Join devRant
Do all the things like
++ or -- rants, post your own rants, comment on others' rants and build your customized dev avatar
Sign Up
Pipeless API

From the creators of devRant, Pipeless lets you power real-time personalized recommendations and activity feeds using a simple API
Learn More
Search - "long passwords"
-
Long but worth it...
So I was cleaning out my Google Drive last night, and deleted some old (2 years and up) files. I also deleted my old work folder, it was for an ISP I worked for over 2 years ago. After deleting the files I had a little twinge of "Man I hope they're not still using those". But seriously, it'd be a pretty big security risk if I was still the owner of those files... right? Surely they copied them and deleted all the info from the originals. IP addresses, Cisco configs, username and passwords for various devices, pretty much everything but customer info.
Guess who I get a call from this morning... "Hi this is Debbie from 'ISP'. I was trying to access the IP Master List and I can't anymore. I was just told to call you and see if there's any way to get access to it again" (Not her real name...)
I had to put her on hold so I could almost die of laughter...
Me: "Sorry about that Debbie, I haven't worked for that company for over 2 years. Your telling me in all that time no one thought to save them locally? No one made a copy? I still had the original documents?!"
Long pause
D: "Uh... Apparently not..."
Another long pause
D: "So is there any way you can give me access to them again?"
Me: "They're gone Debbie. I deleted them all last night."
D: Very worried voice "Can... Can you check?"
This kids is why you never assume you'll always have access to a cloud stored file, make local copies!!
A little bit of background on this company, the owner's wife fired me on trumped up "time card discrepancy" issues so she could hire her freshly graduated business major son. The environment over there was pretty toxic anyway...
I feel bad for "Debbie" and the other staff there, it's going to be a very bad week for them. I also hope it doesn't impact any customers. But... It is funny as hell, especially since I warned the owner as I was clearing out my desk to save copies, and plan on them being gone soon. Apparently he never listened.
This is why you should have a plan in place... And not just wing it...
PS. First Post!25 -
The programmer and the interns part 2.
We will discuss numerous events that happened over the past week or so.
Case 0:
We had our weekly engineering meeting. The interns were invited as well.
We hold meetings in the generic, big, corporate meeting rooms with a huge table in the middle.
There were more than enough chairs for everyone yet the most motivated and awkward intern (let's call him Simon) chose to stand, cause "it's cool man, I always stand". At this point we all know that he probably read about Agile stand up meetings and is confusing it with this one. Otherwise he's simply trying to stand out from the rest. (See what I did there?)
Anyway the meeting has started way later than planned (what a surprise) and took much longer than Simon expected. Everybody is sitting and listening to the CTO while occasionally glancing at the weird looking intern standing awkwardly and refusing to sit because it would make his original intentions pointless. He even tried to nod whith a serious face and his hands crossed when the CTO said something and looked at his general direction. The meeting was about a hour and a half long but with the delay it was at least 2.5 hours.
At the end Simon was so exhausted that he fell asleep on the office puff, was forgotten and locked inside. 3 hours later when I was home I received a call from him with his sleepy-trying-to-sound-awake voice telling the news. Lucky there's a 24/7 Noc team that could rescue him.
Case 1:
An intern who was late on his Linux test connected to every test VM (should I remind you that each one has a personal VM but they share passwords for their roots?) and tried to reset it with "sleep 10s; shutdown -h now".
He took down all 13 of those so I had to turn them on and switch passwords again.
Case 2:
One of the interns didn't do any of his training chores. Apparently he forgot what he was told to use, ignored all online documentation and used Windows CMD with Linux commands for almost a week already.
Case 3:
Simon uses Vim to write all text possible. Even mails, he then selects all and copies into the mail body. He spent half a day on a homework task I gave them. He wrote everything inside one text file using Vim. When he was done he saved the file and quit the editor. He then said "Oh shit! I've forgot to sign my name!". I explicitly told him that theres absolutely no need for that because I see which mail the file was sent from. He said "I don't even need a program for that!" and gave a couple of strokes on the keyboard.
Later I received an email from him with a .txt attachment. When I opened it the only text that was inside was "by Simon ;)".
I logged to his machine and checked the last command ran on the file:
echo "by Simon ;)" > linuxtasks.txt
Case 4:
The girl here uses a MacBook. She keeps getting confused with the terminal windows and rebooting her own machine instead of the remote VM.
Case 5:
Haven't checked yet how this happened but one of the interns deleted the gui from his local Centos.33 -
Omg...
T-Mobile AT was asked, why they store passwords in plain text, and in a long discussion, they answered this (see img)
I don't know, if this is a late april fool... 25
25 -
Da Fuck!?!
Yesterday I found some abnormal activity on my server, someone was trying to brute force my ssh as root since two days! Started raging and installed fail2ban (which automatically bans an IP if it fails to log X times and eventually sends me an email). Woke up this morning to find that a fucking Chinese guy/malware spent the whole night trying to brute Force me!
Fucking cunt! Don't you have any better to do!!
My key is a 32 characters long encrypted key, with the ban he can try 3 passwords /2 hours, good luck brute forcing it you bitch!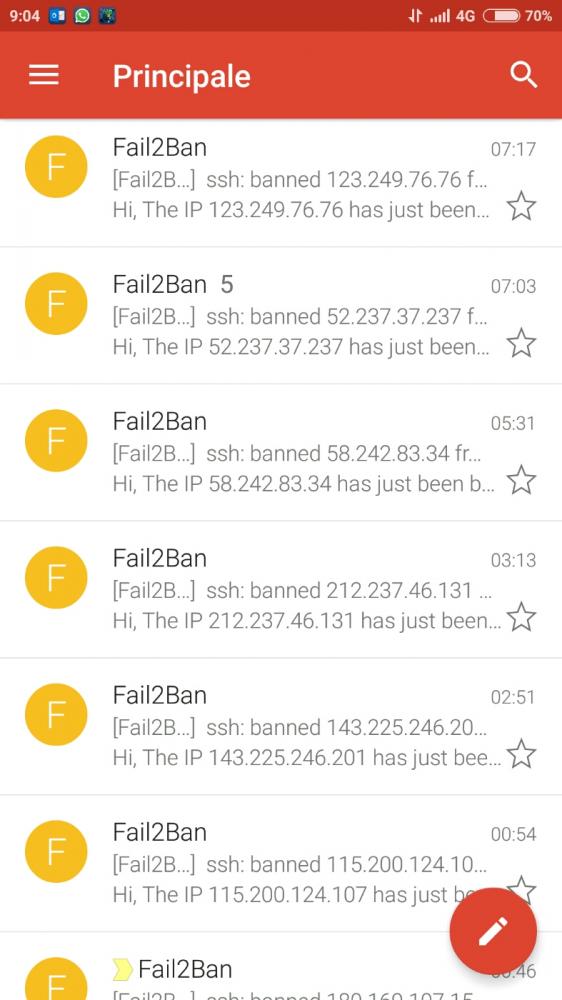 36
36 -
Me: *enters password on phone (long PIN)*
Person next to me is looking at my phone WHILE I enter my password, and as I look at him, he doesn't even turn away and even has the nerve to say:
"Wow, why do you have such a long password!"
Μy answer: "Because of security reasons."
What I actually wanted to say:
"Because of pieces of SHIT like you who can't keep their eyes to themselves, even when PASSWORDS are involved, you FUCK! Guess why everytime I enter a password in public, I have to dim my screen and turn my screen sideways? Because of fuckheads like you, not knowing shit about privacy and security! Fuck you!"7 -
So I was looking at the linux environment at my new job. Found 2 VM's in the local network, only one of them is documented. Noone knows about the other one or what it does, let alone usernames and passwords.
Spent over an hour trying to break in, only to find out that a couple of bored devs, that have long since left the company, set up a game server on there and noone noticed it for the past 3 years..5 -
Our website once had it’s config file (“old” .cgi app) open and available if you knew the file name. It was ‘obfuscated’ with the file name “Name of the cgi executable”.txt. So browsing, browsing.cgi, config file was browsing.txt.
After discovering the sql server admin password in plain text and reporting it to the VP, he called a meeting.
VP: “I have a report that you are storing the server admin password in plain text.”
WebMgr: “No, that is not correct.”
Me: “Um, yes it is, or we wouldn’t be here.”
WebMgr: “It’s not a network server administrator, it’s SQL Server’s SA account. Completely secure since that login has no access to the network.”
<VP looks over at me>
VP: “Oh..I was not told *that* detail.”
Me: “Um, that doesn’t matter, we shouldn’t have any login password in plain text, anywhere. Besides, the SA account has full access to the entire database. Someone could drop tables, get customer data, even access credit card data.”
WebMgr: “You are blowing all this out of proportion. There is no way anyone could do that.”
Me: “Uh, two weeks ago I discovered the catalog page was sending raw SQL from javascript. All anyone had to do was inject a semicolon and add whatever they wanted.”
WebMgr: “Who would do that? They would have to know a lot about our systems in order to do any real damage.”
VP: “Yes, it would have to be someone in our department looking to do some damage.”
<both the VP and WebMgr look at me>
Me: “Open your browser and search on SQL Injection.”
<VP searches on SQL Injection..few seconds pass>
VP: “Oh my, this is disturbing. I did not know SQL injection was such a problem. I want all SQL removed from javascript and passwords removed from the text files.”
