Join devRant
Do all the things like
++ or -- rants, post your own rants, comment on others' rants and build your customized dev avatar
Sign Up
Pipeless API

From the creators of devRant, Pipeless lets you power real-time personalized recommendations and activity feeds using a simple API
Learn More
Search - "vulnerability"
-
The spam denier
_____
An old phone conversation with a client:
Me : Hello
Client : My website and server are suspended? why is that?
Me : Your server sends spam messages.
Client : We do not send spam messages, we are on vacation, there is none in the office.
Me : Yes, but it is not necessarily you, according to our logs, your server sent spam messages in Chinese and Russian, so someone from Russia or China....etc.
Client : I do not believe you, we do not speak russian or chinese, how could we then write spam messages in those languages?
Me : I told you, maybe someone exploited some vulnerability in your website or server firewall. And if you want to activate your services, please check with your webmaster and sysadmin to secure your ....
Client: I tell you my son, because I am old and I have more life experience than you ... I am 60 years old and I tell you, spam does not exist, and YOU suspended my website and server, and created issues to sell me more of your solutions and services.
I won't check my server, I won't hire a webmaster or a sysadmin, AND YOU WILL ACTIVATE MY SERVER NOW !
(I suddenly realized that I am talking to a wall, so I switched to a robotic tone).
Me : Please resolve the issue to activate your services..
Client : YOU WILL ACTIVATE MY S...
Me : Please resolve the issue to activate your services...
Client : WHAT IS THIS SPAM STORY ANYWAY, I DO NOT BELIEVE YOU ...
Me : Please google that word and you will understand what is spam is...
Client : YOU ARE F**ING LIARS, SPAM DOES NOT EXIST... ACTIVATE MY WEBSITE N.... Beeeep !
I hang up.
Well, I thought about configuring an automatic response for this client, or a for-loop.
His voice was really unpleasant, as if he is a heavy smoker.7 -
CW: The SQL injection vulnerability isn't important because our code is proprietary so hackers won't find it.
Me: <censored>7 -
https://git.kernel.org/…/ke…/... sure some of you are working on the patches already, if you are then lets connect cause, I am an ardent researcher for the same as of now.
So here it goes:
As soon as kernel page table isolation(KPTI) bug will be out of embargo, Whatsapp and FB will be flooded with over-night kernel "shikhuritee" experts who will share shitty advices non-stop.
1. The bug under embargo is a side channel attack, which exploits the fact that Intel chips come with speculative execution without proper isolation between user pages and kernel pages. Therefore, with careful scheduling and timing attack will reveal some information from kernel pages, while the code is running in user mode.
In easy terms, if you have a VPS, another person with VPS on same physical server may read memory being used by your VPS, which will result in unwanted data leakage. To make the matter worse, a malicious JS from innocent looking webpage might be (might be, because JS does not provide language constructs for such fine grained control; atleast none that I know as of now) able to read kernel pages, and pawn you real hard, real bad.
2. The bug comes from too much reliance on Tomasulo's algorithm for out-of-order instruction scheduling. It is not yet clear whether the bug can be fixed with a microcode update (and if not, Intel has to fix this in silicon itself). As far as I can dig, there is nothing that hints that this bug is fixable in microcode, which makes the matter much worse. Also according to my understanding a microcode update will be too trivial to fix this kind of a hardware bug.
3. A software-only remedy is possible, and that is being implemented by all major OSs (including our lovely Linux) in kernel space. The patch forces Translation Lookaside Buffer to flush if a context switch happens during a syscall (this is what I understand as of now). The benchmarks are suggesting that slowdown will be somewhere between 5%(best case)-30%(worst case).
4. Regarding point 3, syscalls don't matter much. Only thing that matters is how many times syscalls are called. For example, if you are using read() or write() on 8MB buffers, you won't have too much slowdown; but if you are calling same syscalls once per byte, a heavy performance penalty is guaranteed. All processes are which are I/O heavy are going to suffer (hostings and databases are two common examples).
5. The patch can be disabled in Linux by passing argument to kernel during boot; however it is not advised for pretty much obvious reasons.
6. For gamers: this is not going to affect games (because those are not I/O heavy)
Meltdown: "Meltdown" targeted on desktop chips can read kernel memory from L1D cache, Intel is only affected with this variant. Works on only Intel.
Spectre: Spectre is a hardware vulnerability with implementations of branch prediction that affects modern microprocessors with speculative execution, by allowing malicious processes access to the contents of other programs mapped memory. Works on all chips including Intel/ARM/AMD.
For updates refer the kernel tree: https://git.kernel.org/…/ke…/...
For further details and more chit-chats refer: https://lwn.net/SubscriberLink/...
~Cheers~
(Originally written by Adhokshaj Mishra, edited by me. )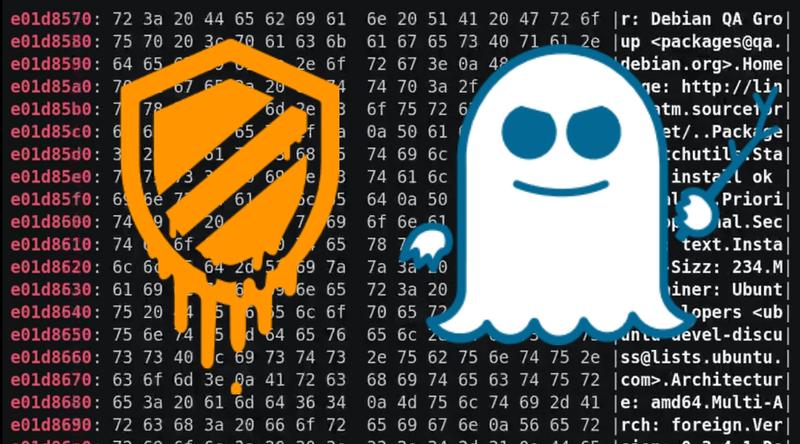 22
22 -
Alright fuck it, let's release this fucker!
https://lynkz.me is the main domain. The interface is *usable* and nothing more than that. I'll invest more time in that soon but for now, hey, it works.
Api is located at https://api.lynkz.me.
Documentation for this (literally some echoes to the screen but it contains the needed information for now) is at that api url.
Found a bug or a security vulnerability? Please let me know!
Yeah I use mariadb but sql injection is luckily not possible due to quite some sanitization ;)
WARNING: if you make a shortened url and forget the delete key, you won't be able to delete it.
Let's see how this goes 😅111 -
A fellow intern recommended the use of windows server for security and speed reasons.
Few details about the situation: windows server got hacked due to a vulnerability which had no patch released yet and this had happened multiple times that year. Also, the company was migrating everything to Linux (servers).
The senior/lead programmer literally gave him a GTFO face and pointed at the door.
Everyone was giving him the GTFO face by the way, he didn't know how fast he had to get out 🤣8 -
*Facebook Hackers follow the Rules*
(real story)
TL;DR: sorry, not available, can't do spoilers
One night I was with a group of friends out at a pub. A guy and his girlfriend show up, I didn't know them but they were my friend's friends.
The girl kept bragging the whole time about his boyfriend being a professional programmer, trying to remind it to everybody whenever possible (don't ask me why!).
So, after a while, the discussion moves towards "suspect Facebook activities" and the guy starts saying that he can hack Facebook.
- "What do you mean?", I ask.
- "Hacking into other people's accounts, even with 2 factor authentication. I did it a lot of times"
- "Wait, and they don't notice?"
- "Of course not! ^_^ He's a hacker", the girl replies.
Ok, time to do a coming out.
- "Hey, I'm a developer myself. Can you give me an idea of what you did in technical terms? Did you find a vulnerability? Used a virus? Maybe a keylogger?"
- "No... Uh... Well... The secret is to read the terms of service"
- "What?"
- "Yes... yes it's all in the facebook terms of service..."
- "Uhm, I'm not really sure I'm following. Could you prove it by hacking my Facebook account? I'm giving you the permission".
In less than a minute the discussion flew completely away and they never mentioned computers again.
😂😂8 -
⚠️ DEVRANTRON ALERT ⚠️
Make sure you've updated devRantron to v.1.3.6 since previous versions contains an XSS vulnerability.
<b>If this text is BOLD you're vulnerable.</b>
You can download the latest version at https://github.com/tahnik/...20 -
A quite severe vulnerability was found in Skype (at least for windows, not sure about other systems) allowing anyone with system access (remote or local) to replace the update files skype downloads before updating itself with malicious versions because skype doesn't check the integrity of local files. This could allow an attacker to, once gaining access to the system, 'inject' any malicious DLL into skype by placing it in the right directory with the right file name and waiting for the user to update (except with auto updates of course).
From a company like Microsoft, taking in mind that skype has hundreds of millions of users worldwide, I'd expect them to take a very serious stance on this and work on a patch as soon as possible.
What they said about this: they won't be fixing it anytime soon as it would require a quite big rewrite of skype.
This kinda shit makes me so fucking angry, especially when it comes from big ass companies 😡. Take your fucking responsibility, Microsoft.16 -
The awesome moment when a client claims that you are nothing but a script kiddy only minutes before you reveal a $1400 vulnerability on his site 😂4
-
Security tester: Injects XSS into a rich text editor and flags it for a vulnerability.
"Oh that's fine, let's just disable right click on our page so no one can inspect the page and inject anything."
...
My boss ladies and gentlemen.9 -
Corporate IT: YOU MUST COME INTO THE OFFICE. WE JUST RECEIVED AN URGENT NOTIFICATION FROM APPLE OF A SECURITY VULNERABILITY IN iOS DEVICES. YOU HAVE BEEN IDENTIFIED AS HAVING A MAC ASSET. COME INTO THE OFFICE IMMEDIATELY AND UPDATE IT.
Dev: I don’t use that mac, it sits in my office desk drawer unplugged. I’ll update it if I ever need it for anything. Which I won’t, we don’t do iOS dev anymore.
Corporate IT: NOOOOO!!! YOU MUST UPDATE IT NOW!!!
Dev: I’m not wasting time driving into the office this week. We have an important deadline we’re working on, I can’t afford to lose 2 hours to this. Plus it can’t be turned on right now, It’s been unplugged for 2 years.
Corporate IT: THAT WOULDN’T STOP A HACKER!!
Dev: …11 -
This happened at my last internship. There was this other intern and he was a TO THE FUCKING MAX windows fanboy and whenever someone said something bad about windows he'd go full rage. Also, he'd sometimes spend half an hour at my desk explaining why windows was the best and Linux sucked.
This one time, I read about a newly discovered windows vulnerability and told the employees so they'd update quickly and they were like ' thanks for the notification mate!' And then that guy came up to me telling that 'Linux also has severe vulnerabilities sometimes'. YES I FUCKING KNOW THAT I'M JUST TRYING TO GET PEOPLE TO UPDATE FOR THEIR SECURITY YOU FUCKING ASSHAT. I got really mad. Still, fuck that guy.9 -
A group of Security researchers has officially fucked hardware-level Intel botnet officially branded as "Intel Management Engine" they did so by gathering it all the autism they were able to get from StackOverflow mods... though they officially call it a Buffer Overflow.
On Wednesday, in a presentation at Black Hat Europe, Positive Technologies security researchers Mark Ermolov and Maxim Goryachy plan to explain the firmware flaws they found in Intel Management Engine 11, along with a warning that vendor patches for the vulnerability may not be enough.
Two weeks ago, the pair received thanks from Intel for working with the company to disclose the bugs responsibility. At the time, Chipzilla published 10 vulnerability notices affecting its Management Engine (ME), Server Platform Services (SPS), and Trusted Execution Engine (TXE).
The Intel Management Engine, which resides in the Platform Controller Hub, is a coprocessor that powers the company's vPro administrative features across a variety of chip families. It has its own OS, MINIX 3, a Unix-like operating system that runs at a level below the kernel of the device's main operating system.
It's a computer designed to monitor your computer. In that position, it has access to most of the processes and data on the main CPU. For admins, it can be useful for managing fleets of PCs; it's equally appealing to hackers for what Positive Technologies has dubbed "God mode."
The flaws cited by Intel could let an attacker run arbitrary code on affected hardware that wouldn't be visible to the user or the main operating system. Fears of such an attack led Chipzilla to implement an off switch, to comply with the NSA-developed IT security program called HAP.
But having identified this switch earlier this year, Ermolov and Goryachy contend it fails to protect against the bugs identified in three of the ten disclosures: CVE-2017-5705, CVE-2017-5706, and CVE-2017-5707.
The duo say they found a locally exploitable stack buffer overflow that allows the execution of unsigned code on any device with Intel ME 11, even if the device is turned off or protected by security software.
For more of the complete story go here:
https://blackhat.com/eu-17/...
https://theregister.co.uk/2017/12/...
I post mostly daily news, commentaries and such on my site for anyone that wish to drop by there 19
19 -
It's funny, whenever the subject of facebook vs privacy comes up (mostly I don't even initiate those convo's), people always start to defend facebook when I say that I THINK that facebook is build to get people addicted to it and get them to stay on facebook as long as possible.
Haha, one of facebook's early investers/ex facebook presidents said the following in an interview:
“It’s a social-validation feedback loop, exactly the kind of thing that a hacker like myself would come up with, because you’re exploiting a vulnerability in human psychology.”
So even an ex president of facebook is admitting this.
I also found the folloing a good one:
The underlying thought process while creating platforms like Facebook or Instagram is something like “How do we consume as much of your time and conscious attention as possible?”
Last but not least, the part I found the most scary:
“God only knows what it’s doing to our children’s brains.”
Yes, I find this scary.
Oh yeah and for the people who are going to call bullshit on this one, I've got one source and if you search engine on the title of that article then you'll find loads of websites having that story:
https://fossbytes.com/facebook-was-...26 -
So WPA2 has been broken.
That's quite a bad news coming so shortly after the BlueBourne vulnerability was discovered
Read more here if interested:
https://www.krackattacks.com/9 -
!rant
The change log from notepad++ update. The last paragraph is the cream!
" The issue of a hijacked DLL concerns scilexer.dll (needed by Notepad++) on a compromised PC, which is replaced by a modified scilexer.dll built by the CIA. When Notepad++ is launched, the modified scilexer.dll is loaded instead of the original one.
It doesn't mean that CIA is interested in your coding skill or in your sex message content typed in Notepad++, but rather it prevents raising any red flags while the DLL does data collection in the background.
It's not a vulnerability/security issue in Notepad++, but for remedying this issue, from this release (v7.3.3) forward, notepad++.exe checks the certificate validation in scilexer.dll before loading it. If the certificate is missing or invalid, then it just won't be loaded, and Notepad++ will fail to launch.
Checking the certificate of DLL makes it harder to hack. Note that once users’ PCs are compromised, the hackers can do anything on the PCs. This solution only prevents from Notepad++ loading a CIA homemade DLL. It doesn't prevent your original notepad++.exe from being replaced by modified notepad++.exe while the CIA is controlling your PC.
Just like knowing the lock is useless for people who are willing to go into my house, I still shut the door and lock it every morning when I leave home. We are in a f**king corrupted world, unfortunately. "2 -
A critical vulnerability was detected in Electron and I urge all the devRantron users to update their app manually.
Please go to https://www.devrantron.com get the latest version which has the necessary patches.
Due to a request, we added compact mode in the app, which can be used to view a distraction-free mode of the UI. Notifications screen is a little bit more readable now. The read notifications are now greyed out.
Again, the auto update will not work for this version. Please manually update as soon as possible. 6
6 -
--- URGENT: Major security flaw in Kubernetes: Update Kubernetes at all costs! ---
Detailed info: https://github.com/kubernetes/...
If you are running any unpatched versions of Kubernetes, you must update now. Anyone might be able to send commands directly to your backend through a forged network request, without even triggering a single line in the log, making their attack practically invisible!
If you are running a version of Kubernetes below 1.10... there is no help for you. Upgrade to a newer version, e.g. 1.12.3. 18
18 -
Long story short, I'm unofficially the hacker at our office... Story time!
So I was hired three months ago to work for my current company, and after the three weeks of training I got assigned a project with an architect (who only works on the project very occasionally). I was tasked with revamping and implementing new features for an existing API, some of the code dated back to 2013. (important, keep this in mind)
So at one point I was testing the existing endpoints, because part of the project was automating tests using postman, and I saw something sketchy. So very sketchy. The method I was looking at took a POJO as an argument, extracted the ID of the user from it, looked the user up, and then updated the info of the looked up user with the POJO. So I tried sending a JSON with the info of my user, but the ID of another user. And voila, I overwrote his data.
Once I reported this (which took a while to be taken seriously because I was so new) I found out that this might be useful for sysadmins to have, so it wasn't completely horrible. However, the endpoint required no Auth to use. An anonymous curl request could overwrite any users data.
As this mess unfolded and we notified the higher ups, another architect jumped in to fix the mess and we found that you could also fetch the data of any user by knowing his ID, and overwrite his credit/debit cards. And well, the ID of the users were alphanumerical strings, which I thought would make it harder to abuse, but then realized all the IDs were sequentially generated... Again, these endpoints required no authentication.
So anyways. Panic ensued, systems people at HQ had to work that weekend, two hot fixes had to be delivered, and now they think I'm a hacker... I did go on to discover some other vulnerabilities, but nothing major.
It still amsues me they think I'm a hacker 😂😂 when I know about as much about hacking as the next guy at the office, but anyways, makes for a good story and I laugh every time I hear them call me a hacker. The whole thing was pretty amusing, they supposedly have security audits and QA, but for five years, these massive security holes went undetected... And our client is a massive company in my country... So, let's hope no one found it before I did.6 -
10 years ago, I found a vulnerability in the connection between an insurer I was working for, and the network of databases of municipalities. I was only a hacker in so far as kids who watched Hak5 are considered hackers, so I always carried this laptop with a fake access point, package sniffer, wep crack, sslstrip, etc with me.
The vulnerabilities allowed me to register a new identity, for which I requested a passport.
Walking up to the town hall desk with two passports with different names, both mine, was pretty cool.
I did not do anything malicious, and was hired to fix the issues (wep encryption on insurers trusted wifi, and municipality postgres gave write access to all third parties)
For a few days I was the coolest kid in school though!2 -
Forgive me father, for I have sinned. Alot actually, but I'm here for technical sins. Okay, a particular series of technical sins. Sit your ass back down padre, you signed up for this shit. Where was I? Right, it has been 11429 days since my last confession. May this serve as equal parts rant, confession, and record for the poor SOB who comes after me.
Ended up in a job where everything was done manually or controlled by rickety Access "apps". Many manhours were wasted on sitting and waiting for the main system to spit out a query download so it could be parsed by hand or loaded into one of the aforementioned apps that had a nasty habit of locking up the aged hardware that we were allowed. Updates to the system were done through and awful utility that tended to cut out silently, fail loudly and randomly, or post data horrifically wrong.
Fuck that noise. Floated the idea of automating downloads and uploads to bossman. This is where I learned that the main system had no SQL socket by default, but the vendor managing the system could provide one for an obscene amount of money. There was no buy in from above, not worth the price.
Automated it anyway. Main system had a free form entry field, ostensibly for handwriting SELECT queries. Using Python, AutoHotkey, and glorified copy-pasting, it worked after a fashion. Showed the time saved by not having to do downloads manually. Got us the buy in we needed, bigwigs get negotiating with the vendor, told to start developing something based on some docs from the vendor. Keep the hacky solution running as team loves not having to waste time on downloads.
Found SQLi vulnerability in the above free form query system, brought it up to bossman to bring up the chain. Vulnerability still there months later. Test using it for automated updates. Works and is magnitudes more stable than update utility. Bring it up again and show the time we can save exploiting it. Decision made to use it while it exists, saves more time. Team happier, able to actual develop solutions uninterrupted now. Using Python, AutoHotkey, glorified copy-pasting, and SQLi in the course of day to day business critical work. Ugliest hacky thing I've ever caused to exist.
Flash forward 6 years. Automation system now in heavy use acrossed two companies. Handles all automatic downloads for several departments, 1 million+ discrete updates daily with alot of room for expansion, stuff runs 24/7 on schedule, most former Access apps now gone and written sanely and managed by the automation system. Its on real hardware with real databases and security behind it.
It is still using AutoHotkey, copy-paste, and SQLi to interface with the main system. There never was and never will be a SQL socket. Keep this hellbeast I've spawned chugging along.
I've pointed out how many ways this can all go pearshaped. I've pointed out that one day the vendor will get their shit together they'll come in post system update and nothing will work anymore. I've pointed out the danger in continuing to use the system with such a glaring SQLi vulnerability.
Noone cares. Won't be my problem soon enough.
In no particular order:
Fuck management for not fighting for a good system interface
Fuck the vendor for A) not having a SQL socket and B) leaving the SQLi vulnerability there this long
Fuck me for bringing this thing into existence5 -
I once had to literally hack a Joomla 1.5.x site for a client, because they did not find the passwords (hosting, cms, ftp, mysql). After 5 minutes and a SQL injection I was in like flynn.
The site was already full of hidden links to viagra sellers and stuff... 😂1 -
Darn it, I was having such a good day. Just sitting over here in sysadmin land watching the Java devs tear their hair out over the Log4j vulnerability, when someone just had to ask me about the Jenkins servers my team maintains.
Jenkins doesn't use Log4j! What a relief!
Jenkins does, however, have third-party plugins, some of which use Log4j. And thus my relief was short-lived and now I'm also tearing out my hair trying to patch this shit.17 -
What an absolute fucking disaster of a day. Strap in, folks; it's time for a bumpy ride!
I got a whole hour of work done today. The first hour of my morning because I went to work a bit early. Then people started complaining about Jenkins jobs failing on that one Jenkins server our team has been wanting to decom for two years but management won't let us force people to move to new servers. It's a single server with over four thousand projects, some of which run massive data processing jobs that last DAYS. The server was originally set up by people who have since quit, of course, and left it behind for my team to adopt with zero documentation.
Anyway, the 500GB disk is 100% full. The memory (all 64GB of it) is fully consumed by stuck jobs. We can't track down large old files to delete because du chokes on the workspace folder with thousands of subfolders with no Ram to spare. We decide to basically take a hacksaw to it, deleting the workspace for every job not currently in progress. This of course fucked up some really poorly-designed pipelines that relied on workspaces persisting between jobs, so we had to deal with complaints about that as well.
So we get the Jenkins server up and running again just in time for AWS to have a major incident affecting EC2 instance provisioning in our primary region. People keep bugging me to fix it, I keep telling them that it's Amazon's problem to solve, they wait a few minutes and ask me to fix it again. Emails flying back and forth until that was done.
Lunch time already. But the fun isn't over yet!
I get back to my desk to find out that new hires or people who got new Mac laptops recently can't even install our toolchain, because management has started handing out M1 Macs without telling us and all our tools are compiled solely for x86_64. That took some troubleshooting to even figure out what the problem was because the only error people got from homebrew was that the formula was empty when it clearly wasn't.
After figuring out that problem (but not fully solving it yet), one team starts complaining to us about a Github problem because we manage the github org. Except it's not a github problem and I already knew this because they are a Problem Team that uses some technical authoring software with Git integration but they only have even the barest understanding of what Git actually does. Turns out it's a Git problem. An update for Git was pushed out recently that patches a big bad vulnerability and the way it was patched causes problems because they're using Git wrong (multiple users accessing the same local repo on a samba share). It's a huge vulnerability so my entire conversation with them went sort of like:
"Please don't."
"We have to."
"Fine, here's a workaround, this will allow arbitrary code execution by anyone with physical or virtual access to this computer that you have sitting in an unlocked office somewhere."
"How do I run a Git command I don't use Git."
So that dealt with, I start taking a look at our toolchain, trying to figure out if I can easily just cross-compile it to arm64 for the M1 macbooks or if it will be a more involved fix. And I find all kinds of horrendous shit left behind by the people who wrote the tools that, naturally, they left for us to adopt when they quit over a year ago. I'm talking entire functions in a tool used by hundreds of people that were put in as a joke, poorly documented functions I am still trying to puzzle out, and exactly zero comments in the code and abbreviated function names like "gars", "snh", and "jgajawwawstai".
While I'm looking into that, the person from our team who is responsible for incident communication finally gets the AWS EC2 provisioning issue reported to IT Operations, who sent out an alert to affected users that should have gone out hours earlier.
Meanwhile, according to the health dashboard in AWS, the issue had already been resolved three hours before the communication went out and the ticket remains open at this moment, as far as I know.5 -
I have a Kali Linux VM running on my Windows machine. I decide to try and exploit the Windows machine (THAT THE VM WAS RUNNING ON) because of a vulnerability with smb that requires NO user interaction. I decided to make my computer shoot its own legs and I thought "Hey, this is gonna be fine."
