Join devRant
Do all the things like
++ or -- rants, post your own rants, comment on others' rants and build your customized dev avatar
Sign Up
Pipeless API

From the creators of devRant, Pipeless lets you power real-time personalized recommendations and activity feeds using a simple API
Learn More
Search - "hackerman"
-
When you "fix" a bug not by actually fixing the bug but by disabling the user's ability to cause the bug.
 14
14 -
Alexa (in another room): ***ALARM***
Me: Hey Google, broadcast "Alexa, stop"
Alexa: ***stops***
Me: 11
11 -
When I Made Passworts visible in Chrome and the teacher sent me home...
...It was Friday!
Ps:
She sent me home because she was really fu**ing scared of what I did and even called my Parents 8
8 -
Found this guy at my school who was trying to impress n00bs around the place by using Inspect Element in Chrome to change the content of webpages. He was claiming that he hacked the website 😂😂😂 I'm still crying14
-
How to hide your important files from people without making Hidden folders
1. Go to Desktop and create a new folder
2. Name the folder Internet Explorer
3. Change the folder icon to Internet Explorer
4. Keep it in a corner of the desktop
Now, no one will open internet explorer :D10 -
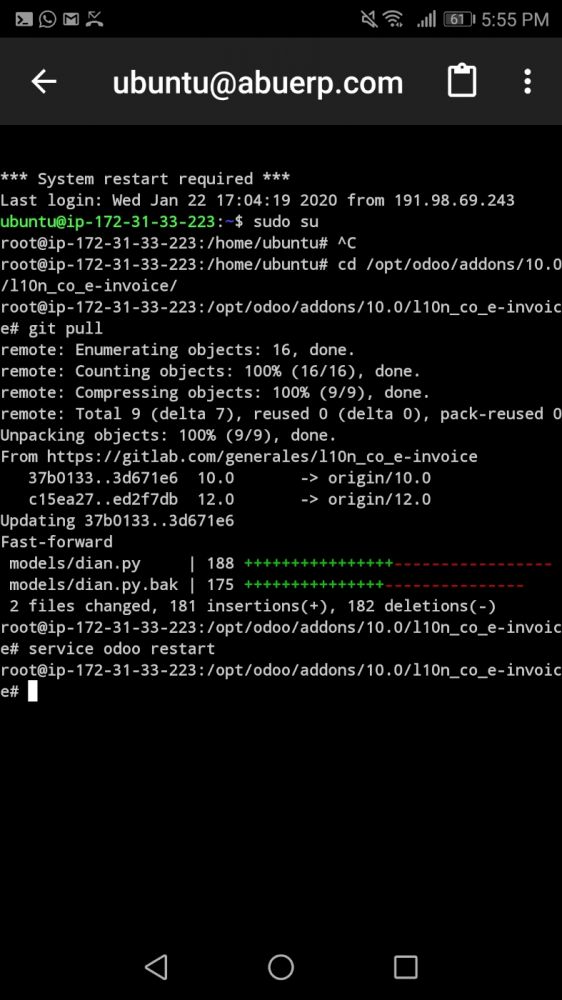
Recently I've been upgrading ubuntu. It took almost midnight.
Suddenly my area witnessed low voltage.
That woke up my dad.
(Now the funny part)
He looked at my laptop. Ordered me to stop whatever is running on it.
Naturally, I asked why!
No response.
Next morning, I came to know my dad thought those gibberish commands running on terminal caused that voltage to drop.
I laughed like hell...
(Me infornt of dad - hackerman)
(Not that funny tho)
Fin.3 -
When you're just coding away in some Coffee Shop and some random guy/girl asks you
"are you trying to hack the wifi" smh12 -
I guess that is what you get for bringing up security issues on someones website.
Not like I could read, edit or delete customer or company data...
I mean what the shit... all I did was try to help and gives me THIS? I even offered to help... maybe he got angry cause I kind of threw it in his face that the whole fucking system is shit and that you can create admin accounts with ease. No it's not a framework or anything, just one big php file with GET parameters as distinction which function he should use. One fucking file where everything goes into. 21
21 -
> 3 hour long mandatory online cybersecurity training
> Preaches that the company is very secure and the only risk of being “hacked” is if employees post company data on social media
> oksure.tar.gz
> Bored out of my mine
> Open dev console
> JSON continually getting sent to backend
> Simple structure and human readable fields including {complete: false}
> Open postman
> {complete: true}
> Send
> 200 response
> Refresh page
> Course complete
> :’ )
Muppets.4 -
And the title of hackerman goes to he who is now running macOS Sierra inside of VMWare on Windows 😂
 18
18 -
I'm sure it's been said a million times before, and will be said a million times after, but:
*Right clicks website*
*Selects Inspect Element*
*Changes something for giggles*
...