WebMgr: “Our team is already removing the SQL, but our apps need to read the SQL server login and password from a config file. I don’t know why this is such a big deal. The file is read-only and protected by IIS. You can’t even read it from a browser.”
VP: “Well, if it’s secured, I suppose it is OK.”
Me: “Open your browser and navigate to … browse.txt”
VP: “Oh my, there it is.”
WebMgr: “You can only see it because your laptop had administrative privileges. Anyone outside our network cannot access the file.”
VP: “OK, that makes sense. As long as IIS is securing the file …”
Me: “No..no..no.. I can’t believe this. The screen shot I sent yesterday was from my home laptop showing the file is publicly available.”
WebMgr: “But you are probably an admin on the laptop.”
<couple of awkward seconds of silence…then the light comes on>
VP: “OK, I’m stopping this meeting. I want all admin users and passwords removed from the site by the end of the day.”
Took a little longer than a day, but after reviewing what the web team changed:
- They did remove the SQL Server SA account, but replaced it with another account with full admin privileges.
- Replaced the “App Name”.txt with centrally located config file at C:\Inetpub\wwwroot\config.txt (hard-coded in the app)
When I brought this up again with my manager..
Mgr: “Yea, I know, it sucks. WebMgr showed the VP the config file was not accessible by the web site and it wasn’t using the SA password. He was satisfied by that. Web site is looking to beat projections again by 15%, so WebMgr told the other VPs that another disruption from a developer could jeopardize the quarterly numbers. I’d keep my head down for a while.”8 -
Day 1 10:00 am
Login to email account (Zimbra)
Your password is incorrect (I entered it correctly, this was a permanent issue ,used to happen in the company with many employees)
Reset your password by logging into internal company portal.
11:00 am
Logged into company portal, somehow. 2 Mbps internet shared among 104 people, you can imagine the speed.
Reset email password
* your password has been sent to your email id*
Are you fucking kidding me? U have emailed me the password to the same email I can't log in to?
Where did the architecture designer get this top notch weed from?
Day 2
Asked HR to reset my password (using a colleague's email)
Day 3
No reply from HR yet
Day 4
I went to meet HR, she's on vacation. So they have 1 person managing the password reset, for 5000 people with no backup person. Cool.
Day 5
Your internal company password has expired. Check your email for link to create new password. This is some next level shit going on.
Day 6
I called up Internal IT team to generate a new email for me.
They asked me to raise a ticket.
I can't raise a ticket because the only way to do so, is through the portal.
Day 7
Nothing. Btw, personal email and all social networks were banned. You can't even open stackoverflow.
And this was a research lab, amazing huh?
Day 8
Loss of pay for 4 days since I can't login to company portal to fill timesheet.
Day 9
HR comes back. Resets my password.
I try to generate my new password for portal.
The password policy:
Password can't be same as last 10 passwords
Passwords expire every week
8 characters minimum, 2 upper case, 2 lower case, NO SPECIAL SYMBOL. WTF. How long do u think its gonna take to crack that?
Fuckers had a company wise policy to automatically lock PC every 1 min if not used. Who the fuck can keep on using it continuously! I'm reading an article, and bam ! Locked. 2 wrong entries and that's it, repeat all steps again. Fuckers really didn't want to let me do my job, just keep on logging in all day.11 -
My private Email Account got hacked when I was in school, and they sent out a mail with something along the lines of "hey, you should really use this product to lose weight, it is great" to all of my contacts. Many of them ignored it, some of them called me to inform me about the issue (the worst part was, long after I used 2fa and changed passwords regularly, they still had my name and contact list, so they just made email adresses that looked like mine and continued to send out spam to my contacts). Anyway, one teacher of mine didn't know that this was a scam and was insulted because I regularly sent emails about her losing weight. And as if the whole situaion, which I couldn't do anything about, wasn't bad enough, my parents and I had do have a 1h conversation (which ended up in me explaining how those hacks work, and luckily she understood, but still). Never again. I prefer those fake ms support guys that call me over this every day.8
-
The company i work for has a jenkins server (for people that don't know jenkins, it's an automated build service that gets the latest git updates, pulls them and then builds, tests and deploys it)
Because it builds the software, people were scared to update it so we were running version 1.x for a long time, even when an exploit was found... Ooh boy did they learn from that...
The jenkins server had a hidden crypto miner running for about 5 days...
I don't know why we don't have detectors for that stuff... (like cpu load being high for 15 minutes)
I even tried to strengthen our security... You know basic stuff LIKE NOT SAVING PASSWORDS TO A GOOGLE SPREADSHEET! 😠
But they shoved it asside because they didn't have time... I tried multiple times but in the end i just gave up...13 -
Story time:
Yesterday I wanted to go to the theater with my girlfriend. It was her idea because as a student you can get reduced tickets for the play, but only via the online store exactely two hours before the play starts. We had already tried two weeks before but with no success. So this time I said i want to be on my pc with a proper browser and not a mobile version like last time. So we are sitting at home me in front of their website on one screen and with a clock on the other screen. Two minutes realy i hit refresh and I get a selection for the reduced tickets, nice.
You would think.
After selecting the amount. ERROR: Can not get your tickets. I was like fuck they are already sold out because it's a popular play. But hey let's try again. I got one ticket but not the second one, okay strange lets try again, same ERROR again. WHAT the FUCK, no feedback what so ever. My girlfriend had then the idea that they maybe restricted the amount for reduced tickets to one (does not state this explicitly but hey lets give it a shot). Use second browser select one ticket. ERROR can not get you the amount of seats. Rage level near to a 1000 why did it work two minutes before but not anymore. Trying around for five more minutes finally got the second ticket.
Now the real fun begins.
Proceeding to checkout should not be that hard you would think, but you need to be registered for that. Okay so let's do that. The salutation is not required neither is the address for the tickets but you need to have a company name??!!!!! The fuck?? I am not self employed and neither are a most other people around here so why is this field mandatory? Beeing a little under stress I decided to found the "asdf" company with my girlfriend.
Now one would think checking out is easy. Not so fast.
After accepting the terms of service another ERROR, unable to accept your data. What data? I did not input anything new? Where does this come from? Ok never mind I am going to pay with credid card that must work!
ERROR: Internal paymentservice initialization failure! Sorry what? I thought maybe I was to long idle in this browser and they do not reserve the tickets for so long (which would be no surprise to me at this point). Let's try again. Nope same error.
Now my rage level was really over 9000 but we really wanted to go so I decided to call the customer SUPPORT. Or better to say I had a answering maching telling me for ten minutes how sorry they are that this takes so long, yeah you bet. Then and this is now really great: the support guy asks me: "What error do you see? Internal paymentservice initialization failure?" I was like, okay he knows this so they need to know how to handle it. FUCK NO. "Sorry I can't help you. This is our payment system maybe they (IT) are doing some maintenance I can't halp you. Call the theater directly good day." Sorry what just happened, you fuckers are the vendors for the tickets for nearly all big events around here and the theater explicitly states to call you for tickets but you can not help me? Like hell.
This process took 25 very frustrating minutes and I was really angry and wanted to quit, then I saw that there is also a paypal option which I had not tried. With very little hope i selected everything for the payment, registered with paypal and they told me I already had an account. So reactivated this five year old account payed with all the mobile passwords and tans to finally, after 30 fucking minutes, get a pdf file for a ticket. Repeated the last step for the second ticket and with some time left to get there we were off.2 -
Idea: Emoji passwords
Bdixbsufhdbe HEAR ME OUT
I know, I know, emojis belong with teenage girls on Snapchat but there are some theoretical benefits to emoji passwords.
Brute Force attacks are useless! With such a wide range of characters and so many different combinations, they just wouldn't be viable.
Dictionary attacks are less useful! Because those require...words.
They can be easier to remember. Tell a story with your emojis. Images are easier to commit to memory than combinations of letters and numbers.
Users would adopt the feature! For whatever reason, the general population fucking loves these things. So emoji passwords probably won't take very long to see use.
I don't know much about this last one, so I saved it for last, but I would imagine that decryption would be more difficult if the available values is quite vast. I dunno how rainbow tables and hash defucking works so I'll just put this here as a "maybe"
😀33 -
TL;DR I'm fucking sick and tired of Devs cutting corners on security! Things can't be simply hidden a bit; security needs to be integral to your entire process and solution. Please learn from my story and be one of the good guys!
As I mentioned before my company used plain text passwords in a legacy app (was not allowed to fix it) and that we finally moved away from it. A big win! However not the end of our issues.
Those Idiot still use hardcoded passwords in code. A practice that almost resulted in a leak of the DB admin password when we had to publish a repo for deployment purposes. Luckily I didn't search and there is something like BFG repo cleaner.
I have tried to remedy this by providing a nice library to handle all kinds of config (easy config injection) and a default json file that is always ignored by git. Although this helped a lot they still remain idiots.
The first project in another language and boom hardcoded password. Dev said I'll just remove before going live. First of all I don't believe him. Second of all I asked from history? "No a commit will be good enough..."
Last week we had to fix a leak of copyrighted contend.
How did this happen you ask? Well the secure upload field was not used because they thought that the normal one was good enough. "It's fine as long the URL to the file is not published. Besides now we can also use it to upload files that need to be published here"
This is so fucking stupid on so many levels. NEVER MIX SECURE AND INSECURE CONTENT it is confusing and hard to maintain. Hiding behind a URL that thousands of people have access to is also not going to work. We have the proof now...
