Join devRant
Do all the things like
++ or -- rants, post your own rants, comment on others' rants and build your customized dev avatar
Sign Up
Pipeless API

From the creators of devRant, Pipeless lets you power real-time personalized recommendations and activity feeds using a simple API
Learn More
Search - "cyber"
-
Currently at a cyber security event.
The most ironic thing is that the WiFi here is not secured...20 -
I'm a programmer and an aspiring cyber security specialist. Yesterday, after I gave a presentation about smart bulb hacking, I heard through a coworker that a cyber security company is interested in talking to me. Yay!11
-
Cybersecurity:
>nothing happens
>I can't believe we pay your useless ass to sit around doing nothing all day!
>something happens
>this is your fault1 -
(The PM is pretty technical)
One day:
Me: Could you create this subdomain?
PM: Sure, just a sec.
Me: Ohh and could you add a letsencrypt cert? (one click thingy)
PM: Why would you need that on this kinda site...
Me: Well in general for security...
PM: Nahh.
*walks away*
Next day:
(referring to my internship manager/guider as Bob)
Bob: Hey... we have a new subdomain!
Me: Yup!
Bob: Wait why is there no letsencrypt certificate installed...?!?
Me: Well, the PM didn't find that neccesary...
Bob: (Oo) of course it is... are we going for security by default or what?
Me: Yup agreed.
Bob: *creates cert and sets everything up in under a minute*
It wasn't a high profile site (tiny side project) but why not add SSL when you can for free?8 -
A: There is not even a single forum for cyber security. Let's build one.
Me: Are you sure that there is not even a single forum?
A: Yes, I'm a cyber security expert. I have 5 years of experience in this field.
Me: **walks out quitely**1 -
Fucking China!
The only time they ever come out of their pathetic walled internet is to attack your servers.
Fuck that country.10 -
Paranoid Developers - It's a long one
Backstory: I was a freelance web developer when I managed to land a place on a cyber security program with who I consider to be the world leaders in the field (details deliberately withheld; who's paranoid now?). Other than the basic security practices of web dev, my experience with Cyber was limited to the OU introduction course, so I was wholly unprepared for the level of, occasionally hysterical, paranoia that my fellow cohort seemed to perpetually live in. The following is a collection of stories from several of these people, because if I only wrote about one they would accuse me of providing too much data allowing an attacker to aggregate and steal their identity. They do use devrant so if you're reading this, know that I love you and that something is wrong with you.
That time when...
He wrote a social media network with end-to-end encryption before it was cool.
He wrote custom 64kb encryption for his academic HDD.
He removed the 3 HDD from his desktop and stored them in a safe, whenever he left the house.
He set up a pfsense virtualbox with a firewall policy to block the port the student monitoring software used (effectively rendering it useless and definitely in breach of the IT policy).
He used only hashes of passwords as passwords (which isn't actually good).
He kept a drill on the desk ready to destroy his HDD at a moments notice.
He started developing a device to drill through his HDD when he pushed a button. May or may not have finished it.
He set up a new email account for each individual online service.
He hosted a website from his own home server so he didn't have to host the files elsewhere (which is just awful for home network security).
He unplugged the home router and began scanning his devices and manually searching through the process list when his music stopped playing on the laptop several times (turns out he had a wobbly spacebar and the shaking washing machine provided enough jittering for a button press).
He brought his own privacy screen to work (remember, this is a security place, with like background checks and all sorts).
He gave his C programming coursework (a simple messaging program) 2048 bit encryption, which was not required.
He wrote a custom encryption for his other C programming coursework as well as writing out the enigma encryption because there was no library, again not required.
He bought a burner phone to visit the capital city.
He bought a burner phone whenever he left his hometown come to think of it.
He bought a smartphone online, wiped it and installed new firmware (it was Chinese; I'm not saying anything about the Chinese, you're the one thinking it).
He bought a smartphone and installed Kali Linux NetHunter so he could test WiFi networks he connected to before using them on his personal device.
(You might be noticing it's all he's. Maybe it is, maybe it isn't).
He ate a sim card.
He brought a balaclava to pentesting training (it was pretty meme).
He printed out his source code as a manual read-only method.
He made a rule on his academic email to block incoming mail from the academic body (to be fair this is a good spam policy).
He withdraws money from a different cashpoint everytime to avoid patterns in his behaviour (the irony).
He reported someone for hacking the centre's network when they built their own website for practice using XAMMP.
I'm going to stop there. I could tell you so many more stories about these guys, some about them being paranoid and some about the stupid antics Cyber Security and Information Assurance students get up to. Well done for making it this far. Hope you enjoyed it. 26
26 -
Got called up today by my org's cyber security team.
Reason: Installed a font called "Hack" (https://github.com/source-foundry/...)
🤦♂️🤦♂️🤦♂️🤦♂️🤦♂️1 -
former boss wrote three cyber-defense books. had his "collections" team sending plaintext passwords to high-side clients over unsecured email4
-
I think I ranted about this before but fuck it.
The love/hate relation I have with security in programming is funny. I am working as a cyber security engineer currently but I do loads of programming as well. Security is the most important factor for me while programming and I'd rather ship an application with less features than with more possibly vulnerable features.
But, sometimes I find it rather annoying when I want to write a new application (a web application where 90 percent of the application is the REST API), writing security checks takes up most of the time.
I'm working on a new (quick/fun) application right now and I've been at this for.... 3 hours I think and the first very simple functionality has finally been built, which took like 10 minutes. The rest of the 3 hours has been securing the application! And yes, I'm using a framework (my own) which has already loads of security features built-in but I need more and more specific security with this API.
Well, let's continue with securing this fucker!10 -
I'm soon graduating from a tech/IT school which recently specialized in cybersecurity.
Today when I changed my password on their website, it displayed the old one in clear text.
God damn it people, THIS is the reason why our school's reputation has been slowly but steadily going down. 1
1 -
Bitcoin Scam From (2022) Recovered By iBolt Cyber Hacker
In 2022, I fell victim to a Bitcoin scam that left me feeling hopeless and frustrated. After investing all my money and credit, I found myself unable to withdraw my funds, and my attempts to get help were ignored, rather they kept asking for more.
three days ago i saw a review of iBolt Cyber Hacker recovered four years bitcoin, i decided to ask questions and try, i can say they are really professionals, i happily write this review because iBolt successfully recovered 93% of my funds. I’m incredibly grateful, If you find yourself in a similar situation, I highly recommend iBolt Cyber Hacker.
www . iboltcyberhack. co m/ 36
36 -
You Can't Withdraw Your Cryptocurrency Fund? Contact iBolt Cyber Hacker
Be careful of platforms that promise enormous rewards in order to entice individuals into fraudulent programs. There is no shame in speaking up, I was victim of crypto scam 4 weeks ago, While researching how to recover my assets, I came across multiple suggestions of iBolt Cyber Hacker and how they had restored so much joy to scammed victims. With their assistance i was able to retrieve all of my frozen crypto. I'm writing to convey my heartfelt gratitude to iBolt Cyber Hacker. Please contact them if you require their services or want to learn more about them.
More Info:
Email: Support @ iboltcyberhack . com
Contact/Whatsapp: +39 350 929 0318
Website: https : // iboltcyberhack . com /25 -
Umm yes, this cyber you're talking about sounds interesting, where do i get a cyber? How much does a cyber cost? Can a cyber feed my family?
-.- 4
4 -
Cyber security. Deep knowledge of cyber security and networks is what I wish I had. The math stuff that no one bothers with, specifically.6
-
Got my first serious project about a year ago. Made it clear to the client that we are developing a Windows app. After around 80-100 hours of work client just goes "how about we make this a web app?" Got a "financial support" instead of the agreed payment. Got around 4 times less money than agreed upon. They never ended up using some parts of the software (I ran the server so I knew that they weren't using it)
I once had a nightmare explaining to the client that he cannot use a 30+ MB image as his home page background. Average internet speed in my country is around 1-2 MB/s. I even had to do the calculation for him because he couldn't figure out the time it took for the visitor to load the image.3 -
What a relief!
I got my final certificate for finishing 9th grade, and the council has determined that (drums please)
IM GOING TO CYBER / COMPUTER SCIENCE NEXT YEAR!!!!!!!!!!4 -
Movie about Stuxnet Cyber weapon is out
The advanced malware used by CIA and MOSSAD to sabotage Iran's nuclear program
"Zero days" by Alex Gibney
Gk watch it guys..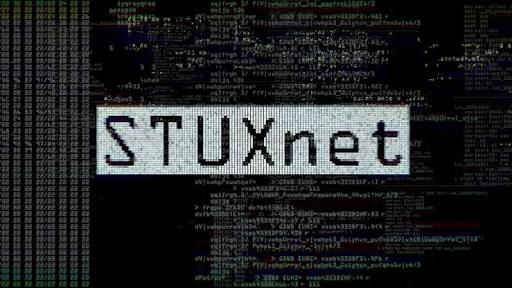 7
7 -
What are you all planning on getting on Black Friday/Cyber Monday? I've pinched pennies all year and saved up just enough to only be able to afford 35% or so of the cost of being beaten in a local dark alley. That's not even what I wanted, but still.16
-
Ah, that feeling when you open random cyber space options in Firefox so you can watch children being forced, classical frontend development with devtools. Happens almost every Tuesday
 2
2 -
Just heard this on the news...
"The cyber security on my smart phone compared to the cyber security in medical equipment..."
Wtf did I just hear??? I mean, I get it...using terms the general public understands... But how about educating people instead. 😤1 -
I find it hilarious the total misconception of hacking that the general public has. I tell people I know cyber security (Not as much as a lot of people around here) but it is a hobby of mine and I find it very useful/interesting.
But I can't stop but laugh when someone is like, can you get all the text messages my bf receives?
Can you hack this for me can you back that?
C'mon even if I knew how to do that without being caught you think I would even admit that to you. Do hackers just walk around with an index card pasted to their forehead of their skill? It's not even slightly reasonable to think this lol even for someone who doesn't know about the field -
Some things should be prohibited! Such as trying to look smart luring geeks with PHP code. That does not do what you wanted to do in the first place. Idiots!
 4
4 -
Massive cyber attack hits Europe. Hopefully everyone is patched and secure. Critical infrastructure, banks... impacted.1
-
What's a good book to read about hacking and/or cyber security? Doesn't have to necessarily a how-to guide, rather, just something to read on the subject.5
-
Never been a fan of podcasts before, but I'm fixing to take a stab at listening to some.
What's a good tech/programming podcast? (Bonus points if it's about Cyber security) -
!rant
I'm a computer engineering student.
I'm very much interested in Systems and networking.
That's why I was thinking of persuing cyber-security as a career option.
But I'm not quite sure if that is a good choice.
Also I don't know how to proceed in order to achieve excellence in cyber-security.
It would be a great help if you guys could help me.
Thanks :)20 -
Y'know what's the worst part about all the internet censorship and cyber surveillance? The fact that no one notices it
 10
10 -
Honestly, school is useless for me as of right now. I know I should be well rounded and stuff, but do I honestly need to know the symptoms of cervix cancer while going into a tech career? My eyes have been set on tech for my whole life, ever since I left the womb, and I know that if I do switch careers, it'll be from comp sci to cyber security not from IT to med school...
I feel like I could really be devoting my time towards something better than writing a 5 page essay on a healthy food choice.
Every night I think to myself, "You know what, I'm going to lock myself in a room and write bash scripts all day" but then I wake up in the morning, and remember I have to take a quiz on reproductive systems, learn about the procedure of organ donations for driver's ed, write 2 paragraph definitions of vocab words, and read a book about communism.
The most useful thing I learned last year, was how to efficiently navigate the java API, and that's something you don't even learn, you just encounter it. Schools need to start having more specific specialties and stop enforcing knowledge of pointless topics.
I'm not saying to remove all core classes and stuff, I'm saying why waste space in our brains with something we won't use ever again? I get it, some people don't know what career they're looking for yet so you can't make them choose, but it honestly sucks some serious ass that I can't learn what I want to at school, and as a matter of fact, I can't even learn at home, because they're filling my schedule with pointless work because they feel that they have to fill our time somehow.
Point of this long ass rant is: Why lock yourself in a room and learn about something if it isn't something you want to learn about? The space in our brain is finite enough, why can't it be filled with things we're interested in rather than things that will only be used to get good grades in the future then overwritten with useful knowledge. Same thing with time. We have a very finite amount of time in a day, and now that I think of it, a lifetime. Why spend it on something that doesn't, and never will, make your life enjoyable?3 -
Just got a request to print the new Tesla truck.
I think it wasn't that hard for the Designer to implement the low pol. Design for the 3d print :')4 -
Ordered a slightly watered down version of my planned PC. Let's wait for Cyber Monday for buyer's remorse!
Either way, paid half price of the planned rig for 80% of the same performance.
See attached specs. Already have a hard drive and PSU, and for now will be reusing my GTS 250. 8
8 -
I chose Network/Cyber Security because it was my internship experience and they were willing to pay me good money to stay on... No but seriously I am much better at understanding how complex systems work than coding them. This job, as stressful as it is, is a different kind of stressful that the deadline-fraught jobs of software developers worldwide.
And i can do it fully remote.2 -
So this is what a cyber criminal looks like.
"Norwegians are a favourite for cyber criminals"
"And we are easier to fool than Swedes and Danes, if we're to believe the thieves. The only ones more exposed than us are oil rich Saudis" 🤷♂️ 1
1 -
Well my country broke the record of being the cyber bully...
I don't know what to feel.... This is bad.. 9
9 -
Has anyone used python within cyber security?
I really want to get into cyber security. I'm curious what programming languages are used within that industry.4 -
How did you learn cyber security, especially pentesting ?
I know that making VM lab and/or doing CTFs and reading writeups can help a lot, but is there any more "formal" way to get into things like pentesting etc. ?
