Join devRant
Do all the things like
++ or -- rants, post your own rants, comment on others' rants and build your customized dev avatar
Sign Up
Pipeless API

From the creators of devRant, Pipeless lets you power real-time personalized recommendations and activity feeds using a simple API
Learn More
Search - "thanks for my password"
-
I had a secondary Gmail account with a really nice short nickname (from the early invite/alpha days), forwarded to another of my mailboxes. It had a weak password, leaked as part of one of the many database leaks.
Eventually I noticed some dude in Brazil started using my Gmail, and he changed the password — but I still got a copy of everything he did through the forwarding rule. I caught him bragging to a friend on how he cracked hashes and stole and sold email accounts and user details in bulk.
He used my account as his main email account. Over the years I saw more and more personal details getting through. Eventually I received a mail with a plaintext password... which he also used for a PayPal account, coupled to a Mastercard.
I used a local website to send him a giant expensive bouquet of flowers with a box of chocolates, using his own PayPal and the default shipping address.
I included a card:
"Congratulations on acquiring my Gmail account, even if I'm 7 years late. Thanks for letting me be such an integral part of your life, for letting me know who you are, what you buy, how much you earn, who your family and friends are and where you live. I've surprised your mother with a cruise ticket as you mentioned on Facebook how sorry you were that you forgot her birthday and couldn't buy her a nice present. She seems like a lovely woman. I've also made a $1000 donation in your name to the EFF, to celebrate our distant friendship"31 -
And here comes the last part of my story so far.
After deploying the domain, configuring PCs, configuring the server, configuring the switch, installing software, checking that the correct settings have been applied, configuring MS Outlook (don't ask) and giving each and every user a d e t a i l e d tutorial on using the PC like a modern human and not as a Homo Erectus, I had to lock my door, put down my phone and disconnect the ship's announcement system's speaker in my room. The reasons?
- No one could use USB storage media, or any storage media. As per security policy I emailed and told them about.
- No one could use the ship's computers to connect to the internet. Again, as per policy.
- No one had any games on their Windows 10 Pro machines. As per policy.
- Everyone had to use a 10-character password, valid for 3 months, with certain restrictions. As per policy.
For reasons mentioned above, I had to (almost) blackmail the CO to draft an order enforcing those policies in writing (I know it's standard procedure for you, but for the military where I am it was a truly alien experience). Also, because I never trusted the users to actually backup their data locally, I had UrBackup clone their entire home folder, and a scheduled task execute a script storing them to the old online drive. Soon it became apparent why: (for every sysadmin this is routine, but this was my first experience)
- People kept deleting their files, whining to me to restore them
- People kept getting locked out because they kept entering their password WRONG for FIVE times IN a ROW because THEY had FORGOTTEN the CAPS lock KEY on. Had to enter three or four times during weekend for that.
- People kept whining about the no-USB policy, despite offering e-mail and shared folders.
The final straw was the updates. The CO insisted that I set the updates to manual because some PCs must not restart on their own. The problem is, some users barely ever checked. One particular user, when I asked him to check and do the updates, claimed he did that yesterday. Meanwhile, on the WSUS console: PC inactive for over 90 days.
I blocked the ship's phone when I got reassigned.
Phiew, finally I got all those off my chest! Thanks, guys. All of the rants so far remind me of one quote from Dave Barry: 7
7 -
I was 15 years old and the first year of high school. Everything was new to me and I was such a newbie. At that time I had 2-3 year of programming behind me at an institution where they taught competitive programming. And I knew something about computers. Not much but more than most of my school mates. At that time I wanted to become "super cool hacker".
So we had this very very thought teacher for history which was also our form master. She really knows how to explained everything about history and in an interesting way. But while she was teaching we also had to write down notes from her powerpoints that were on a projector. And occasionally she would wait for us to copy everything and then move on with her lecture. But sometimes she didn't. This was frustrating as hell. The whole class would complain about this because you couldn't take notes down normal, you had to do it at double speed.
But she got one weak spot. She was not very good with computers. Our school computers were locked in some kinda closet so that students didn't have physical access to a computer and were also password protected. So I came up with the plan to plant wireless mouse in her computer so that I could control her mouse. At that time it seemed like SUPER HACKER MASTER PLAN.
So I got an opportunity one time when she left the classroom and let closet where the computer was open. I quickly sneaked the USB of the wireless mouse in the computer and then go back to the seat.
So THE FUN began.
Firstly I would only go back in powerpoint so that all my schoolmates could write down notes including me. And it was hilarious to watch when she didn't know what is happening. So then I would move her mouse when she tried to close some window. I would just move it slightly so she wouldn't notice that somebody else is controlling mouse. And by missing X button just by slight she would click other things and other things would pop up and now she had to close this thing so it became a nightmare for her. And she would become angry at the mouse and start complaining how the computer doesn't work and that mouse doesn't obey her.
One time when she didn't pay attention to her computer and projector I went to paint program and drew a heart and wrote we love you (In Slovenian Imamo vas radi -> See the picture below) and one of my school mates has the picture of it. We were all giggling and she didn't know what is was for. And I managed to close everything before she even noticed.
So it got to the point where she couldn't hand it more so she called our school IT guy so that he would check her computer (2 or 3 weeks passed before she called IT guy). And he didn't find anything. He was really crappy IT guy in general. So one week passed by and I still had messed with her mouse. So she got a replacement computer. Who would guessed all the problems went away (because I didn't have another mouse like that). I guess when our IT guy took the computer to his room and really thoroughly check it he found my USB.
So he told her what was the problem she was so pissed off really I didn't see her pissed off so much in all my 4 years in high school. She demanded the apology from whom did it. And at that moment my mind went through all possible scenarios... And the most likely one was that I was going to be expelled... And I didn't have the balls to say that I did it and I was too afraid... Thanks to God nobody from my school mates didn't tell that it was me.
While she waited that somebody would come forward there was one moment when our looks met and at that moment both of us knew that I was the one that did it.
Next day the whole class wrote the apology letter and she accepted it. But for the rest of 4 years whenever was there a problem with the computer I had to fixed it and she didn't trust anybody not even our IT guy at school. It was our unwritten contract that I would repair her computer to pay off my sin that I did. And she once even trusted me with her personal laptop.
So to end this story I have really high respect for her because she is a great teacher and great persons that guide me through my teen years. And we stayed in contact.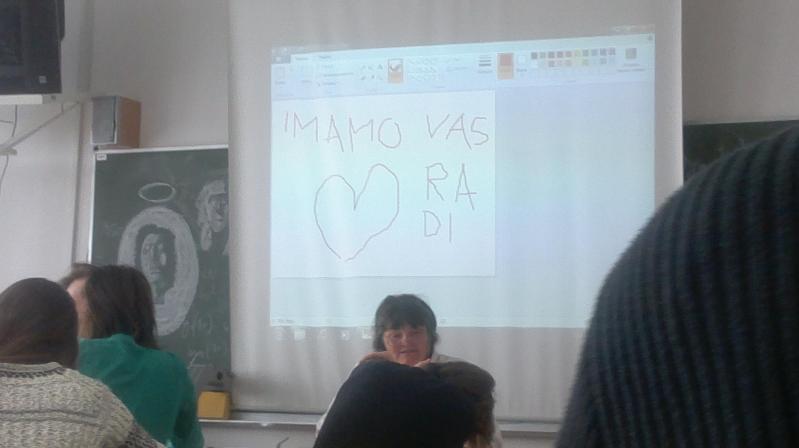 11
11 -
I suddenly remembered this after being gone from my previous company for nearly a year.
So, I worked there as a tech supporter and Linux engineer.
What would often happen was clients calling with an issue regarding software of some sorts and about half the time, instead of LOOKING AT THE GODDAMN ERROR MESSAGE they'd just click it away fast and complain shit wasn't working.
I specifically remember this one case:
*big client mails complained that one of their clients' email isn't working. Screenshots weren't possible apparently so after emailing back and forth for way too long, we decide to do a screen sharing session (which we never do).*
(for the record, already emailing for hours, client very frustrated, me as well because the behavior of the software sounds impossible)
Me: alright, close everything, then open it again so I can see what happens.
Client: *opens mail client, error appears, client clicks error away faster than an arch user being able to mention they use arch*
Me: uhm.... I assume you already know what that message said and that it has nothing to do with the issue?
Client: it has nothing to do with the issue.
Me: okay... But have you at least looked the message?
Client: no but it has nothing to do with the issue.
Me: but, how'd you know if you won't look at it?
Client: it has nothing to do with the issue, okay?
Me: okay.... so, what's happening here?
Client: the user isn't receiving email anymore at this point!
Me: alright, have you checked the settings and everything?
Client: of course, all good
Me: okay but can we at least restart the software again to at least check the error message?
Client: FINE. *restarts client (pun intended, of course)*
Error message: username or password incorrect, can't connect to the server.
Client:..........
Client:............
Client:...............
Client:..................
Client:.....................
Client:..................
Client:...............
Client:............
Client:.........
Client: 😐
Client: 😶
Client: 😅
Client: 😬
Client:..... Right, I changed the password...
Client: *sets correct password*
*poof, error message gone*
Client:..... Thanks 💀
Me: you're welcome 😄
💀3 -
!rant
I was in a hostel in my high school days.. I was studying commerce back then. Hostel days were the first time I ever used Wi-Fi. But it sucked big time. I'm barely got 5-10Kbps. It was mainly due to overcrowding and download accelerators.