Will they learn? Maybe for a short while but I remain sceptic. I hope a few DevrRanters do!7 -
Paranoid Developers - It's a long one
Backstory: I was a freelance web developer when I managed to land a place on a cyber security program with who I consider to be the world leaders in the field (details deliberately withheld; who's paranoid now?). Other than the basic security practices of web dev, my experience with Cyber was limited to the OU introduction course, so I was wholly unprepared for the level of, occasionally hysterical, paranoia that my fellow cohort seemed to perpetually live in. The following is a collection of stories from several of these people, because if I only wrote about one they would accuse me of providing too much data allowing an attacker to aggregate and steal their identity. They do use devrant so if you're reading this, know that I love you and that something is wrong with you.
That time when...
He wrote a social media network with end-to-end encryption before it was cool.
He wrote custom 64kb encryption for his academic HDD.
He removed the 3 HDD from his desktop and stored them in a safe, whenever he left the house.
He set up a pfsense virtualbox with a firewall policy to block the port the student monitoring software used (effectively rendering it useless and definitely in breach of the IT policy).
He used only hashes of passwords as passwords (which isn't actually good).
He kept a drill on the desk ready to destroy his HDD at a moments notice.
He started developing a device to drill through his HDD when he pushed a button. May or may not have finished it.
He set up a new email account for each individual online service.
He hosted a website from his own home server so he didn't have to host the files elsewhere (which is just awful for home network security).
He unplugged the home router and began scanning his devices and manually searching through the process list when his music stopped playing on the laptop several times (turns out he had a wobbly spacebar and the shaking washing machine provided enough jittering for a button press).
He brought his own privacy screen to work (remember, this is a security place, with like background checks and all sorts).
He gave his C programming coursework (a simple messaging program) 2048 bit encryption, which was not required.
He wrote a custom encryption for his other C programming coursework as well as writing out the enigma encryption because there was no library, again not required.
He bought a burner phone to visit the capital city.
He bought a burner phone whenever he left his hometown come to think of it.
He bought a smartphone online, wiped it and installed new firmware (it was Chinese; I'm not saying anything about the Chinese, you're the one thinking it).
He bought a smartphone and installed Kali Linux NetHunter so he could test WiFi networks he connected to before using them on his personal device.
(You might be noticing it's all he's. Maybe it is, maybe it isn't).
He ate a sim card.
He brought a balaclava to pentesting training (it was pretty meme).
He printed out his source code as a manual read-only method.
He made a rule on his academic email to block incoming mail from the academic body (to be fair this is a good spam policy).
He withdraws money from a different cashpoint everytime to avoid patterns in his behaviour (the irony).
He reported someone for hacking the centre's network when they built their own website for practice using XAMMP.
I'm going to stop there. I could tell you so many more stories about these guys, some about them being paranoid and some about the stupid antics Cyber Security and Information Assurance students get up to. Well done for making it this far. Hope you enjoyed it. 26
26 -
Let me tell you a story:
One upon a time poor lil PonySlaystation received a call. It was a nice guy who cried about his WordPress website had been hacked. So the clusterfuck began...
He gave me the login credentials for the hosting back-end, DB, FTP and CMS.
A hacked WP site was not new for me. It was probably the 6th of maybe 10 I had to do with.
What I didn't expect was the hosting back-end.
Imagine yourself back in 1999 when you tried to learn PHP and MySQL and all was so interesting and cool and you had infinite possibilities! Now forget all these great feelings and just take that ancient technology to 2018 and apply it to a PAID FUCKING HOSTING PROVIDER!
HOLY FUCKING ASSRAPE!
Wanna know what PHP version?
5.3.11, released the day before gomorrah was wiped.
The passwords? Stored in fucking plaintext. Shown right next to the table name and DB user name in the back-end. Same with FTP users.
EXCUSE ME, WHAT THE FUCK?!
I have to call Elon Musk and order some Boring Company Flame Throwers to get rid of this.
Long story long, I set up a new WP, changed all passwords and told the nice guy to get a decent hoster.4 -
It was a normal school day. I was at the computer and I needed to print some stuff out. Now this computer is special, it's hooked up onto a different network for students that signed up to use them. How you get to use these computers is by signing up using their forms online.
Unfortunately, for me on that day I needed to print something out and the computer I was working on was not letting me sign in. I called IT real quick and they said I needed to renew my membership. They send me the form, and I quickly fill it out. I hit the submit button and I'm greeted by a single line error written in php.
Someone had forgotten to turn off the debug mode to the server.
Upon examination of the error message, it was a syntax error at line 29 in directory such and such. This directory, i thought to myself, I know where this is. I quickly started my ftp client and was able to find the actual file in the directory that the error mentioned. What I didn't know, was that I'd find a mountain of passwords inside their php files, because they were automating all of the authentications.
Curious as I was, I followed the link database that was in the php file. UfFortunately, someone in IT hadn't thought far enough to make the actual link unseeable. I was greeted by the full database. There was nothing of real value from what I could see. Mostly forms that had been filled out by students.
Not only this, but I was displeased with the bad passwords. These passwords were maybe of 5 characters long, super simple words and a couple number tacked onto the end.
That day, I sent in a ticket to IT and told them about the issue. They quickly remedied it by turning off debug mode on the servers. However, they never did shut down access to the database and the php files...2 -
OK I can't deal with this user anymore.
This morning I get a text. "My laptop isn't getting emails anymore I'm not sure if this is why?" And attached is a screenshot of an email purporting to be from "The <company name> Team". Which isn't even close to the sort of language our small business uses in emails. This email says that his O365 password will soon be expiring and he needs to download the attached (.htm) file so he can keep his password. Never mind the fact that the grammar is awful, the "from" address is cheesy and our O365 passwords don't expire. He went ahead and, in his words, "Tried several of his passwords but none of them worked." This is the second time in less than a year that he's done this and I thought we were very clear that these emails are never real, but I'll deal with that later.
I quickly log into the O365 admin portal and reset his password to a randomly-generated one. I set this to be permanent since this isn't actually a password he should ever be needing to type. I call him up and explain to him that it was a phishing email and he essentially just gave some random people his credentials so I needed to reset them. I then help him log into Outlook on his PC with the new password. Once he's in, he says "so how do I reset this temporary password?" I tell him that no, this is his permanent password now and he doesn't need to remember it because he shouldn't ever need to be typing it anyway. He says "No no no that won't work I can't remember this." (I smile and nod to myself at this point -- THAT'S THE IDEA). But I tell him when he is in the office we will store the password in a password manager in case he ever needs to get to it. Long pause follows. "Can't I just set it back to what it was so I can remember it?"9 -
Recently, one of our passwords was accidently published on a public page for a few minutes before it was noticed and removed. Unfortunately, this password opens nearly every locked account so it's a pretty big deal.
Management was informed of this mistake and told that we should change the passwords as well as implement a few other protocols to make sure this doesn't happen again including things like unique passwords, more secure passwords, using a password manager, etc.
Their response? It wasn't online long, probably no one saw it. There will be no changes in how we handle ours or our clients' secure passwords.6 -
Microsoft brute-forces password-protected archives in OneDrive.
“Microsoft will decrypt, open, and scan protected Zip archives uploaded to the company's cloud servers in search of potential computer threats. Security researcher Andrew Brandt recently discovered the issue while trying to share malware samples with other researchers through SharePoint.”
This is when I encrypt my archives, I use _very_ long passwords generated by Bitwarden. Like this: qkYdE5i@27yHTTj8YsMDKQ9^mo$j@!P^M4qA95Y5VqR*53otAMuMv$9sdxtF4HAuNdAYoW9RPVxucJ3
Good luck bruteforcing that, Microsoft!
https://techspot.com/news/... 10
10 -
The entire IT department was HATED by the rest of the company at the last place I worked because of the complete ineptitude of the IT director and the executives refusing to do anything about it.
I was hired as a sys-admin and on my first day I knew I was in trouble. The help desk was just two guys and the only other sys-admin was the IT director. Our tiny team was supposed to handle everything for a company with a couple thousand employees spread across the country.
There was a budget for staffing but nobody would stick around for too long because of the IT director.
Here are some highlights:
- Servers were so far out of date that it was scary
- There was no documentation besides an excel spreadsheet with some passwords and IPs
- He just DISAPPEARED for a month ???
Turns out, he's related to one of the executives and was given the position with next to no prior experience. Nepotism is a bitch and I'm so glad I was only there for six months.4 -
Fucking hell with the password fields.
Why in the fucking hell you can't tell me what's the max characters count? Why I have to deal with auto-truncated passwords after the fact?
Go eat exquisite shit, peasant punks, pussy cutters.2 -
*logs in to pc*
- Your password will expire in 3 days. Consider changing it.
+ yeah sure...
*tries to change password*
- Your password must be different from your old 25 passwords
+ ....
+ What the fuck?!? I mean, really, what the fuck is this bullshit? You force me to use EXACTLY 8 char long passwords and this? Fuck you!5 -
Long story short: University fucked up single sign on.
For every online service I have, I set a different password, randomly generated ~ 20 characters long. At our university we have multiple systems but they offer a single sign on service which is quite nice because it is so non-transparent which service now uses which authorization. I changed my password a while ago and around the same time they also updated our mail client. Since then I am not able to log in which is not a big deal for me because I have mail forwarding.
