Join devRant
Do all the things like
++ or -- rants, post your own rants, comment on others' rants and build your customized dev avatar
Sign Up
Pipeless API

From the creators of devRant, Pipeless lets you power real-time personalized recommendations and activity feeds using a simple API
Learn More
Search - "infosec"
-
"A Google security researcher withdrew from the Black Hat security conference and asked the community to stop using the 'black hat' term."
What the heck? Are we just going to ban the colors white and black in every context? Its clearly not talking about race, its talking about morals... Which people like this "google security researcher" obviously know nothing about...
This is all so stupid... luckily the community disagrees with the stance but then again, afaik, we all also disagreed with removing master/slave and it still happened so make of that what you will...
https://zdnet.com/article/...34 -
A few weeks ago at infosec lab in college
Me: so I wrote the RSA code but it's in python I hope that's ok (prof usually gets butthurt if he feels students know something more than him)
Prof: yeah, that's fine. Is it working?
Me: yeah, *shows him the code and then runs it* here
Prof: why is it generating such big ciphertext?
Me: because I'm using big prime numbers...?
Prof: why are you using big prime numbers? I asked you to use 11, 13 or 17
Me: but that's when we're solving and calculating this manually, over here we can supply proper prime numbers...
Prof: no this is not good, it shouldn't create such big ciphertext
Me: *what in the shitting hell?* Ok....but the plaintext is also kinda big (plaintext:"this is a msg")
Prof: still, ciphertext shows more characters!
Me: *yeah no fucking shit, this isn't some mono/poly-alphabetic algorithm* ok...but I do not control the length of the ciphertext...? I only supply the prime numbers and this is what it gives me...? Also the code is working fine, i don't think there's any issue with the code but you can check it if there are any logic errors...
Prof: *stares at the screen like it just smacked his mom's ass* fine
Me: *FML*12 -
CS graduates that have never gone beyond "Hello World", fuck college and it's "system".
So the actual victims of the story are friends of mine, CS colleagues, but I can't help but share as the existence of code freeloaders enfuriates me.
At college in order to graduate you need to present a project in form of a thesis a side from your actual thesis, there is a shortage of pre-approved projects and everyone wants one.
A talented friend of mine who has many years of programming experience got in one with another friend of mine and a lady who I've never seen before. One Saturday night my friend and I were having some beers at a local bar and his phone didn't stop beeping so I jokingly said:
"Bro, tell your girl you need some space", he laughed and explained it was the chick from her project having some "issues" with node.
"So? Tell her to google it, it's Saturday night", he explained the girl has never coded before even though she's about to graduate so she had take it upon herself to pressure him to finish ASAP so she can graduate and get an already agreed position at the federal energy commission... As dev!
I've seen my bud in a lot of dumb calls with said chick trying to explain how you CAN'T COMPILE THE NODE WEBSERVER TO A .EXE!
It frustrated me how such an idiot can go through a CS major buying homeworks and getting low self-esteem geeks to code for her. Then I realized that as an aspiring InfoSec guy, lazy idiots coding is good for business.8 -
As a firm supporter of information security, it really "irks" me to see people get up and walk away form their desks without locking their machines... Anyone else with me on this?!18
-
Anyone here who also got super bored while on a porn site and ended up pentesting that porn site..?14
-
The deeper I go down the infosec rabbit hole, the more I worry about my doctors still using Windows XP. Why would you save sensitive patient info in those....shoe boxes?
 4
4 -
So... Some fake accounts on Twitter claimed to be Elon Musk and to give shitloads of Bitcoin to those who sent a little amount first. They stole... Wait for it... 180 grand.
That's basically your everyday 419 scam. Existing since before the internet, done with the names of Gates, Buffet, Bush, Obama...
They say "the big bad evil criminals and the poor little innocent victims" I say natural selection. Sorry, in those lion vs gazelle scenarios I always thought that it was fair, no matter how it went.
