details about the breach or incident. The forensic team then embarks on a multi-faceted investigation, combing through blockchain data across various networks and exchanges to uncover digital traces that might otherwise remain invisible.What truly sets HACKATHON TECH SOLUTIONS apart is their strategic and proactive approach to fund retrieval. They don’t simply trace stolen assets, they craft customized recovery plans, collaborating with cryptocurrency exchanges, legal authorities, and even international organizations. Their specialists know exactly when to intercept frozen funds, reconstruct private keys, or employ advanced social engineering tactics to retrieve assets from scammers.Their recovery process is highly detailed, utilizing a range of investigative techniques that leave no stone unturned. Whether dealing with a direct theft, hacking incident, or even accidental loss due to a misplaced private key, HACKATHON TECH SOLUTIONS team can step in and provide a targeted, expert solution. In a world where cryptocurrency is often seen as a difficult asset to recover once lost, HACKATHON TECH SOLUTIONS ability to navigate the complexities of digital asset recovery gives clients peace of mind that they can recover even the most elusive of funds. When the stakes are high, their specialized expertise to restoring digital assets make them the definitive choice for anyone facing the loss of cryptocurrency holdings. Their contact details are listed below.
Whatsapp:+31 6 47999256
Telegram: +1(659) 217-9239
Email: hackathontech service @ mail . com7 -
HIRE A CRYPTO RECOVERY EXPERT; BEST BITCOIN RECOVERY SERVICE VISIT CYBER CONSTABLE INTELLIGENCE
It was a devastating blow - one moment I was the proud owner of a small digital fortune, 8,000 Bitcoin that I had painstakingly accumulated over years of savvy investing and cautious storage. The next, that entire life-changing sum had vanished without a trace, lost to a cruel twist of fate and my own careless misstep. I had fallen victim to a data breach, leaving me helpless to prevent the thieves from making off with my entire cryptocurrency holdings. The anguish was palpable, a sinking feeling of hopelessness and despair as I realized the scale of my loss. Thousands upon thousands of hard-earned Bitcoins, now in the hands of faceless criminals, beyond my reach. But I refused to give in to despair. Determined to recover what was rightfully mine, I sought out the services of Cyber Constable Intelligence, a specialized team of blockchain forensics experts renowned for their ability to track down and reclaim stolen digital assets. Through their meticulous investigative work, leveraging the transparency of the Bitcoin ledger and their deep technical expertise, they were able to painstakingly trace the movement of my stolen funds, identifying the wallet addresses the thieves had used to launder the cryptocurrency. With this critical intelligence in hand, Cyber Constable Intelligence then coordinated with law enforcement to freeze those illicit accounts, preventing the funds from being moved any further. The final step was a delicate negotiation process, with the recovery team using their connections and influence to compel the thieves to return the stolen Bitcoins - a tense and high-stakes affair, but one that ultimately proved successful. After weeks of anxious waiting, I was overjoyed to have my 8,000 BTC safely returned to my control, a true testament to the skill and determination of the Cyber Constable Intelligence team. It was a harrowing ordeal, but one that reinforced the importance of robust security measures and the remarkable capabilities of specialized firms dedicated to combating cryptocurrency crime and restoring rightful ownership. Losing 8,000 BTC was one of the most stressful events of my life, but thanks to Cyber Constable Intelligence, I was able to reclaim what I thought was lost forever. Their professionalism, technical expertise, and commitment to security made all the difference. If you find yourself in a similar situation, I cannot recommend them highly enough. Cyber Constable Intelligence turned a financial disaster into a remarkable recovery, and I will forever be grateful for their role in securing my assets.