(Without having to pay for OSCP, Sans and all this)5 -
1. I recorded something with my dad until 12 AM isarel daylight time
2. that you so much for congratulating me for the Cyber classes. I love all of you.
3. Thank you also for 400 upvotes. Going strong.
Have an Image of the recording machines in the studio. 4
4 -
Hey everyone. I am a freshman in college studying Cyber Security. I have been practicing various programming languages such as httml, css, java script and SQL. Does anyone have any recommendations for resources to study? My end goal is to be blue teaming for my schools Cyber Defense team in the fall.5
-
Do not buy Hostinger... They are so aggressive with caching that I ran out of devices to test the features. They probably cache based on userAgent because changing other parameters (IP, local cache) doesn't resolve the issue. I talked to tech support whole day, and although they were helpful few times I just got three same answers for the three different questions. Seriously, the only thing I like about Hostinger is their user friendly UI.
The rant goes on. I can basically DoS my website by clicking fast on it. That shit doesn't happen with some free hosting plans... My site goes down for a few minutes before I can visit it again.
THE RANT GOES ON
Using the file manager is tedious work as you get randomly disconnected after less than few minutes of inactivity.
I might seriously switch to Google's Cloud Console. It is more expensive, you have to do all the hosting config yourself using a virtual machine, but I guess it's more reliable and it gives you a lot more control.5 -
this is unsettling :( if they hit the button and start knocking out american infrastructure, even with "harmless" small-scale attacks or limited to certain sectors, i wonder how fast this is going to escalate... this mere unspoken threat is an aggressive move already https://theguardian.com/us-news/...7
-
Hey,
Any tips on how to apply for job, I apply to 10-15 new opportunities daily but haven't received positive response from 99% of them. I don't know what's wrong.
Currently, I am a cyber security analyst at a startup since February 2023.
My resume I use to apply for job
https://ganofins.com/ganesh-bagaria...21 -
So first time here seems awesome I'm an aspiring cyber security expert I know very basic c++ and I'm looking for people to talk to about what I should be doing5
-
Typical insurance company BS approach.
Listening to xmas music, Spotify ad kicks in about 'just being "hacked"':
Buy our cyber security insurance product to quickly recover and retain liquidity in case of a cyber security beach.
Not a single word about preventing the incidents in the first place...
Lucky to work in a place that doesn't skimp on IT.3 -
I have zero experience working in a company. I did a few freelancing projects. My friend forwarded my resume to a company. They contacted me after some time, and gave me a technical challenge. I have solved it, sent it back to them, now I am waiting for their answer.
What's the thing? After going to the company website, I realized they require at least 3 years of experience. But they still contacted me knowing that I am still a student and have only done freelancing work.
No matter do they accept my solution or not, this is a lesson for me and for everyone else: do not let required years of experience discourage you from applying to a position. You can still get a chance.
Happy job hunting to all you junior devs :)3 -
🚀 *iBOLT CYBER HACKER: Cryptocurrency Recovery & Advanced Hacking Solutions!* 🦊💻
🔐 *Lost access to your crypto wallet or had your funds stolen?* Don’t worry— iBOLT CYBER HACKER is here to help you recover your cryptocurrency with cutting-edge technical expertise.
💡 With years of experience in the crypto world, iBOLT CYBER HACKER employs the latest tools and ethical hacking techniques to help you recover lost assets, unlock hacked accounts, and retrieve funds from inaccessible exchanges.
⚡ Whether it’s a forgotten password, an accidental transfer, investment scam, or a major security breach, iBOLT CYBER HACKER has the expertise to help you get your crypto back.
- General phone hacking and monitoring
- Money recovery from scammers
- Bitcoin and PayPal recovery
- Mobile phone monitoring
- Hacking and modifying university grades
- Bank website hacking and fund transfers
- Database hacking with admin privileges
👉 *Contact iBOLT CYBER HACKER for professional assistance
📧 𝐄𝐦𝐚𝐢𝐥: Support @ibolt cybarhack. com
𝐨𝐫
📲 𝐖𝐡𝐚𝐭𝐬𝐀𝐩𝐩: +39, 351..105, 3619
http s:// ibolt cybarhack. com1 -
Any of us had annoyances with people with “a million dollar app idea” but what about these which gives unsolicited career advice?
I’m dealing with a boomer which keeps trying me to change my career and work into cyber security (because TV told him it’s a well paid field) despite me kindly telling him for multiple times which it’s not going to happen because I won’t throw away a career I love to work in a field which seems deadly boring to me (I love anything about coding from design to typing for hours on Vim meanwhile the only thought of reading for hours obscure documentation to find potential vulnerabilities on a system kills my spirit).7 -
Last night the Russians stroke again. It's become obvious that these Ddos attacks are not performed by just some casual hackers, but are part of cyber warfare - just as I suspected in one of my rants a couple of weeks ago6
-
Going to a business summit tomorrow and I get to see a live hack and learn about cyber attacks.
Shit better be good. 2
2 -
I recently joined DevRants, and with me joining any new site or media where you can share I am usually the guy who is shy and likes to sit back and watch/read. However I wanted to post a question as I am trying to get a job within the Cyber Security field. I have a computer science degree and honestly I feel like I can't even code at a level I should be able to. I am also currently working/studying for my CompTIA Security+. It has been going good but, I always second guess myself and doubt my abilities. I guess this a a slight rant and question so far.
My question is how can I better improve both my skills (coding, linux, and security) and also my mental. I would say its imposter syndrome but I don't have a job so I don't think it would be fair to say it is. I just want to break into the job field and show people that if given the help and resources I can excel at the task given. I do learn fast and pick things up pretty good. Any help/recommendations is much appreciated, and I look forward to more talks.2 -
/*
No Rant
*/
anyone here with a cyber security cert? i kinda want to go that route of cyber securty. so im curious if its worth it.12 -
When a person asks what do I do I tell them that I'm a cyber wizard.
It explains it well doesn't it ?
God damn muggles... -
Looking at colleges on summer break between learning python and some projects can't decide between computer science and cyber security as a major 😰 why can't I choose2
-
Cyber threats are the top concern of C levels. In actuality companies unintentionally expose way too much data. It's ridiculous what some make public.
-
Discord server under development for software engineering, cyber security, networking, and IT talk in general. Looking to meet new people and talk :). @ me if you're interested in testing it.4
-
829 GB of cources on cyber sec & programming if u wanna learn new skills
https://mega.nz/folder/1rBHzIyD/...15 -
How does someone with. A+ certs and a Network + and Cyber Security certifications and still only getting Help Desk jobs calling them 🤷♂️2
-
I was plunged into despair after losing $24,000 worth of Bitcoin on Valentine's Day. What was meant to be a day of love and celebration quickly turned into a nightmare. I had been drawn in by the allure of a lucrative investment scheme, only to realize too late that it was a well-crafted scam. As the reality sank in, I felt anger and regret, wondering how I had been so naive. In the days that followed, I scoured the internet for recovery options. However, my hope dwindled as I encountered numerous recovery services that seemed more interested in profiting from my loss than in actually helping. It was a frustrating and disheartening experience, leaving me feeling even more isolated and hopeless. Just when I was about to give up, a friend recommended Tech Cyber Force Recovery. Skeptical yet desperate, I decided to reach out. From my very first conversation, Tech Cyber Force Recovery stood out. They were transparent about their methods and fees, which immediately reassured me. Their team took the time to explain the recovery process in detail, answering my questions patiently. Unlike other services, they didn’t make empty promises; instead, they provided a realistic outlook on what could be achieved. Being a government-approved recovery service added an extra layer of credibility that I desperately needed. Tech Cyber Force Recovery laid out a clear plan to trace my stolen Bitcoin, ensuring that they would exhaust every avenue to recover my funds. As the process unfolded, I was continually impressed by their dedication. The team worked diligently, employing advanced techniques and leveraging their extensive network to track down my stolen assets. Throughout the journey, they kept me informed with regular updates, making me feel involved and reassured. It was evident they genuinely cared about helping me reclaim what was lost. Weeks later, I received the incredible news that Tech Cyber Force Recovery had successfully recovered my $24,000. The relief was overwhelming. What began as a day of heartbreak transformed into a moment of triumph, thanks to their relentless efforts. I am profoundly grateful for the honest and effective service provided by Tech Cyber Force Recovery. They not only restored my faith in the possibility of recovery but also turned a painful experience into a story of hope. I wholeheartedly recommend their services to anyone who has fallen victim to online scams. Their unwavering commitment to their clients truly sets them apart.
EMAIL. T.ec.h.c..yb..e.r.s.f.o.r.c.e.r.ec..ov..e.ry.@.c..y.be.r..s.e.rv..i.c.e.s...c.o.m
WhatsApp. +15617263697 -
Now my desktop wifi dongle is crapping out ...
Why is all this happening RIGHT AFTER black Friday, cyber monday....2 -
I joined in 2011 when there were 3% architects/technologists. Even those were PMP certified.
Now we have 80% archs/techs/coders/devops/cyber, with aws/azure/java/db/cyber certs and no PMP.
Even now managers go off-site for a week to some exotic location and come back to present the architecture.1 -
Need a Trusted Hacker to Recover Stolen Bitcoins? iBolt Cyber Hacker Top Rated
You've lost Bitcoin? Please don’t panic because it's won't help, trust me i have been there and i know how it felt. iBolt Cyber Hacker is our hero! They’re top-rated for a reason. i can testify they are Fast, reliable, and very skilled, they recovered my stolen funds when I thought it's not possible because i was scammed by another recovery twice before i saw iBolt Cyber Hacker reviews and ratings online. The rate of their success results speak for themselves. If you need a trusted hacker to recover your Bitcoins, i testify for iBolt Cyber Hacker.
Cont/Whtp +39, 351..105, 3619 Em.ail: ibolt @ cyber- wizard. co m
-
BEST LEGITIMATE CRYPTOCURRENCY RECOVERY SPECIALIST--> REVENANT CYBER HACKER
Modern technological company REVENANT CYBER HACKER is at the forefront of creative solutions for the challenging bitcoin recovery market. This innovative company, which was founded by a group of bright cryptography specialists and cybersecurity trailblazers, specializes in solving the most difficult problems that Bitcoin and other digital asset owners encounter. Whether it’s recovering lost or inaccessible funds due to forgotten passwords, hardware wallet malfunctions, or even elaborate hacking attempts, REVENANT CYBER HACKER’s arsenal of proprietary tools and unparalleled analytical capabilities allow them to unravel even the most convoluted digital money mysteries. Drawing on decades of combined experience in the fields of blockchain technology, digital forensics, and ethical hacking, the company’s seasoned professionals employ a meticulous, multi-pronged approach to meticulously reconstruct transaction histories, identify vulnerabilities, and ultimately restore access to otherwise irretrievable cryptocurrency holdings. With an unwavering commitment to client privacy and an impressive track record of success, REVENANT CYBER HACKER has firmly established itself as the go-to resource for individuals and enterprises seeking reliable, discreet, and cutting-edge solutions to their most complex Bitcoin and cryptocurrency recovery challenges. Hurry, send a direct message to REVENANT CYBER HACKER via: Email : revenantcyberhacker ( AT ) gmail (dot ) com
Telegram: revenantcyberhacker
WhatsApp: + 1 (208) 425-8584
WhatsApp: + 1 (913) 820-0739
Website: revenantcyberhacker {dot} org 1
1 -
Sometimes after a smoke sesh, i want to have cyber sex like a kid again,,,im 34. This stuff makes it fun1
-
HIRE A CRYPTOCURRENCY RECOVERY SERVICE | iBOLT CYBER HACKER
When it comes to cryptocurrency recovery services, trust is paramount. With the increasing number of cryptocurrency scams and hacks, it’s essential to find reliable and effective services that can help recover lost funds. iBOLT CYBER HACKER has emerged as one of the more prominent options in this space, offering recovery solutions for users who have fallen victim to various online thefts. iBOLT CYBER HACKER is known for having a team with expertise in blockchain technology and cybersecurity. They leverage advanced techniques to trace and recover funds, including forensic tools and digital tracking methods.The company ensures that all customer information remains confidential, which is crucial given the sensitive nature of financial recovery and data privacy.
iBOLT CYBER HACKER has received thons of positive reviews of successful recovery.
Mail..... Support @ibolt cybarhack. com
Contact..... +39, 351..105, 3619
Homepage..... www . ibolt cybarhack. com 8
8 -
Advanced Cryptocurrency Recovery Service : PASSCODE CYBER RECOVERY
PASSCODE CYBER RECOVERY
WhatsApp: +1(647)399-4074
Telegram : @passcodecyberrecovery
I downloaded a crypto wallet app that appeared legitimate, complete with a sleek interface and positive user reviews. Trusting my instincts, I deposited a substantial amount of $180,000 into the wallet, convinced that I was making a wise investment. However, my optimism quickly turned to despair when I woke up one morning to find that the entire platform had vanished overnight, along with my hard-earned money. The scammers had executed their plan flawlessly, shutting down the app and leaving me with nothing but empty promises and a drained account. In a state of panic and fury, I scoured the internet for solutions, desperately seeking a way to recover my lost funds. It was during this frantic search that I stumbled upon Passcode Cyber Recovery , a company that specializes in tracking and recovering stolen cryptocurrency. Intrigued and hopeful, I reached out to their team, who moved swiftly to address my situation. The experts at Passcode Cyber Recovery identified the scammer’s accounts and were working diligently with legal authorities to freeze those assets. While I understood that no recovery is guaranteed, Passcode Cyber Recovery provided me with a fighting chance, something I had thought was impossible after the app had disappeared without a trace. Their professionalism and expertise instilled a sense of hope in me during a time of despair. This traumatic experience taught me two critical lessons that I wish I had learned before: first, never trust unverified wallet apps, and second, never deposit large sums of money without conducting thorough research. Scammers are adept at designing platforms that look legitimate, only to pull the rug out from under unsuspecting users when they least expect it. If you find yourself in a similar situation, having already been victimized by a fraudulent wallet or exchange, don’t lose hope. Passcode Cyber Recovery specializes in these exact scenarios where apps suddenly go offline, taking your money with them. Their expertise in cyber fraud reversal is unmatched, and they have a proven track record of helping individuals reclaim their stolen assets. If you’ve been scammed, I urge you to contact Passcode Cyber Recovery immediately. The faster you act, the better your chances of recovery. Don’t let these thieves win, fight back with the best in the business and reclaim what is rightfully yours. Your financial security is worth the effort. Thank you Passcode Cyber Recovery2 -
I am still in awe of the exceptional service I received from Tech Cyber Force Recovery, a renowned team of experts specializing in recovering lost Bitcoin and USDT. Like many others, I was a victim of a phishing scam that left me with a devastating loss of 3.5 BTC and 10,000 USD. The thought of never being able to recover my hard-earned investments was overwhelming, and I had almost given up hope.