Yesterday however I needed another service and also got rejected with my password. I knew from a friend that the passwords are fucked up and that some services have different restrictions (only 12 chars max.), so I decided to search how to reset my password. What the fuck was wrong with these people? It takes you five different pages to get the tiniest bit of information how to reset the password. Then on one page you can login with your single sign on and change the password. On that page you can also set the single sign on password, but if you enter an invalid password (in respect of the the other services) guess what? No feedback that you just locked yourself out of half the systems. Nice job. Also the password requirements are not next to the input fields where you change the password. Noo. That would be way to easy, remember the little small one line on the wall of text three pages ago? There you go.
Ok step one done. Now it should work, shouldn't it? Ohh no not so fast. One needs to activate the seperate service. Where you ask? Perfectly fine question. On the top of page four is a fucking one line table which looks like some five year old had some fun in excel. The button which takes you to the activation page is nearly invisible because of the non existing contrast. Also it is not a button but some arrow pointer thingy. Behind set arrow you have a page listing all differnt kinds of services, the description which you find on page two btw. No padding to decipher this shit what so ever. Nearly on the bottom is your needed button. Yes finally.
Finally I want to login, no good. Try again. Still no good. Go back to the fucked up excel table look at my username and think to myself what's the difference here? The table is so small and again no margin or padding. Apparently they cut of the last character of my normal username which i have which is fucking ridiculous.
What is wrong with you people, we are a TECHNICAL UNIVERSITY, is it so hard for you to find someone decend to unify this shit?1 -
I might lose my job this week
I'm part of a team of 2 tech people
We were hired as programmers. But over these past 10 months we've done everything from helpdesk to fixing network infrastructure, i setup a backup server for the company, started properly managing the companies passwords,and a host of other things not in my contract.
But my boss is changing the deadline again and she refuses to listen to anyone's concerns, she doesn't understand the complexity of what she wants and since the best we've done so far can be considered at best a prototype in my opinion shes going to be disappointed
So at the next meeting me and my coworker are going to politely list our grivences point out all shes had us do at the same time and the impossible deadlines.
I've seen herpitch a fit for less so I'm fully prepared to be fired in rage in which case I'll compile the documentation and information on what we've done to email her.
But I'm pretty sure she won't find anything long term for the 40k salary shes expecting. Especially with how slow she is to do work herself. I was supposed to be on company health insurance since October 2020
In a way I'm kinda relieved at the potential of being fired.2 -
One of my clients got hacked.
FML. It was fucking bad passwords by a team member.
Google has now blacklisted the domain.
Removed the shady code, requested for review. Hope it recovers soon.
Any idea how long it takes for Google to remove the red warning page before you even enter the page ?2 -
A few days ago Aruba Cloud terminated my VPS's without notice (shortly after my previous rant about email spam). The reason behind it is rather mundane - while slightly tipsy I wanted to send some traffic back to those Chinese smtp-shop assholes.
Around half an hour later I found that e1.nixmagic.com had lost its network link. I logged into the admin panel at Aruba and connected to the recovery console. In the kernel log there was a mention of the main network link being unresponsive. Apparently Aruba Cloud's automated systems had cut it off.
Shortly afterwards I got an email about the suspension, requested that I get back to them within 72 hours.. despite the email being from a noreply address. Big brain right there.
Now one server wasn't yet a reason to consider this a major outage. I did have 3 edge nodes, all of which had equal duties and importance in the network. However an hour later I found that Aruba had also shut down the other 2 instances, despite those doing nothing wrong. Another hour later I found my account limited, unable to login to the admin panel. Oh and did I mention that for anything in that admin panel, you have to login to the customer area first? And that the account ID used to login there is more secure than the password? Yeah their password security is that good. Normally my passwords would be 64 random characters.. not there.
So with all my servers now gone, I immediately considered it an emergency. Aruba's employees had already left the office, and wouldn't get back to me until the next day (on-call be damned I guess?). So I had to immediately pull an all-nighter and deploy new servers elsewhere and move my DNS records to those ASAP. For that I chose Hetzner.
Now at Hetzner I was actually very pleasantly surprised at just how clean the interface was, how it puts the project front and center in everything, and just tells you "this is what this is and what it does", nothing else. Despite being a sysadmin myself, I find the hosting part of it insignificant. The project - the application that is to be hosted - that's what's important. Administration of a datacenter on the other hand is background stuff. Aruba's interface is very cluttered, on Hetzner it's super clean. Night and day difference.
Oh and the specs are better for the same price, the password security is actually decent, and the servers are already up despite me not having paid for anything yet. That's incredible if you ask me.. they actually trust a new customer to pay the bills afterwards. How about you Aruba Cloud? Oh yeah.. too much to ask for right. Even the network isn't something you can trust a long-time customer of yours with.
So everything has been set up again now, and there are some things I would like to stress about hosting providers.
You don't own the hardware. While you do have root access, you don't have hardware access at all. Remember that therefore you can't store anything on it that you can't afford to lose, have stolen, or otherwise compromised. This is something I kept in mind when I made my servers. The edge nodes do nothing but reverse proxying the services from my LXC containers at home. Therefore the edge nodes could go down, while the worker nodes still kept running. All that was necessary was a new set of reverse proxies. On the other hand, if e.g. my Gitea server were to be hosted directly on those VPS's, losing that would've been devastating. All my configs, projects, mirrors and shit are hosted there.
Also remember that your hosting provider can terminate you at any time, for any reason. Server redundancy is not enough. If you can afford multiple redundant servers, get them at different hosting providers. I've looked at Aruba Cloud's Terms of Use and this is indeed something they were legally allowed to do. Any reason, any time, no notice. They covered all their bases. Make sure you do too, and hope that you'll never need it.
Oh, right - this is a rant - Aruba Cloud you are a bunch of assholes. Kindly take a 1Gbps DDoS attack up your ass in exchange for that termination without notice, will you?4 -
My company email:
- It's time for the monthly password change!
<writes the usual passwod>
- The password must be over 50 characters long!
<adds more letters>
- The password must have numbers!
<adds some numbers, though it's getting irritating>
- The password must have special characters!
<wtf?? Adds a pound character>
- The password must have at least 20 different special characters!
<da fuq???>
- The password must be at least 50 characters, only special characters and invisible tab/LF/CR characters and it must be changed daily!
<head explodes>
- Thank you! Now please sign in with your new password for 200 times per day.
<closes the laptop and starts using Remington type writer>
Usually these remainders start popping up during the 1st vacation day. When you return to the office, the account is already locked.
And then you wonder why people have the passwords written on a post-it or as a plain txt file in SkyDrive.11 -
So I enventually spent 2 years working for that company with a strong b2b market. Everything from the checkouts in their 6 b2c stores to the softwares used by the 30-people sales team was dependant on the main ERP shit home-built with this monstruosity we call Windev here in France. If you don't know it just google and have some laugh : this is a proprieteray FRENCH language. Not french like made by french people, well that too, but mostly french like the fucking language is un fucking french ! Instructions are on french, everything. Hey that's my natural language okay, but for code, really ?
The php website was using the ERP database too, even all the software/hardware of the massive logistic installation they had (like a tiny Amazon depot), and of course the emails of all employees. Everything was just handled by this unique shitty and so sloooooow fucking app. When there was to many clients on the website or even too many salespeople connected to the ERP at the same time, every-fuckin-piece of the company was slowing down, and even worse facing critical bugs. So they installed a monitor in the corner of a desk constantly showing the live report page of Google analytics and they started panic attacks everytime it was counting more than 30 sessions on the website. That was at the time fun and sad to observe.
The whole shit was created 12 years ago and is since maintened locally by one unique old-fashion-microsoft dev who also have to maintain all the hardware of all the fucking 150+ people business. You know, when the keyboard of anyone is "broken" cause it's unplugged... That's his job too. The poor guy was totally overstressed on a daily basis and his tech knowledge just saddly losts themeselves somewhere in the way. He was my n+1 in a tech team of 3 people : him, a young and inexperimented so-called "php developer" who was in charge of the website (btw full of security holes I discovered and dealed with when I first arrive at the job), and myself.
The database was a hell of 100+ tables of business and marketing data with a ton of specific logic added on-the-go during years. No consistent data model or naming. No utf8. Fucked up relations that ends with queries long enough to fill books. And that's not all, all the customers passwords was just stored there uncrypted. Several very big companies and administrations were some of these clients. I was insisting on the passwords point litterally all the time, that was an easy security fix and a good start... But no, in two years of discussions on the subject I never achieved to have them focusing on other considerations than "our customers like that we can remind them their password by a simple phone call if they lost it". What. The. Fuck. WHATTHEFUCK!
Eventually I ran myself out of this nightmare. I had a few bad jobs already, and worked on shitty software already. But that one really blows my mind (and motivation for a time too). Happy it's over.1 -
I'd never do anything "risky" in a prod environment if I considered it so at the time, but in retrospect there's *lots* of things considered risky now (both from a security and good practice viewpoint) that were standard practice not long ago:
- Not using any form of version control
- No tests (including no unit tests)
- Not considering XSS vulnerabilities
- Completely ignoring CSRF vulnerabilities
- Storing passwords as unsalted MD5 hashes (heck that was considered very *secure* in the days of plaintext password storage.)