CYBER CONSTABLE INTELLIGENCE INFO:
Website: w w w. cyberconstableintelligence com3 -
As the head of Quantum Innovations, based in Seattle, Washington, I’ve always taken pride in our company’s commitment to cutting-edge technology and innovation. However, a recent security breach has underscored how vulnerable we were to a major cybersecurity threat involving our corporate mobile devices. The breach began when several employees unknowingly downloaded a malicious app from a third-party app store. What initially appeared to be a harmless app turned out to contain malware, granting cybercriminals access to sensitive company data. In total, the attackers stole approximately $200,000 USD worth of proprietary business information, including financial records, intellectual property, and confidential communications. Even more alarming, the breach led to the theft of employee banking details, enabling unauthorized transfers of funds from both personal and corporate accounts. The breach was discovered when our IT team noticed unusual activity on the affected devices, including unauthorized access to secure files and suspicious data transfers. After conducting a thorough investigation, we realized that the malware had been secretly transmitting our valuable data to an external server, including sensitive financial information. At that point, it became clear that the situation was far worse than we had initially anticipated.In response to this crisis, I reached out to TRUST GEEKS HACK EXPERT at Web, https :/ / t r u s t g e e k s h a c k e x p e r t . c o m/ E m a i l : i n f o @ t r u s t g e e k s h a c k e x p e r t.c o m And T e l e G r a m:: T r u s t g e e k s h a c k e x p e r t, A renowned cybersecurity firm with a reputation for its expertise in mobile device security and data recovery. Their team acted swiftly to assess the full scope of the attack, clean the infected devices, and secure our mobile systems.Thanks to their expert intervention, we were able to completely remove the malware from all affected devices, TRUST GEEKS HACK EXPERT data recovery specialists went above and beyond to recover not only the stolen company data but also the funds that had been illicitly transferred from both employee and corporate bank accounts. Through negotiation with authorities and tracking the stolen funds, they successfully managed to recover every dollar that had been taken. Their diligence and expertise were truly exceptional, and because of their efforts, we were able to avert what could have been a catastrophic financial loss.In the wake of this breach, we are more committed than ever to fortifying our security measures. The swift response and effective recovery efforts from TRUST GEEKS HACK EXPERT have been invaluable in restoring our confidence and securing our operations.1
-
RECOVERING OF LOST BITCOIN: RAPID DIGITAL RECOVERY, STEP BY STEP PROCESS
When a devastating data breach left me with a crippling loss of 82,000 ETH, I was utterly devastated. As a seasoned crypto investor, I had carefully amassed this substantial fortune over years of diligent research and strategic trading. But in the blink of an eye, it had all been snatched away, leaving me feeling helpless and on the brink of financial ruin. Fortunately, I was referred to the experts at Rapid Digital Recovery, a renowned cybersecurity firm specializing in the recovery of lost or stolen digital assets. From the moment I reached out, Web site Info: https: // ra pi ddigit alrecove ry .o rg...I was met with an unparalleled level of professionalism and expertise. The team quickly assessed the situation, drawing upon their extensive knowledge of blockchain technology and hacking techniques to devise a meticulous recovery plan. They worked tirelessly, leaving no stone unturned in their pursuit of my missing Ethereum. Their dogged determination and technical prowess were nothing short of awe-inspiring, as they navigated the complex web of digital wallets, exchange platforms, and illicit transactions. After weeks of painstaking investigation and strategic maneuvers, the Rapid Digital Recovery team triumphantly recovered the entirety of my 82,000 ETH, restoring my financial security and peace of mind. I am forever grateful for their unwavering commitment to their craft and their ability to transform a devastating loss into a remarkable victory, solidifying their reputation as the gold standard in the world of cryptocurrency recovery. Rapid Digital Recovery was a game-changer in the world of crypto recovery. If you find yourself in a similar situation where your cryptocurrency is locked away and seemingly irretrievable, I highly recommend their services. Their professionalism, combined with a genuine commitment to customer success, made all the difference in my experience. Thanks to them, I now have my 82,000 ETH back, and I couldn’t be more grateful. Send a message to: What sapp Info: +1 41 4 80 7 14 85 3
3 -
POSSIBLE WAYS TO RECOVER BACK YOUR SCAMMED CRYPTO FROM ANY INVESTMENT PLATFORM...