*Someone sees over your shoulder*
"OMFG DID YOU JUST HACK THE INTERNET!"4 -
Long story short, I'm unofficially the hacker at our office... Story time!
So I was hired three months ago to work for my current company, and after the three weeks of training I got assigned a project with an architect (who only works on the project very occasionally). I was tasked with revamping and implementing new features for an existing API, some of the code dated back to 2013. (important, keep this in mind)
So at one point I was testing the existing endpoints, because part of the project was automating tests using postman, and I saw something sketchy. So very sketchy. The method I was looking at took a POJO as an argument, extracted the ID of the user from it, looked the user up, and then updated the info of the looked up user with the POJO. So I tried sending a JSON with the info of my user, but the ID of another user. And voila, I overwrote his data.
Once I reported this (which took a while to be taken seriously because I was so new) I found out that this might be useful for sysadmins to have, so it wasn't completely horrible. However, the endpoint required no Auth to use. An anonymous curl request could overwrite any users data.
As this mess unfolded and we notified the higher ups, another architect jumped in to fix the mess and we found that you could also fetch the data of any user by knowing his ID, and overwrite his credit/debit cards. And well, the ID of the users were alphanumerical strings, which I thought would make it harder to abuse, but then realized all the IDs were sequentially generated... Again, these endpoints required no authentication.
So anyways. Panic ensued, systems people at HQ had to work that weekend, two hot fixes had to be delivered, and now they think I'm a hacker... I did go on to discover some other vulnerabilities, but nothing major.
It still amsues me they think I'm a hacker 😂😂 when I know about as much about hacking as the next guy at the office, but anyways, makes for a good story and I laugh every time I hear them call me a hacker. The whole thing was pretty amusing, they supposedly have security audits and QA, but for five years, these massive security holes went undetected... And our client is a massive company in my country... So, let's hope no one found it before I did.6 -
Regular Person = Regular Person;
Regular Person + Google = Hackerman;
Why are people so lazy they can't google their problem before calling help desk?
I hate mental lazyness!4 -
Mom: Oh cool! So you can hack sites and accounts now?
Me: No mom.. I'll be making stuff, not breaking it.
Mom: Well what's the fun in that 😐
Me: ...4 -
!rant
Really happy about this one! I cannot go into details yet but hopefully will write a blogpost about it when I may disclose it :) 24
24 -
"Can you get me free in app purchases?"
"Well i mean lucky patcher is kind of a gray area but I guess if y-"
"Can't you just have it with the command prompt?"
"I don't know CMD, I know Java."
"But you said you could code!"6 -
Teacher: Write a program to print fibonacci series up to 8 terms
Me: *hardcodes 0,1,1,2,3,5,8,13*
Teacher: *runs the programs*
Me: *relieved*
Teacher: *checks the code*
Me: 5
5 -
So after my phone got stolen I am now using a series30 Nokia device, problem was synching contacts dumped from Google contacts. Run a Python script that modified the vcf into a format compatible with the series 30, never felt more of a hacker man than this
-
When you redirect every movie link to XXX links on your rip-off netflix school project and nobody suspects a thing
 17
17 -
Thought Amazon servers went bonkers seeing these names. Later realized these are episode names for TV series, Mr Robot.

-
It happened just now.
Yes, I put "there is no need to be upset 10 hours" on governmental terminal.
#hackerman
How? Well, I discovered that it was web ui, so random menu category -> random external governmental website with Google map on it -> you know the rest. 4
4 -
TL;DR
I accidentally surpassed(?) my user permissions and closed some of my classmates browsers and locked up a terminal for me
In school we have 2 primary operating systems: Windows and Ubuntu. Windows is hell in general and but not as hell as the firefox installation on Ubuntu.
"Just loaded this page. Now wait half a minute so that I can render it"
"Woah, woah, woah. Slow there. You just made an input event. Give me those 5 seconds to compute what you just did"
Executing "top" or "htop" shows you a long list of firefox processes with a cpu usage of 99.9%, since the whole school shares that linux environment.
Anyway, one day it was way more servere than normally and I way forced to kill my firefox instances. So I pressed CTRL+ALT+T for that terminal, waited 5 minutes until it accepted input typed "killall firefox" with a delay of half a minute per character and smahed that enter key.
At this very point in time I could hear confusion from every corner of the room. "What happened to firefox?"
Around 30% of the opened browsers where abruptly stopped. I looked back to my screen noticed I was logged out. I couldn't login from that terminal for the rest of that day.