So, I decided to do something about it. After doing some research, I discovered NetCut. And it did help me for my purposes to some extent. But it wasn't enough. I soon discovered that my floor shared the bandwidth with another floor in the hostel, and the only way I could get the 1Mbps was to go to that floor and use NetCut. That was riskier and I was lazy enough to convince myself look for a better solution rather than go to that floor every time I wanted to download something.
My hostel used Netgear's routers back then. I decided to find some way to get into those. I tried the default "admin" and "password", but my hostel's network admin knew better than that. I didn't give up. After searching all night (literally) about how to get into that router, I stumbled upon a blog that gave a brief info about "telnetenable" utility which could be used to access the router from command line. At that time, I knew nothing about telnet or command line. In the beginning I just couldn't get it to work. Then I figured I had to enable telnet from Windows settings. I did that and got a step further. I was now able to get into the router's shell by using default superuser login. But I didn’t know how to get the web access credentials from there. After googling some and a bit of trial and error, I got comfortable using cd, ls and cat commands. I hoped that some file in the router would have the web access credentials stored in cleartext. I spent the next hour just using cat to read every file. Luckily, I stumbled upon NVRAM which is used to store all config details of router. I went through all the output from cat (it was a lot of output) and discovered http_user and http_passwd. I tried that in the web interface and when it worked, my happiness knew no bounds. I literally ran across the floor screaming and shouting.
I knew nothing about hiding my tracks and soon my hostel’s admin found out I was tampering with the router's settings. But I was more than happy to share my discovery with him.
This experience planted a seed inside me and I went on to become the admin next year and eventually switch careers.
So that’s the story of how I met bash.
Thanks for reading!10 -
Thanks, I am happy to be sharing my payment details with your company.
ATTACHED TO THE LOGIN DETAILS YOU EMAILED ME! 3
3 -
Hello!
I'm a member of an international hacker group.
As you could probably have guessed, your account [cozyplanes@tuta.io] was hacked, because I sent message you from it.
Now I have access to you accounts!
For example, your password for [cozyplanes@tuta.io] is [RANDOM_ALPHABET_HERE]
Within a period from July 7, 2018 to September 23, 2018, you were infected by the virus we've created, through an adult website you've visited.
So far, we have access to your messages, social media accounts, and messengers.
Moreover, we've gotten full damps of these data.
We are aware of your little and big secrets...yeah, you do have them. We saw and recorded your doings on porn websites. Your tastes are so weird, you know..
But the key thing is that sometimes we recorded you with your webcam, syncing the recordings with what you watched!
I think you are not interested show this video to your friends, relatives, and your intimate one...
Transfer $700 to our Bitcoin wallet: 13DAd45ARMJW6th1cBuY1FwB9beVSzW77R
If you don't know about Bitcoin please input in Google "buy BTC". It's really easy.
I guarantee that after that, we'll erase all your "data" :)
A timer will start once you read this message. You have 48 hours to pay the above-mentioned amount.
Your data will be erased once the money are transferred.
If they are not, all your messages and videos recorded will be automatically sent to all your contacts found on your devices at the moment of infection.
You should always think about your security.
We hope this case will teach you to keep secrets.
Take care of yourself.
>> RE >>
Well f### you, thanks for telling my password which is obviously fake. I have sent your details to the local police department, shall rest in peace. Don't earn money by this kind of action. STUPID!14 -
I really, honestly, am getting annoyed when someone tells me that "Linux is user-friendly". Some people seem to think that because they themselves can install Linux, that anyone can, and because I still use Windows I'm some sort of a noob.
So let me tell you why I don't use Linux: because it never actually "just works". I have tried, at the very least two dozen times, to install one distro or another on a machine that I owned. Never, not even once, not even *close*, has it installed and worked without failing on some part of my hardware.
My last experience was with Ubuntu 17.04, supposed to have great hardware and software support. I have a popular Dell Alienware machine with extremely common hardware (please don't hate me, I had a great deal through work with an interest-free loan to buy it!), and I thought for just one moment that maybe Ubuntu had reached the point where it just, y'know, fucking worked when installing it... but no. Not a chance.
It started with my monitors. My secondary monitor that worked fine on Windows and never once failed to display anything, simply didn't work. It wasn't detected, it didn't turn on, it just failed. After hours of toiling with bash commands and fucking around in x conf files, I finally figured out that for some reason, it didn't like my two IDENTICAL monitors on IDENTICAL cables on the SAME video card. I fixed it by using a DVI to HDMI adapter....
Then was my sound card. It appeared to be detected and working, but it was playing at like 0.01% volume. The system volume was fine, the speaker volume was fine, everything appeared great except I literally had no fucking sound. I tried everything from using the front output to checking if it was going to my display through HDMI to "switching the audio sublayer from alsa to whatever the hell other thing exists" but nothing worked. I gave up.
My mouse? Hell. It's a Corsair Gaming mouse, nothing fancy, it only has a couple extra buttons - none of those worked, not even the goddamn scrollwheel. I didn't expect the *lights* to work, but the "back" and "Forward" buttons? COME ON. After an hour, I just gave up.
My media keyboard that's like 15 years old and is of IBM brand obviously wasn't recognized. Didn't even bother with that one.
Of my 3 different network adapters (2 connectors, one wifi), only one physical card was detected. Bluetooth didn't work. At this point I was so tired of finding things that didn't work that I tried something else.
My work VPN... holy shit have you ever tried configuring a corporate VPN on Linux? Goddamn. On windows it's "next next next finish then enter your username/password" and on Linux it's "get this specific format TLS certificate from your IT with a private key and put it in this network conf and then run this whatever command to...." yeah no.
And don't get me started on even attempting to play GAMES on this fucking OS. I mean, even installing the graphic drivers? Never in my life have I had to *exit the GUI layer of an OS* to install a graphic driver. That would be like dropping down to MS-DOS on Windows to install Nvidia drivers. Holy shit what the fuck guys. And don't get me started on WINE, I ain't touching this "not an emulator emulator" with a 10-foot pole.
And then, you start reading online for all these problems and it's a mix of "here are 9038245 steps to fix your problem in the terminal" and "fucking noob go back to Windows if you can't deal with it" posts.
It's SO FUCKING FRUSTRATING, I spent a whole day trying to get a BASIC system up and running, where it takes a half-hour AT MOST with any version of Windows. I'm just... done.
I will give Ubuntu one redeeming quality, however. On the Live USB, you can use the `dd` command to mirror a whole drive in a few minutes. And when you're doing fucking around with this piece of shit OS that refuses to do simple things like "playing audio", `dd` will restore Windows right back to where it was as if Ubuntu never existed in the first place.
Thanks, `dd`. I wish you were on Windows. Your OS is the LEAST user friendly thing I've ever had to deal with.32 -
!dev
GOD FUCKING DAMMIT
My Mother was intelligent enough to get her phone stolen and screams at me over the phone of my brother why I can't do more than telling her the last known location
BECAUSE THEY SHUT IT DOWN
I CAN'T DO SHIT WITHOUT THE PHONE HAVING AN INTERNET CONNECTION
But what if they go through my files go into my bank account
THEY CAN'T BECAUSE YOU HAVE A PASSWORD ON IT
but they could crack it or something
NO THEY CAN'T WITHOUT TRYING FOR MONTHS OR YEARS OF POSSIBLE COMBINATIONS
but
NO BUT JUST FUCKING CALM DOWN IF THEY AREN'T THAT BAD THEN THEY WILL CALL ME IF THEY ARE ASSHOLES THEY NEED AT LEAST MAKE A FACTORY RESET AND DELETE ALL YOUR FILES
I CAN'T DO MORE THAN THIS SO FUCKING SHUT UP AND DON'T LEAVE YOUR PHONE AT A FUCKING WAITING ROOM AND DON'T BELIEVE EVERYTHING ON THE FUCKING INTERNET ESPECIALLY FACEBOOK
Thanks know I can't concentrate anymore........5 -
Well, i have a few stories i would like to share with you :)
My neighbour asked me to fix her webcam.
I told her: But I am a programmer, not a repair service .
Next time my neighbour forgot her Skype password. Se asked me to hack it for her.
I told her: But I am a programmer, not a hacker.
My sister asked me to help her out in her program, because of some bug. Well, she is in the other part of the Country. But, i said, lets give it a try.
Well, it turned out to be some kind of mechanical remote scanner, with needed that exact same remote locally.
I told her: But I am a programmer, not a fictional remote signal scanner repairer.
My grandpa asked me, to copy his old gmail emails into his new laptop.
Well, i told him to log in. He logged in. Than i told him: It is done :D
Thanks for reading it :)4 -
Discord and captchas can go get fucked in the ass by a rusty, tetanus ridden 2m pole....
I changed my discord-password yesterday and, naturally it prompted me for a login today. So I enter my new password and that motherfucking spawn from satans anus himself with the name of captcha threw itself at me... I seriously had to select fucking street signs for about 5min before Discord let me know that I apparently logged in from a new IP (thanks VPN) and therefore needed to confirm my e-Mail address. Alright, so off to my inbox I go.
SURPRISE, I also changed my password there yesterday (LastPass Security Challenge, I changed like 30 passwords yesterday) and guess what was waiting for me?... If you guessed a captcha, you just got full fucking marks. So I was busy selecting busses and streets for the next 3min again before I could finally log into that piece of trash and autorize my IP-address and log into Discord6 -
Thanks to mandatory password change, today:
- My windows account got locked because my phone kept logging into wifi using
old password.