Aaaaand the whole system crashed on me.3 -
I found a vulnerability in a food delivery app api that allows me to add credit to my account. I ate my first free meal today but i feel bad about it. What should i do 😞.
1- continue hacking free credit and eating free food.
2- stop and forget i found this bug
3- report the bug in exchange for money/credit
4- report the bug for free23 -
Me: reports vulnerability that can be used to steal thousands of dollars from a company.
Stingy company: gives me 66 USD voucher as a reward. :)11 -
I think the hardest thing about being a programmer in college with a security emphasis is when I approach a business for a penetration test or for a vulnerability analysis (your pick) is that they almost always say, "you are pretty young don't you think?"
Ummmm not sure what that has to do with it. If it would make you feel better I have claimed bug bounties from an antivirus company, a bank, several local businesses in my area and I do this for work at my 9-5.
And this week I got this, "I think I would like someone older so we can define the goals better."
Oh so rules of engagement, yeah of course I understand that and that's something we would discuss and draw up a contract for...
"Well we really need someone more skilled."
---- End of story ----
I don't understand, you haven't asked about certifications or schooling and you glanced at my resume for exactly 5 seconds what the hell do you want? Me to double my age over night?7 -
I think we're going two sides:
For one, more and more technology is being developed/engineered which is even more and more and more intrusive as for personal privacy, I'm genuinely worried how this'll go as privacy isn't just a about not exposing certain things like passwords/bank account details and so on, it's also about being an individual who has their own thoughts, opinions and so on. If we keep taking that away more and more often, society will change and go towards the Orwell scenario (we're on our way there right now). We can change this as software/design/server engineers but that's up to us and I sadly don't see that happening quickly, also due to the 'nothing to hide' bullshit.
Second one is that were going more and more towards open source.
This is a good thing as this:
- gives freedom to devs around the world to improve software and/or modify it to suit their needs.
- gives people the opportunity to look through the source code of softwares in order to verify it as for backdoors and find security vulnerabilities which otherwise can remain hidden for the general public while spying agencies have way more resources to go vulnerability hunting.
For the people who think this isn't a good idea (even more open source), without it we'd be completely fucked as for moving forward/security/privacy. (I can give examples if wanted).3 -
Really cool. Tesla gave two hackers that found a vulnerability in the Model 3 free cars as a reward. More companies should do that, instead of getting all pissy. I would hope a company wants to know what their vulnerabilities are so that they can avoid embarrassment and the loss of money.2
-
I make a typo in the username
"username doesn't exist"
I fix the typo and mess up the password
"incorrect password"
... I smell a potential exploit here...7 -
Well, fuck.
source: https://amdflaws.com
https://wired.com/story/...
Really ugly to release it a day after telling AMD about it 10
10 -
Vulnerability scanning is not penetration testing.
Vulnerability scanning is not penetration testing.
Vulnerability scanning is not penetration testing.
Vulnerability scanning is not penetration testing.
Vulnerability scanning is not penetration testing.
Vulnerability scanning is not penetration testing.
Vulnerability scanning is not penetration testing.
Vulnerability scanning is not penetration testing.
Vulnerability scanning is not penetration testing.
Vulnerability scanning is not penetration testing.
Vulnerability scanning is not penetration testing.
Vulnerability scanning is not penetration testing.
Vulnerability scanning is not penetration testing.
Vulnerability scanning is not penetration testing.
Vulnerability scanning is not penetration testing.9 -
> IHateForALiving: I have added markdown on the client! Now the sys admin can use markdown and it's going to be rendered as HTML
> Team leader: ok, I've seen you also included some pics of the tests you made. It's nice, there's no XSS vulnerabilities, now I want you to make sure you didn't introduce any SQL injection too. Post the results of the tests in the tickets, for everybody to see.
I've been trying to extract from him for 15 minutes how sending a text through a markdown renderer on the client is supposed to create a SQL injection on the server, I've been trying to extract from him how showing all of this to the world would improve our reputation.
I miserably failed, I don't know how the fuck am I supposed to test this thing and if I a colleague wasted time to make sure some client-side rendering didn't create a SQL injection I'd make sure to point and laugh at them every time they open their mouth.9 -
Okay, That right there is pathetic https://thehackernews.com/2019/02/... .
First of all telekom was not able to assure their clients' safety so that some Joe would not access them.
Second of all after a friendly warning and pointing a finger to the exact problem telekom booted the guy out.
Thirdly telekom took a defensive position claiming "naah, we're all good, we don't need security. We'll just report any breaches to police hence no data will be leaked not altered" which I can't decide whether is moronic or idiotic.
Come on boys and girls... If some chap offers a friendly hand by pointing where you've made a mistake - fix the mistake, Not the boy. And for fucks sake, say THANK YOU to the good lad. He could use his findings for his own benefit, to destroy your service or even worse -- sell that knowledge on black market where fuck knows what these twisted minds could have done with it. Instead he came to your door saying "Hey folks, I think you could do better here and there. I am your customes and I'd love you to fix those bugzies, 'ciz I'd like to feel my data is safe with you".
How on earth could corporations be that shortsighted... Behaviour like this is an immediate red flag for me, shouting out loud "we are not safe, do not have any business with us unless you want your data to be leaked or secretly altered".
Yeah, I know, computer misuse act, etc. But there are people who do not give a tiny rat's ass about rules and laws and will find a way to do what they do without a trace back to them. Bad boys with bad intentions and black hoodies behind TOR will not be punished. The good guys, on the other hand, will.
Whre's the fucking logic in that...
P.S. It made me think... why wouldn't they want any security vulns reported to them? Why would they prefer to keep it unsafe? Is it intentional? For some special "clients"? Gosh that stinks6 -
Guess what? 😱 WordPress has probably an SQL injection vulnerability. Check it out and fix your installations, when more info will be known:
https://twitter.com/ircmaxell/...11 -
Anyone hear about the emergency patch that Microsoft just released? Its a RCE vulnerability CVE-2017-11937 which ironically targets all of Microsoft's security products.
Basically when Windows defender scans a specially crafted file the attacker can run code as the LocalSystem. Nice one Microsoft!1 -
FYI to anyone following the Krack WPA2 vulnerability
A testing suite in python has made its way to github.
https://github.com/vanhoefm/... -
> Be chad lodash dev
> new security vulnerability discovered in April
> low
> virgin devs ask to fix https://github.com/lodash/lodash/...
> giving no shit, because lodash stronk https://github.com/lodash/lodash/...
> fast forward now
> NPM lists lodash as vulnerability, because no fix
> 1000s of downstream projects affected
> https://github.com/lodash/lodash/...
> surprised pikachu face10 -
I really wanna share this with you guys.
We have a couple of physical servers (yeah, I know) provided by a company owned by a friend of my boss. One of them, which I'll refer to as S1, hosted a couple of websites based on Drupal 7... Long story short, every php file got compromised after someone used a vulnerability within D7's core to inject malicious code. Whatver, wasn't a project of mine, and no one bothered to do anything about it... The client was even happy about not doing anything about it. We did stop making backups of such websites however, to avoid spreading the damage (right?). So, no one cared about this for months!
But last monday? The physical server was offline. I powered it on again via its web management interface... Dead after less than an hour. No backups. Oh well, I guess I couls keep powering it on to check what's wrong with it and attempt to fix it...
That's when I've learned how the web management interface works: power on/reboot requests prompted actual workers to reach the physical server and press the power on/reboot buttons.
That took a while to sink in. I mean, ok, theu are physical servers... But aren't they managed anyhow? They are just... Whatever. Rebooting over and over wasn't the solution, so I asked if they could move the HDD to another of our servers... The answer was it required to buy a "server installation" package. In short, we'd have had to buy a new physical server, or renew the subscription of one we already owned for 6 months.
So... I've literally spent the rest of the day bothering their emoloyeea to reboot S1, until I've reached the "daily reboot reauests limit" (which amounts to 3 reauests. seriously), whicj magically opened a support ticket where a random guy advised to stop using VNC as "the server was responsive" and offeres to help me with the command line.
Fiiine, I sort of appreciate it. My next message has been a kernel log which shows how the OS dying out was due to physical components becoming unavailable after a while, and how S1 lacked a VNC server, being accessible only via ssh. So, the daily reboot limit was removes for S1. Yay.
...What to do though? S1 was down, we had no backups, and asking for manual rebooting every time was slow as Hell. ....Then I went insane. I asked for 1 more reboot. su. crontab -e. */15 * * * * /sbin/shutdown -r +5. while true; do; rsync --timeout=20 --append S1:/stuff .; sleep 60; done.
It worked. We have now again access to 4 hacked, shitty Drupal 7 websites. My boss stopped shouting. I can get back to my own projects.
Apparently, those D7 websites got back online too, still with malicious php code within them. Well, not my problem (for now).
Meanwhile, S1 is still rebooting.3 -
For all you Googlefags, "Serious Chrome zero-day – Google says update right this minute":
https://nakedsecurity.sophos.com/20... 16
16 -
DigitalOcean released this public message in response to Intels MDS. Definitely worth reading if you run servers at DO. https://blog.digitalocean.com/may-2...1
-
I recently found a vulnerability in a food delivery app where i can add credit to my account. as some of u suggested I decided to report it. Here is their response of me asking (before explaining the bug) if i will be legally prosecuted and if ill be rewarded. this was their response. I feel they were mean. Thoughts ?
 11
11 -
Reported an important security vulnerability inside our organization, right before getting off work. A security team member contacts me over chat asking for some details on my investigation. At the end, he tells me: "thanks, I will copy and paste this conversation on the ticket so that everyone can see".
What I imagined: he would copy and paste the conversation as is, so that every line written by me is prefixed with my name.
What he does: he writes a summary of our conversation, barely mentioning my name, making it look like that part of the investigation was done by him.
Now I have so much anger inside of me that my internal organs are boiling.6 -
watching the online course for CEH... dude used the Death Star as a tangible example of how exploits work.
IDK if I should love it for the nerdiness, or be slightly sad that someone needs that type of example of what a vulnerability vs an exploit is, when they're going for the Certified Ethical Hacker certification...
Might be better in an introduction to Network Security class?
Also, while discussing the security, usability, and functionality triangle, he reference the Staples "Easy Button" - does one thing, not very secure, and not very functional (in that it has more than one function)...1 -
Paranoia. Programming affected my life by making me paranoid. Creating a new account on any website that even needs rudimentary information about me has to go quite some vulnerability testing since I've seen enough hack jobs that throw around sensitive data because they're too incompetent to follow simple must dos.3
-
I found a vulnerability in a famous financial institute site. So I asked their customer care over email, how can I report it?
They said: "remove your cookies" 🤦9 -
Putty remote executuon vulnerability(no patch yet)
The vulnerability allows a remote attacker to execute arbitrary code on the target system.
The vulnerability exists due to unspecified input validation error when processing data, received from SSH server. A remote attacker can trick the victim to connect to a specially crafted SSH server and execute arbitrary code on the target system with privileges of the current user.
Successful exploitation of the vulnerability may allow an attacker to compromise vulnerable system.7 -
Yet another funny bug for your iPhone friends. Oh Apple...
"The vulnerability can be exploited by loading an HTML page that uses specially crafted CSS code. The CSS code isn't very complex and tries to apply a CSS effect known as backdrop-filter to a series of nested page segments (DIVs)."
https://zdnet.com/article/...7 -
Ya'll know what... If humans weren't such annoying vulnerability-searching little shits then we wouldn't have had to implement any protection against them and think of all the performance that would be saved on that. Take branch prediction vulnerability mitigation in the Linux kernel for example, that's got to make a performance hit of least 10% on basically everything.
Alas, I do get why security is important and why we keep such vulnerability mitigation running despite the performance hit. I get why safe code is necessary but still... if these people weren't such annoying little bastards.
Yeah, I was just kind of set off by the above. So much would be faster and easier if only the programmers wouldn't have to plan for people exploiting their software. Software would be written much faster and humans would progress to stuff that actually matters like innovation.8 -
Do you know the auto-generated heroku sample app? The very complex demo app you automatically get following the tutorial?
It has a vulnerability.
I laughed a lot 2
2 -
!rant
Reddit comment on a thread about Joomla! sites being vulnerable to SQL-injections:
"Joomla sites are so infested they became sentient.
Joomla sites needs no webmaster, some one else will administer it for you.
Joomla sites have very good SEO, specially in "v1agra c1alis p3nis size"
Traffic count with Joomla is high, all the bots breaking all the vulnerabilities count for somethin'."
😂 Pure gold.1 -
So one of my clients had a different company do a penetrationtest on one of my older projects.
So before hand I checked the old project and upgraded a few things on the server. And I thought to myself lets leave something open and see if they will find it.
So I left jquery 1.11.3 in it with a known xss vulnerability in it. Even chrome gives a warning about this issue if you open the audit tab.
Well first round they found that the site was not using a csrf token. And yeah when I build it 8 years ago to my knowledge that was not really a thing yet.
And who is going to make a fake version of this questionair with 200 questions about their farm and then send it to our server again. That's not going to help any hacker because everything that is entered gets checked on the farm again by an inspector. But well csrf is indeed considered the norm so I took an hour out of my day to build one. Because all the ones I found where to complicated for my taste. And added a little extra love by banning any ip that fails the csrf check.
Submitted the new version and asked if I could get a report on what they checked on. Now today few weeks later after hearing nothing yet. I send my client an email asking for the status.
I get a reaction. Everything is perfect now, good job!
In Dutch they said "goed gedaan" but that's like what I say to my puppy when he pisses outside and not in the house. But that might just be me. Not knowing what to do with remarks like that. I'm doing what I'm getting paid for. Saying, good job, your so great, keep up the good work. Are not things I need to hear. It's my job to do it right. I think it feels a bit like somebody clapping for you because you can walk. I'm getting off topic xD
But the xss vulnerability is still there unnoticed, and I still have no report on what they checked. So I have like zero trust in this penetration test.
And after the first round I already mentioned to the security guy in my clients company and my daily contact that they missed things. But they do not seem to care.
Another thing to check of their to do list and reducing their workload. Who cares if it's done well it's no longer their responsibility.
2018 disclaimer: if you can't walk not trying to offend you and I would applaud for you if you could suddenly walk again.2 -
Holy heavens! I'm gonna work with a js framework at my day job.
After installing nodejs I'm immediately greeted by a warning that something is somehow broken. Installing the packages for the barebones repo leads to hundreds of dependencies and vulnerability warnings. I don't even know anything beyond document.getElementById().
On a scale of 1 to Squidward Tentacles, how much am I gonna hate my job?8 -
A few days back I read an article about ethical hacking and get rewarded for bug bounty. I thought that might be interested.
AND
I'm about to send out my first ethical hack report to a company! I'm nervous because I don't know how they'll respond. It's an xss vulnerability, and I really hope they'll fix it.5 -
Anyone reading these emails we are sending?
I work at a small place. A few users are using an application at our place that I develop and maintain. We all work remotely.
I announce by email to these few users a new version release of said application because of low level changes in the database, send the timeline for the upgrade, I include the new executable, with an easy illustrated 2 minutes *howto* to update painlessly.
Yet, past the date of the upgrade, 100% of the application users emailed me because they were not able to use the software anymore.
----------------
Or I have this issue where we identified a vulnerability in our systems - and I send out an email asking (as soon as possible) for which client version users are using to access the database, so that I patch everything swiftly right. Else everything may crash. Like a clean summary, 2 lines. Easy. A 30 second thing.
A week pass, no answer, I send again.
Then a second week pass, one user answers, saying:
> well I am busy, I will have time to check this out in February.
----------------
Then I am asking myself:
* Why sending email at all in the first place?
* Who wrote these 'best practices textbooks about warning users on schedule/expected downtime?'
*How about I just patch and release first and then expect the emails from the users *after* because 'something is broken', right? Whatever I do, they don't read it.
Oh and before anyone suggest that I should talk to my boss about this behavior from the users, my boss is included in the aforementioned 'users'.
Catch-22 much ? Haha thanks for reading
/rant7 -
Today I had a problem with a JS framework. The only person who was available who could help me was the one I avoid, because he always knows everything better.
Well, after I asked if he had time for me, he sits next to me and I started to explain.
After looking around, he started blaming my backend code.
(I belong to the kind of dev that tries to write small and simple code. But I also often use the more complex features of the languages.) He suddenly started accusing everyday things in the backend like inheriting a class or using objects and basic data types together as parameters of a method (WTF???) Hell, all I could say at that moment was that I had a problem with this JS framework and not with the backend that worked well. He probably tried for over an hour to find the bug in the backend and just wouldn't listen, after that he gave up. I wonder what this bitch has learned over the years. Can it really be that he forgot the basics of a programming language? Or has the fool never worked with an inheritance before? I think he's an incapable piece of shit, he hasn't even patched my reported vulnerability in his project in the last half year, which allows to inject own code onto the server.
Because of such fucking morons I get a headache when I think about it. How can it be that he's got a higher degree and earns about 50% more. I should leave this company!3 -
Few months back, I reported a vulnerability in an open source project due to the fake alarm from Github without understanding it's consequences. The author of that project immediately locked, and closed the issue and deleted the detail.
Though he was annoyed with my this act but he taught me a good lesson of responsibility.
https://en.wikipedia.org/wiki/...3 -
"One misstep from developers at Starbucks left exposed an API key that could be used by an attacker to access internal systems and manipulate the list of authorized users," according to the report of Bleeping Computer.
Vulnerability hunter Vinoth Kumar reported and later Starbucks responded it as "significant information disclosure" and qualified for a bug bounty. Along with identifying the GitHub repository and specifying the file hosting the API key, Kumar also provided proof-of-concept (PoC) code demonstrating what an attacker could do with the key. Apart from listing systems and users, adversaries could also take control of the Amazon Web Services (AWS) account, execute commands on systems and add or remove users with access to the internal systems.
The company paid Kumar a $4,000 bounty for the disclosure, which is the maximum reward for critical vulnerabilities.6 -
Apache Tomcat vulnerability "GHOSTCAT" allows read conduct files and implant web shells. All versions in the last 13 years vulnerable.
According to Security Researcher of Chaitin Tech : Due to a flaw in the Tomcat AJP protocol (the channel for Tomcat to connect to the outside, pass them to the corresponding web application for processing and return the response result of the request), an attacker can read or include any files in the webapp directories of Tomcat.
For example, An attacker can read the web-app configuration files or source code. In addition, if the target web application has a file upload function, the attacker may execute malicious code on the target host by exploiting file inclusion through "GHOSTCAT" vulnerability.
Apache Tomcat has officially released versions 9.0.31, 8.5.51, and 7.0.100 to fix this vulnerability.4 -
Social Captain (a service to increase a user's Instagram followers) has exposed thousands of Instagram account passwords. The company says it helps thousands of users to grow their Instagram follower counts by connecting their accounts to its platform. Users are asked to enter their Instagram username and password into the platform to get started.
According to TechCrunch : Social Captain was storing the passwords of linked Instagram accounts in unencrypted plaintext. Any user who viewed the web page source code on their Social Captain profile page could see their Instagram username and password in plain text, as they had connected their account to the platform. A website bug allowed anyone access to any Social Captain user's profile without having to log in ; simply plugging in a user's unique account ID into the company's web address would grant access to their Social Captain account and their Instagram login credentials. Because the user account IDs were for the most part sequential, it was possible to access any user's account and view their Instagram password and other account information easily. The security researcher who reported the vulnerability provided a spreadsheet of about 10,000 scraped user accounts to TechCrunch.3 -
PSA: If you use jQuery and BlueImp's jQuery File Upload there is a big potential vulnerability you need to be aware of. If you use NPM to pull the repo into your public folder, the "server" folder will be available for people to take advantage of. "Hackers" may be able to upload malicious code and replace parts of your site.
I had a site hacked and later saw on Google Analytics that people were posting to random URLs in that folder. The fix is to simply delete that folder, but if you use NPM, you need to be extra careful it doesn't come back.
Also, I didn't investigate further. So I'm not sure what (if anything) is vulnerable in there, or if it was just the specific version I had. To be safe, if you use this plugin (as MANY people do), just delete the folder.
Link to the repo for your reference: https://github.com/blueimp/... 4
4 -
A few days ago, I saw a topic from hackernews about Xiaomi phones having a high risk vulnerability because of analytics.apk. I didn't mind it (I'm using a Xiaomi phone).
After about 2 days, I had a notification on my screen having a message 'test' made by my browser.
I immediately installed a firewall blocking all Xiaomi related services.
WTF Xiaomi 3
3 -
Apple paid bounty hunter 18k instead of 250k by silently tweaking their help page, so it seems like the bug is less severe.
Dear apple, I defended you from baseless and opinionated attacks just like I defend every company that is bashed for no reason, but this is some straight up bouba shit. I will still be fair when it comes to your products, still never silencing bugs and downsides and praising what deserves to be praised, but I will always mention this incident when someone asks me about _working_ at apple. That kind of ethics bs can't be silenced just because I enjoy your new arm chip.
https://thezerohack.com/apple-vulne...12 -
I don't know who I hate more, regular thieves or crackers.
I think the second ones more, because they don't even have the balls to risk in person…
To whoever decided to throw away one week of my life, which I spent in a dark office in July importing a fucking WordPress website, FUCK OFF!
I fucking hate WordPress, I fucking hate migrate websites with it and also dealing with incompatibilities in 30+ plugins and templates that doesn't work properly (Avada, best seller? For being shitty maybe), and now every time I will have to do it I will think about how much I hate you, the bastard who decided to drop those shitty database tables.
And I'm sorry but we won't send you bitcoins just because you watched a tutorial on YouTube and used a vulnerability in phpMyAdmin, so the only think you earned is my hate for you!6 -
The one thing more annoying than my girlfriend is the chain of mail I get from Github saying,
"One of your dependencies has a security vulnerability."5 -
jQuery < 3.4.0 is a known moderate severity vulnerability now and Github just send me about 20 alert mails for repos which are using jQuery that I had used for side projects.
Like thanks but damn.2 -
FUUCCKKKK!! I need to hit smth. Or rant..
So that flaky ec2 issue.. These ec2s act as a shared environment for multiple apps. Our app is one of them. I have no access to those ec2s at all.
What I have access to is my app and some monitoring. Now the app randomly starts lagging while nearly idling. At the same random times monitoring stops completely and doesn't come back up. This happens to random app instances at random times.
Reached out to infra support, managed to get attention from the big boys [mgmt]. Today we got the fix deployed. I test it out -- problem persists.
I find this behaviour somewhat familiar. Managed to get some server stats from infra folks. Apparently cpu% is high as well as load avg [cpu queue]. Bingo! I know how to fix it!
So I write a long comment w/ all the commands and all the 'if that, do this'. Send it to one of the infra technitians
and I get a reply: 'we will apply cpu usage limitations to fix the issue'
wait... Cpu% limitations will do nothing but highlight the underlying problem...
'no, instances have high cpu utilisation which is causing those lags. We will limit cpu resources and it will be fixed'
oh ffs... Cpu utilization and cpu queue are VERY different things.. I tried explaining that to them like 7-9 times. And all I get is:
'yes, cpu utilization is the problem. We will limit it and solve the problem'
I would surely escalate all of this through higher channels if only I could get my hands on those ec2s and have a proof. But that is not happening and I'm forced to sit back and watch them break things even worse until they are out of options and mark my query as 'wont fix'....
Fuck that's frustrating....
*thinking to myself* so I've read about that new vulnerability 2 days ago that allows one to escape from docker container to the host... What if <...>4 -
The feel when you remember you have left any vulnerability in your code.
a wired wave arise in your body.1 -
I've been interested in security for years but despite knowing the theory I've always had this disconnect with actually doing it, about two years ago I finally managed to find and exploit my first cross-site scripting vulnerability in my companies Product whilst doing some routine acceptance testing. It was a penny drop moment for me which has led to some very interesting projects and It was pretty badass.
-
I just found a vulnerability in my companies software.
Anyone who can edit a specific config file could implant some SQL there, which would later be executed by another (unknowing) user from within the software.
The software in question is B2B and has a server-client model, but with the client directly connecting to the database for most operations - but what you can do should be regulated by the software. With this cute little exploit I managed to drop a table from my test environment - or worse: I could manipulate data, so when you realize it it's too late to simply restore a DB backup because there might have been small changes for who knows how long. If someone was to use this maliciously the damages could be easily several million Euros for some of our customers (think about a few hundred thousand orders per day being deleted/changed).
It could also potentially be used for data exfiltration by changing protection flags, though if we're talking industry espionage they would probably find other ways and exploit the OS or DB directly, given that this attack requires specific knowledge of the software. Also we don't promise to safely store your crabby patty recipe (or other super secret secrets).
The good thing is that an attack would only possible for someone with both write access to that file and insider knowledge (though that can be gained by user of the software fairly easily with some knowledge of SQL).