At TaxEase Solutions, based in New York, USA, we faced a critical crisis when our tax filing system was hacked overnight. The breach exposed sensitive personal data, including Social Security numbers, financial details, and addresses of our clients. The attackers used this stolen information to apply for fraudulent tax refunds, resulting in a significant loss of $1 million USD. The breach occurred during the night while our team was off-duty, leaving us unaware until the following morning when we discovered the extent of the damage. With such a large amount of money lost and the integrity of our business compromised, we knew we needed immediate assistance to recover and secure both our clients’ data and our reputation. That’s when we reached out to Digital Gold Hunter. Digital Gold Hunters team responded promptly and demonstrated their deep expertise in dealing with cybersecurity breaches. They quickly identified the source of the vulnerability and acted decisively to patch the system flaw. Their ability to rapidly assess the situation and implement corrective actions helped to prevent any further unauthorized access to our platform.Once the system was secured, Salvage Asset Recovery shifted their focus to assisting our affected clients. They worked diligently with financial institutions and law enforcement to help some clients who were able to reach out and report the fraudulent tax refund applications. Through their intervention, these clients were able to stop the fraudulent transactions and recover some of their funds. As of now, Digital Gold Hunter has managed to recover $980,000 of the lost $1 million, but they are still continuing to work with authorities and financial institutions to recover the remaining funds. Digital Gold Hunter helped us implement more robust security measures to prevent any future breaches. They introduced advanced encryption techniques and worked with us to update our cybersecurity protocols, ensuring that our clients' data would be better protected going forward. Their consultation also guided us in strengthening our internal data protection policies, which reassured our clients that we were committed to safeguarding their sensitive information.Thanks to the quick and efficient actions of Digital Gold Hunter, and protect the majority of our clients’ data. Their professionalism, expertise, and dedication to helping both our company and our clients made all the difference in mitigating the effects of the breach and stabilizing our business. The recovery process is still ongoing, but we remain confident that with Digital Gold Hunter ’s continued support, we will fully resolve the situation.
Their Contact info,
Email: Digitalgoldhunter@tech-center . c o m1 -
CHANCES OF CRYPTO RECOVERY OPTIONS:USE SPARTAN TECH GROUP RETRIEVAL
WhatsApp:+1 (971) 4 8 7 - 3 5 3 8
Email: spartantech (@) cyberservices . com
Telegram:+1 (581) 2 8 6 - 8 0 9 2
For many individuals and businesses, the experience of financial loss, whether caused by cyberattacks, data breaches, or unforeseen events, can feel overwhelming and intimidating. The emotional and financial toll can be immense, leaving people uncertain of where to turn. In these challenging times, SPARTAN TECH GROUP RETRIEVAL offers a crucial lifeline, providing expert services that guide clients through the recovery process with both skill and compassion. At SPARTAN TECH GROUP RETRIEVAL, the team recognizes the profound impact financial loss can have on clients, not only in terms of their finances but also on their sense of security and well-being. Their highly trained professionals specialize in assessing the full extent of damage caused by various disruptions, carefully identifying the underlying issues and working to develop tailored recovery strategies. Whether the challenge involves restoring lost data, recovering compromised systems, or securing vulnerable networks, SPARTAN TECH GROUP RETRIEVAL utilizes the latest technology and industry best practices to restore both operational efficiency and peace of mind. Data loss can be a particularly devastating consequence of a cyberattack or system failure. In a world where information is the lifeblood of businesses, recovering lost or corrupted data is crucial to regaining normal operations. SPARTAN TECH GROUP RETRIEVAL’s experts employ advanced data recovery techniques to retrieve vital information, ensuring that clients do not suffer irreversible setbacks. By recovering valuable data, they allow businesses to continue their operations with minimal disruption. Beyond data recovery, SPARTAN TECH GROUP RETRIEVAL excels at restoring and securing compromised systems. After a breach or attack, the threat of future vulnerabilities looms large. The team’s cybersecurity experts take swift action to secure networks and systems, implementing robust protection measures to defend against future threats. Through a combination of proactive monitoring, vulnerability assessments, and real-time security solutions, SPARTAN TECH GROUP RETRIEVAL works tirelessly to ensure that businesses and individuals can rebuild trust and safeguard their digital assets for the long term. However, what truly distinguishes SPARTAN TECH GROUP RETRIEVAL is its unwavering