Join devRant
Do all the things like
++ or -- rants, post your own rants, comment on others' rants and build your customized dev avatar
Sign Up
Pipeless API

From the creators of devRant, Pipeless lets you power real-time personalized recommendations and activity feeds using a simple API
Learn More
Search - "stolen"
-
Stolen from an awesome book but my new favourite line ;)
Someone: “Can you repair my computer, it`s not working anymore?”
Me: “Do you call Leonardo Dicaprio when your Tv is broken?”7 -
// sorry, again a story not a rant
Category->type = 'Story';
Category->save();
Today at work I got a strange email
'about your msi laptop'
(Some background information, a few months ago I went on vacation and left my work laptop at home. Long story short some one broke in and stole my msi laptop)
So this email had my interest. I opened it and the content was something like:
Hi! My name is x, I clean/repair laptops partime and I noticed your personal information on this laptop, normally people whipe their data from their laptop before selling so this is just a double check, if the laptop was stolen please call me on xxx
If I hear nothing I'll assume its alright and will whipe your data
So of course I immediately called him, after a conversation I informed the police who is now working on the case7 -
I fucked up again.
Someone needed a flashdrive for a presentation. Forgot that I keep personal code on on of them for backups (it's always nice when there is no reception to have an offline copy of my code, for instance when we go out into the bush or to remote areas).
I gave them my flashdrive. Forgot it had the code on.
Now someone at head office has taken my program, claimed it as their own - and has just earned themselves a decent amount of money (praised in the monthly company newsletter).
My program has been stolen (by my own stupidity) and butchered. It has been made into something that it was never intended to be.
Fuck that guy.13 -
So some guy decided to steal my laptop. I don't know if they thought my machine wasn't happy with me or what but whoever did that, all I can say is your time is coming motherfucker.
I will always miss you 😭😭13 -
Everything has to have MAC-Addresses. EVERYTHING!
(yes, I know. That's not one. But similar)
(stolen from https://twitter.com/istar_nil/...)
-
Little Jakob finds out you can open a js in (mobile) text editor.
Little Jakob finds an nether mod for early Minecraft PE editions (0.7 @ that time or so).
Little Jakob changes some number and vars and creates an Aether mod. (works the same like nether but other blocks&tools).
Little Jakob publishes it with screenshots in a video, gets 30.000+ views on youtube, mod reviews etc. There hasn't been an Aether mod before.
Little jakob feels badass.
2 years later I revited the video - and found out that the mod was licensed and I did something "illegal".
Seeked the internet and apologized to the original author (who was aware of this copy mod) - felt bad, he forgave me.1 -
Hire a Bitcoin Recovery Expert Solution: Best Crypto Recovery services | Captain WebGenesis
CAPTAIN WEBGENESIS stands out as an ideal cryptocurrency recovery expert, renowned for his exceptional proficiency in navigating the intricate realm of digital assets. With an impressive track record of successfully retrieving lost, stolen, or inaccessible cryptocurrencies, CAPTAIN WEBGENESIS has earned the trust of numerous individuals and organizations seeking to retrieve their valuable digital possessions.
How can I recover my stolen bitcoin from an investment scam?
What is the best recovery company to help me recover my stolen Bitcoins?
How to Hire a Hacker to Recover Stolen Crypto/Bitcoin?
Can a hacked crypto be recovered?
How can I recover my lost cryptocurrency within 24 hours?132 -
Gets run over by truck. Laptop in peaces. Insurrance needed to be sure it was actually broken. Sends laptop to a repair center. They tell me its broken. Repair center asks if I want my laptop back. I said: yes pls. Get laptop back. RAM stolen SSD stolen. Reee! They forgot to send it back..... I mean, you did not have to take out those parts to see it i broken.
 12
12 -
I hate this country!
This was the third time this month that the power cables got stolen. Looks like it is going to be takeouts and project planning on paper tonight. 11
11 -
Previously on devrant
https://www.devrant.io/rants/455085
This little shit is actually worried about her ideas getting stolen.
Do you think she'll pay me in stocks or pennies?
#INB4itsAShitIdea 14
14 -
Remember that fine girl that used to bedwet & was dirty in high school.
Then you met her recently, all looking hot & steamy.
That's PHP!