- Google Hangouts were silently running in background with old session until I re-opened it. Work of others delayed by 4 hours due to missing message notifications.
- Docker for Windows lost credentials needed to use SMB mounts - 1h of debugging why my containers mount empty folders ( now I will know)
- Google G-Sync for Outlook asked for new password on outlook restart - few mails delayed.
All of that for sake of security that could be easily solved with 2FA instead, not faking that "I do not change number at the end of my password" -
tldr; Windows security sucks. You as a org-admin cant do anything about it. Encrypt your device. Disable USB Live boot in the bios and protect it with a STRONG password.
First of i just want to say that i DO NOT want to start the good ol' Linux VS Windows debate. I'm just ranting about Windows Security here...
Second, here's why i did all of this. I did all of this mainly becuase i wanted to install some programs on my laptop but also to prove that you can't lock down a Windows pc. I don't recomend doing this since this is against the contract i signed.
So when i got my Laptop from my school i wanted to install some programs on it, sush as VS Code and Spotify. They were not avalible in the 'Software Center' so i had to find another way. Since this was when we still used Windows 7 it was quite easy to turn sticky keys in to a command prompt. I did it this way (https://github.com/olback/...). I decided to write a tutorial while i was at it becuase i didn't find any online using this exact method. I couldn't boot from a USB cause it's disabled in the bios wich is protected by a password. Okey, Sticky keys are now CMD. So let's spam SHIFT 5 times before i log in? Yeah, thanks for the command promt. Running 'whoami' returned 'NT SYSTEM'. Apparantly NT System has domain administator rights wich allowed me to make me an Administrator on the machine. So i installed Everything i wanted, Everything was fine untill it was time to migrate to a new domain. It failed of course. So i handed my Laptop to the IT retards (No offense to people working in IT and managing orgs) and got it back the day after, With Windows 10. Windows 10 is not really a problem, i don't mind it. The thing is, i can't use any of the usual Sticky keys to CMD methods since they're all fixed in W10. So what did i do? Moved the Laptop disk to my main PC and copied cmd.exe to sethc.exe. And there we go again. CMD running as NT System on Windows 10. Made myself admin again, installed Everything i needed. Then i wanted to change my wallpaper and lockscreen, had to turn to PowerShell for this since ALL settings are managed by my School. After some messing arround everything is as i want it now.
'Oh this isnt a problem bla bla bla'. Yes, this is a problem. If someone gets physical access your PC/Laptop they can gain access to Everything on it. They can change your password on it since the command promt is running as NT SYSTEM. So please, protect your data and other private information you have on your pc. Encypt your machine and disable USB Live boot.
Have a good wekend!
*With exceptions for spelling errors and horrible grammar.4 -
TL;DR: Google asked me to PROVIDE a phone number to verify connection from a new device, on the said device.
Yesterdayto log into my work Google account from my personal laptop to check emails, calendars update and so on. I opened up a private navigation window, went to Google sign-in page, entered my credentials, all is well.
Google then decided to "verify it's me" and prompted me to PROVIDE a phone number (work account without work phone means no phone number set up) so that they can send a verification code to the number I just provided to make sure the connection is legit.
Didn't want to do that, clicked "use another method" and got asked to fill the last password I remember, which would be my current password thanks to my trusty password manager. After submitting, I'm prompted with an error saying I have to contact my admin to reset my password because they can't log me in with my CURRENT password.
I ain't gonna do that, so went back to login page, provided my phone number, got the code, filled in the code, next thing I know I'm browsing through my emails.
What the duck? Could have been anybody giving any phone number. So much for extra security.
Also don't care that they have my phone number, the issue is more about the way used to obtain it: locking me out of my account and having no other way of logging in.6 -
tldr: Fuck Apple AND Microsoft...
Tried to check my "me" email today (iCloud)... and well it's apparently "locked" for god only knows what reason, and they will only let me recover it through a Hotmail account that I haven't used in >10years.. So I tried that and after one login attempt outlook.com is telling me "you've entered too many wrong password attempts, you must reset your password"... ugh OK, so I hit the button and it's asking me "my" security question.. 'where did you and your spouse meet?'.. wtf? I'm not married now nor was I @12yrs old when I made this account....
Well thanks so I guess that's fucked for forever...7 -
Not as much of a rant as a share of my exasperation you might breathe a bit more heavily out your nose at.
My work has dealt out new laptops to devs. Such shiny, very wow. They're also famously easy to use.
.
.
.
My arse.
.
.
.
I got the laptop, transferred the necessary files and settings over, then got to work. Delivered ticket i, delivered ticket j, delivered the tests (tests first *cough*) then delivered Mr Bullet to Mr Foot.
Day 4 of using the temporary passwords support gave me I thought it was time to get with department policy and change my myriad passwords to a single one. Maybe it's not as secure but oh hell, would having a single sign-on have saved me from this.
I went for my new machine's password first because why not? It's the one I'll use the most, and I definitely won't forget it. I didn't. (I didn't.) I plopped in my memorable password, including special characters, caps, and numbers, again (carefully typed) in the second password field, then nearly confirmed. Curiosity, you bastard.
There's a key icon by the password field and I still had milk teeth left to chew any and all new features with.
Naturally I click on it. I'm greeted by a window showing me a password generating tool. So many features, options for choosing length, character types, and tons of others but thinking back on it, I only remember those two. I had a cheeky peek at the different passwords generated by it, including playing with the length slider. My curiosity sated, I closed that window and confirmed that my password was in.
You probably know where this is going. I say probably to give room for those of you like me who certifiably. did. not.
Time to test my new password.
*Smacks the power button to log off*
Time to put it in (ooer)
*Smacks in the password*
I N C O R R E C T L O G I N D E T A I L S.
Whoops, typo probably.
Do it again.
I N C O R R E C T L O G I N D E T A I L S.
No u.
Try again.
I N C O R R E C T L O G I N D E T A I L S.
Try my previous password.
Well, SUCCESS... but actually, no.
Tried the previous previous password.
T O O M A N Y A T T E M P T S
Ahh fuck, I can't believe I've done this, but going to support is for pussies. I'll put this by the rest of the fire, I can work on my old laptop.
Day starts getting late, gotta go swimming soonish. Should probably solve the problem. Cue a whole 40 minutes trying my 15 or so different passwords and their permutations because oh heck I hope it's one of them.
I talk to a colleague because by now the "days since last incident" counter has been reset.
"Hello there Ryan, would you kindly go on a voyage with me that I may retrace my steps and perhaps discover the source of this mystery?"
"A man chooses, a slave obeys. I choose... lmao ye sure m8, but I'm driving"
We went straight for the password generator, then the length slider, because who doesn't love sliding a slidey boi. Soon as we moved it my upside down frown turned back around. Down in the 'new password' and the 'confirm new password' IT WAS FUCKING AUTOCOMPLETING. The slidey boi was changing the number of asterisks in both bars as we moved it. Mystery solved, password generator arrested, shit's still fucked.
Bite the bullet, call support.
"Hi, I need my password resetting. I dun goofed"
*details tech support needs*
*It can be sorted but the tech is ages away*
Gotta be punctual for swimming, got two whole lengths to do and a sauna to sit in.
"I'm off soon, can it happen tomorrow?"
"Yeah no problem someone will be down in the morning."
Next day. Friday. 3 hours later, still no contact. Go to support room myself.
The guy really tries, goes through everything he can, gets informed that he needs a code from Derek. Where's Derek? Ah shet. He's on holiday.
There goes my weekend (looong weekend, bank holiday plus day flexi-time) where I could have shown off to my girlfriend the quality at which this laptop can play all our favourite animé, and probably get remind by her that my personal laptop has an i2350u with integrated graphics.
TODAY. (Part is unrelated, but still, ugh.)
Go to work. Ten minutes away realise I forgot my door pass.
Bollocks.
Go get a temporary pass (of shame).
Go to clock in. My fob was with my REAL pass.
What the wank.
Get to my desk, nobody notices my shame. I'm thirsty. I'll have the bottle from my drawer. But wait, what's this? No key that usually lives with my pass? Can't even unlock it?
No thanks.
Support might be able to cheer me up. Support is now for manly men too.
*Knock knock*
"Me again"
"Yeah give it here, I've got the code"
He fixes it, I reset my pass, sensibly change my other passwords.
Or I would, if the internet would work.
It connects, but no traffic? Ryan from earlier helps, we solve it after a while.
My passwords are now sorted, machine is okay, crisis resolved.
*THE END*
If you skipped the whole thing and were expecting a tl;dr, you just lost the game.
Otherwise, I absolve you of having lost the game.
Exactly at the char limit9 -
They've been in a meeting with some clients the whole morning.
12PM, time for me to go. Say Happy New Year and am on my way home.
12:20 Got home, took shirt off, got something to eat from the fridge.
12:22 Bit the first slice of pizza. Phone rings.
- "Yo' we wanted to show them app 2 but I can't log in."
+ "I left the laptop (and the whole dev environment) there, and there's no PC on in my house (and no dev environment whatsoever)."
- "Well check with your phone. [SIC] Tell me when you fix it."
12:32 I had turned my personal computer on; checked the problem was what I imagined (unpkg lib with no version defined on the link had a new major/non-retrocompatible version); grabbed an online FTP tool; remembered IP, user & password; edited the single line that caused the problem; and checked it worked. Calling back.
+ "It's fixed."
- "Thanks!"
12:38 CEO sent me an image of the app not working, due to a known bug.