commitment to client care. While the technical aspects of recovery are vital, the company understands the emotional strain that often accompanies financial loss. Their compassionate case managers offer much-needed emotional support and practical guidance, helping clients navigate both the logistical and psychological challenges they face. By addressing the emotional as well as the practical aspects of recovery, SPARTAN TECH GROUP RETRIEVAL ensures that clients feel understood and supported throughout the entire process. In the face of financial hardship, SPARTAN TECH GROUP RETRIEVAL is a trusted partner that combines technical expertise with empathy and dedication. Their holistic approach ensures that businesses and individuals can recover, rebuild, and emerge from financial challenges stronger, more secure, and better prepared for the future. 1
1 -
The topic of recovery services and the efficacy of Wizard Hilton Cyber Tech warrants a closer examination. Recovery services are a critical component of any comprehensive cybersecurity strategy, as they provide the means to restore systems, data, and operations in the event of a breach or other disruptive incident. Wizard Hilton Cyber Tech is a leading provider in this space, offering a suite of advanced recovery solutions designed to ensure business continuity and mitigate the potentially devastating impacts of cyber attacks. At the core of their offerings is a robust, AI-driven platform that continuously monitors systems, detects anomalies, and triggers rapid, automated recovery procedures. This allows organizations to bounce back quickly, often with minimal downtime or data loss. Wizard Hilton's approach also emphasizes the importance of comprehensive testing and simulation, putting recovery protocols through their paces to validate effectiveness and uncover potential weaknesses. Additionally, their team of seasoned cybersecurity experts provides hands-on guidance, tailoring solutions to the unique needs of each client. By combining cutting-edge technology with deep industry expertise, Wizard Hilton Cyber Tech has established itself as a trusted partner in the realm of recovery services, empowering organizations to safeguard their most valuable digital assets and ensure business resilience in the face of ever-evolving cyber threats. Contact: for assistance,
Email : wizardhiltoncybertech ( @ ) gmail (. ) com
OR
support ( @ ) wizardhiltoncybertech (.) com
WhatsApp number +130244578951 -
RECOVER BACK YOUR HARD EARN MONEY SCAMMED BY ONLINE IMPERSONATORS OR HACKERS FROM ANY PLATFORM.
At TaxEase Solutions, based in New York, USA, we faced a critical crisis when our tax filing system was hacked overnight. The breach exposed sensitive personal data, including Social Security numbers, financial details, and addresses of our clients. The attackers used this stolen information to apply for fraudulent tax refunds, resulting in a significant loss of $1 million USD. The breach occurred during the night while our team was off-duty, leaving us unaware until the following morning when we discovered the extent of the damage. With such a large amount of money lost and the integrity of our business compromised, we knew we needed immediate assistance to recover and secure both our clients’ data and our reputation. That’s when we reached out to Digital Gold Hunter. Digital Gold Hunters team responded promptly and demonstrated their deep expertise in dealing with cybersecurity breaches. They quickly identified the source of the vulnerability and acted decisively to patch the system flaw. Their ability to rapidly assess the situation and implement corrective actions helped to prevent any further unauthorized access to our platform.Once the system was secured, Salvage Asset Recovery shifted their focus to assisting our affected clients. They worked diligently with financial institutions and law enforcement to help some clients who were able to reach out and report the fraudulent tax refund applications. Through their intervention, these clients were able to stop the fraudulent transactions and recover some of their funds. As of now, Digital Gold Hunter has managed to recover $980,000 of the lost $1 million, but they are still continuing to work with authorities and financial institutions to recover the remaining funds. Digital Gold Hunter helped us implement more robust security measures to prevent any future breaches. They introduced advanced encryption techniques and worked with us to update our cybersecurity protocols, ensuring that our clients' data would be better protected going forward. Their consultation also guided us in strengthening our internal data protection policies, which reassured our clients that we were committed to safeguarding their sensitive information.Thanks to the quick and efficient actions of Digital Gold Hunter, and protect the majority of our clients’ data. Their professionalism, expertise, and dedication to helping both our company and our clients made all the difference in mitigating the effects of the breach and stabilizing our business. The recovery process is still ongoing, but we remain confident that with Digital Gold Hunter ’s continued support, we will fully resolve the situation.