Our network admin, which happened to be there, since the server is just next door, said that this was just convenience, but the timing was too perfect so I heighly doubt that.
I felt like a real hackerman even if it was by accident :)8 -
!rant
Conversation between [C]oworker and... some kind of customer-side [P]roject manager.
P: Hey, our release 2.0 is ready, but somehow I can't add tag to master. Could you try, please?
C: Yeah, sure.... Done... We are missing tag for 1.2 still, should we add it?
P: Oh, right, I forgot about that.
C: Ok, found merge... Done.
P: *displaying repo in GitBlit* Uh, now the order is wrong. And date is the same. Can we do something about that?
Me: We can just push that tag with replaced date. *just guessing*
P&C: You can do that??
Me: Sure
Me.thinking: Thats git... I would be suprised if we could not.
Me: *pushing tag* Check it now.
P: Whoa, nice! 3
3 -
Had to use a cmd window for adb to push some files to my phone so I could flash them and everyone is staring at me...
It's just a cmd window people... #Hackerman4 -
So my story has some little backstory.
I got into computers and technology because of my dad. He was very enthusiastic when I was little and when I grew older and started my apprenticeship as a software developer he was really proud. Note that he never learned anything like that. He just loved computers and games.
Now to the story itself.
I learned more and more, also about networking and came to the conclusion that our slow internet and rare internet problems probably come from stock/weird configurations. But my dads proud probably told him thats a thing he still has to do as the dad. But it annoyed me so much that I booted into kali linux, loaded an exploit to get the web admin passwort and cracked it within a minute. 😎
Finally I was able to configure everything correctly ( channels were spammed from neighbours so I switched to very unused and the disturbions got less ).
TL;DR: Dad didnt want me to configure our router and didnt give me the admin password, so I booted Kali Linux and used an exploit to get it myself 😎😎3 -
So, there was an art student yesterday at my dorm complaining about free speech etc. She told me that they where trying to bring the schools proxy down.
I was pretty impressed because it's an art student!
She then proceeded to tell me she had downloaded kali linux and was learning html...3 -
A bit different than wk93, but still connected and a fun story.
Back in high school when it began to digitalize everything, so began our teachers journey with technology. We, as IT class were into these things, but as far as I can say, others in the school including both teachers and students were like cave mans when it came to IT.
Most of them kept the different wifi networks password on the windows desktop, in a file 'wifipassword.txt'. When we were on robotics seminar, we had to use a teacher's laptop. The wifi network was incredibly fast and powerful,, yet so poorly configured that even the configuration page user/pass was the default admin/admin, because the IT admin wasn't the most skilled one.
We got the idea to sell the password of the wifi network to other students. Not much, for about 1 dollar a week. The customer came to us, we took the phone, took note of the MAC address, entered the password, and if the guy were to stop paying every week, we just blacklisted that MAC on the next robotics course.
Went well for months, until a new sysadmin came and immediately found it out, we were almost fired from the school, but my principal realized how awesome this idea was. You may say that we were assholes, and partially that is true, I'd rather say we made use of our knowledge.2 -
Secretly installed Automate app on my friend's Android phone to mess with him. (For those who don't know, with Automate you can automate anything on an Android device).
Made a 'flow' that would read his incoming sms's, and send an email to me with his exact location if I sent him an SMS saying 'where are you?'.
Was funny to mess with him and tell him his exact location even though we were miles apart.
Cleared it up for him a while later but it made me feel like #hackerman8 -
So I found a thing. On my laptop, I am able to create a hotspot. So someone can connect to it and I can share my internet access. Couldn't I theoretically impersonate a wifi name, by setting up the hotspot to use the SSID of the target network, then the clients that already have access to the target network would feed me the network credentials? If so, how would I go about capturing the creds?12
-
Interesting thing. Ya know how when turning on your phones hotspot it has to verify that you are in fact allowed to use a hotspot. Well if you have Unlimited Data like myself, hotspotting is not allowed. HOWEVER, if you spam the hotspot button, it after several tries, gives up and lets you hotspot. THIS IS MY LITTLE TRICK. NO BUG BOUNTY. BESIDES, youd need my carrier.10
-
When you can't hack even a toaster so you use www.hackertyper.com to look cool at school but as you "write" the code you realize it's probably written in C or C#...5
-
Enter E-Mail-Address:
"finiteAutomaton@gmail.com"
|> E-Mail-Address is already taken!
Enter E-Mail-Address:
"finiteAutomaton+1@gmail.com"
|> Verification code sent!