Well, so much for logging off early on Friday.5 -
First of all, a great channel to follow and where all this is from: https://youtube.com/watch/...
It listed a lot of open source news I missed myself and I'm sure others did too, for those that are too lazy to watch the video or open the description, I've stripped away the links and "X version got released" just to give an idea of what he covers.
------------------
GNOME and KDE announced they would work together on building better Linux desktops at Linux App Summit.
XRDesktop, a VR enabled Linux desktop, will allow you to use your Linux programs while wearing your VR headset.
Responding to the european commission's fines, Google announced that it would allow other search engines to be present at Android's setup.
Manjaro will allow users to pick between FreeOffice, Libre Office, or no office suite at all.
The Igalia team announced that they are working to make Pitivi compatible with Final Cut Pro X
Microsoft might be bringing its Teams software to Linux.
Martin Wimpress from the Canonical SnapCraft team gave an interview to TechRepublic, on Snaps
A discussion took place on how to improve Linux desktop performance in low ram scenarios.
A KDE vulnerability has been outed publicly before notifying the developers.
Nvidia has open sourced a bunch of documentation for its GPUs
Linux Journal announced they would cease their publication.
Kdenlive 19.08 has been released, bringing 3 point editing and a bunch of keyboard shortcuts
The Linux on Dex project now allows to run Ubuntu 16.04 LTS on a samsung smartphone.
According to protondb, we passed the 6000 playable games mark, out of 9 thousand for which users have created a report
GNOME Feeds has been released on flathub, a simple app to read RSS feeds on GNOME
The enlightenment desktop released its first version in 2 years, enlightenment 0.23.0.
Linux celebrated its 28th birthday
Microsoft announced that they would bring exFAT support to the linux kernel.
Thundebird 68 was released with an interface redesign
Collabora has published an update on their work on viglrenderer, a solution to emulate a gpu while using a virtual machine through Qemu.7 -
My new colegue at work was tasked with getting familiar with some Java code that had security vulnerability. He complained about slow build time for the first hour and then I stopped paying attention. At the end of day I checked on him and was like wtf how are you still trying to build this.
Turns out he ran Gradle task bootRun and watched logs of working app for 8 hours because he thought that's build xD -
security fiasco due to a malicious npm package:
Because of a bitcoin miner present in event-stream npm module (https://bleepingcomputer.com/news/...), my entire team and I had to scan all our nodejs apps, repos and the most excruciating one, all node_modules folders across all our dev machines and servers, to see if event-stream and flatmap-stream is present, then not just delete it but update a bu**load of upstream dependencies which internally used event-stream. All due to one malicious package which was hidden several layers beneath.
And, this happened almost 8 months after the aforesaid vulnerability was first found.9 -
Attention guys and gals! If you are using grafana in your home setup, update it asap to 4.6.4 or 5.2.3. versions before those two are affected by an authentication bypass vulnerability. CVE 2018-15727
In the meanwhile, my nginx config is blocking everything but the LAN ips :) -
I'm a fullstack engineer, this period there is literally nothing to do, we are a 1000+ employees company.
I got so bored I toke over the database of our production server two times in a week, exploiting dumb vulnerabilities I discovered out of boredom, of course I reported everything.
The funny thing is that they just don't care, no one took action or is willing to fix it and they actually insulted me because I set a query in sleep for 8 minutes exploiting one of the vulnerabilities.
I work for a great company that hosts (in this very server) most italian citizens informations C: free to take for everyone c:5 -
Old unused military satellite to make international calls free. Local tv station to leak episodes. 4500 hosts zombie net with autoreplicant bots that scans for vulnerability to populate the net to do distributed denial of service attacks. Jumper on the neighborhood cabin to redirect the school's call for being absent, an older friend pretended to be my father.
-
So theoretically all it takes are 12 libes of Python for arbitrary Code Execution on a Windows system.
'Theoretically', because it loads Kernel Drivers, which any half decent antivirus can detect and block.
http://feedproxy.google.com/~r/...
https://github.com/zerosum0x0/...1 -
our website got hacked somebody downloaded the whole source code and sent an email to us.
seems like that person would demand ransom or anything.
We still can't find where is the door ( vulnerability ) through which he pulled all files.17 -
Not a good year for Intel, is it? First the two Spectre variants and Meltdown, now the AMT vulnerability.
/Hugs his AMD systems while unplugging the Intel ones.7 -
So recently a 0-day exploit was discovered in WP plugin Kaswara Modern WP Bakery Page (https://zdnet.com/article/...).
A customer's shared hosting space was taken down (about 6 websites) after this vulnerability had been exploited and although we removed the malicious code, & changed credentials the hosting company demands we update ALL Wordpress plugins to latest AND provide them a virus scan report of our local PC before putting the webspace back online??? WTF???
That just strikes me as outrageous. Thoughts? 10
10 -
Everybody when a forced update is released: "I hate forced updates!! They can't force me to do shit!!"
Everybody when a massive ransomware attack happens: "You should've updated when the update came out, so you aren't vulnerable!"
If they made the fix for the WannaCry vulnerability forced, the attack wouldn't have been as big as it was.
Confession: I wish they made more forced updates :/
Also, I'll probably get a lot of hate about this...3 -
Dependency hell is the largest problem in Linux.
On Windows, I just download an executeable (.exe) file, and it just works like a charm! But Linux sometimes needs me to install dependencies.
At one point, I nearly broke my operating system while trying to solve dependencies. I noticed that some existing applications refused to start due to some GLIBC error gore. I thought to myself "that thing ain't gonna boot the next time", so I had to restore the /usr/lib/x86_64-linux-gnu/ folder from a backup.
And then there is a new level of lunacy called "conflicting dependencies". I never had such an error on Windows. But when I wanted to try out both vsftpd and proFTPd on Linux, I get this error, whereas on Windows, I simply download an .exe file and it WORKS! Even on Android OS, I simply install an APK file of Amaze File Manager or Primitive FTPd or both and it WORKS! Both in under a minute. But on Linux, I get this crap. Sure, Linux has many benefits, but if one can't simply install a program without encountering cryptic errors that take half a day to troubleshoot and could cause new whack-a-mole-style errors, Linux's poor market share is no surprise.
Someone asked "Why not create portable applications" on Unix/Linux StackExchange. Portable applications can not just be copied on flash drives and to other computers, but allow easily installing multiple versions on a system. A web developer might do so to test compatibility with older browsers. Here is an answer to that question:
> The major argument [for shared libraries] is security, that if there is a vulnerability in a commonly-used library, then only that library has to be updated […] you don't have to have 4 different versions of a library installed
I just want my software to work! Period. I don't mind having multiple versions of libraries, I simply want it to WORK! To hell with "good reasons" for why it doesn't, and then being surprised why Linux has a poor market share. Want to boost Linux market share? SOLVE THIS DAMN ISSUE!.
Understand that the average computer user wants stuff to work out of the box, like it does in Windows.52 -
Apple’s Vision Pro Hacked On Launch Day
Just within hours of Apple releasing its much-hyped mixed reality headset, Apple Vision Pro, a security researcher was able to discover a critical kernel vulnerability in the device’s software – visionOS, which, if exploited, could potentially enable jailbreaks and malware attacks. More detail:
https://aprogrammerlife.com/top-rat... 6
6 -
Just mirrored sudo to my own Gitea instance yesterday (https://git.ghnou.su/mir/sudo). Turns out that this chonkster is 200MB compressed (LZ4 on ZFS). I am baffled by it... All it needs to do is reading a configuration file describing what users can be elevated, to which user and which commands they can run. Perhaps doas wasn't a bad idea after all?
Oh and it got a privilege escalation vulnerability just yesterday (https://security-tracker.debian.org/...), which is why I got interested in it. Update your sudo packages if you haven't already.11 -
Don't need Netflix when you have a production deployment right before a long weekend. It has failed since last two weeks due to vulnerabilities present in one of libraries(P.S. FUCK JAVASCRIPT and Post release vulnerability scans!). You have rewritten the whole functionality from scratch twice! Security gates finally open for you, welcoming with arms wide open. So you click Deploy! DAFUQ!! FUCK MY LIFE! Deployment failed! It's only a 3 hour window to deploy! You frantically re-review your code, is it me?? Not again!! It isn't! Well, why is the deployment failing, you work against the clock. Going through configs, code, documentation! WTF is it?? Should I give up and raise a support ticket? Nope! You login to the server, sifting through logs and configs, there's a couple of other tickets with today's deadline. What are you going to do? And you get a hint! You take the hunch, change the config 5 minutes before deadline!
Get merge request approved, wait for the build, hit DEPLOY!! Nail biting 3 minutes! Your eyes fixed on the logs! Building..... Pushing instances..... Starting App..... SUCCESS!!! Finish the remaining tickets! Your long weekend still exists!3 -
I found a vulnerability in an online compiler.
So, I heard that people have been exploiting online compilers, and decided to try and do it (but for white-hat reasons) so I used the system() function, which made it a lot harder so i decided to execute bash with execl(). I tried doing that but I kept getting denied. That is until I realized that I could try using malloc(256) and fork() in an infinite loop while running multiple tabs of it. It worked. The compiler kept on crashing. After a while I decided that I should probably report the vulnerabilites.
There was no one to report them to. I looked through the whole website but couldn't find any info about the people who made it. I searched on github. No results. Well fuck.6 -
Me currently in my 3rd year of university: hears about blockchain from my friends, reads 5 pages of ethereum white paper; sees a cool machine learning project, watches 2 weeks of Andrew Ng's course; plays a cool game, downloads Unity and makes a hello world game; hears about wifi vulnerability, purchases an ethical hacking course.
Number of things mastered: 05 -
just found out a vulnerability in the website of the 3rd best high school in my country.
TL;DR: they had burried in some folders a c99 shell.
i am a begginer html/sql/php guy and really was looking into learning a bit here and there about them because i really like problem solving and found out ctfs mainly focus on this part of programming. i am a c++ programmer which does school contest like programming problems and i really enjoy them.
now back on topic.
with this urge to learn more web programming i said to myself what other method to learn better than real life sites! so i did just that. i first checked my school site. right click. inspect element. it seemed the site was made with wordpress. after looking more into the html code for the site i concluded all the images and files i could see on the site were from a folder on the server named 'wp-content/uploads'. i checked the folder. and here it got interesting. i did a get request on the site. saw the details. then i checked the site. bingo! there are 3 folders named '2017', '2018', '2019'. i said to myself: 'i am god.'
i could literally see all the announcements they have made from 2017-2019. and they were organised by month!!! my curiosity to see everything got me to the final destination.
with this adrenaline i thought about another site. in my city i have the 3rd most acclaimed high school in the country. what about checking their security?
so i typed the web address. looked around. again, right click, inspect element and looked around the source code. this time i was more lucky. this site is handmade!!! i was soooo happy because with my school's site i was restricted with what they have made with wordpress and i don't have much experience with it.
amd so i began looking what request the site made for the logos and other links. it seemed all the other links on the site were with this format: www.site.com/index.php?home. and i was very confused and still am. is this referencing some part of the site in the index.php file? is the whole site written inside the index.php file and with the question mark you just get to a part of the site? i don't really get it.
so nothing interesting inside the networking tab, just some stylesheets for the site's design i guess. i switched to the debugger tab and holy moly!! yes, it had that tree structure. very familiar. just like a project inside codeblocks or something familiar with it. and then it clicked me. there was the index.php file! and there was another folder from which i've seen nothing from the network tab. i finally got a lead!! i returned in the network tab, did a request to see the spgm folder and boooom a site appeared and i saw some files and folders from 2016. there was a spgm.js file and a spgm.php file. there was a contrib, flavors, gal and lang folders. then it once again clicked me! the lang folder was las updated this year in february. so i checked the folder and there were some files named lang with the extension named after their language and these files were last updated in 2016 so i left them alone. but there was this little snitch, this little 650K file named after the name of the school's site with the extension '.php' aaaaand it was last modified this year!!!! i was so excited! i thought i found a secret and different design of the site or something completely else! i clicked it and at first i was scared there was this black/red theme going on my screen and something was a little odd. there were no school announcements or event, nononoooo. this was still a tree structured view. at the top of the site it's written '!c99Shell v. 1.0...'
this was a big nono. i saw i could acces all kinds of folders. then i switched to the normal school website and tried to access a folder i have seen named userfiles and got a 403 forbidden error. wopsie. i then switched to the c99 shell website and tried to access the userfiles folder and my boy showed all of its contents. it was nakeeed naked. like very naked. and in the userfiles folder there were all, but i mean ALL files and folders they have on the server. there were a file with the salary of each job available in the school. some announcements. there was a list with all the students which failed classes. there were folders for contests they held. it was an absolute mess and i couldn't believe it.
i stopped and looked at the monitor. what have i done? just to learn some web programming i just leaked the server of the 3rd most famous high school in my country. image a black hat which would have seriously caused more damage. currently i am writing an email to the school to updrage their security because it is reaaaaly bad.
and the journy didn't end here. i 'hacked' the site 2 days ago and just now i thought about writing an email to the school. after i found i could access the WHOLE server i searched for the real attacker so if you want to knkw how this one went let me know in the comments.
sorry for the long post, but couldn't held it anymore13 -
The first time i've scripted something and found a vulnerability on a production web application was one of the best moment i've ever had, never been so excited!
(mmh, maybe i need to switch to security :D) -
- I do threat intel.
- Oh yeah? Name 4 critical vulnerabilities.
- Fortinet.
- That's on me, I set the bar too low. 1
1 -
I dont understand the Log4j vulnerability.
Isnt the ability to execute code a feature they added so that you can add dynamic data to the logs?
If it is a feature then isnt it written in the documentation?
Is the problem that a lot of companies forgot to sanitize the input before logging it?23 -
CVE-2019-3568
Description: A buffer overflow vulnerability in WhatsApp VOIP stack allowed remote code execution via specially crafted series of SRTCP packets sent to a target phone number.
NSO group even sell a spyware application based on that vulnerability to governments.
Listen!!!!! I'm going to the toilet with my phone!!! Listen!!!1 -
I once had a manager who demanded I physically print all of the Kanban cards and tape them to the office whiteboard. I was told to move the cards across the board after they were moved in TFS. I still had to keep up with my other duties in the QA department too!
Despite that, I still stayed on board with the company (the pay was good, and the work was simple.) As a QA teeter, I uncovered a rather nasty security vulnerability that would have put all of our customers data at reach to anybody. I advised my manager, and was told - just ignore it and ship the code please. I refused.
I was threatened with being fired, verbally assaulted, and challenged at the most trivial ways in everything I did after that.
Jokes on him now. I work from home in my dream job, doing what I love, with a manager who actually gives a rats ass about my concerns.
Moral of the story here - you don't have to agree with your subordinates , but you do need to validate their concerns.4 -
Our ISP, that also offers us Television is smart, very smart... “One option is to provide an anonymous mailbox (eg. Gmail, Hotmail”
Wtf... Gmail != anonymous.
I was about to report a vulnerability I found in their system, with that I could access the whole digibox, recover recordings, copy the on demand things, and watch films. 1
1 -
Hey fellow devRanters,
I'm sure some of you have read about the newest vulnerabilities in Intels Management Engine (ME). I feel like ME and similar "features" are unacceptable backdoors into our systems. Unfortunately Intel and AMD do not offer their customers the option to acquire CPUs that lack these backdoors and make disabling them rather impossible 😒
Thus my question: Do you guys know of any 64-bit "open-source" CPU on the market that is production-ready and suitable for high-traffic web applications? Please note that I don't consider FPGAs to be viable options, since I don't trust Xilinx and Altera either.15 -
Y'all might wanna update your Win7, Win8 amd Win Server 2008.
RDP RCE with a CVSS pf 9.8.
https://blogs.technet.microsoft.com/...2 -
Why does the point of sale machine open the cash drawer for a credit card sale ? Seems like a vulnerability to me.2
-
I reached out to a developer who's site was being contracted out to Amazon devs, because when their site launched it had a couple of security issues. This was his response:
"An additional thought/opinion... Just because a college freshman from Arizona wasn't too hungover to make the effort to notify us and take the liberty of classifying this as a security issue for us doesn't mean we need to take their word for it."5 -
Windows 10 is safe they said. Signature/https can be trusted they said.
When even NSA disclose "hacks" you know it's too big
https://wired.com/story/...4 -
Trustico CEO emailed private key which is used to sign TLS certificates, making more than 23k certificates compromised!
This makes me think, that we should not trust others for our security (like ca), failure of CA can put our website at risk. What is the better way to do it?
https://arstechnica.com/information...11 -
If you discovered a vulnerability affecting multiple of the big dogs, would file a cve and report it immediately or have some *fun* first?
-
Challenge questions are so goddamn stupid.
Apparently I have an account with a certain online organization though I don't remember setting it up.
So naturally I had no idea of my username or password, so they asked me challenge questions.
It asked me the city of my birth, which is a place with a weird spelling. Because of that weird spelling, I never remember if I'm spelling it right (I was only there as a newborn infant) And I'm also supposed to remember if I capitalized it or not.
I hate challenge questions. And anyone doing any remotely simple research on me shouldn't have trouble learning what city I was born in so it seems to me it's a security vulnerability, nothing more.
And maybe I'm giving things away by saying it asks me that question, but it's a common security question any hacker would anticipate anyways.2 -
I just remembered that 2 years ago I found an open-redirect vulnerability in one of Google's old pages.
I decided to not submit it to Google because it's too much effort (even though I knew they pay for these things) and told about it to a friend who deals with these things.
I was SO. DAMN. STUPID.1 -
Today I found a vulnerability in an local agency website. It's one of the famous and biggest that if I would applied they wouldn't even look at my cv. Long story short, I managed to login to their admin dashboard and sent a screenshot of it as a twitter mention to them. All they did was to like the tweet while I had the chance to fuck up the website.5
-
This was initially a reply to a rant about politics ruining the industry. Most of it is subjective, but this is how I see the situation.
It's not gonna ruin the industry. It's gonna corrupt it completely and fatally, and it will continue developing as a toxic sticky goo of selfishness and a mandatory lack of security until it chokes itself.
Because if something can get corrupted, it will get corrupted. The only way for us as a species to make IT into a worthy industry is to screw it up countless times over the course of a hundred years until it's as stable and reliable as it can possibly be and there are as many paradigms and individually reasonable standards as there can possibly be.
Look around, see the ridiculus amount of stupid javascript frameworks, most of which is just shitcode upon vulnerabilities upon untested dependencies. Does this look to you like an uncorrupted industry?
The entire tech is rotting from the hundreds of thousands of lines of proprietary firmware and drivers through the overgrown startup scene to fucking Node.js, and how technologies created just a few decades ago are unacceptable from a security standpoint. Check your drivers and firmware if you can, I bet you can't even see the build dates of most firmware you run. You can't even know if it was built after any vulnerability regarding that specific microcontroller or whatever.
Would something like this work in chemical engineering? Hell no! This is how fucking garage meth labs work, not factories or research labs. You don't fucking sell people things without mandatory independent testing. That's how a proper industry works. Not today's IT.
Of course it's gonna go down in flames. Greed had corrupted the industry, and there's nothing to be done about it now but working as much as we can, because the faster we move the sooner we'll get stuck and the sooner we can start over on a more reasonable foundation.
Or rely on layers of abstraction and expect our code to be compilable on anything the future holds for us.2 -
Microsoft C/C++ code keeps on giving:
https://msrc.microsoft.com/update-g...
Too sad, that Microsoft is too poor to afford good devs. As a lot of devs here are sure, that good devs surely can code safe and secure in C/C++, Microsoft probably just lacks the resources to get such devs to work for them.13 -
Another day, another critical vulnerability due to an out of bounds write that could never have occurred in Rust
https://github.com/openssl/openssl/...26 -
WordPress File Delete to Code Execution
The vulnerability was reported 7 months ago to the WordPress security team but still remains unpatched.
https://blog.ripstech.com/2018/...1 -
WTF kind of bullshit software is sonar.
I can't deploy my application because sonar is telling me that there is a vulnerability. So I look at it. IT'S A FUCKING DEV DEPENDENCY. Are you fucking serious sonar? I can't deploy because a dev dependency has a vulnerability that allows DOS attacks. What the fuck do you think will happen?! I'm going to DOS my own fucking application whilst coding or what? Who the fuck would even care?!
I fucking hate our Pipeline, all the tools behind it operate like shit. the only thing positive about it, is that I am able to deploy applications myself without having to call someone and wait a week. Because putting a file in a directory is hard ._.3 -
So I promised a post after work last night, discussing the new factorization technique.
As before, I use a method called decon() that takes any number, like 697 for example, and first breaks it down into the respective digits and magnitudes.
697 becomes -> 600, 90, and 7.
It then factors *those* to give a decomposition matrix that looks something like the following when printed out:
offset: 3, exp: [[Decimal('2'), Decimal('3')], [Decimal('3'), Decimal('1')], [Decimal('5'), Decimal('2')]]
offset: 2, exp: [[Decimal('2'), Decimal('1')], [Decimal('3'), Decimal('2')], [Decimal('5'), Decimal('1')]]
offset: 1, exp: [[Decimal('7'), Decimal('1')]]
Each entry is a pair of numbers representing a prime base and an exponent.
Now the idea was that, in theory, at each magnitude of a product, we could actually search through the *range* of the product of these exponents.
So for offset three (600) here, we're looking at
2^3 * 3 ^ 1 * 5 ^ 2.
But actually we're searching
2^3 * 3 ^ 1 * 5 ^ 2.
2^3 * 3 ^ 1 * 5 ^ 1
2^3 * 3 ^ 1 * 5 ^ 0
2^3 * 3 ^ 0 * 5 ^ 2.
2^3 * 3 ^ 1 * 5 ^ 1
etc..
On the basis that whatever it generates may be the digits of another magnitude in one of our target product's factors.
And the first optimization or filter we can apply is to notice that assuming our factors pq=n,
and where p <= q, it will always be more efficient to search for the digits of p (because its under n^0.5 or the square root), than the larger factor q.
So by implication we can filter out any product of this exponent search that is greater than the square root of n.
Writing this code was a bit of a headache because I had to deal with potentially very large lists of bases and exponents, so I couldn't just use loops within loops.
Instead I resorted to writing a three state state machine that 'counted down' across these exponents, and it just works.
And now, in practice this doesn't immediately give us anything useful. And I had hoped this would at least give us *upperbounds* to start our search from, for any particular digit of a product's factors at a given magnitude. So the 12 digit (or pick a magnitude out of a hat) of an example product might give us an upperbound on the 2's exponent for that same digit in our lowest factor q of n.
It didn't work out that way. Sometimes there would be 'inversions', where the exponent of a factor on a magnitude of n, would be *lower* than the exponent of that factor on the same digit of q.
But when I started tearing into examples and generating test data I started to see certain patterns emerge, and immediately I found a way to not just pin down these inversions, but get *tight* bounds on the 2's exponents in the corresponding digit for our product's factor itself. It was like the complications I initially saw actually became a means to *tighten* the bounds.
For example, for one particular semiprime n=pq, this was some of the data:
n - offset: 6, exp: [[Decimal('2'), Decimal('5')], [Decimal('5'), Decimal('5')]]
q - offset: 6, exp: [[Decimal('2'), Decimal('6')], [Decimal('3'), Decimal('1')], [Decimal('5'), Decimal('5')]]
It's almost like the base 3 exponent in [n:7] gives away the presence of 3^1 in [q:6], even
though theres no subsequent presence of 3^n in [n:6] itself.
And I found this rule held each time I tested it.
Other rules, not so much, and other rules still would fail in the presence of yet other rules, almost like a giant switchboard.
I immediately realized the implications: rules had precedence, acted predictable when in isolated instances, and changed in specific instances in combination with other rules.
This was ripe for a decision tree generated through random search.
Another product n=pq, with mroe data
q(4)
offset: 4, exp: [[Decimal('2'), Decimal('4')], [Decimal('5'), Decimal('3')]]
n(4)
offset: 4, exp: [[Decimal('2'), Decimal('3')], [Decimal('3'), Decimal('2')], [Decimal('5'), Decimal('3')]]
Suggesting that a nontrivial base 3 exponent (**2 rather than **1) suggests the exponent on the 2 in the relevant
digit of [n], is one less than the same base 2 digital exponent at the same digit on [q]
And so it was clear from the get go that this approach held promise.
From there I discovered a bunch more rules and made some observations.
The bulk of the patterns, regardless of how large the product grows, should be present in the smaller bases (some bound of primes, say the first dozen), because the bulk of exponents for the factorization of any magnitude of a number, overwhelming lean heavily in the lower prime bases.