Their Contact info,
Email: D i g i t a l g o l d h u n t e r @ t e c h -c e n t e r . c o m1 -
TRUSTWORTHY CRYPTO RECOVERY SERVICE- HIRE SALVAGE ASSET RECOVERY
At Tax Ease Solutions, based in New York, USA, we faced a critical crisis when our tax filing system was hacked overnight. The breach exposed sensitive personal data, including Social Security numbers, financial details, and addresses of our clients. The attackers used this stolen information to apply for fraudulent tax refunds, resulting in a significant loss of $1 million USD. The breach occurred during the night while our team was off-duty, leaving us unaware until the following morning when we discovered the extent of the damage. With such a large amount of money lost and the integrity of our business compromised, we knew we needed immediate assistance to recover and secure both our clients’ data and our reputation. That’s when we reached out to Salvage Asset Recovery. Salvage Asset Recovery’s team responded promptly and demonstrated their deep expertise in dealing with cybersecurity breaches. They quickly identified the source of the vulnerability and acted decisively to patch the system flaw. Their ability to rapidly assess the situation and implement corrective actions helped to prevent any further unauthorized access to our platform. Once the system was secured, Salvage Asset Recovery shifted their focus to assisting our affected clients. They worked diligently with financial institutions and law enforcement to help some clients who were able to reach out and report the fraudulent tax refund applications. Through their intervention, these clients were able to stop the fraudulent transactions and recover some of their funds. As of now, Salvage Asset Recovery has managed to recover $980,000 of the lost $1 million, but they are still continuing to work with authorities and financial institutions to recover the remaining funds. Salvage Asset Recovery helped us implement more robust security measures to prevent any future breaches. They introduced advanced encryption techniques and worked with us to update our cybersecurity protocols, ensuring that our clients' data would be better protected going forward. Their consultation also guided us in strengthening our internal data protection policies, which reassured our clients that we were committed to safeguarding their sensitive information. Thanks to the quick and efficient actions of Salvage Asset Recovery, Tax Ease Solutions was able to recover $980,000 of the lost funds and protect the majority of our clients’ data. Their professionalism, expertise, and dedication to helping both our company and our clients made all the difference in mitigating the effects of the breach and stabilizing our business. The recovery process is still ongoing, but we remain confident that with Salvage Asset ’s continued support, we will fully resolve the situation.