I am a hacker!2 -
Years ago I was working in local cinema as a student job from time to time and used to sleep after shifts at my uncle's. Uncle did not had internet but there were so many wlans all around. Since I had nothing to do for hours after shift, I downloaded Backtrack linux at home, made live dvd of it and saved a two articles of "how to hack wifi" to text files.
It took me 4 hours to break WEP, since I was total lame, and it was the only one WEP around. They also had mac restrictions set to router, so I changed my mac address to one of their devices, logged in to router and added our mac address. For my uncle it was complete magic but since he is total geek to linux he liked it.
Fast forward weeks later. When I came to my uncle's house he was downloading like ton of linux distributions. Literally each one. Gigabytes of data. I told him not to do so because sooner or later neighbour will notice, but he did not care. Guess what, he notices, probably slow internet and (maybe) bigger bills, I do not know, but owner just changed protocol to WPA2, not changing password. So the story continued for almost 2 years. Felt a bit sorry for neighbour but did not expect such an outcome. I just wanted to watch youtube videos and scroll social networks, keeping low profile so no one notice.1 -
*sees a new tech/framework/language*
*dives straights to download just checking for windows/mac/linux*
*downloaded product doesn't start/gives error/complains because some prerequisites are not met*
*after some frustration it starts to work*
*To not offend the Gods, writes "Hello World"*
*Carry a "Hackerman" face all day*
*Updates resume* -
Just did something hackerman-ish! 😎
Since a lot of new iPhones are out after the XR, Apple "removed" the page for iPhone XR and redirect to the /specs page. I tried adding /index.html to the url and tada! :D hahah "I'm in!"
Any other ways I could've gotten to this page? I was going to try the sitemap and the web archive.2 -
😂😂😂 lol oh no what will we do when hackers takeover the world by printing an endless stream of planetary gears. Shame on you Harvard for such a poor picture choice.

-
Every morning I start visual studio code from cmd... So I wanted to make a script to open that specific folder and start it in code...
The time I spent trying to make this thing is longer than the time it would take me to start code every morning.
Guess I'm no hackerman :/9 -
Fun experience backing up my laptop drice to external hdd :
1 folder : 100 sub folders with 12000 files, size 6gb
>> Ctrl A-> ctrl C -> ctrl v
>> Copying time 55 mins , files remaining 12000
CANCEL CANCEL CANCEL!!
>> add to archive (5 mins) -> ctrl c, ctrl v
>> copying time 6 mins , files remaining 1
(*Insert hackerman meme here*)2 -
!RANT
Bet the diff between a beginner developer and an intermediate developer is where to get code snippets either from old codebases or remote resources. -
So this is what a cyber criminal looks like.
"Norwegians are a favourite for cyber criminals"
"And we are easier to fool than Swedes and Danes, if we're to believe the thieves. The only ones more exposed than us are oil rich Saudis" 🤷♂️ 1
1 -
Our ISP, that also offers us Television is smart, very smart... “One option is to provide an anonymous mailbox (eg. Gmail, Hotmail”
Wtf... Gmail != anonymous.
I was about to report a vulnerability I found in their system, with that I could access the whole digibox, recover recordings, copy the on demand things, and watch films. 1
1 -
Noooooooooo 😢
What will I do without stack overflow?
....
Oh yeah, *inserts* "cache:"
Crisis averted 😎
-
So a while back I had found a hole in a website's security, one that I has used pretty frequently. I was able to change my cookies and become any user I wanted. The only caveat was that I had to log in as a user in order to get things started. But once I was in I could basically be anyone I wanted to be just by changing a few numbers in the user ID of the cookie. They also did all of their user processing on the client side. Even password checks.
A couple weeks back I decided to go back in to see if anything had changed since then. It did! But not in the way I had thought.
So these guys decided that instead of fixing their security hole, they would have users just contact their people directly in order to get a new account.
Wow that's so much fucking overhead for basically being a lazy shit and not fixing the security holes. I mean how bad is your architecture if you can't go in and fix this?
Not only that I found that they actually stripped all of the users of their original subscriptions. So now if you want to get back on your subscription you'll have to fork over another $399. So that means going to their shitty form filling out your name, your number, email, and just hope that someone contacts you via phone call.
I'm glad I dropped this service. They clearly can't get their shit together.rant hackerman what the fuck are you doing bold and brash it's all shit more like belongs in the trash front end is shit back end is shit -
why do all of you get so hyped when you install arch linux? you guys sound like the type of people who jack off to arch lmao. lets keep it real tonight, some of you legit ejaculate fantasizing about arch linux like "ohh archh mm 💦💦 ohh tmux 💦 i3💦💦💦linux baby give me more👅💦"
maybe even cool hackermans who brag about installing arch wanna use it for hacking. r u a better hackerman now that u use arch linux ?10 -
Ok I got a new position with a client which is a big pharma company (like evil corp). What script do I need to write now to make drugs free?4
-
Context: at my current job I work as a product photographer as well as studio admin. On side I go online to different brands websites in search for product images (if we haven't the product in store yet).