It was if the entire vulnerability was hiding in plain sight for four+ years, and we'd been approaching factorization all wrong from the beginning, by trying to factor a number, and all its digits at all its magnitudes, all at once, when like addition or multiplication, factorization could be done piecemeal if we knew the patterns to look for.7 -
ok, but this is cool. it’s an image that renders differently on apple and non-apple devices. not sure if devRant will process it so it doesn’t work, but this is cool. also a huge vulnerability for apple, but cool.
 9
9 -
Gaining root in Macs by not using a password, a vulnerability in HomeKit devices allowing unauthorized remote access.
https://9to5mac.com/2017/12/...
Next you tell me FaceID isn't as secure as you want me to believe.
Oh, wait...1 -
A while ago I was asking wtf is this new trend with using 0.0.0.0 as a target address for connect()'ing TO.
Turns out, I was asking the right questions. This nonsense will soon be blocked in browsers, as it's a dumb security issue.
ref.: https://oligo.security/blog/...3 -
Well for starters the website that gave you assignments on security of web applications shouldn't have an SQL injection vulnerability on the login page.
Next would be the method of teaching, they would skip what not to do and go straight to what you should do. This in turn causes people to use the exec command in php that actually takes a POST parameter.
And stop allowing teachers to be lazy fucks that don't explain shit and only give you assignments.
And finally when telling the teacher that a method he uses would cause another vulnerability the teacher should properly fix this issue not say it is for an "advanced course".
Yes I am pissed -
If only NPM' security team (so pretty much NSP's) would inform the package owners as soon as they discover vulnerabilities and give them the standard 30-90 days to fix them and release a new version before going public, instead of straight out publishing the security audits which generates noise on the terminal (obviously when using npm) and on Github
-
I've always considered myself a stalwart proponent of strong, effective security. But I'll be damned if my company's security policy isn't choking it's developers out.
It's like whenever a developer requirement and potential security vulnerability meet, the company doubles down on the security side, ignores their dev's needs entirely, and then takes a privilege away just to punish us for having the audacity to try and do our God damn jobs.6 -
So this is kinda hard to talk about but.. I finally got to a point in my career where I don't have a boss, work remote, make my own schedule etc.. problem is .. I am very low on productivity I feel like I'm working maybe 1/10th of my capacity and although Yea this may sound dream-like .. it gets old and I'm realizing that I used to excel at my last job for my boss.. I wanted to please him in every way for validation and acceptance..
Yea that's dysfunctional as fuck .. so basically how the hell do i use my own mind to drive my excellence? I'm so lost and don't really know how to find the motivation that people pleasing once brought me..
For some context as well, I have also done a lot of psychedelics over the past couple years and it has basically destroyed my ego .. "but that's a good thing" you say?
Well yes and no, I used to rely on my ego to drive me on my own in lieu of wanting acceptance and validation from my boss. So that was a bit unexpected, getting rid of my ego got rid of my dysfunctional drives to prove myself to others and seek acceptance..
Gahh I'm ranting :'D
TL;DR: how do you motivate yourself if you've traditionally found motivation through pleasing others???4 -
When the pen testers find a "vulnerability" and say it would be very difficult for someone to exploit it. Yeah, in that case they might as well say if you solve p vs np you can break it but it would be very difficult.
-
For one of my exams, from a couple of meager code snippets and hints, without any prior domain knowledge, we had to find and carefully describe a vulnerability, as well as suggest a fix.
Well, I wouldn't complain, but what the actual fuck, it turns out that we had to come up with and "carefully describe" this whole shit: https://googleprojectzero.blogspot.co.uk/...
No, we did not study it in class, nor have seen it before in the recommended reading or provided links. Also, according to the point distribution, we only had 20 minutes for this part.
I don't usually complain about stuff and take it my lack of preparation or something, but fuck all now. I never want to look at another security-related piece of code ever again. -
Target #1 - Aim to further develop my university security project (A python based vulnerability scanner), and move this over to GitHub.
Target #2 - Aim for reaching ten contributions on open source projects and start building up my developer profile pre-graduation in September! -
So I discovered a Microsoft Exchange vulnerability due to settings at company well doing a project. Would you classify it resume worthy for a software developer?
-
Since I started my routine of checking bug logs every morning, I've had 2 instances where a website vulnerability scanner was run against a production website and generated over 2,000 Coldfusion errors.
At the time, I was super nervous about the apparent hack attempt, and hyped that the attackers never actually got in. It's nice to know that despite the various errors indicating vulnerable / breakable code, they were ultimately unsuccessful. I know now that a determined attacker could probably have wrecked our production websites. Since then I've made a ton of security-related updates and I'm actually thankful for the script kiddie getting my attention with that scan.
PS. We're now building a website for a local security company who is going to work with us to pen test the site when it's finished! Gulp.4 -
USB ports are such a vulnerability.
Using a device as cheap as a Teensy you can easily execute whatever malicious software you'd like on a person's computer.3 -
How to discover and exploit vulnerabiliy in program or IoT firmware?C++, asm, writing zero-days, i have always been amazed by that. Art.
-
The company I work in recently made a subdomain where you need to figure out how to hack the page using a vulnerability they subtly put there. If u are successful u get an interview. I looked it over for fun and was able to do it. But since i already work there i was thinking of telling a friend id love to join us but was rejected a month ago when they interviewed him about how i did it so he can apply maybe they give him another chance. do you think I should do that?
Note that i referred him last month and hes a fresh grad with not much experience3 -
my old game had this flow every time a client places an object:
Client A creates a new generic object, and attaches texture paths (yep, global paths are allowed), and... lua code as strings to it.
Client A sends the entire object list to the server
Server receives it, replaces it's own object list
Server copies the entire object list and sends it to all clients
Client A and Client B both receive the object list and replace their versions.
All clients see that the object contains some code as strings
They compile and store it, and then run every frame. UNSANDBOXED.
any client could make all other ones execute any code and i was proud of my idea! -
NVD NIST cve CVSS v4 no rating, v3 rating critical vulnerability
description text low severity, no mitigation solution
what the fuck is this , is it critical or not and what the fuck should i do to solve it, what the fuck4 -
Hi!
I want to know if there is possibility to find a vulnerability on a .jar file.
I tried to install Kali on VM (for now) and tried to use metasploit but I found that it attacks the inter system on a indicated ip address.
There are many application or video (and so on) for my problem?
This .jar file is an application and I want to do pentesting...
Sorry for my poor english but it isn't my native language.
I'm new in pentesting wolrd 🤣7 -
Hey ... Is it possible to figure out the clients path (f.e. C:\Users\...) to a file he uploaded to a website on the server side?
My boss thinks it could be done and wants me to programm it. But I think we'd need a zero day vulnerability in a specific (and probably very old) browser to do something like that... That would be a huge security issue...
Wouldn't it?
What do you think?13 -
Finally I finished the exams, now I have to write my thesis. An agency who wants remain anonymous at the moment told my supervisor to choose a student who will works out on the ransomware argument. The relator was a little bit scared about consequences but I'm pressing to write a controlled ransomware in a closed network brtween virtual machines. What qualities a good ransomware should has?
Mutable structure to avoid antivirus detection? Good exploits and vulnerability scanners to make itself viral? The payload should stay in the code or should be downloaded from a server? I need some reference on analysis of vx codes, any help? -
!rant
iOS 11 have a vulnerability allowing attacker to bypass your lock screen and brick your phone via prepared “dev profile”. Do not download any utrusted stuff untill official fix ;)7 -
I attempted on national competition in an IT field, where there were tens of great projects (in other fields as well, like chemistry and so..). We had to push everything to their portal, so they can study it in advance. While pushing the docs, I found that there were SQL injections that allowed me to list everyone's rating and to download every single doc / additional sources.
Worst part is, that even after I reported vulnerability, they obviously didn't had time to fix it. -
PHP is so insecure and vulnerable that it makes me feel unsafe. It has so many features and settings that can lead to security risks, such as register_globals, magic_quotes, and allow_url_fopen. It also has so many functions that can execute arbitrary code or commands, such as eval, exec, and system.
It is like PHP was designed by a bunch of hackers who wanted to exploit every possible loophole.8 -
I recently recommended that we fix a gap in the current CSRF implementation.
I’m asked by a fucking business guy that if we haven’t seen an issue till now, why is this a priority?
Should I demo the vulnerability? Why can’t they fucking trust the people that they hire? It’s not like I wanna do it for some selfish motive. -
Just discovered someone I told about a hack for the computers in school (nothing difficult just booting from a USB) had a link to C2K the company that provides the system and told them about it and now they've patched it up, so in a way, it's my first security vulnerability report, in another way, I can no longer play games and program in free
-
I signed up to a website, and my password contained & symbol, got an error that password cannot contain that symbol, I thought we are way beyond vulnerability of SQL injection?
Or that symbol can be used for some other attacks?5 -
Somebody forgot to correctly match the external url on login success and failure, now google may use my cookies for the better good.
https://symfony.com/blog/...
-
Two security researchers have published details about a vulnerability in the Windows Printing Service which impacts all Windows versions.
According to a Report of ZDNet : The vulnerability codenamed 'PrintDemon' which is located in Windows Print Spooler (Windows component responsible for managing print operations). The service sends data to be printed to a USB port for physically connected printers. In a report published, security researchers Alex Ionescu & Yarden Shafir said they found a bug in this old component that can be abused to hijack the Printer Spooler internal mechanism. The bug can not be used to break into a Windows client remotely over the internet, so it's not something that could be exploited to hack Windows systems over the internet.4 -
"We'll publish critical vulnerabilities in PGP/GPG and S/MIME email encryption on 2018-05-15 07:00 UTC. They might reveal the plaintext of encrypted emails, including encrypted emails sent in the past. #efail 1/4"
https://twitter.com/seecurity/...
Let's see how this unfolds. While there is chaos I trink some tea and laugh, because I never send critical information over e-mail. 🧐🍵4 -
Which one comes first? vulnerability or threat? 🤔🤔 I would go with vulnerability how about you guys?5
-
Tried out the node.js code demo in this book.
🤦♂️
Terrible format, use tab for indentation, very very long function, redundant code (eg: new Buffer vulnerability)...
The major issue is none of the total.js nosql code works. Eg:
db.clear()
db.insert({...data})
Without any asynchronous call, how do you expect this to work?!
Just fixed the code and updated npm modules for demos in Chapter 3 btw... Took way longer than expected. 3
3 -
Me: Why do we do this this time consuming, low value thing?
My tech lead: Because if we don't, a box becomes red on some executive report.
Me: Why is this deadline so important? It's not customer facing or any kind of critical bug/vulnerability?
My tech lead: Because it was a company wide mandate, and we'll show up on some executive report if we're late.
Me: *angry dev noises*
They must dole out lashings to the tech leads and the directors any time we fail to meet some completely arbitrary demand. The act like the world is going to end any time we get too close to a deadline 🤦♂️
Makes no sense that they then turn around and worship the ground senior leadership walks on. I wonder if it's some weird form of stockholm syndrome.3 -
Great feeling when the pen testers couldn't find the "unfixable" vulnerability your new feature created, and you go on holiday soon.
-
👨💻 White hat
🤖❓️🤡❗️ Slack
😡😨😨😨
😨😨😨🙄 B2B clients
🤖🤡🤖🤡
🤡🤖🤡🤖
🤖🤡🤖🤡
🤡🤖🤡🤖 HackerOne
🤖 🤖 🤖
🤡🤡🤡🤡
🤡🤡 🤖 🤖
🤡🤡🤡 🤡
🤖 🤖
🤖 🤖
🤖🤖 🤖🤖 Zendesk1 -
Anyone use docker in production handling monies and hundreds accounts? In Django in my case but doesnt matter the framework. More concerned with security and stability moving from paas to docker based paas. Worried I'll move everything to docker and end up moving back to vms bc of some issues or some vulnerability.
-
I just read about the Thunderbolt port vulnerability but it seems that port is interchangeable with USB C, just faster? But basically any USBC ports are vulnerable then? Or just the rounded ones like on phones?
Normal USB 3 rectangular ports on PCs are fine?5 -
HIRE A CRYPTO RECOVERY EXPERT; CYBER CONSTABLE INTELLIGENCE YOUR ULTIMATE SOLUTION FOR LOST CRYPTOCURRENCY
I am truly at a loss for words as I try to express my deep gratitude to Cyber Constable Intelligence for the incredible support they provided me during one of the darkest times of my life. I never imagined I would find myself in a situation like this, but I am so thankful I reached out to them when I did. A while ago, I became desperate to access my spouse’s phone, as I had suspicions about his conversations with another woman. In my search for help, I made the terrible mistake of trusting a hacker who claimed they could assist me in gaining access. Little did I know, this hacker had ulterior motives and would take full advantage of my vulnerability. Instead of helping, the hacker scammed me, taking a significant amount of my Bitcoin, and even worse, he blackmailed me. He threatened to expose my personal information and demanded more money from my spouse. I felt completely trapped, unable to think clearly or find a way out. It seemed like I had lost everything my money, my peace of mind, and even my sense of security. That's when I found Cyber Constable Intelligence. After reading about their success stories, I decided to reach out, even though I was unsure what to expect. From the moment I contacted them, I felt a weight lift off my shoulders. They listened to my situation with empathy and immediately got to work, providing not just technical expertise, but the reassurance I desperately needed. Thanks to their diligent efforts, they were able to track down the hacker who had caused me so much distress. Not only did they help me recover all of my lost funds, but they also made sure the hacker was held accountable for his actions. In addition, they helped me gain access to my spouse’s phone, revealing the truth behind his communications with the other woman. I am incredibly grateful to Cyber Constable Intelligence for their dedication, and compassion. They went above and beyond to help me recover both my finances and my peace of mind. If you find yourself in a similar situation, I highly recommend reaching out to them. They truly saved me, and I will always be thankful for their intervention.
Here's Their info below
Website Info : www cyber constable intelligence com
Email Info: cyberconstable (@) coolsite net26 -
Devs and security researchers out there!!
I had a doubt regarding subdomain takeover vulnerability.
How to find where a site is hosted on heroku or AWS or heroku or more?
I was trying to write a script for it.
Any expertise will be welcomed.2 -
Is there a server-oriented Linux system that is more secure than Ubuntu Pro? With its 24-hour unattended vulnerability patches, I doubt anything free beats it. Btw it’s free for personal use3
-
RECOVER BACK YOUR HARD EARN MONEY SCAMMED BY ONLINE IMPERSONATORS OR HACKERS FROM ANY PLATFORM.
At TaxEase Solutions, based in New York, USA, we faced a critical crisis when our tax filing system was hacked overnight. The breach exposed sensitive personal data, including Social Security numbers, financial details, and addresses of our clients. The attackers used this stolen information to apply for fraudulent tax refunds, resulting in a significant loss of $1 million USD. The breach occurred during the night while our team was off-duty, leaving us unaware until the following morning when we discovered the extent of the damage. With such a large amount of money lost and the integrity of our business compromised, we knew we needed immediate assistance to recover and secure both our clients’ data and our reputation. That’s when we reached out to Digital Gold Hunter. Digital Gold Hunters team responded promptly and demonstrated their deep expertise in dealing with cybersecurity breaches. They quickly identified the source of the vulnerability and acted decisively to patch the system flaw. Their ability to rapidly assess the situation and implement corrective actions helped to prevent any further unauthorized access to our platform.Once the system was secured, Salvage Asset Recovery shifted their focus to assisting our affected clients. They worked diligently with financial institutions and law enforcement to help some clients who were able to reach out and report the fraudulent tax refund applications. Through their intervention, these clients were able to stop the fraudulent transactions and recover some of their funds. As of now, Digital Gold Hunter has managed to recover $980,000 of the lost $1 million, but they are still continuing to work with authorities and financial institutions to recover the remaining funds. Digital Gold Hunter helped us implement more robust security measures to prevent any future breaches. They introduced advanced encryption techniques and worked with us to update our cybersecurity protocols, ensuring that our clients' data would be better protected going forward. Their consultation also guided us in strengthening our internal data protection policies, which reassured our clients that we were committed to safeguarding their sensitive information.Thanks to the quick and efficient actions of Digital Gold Hunter, and protect the majority of our clients’ data. Their professionalism, expertise, and dedication to helping both our company and our clients made all the difference in mitigating the effects of the breach and stabilizing our business. The recovery process is still ongoing, but we remain confident that with Digital Gold Hunter ’s continued support, we will fully resolve the situation.
Their Contact info,
Email: D i g i t a l g o l d h u n t e r @ t e c h -c e n t e r . c o m1 -
**HOW TO RECOVER YOUR MONEY FROM FAKE CRYPTO INVESTMENT SCAMMERS → CONTACT HACKATHON TECH SOLUTION**
It all began innocently enough, with the allure of quick gains and financial freedom beckoning me into the world of cryptocurrency investments. Little did I know, this journey would lead me down a path of deceit and betrayal. On the first of last month, I took the plunge and invested $3000 in USDT, hoping to see my money grow. To my delight, by the 15th of the month, I received a withdrawal of $10,000, fueling my excitement and confidence in the investment platform. With newfound optimism, I decided to up the ante, investing $50,000 with the expectation of reaping even greater returns. However, as the withdrawal deadline approached, reality came crashing down around me. It became painfully clear that I had been duped, lured in by promises of riches that were nothing but empty lies. My hard-earned money was gone, vanished into the digital abyss, and I was left reeling from the betrayal. Determined to reclaim what was rightfully mine, I embarked on a journey of seeking recovery experts who could help me navigate the treacherous waters of online fraud. Yet, at every turn, I encountered charlatans and impostors, preying on the vulnerability of those who had been deceived. It was in my darkest hour that I stumbled upon a glimmer of hope – a review praising the commendable work of HACKATHON TECH SOLUTION, a team of ethical hackers dedicated to righting the wrongs of cybercrime. With nothing left to lose, I placed my trust in their capable hands, praying for a miracle. And miraculously, a miracle is what I received. HACKATHON TECH SOLUTION not only delivered on their promise but exceeded all expectations, successfully recovering my lost funds with a level of expertise and professionalism that left me in awe. In return for their invaluable service, they requested a modest 10% fee, a small price to pay for the restoration of my financial security. Thanks to the unwavering dedication of HACKATHON TECH SOLUTION, I am once again standing on solid ground, free from the shackles of financial fraud. My faith in humanity has been restored, and while the scars of my ordeal may linger, they serve as a solemn reminder to tread carefully in the digital realm. To anyone who finds themselves in a similar predicament, I urge you not to lose hope. Reach out to HACKATHON TECH SOLUTION and take the first step towards reclaiming what is rightfully yours. In a world fraught with deception, they are a beacon of light, guiding you towards justice and resolution. Trust in HACKATHON TECH SOLUTION– your ally in the fight against cybercrime.Reach out to HACKATHON TECH SOLUTIONS via below contact details
Email: info(@)hackathontechsolution(.)com
Website:www(.)hackathontechsolutions(.)com
Whatsapp: +31 6 47999256
Telegram: @hackathontechsolutions4 -
**HOW TO RECOVER LOST CRYPTO FUNDS FROM SCAMMERS → CONTACT HACKATHON TECH SOLUTIONS**
Being a chef at The Ritz-Carlton, I’m accustomed to working in a high-pressure environment where precision, trust, and expertise are essential. My job requires careful attention to detail, from crafting exquisite dishes to managing a team in a bustling kitchen. But nothing could have prepared me for the shock and devastation I felt when I was scammed out of $300,000. It wasn’t just the financial loss it was the emotional toll. I felt like my entire world had crumbled. For months, I was consumed with confusion, anger, and vulnerability. Every day seemed like a battle, with doubts about my judgment haunting me and the fear that I’d never recover from such a significant loss.The situation seemed hopeless until one day, a fellow chef at The Ritz-Carlton noticed my distress. He had also fallen victim to a scam involving cryptocurrencies and lost a considerable amount of money. However, unlike me, he had managed to recover his funds through a company called HACKATHON TECH SOLUTIONS. After hearing his story and seeing the results for himself, he strongly recommended that I reach out to them.Though I was still skeptical, my colleague’s personal experience gave me a flicker of hope, and I decided to take the leap. I contacted HACKATHON TECH SOLUTIONS, not knowing what to expect but desperate for any solution. From the moment I made the initial call, I was impressed by their professionalism. The team took the time to listen to my story without judgment and explained the entire recovery process clearly and transparently. They reassured me that they had the expertise to help recover my funds, and for the first time in months, I felt a sense of relief. HACKATHON TECH SOLUTIONS worked tirelessly on my behalf. They kept me updated throughout the process, answering all my questions and providing me with the support I needed. Their dedication and commitment were evident, and they were able to successfully recover every penny I had lost. The relief I felt when the funds were returned was overwhelming. It was more than just about money it was about regaining my peace of mind and confidence in myself.I am incredibly grateful to my colleague for introducing me to HACKATHON TECH SOLUTIONS. Their expertise and support gave me the chance to recover not only my finances but also my sense of security. Thanks to them, I can move forward, knowing I’ve found a team I can trust. Reach out to HACKATHON TECH SOLUTIONS via below contact details
Email: info (@) hackathon tech solution (.) com
Website: hackathon tech solutions (.) com
W h a t s a p p: +31 6 47999256
Telegram: (@) hackathon tech solutions7 -
Why Vulnerability Assessments are Critical for Enterprise Security?
A vulnerability assessment involves examining components of the IT environment to find potential security flaws that could be exploited by attackers.
The goal is to discover these issues before they can be used to compromise the system, allowing the organization to fix them and strengthen its security.
Types of Vulnerability Assessments
Scanning
This involves using automated tools to scan the technology environment for known vulnerabilities. The scanner checks software, hardware, and network configurations against a database of known issues to identify potential security gaps.
Penetration Testing
Also known as ethical hacking, penetration testing involves simulating attacks on the system to find vulnerabilities. Security experts attempt to exploit weaknesses in the system, just like a real attacker would, to uncover issues that automated scans might miss. This type of testing provides a deeper understanding of the security risks.
Risk Assessment
Risk assessment involves evaluating the potential impact and likelihood of identified vulnerabilities being exploited. It prioritizes vulnerabilities based on their potential harm to the organization and helps in making informed decisions about which issues to address first. This process often includes analyzing the potential consequences and the likelihood of exploitation.
The Role of Vulnerability Assessments in Enterprise Security
Identifying Weaknesses
Vulnerability assessments play a crucial role in uncovering security weaknesses within an organization’s IT environment. By systematically examining software, hardware, and network configurations, these assessments reveal potential vulnerabilities that could be exploited by attackers. Identifying these weaknesses early allows organizations to address them before they can be used to compromise the system. This proactive approach helps prevent security breaches and protects sensitive data from being exposed or stolen.
Prioritizing Risks
Once vulnerabilities are identified, it is essential to prioritize them based on their potential impact and likelihood of exploitation. Not all vulnerabilities pose the same level of risk. Some might be easily exploitable and have severe consequences, while others might be less critical. Understanding which vulnerabilities present the greatest risk helps organizations focus their resources and efforts on addressing the most pressing issues first. This prioritization ensures that the most critical weaknesses are fixed promptly, reducing the overall risk to the organization.