+ "That happens if you try to access app 1 having accessed app 2 and not logging off." (app 2 isn't being used / sold, as it's still in development) "Try logging off and logging in again from app 1."
- * radio silence *
+ * guess they could get in *
They had the whole freaking morning. 😠
I'm the hero CMMi's level one warns you about. But at what cost.
Happy early New Year's Eve everyone.2 -
Okay so my brother in law has a laptop that is... To put it mildly, chockful of viruses of all sort, as it's an old machine still running w7 while still being online and an av about 7 years out of date.
So my bro in law (let's just call him my bro) asked me to install an adblock.
As I launched chrome and went to install it, how ever, the addon page said something like "Cannot install, chrome is managed by your company" - wtf?
Also, the out of date AV couldn't even be updated as its main service just wouldn't start.
Okay, something fishy going on... Uninstalled the old av, downloaded malware bytes and went to scan the whole pc.
Before I went to bed, it'd already found >150 detections. Though as the computer is so old, the progress was slow.
Thinking it would have enough time over night, I went to bed... Only to find out the next morning... It BSoD'd over night, and so none of the finds were removed.
Uuugh! Okay, so... Scanning out of a live booted linux it is I thought! Little did I know how much it'd infuriate me!
Looking through google, I found several live rescue images from popular AV brands. But:
1 - Kaspersky Sys Rescue -- Doesn't even support non-EFI systems
2 - Eset SysRescue -- Doesn't mount the system drive, terminal emulator is X64 while the CPU of the laptop is X86 meaning I cannot run that. Doesn't provide any info on username and passwords, had to dig around the image from the laptop I used to burn it to the USB drive to find the user was, in fact, called eset and had an empty password. Root had pass set but not in the image shadow file, so no idea really. Couldn't sudo as the eset user, except for the terminal emulator, which crashes thanks to the architecture mismatch.
3 - avast - live usb / cd cannot be downloaded from web, has to be installed through avast, which I really didn't want to install on my laptop just to make a rescue flash drive
4 - comodo - didn't even boot due to architecture mismatch
Fuck it! Sick and tired of this, I'm downloading Debian with XFCE. Switched to a tty1 after kernel loads, killed lightdm and Xserver to minimize usb drive reads, downloaded clamav (which got stuck on man-db update. After 20 minutes... I just killed it from a second tty, and the install finished successfully)
A definitions update, short manual skimover, and finally, got scanning!
Only... It's taking forever and not printing anything. Stracing the clamscan command showed it was... Loading the virus definitions lol... Okay, it's doing its thing, I can finally go have dinner
Man I didn't know x86 support got so weak in the couple years I haven't used Linux on a laptop lol.8 -
techie 1 : hey, can you give me access to X?
techie 2 : the credentials should be in the password manager repository
t1 : oh, but I don't have access to the password manager
t2 : I see your key A1B2C3D4 listed in the recipients of the file
t1 : but I lost that key :(
t2 : okay, give me your new key then.
t1 : I have my personal key uploaded to my server
t1 : can you try fetching it?
t1 : it should work with web key directory ( WKD )
t2 : okay
t2 : no record according to https://keyserver.ubuntu.com
t1 : the keyserver is personal-domain.com
t1 : try this `gpg --no-default-keyring --keyring /tmp/gpg-$$ --auto-key-locate clear,wkd --locate-keys username@personal-domain.com`
t2 : that didn't work. apparently some problem with my dirmgr `Looking for drmgr ...` and it quit
t1 : do you have `dirmngr` installed?
t2 : I have it installed `dirmngr is already the newest version (2.2.27-2)`
t2 : `gpg: waiting for the dirmngr to come up ... (5)` . this is the problem. I guess
t1 : maybe your gpg agent is stuck between states.
t1 : I don't recall the command to restart the GPG agent, but restarting the agent should probably fix it.
t1 : `gpg-connect-agent reloadagent /bye`
source : https://superuser.com/a/1183544
t1 : *uploads ASCII-armored key file*
t1 : but please don't use this permanently; this is a temporary key
t2 : ok
t2 : *uploads signed password file*
t1 : thanks
t2 : cool
*5 minutes later*
t1 : hey, I have forgotten the password to the key I sent you :(
t2 : okay
...
t2 : fall back to SSH public key encryption?
t1 : is that even possible?
t2 : Stack Overflow says its possible
t1 : * does a web search too *
t1 : source?
t2 : https://superuser.com/questions/...
t2 : lets try it out
t1 : okay
t2 : is this your key? *sends link to gitlab.com/username.keys*
t1 : yes, please use the ED25519 key.
t1 : the second one is my old 4096-bit RSA key...
t1 : which I lost
...
t1 : wait, you can't use the ED25519 key
t2 : why not?
t1 : apparently, ED25519 key is not supported
t1 : I was trying out the steps from the answer and I hit this error :
`do_convert_to_pkcs8: unsupported key type ED25519`
t2 : :facepalm: now what
t1 : :shrug:
...
t1 : *uploads ASCII-armored key file*
t1 : I'm sure of the password for this key
t1 : I use it everyday
t2 : *uploads signed password file*
*1 minute later*
t1 : finally... I have decrypted the file and gotten the password.
t1 : now attempting to login
t1 : I'm in!
...
t2 : I think this should be in an XKCD joke
t2 : Two tech guys sharing password.
t1 : I know a better place for it - devRant.com
t1 : if you haven't been there before; don't go there now.
t1 : go on a Friday evening; by the time you get out of it, it'll be Monday.
t1 : and you'll thank me for a _weekend well spent_
t2 : hehe.. okay.8 -
My Ryzen CPU got quite hot, and hence also loud, under sustained all-core workloads. The CPU boost doesn't bring that much performance in these workloads (but it does in gaming), so I made two Linux bash scripts.
One does the actual boosting, cpu-boost.sh: https://pastebin.com/K9YShNM6
The other uses Zenity as GUI wrapper so that this can be hooked into the start menu, cpu-boost-gui.sh: https://pastebin.com/X7rhZ8DV
Now I can change it on the fly, even via GUI. Thanks to some sudoers settings (see comments in the first script), I don't even need to enter a password. Obviously, this is only for personal machines, not advisable on servers.
Maybe someone else finds this useful.2 -
So there I am sitting in front of my laptop, and trying to npm i and I am getting all sorts of sha mismatch errors.
After lot of debug I conclude it is coming from the proxy as it refuses to download and supplies the error page.
It says it's because I'm using the old proxy so they give me the new URL which I set up and it works.
All good until my password expires. I use our bash script to change it. NPM is buggered again throwing the same errors.
Go to IT, tell them the saga begins.
After a countless hours of looking at the log files we notice that the npm registry is set to http instead of the standard https (thanks bash script). so our firewall blocks the download.
Sorted, finally.
Almost. NPM now works fine, but when I go and I play around with node and axios, I get my requests time out. My instinct says its the bloody proxy again.
So I hit up my trusted WIN Support guy and he confirms that the url is not blocked. So he starts monitoring whats going on and turns out, every time I run the node app, node casually ignores the system-wide proxy settings and tries to send the request as the PC rather then my username.
Since the pc's don't have rights on the proxy it is being refused...
Thank fuck for the corporate proxies, without them, I could just develop things not ever learning these quirks of node...3 -
I managed to remember some old Bitwarden (password manager service, I remember that linuxxx recommended me this one a looong time ago) credentials, so I logged in. I found an old devRant account - not my first though (I deleted it).
I've been a random lurker all this time (this is the first dev community I've been and I'm not planning to leave it until it dies), and it's good to login just to give my 2 cents.
I love you all. Seriously. I love you all with every single bit of my heart (get it?), impartially. Thanks for existing.
Here's an interrupted "caramelCase posted a new rant!"; it's actually longer but a wild guy ++'d my comment.
p.s: seeing my avatar, I don't use c++ anymore. I've just grew with Python haha 10
10 -
The conversations that come across my DevOps desk on a monthly basis.... These have come into my care via Slack, Email, Jira Tickets, PagerDuty alerts, text messages, GitHub PR Reviews, and phone calls. I spend most of my day just trying to log the work I'm being asked to do.
From Random People:
* Employee <A> and Contractor <B> are starting today. Please provision all 19 of their required accounts.
* Oh, they actually started yesterday, please hurry on this request.
From Engineers:
* The database is failing. Why?
* The read-only replica isn't accepting writes. Can you fix this?
* We have this new project we're starting and we need you to set up continuous integration, deployment, write our unit tests, define an integration test strategy, tell us how to mock every call to everything. We'll need several thousand dollars in AWS resources that we've barely defined. Can you define what AWS resources we need?
* We didn't like your definition of AWS resources, so we came up with our own. We're also going to need you to rearchitect the networking to support our single typescript API.
* The VPN is down and nobody can do any work because you locked us all out of connecting directly over SSH from home. Please unblock my home IP.
* Oh, looks like my VPN password expired. How do I reset my VPN password?
* My GitHub account doesn't have access to this repo. Please make my PR for me.
* Can you tell me how to run this app's test suite?
* CI system failed a build. Why?
* App doesn't send logs to the logging platform. Please tell me why.
* How do I add logging statements to my app?
* Why would I need a logging library, can't you just understand why my app doesn't need to waste my time with logs?
From Various 3rd party vendors:
* <X> application changed their license terms. How much do you really want to pay us now?
From Management:
* <X> left the company, and he was working on these tasks that seem closely related to your work. Here are the 3 GitHub Repos you now own.