Now the banger, I searched for some peacoat colored pants but the brand didn't put it out yet. Pulling out some Super AI hacks I changed some stuff and things in the URL (color ID + small amount of ?doThisAndThatPhP) and... BOOM result! Right color, high Res image. The Color isn't searchable or shown via Google or the brands page, but the image is already on their server 🤔*yoinking the image*
Just wanted to share it with you guys 👌 none at my coworkers speak computer 😔
cheers ☕1 -
Clueless child thinks he got hacked.
So me and my friend were just messing around in class and he says to this other guy that he "hacked him" as a joke. He showed him a CMD shortcut of the file saying "[guys name] OS SYSTEM." He fucking fell for it. He actually thought a cmd renamed shortcut was his OS system and my friend could access it. He tried to grab his computer and delete it. My friend thought he was joking so he opened it and the kid actually screamed. We burst out laughing and make a scene. The teacher got kinda triggered so we stopped haha.9 -
I want to break my win 10 password which I have forgot . I know one method of breaking the passcode by using bootable Device . Is there any other method to other than using bootable device for breaking the passcode? please suggest some technique9
-
I wish it was as easy as:
> hack FBI
Cannot hack, root privileges needed
> sudo hack FBI
Hacking...2 -
> Be me
> Fresh out of school
> Do some volunteer work for 1 year before starting to work
> Start work at local hospital
> One day get assigned new task
> "We have this directory where there is a file for every employee who has a key - File contains legal stuff"
> Current naming scheme "MaxMustermann"
> Desired naming scheme "Max Mustermann"
> Task: rename every file.
> 1974 Files
> OHNONONONO.JPG
> Hol up buddy
> A repetetive automatable task?
> I know this
> Im a hackerman
> Let's write a script....
> *SMASHES WINDOWS BUTTON*
> "Python"
> No results
> I could have guessed that
> *SMASHES WINDOWS BUTTON*
> "Java"
> No Java compiler
> OH no
> *SMASHES WINDOWS BUTTON*
> "Powershell"
> "tHe eXEcUTIon oF poWeRsheLL sCriPts Is dIsAbLeD"
> REEEEEEEE
> *SMASHES WINDOWS BUTTON*
> "cmd"
> "YOu dO noT haAV thE rEqUiReD peRmIsSionS To oPeN tHis proGrAm"
> DAFUQ
> Wait this is windows.
> Windows ships with .NET
> *SMASHES WINDOWS BUTTON*
> "csc"
> No results
> OHHELLONO.gif
> mfw I have to rename 1794 files by hand.
( Please send help )7 -
Hackerman strikes back. Always thought the new knowledge about stego tools, reversing, enumeration, privesc were just my private amusement. But could now use it, hopefully resolving a severe crash by dropping our binary into radare2 (cutter) and ghidra, identifying some dangerous code.
Also it gives you new angles to look at things. E.g. the vectors your code might expose...3 -
(Hackerman intensifies)
Sadly that's all I've implemented so far and I don't have a lot of time for these things :-/
But damn puppeteer is cool!
shit I mixed up kissmanga and kissanime...
-
Are you out of your free medium articles?😢 My Scrapy is here for the rescue.💸
This is simple application of web scraping, it scrapes the articles of medium and allows you to read or hear the article. If you use this on computer there will be a number of accents in the option.
The audio feature is provided only to the premium medium users, so here comes My Scrapy to save your 5$/month. 💸
.
Tech Stack used :
Python, beautiful soup, Django, speech synthesis
.
PS: This application was built for educational purpose and the source code for this application is not open sourced anywhere.
Fun Fact : You can still read any medium articles if they ask you to upgrade, you must be wondering how? Well, copy the link of the article and browse it in incognito mode on any browser.😂🤣
Try the app and lemme know if you liked it:
https://mymediumscraper.herokuapp.com/...4 -
!rant
Just a little questiom. What's the movie or TV series where you've seen a hacking scene which is probably very close to reality?5 -
The music which I listen while programmimg <3
https://youtu.be/TkZmwoRy__c
It makes me feel like HACKERMAN while im only doing HTML/CSS stuff 😂
By the way... What music do you listen while programmimg? 2
2 -
I format the memory card of my PS2 with Free MC Boot. 👨🏻💻*Hackerman*
Mhe is not that hard just need to play from my HDD I'm kinda bored.
Have any game to recommend?!5