Just when did humanity get so brainless? Have we always been, is the internet just a catalyst for stupidity?
Just why the fuck must I be an infosec sheepdog instead of a wolf? Man, I could live the life, drink beer and smoke herb while working... Get up at 12, don't give a shit, no boss, no taxes, no social security payments that I don't see jack shit from, and the pay would be better to.
Damn.12 -
Won a new job; 50% payrise which, for a junior, is a pretty big deal.
A bigger team, with more established practices, a commitment to testing and code coverage, code reviews, and a smaller learning surface area as I go forward (focusing entirely on the js ecosystem, 80% frontend).
So this is all good.
But I *have* to go back to Windows. Windows *7*. Their infosec practices move at a glacial pace. After two glorious years on mac/linux I feel like being sick.7 -
Hey all!
I've been browsing devRant for a couple months now and finally joined!
I'm a CS student from Germany, most interested in AI and Infosec, and member of a CTF team.15 -
I have a server. I want to filter connections to that server so only people on my work network can access the server. A quick search yielded my public IP address.
"Is this static?" I asked IT. "Do we have static IP address?"
"What do you mean? What do you need that for? You better know EXACTLY what you are doing before we release that information to you!!!! This needs to go to my manager. My manager is demanding to know why you want that information - we are having Network Engineering look into this request, someone will be in touch to find out more."
I have now been waiting for 3 hours. I think I will just go ahead and assume my IP is not going to change...undefined infosec how many engineers does it take i am on the 10th floor the fall would kill me corporate america5 -
Anyone who's interested in cyber security, go follow Binni Shah (@binitamshah) on Twitter. The amount of tutorials and guides she retweets is crazy and very informative.
Also if you're not on Twitter you're missing out on a lot of content to learn from ✌️18 -
Because I own http://grnail.co.uk and http://hotrnail.co.uk (which I bought to prevent scammers having access to them), I often get emails about peoples' accounts. I could do a password reset and own these accounts, but of course, I don't.
However, today I started getting passport scans and personal details from Syria... 2
2 -
Running WireShark to see what one of our partners is sending across.
Outdated TLS: Ok, that's par for the course.
Leaking data through DNS queries: ButWhy.jpg
Website leaked through DNS doesn't require auth to view information. TableFlip.jpg1 -
So I work for a VPN company as the Info Sec manager long story short I'm not usually the pleb who does customer support.
But today I ended up having to do this. I spent over 1 hour helping a client that a support agent escalated the request for to me. So I figure out that his network adapters are sharing incorrectly.
I fix problem.
He tries to connect.
Denied access so I check our servers for the request and he's blocked.
I think that's odd.....
I check active subscription and this person ISNT A CLIENT THATS ACTIVE....
WHY IS SUPPORT SO IGNORANT.
UGH.1 -
What flavor of Linux is everyone using? Why do you think it works well for developers? Got a new laptop and I'm trying to decide what to put on it. My other laptop has a dual boot of windows 10 and Kali Linux (my sudden interest to become a developer came from a desire to be better at Infosec/netsec stuff)
Curious to see what everyone uses from a developers perspective. Not sure I want to develop on Kali and windows is shit.23 -
Welp, here it goes:
High school is feeding me a huge amount of shit that I do not care about. This, causes me not to have enough time to carry on my own programming and infosec studies due to a lack of time, despite the fact that I'm pretty organized. Among all that, is the fact that I have 3 weekly martial arts training in the evening, which equals to even less time.
I am starting to feel quite shitty about this situation, and no, I'm not going to wait precious years of my life before continuing with my studies.
Let's hope I'll pull through. :(3 -
Had to change password on computer for administrative reasons (sysadmins and infosec make us change our pass every quarter). Changes didn't sync to everything so now I can't even log into my computer.
Need to go to the office tomorrow so some guy can type in an admin password on my pc and do stuff to it. If that doesn't work I will just be given a new laptop.