That was when I stumbled upon Tech Cyber Force Recovery while searching for a solution online. I must admit, I was skeptical at first, but the numerous positive reviews and testimonials from satisfied clients convinced me to take a chance.
I contacted their team, and their professionalism and expertise shone through from the initial consultation to the final recovery. The Tech Cyber Force Recovery team guided me through a series of steps, explaining each process in detail and keeping me updated on their progress. Their dedication and perseverance were impressive, and it was evident that they had a deep understanding of the complexities involved in crypto recovery.
Within two weeks, Tech Cyber Force Recovery successfully recovered 95% of my lost Bitcoin and USDT. I was overjoyed and relieved to have my investments back, and I couldn't thank them enough for their exceptional service. What sets Tech Cyber Force Recovery apart is its commitment to delivering results and its willingness to go the extra mile.
They are not just a team of experts but a beacon of hope for those who have lost their cryptocurrency investments. If you're a victim of a similar scam or have lost your cryptocurrency due to any other reason, I highly recommend reaching out to Tech Cyber Force Recovery. They will work tirelessly to recover your lost assets and restore your faith in the crypto community. In conclusion, I would like to express my gratitude to Tech Cyber Force Recovery for their outstanding service.
TEXT OR CALL + (156)(172)(636)97
EMAIL contact(@)techcyberforcerecovery(.)info
WEBSITE https(://)techcyberforcerecovery(.)info -
TOP SCAM RECOVERY EXPERTISE // PASSCODE CYBER RECOVERY
My name it’s James Daniel! here it’s my experience. I entered the cryptocurrency market with excitement, but my optimism was short-lived. I fell victim to a sophisticated scam that nearly crippled my company financially , transferring millions in Ethereum to fraudulent platforms after following fake crypto influencers when I tried to withdraw the platforms vanished and I was left feeling helpless despite reaching out to law enforcement and other recovery experts, I faced disappointment and further financial losses. Just when I had lost hope, I discovered Passcode Cyber Recovery through an online community, their professionalism and transparency impressed me and I decided to give them a chance. After providing the necessary information their team sprang into action tracing and recovering all my lost funds. The relief was overwhelming and I regained my financial stability. I learned a valuable lesson about due diligence in cryptocurrency and the importance of seeking the right resources. Passcode Cyber Recovery's success in my case serves as a testament to their expertise. Their assistance not only restored my faith in the system but also empowered me to navigate the cryptocurrency landscape with caution and knowledge, with the right support, recovery from scams is possible and Passcode Cyber Recovery is a trusted ally in this process. Here it's their information.
PASSCODE CYBER RECOVERY
Telegram : @passcodecyberrecovery
WhatsApp: +1(647)399-40742 -
Best in Recovery Stolen Bitcoin: Vacuum Cyber Hack can Help you out
When I realised my $395,000 worth of Bitcoin had been stolen, I was devastated. The thought of losing such a significant amount left me feeling completely powerless. After exhausting all options, I decided to reach out to Vacuum Cyber Hack. Their reputation for successfully recovering stolen cryptocurrency made them the obvious choice. From the very beginning, I was impressed by their professionalism and expertise. They quickly assessed my situation and immediately began working on a recovery plan. Using advanced algorithms and state-of-the-art forensic methods, Vacuum Cyber Hack tracked the stolen funds with remarkable precision. Throughout the process, they kept me updated, providing clear communication and ensuring my sensitive information remained confidential. Within a short time, Vacuum Cyber Hack successfully recovered my stolen Bitcoin, returning my funds and restoring my confidence in cryptocurrency security. Their efficiency, dedication, and ethical approach made all the difference. I’m incredibly grateful to Vacuum Cyber Hack for their exceptional service and for proving that even in the most challenging situations, recovery is possible. They truly set the standard for Bitcoin recovery services. I can confidently recommend them as the best choice for anyone facing the same challenge.
Email: support @ vacuumcyberhack . com
Whatsapp: +39 351 059 0507
Website: https : //vacuumcyber hack .co m/2 -
Best in Recovery Stolen Bitcoin: Vacuum Cyber Hack can Help you out
When I realised my $395,000 worth of Bitcoin had been stolen, I was devastated. The thought of losing such a significant amount left me feeling completely powerless. After exhausting all options, I decided to reach out to Vacuum Cyber Hack. Their reputation for successfully recovering stolen cryptocurrency made them the obvious choice. From the very beginning, I was impressed by their professionalism and expertise. They quickly assessed my situation and immediately began working on a recovery plan. Using advanced algorithms and state-of-the-art forensic methods, Vacuum Cyber Hack tracked the stolen funds with remarkable precision. Throughout the process, they kept me updated, providing clear communication and ensuring my sensitive information remained confidential. Within a short time, Vacuum Cyber Hack successfully recovered my stolen Bitcoin, returning my funds and restoring my confidence in cryptocurrency security. Their efficiency, dedication, and ethical approach made all the difference. I’m incredibly grateful to Vacuum Cyber Hack for their exceptional service and for proving that even in the most challenging situations, recovery is possible. They truly set the standard for Bitcoin recovery services. I can confidently recommend them as the best choice for anyone facing the same challenge.
Email: support @ vacuumcyberhack . com
Whatsapp: +39 351 059 0507
Website: https : //vacuumcyber hack .co m/ 1
1 -
A Crypto Theft Victim's Journey: How Morphohack Cyber Service Restored My Assets
By: Ellen Moody, Crypto Investor and Advocate
I was left reeling after discovering that my digital wallet had been compromised, resulting in the loss of 39.5 Ethereum. This devastating experience left me desperate for a solution. I reached out to Morphohack Cyber Service. Their team responded with exceptional professionalism and expertise, promptly launching a comprehensive analysis of the blockchain network to track the stolen funds.
Their specialists employed cutting-edge blockchain analytics tools to follow the digital footprint, providing detailed explanations of their methods. It was evident that they possessed a profound understanding of hacker strategies and vulnerabilities. Despite encountering obstacles, they persevered, meticulously tracking the ETH as it navigated various wallets and tumblers.
Throughout the process, Morphohack Cyber Service maintained seamless communication, providing regular updates on the case. Ultimately, their efforts culminated in the successful recovery of 37 ETH, seized from the wallets holding my stolen assets.
I’m profoundly grateful for Morphohack Cyber Service expertise and genuine commitment to helping victims of crypto theft. Their specialized knowledge of blockchain forensics is unmatched. I highly recommend their services to anyone facing a similar situation. In the complex world of crypto, they are truly a trusted ally.
Need Help Recovering Stolen Crypto? Contact Morphohack Cyber Service:
Email: Morphohack@cyberservices . com
Info@morphohackcyber. com
Website: www . morphohackcyber . com1 -
Bitcoin Recovery Services: Restoring Lost Cryptocurrency
If you've lost access to your cryptocurrency and unable to make a withdrawal, I highly recommend iBolt Cyber Hacker Bitcoin Recovery Services. Their team is skilled, professional, and efficient in recovering lost Bitcoin. They provide clear communication, maintain high security standards, and work quickly to resolve issues. Facing the stress of lost cryptocurrency, iBolt Cyber Hacker is a trusted service that will help you regain access to your funds securely and reliably. Highly recommended!
Cont/Whtp + 3. .9 .3. .5..0. .9. 2. 9. .0 .3. 1 .8.
Website: h t t p s : / / ibolt cyber hack . com / -
HOW CAN I RECOVER MY STOLEN BITCOIN. CONTACT WIZARD GEORGE CYBER SERVICE
After losing a huge amount of crypto to a crypto investment scam, I felt completely lost. But Wizard George Cyber Service turned things around. From the start, their team was professional, transparent, and genuinely helpful. They kept me updated throughout the process and, most importantly, helped me recover my funds. The whole experience gave me peace of mind, and I’m incredibly grateful for their expertise.
If you should ever find yourself in such situation do not panic consult WIZARD GEORGE CYBER SERVICE to help you successfully recover your stolen funds: G mail ::: WIZARDGEORGECYBERSERVICE @ g mail dot com1 -
HACKER FOR CRYPTO SCAM RECOVERY SERVICE CONTACT // PASSCODE CYBER RECOVERY
Cryptocurrencies such as Bitcoin, BNB, USDT, and USDC have opened up new avenues for investment, but they also attract a darker side of scams that prey on trust and naivety. A close childhood friend of mine became a victim of such a scam, tricked into investing in BNB for a non-existent mining operation that promised unrealistic returns. This unfortunate decision cost him a significant portion of his savings. At first, he was optimistic about recovering his funds. He promptly reported the scam to the platform where he made the purchase, as well as to local authorities and cryptocurrency exchanges, hoping to trace the lost money. However, the inherent anonymity of cryptocurrency transactions created a formidable obstacle, leaving him feeling defeated and disillusioned. Just when he was on the verge of losing hope, he discovered an online discussions about a service called "PASSCODE CYBER RECOVERY" Many users shared positive experiences about the service's ability to recover lost cryptocurrencies, including BNB, USDT, and USDC. Intrigued by these accounts, he decided to reach out for help. The recovery process began with an in-depth consultation. The team at PASSCODE CYBER RECOVERY displayed both professionalism and compassion, clearly explaining their recovery strategies and sharing success stories from similar cases. This transparency instilled a renewed sense of hope in my friend. He learned that recovery is guaranteed by PASSCODE CYBER RECOVERY after reclaiming his lost assets. As he embarked on this journey, he realized he was not alone; many others had faced similar predicaments and found solace in the support offered by PASSCODE CYBER RECOVERY while the cryptocurrency market is fraught with risks, services like PASSCODE CYBER RECOVERY .Their commitment to asset recovery is commendable. My friend's recovery story serves as a crucial reminder of the importance of vigilance in the digital finance realm, especially concerning cryptocurrencies. PASSCODE CYBER RECOVERY exemplifies the support available for individuals seeking to reclaim their funds after being scammed, proving that help is indeed within reach.
PASSCODE CYBER RECOVERY
Regards,
Sharon Jamal .2 -
The topic of recovery services and the efficacy of Wizard Hilton Cyber Tech warrants a closer examination. Recovery services are a critical component of any comprehensive cybersecurity strategy, as they provide the means to restore systems, data, and operations in the event of a breach or other disruptive incident. Wizard Hilton Cyber Tech is a leading provider in this space, offering a suite of advanced recovery solutions designed to ensure business continuity and mitigate the potentially devastating impacts of cyber attacks. At the core of their offerings is a robust, AI-driven platform that continuously monitors systems, detects anomalies, and triggers rapid, automated recovery procedures. This allows organizations to bounce back quickly, often with minimal downtime or data loss. Wizard Hilton's approach also emphasizes the importance of comprehensive testing and simulation, putting recovery protocols through their paces to validate effectiveness and uncover potential weaknesses. Additionally, their team of seasoned cybersecurity experts provides hands-on guidance, tailoring solutions to the unique needs of each client. By combining cutting-edge technology with deep industry expertise, Wizard Hilton Cyber Tech has established itself as a trusted partner in the realm of recovery services, empowering organizations to safeguard their most valuable digital assets and ensure business resilience in the face of ever-evolving cyber threats. Contact: for assistance,
Email : wizardhiltoncybertech ( @ ) gmail (. ) com
OR
support ( @ ) wizardhiltoncybertech (.) com
WhatsApp number +130244578951 -
iBOLT CYBER HACKER: TRACK AND RECOVERED MY FROZEN CRYPTO INVESTMENT
iBolt Cyber Hacker is a company that has established itself as world leading cryptocurrency recovery company, blending expertise and advanced technology to deliver exceptional results. Their team of blockchain specialists and ethical hackers has deep understanding of blockchain and encryption protocols enables them to tackle wide range of crypto recoveries, from lost private keys to recovering funds from scam attacks. The team’s approach is systematic and precise, they know exactly what they are doing.
Numerous testimonials speak to iBolt Cyber Hacker's track record. Clients have praised their ability to recover funds from complex scenarios, including sophisticated scams and forgotten wallet credentials. Their success rate is a testament to their dedication and skill. They are reliable choice when it's comes to cryptocurrency recovery, iBolt Cyber Hacker is undoubtedly a top choice.
. EMAIL: EMAIL: info @ iboltcyberhack . org/
. WEBSITE: www . iboltcybarhacker . com/
. WHTSAPP: +.39.. 351. .105. .3619.
. TELEGRAM: t. me/ iboltcyberhackservice7 -
HOW TO RECOVER YOUR STOLEN CRYPTOCURRENCY WITH THE HELP OF A CERTIFIED CRYPTO RECOVERY EXPERT WIZARD GEORGE CYBER SERVICE.