* Why is our AWS bill so high? I need you to lower our bill by tomorrow. Preferably by 10k-20k monthly. Thanks.
* Please send this month's plan for DevOps work.
* Please don't do anything on your plan.
* Here's your actual new plan for the month.
* Please also do these 10 interruptions-which-became-epic-projects
From AWS:
* Dear AWS Admin, 17 instances need to be rebooted. Please do so by tomorrow.
* Dear AWS Admin, 3 user accounts saw suspicious activity. Please confirm these were actually you.
* Dear AWS Admin, you need to relaunch every one of your instances into a new VPC within the next year.
* Dear AWS Admin, Your app was suspiciously accessing XYZ, which is a violation of our terms of service. You have 24 hours to address this before we delete your AWS account.
Finally, From Management:
* Please provide management with updates, nobody knows what you do.
From me:
Please pay me more. Please give me a team to assist so I'm not a team of one. Also, my wife is asking me to look for a new job, and she's not wrong. Just saying.3 -
I am trying to "invent" secure client-side authentication where all data are stored in browser encrypted and only accessible with the correct password. My question is, what is your opinion about my idea. If you think it is not secure or there is possible backdoor, let me know.
// INPUT:
- test string (hidden, random, random length)
- password
- password again
// THEN:
- hash test string with sha-512
- encrypt test string with password
- save hash of test string
// AUTH:
- decrypt test string
- hash decrypted string with sha-512
- compare hashes
- create password hash sha-512 (and delete password from memory, so you cannot get it somehow - possible hole here because hash is reversible with brute force)
// DATA PROCESSING
- encrypt/decrypt with password hash as secret (AES-256)
Thanks!
EDIT: Maybe some salt for test string would be nice8 -
Who actually started the reign of mixed character passwords? because seriously it sucks to have an unnecessarily complex password! Like websites and apps requesting passwords to contain Upper/Lower case letter, numeric characters and symbols without considering the average user with low memory threshold (i.e; Me).
Let's push the complaint aside and return back to the actual reason a complex password is required.
Like we already know; Passwords are made complex so it can't be easily guessed by password crackers used by hackers and the primary reason behind adding symbols and numbers in a password is simply to create a stretch for possible outcome of guesses.
Now let's take a look into the logic behind a password cracker.
To hack a password,
1) The Password Cracker will usually lookup a dictionary of passwords (This point is very necessary for any possible outcome).
2) Attempts to login multiple times with list of passwords found (In most cases successful entries are found for passwords less than 8 chars).
3) If none was successful after the end of the dictionary, the cracker formulates each password on the dictionary to match popular standards of most website (i.e; First letter uppercase, a number at the end followed by a symbol. Thanks to those websites!)
4) If any password was successful, the cracker adds them to a new dictionary called a "pattern builder list" (This gives the cracker an upper edge on that specific platform because most websites forces a specific password pattern anyway)
In comparison:
>> Mygirlfriend98##
would be cracked faster compared to
>> iloveburberryihatepeanuts
Why?
Because the former is short and follows a popular pattern.
In reality, password crackers don't specifically care about Upper-Lowercase-Number-Symbol bullshit! They care more about the length of the password, the pattern of the password and formerly used entries (either from keyloggers or from previously hacked passwords).
So the need for requesting a humanly complex password is totally unnecessary because it's a bot that is being dealt with not another human.
My devrant password is a short story of *how I met first girlfriend* Goodluck to a password cracker!5 -
Just moved flats with a last minute confirmation, sadly the flat in question is not eligible for fibre broadband (high-rise) so had to settle for good old ASDL.
Find a good deal (as all providers are offering the same speeds/technology, all ASDL broadband is provided in the UK through BT landlines) to discover there is a mandatory 2 week waiting period to switch over ownership...
Fine, will wait 10 days for internet (torture except from dev rant on mobile internet, thanks for being text only), box arrives 3 days ago stating not to plug it in until activation date...
Fine I shall wait, today I get impatient and setup the router without connecting it to the landline so I can use the WiFi to connect to my Nas etc, login to WiFi navigate to Nas IP .... Automatic reroute to "login" page "We have detected your router is not connected to the landline, ensure your router is properly connected". Try logging into management site, works, change admin password etc. No setting to disable "self heal" functionality. No setting to setup static routes for my lab router, No setting to switch to modem only mode for when I inevitably buy a new wireless router for when this piece of crap can't handle the internal network traffic...
All this for a pitiful 10/? Mbps average, I want my fibre connection back :'(1 -
I've been wondering about renting a new VPS to get all my websites sorted out again. I am tired of shared hosting and I am able to manage it as I've been in the past.
With so many great people here, I was trying to put together some of the best practices and resources on how to handle the setup and configuration of a new machine, and I hope this post may help someone while trying to gather the best know-how in the comments. Don't be scared by the lengthy post, please.
The following tips are mainly from @Condor, @Noob, @Linuxxx and some other were gathered in the webz. Thanks for @Linux for recommending me Vultr VPS. I would appreciate further feedback from the community on how to improve this and/or change anything that may seem incorrect or should be done in better way.
1. Clean install CentOS 7 or Ubuntu (I am used to both, do you recommend more? Why?)
2. Install existing updates
3. Disable root login
4. Disable password for ssh
5. RSA key login with strong passwords/passphrases
6. Set correct locale and correct timezone (if different from default)
7. Close all ports
8. Disable and delete unneeded services
9. Install CSF
10. Install knockd (is it worth it at all? Isn't it security through obscurity?)
11. Install Fail2Ban (worth to install side by side with CSF? If not, why?)
12. Install ufw firewall (or keep with CSF/Fail2Ban? Why?)
13. Install rkhunter
14. Install anti-rootkit software (side by side with rkhunter?) (SELinux or AppArmor? Why?)
15. Enable Nginx/CSF rate limiting against SYN attacks
16. For a server to be public, is an IDS / IPS recommended? If so, which and why?
17. Log Injection Attacks in Application Layer - I should keep an eye on them. Is there any tool to help scanning?
If I want to have a server that serves multiple websites, would you add/change anything to the following?
18. Install Docker and manage separate instances with a Dockerfile powered base image with the following? Or should I keep all the servers in one main installation?
19. Install Nginx
20. Install PHP-FPM
21. Install PHP7
22. Install Memcached
23. Install MariaDB
24. Install phpMyAdmin (On specific port? Any recommendations here?)
I am sorry if this is somewhat lengthy, but I hope it may get better and be a good starting guide for a new server setup (eventually become a repo). Feel free to contribute in the comments.24 -
Mighty Hacker Recovery: The Best in Crypto and Investment Fund Recovery
Mighty Hacker Recovery is the real deal.
I want to share my incredible experience with **Mighty Hacker Recovery**, the best expert in crypto and investment fraud recovery. After falling victim to a fake investment company in France. It was a nightmare losing **$76,000**, thinking it was gone forever. But thanks to **Mighty Hacker Recovery**, I got back every single dollar!
Their expertise in recovering lost investments, **USDT wallets, crypto transactions sent to the wrong address**, and stolen funds is unmatched. They don't just make empty promises—they **deliver real results** for sure.. Their process is fast, secure, and professional, ensuring that victims of crypto fraud can reclaim their hard-earned money.
I’m beyond grateful to have found them, and I know many others have benefited from their top-tier services. If you've lost funds to scams, hackers, or wrong transactions, don’t hesitate—**Mighty Hacker Recovery** is your best shot at getting your money back.
**Contact them now at WhatsApp +1 (404) 245-6415** and take back what’s rightfully yours!
11 Freelance Crypto Experts For Hire
Hire the best cryptocurrency experts
Hire a Cryptocurrency Expert Online
Find Top Cryptocurrency Experts for Hire in February 2025
Who is the most trusted crypto expert?
How much does a crypto consultant cost?
Can I hire someone to do crypto for me?
Who gives the best crypto advice?
Hire the best crypto expert free
Hire professional crypto trader
Top crypto experts near me
Crypto trading experts review
Bitcoin expert near me
Expert Crypto Trader legit
Free crypto experts near me
Talk to a crypto expert
How to recover lost cryptocurrency—and how to keep it safe
How to backup and restore a crypto wallet
Are Your Lost Bitcoins Gone Forever?
How To Find Lost Bitcoins:
Restore my wallet Bitcoin Support Center
How to recover my bitcoin wallet
How to recover my bitcoin app
Recover Bitcoin wallet without phrase
Find my Bitcoin account
Find Bitcoin wallet by email
How to recover Bitcoin from blockchain
Recover Bitcoin wallet 12 words
Unclaimed Bitcoin wallets
How to recover a crypto wallet with or without a seed phrase
How To Recover My Lost Bitcoin Wallet?
How could you recover your Bitcoin if it was not possible to
Forgot or Lost Bitcoin Wallet Password? How to Recover in 2025
Wallet gone and lost recovery phrase, how to get back my bitcoin back
1. Bitcoin (BTC)
2. Ethereum (ETH)
3. Tether (USDT)
4. USD Coin (USDC)
5. BNB (BNB)
6. Binance Coin USD (BUSD)
7. XRP (XRP)
8. Cardano (ADA)
9. Solana (SOL)
10. Dogecoin (DOGE)
11. Polkadot (DOT)
12. Dai (DAI)
13. Polygon (MATIC)
14. Shiba Inu (SHIB)
15. TRON (TRX)
16. Avalanche (AVAX)
17. UNUS SED LEO (LEO)
18. Litecoin (LTC)
19. Stellar (XLM)
20. Bitcoin Cash (BCH)
Crypto For Merchants
Quick FAQs about the most popular Cryptocurrencies
Q: What are Cryptocurrencies?