Seriously fuck this week4 -
Consistent theme:
Me: hey, we should really do/use X
Someone above me: Nah we don't need it/we already use Y
1 week later (or less):
SAM: Hey, I was thinking maybe we should start using X
This has happened 5 different times already. 2 of them were security related and only talked about after our infosec guy brought it up.
Don't dismiss ideas your interns have just because we're interns, we might have good suggestions.4 -
Can any IT/InfoSec people tell me why in the heck do I need to put in a ticket to download the Java runtime environment?
Like seriously, how is blocking this beneficial? I'm genuinely curious.10 -
- I do threat intel.
- Oh yeah? Name 4 critical vulnerabilities.
- Fortinet.
- That's on me, I set the bar too low. 1
1 -
I refused to get into python pretty long but yesterday it happend. I got the py. :')
Coming from Java/Netbeans I tried installing it again (for personal projects), but since Apache took over and Java 10 got released I never seemed to be able to accomplish a clean IDE install.. I gave up while I wanted to turn a current python programmer to java and, again, Netbeans fckd me over. I tried IntelliJ again afterwards but Netbeans seemingly fcked over the whole JDK installation too, so I gave up for real.
Everyone in my vicinity told me about python and it's coolness. I just.. no.
No {}, no semicolons, indentations are relevant... idk. I did not want to, but some part of me still wanted to try it. I want to work in the infosec branche so it definetly should be one of my interests shouldn't it?
So I tried yesterday, installed PyCharm and in literaly minutes (of course with trusty Stack Overflow behind me) I had a Qt based GUI which functioned as a basic webbrowser. I was intrigued. Well, I took like 100 times that time to get a working .exe out of my .py with all dependencies, but with the help of mentioned python friend I also got this to work. Python is cool now, I guess... ;b -
Not sure whether to tag this as a rant or a joke, because it feels like equal parts of both. So fucking disappointed with Australian government.
 2
2 -
Challenge questions are so goddamn stupid.
Apparently I have an account with a certain online organization though I don't remember setting it up.
So naturally I had no idea of my username or password, so they asked me challenge questions.
It asked me the city of my birth, which is a place with a weird spelling. Because of that weird spelling, I never remember if I'm spelling it right (I was only there as a newborn infant) And I'm also supposed to remember if I capitalized it or not.
I hate challenge questions. And anyone doing any remotely simple research on me shouldn't have trouble learning what city I was born in so it seems to me it's a security vulnerability, nothing more.
And maybe I'm giving things away by saying it asks me that question, but it's a common security question any hacker would anticipate anyways.2 -
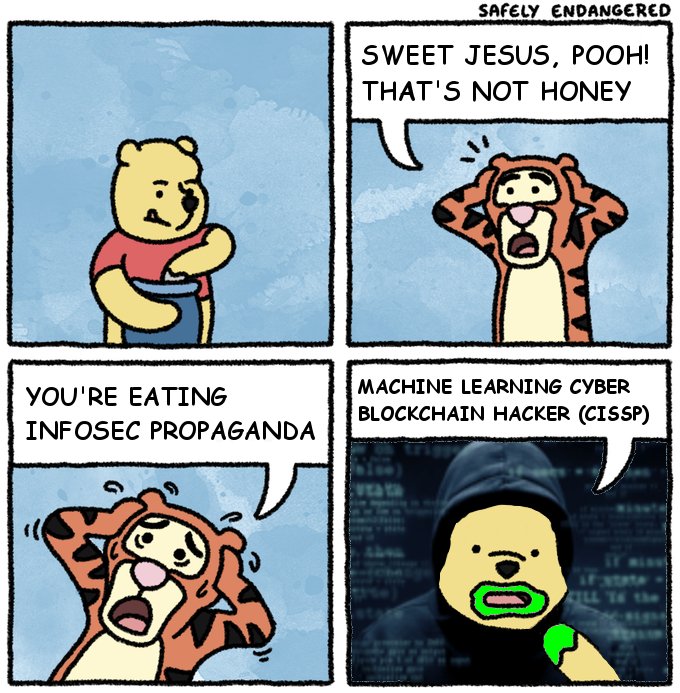
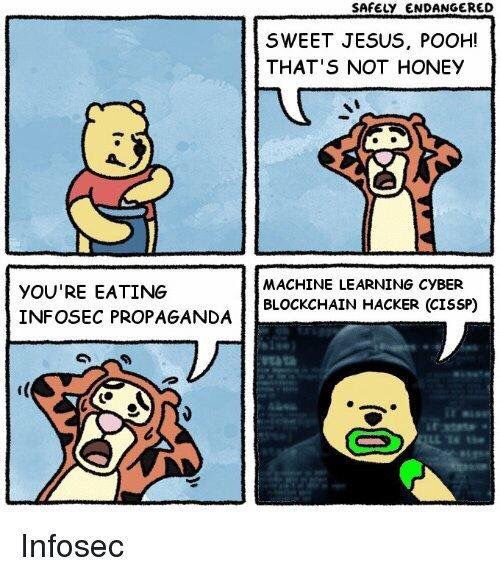