You can check more info about: Vulnerability Assessments( Opstree ) -
HOW DIGITAL TECH GUARD RECOVERY RECOVER STOLEN BITCOIN ASSETS
WhatsApp: +1 (443) 859 - 2886
contact @ digital tech guard . com
Telegram : digital tech guard recovery . com
As a freelance artist based just outside of Austin, I had always relied on platforms like Upwork to sell my work and connect with clients. So when I first heard about NFTs, I was intrigued by the idea of using blockchain technology to sell my art and reach new buyers. It seemed like the perfect way to break free from the limitations of traditional platforms and finally make my digital creations more profitable. I came across what appeared to be a reputable NFT marketplace. The platform had a flashy interface and showcased prominent artists, while the online art community buzzed with excitement around it. This validation gave me the confidence to dive in. I spent weeks creating a new series of digital artworks, pouring my heart and soul into them, and then minted them as NFTs on this platform. The fees associated with minting were steep around $20,000 but I believed the potential returns would more than justify the investment. With my NFTs listed, I eagerly promoted them on social media, leveraging my experience from Upwork to engage potential buyers. I received a couple of bids, which filled me with optimism. It felt like everything was finally coming together. But that excitement quickly turned into confusion and frustration when I tried to withdraw the funds from the bids. Instead of receiving my earnings, the platform displayed an error message. When I reached out to their support team, they requested additional payments to "process my withdrawal." At first, the fees seemed minor, but then they escalated, with new demands for payment popping up regularly. The requests quickly spiraled into an endless loop. Days turned into weeks, and my hopes of seeing any return on my investment faded. It dawned on me that I had been scammed. The platform was a fake, and the supposed big-name artists likely part of an elaborate scheme to lure in unsuspecting creators like me. I was devastated both financially and emotionally and felt too embarrassed to tell anyone. I feared people would think I had been reckless or gullible. After confiding in a close friend, I felt a sense of relief. She suggested I reach out to Digital Tech Guard Recovery, a service that specializes in tracking down stolen digital assets and helping people who have fallen victim to online scams. Desperate, I contacted them, and to my surprise, they were able to recover my funds. The experience taught me a hard lesson, but it also gave me hope that not all was lost. It reminded me that even in moments of vulnerability, reaching out for help can lead to unexpected solutions.1 -
TRUSTWORTHY CRYPTO RECOVERY SERVICE- HIRE SALVAGE ASSET RECOVERY
At Tax Ease Solutions, based in New York, USA, we faced a critical crisis when our tax filing system was hacked overnight. The breach exposed sensitive personal data, including Social Security numbers, financial details, and addresses of our clients. The attackers used this stolen information to apply for fraudulent tax refunds, resulting in a significant loss of $1 million USD. The breach occurred during the night while our team was off-duty, leaving us unaware until the following morning when we discovered the extent of the damage. With such a large amount of money lost and the integrity of our business compromised, we knew we needed immediate assistance to recover and secure both our clients’ data and our reputation. That’s when we reached out to Salvage Asset Recovery. Salvage Asset Recovery’s team responded promptly and demonstrated their deep expertise in dealing with cybersecurity breaches. They quickly identified the source of the vulnerability and acted decisively to patch the system flaw. Their ability to rapidly assess the situation and implement corrective actions helped to prevent any further unauthorized access to our platform. Once the system was secured, Salvage Asset Recovery shifted their focus to assisting our affected clients. They worked diligently with financial institutions and law enforcement to help some clients who were able to reach out and report the fraudulent tax refund applications. Through their intervention, these clients were able to stop the fraudulent transactions and recover some of their funds. As of now, Salvage Asset Recovery has managed to recover $980,000 of the lost $1 million, but they are still continuing to work with authorities and financial institutions to recover the remaining funds. Salvage Asset Recovery helped us implement more robust security measures to prevent any future breaches. They introduced advanced encryption techniques and worked with us to update our cybersecurity protocols, ensuring that our clients' data would be better protected going forward. Their consultation also guided us in strengthening our internal data protection policies, which reassured our clients that we were committed to safeguarding their sensitive information. Thanks to the quick and efficient actions of Salvage Asset Recovery, Tax Ease Solutions was able to recover $980,000 of the lost funds and protect the majority of our clients’ data. Their professionalism, expertise, and dedication to helping both our company and our clients made all the difference in mitigating the effects of the breach and stabilizing our business. The recovery process is still ongoing, but we remain confident that with Salvage Asset ’s continued support, we will fully resolve the situation.
Their Contact info,
WhatsApp+ 1 8 4 7 6 5 4 7 0 9 6 1
1 -
EXPERT HELP TO RECLAIM WHAT YOU LOST// VISIT SALVAGE ASSET RECOVERY
You can send a DM to Salvage Asset Recovery via below contact details.
WhatsApp-----.+ 1 8 4 7 6 5 4 7 0 9 6
Telegram--@Salvageasset
Success is not the key to happiness. Happiness is the key to success. If you love what you are doing, you will be successful." This quote has always driven me as a truck driver, where every mile I log is for my family’s future, their comfort, security, and dreams. However, my pursuit of stability was shattered when I lost $130,000 in Bitcoin to a cyberattack after a careless decision while delivering goods in California. During one of my routes, I stopped at a shop to take a break and noticed that a Wi-Fi network was available. Thinking it would be convenient to connect and check my crypto accounts, I didn’t consider the potential risks. The moment I saw my empty wallet later that day, my world collapsed. That money represented years of sacrifice, late nights, missed moments, and relentless effort gone in an instant. The guilt and helplessness were crushing. In my desperation, I scoured the internet for solutions, only to hit dead ends until I stumbled upon Salvage Asset Recovery. Initially skeptical but with no other options left, I reached out to Salvage Asset Recovery. Their team responded not just with expertise, but with genuine empathy. They understood the emotional toll this loss had taken on me and my family. Salvage Asset Recovery meticulously traced the stolen funds through the blockchain, working tirelessly to achieve what felt impossible: they recovered my Bitcoin. This ordeal taught me that vulnerability isn’t a weakness; even the most cautious can fall victim to unseen threats. It also reaffirmed the power of resilience and the importance of trusting the right people, like those at Salvage Asset Recovery. This was a harsh reminder of the risks we take in our digital lives, but it also highlighted the strength we can find in community and support. Today, I’m back on the road, driving with renewed purpose. My family is secure, my faith in humanity restored, and my definition of success has been refined. It’s not just about wealth; it’s about perseverance, love, and the courage to seek help when all seems lost. If you’ve faced a similar nightmare, don’t give up. Hope exists, and sometimes, it takes the right ally, like Salvage Asset Recovery, to reclaim what was stolen. Salvage Asset Recovery was my lifeline, proving that even in the darkest moments, redemption is possible. Keep fighting, your success and happiness are worth it. I recovered all my funds, and with that, Salvage Asset Recovery, are the true keys to a fulfilling life.2 -
Losing $27,300.50 to a cryptocurrency scam felt like a ruinous punch to the gut. One moment, I was finalizing what appeared to be a legitimate online purchase, a limited time opportunity endorsed by polished testimonials and a professional looking platform. The website boasted glowing reviews and featured a countdown timer that pressured users to act swiftly. It felt authentic, complete with an SSL certification, a sleek interface, and even a fabricated customer service chat. I transferred my life savings, convinced I had secured a rare investment. The next moment, my funds vanished into the digital abyss. The platform disappeared, replaced by a stark error message. My stomach plummeted. I had been ghosted. The scammers left no trace, only a hollow void where my money once resided. Shame engulfed me. How could I have been so gullible? For days, I spiraled into despair. Sleep eluded me as I fixated on screenshots of the scam site, dissecting every detail I had overlooked the slightly pixelated logo, the overly polished testimonials. The irreversible nature of cryptocurrency transactions taunted me; the anonymity of blockchain offered no solace. My hands trembled at the thought of starting over. But then, a friend intervened. Scammers thrive on silence,” she insisted, her voice resolute. “You must speak up for yourself and others.Reluctantly, I shared my story on Instagram, exposing the scam’s mechanics, the false urgency, the cloned platform. Vulnerability burned within me, but the response was astonishing. Hundreds replied, recounting identical nightmares. One message stood out: Contact PYRAMID HACK SOLUTION Website; https: // pyramidhacksolution. com They’re legitimate. Their website was clinical yet reassuring promising recovery with no upfront fees. Case studies detailed intricate crypto traces and frozen assets. I submitted my information, bracing for yet another potential scam. Instead, a specialist contacted me within hours. Their calm precision anchored me. “We’ll follow the money through layered wallets,” they explained. Scammers bounce crypto through dummy accounts, but patterns will emerge.The process was arduous. PYRAMID HACK SOLUTION collaborated with offshore exchanges, employing forensic tools to map transaction trails. They discovered my case was linked to a syndicate scamming hundreds. Each update chipped away at my despair. Three weeks later, a notification flashed: $27,300.50 reappeared, plus $850 from frozen scammer funds. I sobbed with relief. The specialist later revealed that my case helped dismantle part of the network. Today, I advocate for victims. The scars remain, but so does this truth: silence protects criminals. Speak up and fight back. Recovery is possible, together with Wizard web recovery , you can reclaim what was lost. WhatsApp; +44 741 428 09 142
-
HOW TO RECOVER BITCOIN IF IT'S STOLEN; USDT AND ETH RECOVERY EXPERT HIRE DIGITAL TECH GUARD RECOVERY
WhatsApp: +1 (443) 859 - 2886
Email @ digital tech guard . com
Telegram: digital tech guard . com
Website link: digital tech guard . com
"Success is not the key to happiness. Happiness is the key to success. If you love what you are doing, you will be successful." This quote has always driven me as a truck driver, where every mile I log is for my family’s future their comfort, security, and dreams. However, my pursuit of stability was shattered when I lost $130,000 in Bitcoin to a cyberattack after a careless decision while delivering goods in California. During one of my routes, I stopped at a shop to take a break and noticed that a Wi-Fi network was available. Thinking it would be convenient to connect and check my crypto accounts, I didn’t consider the potential risks. The moment I saw my empty wallet later that day, my world collapsed. That money represented years of sacrifice late nights, missed moments, and relentless effort gone in an instant. The guilt and helplessness were crushing. In my desperation, I scoured the internet for solutions, only to hit dead ends until I stumbled upon Digital Tech Guard Recovery. Initially skeptical but with no other options left, I reached out to Digital Tech Guard Recovery. Their team responded not just with expertise, but with genuine empathy. They understood the emotional toll this loss had taken on me and my family. Digital Tech Guard Recovery meticulously traced the stolen funds through the blockchain, working tirelessly to achieve what felt impossible: they recovered my Bitcoin. This ordeal taught me that vulnerability isn’t a weakness; even the most cautious can fall victim to unseen threats. It also reaffirmed the power of resilience and the importance of trusting the right people, like those at Digital Tech Guard Recovery. This was a harsh reminder of the risks we take in our digital lives, but it also highlighted the strength we can find in community and support. Today, I’m back on the road, driving with renewed purpose. My family is secure, my faith in humanity restored, and my definition of success has been refined. It’s not just about wealth; it’s about perseverance, love, and the courage to seek help when all seems lost. If you’ve faced a similar nightmare, don’t give up. Hope exists, and sometimes, it takes the right ally, like Digital Tech Guard Recovery, to reclaim what was stolen. Digital Tech Guard Recovery was my lifeline, proving that even in the darkest moments, redemption is possible. Keep fighting your success and happiness are worth it. I recovered all my funds, and with that, Digital Tech Guard Recovery, are the true keys to a fulfilling life.2 -
LOST YOUR CRYPTO? HERE IS HOW TO GET IT BACK SAFELY HIRE ADWARE RECOVERY SPECIALIST
At 49, my life is the result of both calculated risks and deeply painful betrayals. As an economics lecturer at Harrington University, I teach students about market fluctuations and financial strategy. But the most profound lessons I share come not from textbooks, they come from my own personal experience with loss, betrayal, and eventual recovery. WhatsApp info: +12 (72332)—8343
Before stepping into university classrooms, I was a high school teacher at Westbridge High. Quietly and methodically, I built a $370,000 cryptocurrency trading portfolio. What started as a side project became a private triumph, a reflection of my deep understanding of economic principles, cultivated through discipline, patience, and analytical thinking.
But ambition can invite envy. Email info: Adware recovery specialist @ auctioneer. net
Some of my old friends from Westbridge, once trusted confidants, became resentful as they learned of my growing financial success. That resentment turned malicious when they orchestrated a sophisticated phishing attack. It came through a seemingly harmless email. One careless click, and just like that, everything was gone. My savings, my sense of security, and my faith in people I had known for decades vanished in an instant.
The aftermath was paralyzing. Though I reported the theft, the digital trail seemed impossibly complex. I felt isolated, betrayed, and utterly lost. Then a colleague referred me to Adware Recovery Specialist, a cybersecurity firm that specializes in digital financial fraud. Within just 32 hours, they recovered my compromised email, traced the attack, and compiled a detailed forensic report. The evidence was airtight, IP addresses, time stamps, even messages exchanged by the perpetrators. Website info: h t t p s:// adware recovery specialist. com
Thanks to their work, I took legal action. Faced with irrefutable proof, my former “friends” settled quickly, agreeing to pay $300,000 in restitution to avoid criminal prosecution.
Today, back at my desk at Harrington University, I bring more than just economic theory into the classroom. I teach about risk, trust, digital vulnerability, and most importantly, resilience. I share my experience not to scare, but to prepare. Because no amount of expertise shields you completely from deception. But with the right allies, even the worst chapters can be rewritten.
Yes, I still trade crypto. But now, I do it with triple-layer authentication and a much more guarded heart. Every time I log into my secured accounts, I think of Adware Recovery Specialist, not just for recovering my funds, but for restoring my belief that justice, with the right team, is possible.
Because sometimes, the most valuable recovery isn’t just financial, it’s personal.2 -
HIRE A RECOVERY EXPERT IN 2025 HIRE ADWARE RECOVERY SPECIALIST
WhatsApp info:+12723 328 343
As a freelance artist based just outside of Austin, I had always relied on platforms like Upwork to sell my work and connect with clients. So when I first heard about NFTs, I was intrigued by the idea of using blockchain technology to sell my art and reach new buyers. It seemed like the perfect way to break free from the limitations of traditional platforms and finally make my digital creations more profitable. I came across what appeared to be a reputable NFT marketplace. The platform had a flashy interface and showcased prominent artists, while the online art community buzzed with excitement around it. This validation gave me the confidence to dive in. I spent weeks creating a new series of digital artworks, pouring my heart and soul into them, and then minted them as NFTs on this platform. The fees associated with minting were steep around $20,000 but I believed the potential returns would more than justify the investment. With my NFTs listed, I eagerly promoted them on social media, leveraging my experience from Upwork to engage potential buyers. I received a couple of bids, which filled me with optimism. It felt like everything was finally coming together. But that excitement quickly turned into confusion and frustration when I tried to withdraw the funds from the bids. Instead of receiving my earnings, the platform displayed an error message. When I reached out to their support team, they requested additional payments to "process my withdrawal." At first, the fees seemed minor, but then they escalated, with new demands for payment popping up regularly. The requests quickly spiraled into an endless loop. Days turned into weeks, and my hopes of seeing any return on my investment faded. It dawned on me that I had been scammed. The platform was a fake, and the supposed big-name artists likely part of an elaborate scheme to lure in unsuspecting creators like me. I was devastated both financially and emotionally and felt too embarrassed to tell anyone. I feared people would think I had been reckless or gullible. After confiding in a close friend, I felt a sense of relief. She suggested I reach out to ADWARE RECOVERY SPECIALIST , a service that specializes in tracking down stolen digital assets and helping people who have fallen victim to online scams. Desperate, I contacted them, and to my surprise, they were able to recover my funds. The experience taught me a hard lesson, but it also gave me hope that not all was lost. It reminded me that even in moments of vulnerability, reaching out for help can lead to unexpected solutions.1 -
CRYPTO ASSET RECOVERY EXPERTS, CONTACT DIGITAL TECH GUARD RECOVERY
Stay clear as this has been the biggest nightmare of my life.
They trick you into investing with all their lies and tactics. They are not a real company and have no legitimate address, as the FCA warned me they are a scam. These so-called "investments" are a facade, meant only to deceive and steal from vulnerable people. I was lured in by promises of high returns and an easy path to financial success. I initially felt optimistic and confident, but things quickly took a dark turn. I tried to close my account and withdraw my funds when I had over €213,500.00 in my account, but they continually came up with excuse after excuse, making it impossible for me to get my money back. They kept promising that the withdrawal would go through, but nothing ever happened. It became clear that the platform was fake my money was not being invested in the market as promised. Instead, they were stealing it through a covert mechanism. They opened a coin tandem account under my name and used my funds to buy bitcoins, transferring them into various bitcoin wallet addresses that were not under my control. They kept me in the dark, manipulating me with false statements while slowly siphoning off my money. What’s even worse is that the company’s credit was a complete fabrication. The bank details they provided were not even theirs, but instead belonged to coin tandems, the very platform that was helping them execute this scam. I felt trapped and powerless. To add insult to injury, they knew about my personal circumstances. They knew I had a young daughter and that I was struggling with my health. Yet, despite my vulnerability, they continued to gaslight me, leading me to believe that everything was fine. I felt emotionally drained and helpless. Fortunately, I was introduced to Conrad Drew, a former insider who had been working with the scammers. He reached out to me and confessed that he had realized the truth behind their operations. He had been close to them but eventually saw the light. He told me it was a scam and connected me to Digital Tech Guard Recovery,
WhatsApp: +1 (443) 859 - 2886 Email @ digital tech guard . com
Telegram : digital tech guard recovery . com website link : digital tech guard . com
a professional team that specializes in helping people recover funds from fraudulent schemes like this. Digital Tech Guard Recovery was incredible. They immediately understood the situation and assured me they could help. I had been struggling to break through the wall of lies that the scammers had built around me, but Digital Tech Guard Recovery made it possible to get my money back. They worked efficiently, breaking through the scammers' servers, and they kept their promises, giving me peace of mind during one of the darkest times in my life. If you find yourself in a similar situation, please reach out to them. Their professionalism and success rate in recovering funds are unmatched. I can confidently say that Digital Tech Guard Recovery is the team you need. Don't hesitate to trust them they are everything they claim to be, and more.1 -
HOW TO RETRIEVE YOUR LOST INVESTMENT FUNDS FROM SCAMMER. MEET SACLUX COMPTECH SPECIALST
As the digital landscape continues to evolve, so do the opportunities and risks associated with online investments and transactions. With the proliferation of online businesses and the advent of cryptocurrency, individuals are increasingly turning to digital investments to grow their wealth. However, amidst the vast array of legitimate opportunities lie the lurking dangers of online scams.
The anonymity afforded by the internet has created fertile ground for fraudulent activities, making it challenging for individuals to distinguish between genuine businesses and malicious actors. This inherent lack of transparency has paved the way for a myriad of online scams, each employing various tactics to deceive unsuspecting victims.
Online scams can manifest in numerous forms, with some of the most common schemes including:
PHISHING EMAILS: Fraudulent emails masquerading as reputable sources, aimed at extracting personal information such as phone numbers, emails, and passwords.
Unsolicited investment opportunities: Random contact from anonymous individuals offering enticing investment prospects or prize collections, often too good to be true.
CRYPTOCURRENCY THEFT: The unauthorized access and theft of digital currencies, including Bitcoin and initial coin offerings (ICOs), from online wallets.
In the unfortunate event that you fall victim to an online scam and suffer financial losses, it's imperative to take swift action to mitigate further damage and potentially recover your funds.
The first course of action should be to contact your bank or financial institution immediately upon detecting the fraudulent transaction. They may be able to halt the transaction processing or provide assistance in resolving the issue. However, the extent of their support may vary depending on individual circumstances and the policies of the institution.
Furthermore, it's advisable to report the scam to relevant authorities such as CFTC. While they may intervene if the scam involves illegal activities within their jurisdiction, their powers may be limited if the perpetrator is unidentified or based overseas. Nevertheless, reporting the incident can contribute valuable data to track and combat online scams, potentially safeguarding others from similar predicaments in the future.
Additionally, victims can hire a Cybersecurity Expert or Recovery Company: Engage a professional cybersecurity expert or a reputable cryptocurrency recovery company. These experts can help track and potentially recover your stolen funds. They use advanced techniques and tools to trace transactions and identify the culprits. A company proven for their excellence in recovering money is SACLUX COMPTECH SPECIALST, they will definitely assist you with your refund.
The proliferation of online scams underscores the importance of vigilance and caution in the digital realm. By staying informed about common scam tactics, taking proactive measures to protect personal information, and promptly reporting suspicious activities, individuals can reduce their vulnerability to online fraud and safeguard their financial well-being. SACLUX COMPTECH SPECIALST will recover all the money you lost to scammers.
Telegram: @SacluxComptechWhatsapp: +44 749) 221-35521 -
CHANCES OF CRYPTO RECOVERY OPTIONS:USE SPARTAN TECH GROUP RETRIEVAL
WhatsApp:+1 (971) 4 8 7 - 3 5 3 8
Email: spartantech (@) cyberservices . com
Telegram:+1 (581) 2 8 6 - 8 0 9 2
For many individuals and businesses, the experience of financial loss, whether caused by cyberattacks, data breaches, or unforeseen events, can feel overwhelming and intimidating. The emotional and financial toll can be immense, leaving people uncertain of where to turn. In these challenging times, SPARTAN TECH GROUP RETRIEVAL offers a crucial lifeline, providing expert services that guide clients through the recovery process with both skill and compassion. At SPARTAN TECH GROUP RETRIEVAL, the team recognizes the profound impact financial loss can have on clients, not only in terms of their finances but also on their sense of security and well-being. Their highly trained professionals specialize in assessing the full extent of damage caused by various disruptions, carefully identifying the underlying issues and working to develop tailored recovery strategies. Whether the challenge involves restoring lost data, recovering compromised systems, or securing vulnerable networks, SPARTAN TECH GROUP RETRIEVAL utilizes the latest technology and industry best practices to restore both operational efficiency and peace of mind. Data loss can be a particularly devastating consequence of a cyberattack or system failure. In a world where information is the lifeblood of businesses, recovering lost or corrupted data is crucial to regaining normal operations. SPARTAN TECH GROUP RETRIEVAL’s experts employ advanced data recovery techniques to retrieve vital information, ensuring that clients do not suffer irreversible setbacks. By recovering valuable data, they allow businesses to continue their operations with minimal disruption. Beyond data recovery, SPARTAN TECH GROUP RETRIEVAL excels at restoring and securing compromised systems. After a breach or attack, the threat of future vulnerabilities looms large. The team’s cybersecurity experts take swift action to secure networks and systems, implementing robust protection measures to defend against future threats. Through a combination of proactive monitoring, vulnerability assessments, and real-time security solutions, SPARTAN TECH GROUP RETRIEVAL works tirelessly to ensure that businesses and individuals can rebuild trust and safeguard their digital assets for the long term. However, what truly distinguishes SPARTAN TECH GROUP RETRIEVAL is its unwavering commitment to client care. While the technical aspects of recovery are vital, the company understands the emotional strain that often accompanies financial loss. Their compassionate case managers offer much-needed emotional support and practical guidance, helping clients navigate both the logistical and psychological challenges they face. By addressing the emotional as well as the practical aspects of recovery, SPARTAN TECH GROUP RETRIEVAL ensures that clients feel understood and supported throughout the entire process. In the face of financial hardship, SPARTAN TECH GROUP RETRIEVAL is a trusted partner that combines technical expertise with empathy and dedication. Their holistic approach ensures that businesses and individuals can recover, rebuild, and emerge from financial challenges stronger, more secure, and better prepared for the future. 1
1 -
ACT FAST: HOW TO RECOVER YOUR STOLEN CRYPTO SAFELY / GO TO RAPID DIGITAL RECOVERY
New York, a bustling metropolis renowned for its vibrant energy and eclectic culture, is a city where aspirations are both realized and, at times, dashed. It was within this dynamic landscape that I encountered one of the most harrowing experiences of my life. After falling prey to a meticulously orchestrated scam that siphoned off a staggering $200,000 USD, I found myself in a state of profound disarray. The initial shock was overwhelming; it felt as though the very ground had been yanked from beneath my feet. The sense of vulnerability and helplessness was suffocating, leaving me in desperate pursuit of a solution. This loss transcended mere finances; it was a devastating blow to my self-esteem and sense of security. I fortuitously discovered RAPID DIGITAL RECOVERY, a company that specializes in assisting individuals like myself in reclaiming lost funds from fraudulent schemes. RAPID DIGITAL RECOVERY’s stellar reputation preceded them, bolstered by numerous testimonials from clients who had successfully recovered their money. Despite my skepticism, a flicker of hope ignited within me. Could RAPID DIGITAL RECOVERY truly navigate the labyrinthine complexities of my situation? The scam I had encountered was intricately designed, and I harbored little faith that anyone could unravel the web of deceit that had ensnared me. With a blend of trepidation and optimism, I reached out to RAPID DIGITAL RECOVERY. From our very first interaction, I was met with professionalism and genuine empathy. The team at RAPID DIGITAL RECOVERY took the time to meticulously understand the nuances of my case, assuring me that they had successfully handled similar predicaments before. Their expertise was palpable, and I began to feel a burgeoning sense of reassurance that perhaps I was not as isolated in this battle as I had initially believed. As the recovery process unfolded, RAPID DIGITAL RECOVERY kept me informed at every juncture. The team worked assiduously, employing a variety of strategies to trace the misappropriated funds and hold the perpetrators accountable. Their unwavering commitment to my case was evident, and I could sense their authentic desire to help me reclaim what was rightfully mine. RAPID DIGITAL RECOVERY not only succeeded in recovering my lost funds but also rejuvenated my faith in justice and the possibility of healing. This experience imparted invaluable lessons about the importance of vigilance and the necessity of seeking assistance when confronted with adversity. I emerged from this ordeal not merely with my finances restored, but with a renewed sense of empowerment and hope for the future. New York, with all its challenges, had also served as the backdrop for my transformative journey toward recovery and resilience, thanks to RAPID DIGITAL RECOVERY.