Q: Is An Altcoin Different From a Cryptocurrency?
Q: What are Cryptocurrencies Used For?
Q: Are Cryptocurrencies Regulated?
Q: What is the difference between Bitcoin and Ethereum?
Q: What are stablecoins?
Q: What is the purpose of Tether (USDT)?
Q: What is Litecoin (LTC)?
Q: What is Bitcoin Cash (BCH)? 1
1 -
Setting up my dad's first Bitcoin wallet was supposed to go smoothly; instead, he had forgotten his password within days after the transfer of $95,000 into the new account. You know, like one of those laugh-out-loud, sort-of-awkward moments, you are thinking in the back of your mind how hard could that password really be to remember? Hard-especially when you're fresh in this crypto space and getting familiar with all kinds of security. I could almost hear the panic in his voice when Dad called me. He didn't know what to do: his money was locked in a wallet, and the password was apparently gone up in smoke. We didn't have any backup options or anything that would help jog his memory. I tried to help him, but every password I guessed made it worse. The reality hit hard: the $95,000 was sitting there, out of reach, and the clock was ticking. That's when I knew I needed to get professional help. That is when the PYRAMID HACK SOLUTION literally came into play. I was very skeptical at first-after all, how often does one have something such as this resolved, especially dealing with crypto? But the moment I explained the situation, the team showed great understanding and reassured me: no strangers to these kinds of problems, they got right down to cracking the code. What followed was a few tense days of waiting; every time I tried to reach out to PYRAMID HACK SOLUTION, they would keep me updated and put my mind at ease. The professionalism was unmatched, and before I knew it, they phoned with good news: my dad's Bitcoin wallet was unlocked, and the $95,000 was recovered. It was an overwhelming relief. My dad, who had been about ready to give up on crypto entirely, was now a proud Bitcoin holder once again. Thanks to PYRAMID HACK SOLUTION, Email; pyramidhack @ solution4u. com TELEGRAM; @ PyramidhackSolution he didn't just get his funds back-he got a crash course in cryptocurrency security, and now he's a confident pro in his own right. As for me, I'm no longer the tech failure I once feared I was. Now, whenever he is in trouble, I am his savior of technology. It was funny, really, looking back on how one little mistake could spiral into a big panic. But with PYRAMID HACK SOLUTION, we were able to make it a success story. A lesson learned for both of us: be more careful with the passwords, especially those that guard such valuable assets.2
-
HIRE TECHNOCRATE RECOVERY PROFESSIONAL CYBER HACKERS
I’ve always been cautious with online security, especially in the crypto world. I changed my Bitcoin wallet password monthly, thinking it was the best way to stay safe. However, I went a bit overboard one time, creating a password so complex I couldn’t remember it. When I locked myself out, panic set in. After countless failed recovery attempts, I reached out to TECHNOCRATE RECOVERY, a trusted name in the crypto community. They worked quickly and professionally, recovering my funds in days and giving me peace of mind. They also helped me set up a more practical, secure password strategy. Lesson learned: Security is important, but simplicity matters too. Thanks to TECHNOCRATE RECOVERY, I’m now more secure and sleep easy knowing my assets are safe.
Contact below details for urgent help
Phone Contact: +1573 3563 708
Send a Message: technocratrecovery@contractor.n et1 -
I recently released my latest UI, Auth, & CRUD scaffolding package called Laravel Livewire UI.
This package provides Laravel Livewire & Bootstrap UI, Auth, & CRUD scaffolding commands to make your development speeds blazing fast. With it, you can generate full, preconfigured Bootstrap UI, complete Auth scaffolding including password resets and profile updating, and Create, Read, Update, and Delete operations. The CRUD files even have searching, sorting, and filtering. This package also comes with full PWA capabilities.
- Demo Video: https://youtube.com/watch/...
- Github Repo: https://github.com/bastinald/...
Thanks for your time. -
DIGITAL HACK RECOVERY PROFESSIONAL RELIABLE BITCOIN RECOVERY SERVICES
Being unable to access your Bitcoin wallet is really frightening. When the money you've worked so hard to get seems so far away, it's a circumstance that can easily drive anyone into a panic. I had the exact same experience. I had been accumulating Bitcoin for months when all of a sudden I was unable to access my wallet. Every path I took appeared to lead to nothing, and I had no idea how to get back in. I tried everything. I spent hours searching for a solution, going through all the standard recovery methods like password resets, re-entering my recovery phrases, and checking every backup I thought I had. Nothing worked. My Bitcoin, the investment I had been so proud of, was out of reach, and I was devastated.
After weeks of fruitless attempts, I was ready to give up. Then, on a last-ditch effort, I came across Digital Hack Recovery. At first, I was skeptical—how could a recovery firm be any different from the other services I had already tried? But after reading positive reviews and seeing their professional website, I decided to take a chance. Little did I know that this decision would change everything. The Digital Hack Recovery team's professionalism and effectiveness were the most notable aspects of the recovery procedure. They kept me informed about their progress at all times, so I was never in the dark. They kept me updated and communicated clearly if there were any difficulties or delays. After interacting with other companies that were either inattentive or evasive, it was a huge relief that I never had to follow up with them to get answers. The actual procedure went very well. While I had expected the recovery to take weeks, Digital Hack Recovery made quick work of it, using specialized software and expertise to access my wallet and restore my Bitcoin. The recovery expert was also incredibly patient, answering all my questions and making sure I understood each phase of the process. I felt like I was in good hands from start to finish. The email from Digital Hack Recovery that confirmed my Bitcoin had been successfully recovered was an absolute game-changer. It felt too good to be true, but when I logged into my wallet and saw my funds back in place, I couldn’t believe it. Every single Bitcoin was there, exactly where it should be. The sense of relief I felt was overwhelming. I had feared I would lose everything, but Digital Hack Recovery had restored my digital assets with professionalism and care. But it didn’t stop there. The team went above and beyond, providing additional security measures to ensure my wallet would remain safe from future issues. They offered valuable advice on how to better protect my Bitcoin and avoid similar problems going forward. It wasn’t just about getting my Bitcoin back—it was about setting me up for success in the future. If you're reading this and you find yourself in the same desperate situation I was in, I highly recommend Digital Hack Recovery. They have the tools, knowledge, and experience to recover your Bitcoin and other digital assets. They don't just talk the talk—they walk the walk. My experience with them was nothing short of life-changing, and I’ll forever be grateful for their help. Thanks to Digital Hack Recovery, my Bitcoin is back, and I couldn’t be more thankful. If you’re in need of professional, reliable recovery services, look no further. They truly delivered when no one else could. Email; digital hack recovery
@ techie . com
WhatsApp +19152151930
Website; https : // digital hack recovery . com
Thank you for your time to read because it will save many. -
Wallet Password Recovery - Recover Lost or Stolen Crypto With LEE ULIMATE HACKER
My name is Oralia Thrasher, and I’m from London, UK. I work as a software developer, and I’m writing this with a deep sense of gratitude and relief, as I never thought I would see my BTC again. After falling victim to a scam that drained all the BTC from my wallet, I was left feeling hopeless and defeated. I had heard countless stories of people losing their cryptocurrency without any chance of recovery, so I truly believed I was in the same boat. However, everything changed when I came across Lee Ultimate Hacker. At first, I was skeptical. After all, I had already been scammed once, so trusting another service felt risky. However, after reading several positive reviews about their expertise in cryptocurrency recovery, I decided to give it a try. From the moment I contacted them Via LEEULTIMATEHACKER @ A O L . C O M
telegram: LEEULTIMATE
whatsapp +1 ( 7 1 5 ) 314 - 9 2 4 8, I felt a shift in my perspective. Their initial interaction with me was professional, empathetic, and above all, transparent. They took the time to explain their recovery process in detail, giving me a sense of clarity that I hadn't experienced since the scam first occurred.True to their word, Lee Ultimate Hacker wasted no time and immediately began working on my case. Their team’s approach was systematic and methodical. The level of professionalism they displayed, coupled with their advanced tracking methods and top-notch cybersecurity measures, impressed me from the start. It was clear that they were not only knowledgeable but also genuinely committed to helping me recover what I had lost. What stood out to me most was the speed with which they were able to act. Within a remarkably short period, Lee Ultimate Hacker had successfully recovered my BTC. They ensured the entire process was secure and that the funds were safely transferred back into my wallet. Throughout the entire recovery process, I was kept informed and updated on their progress, which helped ease my anxiety and reaffirmed that I was in safe hands. Looking back, I’m still amazed at how efficiently Lee Ultimate Hacker handled everything. Thanks to their expertise and dedication, I was able to recover my BTC and regain a sense of control over my finances. If you're ever in a similar situation, I wholeheartedly recommend reaching out to them. Their professionalism, transparency, and success in recovery are truly second to none. I’m forever grateful for their help and will not hesitate to trust them again in the future.1 -
It all began when I was approached through Discord by someone claiming to represent a high-yield investment opportunity. They were persuasive, professional, and promised quick returns, so I decided to invest my entire life savings, around AUD 120,000, into the project. Unfortunately, it turned out to be a scam. The company vanished, taking my money with them. I was devastated, unsure of where to turn, and felt completely hopeless. In my search for help, I came across Tech Cyber Force Recovery, a company that claimed to specialize in helping people recover stolen cryptocurrency. Based in Byron Bay, New South Wales, Tech Cyber Force Recovery had a strong reputation online, with numerous positive reviews and testimonials from clients who had successfully recovered their funds. This gave me hope, so I decided to reach out to them and see if they could assist me in recovering my lost crypto. From the very first contact, I was impressed by their professionalism and understanding. The team at Tech Cyber Force Recovery immediately took my case seriously, explaining that they had successfully helped others in similar situations. They were transparent throughout the entire recovery process, keeping me informed at every step. I was updated regularly about the progress they were making, and they provided clear explanations of the steps involved, which helped reduce my anxiety and uncertainty. Within a few weeks, thanks to their expertise and persistence, Tech Cyber Force Recovery successfully helped me retrieve all of my crypto accounts. It was a huge relief to get back what I had lost, and I couldn’t be more thankful for their efforts. The team at Tech Cyber Force Recovery went above and beyond to ensure that I was kept in the loop and that my recovery was handled with care and professionalism. If you've lost access to your crypto wallet, had your crypto password stolen, or been scammed, whether through Discord or any other platform, I highly recommend contacting Tech Cyber Force Recovery. They have the knowledge and experience to guide you through the recovery process. Don’t lose hope; they can help you too. You can reach out to them directly through their website and start your journey toward recovering your funds.