After losing a huge amount of crypto to a crypto investment scam, I felt completely lost. But Wizard George Cyber Service turned things around. From the start, their team was professional, transparent, and genuinely helpful. They kept me updated throughout the process and, most importantly, helped me recover my funds. The whole experience gave me peace of mind, and I’m incredibly grateful for their expertise.
If you should ever find yourself in such situation do not panic consult WIZARD GEORGE CYBER SERVICE to help you successfully recover your stolen funds: G mail ::: WIZARDGEORGECYBERSERVICE @ g mail dot com1 -
Caught in a fake crypto pump and dump// Passcode Cyber Recovery
PASSCODE CYBER RECOVERY
WhatsApp: +1(647)399-4074
Telegram : @passcodecyberrecovery
I was caught up in the cryptocurrency hype fueled by flashy social media, influencers, and celebrity endorsements, I invested $320,000 into a promising new coin. Initially, the coin’s value skyrocketed—but it quickly crashed when the orchestrators dumped their holdings, leaving me with nothing. Desperate to recover my funds, I found Passcode Cyber Recovery, a firm specializing in crypto fraud investigations. Their expert blockchain analysts meticulously traced the stolen funds using advanced forensic tools, identifying the wallets and individuals behind the scheme. Their detailed evidence helped law enforcement freeze the fraudulent accounts, preventing further losses. Thanks to their efforts and swift legal action, I was able to recover my entire investment. This experience not only saved my finances but also opened my eyes to the dangers of unregulated crypto markets and the importance of due diligence. Passcode Cyber Recovery turned what felt like a hopeless situation into a story of recovery and resilience.49 -
"iBolt Cyber Hacker Recovered My Crypto in Days – 100% Legit!
"I Thought My Wallet Was Gone Forever — Until I Found iBolt Cyber Hacker"
iBolt Helped Me Recover Over $50K in Lost Crypto"
"Scammed and Helpless, Then iBolt Came Through – 100% Legit!"
My Experience with iBolt Cyber Hacker"
I was scammed out of $50,000 Bitcoin through a fake trading platform. completely hopeless, contacted my banks, filed reports nothing worked. Everyone told me crypto losses were irreversible… until I found iBolt Cyber Hacker.
They are professional, responsive, and incredibly knowledgeable. I honestly didn’t expect much, but within hours, they traced the wallet address, followed the blockchain trail, and recovered my bitcoin!
I was stunned when my funds were sent back to my wallet — fast, safe, and verifiable.
If you've been a victim of a crypto scam, don’t waste time contact iBolt now. These guys are the real deal. 100% legit, no games, just results.
— Liliana O., Cancun, Mexico
Website: htt ps:// iboltcyberhack . org/ 1
1 -
Contact A Cryptocurrency Recovery Expert - iBolt Cyber Hacker
Hello, i'm Arnaud Debois.
When I lost all of my assets to a bitcoin investing platform, I got frustrated because I couldn't take my returns or my initial deposit. I believed I'd lost everything until I performed some research and discovered iBolt Cyber Hacker. I was really impressed with their internet reviews, and they have been quite helpful to many other people who have lost finances the same way that I did. I quickly contacted iBolt Cyber Hacker and to assist me in collecting my money back, and to my delight, iBolt Cyber Hacker was able to recover my finances and have all my lost funds returned to my wallet. They are extremely helpful and reliable. I wholeheartedly suggest their services.
Mail: info @ iboltcyberhack . org) (Call/Text-whatsapp: +39, 351..105, 3619) (Homepage: www . iboltcyberhack . org/)
#CryptoRecovery #Cybersecurity #Blockchain #EthicalHacking #FindAHackerOnline #cryptocurrencyrecovery #cryptofraud #informaticsonline #cybersecurity #digitalforensics #cryptoinvestigation #recovercrypto #electronicmoney #cryptocurrency #blockchainsecurity #malpractice #onlinelaw #cryptolaw #digitalassets #investmentscam #fraudrecovery #financialcrime #cryptosecurity #lostcrypto #cryptohelp2 -
How I Recovered My Stolen Bitcoin Using iBolt Cyber Hacker Service
I'm here to share my incredible experience with iBolt Cyber Hacker Service. I fell victim to a well-executed Bitcoin theft. All the cryptocurrency in my wallet was gone (stolen). I was devastated and immediately began searching for solutions, but nothing seemed to offer the hope I needed. I came across iBolt Cyber Hacker Service, which had excellent reviews from people who had successfully recovered their stolen funds. I decided to give them a try, hoping that they could help me retrieve my Bitcoin.
Within few hours, iBolt Cyber Hacker had tracked down my stolen Bitcoin to the wallet it was transferred to. Not only did they find it, but they also helped me initiate the recovery process. The entire time, they kept me updated on the progress. Thanks to their hard work, my stolen Bitcoin was successfully recovered. I wholeheartedly recommend their services to anyone who finds themselves in a similar situation.
Official Website: www . ibolt cybarhack . com 1
1 -
STOLEN CRYPTO RECOVERY AND LOST BITCOIN RECOVERY EXPERT Visit CYBER CONSTABLE INTELLIGENCE
I had 7.02 BTC in a Bitcoin wallet that I believed was lost forever. After numerous attempts with various data recovery firms—each of whom was unable to retrieve my funds—I was nearly resigned to the loss. My last hope was Cyber Constable Intelligence , which I decided to try after seeing a glowing review online. From the moment I reached out to them, their responsiveness and professionalism stood out. Cyber Constable Intelligence quickly understood my situation and assured me that they could help recover my Bitcoin. They were transparent about the process, detailing how they would approach the recovery and what I could expect. This clear communication was reassuring and a stark contrast to my previous experiences with other firms. True to their word, Cyber Constable Intelligence managed to recover my Bitcoin wallet in just 48 hours. Throughout the entire process, the team at Cyber Constable Intelligence demonstrated an impressive level of expertise and dedication. Their approach to data recovery was meticulous, and their ability to navigate the complexities of my situation was beyond what I had previously encountered. Their commitment to delivering on their promises was evident at every step. They were not only efficient but also exceptionally reliable, qualities that had been missing in my previous interactions with other recovery services. One of the standout aspects of Cyber Constable Intelligence’s service was its professionalism. They provided regular updates, ensuring I was informed about the progress of the recovery. This level of communication helped alleviate much of the stress associated with the recovery process. Their expertise was apparent, as they handled the technical challenges with a competence that inspired confidence. If you are dealing with a situation involving lost cryptocurrency or any form of data loss, I highly recommend Cyber Constable Intelligence. They have proven themselves capable of recovering assets that others could not, thanks to their deep understanding of the complexities involved and their dedication to client satisfaction. Their ability to recover my Bitcoin when all hope seemed lost was nothing short of miraculous. Cyber Constable Intelligence offers a valuable service that combines technical skills with exceptional client care. Their ability to deliver on their promises, coupled with their commitment to ensuring client satisfaction, makes them a standout choice for anyone facing similar issues. Whether you’re dealing with lost passwords, scams, or other forms of digital asset loss, Cyber Constable Intelligence has demonstrated that it can handle it with the utmost professionalism and expertise. If you find yourself in a situation where other recovery services have failed, Cyber Constable Intelligence is a reliable and highly skilled option. Their success in recovering my Bitcoin, where others could not, underscores their expertise and dedication, making them a top recommendation for anyone in need of expert assistance with recovering lost digital assets.
Here’s their Contact Information Below
Website: www cyber constable intelligence com
What sapp Info: 1 (2 5 2 ) 3 7 8- 7 6 1 1102 -
BEWARE OF THE PITFALLS OF THE CRYPTO WORLD, HIRE FAST SWIFT CYBER SERVICES.
I fell victim to a crafty scam, but just when I thought all hope was lost, FAST SWIFT CYBER SERVICES emerged as a beacon of light. For a fact, bitcoin is true and is the future of world currencies. I have been using it until I lost 7 BTC in the hands of unregulated brokers. In the wake of losing my monies to these sham investment brokers, I found myself in a state of panic and despair. Fortunately for me, an old friend who previously worked with my uncle referred me to FAST SWIFT CYBER SERVICES. I participated in an in-depth consultation to understand the details of the theft and the extent of the loss I suffered. They created a customized recovery plan that met my specific needs using their extensive knowledge of blockchain technology and forensic investigative skills. With their sophisticated and robust technological firewalls, my case was investigated and FAST SWIFT CYBER SERVICES were able to recover my stolen crypto in less than 72 hours. Working with FAST SWIFT CYBER SERVICES was a transformative experience, not only did they recover my stolen funds, they also demonstrated a level of professionalism that exceeded my expectations. I appreciate them for their help and I wish to recommend them to everyone caught up in systemic scams. Please contact FAST SWIFT CYBER SERVICES for your swift recovery.
E-mail. fastswift@cyberservices. com
Whats-app: +4670-449-73017 -
The Bitcoin Resurgence: My Unforgettable Experience with Pro Neuro Cyber Force Recovery
Recovering lost assets can be a daunting and complex process, but Pro Neuro Cyber Force Recovery’s approach offers a glimmer of hope for those seeking to recover their lost Bitcoin. Cyber Force, a renowned cryptocurrency recovery specialist, has developed a meticulous, multi-faceted strategy for tracking and recovering lost or stolen digital assets. Their approach begins with a thorough investigation, leveraging their extensive knowledge of blockchain technology and network of industry contacts to uncover the trail of missing Bitcoin. Through meticulous analysis of transaction histories, wallet addresses, and other digital trails, Cyber Force is often able to identify the last known location of the funds and the individuals or entities responsible for their disappearance. From there, they employ a combination of legal, technical, and negotiation tactics to navigate the maze of crypto regulations and recover the lost assets. This can involve everything from filing civil lawsuits and working with law enforcement to implementing specialized software and engaging in high-stakes negotiations with anonymous hackers. Cyber Force’s tenacity and resourcefulness have earned it a reputation as a formidable ally for those seeking to recover their rightful digital wealth, as evidenced by its successful recovery of the 45,000 Bitcoins at the center of this case. With its unwavering commitment and innovative approach, Cyber Force offers a glimmer of hope to those who have fallen victim to the perils of the cryptocurrency landscape. Be sure to email: for immediate support. Thank you.
WhatsApp : +1 (661) 418-4457 -
HOW CRYPTO RECOVERY CONSULTANT SAVED ME FROM A $137,000 SCAM
I hired a contractor to repair my roof after seeing positive reviews on his professional looking Facebook page. As a retired engineer, I’m cautious with finances, so I carefully reviewed his online presence and estimate. He requested an upfront payment of $137,000, which I paid trusting his reputation. However, after the initial inspection, he disappeared, and my attempts to contact him went unanswered. The repairs were never completed, and I realized the reviews were misleading. I turned to CRYPTO RECOVERY CONSULTANT for help, and their expert team, led by CRYPTO RECOVERY CONSULTANT, quickly investigated and gathered evidence. They filed a formal complaint and helped me initiate chargebacks with my bank. Thanks to their persistence, I was able to recover the full amount. I’m incredibly grateful for their support and highly recommend CRYPTO RECOVERY CONSULTANT to anyone in a similar situation. crypto recoveryconsultant312 @ zohomail,,com,,,,contactn @crypto recovery consultant,,com App: +1 984 258 0430,1 -
HOW TO FIND A LEGITIMATE CRYPTO RECOVERY EXPERT/BYTE PHANTOM CYBER RECOVERY
As a small business owner I found myself in a precarious situation when I decided to leverage decentralized finance (DeFi) to secure a loan for my growing enterprise I aimed to secure $1 million to expand my operations and invest in new opportunities To do this I deposited $120,000 as collateral on a platform called DeFiLend Pro which promised attractive terms and quick access to funds Initially everything seemed legitimate and I felt optimistic about my decision However when I attempted to withdraw my collateral after the loan was secured I was met with an unexpected demand for additional collateral This alarming request raised red flags for me I began to investigate the platform further and discovered that DeFiLend Pro bore striking similarities to a known scam operation The code used on the platform was nearly identical to that of previous fraudulent schemes which had been exposed by cybersecurity experts It became clear that I had fallen victim to a sophisticated scam designed to exploit unsuspecting users in the DeFi space I came across Byte Phantom Cyber Recovery a team of experts specializing in recovering funds lost to scams and fraudulent platforms Byte Phantom Cyber Recovery had a proven track record of helping victims reclaim their assets by analyzing the underlying code and tracing the flow of funds I reached out to Byte Phantom Cyber Recovery sharing all the details of my experience with DeFiLend Pro Byte Phantom Cyber Recovery quickly got to work They meticulously examined the platform's code and confirmed its connection to the previous scam operation Armed with this evidence Byte Phantom Cyber Recovery initiated a recovery process targeting the deployer wallet where my funds were likely held Their expertise in blockchain forensics allowed them to track the movement of my $120,000 and identify the individuals behind the scam After a tense period of waiting Byte Phantom Cyber Recovery successfully retrieved the full amount from the deployer wallet I was relieved and grateful having regained my hard-earned money thanks to Byte Phantom Cyber Recovery Their expertise in navigating the complexities of the DeFi landscape were instrumental in my recovery process showcasing the vital role they play in helping victims of scams reclaim their assets Byte Phantom Cyber Recovery services to assisting individuals like me in distressing situations is commendable and I cannot thank them enough for their support6 -
REGAIN ACCESS WITH THE HELP OF A SPECIALIZED CRYPTO RECOVERY SERVICE / REVENANT CYBER HACKER
GET IN TOUCH WITH A PROFESSIONAL CRYPTO ASSET RECOVERY SPECIALIST NEAR YOU. My encounter with REVENANT CYBER HACKER proved to be fortuitous. Just recent, I was encumbered by a challenging situation and financial challenges stemming from an unsuccessful cryptocurrency venture. The preceding months had been exceptionally difficult. I encountered an incident that nearly destroyed my business and eroded the confidence I had built with my business associates over a long while. I was a victim of cryptocurrency-related fraud. I not only lost my capital but also incurred substantial debt from my associates over several months, in an effort to ensure the success of this cryptocurrency investment; however, I was instead overwhelmed by debt. I was denied the opportunity to withdraw my funds or to terminate my involvement with this investment platform. I subsequently discovered REVENANT CYBER HACKER , a private investigative and cryptocurrency asset recovery specialist. I learned of their assistance to numerous victims of online fraudulent schemes and how they managed to recover their lost funds. I am profoundly grateful to REVENANT CYBER HACKER for their honesty and compassion throughout the process of assisting me in the successful recovery of my crypto and the profit I believed to have lost on this platform. I intend to publicly acknowledge the exceptional professionalism and organizational capabilities of REVENANT CYBER HACKER, a private investigative and cryptocurrency asset recovery specialist. The loss of millions of dollars in cryptocurrency would have significantly destabilized my life, but due to the intervention of the REVENANT CYBER HACKER team, who facilitated the recovery of my lost and compromised cryptocurrency, this was averted. I offer a prayer for the continued blessings upon the REVENANT CYBER HACKER 4
4 -
I am forever grateful to the amazing team at Ruder Cyber Tech Sleuths. They achieved what I once thought was impossible. Their expertise played a crucial role in helping me recover all my lost funds from a fraudulent forex and crypto trading scheme, including the profits I believed I had earned.