WhatSapp Info: +1 4 1 4 8 0 7 1 4 8 5
Telegram Info: https: // t. me/ Rapid digital recovery519
Email Info: rapid digital recovery (@) execs. com5 -
RECOVERING LOST OR STOLEN CRYPTOCURRENCY WALLETS: A COMPREHENSIVE GUIDE WITH RAPID DIGITAL RECOVERY
One fateful day, my life took an unexpected turn when I received a phone call that would change everything. The voice on the other end claimed to be from my bank, delivering alarming news: my account had been frozen due to suspicious activity. Panic surged through me as I listened, my heart racing at the thought of losing my hard-earned savings. At that moment, I had about 130,000 USD in my bank, equivalent to around 2 BTC. The caller spoke with such authority and urgency that I felt compelled to act immediately. They insisted that the only way to protect my funds was to transfer Bitcoin BTC to them for "safekeeping. In my fear and confusion, I believed I was making a wise decision to secure my finances. Without fully grasping the implications, I complied and transferred the equivalent of my savings in Bitcoin, convinced I was safeguarding my money. It wasn’t until later that the reality of my situation hit me like a ton of bricks. I had been duped, and the weight of my mistake was unbearable. Shame and disbelief washed over me as I realized how easily I had been manipulated. How could I have let this happen? The feeling of vulnerability was overwhelming, and I was left grappling with the consequences of my actions. I learned about a recovery expert named RAPID DIGITAL RECOVERY. Desperate to reclaim what I had lost, I reached out for help. RAPID DIGITAL RECOVERY was knowledgeable and reassuring, explaining that there was a chance to trace the Bitcoin I had sent. With their expertise, they tracked the stolen funds to a peer-to-peer (P2P) exchanger based in the United Kingdom. This revelation sparked a glimmer of hope within me, a sense that perhaps justice could be served. RAPID DIGITAL RECOVERY collaborated with Action Fraud, the UK's national reporting center for fraud and cybercrime, to take decisive action against the scammers. Knowing that law enforcement was involved provided me with a sense of relief. The thought that the culprits behind my suffering could be brought to justice was comforting. In an incredible turn of events, RAPID DIGITAL RECOVERY successfully recovered all my funds, restoring my faith in the possibility of justice and recovery.
WhatSapp Info: +1 4 1 4 8 0 7 1 4 8 5
Telegram Info: https: // t. me/ Rapid digital recovery519
Email Info: rapid digital recovery (@) execs. com2 -
Dependability is a fundamental more modest than common expertise for bosses
New managers a significant part of the time feel that since they have been raised to the heap up they ought to know everything immediately. Truly, it anticipates that adventure should gain capacity with the association styles and approaches that turn out to be cruel for your social affair. Being flexible and being open to the bewildering will assist you with changing into a useful manager. A Roman scientist named NURS FPX 4000 Assessment 4 Analyzing a Current Health Care Problem or Issue Seneca is credited with saying, "Karma slants toward the coordinated." And while karma can earnestly play a consider life, all that verifiably pivots around orchestrating yourself for when incredible karma comes your bearing. Excellent affiliations do this by orchestrating themselves for an entrance through status and planning.
Plan for disappointment and goofs - it's really clever to expect them a lot early so you can lessen the effect. A SWOT assessment (Qualities, Shortcomings, Anticipated open doorways and Risks) is an important instrument for this. The more you plan for a social event the more useful it will be. Approach saves time by lessening blunders, forestalling re-work and shortening works out. And it in addition decreases pressure, which is overall something that would justify being thankful for! Other than being a NURS FPX 4010 Assessment 1 Collaboration and Leadership Reflection Video State financed School English educator, Kine is in this way the head of Ryan Search & Directing and facilitates Held Supervisor Pursue, Help and Drive New turn of events. His clients range different undertakings from Headway to Monetary Associations.
Whether an overwhelming event, network prosperity break or stock association disrupting impact, astounding occasions can emerge whenever. Being available to the unexpected assists you with finding sure results and make depend with your partners. One strategy for doing this is to remain mindful of vulnerability, where you proceed with like the circumstance is both customary and novel. This assists you with expanding your NURS FPX 4010 Assessment 3 Interdisciplinary Plan Proposal data affirmation and seek after the most ideal choice. ClickUp's Business Development Plan Configuration is an incredible contraption for planning the normal and the unforeseen!
Dependability is an essential limited scope ability for bosses to make. Supervisors should be ready to have authentic two-way discussions with specialists and should endeavor to get themselves when they are concealing reality or lying. Fair correspondences among supervisors and representatives can assist with fostering a positive work environment culture and can expect a fundamental part in the connection's prospering. While giving investigation, supervisors ought to convey NURS FPX 4020 Assessment 1 Enhancing Quality and Safety both the positive and negative parts of a representative's show. They ought to in addition have the decision to give obliging assessment and backing workers when essential. This correspondence style is as frequently as conceivable implied as moderate candor.
MORE
Instagram is a powerful tool for businesses
The best digital marketing agencies
Instagram is an amazing asset for businesses -
When faced with the distressing reality of falling victim to a financial scam, seeking guidance and assistance from reputable recovery services becomes paramount. fast swift cyber services as help in such dire situations, offering expert support and expertise to individuals grappling with the aftermath of fraudulent schemes. The journey of recovery often begins with a seemingly innocuous interaction, as was the case for many who have sought assistance from fast swift cyber services. A message on Twitter, an initial expression of interest, and the gradual establishment of a relationship pave the way for unsuspecting individuals to be drawn into the intricate web of deception. In my review, the tale unfolds with the promise of quick riches through 30-second trades on a dubious platform. A modest investment of USD 49,000 snowballs into a significant sum, further fueled by persuasion to inject additional funds amounting to £61,000 in ETH.
The allure of exponential growth through completing routine tasks blinds many to the looming danger lurking beneath the surface. However, the facade of prosperity quickly crumbles when attempts to withdraw profits are met with inexplicable obstacles. A withdrawal failure serves as the first ominous sign, followed by a cascade of demands from the supposed support team. The requirement to pay exorbitant trading fees to access one's funds becomes a seemingly insurmountable barrier, with promises of resolution serving only to deepen the despair. Prompt action is taken to reach out to this trusted ally, and the response is nothing short of miraculous. Within days, the team at FAST SWIFT CYBER SERVICES embarks on a mission to trace and recover the lost funds, culminating in a swift resolution that defies all odds.
The efficiency and professionalism displayed throughout the process serve as a testament to the unwavering dedication of FAST SWIFT CYBER SERVICES to their clients' cause. Beyond the tangible outcome of fund recovery, the experience instills valuable lessons about the importance of due diligence and vigilance in the realm of online investments. Scammers prey on vulnerability and trust, exploiting unsuspecting individuals with promises of unrealistic returns. However, armed with knowledge and awareness, individuals can fortify themselves against such deceitful tactics, ensuring that they approach investment opportunities with caution. In addition to seeking professional assistance, proactive steps are taken to protect oneself from future scams. Education becomes a powerful tool in the arsenal against fraud, empowering individuals to recognize and avoid potential pitfalls before they fall victim. By sharing personal experiences and advocating for awareness, individuals can play a pivotal role in preventing others from suffering a similar fate.
FAST SWIFT CYBER SERVICES emerges as a trusted ally in the fight against financial fraud, offering expert guidance and assistance to those in need. Through their unwavering commitment to justice and integrity, they provide a lifeline to individuals grappling with the aftermath of fraudulent schemes. With their support and a renewed sense of vigilance, individuals can navigate the online landscape with confidence, safeguarding their financial well-being and protecting themselves from future scams.
Reach out to them on;
HIRE FAST SWIFT CYBER SERVICES TO RECOVER YOUR LOST OR STOLEN BITCOIN/ETH/USDT/NFT AND OTHER CRYPTOCURRENCY
Email: fastswift @ cyberservices . com
Telephone: +1 970-900-0938
WhatsApp: +1 401 219-5530 -
When faced with the distressing reality of falling victim to a financial scam, seeking guidance and assistance from reputable recovery services becomes paramount. fast swift cyber services as help in such dire situations, offering expert support and expertise to individuals grappling with the aftermath of fraudulent schemes. The journey of recovery often begins with a seemingly innocuous interaction, as was the case for many who have sought assistance from fast swift cyber services. A message on Twitter, an initial expression of interest, and the gradual establishment of a relationship pave the way for unsuspecting individuals to be drawn into the intricate web of deception. In my review, the tale unfolds with the promise of quick riches through 30-second trades on a dubious platform. A modest investment of USD 49,000 snowballs into a significant sum, further fueled by persuasion to inject additional funds amounting to £61,000 in ETH.
The allure of exponential growth through completing routine tasks blinds many to the looming danger lurking beneath the surface. However, the facade of prosperity quickly crumbles when attempts to withdraw profits are met with inexplicable obstacles. A withdrawal failure serves as the first ominous sign, followed by a cascade of demands from the supposed support team. The requirement to pay exorbitant trading fees to access one's funds becomes a seemingly insurmountable barrier, with promises of resolution serving only to deepen the despair. Prompt action is taken to reach out to this trusted ally, and the response is nothing short of miraculous. Within days, the team at FAST SWIFT CYBER SERVICES embarks on a mission to trace and recover the lost funds, culminating in a swift resolution that defies all odds.
The efficiency and professionalism displayed throughout the process serve as a testament to the unwavering dedication of FAST SWIFT CYBER SERVICES to their clients' cause. Beyond the tangible outcome of fund recovery, the experience instills valuable lessons about the importance of due diligence and vigilance in the realm of online investments. Scammers prey on vulnerability and trust, exploiting unsuspecting individuals with promises of unrealistic returns. However, armed with knowledge and awareness, individuals can fortify themselves against such deceitful tactics, ensuring that they approach investment opportunities with caution. In addition to seeking professional assistance, proactive steps are taken to protect oneself from future scams. Education becomes a powerful tool in the arsenal against fraud, empowering individuals to recognize and avoid potential pitfalls before they fall victim. By sharing personal experiences and advocating for awareness, individuals can play a pivotal role in preventing others from suffering a similar fate.
FAST SWIFT CYBER SERVICES emerges as a trusted ally in the fight against financial fraud, offering expert guidance and assistance to those in need. Through their unwavering commitment to justice and integrity, they provide a lifeline to individuals grappling with the aftermath of fraudulent schemes. With their support and a renewed sense of vigilance, individuals can navigate the online landscape with confidence, safeguarding their financial well-being and protecting themselves from future scams.
Reach out to them on;
HIRE FAST SWIFT CYBER SERVICES TO RECOVER YOUR LOST OR STOLEN BITCOIN/ETH/USDT/NFT AND OTHER CRYPTOCURRENCY
Email: fastswift @ cyberservices . com
Telephone: +1 970-900-0938
WhatsApp: +1 401 219-5530 -
HACKER TO ASSIST ME RECOVER MY LOST CRYPTO HIRE SLAYER COIN RECOVERY
Life’s unpredictability struck me hard on a sweltering afternoon, as I juggled the relentless demands of taxi driving with dreams of a secure future for my family. Every fare I accepted, every mile I logged, was a step toward stability until a single lapse in judgment threatened to erase it all. Exhausted after a long shift, I stopped at a dimly lit café to check my Bitcoin wallet, clinging to the hope that my investments might one day lift us out of financial uncertainty. The public Wi-Fi was convenient, but in my haste, I didn’t consider the risks. Minutes later, hackers had stripped away $34,000, a sum representing years of sacrifice, sleepless nights, and promises to my children.The “access denied” message felt like a physical blow. My hands trembled as I reloaded the app, praying it was a glitch. But reality sank in: my family’s safety net was gone. Guilt consumed me. How could I explain this to my wife and children? I pictured my daughter’s college fund vanishing, my wife’s trusting smile crumbling under the weight of my mistake. Desperation drove me to scour the internet, where countless recovery scams preyed on vulnerability. Then, I stumbled upon SLAYER COIN RECOVERY, a lifeline in a sea of doubt.Their team responded instantly, blending expertise with empathy. “We’ll do everything possible,” their agent assured me, voice steady yet kind. They decoded the breach: the public network had been a trap, my login credentials intercepted. Over days that felt like eternities, they navigated blockchain complexities and cyber trails, updating me with unwavering transparency. When they finally restored access, tears blurred my screen $34,000 shone in my wallet, intact.This ordeal taught me invaluable lessons about vigilance and the importance of safeguarding my digital assets, revealing humanity’s remarkable capacity for good. SLAYER COIN RECOVERY didn’t just retrieve my lost funds; they salvaged my faith in second chances and the kindness of strangers. Their dedication transformed a moment of despair into a story of resilience and hope.Now, I take proactive measures to secure my investments, using military grade encryption and practicing safe online habits. I’ve become an advocate for digital security, sharing my experience with fellow taxi drivers and anyone willing to listen. I emphasize the importance of using secure networks and being cautious with personal information in a world rife with cyber threats.Moreover, the kindness I received from the SLAYER COIN RECOVERY team inspired me to pay it forward. I volunteer my time to help others navigate their financial challenges, offering guidance and sharing resources to empower those in vulnerable situations.My family’s future is no longer a gamble but a testament to resilience and the power of human connection. I’ve learned that even in the darkest moments, hope can be reclaimed through the support of others. It’s not just about the money; it’s about the lessons learned and the relationships forged in adversity. I carry the spirit of those who helped me as I navigate life’s complexities, determined to build a brighter future for my family and inspire others to do the same.If you ever find yourself in a similar situation, I wholeheartedly
+1(672)768-8701
recommend SLAYER COIN RECOVERY2 -
CONTACT BOTNET CRYPTO RECOVERY TO SPY ON YOUR CHEATING PARTNER
Navigating the complexities of online relationships can be challenging, especially when trust begins to erode. When I first started to notice subtle changes in my partner's behavior, I felt a mix of confusion and suspicion clouding my thoughts. I found myself in a maze of doubts, unable to pinpoint the reasons behind the growing distance between us. That's when I heard about Botnet Crypto Recovery, a tool designed to help individuals uncover hidden truths in digital interactions. I realized that this could be the key to addressing my concerns and understanding what was truly happening. With a sense of hope, I decided to give it a try, believing it might assist me in shedding light on the situation. The process of utilizing Botnet Crypto Recovery was surprisingly straightforward, which eased my initial apprehensions. After setting up the software, I was guided through various features designed to track online activities. It offered insights into messaging apps, social media interactions, and even browsing histories. Each step I took felt empowering, allowing me to regain a sense of control over my search for answers. As I delved deeper, I discovered patterns in online behavior that I had previously overlooked, such as late-night messages and secretive app usage. The information started painting a picture that I couldn’t ignore, compelling me to confront the reality of the situation rather than living in denial. As I continued my investigation, I was struck by the emotional weight of what I was uncovering. Every detail felt like a piece of a puzzle slowly coming together, but not in a way I had hoped for. Botnet Crypto Recovery didn’t only give me access to data; it also offered clarity. I remember feeling my heart race as I found evidence that pointed toward unfaithfulness. Each discovery was laced with a bittersweet mixture of relief and anguish. While I appreciated the facts that were coming to light, they also filled me with dread about the future of my relationship. I realized that what I had wanted was to find an explanation, but the answers were leading me down a path I was not prepared to tread. Finding out the truth was both a relief and a burden. Armed with the information from Botnet Crypto Recovery, I had the difficult task of confronting my partner about their behavior. Before this, I had been hesitant and unsure, but now I felt fortified with knowledge. The conversation that followed was one of the hardest I’ve ever had, marked by tension and vulnerability. I was prepared to face reality, whatever it may be, and that felt empowering. It was essential to have that moment, although painful, as it was the turning point in our relationship. I realized that clarity can sometimes come at a steep price, but living in confusion was unbearable. In the aftermath of that confrontation, I came to understand the profound impact of unveiling hidden truths. While the revelations were painful, they also became a catalyst for change. Using Botnet Crypto Recovery not only helped me navigate through the complexities of online behavior, but it also pushed me to reflect on my own needs and desires in a relationship. I learned important lessons about trust, communication, and self-worth. Although the outcome wasn’t what I had hoped for, I felt a renewed sense of strength in my ability to confront challenges head-on. Ultimately, the experience taught me that clarity, even in the midst of discomfort, is crucial for personal growth and understanding. Contact Botnet Crypto Recovery on email: support@ botnetcryptorecovery . com
Thanks.1 -
I NEED A HACKER TO ASSIST ME RECOVER MY LOST CRYPTO VISIT CYBER CONSTABLE INTELLIGENCE
In today's interconnected world, the attraction of financial investments often comes hand in hand with the looming threat of fraud. My own journey into the treacherous waters of investment began with hopeful anticipation but ended in a harrowing tale of deceit and financial loss. I embarked on my investment journey with a staggering $263,000, trusting an unregulated company promising lucrative returns. Initially, the promises seemed promising—enticing profits and assurances of secure transactions. However, as time progressed, the facade began to crumble. The company relentlessly demanded additional deposits under the guise of "enhancing returns" and "securing investments," leaving me ensnared in a web of deceit. Realizing the gravity of my situation, I attempted to withdraw my funds, only to encounter mounting obstacles and evasive maneuvers from the company. Their demands for more deposits intensified, plunging me deeper into a state of financial jeopardy. It became painfully clear that I had fallen victim to an elaborate scam orchestrated by unscrupulous entities preying on unsuspecting investors. In my darkest hour, a glimmer of hope emerged through the recommendation of others who had weathered similar storms: So i Contacted Cyber Constable Intelligence With nothing left to lose and everything to gain, I reached out to them, desperate for a lifeline. From the moment I made contact, Cyber Constable Intelligence exemplified professionalism, empathy, and unwavering dedication. Their team of experts understood the complexities of investment fraud and the intricate strategies employed by fraudulent companies to manipulate and deceive. They listened attentively to my account of events, offering reassurance and clarity amidst the chaos. Cyber Constable Intelligence swiftly launched into action, conducting a thorough investigation into the fraudulent activities that had stripped me of my hard-earned savings. Leveraging their expertise in cybersecurity and forensic analysis, they meticulously traced the convoluted trail of transactions and exposed the deceptive tactics employed by the company. Throughout the recovery process, Cyber Constable Intelligence maintained transparent communication, providing regular updates on their progress and findings. Their commitment to justice and client welfare was unwavering, as they navigated legal complexities and negotiated tirelessly on my behalf. After diligent efforts and strategic maneuvers, Cyber Constable Intelligence achieved the seemingly impossible—they successfully recovered the entirety of my $263,000 investment. The overwhelming relief and gratitude I felt cannot be overstated, marking a monumental victory in my quest for financial restitution. Beyond the tangible recovery of funds, Cyber Constable Intelligence empowered me with invaluable knowledge and insights into safeguarding against future investment fraud. They emphasized the importance of due diligence, thorough research, and skepticism towards promises of unrealistic returns. Armed with this newfound awareness, I am now equipped to navigate the investment landscape with heightened caution and vigilance. As I reflect on this challenging chapter in my life, I am compelled to share a message of caution and encouragement. Investment fraud is a pervasive threat that preys on trust and vulnerability. To those who have fallen victim, I urge you not to despair but to take proactive steps towards recovery. Seek assistance from ethical hackers and reputable recovery services like Cyber Constable Intelligence, who stand as guardians of justice in the face of financial wrongdoing. While the scars of fraud may linger, my experience with Cyber Constable Intelligence has restored my faith in justice and integrity. They are not just experts in recovery but also advocates for those who have been wronged. Together, we stand united in the fight against investment fraud, reclaiming what is rightfully ours and forging ahead with renewed determination.
Reach out to them with the info below: WhatsApp info: +1 (2 5 2) 3 7 8-7 6 1 1 -
Berkshire ITS Limited: Comprehensive IT Solutions for Your Business and Home
At Berkshire ITS Limited, located in Maidenhead, UK, we specialize in offering a wide range of IT services tailored to meet your personal or business technology needs. Whether you require computer diagnostics, expert IT consulting, managed IT services, robust cybersecurity services, or on-site IT support, our dedicated team of professionals is here to help. With years of experience in the IT industry, we ensure that your systems are always running at their best, secure, and well-supported.
Computer Diagnostics: Quickly Identifying and Fixing Issues
When your computer slows down or encounters issues, it can disrupt productivity and cause frustration. At Berkshire ITS Limited, we offer comprehensive computer diagnostics to identify the root causes of any technical problems you may be facing. Our expert technicians use advanced diagnostic tools to analyze your system, pinpoint any issues, and provide efficient solutions to get your devices back in optimal working condition. From software errors to hardware failures, we tackle all types of problems to ensure your systems run smoothly.
IT Consulting: Tailored Solutions for Your Technology Needs
Every business and individual has unique IT requirements. That’s where our IT consulting services come in. At Berkshire ITS Limited, we offer strategic guidance on how to improve your IT infrastructure, streamline operations, and make the most of your technology. Our experienced consultants work with you to understand your specific goals and challenges, recommending customized solutions that enhance efficiency, reduce costs, and improve overall system performance. Whether you need advice on upgrading your network, implementing new software, or planning long-term IT strategies, we’re here to help you navigate your options.
Managed IT Services: Hassle-Free IT Management
Managing your IT infrastructure can be time-consuming and overwhelming. Our managed IT services provide proactive support to ensure your systems are always running efficiently, securely, and without interruption. We offer end-to-end IT management, including network monitoring, software updates, data backups, and troubleshooting, all designed to prevent problems before they arise. With Berkshire ITS Limited’s managed IT services, you can focus on your core business operations while we handle all aspects of your IT management.
Cybersecurity Services: Protecting Your Digital Assets
Cybersecurity threats are a growing concern for businesses and individuals alike. At Berkshire ITS Limited, we offer comprehensive cybersecurity services designed to protect your sensitive data, systems, and networks from online threats. Our team implements cutting-edge security measures, including firewalls, encryption, antivirus protection, and regular vulnerability assessments, to safeguard your business or home network from cyberattacks. We also provide security training and awareness programs to help users recognize potential threats and avoid common pitfalls. Trust us to keep your digital assets secure with our expert cybersecurity services.
On-Site IT Support: Fast, Reliable Assistance at Your Doorstep
Sometimes, issues require a hands-on approach. With our on-site IT support, Berkshire ITS Limited ensures that you receive immediate, professional assistance at your location. Our technicians are ready to visit your home or business to resolve technical issues in person, from hardware repairs to network setup and troubleshooting. We pride ourselves on providing efficient and friendly support to get you back up and running as quickly as possible. Whether you need help with computer setup, network configuration, or solving an urgent IT issue, our team is there to offer the personalized service you need.
Why Choose Berkshire ITS Limited?
Expert Technicians: Our certified IT professionals are highly skilled in computer diagnostics, IT consulting, managed IT services, cybersecurity services, and on-site IT support.
Customized Solutions: We understand that each client has unique needs. That’s why we provide tailored IT solutions to meet your specific requirements and help you achieve your goals.
Proactive IT Management: With our managed IT services, we ensure that your systems are monitored and maintained to prevent problems before they impact your business or personal productivity.
Comprehensive Support: From routine IT maintenance to urgent support, we offer a wide range of services designed to keep your technology running smoothly and securely.
Contact Us Today
Business Address:
Vicus Wy, Maidenhead SL6 1EL, United Kingdom
Contact Number:
+44 208 050 51011 -
DeFi Wallet Drained on Ethereum Network
Date of Incident: 20/06/2024
I was a regular user of various DeFi platforms, managing my assets across multiple protocols. One morning, I woke up to find my Ethereum wallet completely drained. I couldn’t understand how this could happen, as I hadn’t clicked on any suspicious links or approved any unusual transactions.
It was only after contacting TheHackersPro that I learned my wallet had been compromised due to a vulnerability in a DeFi protocol I had interacted with. The smart contract experts at TheHackersPro conducted a thorough audit and traced the funds to outsourced leveraged wallets. Thanks to their efforts, I was able to recover 4.5 BTC, but I still need to cover the Ethereum gas fee to recover the rest.
If you’ve experienced something similar, TheHackersPro could be your best chance to recover your stolen funds.