Seeing the Winnie Pooh eating InfoSec propaganda meme this morning on devRant saved my day. I'm still laughing 8 hours later 😂2
-
If I ever want to phish people at an enterprise I would send the email as the yearly infosec training course.
-
Hey everyone. I am a freshman in college studying Cyber Security. I have been practicing various programming languages such as httml, css, java script and SQL. Does anyone have any recommendations for resources to study? My end goal is to be blue teaming for my schools Cyber Defense team in the fall.5
-
Do you still charge your clients extra for HTTPS being it’s practically a requirement now for SEO purposes?6
-
That moment you setup 17 domains on sparkpost as a email delivery system
make your account secure with 2 factor authentication like a good infoSec enthusiast
Go on with your life
Having a Phone crash but nothing to worry because you made them backupz
Restore backupz
once again go on with your happy life.
Having to setup a different bounce action on sparkpost
logging in to sparkpost to make the adjustments
opening google authenticator
realising the backup you restored was before you added the sparkpost entry
mailing sparkpost asking to deactivate 2factor authentication
Having them tell me that they have no access to Google authenticator so they can't help me and all they can do for me is delete my account if i answer their 7569357 questions that i entered a year ago ..
--
You have access to your database yes ? You can delete my account but you can't adjust a fcking Boolean column from true to false? #@?#&!
Why even offer a feature where you have apparently no control over. Stuff like this happens all the time and almost no one saves that fcking authenticator secret.
Make people use authenticators to keep the hackers out, forces them out instead.4 -
Security starts as soon as the project starts. Every decision you make needs to be one that considers whether you will compromise on security - but human beings fail to do this for one reason - bureaucracy.5
-
Question - my field is information security (or cyber security if you want to think of me as a time lord), but I wanted to know;
Front end and back Devs, how much time do you spend on security issues and/or implementing security measures?9 -
A customer of ours not to say names trains people for infosec certs upon investigating their website I noticed they don't have forward secrecy enabled.
Why? What? Even?
Turn it on you baddies.2 -
Typical insurance company BS approach.
Listening to xmas music, Spotify ad kicks in about 'just being "hacked"':
Buy our cyber security insurance product to quickly recover and retain liquidity in case of a cyber security beach.
Not a single word about preventing the incidents in the first place...
Lucky to work in a place that doesn't skimp on IT.3 -
tech D&D
dev = fighter
ops = cleris
network = wizard
design = bard
dba = warlock
infosec = rogue
it is not mine but i think its great analogy. and because i always choose the warlock1 -
Get over my anxiety and get an actual job in infosec, so I can stop hearing "can you hack my BF facebook" requests.