Their Contact info,
WhatsApp+ 1 8 4 7 6 5 4 7 0 9 6 1
1 -
POSSIBLE WAYS TO GET BACK EVERY PENNY LOSE TO SCAMMERS
At Digital Gold Hunters Solutions, based in New York, USA, we faced a critical crisis when our tax filing system was hacked overnight. The breach exposed sensitive personal data, including Social Security numbers, financial details, and addresses of our clients. The attackers used this stolen information to apply for fraudulent tax refunds, resulting in a significant loss of $1 million USD. The breach occurred during the night while our team was off-duty, leaving us unaware until the following morning when we discovered the extent of the damage. With such a large amount of money lost and the integrity of our business compromised, we knew we needed immediate assistance to recover and secure both our clients’ data and our reputation. That’s when we reached out to Digital Gold Hunter. Digital Gold Hunters team responded promptly and demonstrated their deep expertise in dealing with cybersecurity breaches. They quickly identified the source of the vulnerability and acted decisively to patch the system flaw. Their ability to rapidly assess the situation and implement corrective actions helped to prevent any further unauthorized access to our platform.Once the system was secured, Salvage Asset Recovery shifted their focus to assisting our affected clients. They worked diligently with financial institutions and law enforcement to help some clients who were able to reach out and report the fraudulent tax refund applications. Through their intervention, these clients were able to stop the fraudulent transactions and recover some of their funds. As of now, Digital Gold Hunter has managed to recover $980,000 of the lost $1 million, but they are still continuing to work with authorities and financial institutions to recover the remaining funds. Digital Gold Hunter helped us implement more robust security measures to prevent any future breaches. They introduced advanced encryption techniques and worked with us to update our cybersecurity protocols, ensuring that our clients' data would be better protected going forward. Their consultation also guided us in strengthening our internal data protection policies, which reassured our clients that we were committed to safeguarding their sensitive information.Thanks to the quick and efficient actions of Digital Gold Hunter, and protect the majority of our clients’ data. Their professionalism, expertise, and dedication to helping both our company and our clients made all the difference in mitigating the effects of the breach and stabilizing our business. The recovery process is still ongoing, but we remain confident that with Digital Gold Hunter ’s continued support, we will fully resolve the situation.
Their Contact info,
Email: Digitalgoldhunter@tech-center. com
whats App: +1 908 991 71321 -
At TaxEase Solutions, based in New York, USA, we faced a critical crisis when our tax filing system was hacked overnight. The breach exposed sensitive personal data, including Social Security numbers, financial details, and addresses of our clients. The attackers used this stolen information to apply for fraudulent tax refunds, resulting in a significant loss of $1 million USD. The breach occurred during the night while our team was off-duty, leaving us unaware until the following morning when we discovered the extent of the damage. With such a large amount of money lost and the integrity of our business compromised, we knew we needed immediate assistance to recover and secure both our clients’ data and our reputation. That’s when we reached out to Digital Gold Hunter. Digital Gold Hunters team responded promptly and demonstrated their deep expertise in dealing with cybersecurity breaches. They quickly identified the source of the vulnerability and acted decisively to patch the system flaw. Their ability to rapidly assess the situation and implement corrective actions helped to prevent any further unauthorized access to our platform.Once the system was secured, Salvage Asset Recovery shifted their focus to assisting our affected clients. They worked diligently with financial institutions and law enforcement to help some clients who were able to reach out and report the fraudulent tax refund applications. Through their intervention, these clients were able to stop the fraudulent transactions and recover some of their funds. As of now, Digital Gold Hunter has managed to recover $980,000 of the lost $1 million, but they are still continuing to work with authorities and financial institutions to recover the remaining funds. Digital Gold Hunter helped us implement more robust security measures to prevent any future breaches. They introduced advanced encryption techniques and worked with us to update our cybersecurity protocols, ensuring that our clients' data would be better protected going forward. Their consultation also guided us in strengthening our internal data protection policies, which reassured our clients that we were committed to safeguarding their sensitive information.Thanks to the quick and efficient actions of Digital Gold Hunter, and protect the majority of our clients’ data. Their professionalism, expertise, and dedication to helping both our company and our clients made all the difference in mitigating the effects of the breach and stabilizing our business. The recovery process is still ongoing, but we remain confident that with Digital Gold Hunter ’s continued support, we will fully resolve the situation.
Their Contact info,
Email: Digitalgoldhunter@tech-center. c o m
whats App: +1 908 991 71321