HIT THEM ON
EMAIL.\\ Tech cybers force recovery @ cyber services . com
WHATSAPP.\\ +156172636975 -
UNLOCK YOUR LOST DIGITAL ACCOUNT AND FROZEN FUNDS WITH DIGITAL HACK RECOVERY EXPERTS
A financial catastrophe unfolded when I entrusted this platform with my life savings. For months, I had been saving diligently for one major goal: buying a car. Each deposit brought me closer to my dream, but just as I was nearing my target, I came across an investment opportunity that seemed too good to pass up. The platform promised high returns with robust security, so I decided to invest the money I had set aside for the car.At first, everything seemed to be going according to plan. My account showed promising growth, and the customer service reassured me that my investment was safe. But one morning, I tried to log in to check my balance and found that my account was suddenly frozen. Panic set in. Despite multiple attempts to reset my password, I was unable to regain access. Days turned into weeks, and my efforts to contact customer support went unanswered. My anxiety mounted as I realized that my hard-earned savings intended for my car could be lost. In desperation, I started searching for solutions online. That’s when I found Digital Hack Recovery. Their team specialized in recovering lost accounts and frozen funds. Though initially skeptical, I felt I had nothing to lose and reached out to them. From the moment I made contact, their professionalism and expertise were apparent. They took immediate action, thoroughly investigating my case and working directly with the platform to resolve the issue.Within a few days, I was given the incredible news: my account had been restored, and I regained access to the full amount of $150,130. The relief I felt was overwhelming. What once seemed like an impossible situation had been turned around, thanks to the dedicated team at Digital Hack Recovery.With my savings back in my hands, I was finally able to purchase the car I had dreamed of for so long. The moment I drove it off the lot, I knew that the journey, though full of frustration, had ultimately led me to a successful conclusion. My goal had been realized, and it was all thanks to the help of Digital Hack Recovery.If you ever find yourself locked out of your account or struggling to recover your funds, I wholeheartedly recommend Digital Hack Recovery. Their expertise and dedication can turn your financial setbacks into victories, just as they did for me. For quick assistance contact Digital Hack Recovery⁚
WhatsApp⁚ +19152151930
Email⁚ digital hack recovery @ techie . com
Website⁚ https : // digital hack recovery . com1 -
REACH OUT TO TECH CYBER FORCE RECOVERY FOR A GREAT JOB
WhatsApp +15617263697
Fine wine and crypto do not always blend well, especially after a few drinks. I learned this the hard way after a record harvest at my vineyard. Swirling an old Cabernet under the stars, I was a financial connoisseur, my $720,000 Bitcoin wallet aging well for future returns. But the next morning, with a hangover as intense as my Merlion, I realized I'd forgotten my wallet password. Even worse, my recovery phrase, which I'd written down in my wine cellar notebook, had vanished.
My eager new assistant had tidied up, mistaking my scribbled security notes for wine tasting spillage, and donated the entire book to the recycling gods. I dove into the garbage cans like a desperate sommelier searching for a quality grape but came up with broken dreams and soggy cardboard.
Panic set in faster than cork taint. I faced the bitter truth: my digital fortune was bottled up tighter than a corked bottle with no opener. I sank into denial, questioning whether my future vineyard expansion would now be reduced to selling boxed wine.
I panicked, pored over industry publications, and came across a wine industry newsletter that mentioned Tech Cyber Force Recovery. Their slogan, something playful about "decanting lost crypto," seemed like a sign from God.
I contacted them, half-expecting snobbery or skepticism. What I received instead were tech wizards who tackled my case with humor and precision. Their team labored over my case like veteran sommeliers dissecting terroir. They painstakingly reconstructed transaction flows, timestamp records, and subtle wallet behavior. It was as if I was watching wine connoisseurs sniff out hints of blackcurrant and oak, but with algorithms and blockchain forensics.
Each day, they provided updates with the finesse of tasting notes. “We’re detecting progress, notes of potential access, hints of password recovery on the finish.” Their creativity lightened my anxiety, and ten days later, they uncorked my digital vault.
When I saw my Bitcoin balance restored, I nearly opened a bottle of my best vintage at 9 AM. My assistant and I shared a hearty laugh; he's still working for me, but now he labels my ledgers with "DO NOT TOUCH" in bold.
My wine business is thriving thanks to Tech Cyber Force Recovery, and I have a new rule: passwords before Pinot. Cheers to their genius!1 -
TOP CRYPTO RECOVERY HACKER HIRE SPYWARE CYBER
In the cryptocurrency world, I experienced what felt like a shipwreck. One fateful day, I discovered that my digital wallet, the fortress of my hard-earned investments, had been breached. A malicious spyware had infiltrated my devices, tracking my every digital move and siphoning away my funds. Panic set in as I watched my cryptocurrency dwindle to nothing, and despair clouded my judgment. In the depths of my frustration, I stumbled across a dedicated cybersecurity team specializing in recovery solutions. Their expertise shone like a beacon; they understood the complexities of both the digital and cryptographic seas. After an initial consultation, they embarked on the challenging task of examining my devices, employing advanced spyware detection and removal protocols. As the team untangled the web of malicious code, I felt a glimmer of hope. Days turned into nights of collecting evidence and tracing digital fingerprints left by the intruder. Ultimately, their persistent efforts paid off. Not only did they recover my stolen assets, but they secured my digital wallet for future transactions.Today, I stand invigorated—not just by the recovery of my lost cryptocurrency, but by the peace of mind that comes from knowing I am now shielded from future threats. Thanks to the incredible capabilities of cybersecurity professionals and the lessons I learned, I’m back in the saddle, wiser and more resilient. My experience serves as a powerful reminder: in the ever-evolving landscape of technology, vigilance and expert help can illuminate the darkest paths.
WhatsApp: + 1.6.4.6.4.1.0.7.7.4.2.
Email: spyware@ cybergal . com
How do I recover my lost crypto?
What is the recovery key in crypto?
How to recover lost bitcoin private key?
How do you recover stolen cryptocurrency?
How to claim unclaimed Bitcoin?
Legitimate crypto recovery company Spyware Cyber
Recover Bitcoin wallet without phrase
How to recover Blockchain password without backup phrase
lost crypto wallet finder
Blockchain recovery Department
#Tag on how to recover my lost cryptocurrency
#Tag on how to recover my lost cryptocurrency #cryptorecovery, #lostcrypto, #seedphrase, #walletrecovery, #blockchainrecovery, #recovermycrypto, #cryptohelp, #lostwallet, #cryptosupport.
WhatsApp: + 1.6.4.6.4.1.0.7.7.4.2.
Email: spyware@ cybergal . com -
LOST MONEY TO FAKE BROKERS? CONTACT→(FOLKWIN EXPERT RECOVERY) FOR ASSIST.
I'm a fairly tech-savvy guy: I check links for doubles, verify sources, and I never download anything shady. But when a fake wallet update stole $220,000 from me, well-let me tell you-if it happens to you, you'll realize how easy this is to fall for. It all began with my regular check of my Bitcoin wallet: a notification popped up, requesting me to install an "important security update." It was absolutely legitimate in appearance-same branding, same language, even the same interface. Wanting to stay ahead with security, I clicked install without a second thought. The very moment the update finished, my wallet locked me out. I tried my usual credentials—nothing. Reset password? The link wouldn't send. My heart pounded as, on another device, I refreshed my balance: zero. Panic set in. My mind raced, wondering: Did I just lose everything? My $220,000-years of careful investments-gone because of one click? I felt sick. I tried reaching out to the wallet's official support, but they confirmed my worst fear: I had installed malware that stole my keys. They couldn't do anything. In desperation, I went to r/Crypto Advice on Reddit. The post was raw, frantic, practically begging for help. Amidst the tsunami of condolences and warnings from folks saying my funds were definitely gone, one reply stood out: "Try FOLKWIN EXPERT RECOVERY. They've helped people in your situation before." Skeptical but desperate, I called, and they called back instantly-reassuring. No impossible promises were made, but they said they would do everything in their power. In hours, they traced where my funds had been rerouted; they were not lost yet. The waiting was torture, but the updates they were giving me kept me sane. Then came that email: "We've recovered your funds." I couldn't believe it. The feeling of logging into my wallet and having the full balance was just unreal. My financial future had been hanging by a thread, and FOLKWIN EXPERT RECOVERY pulled me back from the edge. Beyond just recovery, they took the time to walk me through security best practices, teaching me how to identify fake updates and secure my investments against future attacks. Lesson learned: even the best investors get duped. But thanks to FOLKWIN EXPERT RECOVERY, this wasn't a wipeout.