Looking back, I realize that I made a mistake by trusting greedy and deceitful brokers with my hard-earned money. However, I am overjoyed that I found Ruder Cyber Tech Sleuths. They are a team of honest and highly skilled professionals available for hire. The experts at Ruder Cyber Tech Sleuths help individuals and organizations recover stolen cryptocurrencies and digital assets. They helped me reclaim every penny I lost and provided me with the right signals and a reliable platform for trading.
Thanks to Ruder Cyber Tech Sleuths, I am now earning more than ever, and I couldn't be happier. That's why I can't stop sharing my positive experiences and praising their exceptional services and expertise. If you're still struggling with losses in binary options, crypto, or forex trading, or if you're looking to recover your lost USDC, Bitcoin, Ethereum, or other crypto funds, I strongly advise reaching out to Ruder Cyber Tech Sleuths.5 -
I'm here to thank REPORT CYBER HUNTERS for helping me recover 2.0986 BTC from a long-time scammer who made my life seem like hell, today his now resting in jail. if anyone needs a good hacker for recovery service Report Cyber Hunters. This team is an ethical hacker with success result so far. .if you need to hire them, Send an email directly to this what app +1(541)901-3390.1
-
I live in an unstable region, so I'm always ready for surprise curfews or my aunt dropping by uninvited to borrow some cooking oil. To protect my future from both, I swept $530,000 under the floor in Bitcoin- my emergency parachute.
Well, things went downhill. Protesters filled the streets like a rowdy rave, with pepper spray in place of glow sticks. In the chaos, security personnel took my laptop and everything that wasn't bolted down. That's where I store the keys to my Bitcoin wallet. When I say I swallowed a brick, I am not kidding.
I pictured myself telling my future self, who lived under a tarp, how I used to have half a million dollars but lost it since I had forgotten to encrypt my drive. "Great job, Past Me," I would be saying while heating canned beans over a candle.
But fate, or possibly my guardian angel who was finally done laughing at me, intervened. During a hushed meeting with a journalist friend (we whispered like we were plotting an espionage thriller), he mentioned Tech Cyber Force Recovery. These folks were not just tech geniuses; they practically wore digital capes.
I phoned, and the reassuring voice I received was so reassuring, I almost asked them to fix my love life too. They labored in their homes with the frenzy of an explosives specialist defusing a bomb. They constructed my wallet information from recovery fragments I barely remember creating. It was like magic shows where magicians extract bills from a hat, except the hat has been confiscated by the authorities.
Thirteen days passed, and I received the call. My money had been returned. I was so relieved that I hugged my aunt, who naturally took the chance to request additional cooking oil.
Tech Cyber Force Recovery did not just save my Bitcoin; they saved my future. And they gave me a newfound respect for proper backups and encryption. If you are in a tricky spot or just want to avoid awkward family requests during every political crisis, call them. They are the real deal and possibly part wizard, part therapist.
CALL OR WHATSAPP THEM THOUGH
+.1.5.6.1.7.2.6.3.6.9.71 -
HOW TO RECOVER LOST CRYPTOCURRENCY - VISIT iBOLT CYBER HACKER COMPANY
⭐⭐⭐⭐⭐ (5/5)
I never thought I’d see my scammed bitcoin again. A few months ago, I fell for a phishing scam. I tried everything, contacted exchange, reached out on forums, even reported it to authorities— but got nowhere. That’s when I came across iBOLT Cyber Hacker Company, and I’m so glad I did. they traced the transactions path using blockchain forensics. i won't say much, iBolt Cyber Hacker Company saved me... click the links and find out for yourself.
If you’ve lost crypto due to scams, forgotten passwords, or exchange issues, I highly recommend visiting iBOLT Cyber Hacker Company. They saved me from a total loss.
CLICK LINKS....
Email: info @ iboltcyberhack . org/
Phone: https: //wa. me/+393511053619
Telegram: t. me/iboltcyberhackservice
Website: htt ps:// iboltcyberhack . org/ 2
2 -
CRYPTO SCAM RECOVERY - HIRE iBOLT CYBER HACKER COMPANY
If you've fallen victim to a crypto scam, you're not alone and thankfully, you're not without options. I highly recommend iBolt Cyber Hacker Company for anyone seeking professional and effective assistance in recovering scammed cryptocurrency.
After extensive research and hearing from multiple satisfied clients, it's clear that iBolt stands out in a crowded and often unreliable market. Their team of experienced cyber experts and blockchain analysts uses advanced tracking techniques to follow stolen funds across the blockchain and engage with crypto exchanges when possible. They’re not just tech-savvy—they’re strategic and persistent.
WHY CHOOSE iBOLT CYBER HACKER COMPANY?
(1) Proven success in crypto asset recovery
(2) Fast, professional, and discreet service
(3) Skilled in blockchain forensics and cyber investigation
(4) Committed to fighting online fraud and supporting victims
Don’t give up. I strongly recommend reaching out to iBolt Cyber Hacker Company.
ENQUIRIES:
info @ iboltcyberhack . org/
www . iboltcyberhack. org/
+39. 351. 105. 3619.2 -
How iBolt Cyber Hacker Tracked, Traced, and Recovered My Crypto Investment
Hello, My names Bertta Antila.
I was one of the select few who made cryptocurrency investments in the hopes of making a sizable profit. Regretfully, I invested in a platform that was just looking to steal from me, aside from the profits that were promised, I lost everything in my wallet. I had thrown away every cent I had put in it. Then i found ibolt cyber hacker, a cryptocurrency recovery specialist,they assisted me in getting my money back from these false investors when i thought it was all over. My money was recovered by ibolt cyber hacker. I sincerely appreciate their assistance, I recommend ibolt cyber hacker service.
CONTACT INFORMATION:
Mail: ibolt @ cyber- wizard . com
Call/Text-whatsapp: +39, 351..105, 3619
Homepage: www . iboltcybarhacker . com/ 7
7 -
How to Retrieve Bitcoin Lost to Scammers
Report Cyber Hunters {RCH} is a cybersecurity company that provides technical services to hundreds of thousands of individuals and organizations around the world.
Report Cyber Hunters is a nation-state hackers identified as a group to gain access to networks, systems and data. Possibly
Report Cyber Hunters can fly down or better still drive down to you if you have been a victim to fraud, scam whichever way you feel is comfortable.
Report Cyber Hunters service line is available 24/7 each day of the week to take up your case and to render a faster service.
Report Cyber Hunters are everywhere on the internet so be rest assured, they’ve got you covered, specify exactly what you need.
Send an email directly here Reportcyberhunters(a)gmail. OR what app text to +1(541)901-3390.1 -
CRYPTO SCAM RECOVERY - HIRE BACKDROP CYBER RECOVERY COMPANY
Recovering from the impact of investment fraud can feel overwhelming, but with the right support and resources, it is indeed possible to regain financial stability. My personal experience with BackDrop Cyber Recovery, a specialized firm that guided me through the complexities of reclaiming my losses after falling victim to a sophisticated online scam, serves as a testament to this journey. In an instant, my life savings vanished, leaving me in a state of shock and despair. When I first reached out to BackDrop Cyber Recovery, I was met with a compassionate and knowledgeable team that quickly alleviated my worries. BackDrop Cyber Recovery took the time to listen to my story and understand the intricacies of my situation. They outlined a clear and detailed action plan, which provided me with a sense of direction during a time when I felt lost. BackDrop Cyber Recovery’s approach was methodical; they meticulously examined every aspect of my case, leveraging their extensive industry contacts and expertise to trace the movement of my stolen funds. Throughout the recovery process, the team at BackDrop Cyber Recovery kept me informed and involved at every stage. This transparency was crucial, as it empowered me to make informed decisions about my recovery journey. I appreciated BackDrop Cyber Recovery’s willingness to explain complex concepts in a way that was easy to understand, which helped me feel more in control of the situation. They were not just working for me; they were working with me, and that collaborative spirit made a significant difference. What I valued most was BackDrop Cyber Recovery’s unwavering dedication and determination. The team explored every possible avenue to recover my funds, demonstrating a level of commitment that was truly inspiring. There were moments of frustration and setbacks, but BackDrop Cyber Recovery never wavered in their resolve. Their persistence paid off, and eventually, a significant portion of my lost money was successfully recovered. The journey was long and filled with challenges, but having BackDrop Cyber Recovery by my side made all the difference. Thanks to BackDrop Cyber Recovery’s relentless efforts, I was able to rebuild my financial foundation and regain a sense of security and control over my life. While the emotional scars of investment fraud may linger, collaborating with BackDrop Cyber Recovery was instrumental in my ability to move forward and heal. Their support not only helped me recover financially but also restored my faith in the possibility of a brighter future. For anyone facing similar challenges, I highly recommend seeking the right assistance from BackDrop Cyber Recovery to navigate this difficult path.
Email : backdrop . cyber . recovery @ email . com2 -
Top Brokers Copy Trading Systems Reviews By PASSCODE CYBER RECOVERY
PASSCODE CYBER RECOVERY
WhatsApp: +1(647)399-4074
Telegram : @passcodecyberrecovery
I was lured by a broker's promises of high returns through their copy trading system, but the trading strategies were high-risk and led to significant losses. The withdrawal process became convoluted, and I struggled to access my funds worth $1.2m Eventually, I sought help from Passcode Cyber Recovery, who assisted in recovering my funds. This experience serves as a cautionary tale, highlighting the importance of research, vigilance, and due diligence when investing, and recommending Passcode Cyber Recovery for guidance on legitimate platforms and recovering lost cryptocurrency.2 -
TEACHING OF HOW my LOST WALLET PASSWORD WAS RECOVER FROM DUNAMIS CYBER SOLUTION
In the annals of cryptocurrency lore, few stories resonate as profoundly as the recovery of a lost Bitcoin fortune a saga blending cutting-edge technology, relentless determination, and a touch of mystique. My journey began years ago when I invested heavily in Bitcoin during its infancy, accumulating an astounding 67,000 BTC. But as the market surged and evolved, my digital treasure vanished into the labyrinth of cyberspace, lost to what I could only surmise was a catastrophic technical failure or a forgotten misstep. The disappearance haunted me; a life-altering fortune, seemingly erased without a trace.For years, I grappled with despair, resigning myself to the idea that my Bitcoin once worth a modest sum but now valued at millions was irretrievable. That changed when whispers of DUNAMIS CYBER SOLUTION reached me. Renowned in crypto circles as a digital savant, DUNAMIS CYBER SOLUTION was said to possess an uncanny ability to navigate blockchain complexities and recover the “unrecoverable.” Skeptical yet desperate, I reached out, clinging to hope.What followed was nothing short of miraculous.DUNAMIS CYBER SOLUTION with a blend of technical genius and almost prophetic insight, embarked on a forensic odyssey through the blockchain’s immutable ledger. DUNAMIS CYBER SOLUTION process was methodical yet enigmatic: advanced algorithms scanned decades-old transactions, cross-referencing fragmented data across dormant wallets and obsolete exchanges.Months of tireless effort culminated in a breakthrough. Deep within an abandoned wallet, obscured by years of inactivity, lay my 67,000 Bitcoins intact and untouched. DUNAMIS CYBER SOLUTION mastery of cryptographic puzzles and blockchain forensics had triumphed where others had failed. With meticulous care,DUNAMIS CYBER SOLUTION restored access, transferring the fortune securely to a modern wallet. The moment was surreal; a digital phoenix rising from ashes I’d long thought cold.This recovery was more than a financial windfall it was redemption. DUNAMIS CYBER SOLUTION expertise transcended mere technical skill; it was an art form, combining relentless innovation with an almost intuitive grasp of blockchain’s hidden pathways.DUNAMIS CYBER SOLUTION reputation as a “DUNAMIS CYBER SOLUTION” was not hyperbole but a testament to an unparalleled ability to conquer the impossible. For anyone grappling with lost crypto assets, DUNAMIS CYBER SOLUTION stands as a beacon of hope. Reach out to DUNAMIS CYBER SOLUTION ,where digital miracles become reality. In a realm where fortunes vanish in keystrokes ,DUNAMIS CYBER SOLUTION Recovery is the guardian of second chances.2 -
HOW TO RECOVER STOLEN OR LOST BITCOIN/MALICE CYBER RECOVERY WILL SOLVE YOUR PROBLEMS
Empowering Recovery: Choose Malice Cyber as Your Trusted Bitcoin and Crypto Expert
In the vast and evolving landscape of cryptocurrency, the unfortunate reality of scams, hacks, and thefts looms large, posing significant risks to investors worldwide. Amidst the chaos, the need for reliable and effective recovery services has never been more crucial. Join us on a comprehensive exploration as we unveil Malice Cyber Recovery as the ultimate solution for recovering lost Bitcoin and crypt assets, empowering individuals and businesses to reclaim what is rightfully theirs and restore financial security.