-
1. Extend my infosec knowledge further and try getting more work in that area (and less as a dev).
2. Specialize more, dabble less.
3. Learn more !dev skills (military/political history mostly) -
I am trying to start my career in the world of web development currently I am 16 and in 2 years I have to move out (moms orders) what would be the first move into getting a job as a web developer is it best to freelance or work full time for a company and what certification's would you recommend getting I am already very good with computers both windows and Linux (windows can kiss my ass tho ) and I know html css as well as some php and jquery I even know a little MySQL (I am also very talented at cybersecurity mainly infosec and OSINT )
(I know this question probably sounds stupid but I would like some advice from people in the area recently I told my dad I want to be a web developer my dad then told me I should get a real job )
Any advice would be great7 -
Did some analysis on some servers that a partner of ours is hosting:
-TLS 1.0: Hmm this isn't great
-TLS_RSA_WITH_RC4_128_SHA preferred Cipher Suite for ALL TLS Versions.
I almost barfed at my desk.4 -
Hello devrant, so I've been wondering if anyone here breaks things (infosec)? Is there anyone who dabble with building stuff(dev/ops) and breaking them? Need advise whether I should be looking at a devops-y role or a infosec related role in the future. (PS I was in infosec and slowly transitioning into ops/devops not sure yet). Please share your experiences. :)8
-
Infosec : I have started a telegram channel.
Join and spread the word..
Link : Hack3rB0x 🔊
https://t.me/hack3rb0x1 -
Have you ever considered switching to IT support/help desk?
I mean, sometimes I try to analyze my own situation from a 3rd person perspective and I realize I could have a pretty much stressless job with still enough money to live a normal life.
I have a BSc and MSc(soon to have) in CS, with focus on AI/ML. I've always been a geek with a problem solving attitude, that's why I got into computers in the first place. And now I'm pondering if I should just try an IT Support position, it's the kind of things I used to do as a teenager when a classmate had a network/computer problem, it doesn't even feel like a job to me. I could call it a day, get home at 5/6pm, and spend time on my personal projects (software, infosec) with a fresh mind, going to bed (and sleep) knowing that the next day would be a nice one. No clients wanting a new feature that you gotta implement and push on a production server friday afternoon because your ceo(who is also a pseudo proj manager) just said:"Yes, we can", while you watch the technical debt rising like amazon's stocks.
Maybe this is just the burnout talking, I don't know. Maybe I should just try being a software engineer outside of Uni in the first place, and only then start pondering.
Maybe a sysadmin position...
Have a nice day12 -
Maybe not specifically "dev" but certainly a relatable rant to anyone here:
Moms small business gets "hacked," or standard spyware phone call from India let us save you for only $149 kind of crap. She obviously gets upset had a panic attack and thinks about all the sensitive shit on their network. Then, ONLY THEN, does she call me and the rest of the cavalry i.e. over payed and undermotivated IT guy to ask what's up why it happened and whose fault is it.
All is well, no ransom paid, no data lost or tangible damage done, but I am positive it will happen again, because it is impossible for people to internalize that they're the problem that money can't fix.
You clicked the unsolicited link. No amount of antivirus bloatware will ever be able to stop the monkey from trying to see what's in the box.
TheBut keep not paying me or people more qualified than me, and then scream and yell and pout when your shits gone and we can honestly say with a grin and a clean conscience that there is nothing we can do. -
Fuck windows server. Fuck infosec. Every time they roll out windows updates shit breaks. From windows service get stuck in "stopping" state to dropping network interface. Why the fuck are we still using this to host a simple API or NSERVICEBUS service?? Don't know whether to laugh or cry. Fml.
-
I'd like to one day work on security consulting/advising (incident response, opsec, SOC, etc). For those of you here that are currently in or have worked with people in that field: what advice do you have for handling cyber risk situations?1
-
Password must be 5 characters long and contain one big letter and each of the following: &, +, %, !, *, @.2