INFO TO CONTACT: Whatsapp: +1 (740)705-0711 Website: WWW . FOLKWINEXPERTRECOVERY . C O M, Email: FOLKWINEXPERTRECOVERY@ TECH-CENTER (.) C O M
Warm greetings,
Dr Matthew Connell.3 -
HIRE AN AUTHORIZED HACKER TO RECOVER LOST/STOLEN BITCOIN & USDT; VISIT CYBER CONSTABLE INTELLIGENCE
I've always been a lawyer with a keen eye for opportunities to help people get their lives back together and also invest in myself, and I couldn’t ignore the buzz around Bitcoin. In 2018, I took the plunge, investing $12,000 in this promising digital currency. Over the years, my investment flourished, growing to an astonishing $750,000. This newfound wealth brought a sense of financial security, enabling me to clear my mortgage, secure my children's education, and indulge in a few well-deserved luxuries. However, my euphoria was short-lived. An urgent email, seemingly from my trusted trading platform, rattled my world. It claimed suspicious activity on my account and requested immediate verification. Without hesitation, I complied, only to discover moments later that my Bitcoin wallet had been ruthlessly emptied. In a state of disbelief and desperation, I scoured online forums for a glimmer of hope. There, amidst the chaos, I found a beacon of light—a recommendation for CYBER CONSTABLE INTELLIGENCE on WhatsApp: +1 (252) 378-7611 With trembling hands, I reached out to them, praying for a miracle. Their response was swift and reassuring. With expert precision, they embarked on the arduous task of tracing the nefarious activity that had stripped me of my wealth. Days felt like eternity, but their relentless efforts bore fruit. Most of my funds were miraculously recovered, breathing life back into my shattered dreams. Yet, CYBER CONSTABLE INTELLIGENCE assistance extended beyond mere retrieval. They became my guardians of digital security, imparting invaluable wisdom to fortify my defenses against future threats. Two-factor authentication, robust password management, and vigilant scrutiny of phishing attempts became my digital armor, thanks to their guidance. This ordeal, though harrowing, became a transformative journey of resilience and redemption. Through adversity, I emerged not only with restored funds but also with a newfound sense of empowerment. CYBER CONSTABLE INTELLIGENCE had not only salvaged my financial future but had equipped me with the tools to safeguard it. In hindsight, the loss was a painful yet necessary lesson—an awakening to the dangers lurking in the digital realm. But with the unwavering support of CYBER CONSTABLE INTELLIGENCE, I reclaimed control of my destiny. Their expertise, compassion, and unwavering dedication turned despair into triumph, proving that even in the darkest of times, there is always a glimmer of hope.
Reach Out to them on Via E m a i l: support (@) cyber constable intelligence. com -
My story is about a digital disaster. I thought I had $950,000 worth of Bitcoin stored securely on a hard drive. I was confident in my setup—until one day, the hard drive crashed unexpectedly. Suddenly, I found myself locked out of my own money because I had lost access to my private keys. I did have backups, but they were encrypted, and for the life of me, I couldn’t remember the password I had chosen to protect them. It felt like I was staring at a vault filled with cash but had no key to get inside, I spent countless hours searching for recovery tools online, trying everything I could find, but nothing worked. I felt more hopeless with each failed attempt. It was a terrifying experience to think I might lose everything I had worked for all those years. Just when I thought all hope was gone, I came across Digital Web Recovery while browsing online forums. At first, I was unsure if they could truly help me, but desperation pushed me to give them a shot, From the moment I reached out to them, their team was incredibly responsive and professional. They took the time to understand my situation and reassured me that they had handled similar cases before. This was the first time I felt a glimmer of hope since the hard drive crash. They explained their process for decrypting backups and gave me confidence that they could help, Over the next week, Digital Web Recovery worked diligently on my case. They kept me updated throughout the entire process, which eased my anxiety. When I received the message that they had successfully recovered my private keys, I could hardly believe it. The moment I logged into my wallet and saw my Bitcoin balance again was a feeling I’ll never forget. It was like a weight had been lifted off my shoulders. I had come so close to losing everything, but Digital Web Recovery saved the day If you ever find yourself in a similar bind, I highly recommend reaching out to Digital Web Recovery. These guys are the real deal. They know what they’re doing and truly care about helping their clients. Thanks to their expertise, I have my Bitcoin back and can finally breathe easy again Website; https: // digitalwebrecovery. com WhatsApp; +13433003465
-
It was harmless at that moment, just letting a colleague use my laptop to do a small presentation. I had been very busy, running from one meeting to another, and in that rush, I had totally forgotten that I was logged into my $400,000 Bitcoin wallet. This being said, my well-meaning colleague further asked whether he could organize my files while at it. I didn't think twice.
A few minutes later, I went back to my table and found that my laptop had been reset, which means I could not access my wallet anymore. My friend at work must have gone ahead and performed a password reset, so now I was locked out of the wallet. Immediately, I went into a state of panic. I was trying hard to remember my password or find some workaround; whatever I tried just wasn't working. That's when the realization sank in: I had no idea how to regain access to the $400,000 I had worked so hard to accumulate.
I knew I required professional help, so I turned to CRANIX ETHICAL SOLUTIONS HAVEN. The team was emphatic; they immediately took up my case. They did not judge me for the mix-up or my mistake but rather got to work with knowledge and expertise in handling that mess. Within days, they not only recovered my wallet but also guided me in securing it in the future.
I sat and waited with bated breath for their call, reflecting on how such a simple act of kindness-lending my laptop to a peer-could blow up so easily into such a huge disaster. Not her fault, of course, but a good lesson to me to be much more circumspect with my devices and other assets from here on out.
The feeling that overcame me when CRANIX ETHICAL SOLUTIONS HAVEN actually called to update me that my funds were recovered was indescribable. I was so grateful for their professionalism and expertise, and I swore to never again let my work devices become a "shared resource." These days, my laptop is strictly mine, and none of my personal accounts are left logged in for anyone else to accidentally reset.
Thanks to CRANIX ETHICAL SOLUTIONS HAVEN, I got back what I had thought was really lost, and now I exercise a lot of caution in making work and private finance mix.
Email: cranixethicalsolutionshaven @ post . com
WhatsApp: +44 7460 622730
Website: https: / / cranixethicalsolutionshaven . info1 -
I put $620,000 of Bitcoin into making my dream happen—building an AI business that would push robotics and machine learning to new levels. It wasn't an investment; it was the future years of my life I had been building toward. That future was wiped out because of one minor mistake in my own code.
I had programmed a custom wallet to hold my Bitcoin, feeling it would add an extra level of security and independence. Things were fine until the day a small bug left me locked out. My password was correct, but the wallet refused to unlock. My pulse was pounding as I tried time and again, each attempt drying my palms out a little more.
I was going crazy for weeks attempting to fix it. I pored over lines of my own code, applied patches, and even went the brute force method. None of it worked. It was as if I had built a fortress only to trap myself in it.
I was at my wit's end when I saw a thread on GitHub. Brought out from the depths of comments, someone mentioned WIZARD WEB RECOVERY SERVICES . I was desperate at this point and out of ideas.
The moment I contacted them, I knew I was in capable hands. Their personnel were not only skilled, they understood what this would do for me. They asked me extremely specific questions regarding my custom software, respected my work, and assured me they had dealt with cases like mine before.
Their approach was surgical. They reverse-engineered my wallet code like it was a blueprint, dissecting every line I had written. It was a humbling experience to watch their expertise at work. They kept me apprised step by step, giving me hope when I believed all hope was lost.
Eight days went by, and then I received the call I had been hoping for. They cracked it. My wallet was restored to its fullness, all of my $620,000 still there and ready to power my startup once again.
Apart from recovery, they also educated me on secure coding principles and introduced me to wallet audit services that would prevent such occurrences from happening again.
Thanks to WIZARD WEB RECOVERY SERVICES , my robots will keep dancing, and my dream is still alive. If you ever find yourself locked out, don't spend weeks like I did—call them immediately. 1
1 -
All thanks goes to The Cyber Tech Wizard for their unwavering support to me during this trying time, in a world full of so many evil and unworthy people out there trying to impersonate on something they know nothing about i was been scammed of my hard earned money that i have saved all my life i nearly loose my life on this process thinking everyday knowing fully well that all my hope of living is gone.
I am a teacher from Oakes i have saved so many years and when i heard and read online about growing your income through bitcoin it sounds so very interesting to me that i had to invest all i have on the platform but not knowing that they are not the real legitimate investment company i fall prey for them they used me and made away with my money i could not access my password i was worried and was having a thought of suicide but one mind came to me and ask me to stumble online to see if there would be any legitimate recovery company that can retrieve scammed crypto. I found so many companies online but my mind pushed me to work with The [Cyber Tech Wizard] and the rest was history.
My money was reversed back and i was been taught so many things on how to guard my money increase my money grow income without falling into scam through The help Cyber Tech Wizard. You can also reach out to them if fallen victim V.i.A. Email cyber tech wizard @ cyber services DOT com 7
7