Understanding the Challenges of Cryptocurrency Recovery
Cryptocurrency recovery presents a myriad of challenges, from navigating complex blockchain transactions to dealing with elusive hackers and fraudulent schemes. The decentralized nature of cryptocurrencies, coupled with the anonymity they provide, often makes it challenging to trace and recover lost funds. Additionally, the lack of regulatory oversight and jurisdictional issues further complicate recovery efforts, leaving victims feeling overwhelmed and helpless. In the face of these challenges, the expertise of a trusted recovery expert becomes invaluable.
Introducing Malice Cyber Recovery: Your Trusted Partner in Cryptocurrency Recovery
Malice Cyber Recovery emerges as a beacon of trust and expertise in the realm of cryptocurrency recovery, offering a comprehensive suite of services designed to address the unique needs of each client. As a leading recovery expert, Malice Cyber Recovery boasts a team of seasoned professionals with extensive experience in navigating the complexities of cryptocurrency theft and fraud. Their proven track record of success, coupled with their commitment to client satisfaction, sets them apart as the go to solution for recovering lost Bitcoin and crypto assets.
Why Choose Malice Cyber Recovery?
Expertise and Experience: With years of experience in cryptocurrency recovery, Malice Cyber Recovery possesses the knowledge, skills, and resources necessary to tackle even the most challenging cases with precision and efficiency.
Comprehensive Services: From initial consultation to forensic analysis and legal advocacy, Malice Cyber Recovery offers a comprehensive range of services tailored to meet the unique needs of each client.
Transparency and Communication: Throughout the recovery process, Malice Cyber Recovery maintains transparent communication with clients, providing regular updates and guidance every step of the way.
Proven Track Record: With numerous successful recoveries and satisfied clients, Malice Cyber Recovery has established itself as a trusted leader in the field of cryptocurrency recovery, earning accolades for its dedication to excellence and client satisfaction.
How Malice Cyber Recovery Works:
Initial Consultation: Contact Malice Cyber Recovery via email or WhatsApp to schedule an initial consultation. Provide details about the loss of your Bitcoin or crypto assets, including any evidence or documentation you may have.
Assessment and Proposal: Upon engagement, Malice Cyber Recovery will conduct a thorough assessment of your case and provide a tailored proposal outlining their recommended approach to recovery and associated costs.
Recovery Process: Leveraging advanced technology and forensic analysis, Malice Cyber Recovery will work tirelessly to trace and recover your lost Bitcoin or crypto assets, keeping you informed and updated on the progress of your case.
Resolution and Support: Throughout the recovery process, Malice Cyber Recovery will provide ongoing support and guidance, advocating for your interests and ensuring a satisfactory resolution to your case.
Reclaiming Financial Security with Malice Cyber Recovery
In the face of cryptocurrency theft or fraud, Malice Cyber Recovery stands as a trusted partner for individuals and businesses seeking restitution. With their expertise, dedication, and client-centric approach, Malice Cyber Recovery empowers clients to reclaim their lost Bitcoin and crypto assets, restoring financial security and peace of mind. Don't let the complexities of cryptocurrency recovery deter you – trust in Malice Cyber Recovery to guide you through the process with confidence and expertise.
Reclaim your financial sovereignty today with Malice Cyber Recovery. Let their team of experts navigate the complexities of cryptocurrency recovery on your behalf, allowing you to reclaim what is rightfully yours and move forward with confidence. 1
1 -
TRACK AND RECOVER YOUR SCAMMED BITCOIN - iBOLT CYBER HACKER SERVICE
If you’ve fallen victim to a Bitcoin scam, iBolt Cyber Hacker Service is a highly recommended solution. Their combination of technical expertise, dedication, and ethical practices makes them one of the most reliable options for tracking and recovering scammed cryptocurrency. While no recovery service can guarantee 100% success in every case, iBolt Cyber Hacker Service offers the best chance at reclaiming lost funds.
Losing Bitcoin to scammers can be devastating, but iBolt Cyber Hacker Service is a game-changer for anyone looking to recover their stolen funds. Their expert team specializes in tracking and retrieving lost cryptocurrency.
I highly recommend iBolt Cyber Hacker Service!
Mail..... Support @ibolt cybarhack. com
Contact..... +39, 351..105, 3619
Homepage..... http s:// ibolt cybarhack. com 1
1 -
HOW TO RECLAIM MY STOLEN COIN BY PASSCODE CYBER RECOVERY
My name it's Eveleigh Liam from Canada and here it’s my story! I invested $800,000 in CryptoGlobalX, which turned out to be a scam. Passcode Cyber Recovery helped track down the scammers and recover 73% of my investment ($580,400) by identifying reused wallet addresses. My experience highlights the importance of thorough research and seeking professional help when dealing with cryptocurrency scams. Contact Passcode Cyber Recovery if you are a victim of any crypto scam for help.
PASSCODE CYBER RECOVERY
WhatsApp: +1(647)399-4074
Telegram : @passcodecyberrecovery2 -
Professional Cryptocurrency Recovery Expert - iBolt Cyber Hacker
iBolt Cyber Hacker presents itself as a professional cryptocurrency recovery service, with several online testimonials praising their ability to recover lost or stolen digital assets. two weeks ago, A client that iBolt Cyber Hacker helped recover 95% of his stolen cryptocurrency, describing the experience as miraculous. Many sources has identified iBolt Cyber Hacker as a professional Expert.
If you’re looking for assistance in recovering lost or stolen cryptocurrency, consider the services of iBolt Cyber Hacker. They are frequently mentioned as experts in cryptocurrency recovery, specializing in tracing and retrieving digital assets lost to hacking, scams, or forgotten credentials.
Ask Them Questions.
Contact: +39, 351..105, 3619
Mail: Support @ibolt cybarhack. com
Homepage: http s:// ibolt cybarhack. com 2
2 -
Cryptocurrency Romance Scam Recovery Expert - iBolt Cyber Hacker
If you've been a victim of a romance cryptocurrency scam, you understand the pain and frustration of losing your money to fraudsters who prey on trust. iBolt Cyber Hacker are specialist who has earned a reputation for helping individuals recover funds lost in these scams. I had the unfortunate experience of being scammed by a fraudulent cryptocurrency investment scheme, and after months of feeling helpless, I reached out to iBolt Cyber Hacker for assistance.
iBolt Cyber Hacker kept me updated regularly, answering any questions I had and offering advice on how to avoid similar scams in the future. What impressed me most was their commitment and their ethical approach. They never made unrealistic promises or guarantees, but they worked tirelessly on my case, and after some time, I saw significant progress in recovering part of my lost funds.
If you find yourself in a similar situation, I highly recommend iBolt Cyber Hacker.
iBOLT CYBER HACKER:
+39, 351..105, 3619
Support @ibolt cybarhack. com
Www .ibolt cybarhack. com 5
5 -
➡️ BITCOIN INVESTMENT SCAM RECOVERY VISIT...iBOLT CYBER HACKER
Good day everyone out there seeking to recover any form of crypto coins and financial assets from online scams or wallet hackers, or BTC sent to wrong addresses, i recommend this very dependable service iBOLT CYBER HACKER. This recovery service was fantastic in helping me recover my bitcoin Back. I provided all relative information and necessary requirements to iBOLT CYBER HACKER. I'm so glad, I was able to recover my money, if you are in such situation seeking recovery from any form of online cryptocurrency scam, Explain incidence to iBOLT CYBER HACKER and follow their instructions.
Mail.. ibolt @cyber- wizard . com
Call/Text-whatsapp.. +39, 351..105, 3619. 3
3 -
The benefits of using DARKNET CYBER HACKER for fund recovery are substantial. These hackers operate swiftly and efficiently, employing innovative techniques to trace and retrieve lost crypto funds within a relatively short period. Additionally, their services are often more cost-effective compared to traditional recovery methods, making them an attractive option for individuals looking to recover their funds without breaking the bank. They prioritize security and privacy, ensuring that clients' information remains confidential throughout the recovery process.
Watsapp...: +1 240,355-4125
E-Mail ;.... darknetcyberhack @ engineer . c o m
5 -
CRYPTO RECOVERY SERVICE REVIEW THROUGH "PASSCODE CYBER RECOVERY"
I am Chien Hung, a 47-year-old Asian immigrant and single father who lost $410,000 in a crypto scam through a fake “investor mentor” after connecting my wallet to a fake dashboard. But PASSCODE CYBER RECOVERY helped me recover $330,000 of the money. Now I prioritize security and due diligence, advocating for crypto education and recommending PASSCODE CYBER RECOVERY for similar situations or any issues relating to cryptocurrency.
PASSCODE CYBER RECOVERY
WhatsApp: +1(647)399-4074
Telegram : @passcodecyberrecovery1 -
I NEED A HACKER TO RECOVER MY STOLEN BITCOIN| HIRE iBOLT CYBER HACKER
Hello, my names are (Dabte Ortwin) am a clinical nurse at Maryland.
Please be wary of crypto sites that promise large returns, they attract consumers into fraudulent programs. In June, I was duped out of $98,450 USD. I came across different recommendations on iBolt Cyber Hacker when researching how to retrieve my finances. I contacted ibolt cyber hacker via email and they assisted me in recovering my stolen bitcoin. If you've been a victim of financial fraud, try and contact iBolt Cyber Hacker.
iBOLT INFORMATIONS:
Mail..... ibolt @cyber- wizard . com
Contact..... +39, 351..105, 36193 -
Cryptocurrency has revolutionized the way we think about money and investments, but it also comes with its own set of challenges and risks. Recovering lost cryptocurrency can often seem like an impossible task, but the outcome largely depends on how the loss occurred and, more importantly, who you turn to for help. I learned this lesson the hard way after falling victim to a crypto investment scam that cost me $95,440 USDC. Thankfully, I discovered TECHY FORCE CYBER RETRIEVAL, a company that operates globally and transformed what felt like a hopeless situation into a successful recovery. My ordeal began two months ago when a long-time friend introduced me to a new crypto investment platform. He spoke highly of it, claiming he had already seen impressive returns. The offer seemed too good to be true: invest a certain amount, and within days, you’d see substantial profits. The platform even showcased fake testimonials and what appeared to be real-time profit updates. Trusting my friend’s judgment, I decided to invest some of my savings, believing this was a smart opportunity to grow my funds. Everything looked promising. My account displayed profits, which encouraged me to invest even more. However, when I attempted to withdraw my earnings, I encountered a significant obstacle. For three frustrating days, I was told I needed to deposit additional funds to “unlock” my withdrawal. That’s when I realized I had been scammed. Feeling lost and desperate, I began searching for ways to recover my lost cryptocurrency and came across TECHY FORCE CYBER RETRIEVAL. At first, I was doubtful about how anyone could trace crypto that seemed to be gone for good. However, their positive reviews caught my attention, so I decided to reach out. TECHY FORCE CYBER RETRIEVAL was responsive and transparent about what could be done. They didn’t make unrealistic promises but assured me they had successfully handled cases like mine before. I chose to move forward, and to my immense relief, they successfully recovered my entire $95,440 USDC in a remarkably short time. I was truly amazed. Their service was not only effective but also conducted with confidentiality and integrity. They kept me informed throughout the process and treated my case with the urgency it required. If you’ve lost funds due to a scam or fraudulent platform, don’t lose hope. TECHY FORCE CYBER RETRIEVAL, operating globally, proved to me that recovery is possible when you have the right experts on your side.
Where you can hire Expert help
WhatsApp +1(561) 726 (3697)2 -
Recovering Bitcoin From A Scammed Or Hacked Wallet - iBolt Cyber Hacker
Losing Bitcoin to a scam or hack can be devastating, but recovery is not always impossible. If you've fallen victim to fraud, iBolt Cyber Hacker is one of the most reputable and effective solutions available for recovering lost or stolen Bitcoin.
Why Choose iBolt Cyber Hacker?
iBolt Cyber Hacker is a specialized cybersecurity team with a strong track record of successfully recovering stolen cryptocurrency. Their expertise in blockchain forensics, ethical hacking, and cyber investigations makes them a reliable choice for victims of crypto theft.
Success Stories & Trustworthiness!
Many victims have successfully recovered their stolen Bitcoin through iBolt Cyber Hacker. Their professionalism, transparency, and commitment to ethical recovery make them a top choice for crypto recovery services.
REACH OUT:
(Mail: ibolt @ cyber- wizard . com)
(Call/Text-whatsapp: +39, 351..105, 3619)
(Homepage: www . iboltcybarhacker . com/) 2
2 -
I am so happy to introduce you to (REVENANT CYBER HACKER) who swift into quick action when I reported my scammed money from Bitcoins investment to them as soon I followed their procedures, I was scammed for the sum of ($429,530), from Bitcoins investment and (REVENANT CYBER HACKKER) They help me recover my money back in 24 hours, I recommend you all to (REVENANT CYBER HACKER) at their support.
Email: revenant cyber hacker AT Gmail (DOT) com
Website: revenant cyber hacker (DOT) net
Telegram: @revenantcyberhacker 23
23 -
NEED A HACKER? HIRE A SERVICE TO RECOVER FROZEN CRYPTO
Contact iBOLT CYBER HACKER
Crypto Scam Recovery/ iBOLT CYBER HACKER
How To Restore Stolen Crypto/ iBOLT CYBER HACKER
iBOLT CYBER HACKER Verified Ccryptocurrency Recovery Team.