...etc. I'm guilty of all of those previously. I daresay in the future there will be yet more things that may be standard practice now, but become taboos we look back on with similar disdain.1 -
Scored another win as the family tech guy! I found out my wife's sister and her husband were storing all their passwords in a Excel spreadsheet. Long story short they are now using a password manager. 😁1
-
Let's talk about the cargo cult of N-factor authentication. It's not some magic security dust you can just sprinkle onto your app "for security purposes".
I once had a client who had a client who I did server maintenance for. Every month I was scheduled to go to the site, stick my fingerprint in their scanner, which would then display my recorded face prominently on their screens, have my name and purpose verified by the contact person, and only then would the guards let me in.
HAHA no of course not. On top of all of that, they ask for a company ID and will not let me in without one.
Because after all, I can easily forge my face, fingerprints, on-site client contact, appointment, and approval. But printing out and laminating a company ID is impossible.
---
With apologies to my "first best friend" in High School, I've forgotten which of the dozens of canonicalisations of which of your nicknames I've put in as my answer to your security question. I've also forgotten if I actually listed you as my first best friend, or my dog - which would actually be more accurate - and actually which dog, as there are times in my High School life that there were more tails than humans in the house.
I have not forgotten these out of spite, but simply because I have also forgotten which of the dozen services of this prominent bullshit computer company I actually signed up for way back in college, which itself has been more than a decade ago. That I actually apparently already signed up for the service before actually eludes me, because in fact, I have no love for their myriad products.
What I have NOT forgotten is my "end of the universe"-grade password, or email, or full legal name and the ability to demonstrate a clear line of continuity of my identity from wherever that was to now.
Because of previous security screwups in the past, this prominent bullshit company has forced its users to activate its second, third, and Nth factors. A possibly decade-old security question; a phone number long lost; whatever - before you can use your account.
Note: not "view sensitive data" about the account, like full name, billing address, and contact info. Not "change settings" of the account, such as changing account info, email, etc. Apparently all those are the lowest tier of security meant to be protected by mere "end of the universe"-grade passwords and a second factor such as email, which itself is likely to be sold by a company that also cargo cults N-factor auth. For REAL hard info, let's ask the guy who we just showed the address to "What street he lived in" and a couple others.
Explaining this to the company's support hotline is an exercise in...
"It's for your security."
"It's not. You're just locking me out of my account. I can show you a government ID corroborating all the other account info."
"But we can't, for security."
"It's not security. Get me your boss."
...
"It's for security."8 -
Workarounds are great. I remember one time, I had a server that let anyone access any file as long as the knew the right path. I wanted to store data in a .txt (it wasnt secure passwords or anything, so calmyourtities), but then had access too it. Now, this server wasn't running anything except PHP, so I created a database.php, and within was just some php tags. I ended up modifying the database.php from other PHP scripts and storing all the data as PHP comment, then parsing thru it as I needed, so loading mydomain.biz/database.php wouldn't show the data. ex of my database.php (to all that might not understand because I'm bad at explaining):
<?php
//USER1:DATA1
//USER2:DATA2
?>2 -
*leaning back in the story chair*
One night, a long time ago, I was playing computer games with my closest friends through the night. We would meet for a whole weekend extended through some holiday to excessively celebrate our collaborative and competitive gaming skills. In other words we would definitely kick our asses all the time. Laughing at each other for every kill we made and game we won. Crying for every kill received and game lost. A great fun that was.
Sleep level through the first 48 hours was around 0 hours. After some fresh air I thought it would be a very good idea to sit down, taking the time to eventually change all my accounts passwords including the password safe master password. Of course I also had to generate a new key file. You can't be too serious about security these days.
One additional 48 hours, including 13 hours of sleep, some good rounds Call of Duty, Counter Strike and Crashday plus an insane Star Wars Marathon in between later...
I woke up. A tiereing but fun weekend was over again. After I got the usual cereals for breakfast I set down to work on one of my theory magic decks. I opened the browser, navigated to the Web page and opened my password manager. I type in the password as usual.
Error: incorrect password.
I retry about 20 times. Each time getting more and more terrified.
WTF? Did I change my password or what?...
Fuck.
Ffuck fuck fuck FUCKK.
I've reset and now forgotten my master password. I completely lost memory of that moment. I'm screwed.
---
Disclaimer: sure it's in my brain, but it's still data right?
I remembered the situation but until today I can't remember which password I set.
Fun fact. I also could not remember the contents of episode 6 by the time we started the movie although I'd seen the movie about 10 - 15 times up to that point. Just brain afk. -
The ticket system blokes - episode 3
So we always had and have very awful performance with our ticket system. You can't get anything to load in under ~4s normally. Now since it has gotten worse over the last weeks i decided to set aside a few hours to closely watch our SQL server.
After i identified a culprit that was hogging the CPU almost every 2 minutes i looked at other long running queries in the server and found out where exactly the 4s come from.
6 tables from various DBs. Sure, no problem.
Left Outer Join. Sure, why not.
Querying every fucking column in every fucking table explicitly adding up to a whopping 160 columns which they need not even 10% of. We're talking about session IDs, passwords, stock count, IBANs and all that stuff to show the work done on a ticket. Absolutely not.
So i extracted the query and reduced it to the stuff we need and the execution time went from 4 seconds to almost instant.
The funny thing is that their idea of performance optimization is throwing LIMIT around everywhere to get these monstrous queries under control.
So in the next few days I'll have an appointment with their lead programmer. I'm looking forwards to it.
So out of curiosity: does anyone know an SQL builder or toolset that does shit like
SELECT X AS [t0_c0],
SELECT Y AS [t0_c1],
SELECT Z AS [t1_c0],
and so on? I'd like to know how they got to this point.4 -
Soo... Let me get this straight... My boss reeeeeeally wants me to reconfigure our database system to sync data between each of our 15 sites... Let me this about this...
Our database is an MS Access database originally written about 17 years ago. It was written as a standalone database that runs a unique instance for each of our sites.The person responsible for the database (still not the original developer) before I took over 6 years ago bragged about how they were "an 80s developer" (w...t...f!). Even with all of the fixes and additions (additions because... F&$#ing of course there are!) It's still basically held together by duct tape and spit.
Hmmm... Ok, still possible. What's the environment I'm working in... I have absolutely ZERO control of our workplace network... That's a whole other department. Due to the nature of the workplace (and it's sites) there is extreme limitation on network access.
Well... If I'm Reeeeeeally nice to the people in charge of the network, maaaaaybe they can give me access to a little server space.
A very long shot, but, doab.... Oh, the boss would really like this handled in the next couple months...
F$#k you! There is no way on God's (still) green earth that I... Alone... Can rewrite a legacy database... written across 4 or 5 different versions of FU$KING MS Access, and give 15 sites, with extremely limited networking, real time data sync in... Oh, a few months.
Now, I do not work with "computer people". I'm usually lucky when my coworkers remember their passwords (which, even if they don't, WHY tell ME! I don't run the network!)
And when I tell my boss basically what I just said... In a nice, pleasant way... They suggest I'm not giving the problem enough thought...
FU#K YOU IGNORANT ASS! Write me a ToDo list in MS Access (no, I'm not going to tell you where to start) in under an hour then, MAYBE, we can talk about... No... Just NO... Can't be done!
*Takes deep breath* so... Lovely weather we're having, right?3 -
Windows 10 Action Center yesterday alerted me to set a PIN for my laptop.
Turned on PC this morning and typed in my regular password then realized it wanted the PIN.
Thinking how this feature came to be....
1. Windows wants you to link your login to your Microsoft/Hotmail Account and it makes it a pain in the ass to set a seperate one (Windows 8)
2. 2018 arrived an logins are a pain, everything is autologin or PIN/code based (aka short 'unsecure' passwords)
3. MS backtracks and realizes email logins are too long so they make a partial fix which basically reverts back to the pre-Win8 days of a seperate system login.. except now its called a new feature!
I realized now under enter a PIN the reason for the checkbox that says: Allow symbols and letters. It's a nice way of saying: please type in your old password again.
**Also rant #2: cuz i dont feel like waiting 1hr**
I felt great yesterday when my boss told me apparantly I have like an Expert designation at the company.
Feel like crap today cuz some user is complaining about some report:
- they asked us to create months ago
- now complaining its all wrong but never gave any formal requirements and actually did sign off on it during testing
- FIXED ASAP
HELLO!!!!!!!!!!! STOP MAKING IT SOUND LIKE IT'S MY FAULT U CAN'T BE BOTHERED TO PROVIDE CLEAR REQUIREMENTS AND THEN TAKING FOREVER TO COME BACK WITH UR PROBLEMS AND NOW NEED IT FIXED ASAP BY USING A NEW DATA SOURCE THAT I HAVE NO IDEA WHAT THE FUCK IS SINCE U USED A RANDOM ABBREVIATION LIKE I CAN MIND READ.
IF I COULD MINDREAD, ID BE WORKING ON A PLAN TO GET UR ASS FIRED.....
Happy friday and long weekend... Got 3 days to relax before i need to deal with this shit again...2 -
Make all fancy Azure blob storage with SFTP connection through firewall with dedicated public IP.
...to just find out that the webcameras you want to send stuff to the blob storage take in max 16 or 30 character passwords for sFTP. While the autogenerated passwords for SFTP in Azure are 32 characters long.
WHO THE HELL RESTRICTS PASSWORD LENGTH!? ASfjksdnfjksdjfnjksdakfadsnjkfjdsa10 -
A long time ago you sent me an email with the subject 'I love you', I then got so excited that I forwarded the letter to all my contacts, and they forwarded it too.. I can't describe the words for the feelings I had back then for you. I felt into love with you, really. But there were always troubling moments for me.