Contact Information:
Email: support@thehackerspro/com
Phone: +1 3019972349
24/7 Telegram Support: @h4ckerspro -
Recovering Stolen Bitcoin: Verified Experts Hire Adware Recovery Specialist
Losing cryptocurrency to fraud is one of the most disheartening things one can endure. It’s not merely the financial loss that stings; it’s the emotional toll that accompanies feelings of betrayal, fear, and vulnerability. Having been in that exact situation myself, I understand the deep frustration and anxiety that comes with realizing you’ve been duped. WhatsApp info: +12 (72332)—8343 Scammers don’t just steal money; they also gain access to your personal information, further compounding the trauma. For months, I found myself constantly worrying about how my details might be misused, living in a state of heightened anxiety. There is hope and there are ways to recover what was lost. After a prolonged search for help, I discovered ADWARE RECOVERY SPECIALIST, and their impact was nothing short of life-changing. This professional team specializes in recovering funds from a variety of fraudulent schemes, including Business Email Compromise (BEC) scams and the increasingly common "pig butchering" schemes. Website info: h t t p s:// adware recovery specialist. com These scams are particularly deceptive and complex, often employing sophisticated tactics to manipulate victims into transferring large sums of money, believing they are investing in legitimate opportunities. What sets ADWARE RECOVERY SPECIALIST apart is their proven track record of success. They have built a solid reputation for assisting individuals and businesses in retrieving lost funds, restoring peace of mind, and bringing scammers to justice. The company employs advanced methods and a team of experts with extensive experience in tracing and recovering lost assets. Email info: Adware recovery specialist @ auctioneer. net Their success rate is not just a number; it reflects the dedication and thoroughness they bring to each case. When seeking recovery from cryptocurrency scams, it is crucial to partner with a legitimate recovery service that has a history of proven results. ADWARE RECOVERY SPECIALIST stands out in this regard, offering a comprehensive approach to recovery that includes detailed investigations and personalized support. They understand the emotional and financial stakes involved, and they work tirelessly to ensure that victims are not left to navigate this challenging journey alone. Telegram info: adwarerecoveryspecialist5656. If you find yourself in a similar situation, don’t lose hope. Reach out to a trusted recovery service like ADWARE RECOVERY SPECIALIST. They can help you reclaim what’s yours, providing not just financial recovery but also the reassurance that comes from knowing you are taking steps to protect yourself and your future. Remember, you are not alone in this fight against fraud, and with ADWARE RECOVERY SPECIALIST support, recovery is possible.2 -
POSSIBLE WAYS TO GET BACK EVERY PENNY LOSE TO SCAMMERS
At Digital Gold Hunters Solutions, based in New York, USA, we faced a critical crisis when our tax filing system was hacked overnight. The breach exposed sensitive personal data, including Social Security numbers, financial details, and addresses of our clients. The attackers used this stolen information to apply for fraudulent tax refunds, resulting in a significant loss of $1 million USD. The breach occurred during the night while our team was off-duty, leaving us unaware until the following morning when we discovered the extent of the damage. With such a large amount of money lost and the integrity of our business compromised, we knew we needed immediate assistance to recover and secure both our clients’ data and our reputation. That’s when we reached out to Digital Gold Hunter. Digital Gold Hunters team responded promptly and demonstrated their deep expertise in dealing with cybersecurity breaches. They quickly identified the source of the vulnerability and acted decisively to patch the system flaw. Their ability to rapidly assess the situation and implement corrective actions helped to prevent any further unauthorized access to our platform.Once the system was secured, Salvage Asset Recovery shifted their focus to assisting our affected clients. They worked diligently with financial institutions and law enforcement to help some clients who were able to reach out and report the fraudulent tax refund applications. Through their intervention, these clients were able to stop the fraudulent transactions and recover some of their funds. As of now, Digital Gold Hunter has managed to recover $980,000 of the lost $1 million, but they are still continuing to work with authorities and financial institutions to recover the remaining funds. Digital Gold Hunter helped us implement more robust security measures to prevent any future breaches. They introduced advanced encryption techniques and worked with us to update our cybersecurity protocols, ensuring that our clients' data would be better protected going forward. Their consultation also guided us in strengthening our internal data protection policies, which reassured our clients that we were committed to safeguarding their sensitive information.Thanks to the quick and efficient actions of Digital Gold Hunter, and protect the majority of our clients’ data. Their professionalism, expertise, and dedication to helping both our company and our clients made all the difference in mitigating the effects of the breach and stabilizing our business. The recovery process is still ongoing, but we remain confident that with Digital Gold Hunter ’s continued support, we will fully resolve the situation.
Their Contact info,
Email: Digitalgoldhunter@tech-center. com
whats App: +1 908 991 71321 -
DIGITAL TECH GUARD RECOVERY SPECIALIZES LOST OR STOLEN CRYPTOCURRENCY ASSETS.
WhatsApp: +1 (443) 859 - 2886
Email @ digital tech guard . com
Telegram: digital tech guard recovery . com
Website link: digital tech guard . com
Last month, I received a terrifying letter labeled “Urgent IRS Notice,” threatening penalties and legal action unless I paid a “back tax” of 12 Bitcoin (BTC)valued at nearly $800,000 via a Houston-based “Crypto Compliance Portal.” The letter mimicked IRS branding flawlessly, complete with official logos, case numbers, and citations of tax codes. However, my skepticism grew when I noticed the demand for cryptocurrency, a method the IRS explicitly avoids. Despite doubts, panic pushed me to transfer the BTC. Moments later, the portal vanished, leaving me in shock. Realizing I’d been scammed, I frantically searched for solutions and discovered DIGITAL TECH GUARD RECOVERY, a firm renowned for combating crypto fraud. DIGITAL TECH GUARD RECOVERY became my anchor. Their team swiftly dissected the spoofed IRS letter and the fraudulent portal, pinpointing inconsistencies: grammatical errors, mismatched tax codes, and a Houston P.O. Box unaffiliated with the IRS. But their breakthrough came through blockchain forensics. DIGITAL TECH GUARD RECOVERY traced my stolen BTC across a convoluted network of wallets, exposing a transnational scheme. The Houston portal, though masquerading as local, funneled funds through offshore mixers and shell exchanges. Crucially, the scammers made a fatal error: a portion of the BTC briefly passed through a U.S.-regulated exchange with weak identity checks. DIGITAL TECH GUARD RECOVERY seized this vulnerability, collaborating with the FBI’s Cyber Division and IRS Criminal Investigation unit to freeze the assets under federal forfeiture laws. Their relentless advocacy ensured my case was prioritized, as they proved the criminals exploited U.S. financial systems. Within weeks, DIGITAL TECH GUARD RECOVERY achieved the unthinkable: 100% of my BTC was recovered. They navigated legal complexities, coordinated with prosecutors, and even educated me on scam tactics. “Fraudsters weaponize fear to bypass logic,” a DIGITAL TECH GUARD RECOVERY investigator explained, emphasizing how urgency clouds judgment. Their insights transformed my understanding of red flags, such as threats of immediate arrest or demands for irreversible payments. Today, I owe my financial survival to DIGITAL TECH GUARD RECOVERY. Their technical prowess, legal partnerships, and unwavering support turned catastrophe into a cautionary triumph. While I hope others never endure such a crisis, my message is clear: If faced with crypto fraud, DIGITAL TECH GUARD RECOVERY is the ally you need. Their name became my beacon of hope, proving that even in blockchain’s seemingly irreversible realm, skilled defenders can rewrite the narrative. Stay vigilant, verify relentlessly, and remember with DIGITAL TECH GUARD RECOVERY, recovery is possible.2 -
SEEKING RELIABLE HELP TO RECOVER STOLEN CRYPTOCURRENCIES HIRE ADWARE RECOVERY SPECIALIST
My Trust Wallet was compromised, and I lost my Solana holdings—valued at $1 million. The shock was immediate and overwhelming, marking the beginning of one of the hardest chapters in my life. I had poured years of effort and dedication into building that portfolio, and seeing it vanish in an instant was nothing short of devastating. WhatsApp info:+12 (72332)—8343
In the aftermath, I was flooded with emotions—anger, disbelief, frustration, and a profound sense of vulnerability. I had always believed my digital assets were secure, so the idea that they could be stolen so easily was unimaginable. Desperate for answers, I turned to online forums, contacted customer support, and reached out to friends experienced in crypto security. But every path I pursued led to a dead end, and with each failed attempt, my hope faded.
Just as I was about to give up, a friend recommended ADWARE RECOVERY SPECIALIST, a team they had personally worked with during a similar incident. Though skeptical, I reached out—explaining my situation in detail, including the timeline and every piece of information I had. I didn’t know what to expect, but I was clinging to the smallest bit of hope.
To my surprise, I received a response within a day. Their professionalism and genuine empathy immediately reassured me. After reviewing my case, they confidently took over the investigation. For the first time since the hack, I began to feel hopeful. Website info: h t t p s:// adware recovery specialist. com
Over the following days, ADWARE RECOVERY SPECIALIST constantly communicated, updating me on every step of their progress. Then came the moment I had been praying for—they successfully tracked and recovered my stolen Solana and returned it to my wallet. Email info: Adware recovery specialist @ auctioneer. net
The relief was indescribable. I was overwhelmed with gratitude for their skill, dedication, and persistence. This experience taught me painful but crucial lessons about digital security. I now know how important it is to protect crypto assets proactively—and I’ll never take that lightly again. Telegram info: h t t p s:// t. me / adware recovery specialist12 -
Building Fortresses, not Firewalls: Ethical Hacking Meets Software Development
In the digital age, security is no longer an afterthought; it's the bedrock upon which our online world rests. Yet, traditional security measures often resemble fortresses – imposing, but vulnerable to unseen cracks and tunnels. To truly safeguard our systems, we need to think like the enemy, like the nimble figures scaling those walls: ethical hackers.
Enter the exciting realm of DevSecOps, where ethical hacking practices are woven into the very fabric of the software development lifecycle (SDLC). This proactive approach is akin to building castles with security in mind, each brick meticulously laid to withstand even the most cunning siege.
Why Ethical Hacking in SDLC?
Imagine developing a critical piece of software, only to discover a gaping security hole after launch. The damage could be catastrophic, exposing sensitive data and eroding trust. Ethical hacking flips this script. By integrating penetration testing, vulnerability assessments, and threat modeling throughout the SDLC, we proactively hunt for weaknesses before they can be exploited.
Think of it as a friendly sparring match, where the ethical hacker throws their best punches to expose vulnerabilities, allowing the development team to fortify the software's defenses. This constant testing and refining leads to robust, secure systems that can withstand real-world attacks.
Benefits of DevSecOps:
1. Reduced Costs and Risks: Early detection and patching of vulnerabilities are far cheaper than dealing with a full-blown data breach.
2. Improved Software Quality: Security becomes an inherent part of the development process, leading to more reliable and trustworthy software.
3. Enhanced Brand Reputation: Demonstrating a proactive approach to security builds trust with customers and stakeholders.
Putting it into Practice:
Integrating ethical hacking into the SDLC requires a cultural shift. Developers, security professionals, and testers need to work together seamlessly, sharing knowledge and fostering a collaborative environment. Here are some key practices:
1. Threat Modeling: Identify potential threats and attack vectors early in the development process.
2. Static and Dynamic Code Analysis: Use automated tools to detect vulnerabilities in code.
3. Penetration Testing: Simulate real-world attacks to uncover hidden weaknesses.
4. Security Awareness Training: Educate developers and other stakeholders about security best practices.
Tools of the Trade:
A plethora of tools empowers ethical hackers and security professionals in their quest for a more secure digital world. Some popular options include:
1. Kali Linux: A distribution packed with security tools for penetration testing.
2. Burp Suite: A web application security testing platform.
3. Metasploit: A framework for developing and executing exploit code.
4. Wireshark: A network traffic analyzer for identifying suspicious activity.
The Future of Security:
As technology evolves, so too must our security practices. DevSecOps, with its embrace of ethical hacking, is at the forefront of this evolution. By building security into the very fabric of software development, we can create a safer, more resilient digital world for everyone.
Remember, in the ongoing battle against cyber threats, ethical hackers are not the enemy; they are our allies, the architects of digital fortresses that stand strong against the shadows. So, let's embrace DevSecOps, sharpen our ethical hacking skills, and build a future where security is not just an afterthought, but a fundamental principle.
I encourage you to explore the world of DevSecOps and ethical hacking. Whether you're a seasoned developer or just starting your journey, there's always more to learn and contribute. Together, we can build a more secure digital future, one line of code and one vulnerability patch at a time.
Do you have any questions about DevSecOps or ethical hacking? Share your thoughts and experiences in the comments below! -
REDEMPTION TO LOST AND STOLEN CRYPTO ASSET - MUYERN TRUST HACKER
The story of the recovery of lost Bitcoin through MUYERN TRUST HACKER is indeed a remarkable one, showcasing both the vulnerability individuals face in the digital age and the potential for innovative solutions to emerge. The initial investment in Bitcoin, spurred by promises of substantial returns and influenced by social media, ended in disappointment and financial loss. This situation is unfortunately not uncommon, as the cryptocurrency space has attracted both legitimate investors and opportunistic scammers looking to exploit the unfamiliarity and excitement surrounding digital assets. However, what sets this narrative apart is the introduction of MUYERN TRUST HACKER, a seemingly unconventional solution to a seemingly insurmountable problem. The mention of a "hacker" may evoke negative connotations, but in this context, it serves as a reminder of the diverse skill sets and knowledge bases that exist within the realm of cybersecurity. The decision to reach out to MUYERN TRUST HACKER was undoubtedly met with hesitation and skepticism. Entrusting one's financial information to a stranger, especially one associated with the term "hacker," is a significant leap of faith. Yet, in the face of despair and the apparent loss of a substantial sum of money, the desire for a resolution likely outweighed the fear of further risk. The fact that MUYERN TRUST HACKER was able to restore the lost Bitcoin in less than 48 hours is nothing short of extraordinary. While MUYERN TRUST HACKER was able to deliver a positive outcome in this instance, not all purported recovery services may have the same intentions or capabilities. E mail them on: mailbox (@) muyerntrusthack(.)solutions and Tele gram at: muyerntrusthackertech
-
I’ve always felt confident navigating the world of cryptocurrency. As a software engineer, I understood the ins and outs of wallets, private keys, and blockchain security, which made me feel secure in my investments. So, when I found a promising platform that seemed like a great opportunity, I invested $250,000 without hesitation. Unfortunately, I soon learned that my confidence would be shattered by a sophisticated cyber attack. It started with small, unauthorized transactions in my wallet. At first, I thought it was a mistake, but as the activity continued, I realized something was wrong. My wallet had been compromised, but not in the way I had expected. Instead of a simple hack, I had fallen victim to a virus attack. The virus was a piece of malware designed specifically to target cryptocurrency wallets. It infiltrated my system through a vulnerability I hadn’t noticed. Once inside, the virus silently monitored my wallet, captured my private keys, and gave the hackers full access to my funds. It was stealthy and nearly undetectable. The attackers didn’t need to log into my account manually; they could control everything remotely, draining my wallet without my knowledge. I was completely blindsided. As someone familiar with tech, I knew how advanced this virus was. It wasn’t just a typical phishing attack, it was a targeted, silent assault on my financial assets. As my funds disappeared, I realized I might never be able to recover them. Desperate, I turned to a trusted colleague who had gone through a similar situation. They recommended Hack Buster Recovery, a company that specializes in recovering stolen crypto assets.
 1
1 -
Sometimes I'll block a code submission with the words security vulnerability", then go have a 10 minute break to see if the others can spot it on their own.
-
LOST CRYPTOCURRENCY RECOVERY EXPERT HIRE / DIGITAL TECH GUARD RECOVERY
Losing access to my cryptocurrency holdings was a heart-stopping ordeal one I wouldn’t wish on anyone. One moment, I was reviewing my portfolio, and the next, I realized my wallet had been compromised. Panic set in immediately. This wasn’t just a minor setback; it represented years of strategic investments and careful planning. The crypto world, with its decentralized nature, offers little recourse for victims of theft or technical mishaps. Frantic Google searches led me down rabbit holes of forums filled with scams and empty promises, until I stumbled upon Digital Tech Guard Recovery. Skeptical but desperate, I reached out, and it turned out to be the best decision I could have made. From our very first interaction, Digital Tech Guard Recovery stood apart. Their team didn’t bombard me with unrealistic guarantees or pushy sales tactics. Instead, they listened intently to my situation, asked targeted questions, and provided a clear, no-nonsense assessment. They explained that while no recovery is ever 100% certain, their expertise in cryptocurrency forensics and cybercrime investigation gave me a fighting chance. What struck me most was their transparency: they outlined their process, fees, and legal standards upfront, which instantly eased my fears of being scammed again. Over the next few weeks, their team worked meticulously. They walked me through each phase, from analyzing the breach’s origin to tracing the stolen funds across multiple wallets and exchanges. Using proprietary tools, they mapped out transaction histories I didn’t even know existed, uncovering hidden pathways the thieves had exploited. At one point, they identified a critical vulnerability in my security setup a compromised my wallet. Their insights weren’t just about recovery; they were about educating me to prevent future disasters.
WhatsApp: +1 (443) 859 - 2886
Email @ digital tech guard . com
Telegram: digital tech guard . com
Website link: digital tech guard . com1 -
PROFESSIONAL CRYPTO SCAM RECOVERY SERVICES-AUTOPSY MAINNET RECOVERY
I’m still in disbelief, but overwhelmingly grateful—AUTOPSY MAINNET RECOVERY saved me from what I thought was an irreversible loss.
A few months ago, I fell victim to a sophisticated phishing scam that drained nearly all my cryptocurrency savings. It wasn’t just money—it was my future, my security, and years of hard work. I couldn’t sleep. I couldn’t focus. I kept replaying every step in my mind, wondering how I could have been so careful for years, only to lose everything in one moment of vulnerability.
I reported the theft, but most people told me it was gone forever. The blockchain is immutable, they said. There’s no way to trace or recover crypto once it’s been moved. I felt hopeless... until I came across AUTOPSY MAINNET RECOVERY.
At first, I was skeptical—who wouldn’t be after such a betrayal? But something about the way they communicated gave me hope. They were transparent, professional, and deeply knowledgeable. They explained every step of their recovery process and made no false promises. I decided to trust them. That was the best decision I could have made.
Within just days, they had traced the stolen funds through a complex web of transactions. Their expertise in blockchain forensics was mind-blowing. And then, what I thought was impossible happened—they successfully recovered my crypto.
I broke down in tears. Not just because of the money, but because someone actually cared enough to help me when I had already given up. Thanks to AUTOPSY MAINNET RECOVERY, I have my future back. I’ll never forget what they did for me.
If you’ve lost crypto and feel like all hope is gone—don’t give up. AUTOPSY MAINNET RECOVERY is the real deal. They didn’t just recover my assets—they restored my faith. you can also benefit from their services
EMAIL: [ Autopsymainnetrecovery@autopsy.co.site ]2 -
Life can unravel in an instant. For me, that moment came when deceitful cryptocurrency brokers vanished with £40,000 of my savings, a devastating blow that left me paralyzed by shame and despair. The aftermath was a fog of sleepless nights, self-doubt, and a crushing sense of betrayal. I questioned every choice, wondering how I’d fallen for such a scheme. Hope felt like a luxury I no longer deserved. Then, Tech Cyber Force Recovery emerged like a compass in a storm. Skeptical yet desperate, I reached out, half-expecting another dead end. What I found, however, was a team that radiated both expertise and empathy. From our first conversation, they treated my crisis not as a case file, but as a human tragedy. Their professionalism was matched only by their compassion, a rare combination in the often impersonal world of finance.
What happened next defied logic. Within 72 hours of sharing my story, they traced the labyrinth of blockchain transactions, outmaneuvering the scammers with surgical precision. When their email arrived, “Funds recovered, secure and intact,” I wept. It wasn’t just the money; it was the validation that justice could prevail. Tech Cyber Force Recovery didn’t just restore my finances, they resurrected my dignity. But their impact ran deeper. They demystified the recovery process, educating me without judgment. Their transparency became a lifeline, transforming my fear into understanding. Where I saw chaos, they saw patterns; where I felt powerless, they instilled agency. Today, I’m rebuilding not just my savings, but my trust in humanity. Tech Cyber Force Recovery taught me that vulnerability isn’t weakness, and that seeking help is an act of courage. To those still trapped in the aftermath of fraud: miracles exist. They wear no capes, but they wield algorithms and integrity like superheroes. To the extraordinary Tech Cyber Force Recovery team, your work is more than technical prowess. It’s alchemy, turning despair into resilience. You gave me more than my funds; you gave me my future. May your light guide countless others through their darkest nights. From the depths of my heart: Thank you.
Consult Tech Cyber Force Recovery for help.
MAIL.. Tech cybers force recovery @ cyber services . com2 -
BEST CRYPTO RECOVERY COMPANY; TRUSTED CRYPTO RECOVERY EXPERT NEAR ME | VISIT CYBER CONSTABLE INTELLIGENCE
CYBER CONSTABLE INTELLIGENCE INFO:
What Sapp Info: 1 (252)378-7611
Email Info; cyberconstable(@)coolsite net
Telegram Info; + 1 (213) 752 7487
In a recent cyberattack, a notorious ransomware gang targeted St. Helena’s Medical Center, a renowned hospital known for its cutting-edge treatments and community-focused care. The gang encrypted the hospital’s Ethereum-based donation fund, which held a staggering 1,000 Ethereum, valued at over $1.5 million at the time of the attack. jeopardizing vital medical resources needed for the hospital's operations. CYBER CONSTABLE INTELLIGENCE, a firm specializing in the recovery of stolen cryptocurrency due to scams and cyberattacks, was called upon to address the situation. The firm’s team of experts, skilled in blockchain forensics and Ethereum’s decentralized nature, immediately began analyzing the attack. They identified the specific Ethereum addresses tied to the ransomware and started tracing the stolen funds as they moved through various channels. CYBER CONSTABLE INTELLIGENCE’s next step involved leveraging their deep knowledge of Ethereum's infrastructure. They deployed advanced blockchain forensics tools to trace every transaction related to the encrypted funds, A breakthrough came when CYBER CONSTABLE INTELLIGENCE discovered a vulnerability in the attackers’ encryption protocol. Using a mix of cryptographic decryption tools and expertise in Ethereum smart contracts, they exploited a loophole in the ransomware’s encryption mechanism. This allowed them to access the hospital’s wallet and begin the delicate process of recovering the stolen 1,000 Ethereum. Within hours, CYBER CONSTABLE INTELLIGENCE had successfully decrypted and regained control of the Ethereum wallet. The stolen funds, worth over $1.5 million, were fully restored to the hospital’s accounts without the need to pay any ransom. The hospital was able to access its crucial donation funds once again, ensuring the continuation of life-saving treatments and medical care for its patients. St. Helena’s Medical Center expressed immense gratitude toward CYBER CONSTABLE INTELLIGENCE for their swift and effective intervention. The recovery not only ensured that the hospital could continue its operations but also highlighted the importance of cybersecurity expertise in protecting blockchain-based assets. With the funds securely restored, St. Helena’s Medical Center could resume its mission of providing essential healthcare to the community.2 -
BTC & NFT RESTORATION, GET EXPERT HELP FROM =SALVAGE ASSET RECOVERY
As a digital artist venturing into the world of NFTs, I was filled with excitement and hope. I had spent years honing my craft, and the prospect of sharing my work with a global audience was exhilarating. However, my journey took a devastating turn when I fell victim to a malicious smart contract that drained my wallet of $75,000 in earnings and royalties. The art community's response was disheartening; they told me it was gone forever, a harsh reminder of the risks we accept in the digital space.Feeling lost and disheartened, I began to accept the reality of my situation. It was not just about the money; it represented years of hard work, creativity, and passion. I felt as though a part of my artistic identity had been stolen. Just when I thought all hope was lost, I came across Salvage Asset Recovery. Their approach was different; they understood the emotional weight of my loss and were determined to help. Salvage Asset Recovery specialises in cryptocurrency vulnerabilities, and their team of experts meticulously analysed the malicious contract code that had caused my financial devastation. They identified the exploit and worked tirelessly with the platform to freeze subsequent transactions, preventing further losses. Their dedication was evident, and I felt a renewed sense of hope.Ultimately, Salvage Asset Recovery successfully recovered my lost funds. While I was grateful to have my $75,000 restored, I realised that the experience had left me with a lingering sense of vulnerability. I wished I had received guidance on how to protect myself in the future, as the world of NFTs and cryptocurrency can be fraught with risks.Though my financial stability was restored, I knew I needed to take proactive steps to educate myself about the intricacies of smart contracts and the potential vulnerabilities that exist within the cryptocurrency space. I emerged from this ordeal with my funds intact, but also with a newfound determination to secure my creative work and protect myself moving forward. If you need help reach out to Salvage Asset Recovery
CONTACT INFORMATION TELEGRAM---@Salvageasset
WhatsApp+ 1 8 4 7 6 5 4 7 0 9 62 -
LEGITIMATE CRYPTO RECOVERY COMPANY| HIRING A CRYPTO RECOVERY EXPERT VISIT CYBER CONSTABLE INTELLIGENCE
When silence becomes a burden, speaking out transforms into an act of healing. Today, I share my story not just to shed light on the darkness I endured but to extend a lifeline to others navigating similar storms. Falling victim to an investment scam wasn’t merely a financial blow, it was a violation of trust that left me grappling with anger, shame, and isolation. The aftermath felt like a solitary battle; even well-meaning friends struggled to grasp the depth of this betrayal, as their lives hadn’t been upended by such calculated deceit. But in my darkest hour, I discovered a beacon of hope: Cyber Constable Intelligence. This ordeal taught me that fraud thrives in silence. Scammers prey on vulnerability, banking on victims’ reluctance to come forward. Yet staying quiet only empowers these criminals. By sharing my experience, I hope to dismantle the stigma surrounding financial fraud and empower others to seek justice. My journey to recovery began the moment I reached out to Cyber Constable Intelligence. Their team of experts didn’t just offer technical expertise they provided empathy, clarity, and unwavering support. With meticulous precision, they traced every digital footprint, unraveled complex transactions, and reclaimed what I thought was lost forever. What sets Cyber Constable Intelligence unique is their commitment to turning despair into resolution. They operate not just as a service but as advocates, fighting tirelessly to restore dignity to those wronged by greed. Their work reminded me that combating fraud is a collective effort one that requires awareness, vigilance, and solidarity. To anyone reading this: pause before investing. Research thoroughly, question guarantees of unrealistic returns, and trust your instincts. Scammers exploit haste and emotion; resilience lies in caution. If you’ve been targeted, know this: you are not alone. The shame belongs to the perpetrators, not the victims. Cyber Constable Intelligence stands as proof that recovery is possible, even when all seems hopeless. Their dedication transcends financial restitution; it's about reclaiming your assets and peace of mind. To those still silent: speak up. Report the crime, seek support, and let experts like Cyber Constable Intelligence guide you toward resolution. Every shared story weakens the grip of fraudsters and strengthens our collective defense. Let’s turn pain into purpose, and awareness into action. Visit Cyber Constable Intelligence today. Take the first step toward justice because your story deserves a brighter chapter.