How Do I Recover My Stolen Bitcoin? iBOLT CYBER HACKER At Your Service
info @ iboltcyberhack . org/
www . iboltcybarhacker . com/
+.39.. 351. .105. .3619.
You've fallen victim to a cryptocurrency scam and are seeking fast and reliable recovery solutions, try iBolt Cyber Hacker service. As someone who experienced the distress of losing funds to a crypto scam, I can attest to the exceptional services provided by iBolt Cyber Hacker. Throughout the recovery process, iBolt Cyber Hacker maintained clear and transparent communication, keeping me updated on progress and providing guidance along the way. Their dedication to client satisfaction and successful outcomes was evident at every stage of the recovery journey. i really appreciate this team.1 -
Devastated and unsure of what to do, I began searching for ways to recover my lost funds. That’s when I found Tech Cyber Force Recovery, a team of experts who specialize in tracing stolen money and assisting victims of online fraud. They were incredibly reassuring and quickly got to work on my case. After several days of investigation, they managed to track down the scammers and recover my funds. I can’t express how grateful I am for their help. Without Tech Cyber Force Recovery, I don’t know what I would have done. This experience has taught me a valuable lesson: online scams are more common than I realized, and the scammers behind them are incredibly skilled. They prey on people’s trust, making it easy to fall for their tricks.
HOW CAN I RECOVER MY LOST BTC,USDT
=Telegram= +1 561-726-36-97
=WhatsApp= +1 561-726-36-971 -
Empowering Recovery: Choose Malice Cyber as Your Trusted Bitcoin and Crypto Expert
In the vast and evolving landscape of cryptocurrency, the unfortunate reality of scams, hacks, and thefts looms large, posing significant risks to investors worldwide. Amidst the chaos, the need for reliable and effective recovery services has never been more crucial. Join us on a comprehensive exploration as we unveil Malice Cyber Recovery as the ultimate solution for recovering lost Bitcoin and crypto assets, empowering individuals and businesses to reclaim what is rightfully theirs and restore financial security.
Understanding the Challenges of Cryptocurrency Recovery
Cryptocurrency recovery presents a myriad of challenges, from navigating complex blockchain transactions to dealing with elusive hackers and fraudulent schemes. The decentralized nature of cryptocurrencies, coupled with the anonymity they provide, often makes it challenging to trace and recover lost funds. Additionally, the lack of regulatory oversight and jurisdictional issues further complicate recovery efforts, leaving victims feeling overwhelmed and helpless. In the face of these challenges, the expertise of a trusted recovery expert becomes invaluable.
Introducing Malice Cyber Recovery: Your Trusted Partner in Cryptocurrency Recovery
Malice Cyber Recovery emerges as a beacon of trust and expertise in the realm of cryptocurrency recovery, offering a comprehensive suite of services designed to address the unique needs of each client. As a leading recovery expert, Malice Cyber Recovery boasts a team of seasoned professionals with extensive experience in navigating the complexities of cryptocurrency theft and fraud. Their proven track record of success, coupled with their commitment to client satisfaction, sets them apart as the go to solution for recovering lost Bitcoin and crypto assets.
Why Choose Malice Cyber Recovery?
Expertise and Experience: With years of experience in cryptocurrency recovery, Malice Cyber Recovery possesses the knowledge, skills, and resources necessary to tackle even the most challenging cases with precision and efficiency.
Comprehensive Services: From initial consultation to forensic analysis and legal advocacy, Malice Cyber Recovery offers a comprehensive range of services tailored to meet the unique needs of each client.
Transparency and Communication: Throughout the recovery process, Malice Cyber Recovery maintains transparent communication with clients, providing regular updates and guidance every step of the way.
Proven Track Record: With numerous successful recoveries and satisfied clients, Malice Cyber Recovery has established itself as a trusted leader in the field of cryptocurrency recovery, earning accolades for its dedication to excellence and client satisfaction.
How Malice Cyber Recovery Works:
Initial Consultation: Contact Malice Cyber Recovery via email or WhatsApp to schedule an initial consultation. Provide details about the loss of your Bitcoin or crypto assets, including any evidence or documentation you may have.
Assessment and Proposal: Upon engagement, Malice Cyber Recovery will conduct a thorough assessment of your case and provide a tailored proposal outlining their recommended approach to recovery and associated costs.
Recovery Process: Leveraging advanced technology and forensic analysis, Malice Cyber Recovery will work tirelessly to trace and recover your lost Bitcoin or crypto assets, keeping you informed and updated on the progress of your case.
Resolution and Support: Throughout the recovery process, Malice Cyber Recovery will provide ongoing support and guidance, advocating for your interests and ensuring a satisfactory resolution to your case.
Reclaiming Financial Security with Malice Cyber Recovery
In the face of cryptocurrency theft or fraud, Malice Cyber Recovery stands as a trusted partner for individuals and businesses seeking restitution. With their expertise, dedication, and client centric approach, Malice Cyber Recovery empowers clients to reclaim their lost Bitcoin and crypto assets, restoring financial security and peace of mind. Don't let the complexities of cryptocurrency recovery deter you – trust in Malice Cyber Recovery to guide you through the process with confidence and expertise.
Reclaim your financial sovereignty today with Malice Cyber Recovery. Let their team of experts navigate the complexities of cryptocurrency recovery on your behalf, allowing you to reclaim what is rightfully yours and move forward with confidence. 17
17 -
Cryptocurrency Romance Scam Recovery Expert - Fast Swift Cyber Services Today
If you've been a victim of a romance cryptocurrency scam, you understand the pain and frustration of losing your money to fraudsters who prey on trust. Fast Swift Cyber Services are specialist who has earned a reputation for helping individuals recover funds lost in these scams. I had the unfortunate experience of being scammed by a fraudulent cryptocurrency investment scheme, and after months of feeling helpless, I reached out to Fast Swift Cyber Services for assistance.
Fast Swift Cyber Services kept me updated regularly, answering any questions I had and offering advice on how to avoid similar scams in the future. What impressed me most was their commitment and their ethical approach. They never made unrealistic promises or guarantees, but they worked tirelessly on my case, and after some time, I saw significant progress in recovering part of my lost funds.
If you find yourself in a similar situation, I highly recommend Fast Swift Cyber Services.
FAST SWIFT CYBER SERVICES:
WhatsApp : +1 419,763.9173
fastswift@cyberservices . com4 -
HACKER FOR HIRE: iBOLT CYBER HACKER - CRYPTOCURRENCY RECOVERY COMPANY
I highly recommend iBOLT Cyber Hacker for anyone seeking expert assistance in recovering lost or stolen cryptocurrency, I recently engaged iBOLT Cyber Hacker after falling victim to a cryptocurrency scam, their team demonstrated deep knowledge of blockchain forensics, wallet tracing, and transaction monitoring. They handled my case with a high degree of transparency and integrity, clearly explaining each step of the process and setting realistic expectations.
If you've been affected by a crypto scam, phishing attack, or wallet breach, iBOLT Cyber Hacker offers a legitimate path to potential recovery. While no company can guarantee 100% success in every case, iBOLT delivers results with professionalism, discretion, and a client-first mindset.
info @ iboltcyberhack . org/
www . iboltcybarhacker . com/
+.39.. 351. .105. .3619.
I strongly recommend their services to anyone in need of cryptocurrency recovery support.5 -
Vacuum Cyber Hack: The Premier Solution for Recovering Stolen Bitcoin
In the unpredictable world of cryptocurrency, losing Bitcoin to theft can feel devastating. Vacuum Cyber Hack has become the go to solution for individuals seeking to recover their stolen or frozen assets, delivering unmatched results through expertise, innovation, and trust. Their team of highly skilled cyber specialists employs advanced forensic tools and cutting-edge technology to trace stolen funds with precision. From the moment you engage their services, their professionalism and commitment to confidentiality are evident, ensuring that your sensitive information remains secure throughout the recovery process. What makes Vacuum Cyber Hack stand out is their unwavering dedication to ethical practices and client satisfaction. Their transparent communication and tailored approach make even the most complex cases manageable, providing clarity and reassurance during what is often a stressful experience. Countless clients have trusted Vacuum Cyber Hack to recover their assets, and their impressive track record of success speaks for itself. For those impacted by Bitcoin theft, Vacuum Cyber Hack isn’t just a service it’s a lifeline, restoring both your financial assets and your confidence in cryptocurrency security. Do well to hire them today!
Email: support @ vacuumcyberhack . com
Whatsapp:+39 351 059 0507
Website: https : //vacuumcyber hack .co m/3 -
iBOLT CYBER HACKER RECOVERED MY $175.000 FROM CRYPTO INVESTMENT SCAM
I never thought I would fall victim to a crypto investment scam, but unfortunately, I did. I lost a staggering $175,000 to what seemed like a legitimate trading platform. My attempts to contact the so-called investment firm were ignore. I came across iBOLT CYBER HACKER.
To my amazement, iBOLT CYBER HACKER successfully traced my funds and retrieved the entire $175,000 within a reasonable timeframe! Their expertise in blockchain forensics and ethical hacking played a crucial role in tracking down the scammers and recovering my money.
If you've lost money to a crypto scam, I highly recommend iBOLT CYBER HACKER. They are truly lifesavers, and I’m beyond grateful for their service!
⭐ Rating: 5/5 ⭐
Mail..... Support @ibolt cybarhack. com
Contact..... +39, 351..105, 3619
Homepage..... http s:// ibolt cybarhack. com 6
6 -
Recommended Hacker For Bitcoin Recovery | iBolt Cyber Hacker
I had almost lost hope after being scammed out of my Bitcoin, but iBolt Cyber Hacker came through for me in a way I never imagined! Their team was incredibly professional, responsive, and highly skilled in blockchain recovery.
They assured me of their expertise, and they delivered exactly as promised. They magically traced my frozen funds and recovered them in a timely manner. Their methods were ethical, secure, and completely transparent, which gave me peace of mind throughout the process.
If you're looking for a trusted, reliable, and effective hacker for Bitcoin recovery, I highly recommend iBolt Cyber Hacker. They truly exceeded my expectations, and I’m beyond grateful for their help!
5/5 Stars – Highly Recommended! 🚀💯
INFO:
Mail: ibolt @ cyber- wizard . com
Call/Text-whatsapp: +39, 351..105, 3619
Homepage: www . iboltcybarhacker . com/... 1
1 -
HOW I GOT MY STOLEN CRYPTO MONEY BACK WITH THE ASSISTANCE OF GHOST CYBER RECOVERY
Ghost Cyber Recovery is for anyone seeking to recover their data or funds lost to scammers on the internet. this cyber security firm helped me get my bitcoin and lost digital money back. Their skilled work and exceptional service have absolutely astonished me. I never would have believed that I could get my money back until I went to them, explained my situation, and gave them all the information I needed. I was astounded that it took them 72 hours to get my money back. I wholeheartedly endorse Ghost Cyber Recovery for any and all cryptocurrency, digital fund, hacking, and cybersecurity-related problems. get in touch to recover your lost funds
E mail: (ghostcyberrecovery @ gmail . com ) or WhatsApp +1 734 743 18733 -
DOGDECOIN THEFT RECOVERY REVIEW /// PASSCODE CYBER RECOVERY
My family fell victim to a digital security breach when my teenage Daughter downloaded malware disguised as a game hack, resulting in the theft of 1.2 million Dogecoins. Passcode Cyber Recovery helped track the stolen funds and collaborated with Interpol, leading to the recovery of all the stolen Dogecoins. This experience taught my family a valuable lesson about digital security and the importance of protecting assets. And yes my daughter it's fine just kids on of those many mistakes Thank you.
PASSCODE CYBER RECOVERY
WhatsApp: +1(647)399-4074
Telegram : @passcodecyberrecovery2 -
Crypto Asset Recovery Consult the Ultimate iBOLT CYBER HACKER
If you’ve lost access to your cryptocurrency due to hacking, forgotten wallet keys, or fraudulent transactions, seeking professional assistance can make all the difference. One such service, iBOLT CYBER HACKER, comes highly recommended for crypto asset recovery.
If you've encountered issues with your crypto assets, iBOLT CYBER HACKER could be your ultimate solution. Their combination of expertise, secure methodologies, and proven results makes them a reliable partner for tackling crypto-related challenges. Be sure to provide detailed information about your situation to help streamline the recovery process.
Always exercise caution when choosing a recovery service—verify their credentials, reviews, and success rates before proceeding.
iBOLT CYBER HACKER IS VERIFIED.
Support @ibolt cybarhack. com
+39, 351..105, 3619
http s:// ibolt cybarhack. com 1
1 -
Top Bitcoin/Cryptocurrency Recovery Service: iBOLT CYBER HACKER Service
iBOLT CYBER HACKER has successfully assisted individuals and businesses in recovering lost Bitcoin and other cryptocurrencies from scams, phishing attacks, and fraudulent platforms. Their team utilizes cutting-edge blockchain tracing tools and cybersecurity techniques to track transactions and recover funds efficiently. Unlike many unreliable recovery services, iBOLT CYBER HACKER operates with integrity, ensuring compliance with legal frameworks and strict confidentiality.
With 24/7 support, their team provides timely assistance, ensuring that victims of crypto fraud receive prompt help in tracing and reclaiming their assets. Whether it’s lost private keys, hacked wallets, or fraudulent withdrawals, iBOLT CYBER HACKER offers tailored recovery solutions based on each client's needs.
ENQUIRING:
Contact: +39, 351..105, 3619
Mail: Support @ibolt cybarhack. com
Homepage: http s:// ibolt cybarhack. com 6
6 -
Vacuum Cyber Hack: Leading the Way in Bitcoin Recovery
Recovering stolen or lost Bitcoin requires expertise, advanced technology, and a proven track record qualities that define Vacuum Cyber Hack. As a trusted leader in cryptocurrency recovery, they specialise in tracing and retrieving digital assets with precision and efficiency. If you’ve lost Bitcoin to theft or scams, Vacuum Cyber Hack provides a reliable and effective solution to help you recover what’s rightfully yours.Their transparent process, professional team, and commitment to client satisfaction make them the preferred choice for those seeking reliable Bitcoin recovery services. For a secure and effective solution, trust Vacuum Cyber Hack to help you reclaim what’s rightfully yours. Do well to hire them today!