For example when 'Code Red' showed up and found your backdoor. Man I was pissed at that time. I didn't know what to do next. But things settled, and we found each other again.
And then that other time when this girl named 'Melissa' was sending me some passwords to pr0n sites, I couldn't resist. She was really awesome, but you know, deep in my heart that was not what I wanted. I somehow managed to go back to you and say sorry. We even moved together in our first flat, and later in our own house. That was a really good time, I love to think back at those moments.
Then my friend 'Sasser' came over to us one night, do you remember how he claimed that big shelf in our living room, and overflooded it with his own stuff, so that we haven't a clue we are reading yet offshelve? Wow that was a disturbing experience.
But a really hard time has come when our dog 'Zeus' got kicked by this ugly trojan horse. I really don't want go into details how the mess looked like after we discovered him on our floor. Still, I am very sorry for him that he didn't survived it :(
Some months later this guy named 'Conficker' showed up one day. I shitted my pants when I discovered that he guessed my password on my computer and got access to all my private stuff on it. He even tried to find some network shares of us with our photos on it. God, I was happy that he didn't got access to the pics we stored there. Never thought that our homemade photos are not secure there.
We lived our lives together, we were happy until that day when you started the war. 'Stuxnet..'! you cried directly in my face, 'you are gonna blow up our centrifuges of our life', and yeah she was right. I was in a real bad mood that days back then. I even not tried to hide my anger. But really, I don't know why all this could happen. All I know is, that it started with that cool USB stick I found on the stairs of our house. After that I don't remember anything, as it is just erased from my memory.
The years were passing. And I say the truth here, we were not able to manage the mess of our relationship. But I still loved you when you opened me that you will leave. My 'Heartbleed' started immediately, you stabbed it where it causes the most pain, where I thought that my keys to your heart are secured. But no, you stabbed even harder.
Because not long after that you even encrypted our private photos on our NAS, and now I am really finished, no memory which can be refreshed with a look at our pictures, and you even want my money. I really 'WannaCry' now... -
Long time ago cleared chrome history. Had the clear passwords box checked... Fuck. Spent hours recovering passwords. Then switched to lastpass
-
This shit is long story of my computer experience over my lifetime.
When I was young I got my first PC with windows it was not so bad. It required safe shut down of it’s fat32 partition. From time to time I needed to reinstall it cause of slow down but I got used to it I was only a gamer.
Time passes and I got more curious about computers and about this linux. Everything worked there but installation of anything was complete madness and none of windows programs worked well, and I wanted to play games and be productive so I sticked with windows.
I bought hp laptop once with nvidia card, it was overheating and got broken. So I bought toshiba and all I told to the seller was I want ATI card. Took me 5 minutes to do it and I was faster then my friend buying pack of cigarettes because I was earning money using computer.
Then I grown up running my small one person programming businesses and I wanted to run and compile every fucking program on this world. I wanted linux shell commands. I wanted package manager, and I wanted my os to be simple because I wasn’t earning money by using my os but by programming. So after getting my paycheck I bought mac. I can run windows and linux on vm if I need it. I try not to steal someones work so I didn’t want to run hackintosh. I am using this mac for some time.
Also I use playstation for gaming. Because I only want to run and play game I am not excited about graphics but gameplay. I think I am pragmatic person.
I can tell you something about my mac.
When I close lid it go sleep when I open it wakes up instantly. I never need to wonder if I want to hibernate or shut down or sleep and drain battery. It is fucking simple.
When I want to run or open something it doesn’t want me to wait but it gives me my intellij or terminal or another browser or whatever I search for. Yeah search is something that works.
Despite it got 8 gigs of ram I can run whatever number of programs I want at the same speed. The speed is not very fast sometimes but it’s constant fast.
I have a keychain so my passwords are in one place I can slow down shared internet speed, I can put my wifi in monitor mode and I don’t need to install some 3rd party software.
And now I updated my mac to high sierra, cause it’s free and I want to play with ios compilation. Before I did it I didn’t even backup whole work. I just used time machine and regular backups. And guess what, it still works at the same speed and all I did was click to run update and cook something to eat.
When I got bored I close the lid, when got idea open lid and code shit, not waiting for fucking wakeup or fucking updates.
I wanted to rant apple products I use but they work, they got fucking updates all along at the same time. And all of updates are optional.
I cannot tell that about all apple products but about products I use.
I think I just got old and started to praise my limited time on this world. Not being excited about new crap. When I buy something I choose wisely. I bought iPhone. I can buy latest iPhone x but I bought iPhone 7 cause it’s from fucking metal. And I know that metal is harder then glass, why the fucking apple forgot about it? I don’t know.
I know that I am clumsy and drop stuff. Dropped my phone at least 100 times and nothing.
I am not a apple fan boy I won’t buy mac with this glowing shit above keyboard that would got me blind at night.
I buy something when I know that it can save my time on this world. I try to buy things that make me productive and don’t break after a year.
So now piece of advise, stop wasting your time, buy and update wisely, wait a week or a month or a year when more people buy shit and buy what’s not broken. And if something’s broken rant this shit so next customer can be smarter.
Cheers1 -
In college, during Novell's heyday, I was working on my Certified Network Administrator certification (totally worthless, in retrospect). As I was becoming an expert in all things Novell, I found a security flaw. Using Visual Basic it was possible to code up an exact replica of the Novell login screen that launched at boot time from a batch file stored on a floppy. You could log peoples' usernames and passwords all day as long as they didn't realize your floppy was in the drive, which worked in certain computer lab setups on campus. I wasn't in it for stealing info or being a criminal. I just did it for the lulz. But if I had gained access to a few of the right computers in admin offices on campus, I could've gotten access to anyone's student profiles and grades.
-
I am glad that firefox for android got an overhaul. I've been waiting a long time for more granular settings, before you couldn't even list websites you gave a particular pernission, and FINALLY passwords can't be viewed before authenticating with your fingerprint.
But after over two years I'm just so used to the old design, that it's glaringly obvious how less fluent the new ui is.
Instead of two clicks to access stored passwords you now need 4. And the button to open the tab list is now half my screen away from the actual tabs, and basically the entire screen away from "new tab".
The starting page isn't as good as before, although I hear they're working on it. But what is this shit, it took me like a week to even find the url bar context nenu! 13
13 -
I’m working on a new app I’m pretty excited about.
I’m taking a slightly novel (maybe 🥲) approach to an offline password manager. I’m not saying that online password managers are unreliable, I’m just saying the idea of giving a corporation all of my passwords gives me goosebumps.
Originally, I was going to make a simple “file encrypted via password” sort of thing just to get the job done. But I’ve decided to put some elbow grease into it, actually.
The elephant in the room is what happens if you forget your password? If you use the password as the encryption key, you’re boned. Nothing you can do except set up a brute-forcer and hope your CPU is stronger than your password was.
Not to mention, if you want to change your password, the entire data file will need to be re-encrypted. Not a bad thing in reality, but definitely kinda annoying.
So actually, I came up with a design that allows you to use security questions in addition to a password.
But as I was trying to come up with “good” security questions, I realized there is virtually no such thing. 99% of security question answers are one or two words long and come from data sets that have relatively small pools of answers. The name of your first crush? That’s easy, just try every common name in your country. Same thing with pet names. Ice cream flavors. Favorite fruits. Childhood cartoons. These all have data sets in the thousands at most. An old XP machine could run through all the permutations over lunch.
So instead I’ve come up with these ideas. In order from least good to most good:
1) [thinking to remove this] You can remove the question from the security question. It’s your responsibility to remember it and it displays only as “Question #1”. Maybe you can write it down or something.
2) there are 5 questions and you need to get 4 of them right. This does increase the possible permutations, but still does little against questions with simple answers. Plus, it could almost be easier to remember your password at this point.
All this made me think “why try to fix a broken system when you can improve a working system”
So instead,
3) I’ve branded my passwords as “passphrases” instead. This is because instead of a single, short, complex word, my program encourages entire sentences. Since the ability to brute force a password decreases exponentially as length increases, and it is easier to remember a phrase rather than a complicated amalgamation or letters number and symbols, a passphrase should be preferred. Sprinkling in the occasional symbol to prevent dictionary attacks will make them totally uncrackable.
In addition? You can have an unlimited number of passphrases. Forgot one? No biggie. Use your backup passphrases, then remind yourself what your original passphrase was after you log in.
All this accomplished on a system that runs entirely locally is, in my opinion, interesting. Probably it has been done before, and almost certainly it has been done better than what I will be able to make, but I’m happy I was able to think up a design I am proud of.8 -
Took a long time to update to high sierra yesterday. Doesn't seem like much has changed, apart from some shinier icons. Oh and now having two different passwords for some reason?2
-
i once changed all of the passwords of my main online accounts(google, apple, facebook, telegram, outlook) as they weren't changed for years.
i decided unique and long passwords for each of them.😎
immediately after changing the passwords, i forgot all of them. 😵fortunately, i was able to reset.