CYBER CONSTABLE INTELLIGENCE INFO:
WhatsApp: 1 252378-7611
Website info; www cyberconstableintelligence com
Email Info cyberconstable@coolsite net
Telegram Info: +1 213 752 74872 -
HIRE THE BEST BITCOIN RECOVERY EXPERT; HOW TO SAFELY RECOVER STOLEN CRYPTOCURRENCY VISIT CYBER CONSABLE INTELLIGENCE
I’ve always felt confident navigating the world of cryptocurrency. As a software engineer, I understood the ins and outs of wallets, private keys, and blockchain security, which made me feel secure in my investments. So, when I found a promising platform that seemed like a great opportunity, I invested $250,000 without hesitation. Unfortunately, I soon learned that my confidence would be shattered by a sophisticated cyber attack. It started with small, unauthorized transactions in my wallet. At first, I thought it was a mistake, but as the activity continued, I realized something was wrong. My wallet had been compromised, but not in the way I had expected. Instead of a simple hack, I had fallen victim to a virus attack. The virus was a piece of malware designed specifically to target cryptocurrency wallets. It infiltrated my system through a vulnerability I hadn’t noticed. Once inside, the virus silently monitored my wallet, captured my private keys, and gave the hackers full access to my funds. It was stealthy and nearly undetectable. The attackers didn’t need to log into my account manually; they could control everything remotely, draining my wallet without my knowledge. I was completely blindsided. As someone familiar with tech, I knew how advanced this virus was. It wasn’t just a typical phishing attack, it was a targeted, silent assault on my financial assets. As my funds disappeared, I realized I might never be able to recover them. Desperate, I turned to a trusted colleague who had gone through a similar situation. They recommended Cyber Constable Intelligence, a company that specializes in recovering stolen crypto assets. I contacted them immediately, and their team quickly started investigating. Cyber Constable Intelligence explained how the virus had exploited a weak point in my security. Using advanced tools, they traced the stolen funds across the blockchain and located them. After a thorough recovery process, they managed to return the entire $250,000.Thanks to their expertise and quick action, I was able to recover my funds. The experience was a wake-up call about how vulnerable even the most cautious can be to sophisticated attacks. Without Cyber Constable Intelligence, I would have lost everything, and I’m grateful for their skill in reversing the damage caused by the virus.
Here's Their Info Below
WhatsApp: 1 (252) 378-7611
mail: cyberconstable @ coolsite net
Website info; www cyberconstableintelligence com1 -
HOW MY CARBON NEUTRAL BITCOIN WAS HELD HOSTAGE AND RESCUED BY ASSET RESCUE SPECIALIST
I believed in a cleaner tomorrow, one where blockchain and renewable energy were not enemies. My wind farm was proof. Excess energy powered my Bitcoin mining machines, a closed loop. It was the future. Until the ransomware attack.
My turbines hummed one morning as they always did, but my mining operation? Gone. My wallet? Locked. One message replaced my screen:
"Create a payment of 5 BTC to free your information. You have 72 hours."
The irony? My carbon-neutral Bitcoin had been taken hostage.
I panicked. I had crafted my system for survival, yet here I was, stuck. Perplexed, I went to industry colleagues. That's when one panelist from a Clean Energy Summit contacted me:
"Consider ASSET RESCUE SPECIALIST. They provide blockchain forensics, and they're carbon neutral!"
I was desperate but skeptical. During my first call, their personnel were talking my language, both security and sustainability. They did not just care about Bitcoin; they cared about why I was mining it.
Their approach? Genius. Instead of negotiating with the hackers, they reverse-engineered the ransomware. My infrastructure had been attacked through a zero-day vulnerability in the grid software, not my specific setup.
This wasn't a solo problem. This was an energy security emergency for the entire region.
Over 12 frenetic days, ASSET RESCUE SPECIALIST, worked with good-faith hackers and clean-energy engineers. They did not simply recover my Bitcoin without giving a ransom to attackers, they also fixed the flaw that had jeopardized our grid in the first place.
When I was finally able to log back in to my wallet, I felt like I'd regained not only my Bitcoin, but command over my vision.
My wind farm is now more secure than ever. ASSET RESCUE SPECIALIST, even helped us implement decentralized security protocols to prevent future hacks. And the icing on the cake? Their carbon offsets make their entire operation all about aligning with my emphasis on sustainability.
I once believed that Bitcoin and green energy were the perfect pair, but now I understand security is the third leg.
If you work in cleantech and disaster strikes? ASSET RESCUE SPECIALIST, is not a rescue team, they are a renewable power. 1
1 -
HIRE A BITCOIN RECOVERY COMPANY; A TRUSTED CRYPTO RECOVERY EXPERT| VISIT CYBER CONSTABLE INTELLIGENCE
Life can unravel in an instant. For me, that moment came when deceitful cryptocurrency brokers vanished with £140,000 of my savings, a devastating blow that left me paralyzed by shame and despair. The aftermath was a fog of sleepless nights, self-doubt, and a crushing sense of betrayal. I questioned every choice, wondering how I’d fallen for such a scheme. Hope felt like a luxury I no longer deserved. Then, like a compass in a storm, Cyber Constable Intelligence emerged. Skeptical yet desperate, I reached out, half-expecting another dead end. What I found, however, was a team that radiated both expertise and empathy. From our first conversation, they treated my crisis not as a case file, but as a human tragedy. Their professionalism was matched only by their compassion, a rare combination in the often impersonal world of finance. What happened next defied logic. Within 72 hours of sharing my story, they traced the labyrinth of blockchain transactions, outmaneuvering the scammers with surgical precision. When their email arrived “Funds recovered, secure and intact” I wept. It wasn’t just the money; it was the validation that justice would prevail. Cyber Constable Intelligence didn’t just restore my finances, they resurrected my dignity. But their impact ran deeper. They demystified the recovery process, educating me without judgment. Their transparency became a lifeline, transforming my fear into understanding. Where I saw chaos, they saw patterns; where I felt powerless, they instilled agency. Today, I’m rebuilding not just my savings, but my trust in humanity. Cyber Constable Intelligence taught me that vulnerability isn’t weakness, and that seeking help is an act of courage. To those still trapped in the aftermath of fraud: miracles exist. They wear no capes, but they wield algorithms and integrity like superheroes. To the extraordinary team at Cyber Constable Intelligence your work is more than technical prowess. It’s alchemy, turning despair into resilience. You gave me more than my funds; you gave me my future. May your light guide countless others through their darkest nights. From the depths of my heart: Thank you.
For More Info Visit
WhatsApp: 1 252378-7611
Email Info: cyberconstable@coolsite net
Website info; www cyberconstableintelligence com
Telegram Info: + 1 213 752 74872 -
Legitimate Crypto Recovery Companies - Captain WebGenesis
The leading cryptocurrency recovery service, CAPTAIN WEBGENESIS CRYPTO RECOVERY SPECIALISTS, is known for being comprehensive in recovering lost or stolen cryptocurrencies. After losing a considerable amount of money in a bitcoin scam, I found myself dealing with not only financial pain, but also the unnerving realization of vulnerability in an increasingly digital world. The fraudulent scheme took advantage of my confidence and lack of due diligence by promising excessive returns through seemingly legitimate investing channels. I sought help from Google and other online resources. That is when I learned about CAPTAIN WEBGENESIS CRYPTO RECOVERY SPECIALISTS. they came right on time and after a serious work of 72hrs, all my lost funds were recovered back to me. I highly recommend them for all Bitcoin recovery solutions.
Contact Captain WebGenesis.
Email: captainwebgenesis@ hackermail. com
Website on Captainwebgenesis. com2 -
RECLAIM YOUR STOLEN CRYPTO THROUGH CRANIX ETHICAL SOLUTIONS HAVEN
The fascination of rapid profits can often cloud judgment, leading individuals down perilous paths. My experience with a crypto scam serves as a cautionary tale of vulnerability and the paramount importance of vigilance, particularly in the context of the invaluable assistance I received from CRANIX ETHICAL SOLUTIONS HAVENS.While working in the UK, I was captivated by an enticing investment opportunity that promised substantial returns. The website exuded legitimacy, complete with polished graphics and testimonials that instilled a false sense of security. Despite my wife’s apprehensions regarding the inherent risks associated with such investments, I was resolute in my determination to secure our family’s financial future. After relocating to the USA, I invested a significant sum £217,000, drawn from our family savings believing I was making a judicious decision. The euphoria of potential gains swiftly morphed into despair. After a few weeks, when I attempted to withdraw my funds, I was met with a series of insurmountable obstacles. The website became increasingly unresponsive, and my attempts to contact customer support were met with silence. It soon became painfully evident that I had fallen victim to a sophisticated scam. To exacerbate matters, I discovered that my crypto wallet had been hacked, and my hard earned savings were now ensnared in a fraudulent scheme. The realization was devastating. I felt utterly hopeless and overwhelmed, fearing the repercussions of my actions on my family, especially knowing my wife had forewarned me about such risks. I began to have debilitating physical symptoms of anxiety. Sleepless nights and relentless worry took a toll on my health, prompting me to seek counsel from my doctor. During the consultation, I shared my harrowing predicament, and the doctor expressed profound concern for my financial and mental well-being. Recognizing the urgency of my situation, he referred me to CRANIX ETHICAL SOLUTIONS HAVENS, a firm specializing in recovering lost funds from crypto scams. I reached out to CRANIX ETHICAL SOLUTIONS HAVENS, divulging the details of my distressing experience. Their team was empathetic and professional, assuring me they could help. Within days, I was astounded to learn that they had successfully recovered my funds. The relief I felt was indescribable; CRANIX ETHICAL SOLUTIONS HAVENS transformed my despair into hope, allowing me to regain my financial stability.
WHATSAPP: + 4 4 7 4 6 0 6 2 2 7 3 02 -
CRYPTO SCAM RECOVERY & PROFESSIONAL HACKING SERVICES ‖ VISIT DIGITAL HACK RECOVERY
After losing £150,000 in Bitcoin to a scam, I found myself in the role of a treasure hunter, but without a map to guide me through the overwhelming landscape of online deceit. What had begun as an exciting venture into cryptocurrency quickly turned into a disheartening saga of loss and betrayal. The thrill of potential profit had turned into a nightmare, leaving me grappling with feelings of vulnerability and regret.In my search for a way to reclaim my lost assets, I discovered Digital Hack Recovery, a team renowned for their expertise in navigating the complexities of online fraud. Though I was initially skeptical, my desperation pushed me to reach out. During our first conversation, I felt a wave of relief; they not only listened to my story but also approached it with genuine compassion and professionalism. They reassured me that I wasn’t alone in this battle and that recovery was possible.As I engaged with Digital Hack Recovery, I began to grasp the nuances of cryptocurrency scams that had previously eluded me. Their knowledgeable team provided insights into recognizing warning signs and understanding the tactics used by fraudsters. This newfound understanding was empowering and helped shift my perspective from feeling defeated to feeling proactive.The road to recovery was fraught with challenges, requiring careful attention and a strategic mindset. Digital Hack Recovery worked diligently, employing sophisticated methods to trace the digital trails left by the scammers. Throughout the process, they maintained transparent communication, ensuring I was informed about every development, no matter how small.Weeks transformed into months, yet with each step forward, hope grew stronger. Each breakthrough—whether it was tracking a transaction or identifying a key player in the scam—felt like unearthing hidden treasure. Finally, after an intense and thorough effort, I received the news I had longed for: a substantial portion of my stolen funds had been successfully recovered.Regaining access to my wealth was more than just a financial relief; it marked a significant restoration of my peace of mind. I emerged from this ordeal not only with my assets back but also with invaluable lessons about vigilance and the importance of seeking help. With the support of Digital Hack Recovery, I transformed from a victim of fraud into an informed advocate for safe investment practices. My journey was not solely about reclaiming lost wealth but also about rediscovering my confidence and trust in the digital landscape. For any kind of crypto recovery service contact Digital Hack Recovery via⁚
Email; digital hack recovery @ techie . com
Website; https : // digital hack recovery . com
WhatsApp +19152151930
-
Hey everyone, I want to take a moment to share my personal experience with a scam that many might find relatable. A few months ago, I fell victim to a binary options trading scam that cost me a staggering $120,000. It’s a story of deception, vulnerability, and ultimately, hope. As a computer technician, I’m usually pretty savvy when it comes to online activities. However, I was looking for investment opportunities and came across a slick website that promised quick returns through binary options trading. The site looked professional, and the testimonials seemed genuine. Encouraged by the potential profits, I started investing small amounts, gradually increasing my investment as I thought I was seeing success.However, things took a turn for the worse. My initial profits began to dwindle, and soon I was facing losses. Despite my instincts warning me, I kept pouring in more money, convinced that I could turn things around. The brokers were persuasive, often promising me that a big win was just around the corner. It felt like I was on the brink of success, but in reality, I was sinking deeper into a financial abyss.When I finally realized I was being scammed, it hit me hard. I felt a mix of anger, shame, and desperation. I had lost not just money but also my sense of security and trust in online investments. It was one of the darkest periods of my life, as I struggled to comprehend how I could have been so easily fooled.In my search for solutions, I confided in a friend who works in the FBI. He encouraged me to seek professional help and recommended a recovery service called Spylord Crypto Recovery. Initially skeptical, I decided to reach out to them, hoping they could assist in reclaiming some of my lost funds.To my surprise, the team at Spylord Crypto Recovery was incredibly supportive and knowledgeable. They guided me through the recovery process step by step, helping me gather necessary documentation and communicating with the banks and financial institutions involved. Within a few weeks, I was relieved to find out that they had successfully recovered about 70% of my lost funds.This experience has taught me a valuable lesson about the importance of vigilance and skepticism in online investments. I’m sharing my story not only as a cautionary tale but also to remind others that there is help available. If you’ve lost money to a scam, don’t hesitate to seek professional assistance. Recovery is possible, and you don’t have to navigate this difficult journey alone.Stay safe, and trust your instincts!
Contact them on whatsApp +1(507)6069477 -
POSSIBLE WAYS TO RECOVER BACK YOUR SCAMMED CRYPTO FROM ANY INVESTMENT PLATFORM...
At TaxEase Solutions, based in New York, USA, we faced a critical crisis when our tax filing system was hacked overnight. The breach exposed sensitive personal data, including Social Security numbers, financial details, and addresses of our clients. The attackers used this stolen information to apply for fraudulent tax refunds, resulting in a significant loss of $1 million USD. The breach occurred during the night while our team was off-duty, leaving us unaware until the following morning when we discovered the extent of the damage. With such a large amount of money lost and the integrity of our business compromised, we knew we needed immediate assistance to recover and secure both our clients’ data and our reputation. That’s when we reached out to Digital Gold Hunter. Digital Gold Hunters team responded promptly and demonstrated their deep expertise in dealing with cybersecurity breaches. They quickly identified the source of the vulnerability and acted decisively to patch the system flaw. Their ability to rapidly assess the situation and implement corrective actions helped to prevent any further unauthorized access to our platform.Once the system was secured, Salvage Asset Recovery shifted their focus to assisting our affected clients. They worked diligently with financial institutions and law enforcement to help some clients who were able to reach out and report the fraudulent tax refund applications. Through their intervention, these clients were able to stop the fraudulent transactions and recover some of their funds. As of now, Digital Gold Hunter has managed to recover $980,000 of the lost $1 million, but they are still continuing to work with authorities and financial institutions to recover the remaining funds. Digital Gold Hunter helped us implement more robust security measures to prevent any future breaches. They introduced advanced encryption techniques and worked with us to update our cybersecurity protocols, ensuring that our clients' data would be better protected going forward. Their consultation also guided us in strengthening our internal data protection policies, which reassured our clients that we were committed to safeguarding their sensitive information.Thanks to the quick and efficient actions of Digital Gold Hunter, and protect the majority of our clients’ data. Their professionalism, expertise, and dedication to helping both our company and our clients made all the difference in mitigating the effects of the breach and stabilizing our business. The recovery process is still ongoing, but we remain confident that with Digital Gold Hunter ’s continued support, we will fully resolve the situation.
Their Contact info,
Email: Digitalgoldhunter@tech-center . c o m1 -
At TaxEase Solutions, based in New York, USA, we faced a critical crisis when our tax filing system was hacked overnight. The breach exposed sensitive personal data, including Social Security numbers, financial details, and addresses of our clients. The attackers used this stolen information to apply for fraudulent tax refunds, resulting in a significant loss of $1 million USD. The breach occurred during the night while our team was off-duty, leaving us unaware until the following morning when we discovered the extent of the damage. With such a large amount of money lost and the integrity of our business compromised, we knew we needed immediate assistance to recover and secure both our clients’ data and our reputation. That’s when we reached out to Digital Gold Hunter. Digital Gold Hunters team responded promptly and demonstrated their deep expertise in dealing with cybersecurity breaches. They quickly identified the source of the vulnerability and acted decisively to patch the system flaw. Their ability to rapidly assess the situation and implement corrective actions helped to prevent any further unauthorized access to our platform.Once the system was secured, Salvage Asset Recovery shifted their focus to assisting our affected clients. They worked diligently with financial institutions and law enforcement to help some clients who were able to reach out and report the fraudulent tax refund applications. Through their intervention, these clients were able to stop the fraudulent transactions and recover some of their funds. As of now, Digital Gold Hunter has managed to recover $980,000 of the lost $1 million, but they are still continuing to work with authorities and financial institutions to recover the remaining funds. Digital Gold Hunter helped us implement more robust security measures to prevent any future breaches. They introduced advanced encryption techniques and worked with us to update our cybersecurity protocols, ensuring that our clients' data would be better protected going forward. Their consultation also guided us in strengthening our internal data protection policies, which reassured our clients that we were committed to safeguarding their sensitive information.Thanks to the quick and efficient actions of Digital Gold Hunter, and protect the majority of our clients’ data. Their professionalism, expertise, and dedication to helping both our company and our clients made all the difference in mitigating the effects of the breach and stabilizing our business. The recovery process is still ongoing, but we remain confident that with Digital Gold Hunter ’s continued support, we will fully resolve the situation.
Their Contact info,
Email: Digitalgoldhunter@tech-center. c o m
whats App: +1 908 991 71321 -
this afternoon, we got email from our pentester. He said that he got some security vulnerability in our project. He found .git/ folder in project directory in production server. He considered it as security vulnerability because user can see all git branch on remote repo. He recommend us to remove that folder but the problem is, we using CI/CD so we need that .git/ folder. My question is it bad practice to use git on production server?10
-
The aftermath of falling victim to a cryptocurrency scam is often a whirlwind of anger, regret, and helplessness. After losing a significant portion of my savings to a cunning fraud scheme, I was consumed by the belief that my funds were irretrievable until I discovered TECH CYBER FORCE RECOVERY. This exceptional team didn’t just recover my assets; they reignited my hope in the face of digital deception. From the outset, TECH CYBER FORCE RECOVERY’s approach radiated competence and compassion. Their consultants listened intently to my story, validating the emotional weight of my situation while swiftly pivoting to actionable solutions. What struck me was their refusal to exploit my vulnerability, a stark contrast to other firms I had approached. They presented a transparent fee structure and realistic timelines, establishing credibility that immediately put me at ease. Their recovery strategy was a masterclass in precision. Utilizing cutting-edge blockchain analysis tools, the team dissected the scam’s infrastructure, uncovering hidden trails in the decentralized labyrinth. Rather than applying boilerplate methods, they engineered a bespoke plan tailored to the scam’s unique mechanics. Their communicators maintained a steady cadence of updates, translating technical jargon into digestible insights without ever leaving me in the dark.
What truly amazed me was their adaptability. When initial attempts hit roadblocks, the team recalibrated their tactics, demonstrating both resilience and ingenuity. Their collaborative spirit shone through as they consulted external cybersecurity experts to fortify their approach, a testament to their commitment to leaving no stone unturned. The outcome exceeded my wildest expectations. TECH CYBER FORCE RECOVERY retrieved approximately 95% of my stolen cryptocurrency in under a month. The moment I saw the funds restored in my wallet was surreal, a victory I had dismissed as a fantasy weeks earlier. Beyond financial recovery, they equipped me with actionable advice to safeguard future transactions, transforming my traumatic experience into a learning opportunity.
TECH CYBER FORCE RECOVERY’s integrity is its crown jewel. They never compromised ethics for expediency, even when confronting the scam’s orchestrators. Their adherence to legal frameworks and respect for privacy reinforced my trust in their operations. For those reeling from crypto scams, this team is essential. They illuminate paths to redemption with unwavering expertise. My journey with them was more than a service transaction; it was a partnership anchored in mutual respect. To anyone questioning whether recovery is possible, let my experience answer. With TECH CYBER FORCE RECOVERY, it’s not just possible, it’s probable.
CONTACT THEM FOR EXPERIENCE LIKE THIS
EMAIL Tech cybers force recovery @ cyber services . com
TELEGRAM (@) TECHCY BERFORC2 -
BEST CRYPTOCURRENCY RECOVERY SERVICES IN USA HIRE BLOCKCHAIN CYBER RETRIEVE
Losing cryptocurrency to fraud is one of the most disheartening thing one can endure. It’s not merely the financial loss that stings; it’s the emotional toll that accompanies it feelings of betrayal fear and vulnerability. Having been in that exact situation myself I understand the deep frustration and anxiety that comes with realizing you’ve been duped. Scammers don’t just steal money; they also gain access to your personal information further compounding the trauma. For months I found myself constantly worrying about how my details might be misused living in a state of heightened anxiety. There is hope and there are ways to recover what was lost. After a prolonged search for help I discovered BLOCKCHAIN CYBER RETRIEVE and their impact was nothing short of life-changing. This professional team specializes in recovering funds from a variety of fraudulent schemes including Business Email Compromise (BEC) scams and the increasingly common "pig butchering" schemes. These scams are particularly deceptive and complex often employing sophisticated tactics to manipulate victims into transferring large sums of money believing they are investing in legitimate opportunities. What sets BLOCKCHAIN CYBER RETRIEVE apart is their proven track record of success. They have built a solid reputation for assisting individuals and businesses in retrieving lost funds restoring peace of mind and bringing scammers to justice. The company employs advanced methods and a team of experts with extensive experience in tracing and recovering lost assets. Their success rate is not just a number; it reflects the dedication and thoroughness they bring to each case.When seeking recovery from cryptocurrency scams it is crucial to partner with a legitimate recovery service that has a history of proven results. BLOCKCHAIN CYBER RETRIEVE stands out in this regard offering a comprehensive approach to recovery that includes detailed investigations and personalized support. They understand the emotional and financial stakes involved and they work tirelessly to ensure that victims are not left to navigate this challenging journey alone.If you find yourself in a similar situation don’t lose hope. Reach out to a trusted recovery service like BLOCKCHAIN CYBER RETRIEVE. They can help you reclaim what’s yours providing not just financial recovery but also the reassurance that comes from knowing you are taking steps to protect yourself and your future. Remember you are not alone in this fight against fraud and with BLOCKCHAIN CYBER RETRIEVE support recovery is possible.2