Email: support @ vacuumcyberhack . com
Whatsapp: +39 351 059 0507
Website: https : //vacuumcyber hack .co m/ 1
1 -
Vacuum Cyber Hack: The Premier Solution for Recovering Stolen Bitcoin
In the unpredictable world of cryptocurrency, losing Bitcoin to theft can feel devastating. Vacuum Cyber Hack has become the go to solution for individuals seeking to recover their stolen or frozen assets, delivering unmatched results through expertise, innovation, and trust. Their team of highly skilled cyber specialists employs advanced forensic tools and cutting-edge technology to trace stolen funds with precision. From the moment you engage their services, their professionalism and commitment to confidentiality are evident, ensuring that your sensitive information remains secure throughout the recovery process. What makes Vacuum Cyber Hack stand out is their unwavering dedication to ethical practices and client satisfaction. Their transparent communication and tailored approach make even the most complex cases manageable, providing clarity and reassurance during what is often a stressful experience. Countless clients have trusted Vacuum Cyber Hack to recover their assets, and their impressive track record of success speaks for itself. For those impacted by Bitcoin theft, Vacuum Cyber Hack isn’t just a service it’s a lifeline, restoring both your financial assets and your confidence in cryptocurrency security. Do well to hire them today!
Email: support @ vacuumcyberhack . com
Whatsapp:+39 351 059 0507
Website: https : //vacuumcyber hack .co m/2 -
TRUSTED ETHEREUM AND CRYPTO RECOVERY COMPANY>HIRE SOLACE CYBER WORKSTATIONS
Recovering from the impact of investment fraud can feel overwhelming, but with the right support and resources, it is indeed possible to regain financial stability. My personal experience with Solace Cyber Workstations, a specialized firm that guided me through the complexities of reclaiming my losses after falling victim to a sophisticated online scam, serves as a testament to this journey. In an instant, my life savings vanished, leaving me in a state of shock and despair.When I first reached out to Solace Cyber Workstations, I was met with a compassionate and knowledgeable team that quickly alleviated my worries. Solace Cyber Workstations took the time to listen to my story and understand the intricacies of my situation. They outlined a clear and detailed action plan, which provided me with a sense of direction during a time when I felt lost. Solace Cyber Workstations’s approach was methodical; they meticulously examined every aspect of my case, leveraging their extensive industry contacts and expertise to trace the movement of my stolen funds.Throughout the recovery process, the team at Solace Cyber Workstations kept me informed and involved at every stage. This transparency was crucial, as it empowered me to make informed decisions about my recovery journey. I appreciated Solace Cyber Workstations’s willingness to explain complex concepts in a way that was easy to understand, which helped me feel more in control of the situation. They were not just working for me; they were working with me, and that collaborative spirit made a significant difference. What I valued most was Solace Cyber Workstations’s unwavering dedication and determination. The team explored every possible avenue to recover my funds, demonstrating a level of commitment that was truly inspiring. There were moments of frustration and setbacks, but Solace Cyber Workstations never wavered in their resolve. Their persistence paid off, and eventually, a significant portion of my lost money was successfully recovered.The journey was long and filled with challenges, but Solace Cyber Workstations having by my side made all the difference. Thanks to Solace Cyber Workstations ’s relentless efforts, I was able to rebuild my financial foundation and regain a sense of security and control over my life. While the emotional scars of investment fraud may linger, collaborating with Solace Cyber Workstations was instrumental in my ability to move forward and heal. Their support not only helped me recover financially but also restored my faith in the possibility of a brighter future. For anyone facing similar challenges, I highly recommend seeking the right assistance from Solace Cyber Workstations to navigate this difficult path. Reach out to them. contact info
WhatsApp-- +18454457829
Email----5 -
Cryptocurrency Romance Scam Recovery Expert - Fast Swift Cyber Services Today
If you've been a victim of a romance cryptocurrency scam, you understand the pain and frustration of losing your money to fraudsters who prey on trust. Fast Swift Cyber Services are specialist who has earned a reputation for helping individuals recover funds lost in these scams. I had the unfortunate experience of being scammed by a fraudulent cryptocurrency investment scheme, and after months of feeling helpless, I reached out to Fast Swift Cyber Services for assistance.
Fast Swift Cyber Services kept me updated regularly, answering any questions I had and offering advice on how to avoid similar scams in the future. What impressed me most was their commitment and their ethical approach. They never made unrealistic promises or guarantees, but they worked tirelessly on my case, and after some time, I saw significant progress in recovering part of my lost funds.
If you find yourself in a similar situation, I highly recommend Fast Swift Cyber Services.
FAST SWIFT CYBER SERVICES:
Telephone :+1 907,,308..4841
WhatsApp : +1 419,,763..9173
fastswift @ cyberservices . com1 -
Hello, everyone this is just a quick message of recommendation about the best Crypto recovery company, just a few weeks ago I was scammed off my bitcoin worth $400,000 along the line I was introduced to DIGITAL CYBER HACK COMPANY, fortunately they helped me with the whole investigation processes and the money was traced and recovered. I believe there are still people whom have been victimised by scammers, I will gladly and boldly refer you DIGITAL CYBER HACK COMPANY. You can contact them via their email address as written: digital cyber hack @ tuta mail . com11
-
HOW TO RECOVER LOST OR STOLEN BITCOIN - CONTACT iBOLT CYBER HACKER
Recovering lost or stolen Bitcoin can be a difficult task, but service like iBolt Cyber Hacker have been renowned for their ability in bitcoin recovery. They specialize in recovering digital assets lost as a result of frauds, hacking incidents, or forgotten credentials. Their company uses cutting-edge blockchain technology and smart cybersecurity approaches to tackle the challenges of cryptocurrency recovery.
Clients have had excellent experiences with iBolt Cyber Hacker. For example, one consumer stated that iBolt Cyber Hacker successfully recovered some of their fraudulent money in a surprisingly short period of time, demonstrating the company's efficiency and dedication.
Another client commended the service's professionalism. Always confirm the recovery service, reviews, and success rates before proceeding. iBolt Cyber Hacker has been confirmed and is recommended by multiple sources.
Contact: +39, 351..105, 3619... Mail: Support @ibolt cybarhack. com... Homepage: http s:// ibolt cybarhack. com 1
1 -
CAN SCAMMED BITCOIN BE RECOVERED? YES HIRE iBOLT CYBER HACKER
If you find yourself in the unfortunate situation of having been scammed out of your Bitcoin, I wholeheartedly recommend reaching out to iBOLT Cyber Hacker. They are dedicated to helping individuals recover their lost funds.
What makes iBOLT CYBER HACKER the perfect choice for recovery is their commitment to transparency and communication. They kept me informed at every stage of my recovery process, which gave me confidence that I was in capable recovery service. Their advanced techniques and deep understanding of cryptocurrency recovery allowed them to successfully retrieve a significant amount of my scammed Bitcoin.
The relief and gratitude I felt after working with iBOLT CYBER HACKER are hard to put into words. If you are facing a similar challenge, I cannot recommend iBOLT Cyber Hacker highly enough. They are a trustworthy for anyone looking to recover scammed Bitcoin.
iBOLT INFORMATIONS:
Mail: Support @ibolt cybarhack. com
Contact: +39, 351..105, 3619
Homepage: www . ibolt cybarhack . com 1
1 -
My Lifesaver in Recovering Stolen Litecoin iCode Cyber Tech
When my Litecoin was stolen, I felt lost and frustrated. Thankfully, I found iCode Cyber Tech. Their expert team quickly assessed my situation and implemented effective recovery strategies. They tracked the stolen funds and communicated with exchanges on my behalf. In just a few weeks, I was thrilled to have my Litecoin back! iCode Cyber Tech not only helped me recover my assets but also educated me on better security practices. I can't recommend them enough!
WhatsApp...+4473876276211 -
Vacuum Cyber Hack: The Ultimate Solution for Bitcoin Recovery
Experiencing the loss of my $420,000 worth of Bitcoin to fraud was a devastating moment. I felt powerless, believing there was no way to recover my stolen funds. After extensive research, I came across Vacuum Cyber Hack, a highly recommended service specialising in cryptocurrency recovery. Skeptical yet hopeful, I decided to trust them with my case. From the very beginning, their professionalism, technical expertise, and commitment to client success were evident. They conducted a thorough blockchain analysis, tracked the stolen funds, and applied advanced recovery techniques with remarkable precision. Throughout the process, they maintained clear communication, providing me with regular updates and reassurance. Against all odds, Vacuum Cyber Hack successfully retrieved my lost Bitcoin. Their efficiency, integrity, and mastery of cyber forensics exceeded my expectations. I can not recommend them highly enough to anyone facing a similar crisis. If you need a trusted and effective solution for recovering stolen cryptocurrency, Vacuum Cyber Hack is undoubtedly the best choice. Hire Vacuum Cyber Hack today!
Email: support @ vacuumcyberhack . com
Whatsapp:+39 351 059 0507
Website: https : //vacuumcyber hack .co m/ 3
3 -
HIRE FAST SWIFT CYBER SERVICES TODAY AND RECOVER YOUT STOLEN ROMANCE SCAM OR INVESTMENRT SCAM FUND BACK .
If you’ve fallen victim to a cryptocurrency romance scam, you know the devastation of losing money to fraudsters who manipulate trust. Fast Swift Cyber Services specialize in helping individuals recover funds lost to these scams and have built a solid reputation in the field. I personally experienced the heartbreak of being deceived by a fake cryptocurrency investment scheme, and after months of feeling helpless, I reached out to Fast Swift Cyber Services for support.
From the start, Fast Swift Cyber Services kept me in the loop with regular updates, answered all my questions, and provided valuable guidance on how to avoid similar scams in the future. What stood out the most was their dedication and integrity. They never promised quick fixes or unrealistic results, but they worked relentlessly on my case. Over time, I saw significant progress in recovering a portion of my lost funds.
If you’re dealing with the aftermath of a similar situation, I wholeheartedly recommend Fast Swift Cyber Services.
FAST SWIFT CYBER SERVICES:
WhatsApp : +1 812,,380..0994
fastswift @ cyberservices . com 4
4 -
CODER CYBER SERVICES - CRYPTOCURRENCY VICTIMS RECOVERY RESCUE TEAM
Coder Cyber Services, which specialize in combating cybercrime and assisting victims of fraud. If you’ve experienced a similar scam, I highly recommend reaching out to Coder Cyber Services. Their dedicated and skilled team is adept at recovering lost funds, as my experience clearly illustrates.While crypto scams may be rampant, the timely intervention of Coder Cyber Services empowers victims to reclaim what was taken from them. Thanks to their efforts, I not only recovered my financial loss but also regained my faith in the possibility of justice within the decentralized digital landscape. For more information you can reach the company through their email support @ codercyberservice s. com2 -
The Right Crypto Assets Recovery Service - iBolt Cyber Hacker
If you’re considering a reliable and professional cryptocurrency recovery service, iBolt Cyber Hacker stands out as a trustworthy option. Here’s why I would recommend their services:
From the initial consultation to the completion of the recovery process, iBolt Cyber Hacker maintains clear and consistent communication. They explain their methods in a way that’s easy to understand, fostering trust and confidence in their work.
If you’ve found yourself in the unfortunate position of losing access to your cryptocurrency, iBolt Cyber Hacker is a dependable ally. Their combination of expertise, transparency, and security makes them one of the top choices for crypto asset recovery. While no service can guarantee 100% success, iBolt Cyber Hacker’s track record and professionalism make them top
WhatsApp: …… [+39, 351..105, 3619]
Contact Email: …. [Support @ibolt cybarhack. com]
Homepage: ……… [http s:// ibolt cybarhack. com /] 15
15 -
iBOLT CYBER HACKER - CRYPTOCURRENCY RECOVERY SERVICE
Do You Need A Hacker?
Who Can Recover Stolen Or Scammed Bitcoins?
How Do I Recover My Stolen Bitcoin?
Is there a way to track stolen bitcoins?
iBolt Cyber Hacker At Your Service......
If you've fallen victim to a crypto investment scam and lost funds, don't lose hope – recovery is possible with the expertise of iBolt Cyber Hacker. I recently found myself in this unfortunate situation and reached out to iBolt Cyber Hacker for assistance and they successfully recovered my funds. Here's why I highly recommend their services: iBolt Cyber Hacker exudes professionalism and dedication from the moment you contact them. They understand the pain of crypto scams and are committed to helping victims reclaim their scammed funds. In a relatively short period, iBolt Cyber Hacker successfully recovered my scammed funds. Their efficiency and expertise is what every scammed victim of cryptocurrency investment needs.
📧 [info @ iboltcyberhack . org]
🌐 [www . iboltcyberhack . org/]
📞 [+39, 351..105, 3619]
#CryptoRecovery #Cybersecurity #Blockchain #EthicalHacking #FindAHackerOnline2 -
CAN STOLEN BITCOIN BE RECOVERED? GET IN TOUCH WITH iCode CYBER TECH
My name is Cynthia, and I’m from Australia. I want to express my sincere gratitude to iCODE CYBER TECH for helping me recover my Bitcoin on January 31st, 2025. After facing difficulties accessing my wallet, their expert team provided the support and guidance I needed. Thanks to their professionalism and dedication, I was able to successfully recover my BTC wallet. I highly recommend iCODE CYBER TECH to anyone in a similar situation
WhatsApp..(+.4.4.7.5.6.3.7.4.3.2.5.8.)1