Has this ever happened to anyone?3 -
Vivaldi browser seemed a good idea to escape Google's misfeatures without swapping it for Microsoft extensions (Edge) or Firefox / Gecko idiosyncrasies (size / magnification issues on Ubuntu, slow Android version, clunky UI). But there are some ongoing issues that I never experienced in any other user agent (maybe I will when switching to Chromium), like URL completion (port URLs without a protocol aren't prepended with https but trigger a xdg-open dialog, autocomplete prefers obscure deep links with long paths instead of the base URL, browsers seems to forget login passwords by default, etc.) - so Chromium seems like the obvious choice. But there seem to be no more Chromium builds for Android? Anyone else disappointed by Vivaldi has a preferred solution?4
-
I believed the only thing that could humble me was leg day. Guess clicking a shady update link can humble you quicker than a botched deadlift. I had developed my app from the ground up, and that Bitcoin reserve was meant to fuel our international expansion. One minute I was meal-prepping protein pancakes; the next, my wallet was thinner than my fridge on cheat day.
My pulse raced as though I was half-burpee. Panic. Sweating. Guilt. I refreshed the page like cardio, praying the money would somehow reappear. Spoiler: It didn't.
After a long night Googling “how to undo catastrophic life mistakes,” I landed on a cybersecurity webinar. The host casually dropped the name Mighty Hacker Recovery like it was common knowledge. To me, they sounded like the Gandalf of Bitcoin, so I figured they could probably handle my little meltdown.
I reached out to them in a panic, the equivalent of a person who's just discovered they double-booked leg day and pizza night. They responded quicker than my personal best sprint time. They were cool, they were professional, and, most importantly, they didn't laugh when I described how I basically bench-pressed my life savings directly into nothingness.
They got to work immediately. Their team of tech wizards (I’m convinced they actually wear robes) dissected the malware and traced the funds like a GPS tracker on my dignity. Every day, they updated me with progress reports that somehow balanced technical jargon and emotional support, the digital equivalent of a personal trainer shouting, “You got this!” while you struggle under a barbell.
Nine days later, I got the call. Funds recovered. I nearly did a victory lap around my living room but pulled a hamstring from pure excitement. Typical. Due to Mighty Hacker Recovery, I didn't simply get my money back; I got a crash course in cybersecurity that rivals my toughest boot camp. My new digital security routine now rivals my meal plan. I have more passwords than protein shake recipes and back-ups on top of other back-ups.
If you value your gains, both financial and physical, trust me, you want Mighty Hacker Recovery in your corner. They spot you when it matters most. What$app Numb3r + 1 4 0 4 2 4 5 6 4 1 5 email support (at) mightyhackerrecovery (dot) com2 -
New ad self-service portal too hard to integrate ssl and can't have users send their passwords in plaintext.
Setup apache proxy with ssl in same vpc to encrypt traffic to and from vpc.
All good as long as nobody is in my vpc sniffing traffic... -
Legitimate Crypto Recovery Companies: Puran Crypto Recovery Leads the Way
As cryptocurrency grows as a preferred investment, so do the risks of falling victim to scams and technical errors. With individuals losing significant digital assets, the role of legitimate recovery companies becomes vital. Among these, Puran Crypto Recovery (PCR) stands out as a reliable name in the field. This article explores how PCR and other legitimate companies help victims reclaim their assets and offers tips for safeguarding crypto investments.
The Rise of Crypto Scams
Crypto scams have surged in recent years, targeting unsuspecting investors with increasingly sophisticated tactics. From phishing schemes and fake ICOs to Ponzi scams, fraudsters exploit the decentralized and anonymous nature of blockchain transactions. Victims often find themselves at a loss for recourse, emphasizing the importance of specialized recovery services like Puran Crypto Recovery.
Characteristics of Legitimate Crypto Recovery Companies
Legitimate crypto recovery firms share several defining traits:
Transparency: Reputable firms like PCR disclose information about their team, methods, and licenses.
Expertise: Companies should employ seasoned blockchain analysts and recovery specialists familiar with tracking stolen or inaccessible assets.
Proven Success: Positive testimonials and successful case studies bolster credibility. PCR, for instance, has earned trust through its consistent recovery outcomes.
Client-Centric Approach: Clear communication, confidentiality, and client advocacy are hallmarks of legitimate providers.
How to Verify a Crypto Recovery Service
Before entrusting any company, conduct thorough due diligence:
Research: Look up the company online, checking for reviews and any past controversies.
Compliance: Verify the firm’s regulatory standing to ensure it operates within legal frameworks.
References: Contact past clients for firsthand feedback on the company's performance.
With PCR, clients gain peace of mind knowing they are engaging a service with a stellar reputation and transparent processes.
Why Choose Puran Crypto Recovery?
Puran Crypto Recovery leads the industry with its advanced recovery techniques and commitment to ethical practices. Here’s what sets PCR apart:
Free Consultations: PCR provides an initial assessment to determine the feasibility of recovering lost assets.
Advanced Tools: Employing cutting-edge blockchain forensics, the team meticulously traces transactions and identifies illicit activities.
Collaborative Efforts: PCR works closely with clients to gather evidence, trace funds, and, if necessary, initiate legal action.
These qualities make PCR a top choice for victims seeking reliable crypto recovery services.
Tips to Safeguard Your Crypto Assets
While services like PCR provide hope for reclaiming lost funds, prevention remains the best approach. Follow these tips to protect your assets:
Secure Your Wallets: Use wallets with multi-factor authentication and cold storage solutions for long-term holdings.
Create Strong Passwords: Avoid using easily guessable credentials and ensure passwords are unique for each platform.
Stay Updated: Keep abreast of the latest scam techniques to recognize potential threats.
Avoid Sharing Keys: Never disclose private keys or sensitive wallet information, even to seemingly legitimate inquiries.
Conclusion
In a landscape fraught with scams and risks, legitimate crypto recovery companies like Puran Crypto Recovery offer a lifeline to victims of fraud. By combining expertise, transparency, and advanced tools, PCR has emerged as a leader in helping individuals reclaim their stolen assets.
However, prevention is always better than cure. Secure your investments, remain vigilant, and trust only proven recovery services like PCR if the need arises. With diligence and trusted support, you can navigate the cryptocurrency world confidently and securely.
FAQs
Q1: What is a crypto recovery service?
A crypto recovery service helps individuals retrieve lost or stolen cryptocurrency assets using forensic techniques and blockchain expertise.
Q2: How do I verify a recovery company’s legitimacy?
Look for transparency, licenses, and positive client reviews. Contact previous clients to assess their experience.
Q3: Can I recover lost private keys?
Yes, experienced companies like PCR often assist in recovering lost private keys or regaining access to wallets.
Q4: How much do crypto recovery services cost?
Costs vary depending on the complexity of the case. PCR offers free consultations to assess recovery prospects.
Q5: How can I avoid scams?
Use secure wallets, set strong passwords, and remain cautious of unsolicited emails or requests for private keys.1 -
WHATSAPP +1 252 378 7611 PROFESSIONAL BITCOIN RECOVERY EXPERT FOR HIRE CONTACT CYBER CONSTABLE INTELLIGENCE
Information of Cyber Constable Intelligence
WhatsApp info: + 1 2 5 2 3 7 8 7 6 1 1
Email info: (support (@) cyberconstableintelligence ). com)
As a retired dentist, I found myself with ample free time but limited financial security. In search of a way to grow my savings, I turned to cryptocurrency trading. I joined several online forums and communities, where I read about the success others had found with Bitcoin. Their testimonies inspired me to take the plunge. With careful research and strategic investments, I managed to turn my initial investment into $250,000.The financial success brought a renewed sense of purpose and stability to my retirement. However, this newfound prosperity also attracted the envy of someone close to me: my financial advisor, whom I had trusted for years. Unbeknownst to me, he had been monitoring my success closely. One evening, while I was cooking supper, my financial advisor accessed my phone and changed the passwords to my accounts, attempting to transfer my Bitcoin to his wallet. I discovered this betrayal shortly after, feeling a mix of shock, panic, and anger. My financial future was in jeopardy, and I needed to act quickly. In my desperate search for a solution, I stumbled upon Cyber Constable Intelligence, a service specializing in recovering hacked accounts and lost cryptocurrency. With my savings hanging in the balance, I reached out to them, hoping for a miracle. The team at Cyber Constable Intelligence was prompt and professional. They reassured me that, despite the seriousness of my situation, there was a good chance they could help. Their calm and confident demeanor provided some much-needed comfort. They guided me through the recovery process, taking over the technical aspects and working tirelessly to regain control of my accounts. In a remarkably short time, Cyber Constable Intelligence managed to restore my access to my accounts and secure my Bitcoin. The relief I felt was indescribable. Not only had they recovered my funds, but they also provided essential advice on how to enhance the security of my digital assets. This experience taught me several valuable lessons. Firstly, trust must be carefully placed, even with long-term associates. Secondly, it's crucial to secure your digital assets with strong, unique passwords and two-factor authentication. Lastly, seeking professional help in times of crisis can make all the difference. After regaining control of my accounts, I severed ties with my financial advisor and took steps to ensure my assets were protected. Despite the ordeal, I emerged more knowledgeable and determined to safeguard my future. My experience with Cyber Constable Intelligence not only saved my investments but also reinforced the importance of vigilance and security in the digital age. -
As cryptocurrency continues to reshape global finance, safeguarding Bitcoin and other crypto wallets is more important than ever. Unfortunately, wallet access issues—whether due to lost passwords, forgotten seed phrases, or even hacking incidents—are a common challenge for Bitcoin owners. Century Web Recovery, trusted since 2017, has emerged as a reputable resource for those seeking to regain access to their cryptocurrency wallets.
What is Bitcoin Wallet Recovery?
Bitcoin wallet recovery is the process of retrieving access to a Bitcoin wallet when the user is locked out. Wallet access issues can occur for various reasons, such as lost private keys, forgotten passwords, or corrupted wallet files. For those who’ve lost access, reputable recovery services can be an invaluable asset, helping them safely regain control of their funds.
Century Web Recovery offers specialized recovery services that cover a broad range of wallet types and access issues, providing the expertise needed to retrieve lost assets and restore access to cryptocurrency wallets.
Why Wallet Recovery Services Matter
Without access to your wallet, Bitcoin holdings can become permanently inaccessible. The decentralized nature of Bitcoin means there’s no central authority or “forgot password” feature that can restore access. This gap has led to a high demand for trustworthy wallet recovery services like Century Web Recovery, which uses a combination of technical expertise and proprietary tools to assist clients.
Century Web Recovery: Trusted Bitcoin Wallet Recovery Since 2017
Century Web Recovery has built a reputation as a reliable and secure recovery service provider since its establishment in 2017. Their team is composed of experienced blockchain analysts and cybersecurity experts who specialize in recovering wallet access in cases of forgotten passwords, corrupted files, or lost keys. Clients seeking to regain access to Bitcoin wallets can learn more about Century Web Recovery can help by contacting them through the details provided below.
Century Web Recovery Approaches Wallet Recovery
Initial Consultation and Assessment
Century Web Recovery begins with a thorough consultation, understanding the client’s situation and the specific wallet issue. This assessment allows the team to determine the best recovery strategy.
Technical Recovery Process
Century Web uses advanced recovery tools and techniques tailored to different wallet types, whether software, hardware, or paper-based. By leveraging cryptographic methods and advanced decryption software, the team can restore access to wallets securely.
Ensuring Client Security and Confidentiality
Security and confidentiality are top priorities. Century Web Recovery applies secure handling protocols throughout the recovery process, ensuring that clients’ information and assets remain protected.
Recovery Completion and Client Education
Upon successful recovery, Century Web provides clients with guidance on how to safeguard their wallets and private keys to avoid future access issues. This education reinforces wallet security and fosters long-term peace of mind.
Why Choose Century Web Recovery?
Not only does Century Web Recovery have a strong track record of successful recoveries, but it also offers an upfront pricing model to keep costs transparent. For clients who are locked out of their wallets, the technical capabilities and secure approach Century Web offers make it a leading choice in the crypto recovery space.
Contact Century Web Recovery
To learn more or initiate the recovery process, clients can reach out to Century Web Recovery. If you’re locked out of your Bitcoin wallet, now is the time to restore access and regain control of your digital assets with a company that’s trusted since 2017. You can reach out to us by searching us on google century web recovery and get all our contact details.1 -
HOW TO SECURE AND RECOVER YOUR STOLEN CRYPTOCURRENCY/ CONSULT TRUST GEEKS HACK EXPERT
( E m a i l : in fo @ trust geeks hack expert . c o m)
(Te le G r a m:: Trust geeks hack expert)
(w h a t's A p p +1 7 1 9 4 9 2 2 6 9 3)
(E m a i l: Trust geeks hack expert @ f a s t se r v i c e .c o m )
Over five years ago, I lost access to two of my crypto wallets, which I hadn’t used in years. These wallets contained valuable crypto assets, but I had completely forgotten the passwords, recovery phrases, and security questions. After trying everything I could think of to regain access, I was left feeling hopeless, thinking my assets were gone forever. That’s when I came across ( Trust Geeks Hack Expert ), and I can honestly say they changed the course of my life. Initially, I was skeptical. The idea of recovering forgotten crypto wallets seemed almost impossible. However, from the first moment I contacted the team, I felt a sense of hope. The staff was incredibly professional, empathetic, and genuinely dedicated to helping me recover my wallets. They took the time to fully understand my situation, offering clear explanations and reassuring me that they could assist. The recovery process wasn’t immediate, but it was methodical and thorough. The team worked diligently, guiding me through every step of the process and explaining things in a way I could easily understand. At times, I felt frustrated, especially given how long it had been since I last used the wallets. But the ( Trust Geeks Hack Expert ) team remained patient, offering constant support, and helping me stay focused on the end goal. They made sure I felt secure throughout the entire process, which provided me with the confidence I needed to continue. Finally, after several weeks of hard work, I regained access to my wallets. It was an overwhelming and life-changing moment. Not only did I recover my crypto assets, but I also felt an immense sense of relief and accomplishment. What I thought was lost forever was now back in my hands. Thanks to the ( Trust Geeks Hack Expert ) team, I’m incredibly thankful for ( Trust Geeks Hack Expert ) expertise and dedication.2 -
I never imagined I would fall victim to an online scam, but that’s exactly what happened. It started innocently enough. I was on a popular social media platform, browsing through posts when I received a direct message from someone claiming to be a “financial expert.” Their pitch seemed solid, and their promises of quick returns on investments seemed too good to pass up. I did my research—or so I thought—but it wasn’t long before my trust led me into a trap. I made an initial deposit to start the investment, and things moved quickly. The first few days were filled with regular updates and even small returns, which convinced me that I was onto something big. But then, the messages started to change. The returns began to slow down, and when I tried to withdraw my funds, I couldn’t get a response. Panic set in as I realized I’d been scammed. i had lost a significant amount of money, and to make matters worse, the scammers had control over my personal details, including access to some of my financial accounts. Desperate for a solution, I turned to Alpha Spy Nest, a cybersecurity service I had heard of through a friend.From the moment I contacted Alpha Spy Nest, I knew I had made the right choice. They took swift action, immediately conducting a thorough investigation into my digital accounts. They discovered that the scammer had used several techniques to track my online activity, intercept communications, and even mimic legitimate financial websites. Alpha Spy Nest’s team of experts worked tirelessly to gather evidence, trace the scammer’s digital footprint, and recover my lost funds.But it didn’t stop there. Alpha Spy Nest helped me secure my online presence by identifying vulnerabilities in my accounts and recommending tools to fortify my digital defenses. They guided me through implementing multi-factor authentication, strengthened my passwords, and even educated me on how to spot future scams.Within days, they were able to trace the scammer’s digital identity, and with the evidence they provided, law enforcement was able to step in. I regained access to my financial accounts and received a refund of the funds that were stolen, though the emotional toll remained.The experience left me shaken, but Alpha Spy Nest’s professional and supportive team helped me not only reclaim my wealth but also regain my peace of mind. Now, I’m more cautious online, but I know I have the right tools and the right support if anything ever happens again.Thanks to Alpha Spy Nest, I’m no longer a victim. I’m a survivor. You can also reach out to them WhatsApp: +14159714490
 1
1 -
BITCOIN RECOVERY EXPERT FOR HIRE REVIEWS \\ REVENANT CYBER HACKER
Losing a Bitcoin wallet containing a substantial amount of cryptocurrency can be a devastating experience. However, the feeling of despair and loss was transformed into pure happiness when I received the incredible news from REVENANT CYBER HACKER that my lost Bitcoin wallet, holding 132,000 bitcoins, had been successfully recovered. In this article, I will share the rollercoaster emotional journey I went through when I lost my wallet, the subsequent discovery of REVENANT CYBER HACKER, the process they employed to retrieve my precious digital assets, and the lessons learned along the way. This is a story of hope, resilience, and the power of professional recovery services in restoring lost Bitcoin wallets. Ah, the sweet sound of good news. There I was, minding my own business on an average Tuesday morning, when I got a notification that would make any bitcoin enthusiast jump for joy. It was a message from none other than REVENANT CYBER HACKER, informing me that my long-lost bitcoin wallet had been found. And not just any bitcoin wallet, mind you, but one containing a whopping 132,000 units of the beloved cryptocurrency. Now, for those living under a rock or perhaps too preoccupied with the latest cat videos, let me give you a crash course in Bitcoin 101. Bitcoin is a digital currency that has taken the world by storm, captivating the minds of tech-savvy investors and casual enthusiasts alike. It operates on a decentralized network, meaning it doesn't answer to any central authority like a bank. Instead, it relies on blockchain technology, which adds a layer of security and transparency to every transaction. To own bitcoin, you need a wallet – a digital container where your precious coins reside. Think of it as a virtual piggy bank, except you don't need a hammer to break it open. Your wallet comes with a unique address, like a digital fingerprint, that allows you to send and receive bitcoin. Losing access to this wallet is as heart-wrenching as misplacing your favorite pair of socks. Trust me, it's not a pleasant feeling. My encounter with the disappearance of my Bitcoin wallet taught me a valuable lesson about the importance of implementing proper security measures. It's not enough to rely on luck or hope that your digital assets will remain safe. Taking proactive steps to protect your investments is crucial in the wild world of cryptocurrencies. From using strong and unique passwords to enabling two-factor authentication, every layer of security adds another brick to the fortress that safeguards your digital wealth. Trust me, you don't want to learn this lesson the hard way. It has changed my life to be able to retrieve my misplaced Bitcoin wallet thanks to REVENANT CYBER HACKER amazing services. It made me realize the worth of tenacity.
Website: revenantcyberhacker {DOT} org
Email: revenantcyberhacker {AT} Gmail {DOT} com
Telegram: revenantcyberhacker
WhatsApp: + 1 (208) 425-8584
WhatsApp: + 1 (913) 820-07392