Stolen from the @unicodedeveloper om twitter2 -
The sell: “become a designer, change the world”
The reality: “become a designer, create Jira tickets for devs to fix stuff you’ve noticed” -
After two iPhones stolen in a month I decided to buy a Samsung and I really like it much more than iOS8
-
Necessary context for this rant if you haven't read it already: https://devrant.com/rants/2117209
I've just found my LUKS encrypted flash drive back. It was never stolen.. it somehow got buried in the depths of my pockets. No idea how I didn't look into my jacket for the entire time since that incident happened... But I finally found it back. None of my keys were ever compromised. And there's several backups that were stored there that have now been recovered too. Time to dd this flash drive onto a more permanent storage medium again for archival. Either way, it did get me thinking about the security of this drive. And I'll implement them on the next iteration of it.
For now though.. happy ending. So relieved to see that data back...
Full quality screenshot: https://nixmagic.com/pics/... 10
10 -
First of all how the fuck you are able to tell that MY password is one of many that have been stolen? How you are able to get those stolen passwords AND WHY YOU ARE EVEN ABLE TO COMPARE THEM?! Are you storing as plain text or just randomly salt all stolen passwords and chceck if they are in your base?
Now that is an INSTAdelete. 8
8 -
He read "Knowledge is a wealth that cannot be stolen"
Then saw me doing something with chmod and then he typed on his terminal
chmod 777 -R3 -
Steeling crime in our office
My mug is stolen and being used by a colleague
I am suspecting the newbies that started 2 weeks ago19 -
Was busy today doing some house work. Everything was normal till afternoon.
Me thinking of using laptop noticed that there was no laptop
My office laptop and another bag was stolen from my home .
It had most of the production details and source code. Running behind police for help now.
Informed my boss too about this incident.
Will update on what happens tomorrow in office.
Fuck that person who stole my office laptop and destroyed my Peace.8 -
work from home. desk and pretty much everything with it stolen in family dispute. I'm holding my laptop on a small nightstand. finally got a new pc today at least :/1
-
My december salary is delayed for a year (i’ll get paid around 2 or 3 january).
This broke af fireworks pic is how my new year looks like.
P.S Pic is stolen from facebook 4
4 -
What's the best Slav programming language?
Hint: czech motorcycle, typically red
Stolen from Life of Boris Q&A -
concerned parent: if all your friends jumped off a bridge would you follow them?
machine learning algorithm: yes.1 -
What's worse in an open office?
A) Music
B) People
(Shamelessly stolen from Twitter, credit @dustin)19 -
How to Recover Lost / Stolen BTC, Tether USDT - Go to OMEGA CRYPTO RECOVERY SPECIALIST HACKER
OMEGA CRYPTO RECOVERY SPECIALIST is a company that specializes in recovering lost or stolen Bitcoin and Tether USDT. Users can lose access to their funds by forgetting their private keys or passwords. or investment in a fake online platform.
Consult OMEGA CRYPTO RECOVERY SPECIALIST and thank me Later. Ever Recommended.
Webpage; ( omegarecoveryspecialist .c o m52 -
Client: *Sends beautiful screenshot*. I created the newsletter (template) with chatgpt.
Me: Nice. Did it add the header and the footer as well ?
Client : I'm asking him to do it right now.
Me: Ok.
As a trash developer I fear for my job.
/s
Ughh 15
15 -
Apple corp. (Apple) founded in London in January 1968 by the members of the Beatles.
So Apple name is also stolen 😂6 -
Legit questions!
How does facebook secures itself, we never heard news like facebook hacked, user data stolen, recently with ddos, twitter and other websites were affected but not Facebook?
Are they superhumans?9 -
Wakes up in the morning to find some fucking asshole has stolen my wifi reciever and I have a fucking deadline! Wtf is wrong with human beings nowadays?
Does anyone know a witch?2 -
fuck people who need to be hacked to care about security.
i hope everyone who used that early ap scores gets their credit cards stolen because they don't know how to use a vpn.8 -
Fuck the feelings of powerlessness and helplessness. when a friend comes crying for you for help with their hacked account and you keep asking them about what they did to protect it in the first place and they reply with nothing, no recovery email, no recover phone, no secondary verification, NOTHING. and you can do nothing but stand there and watch them cry while you can literally do nothing because there literally nothing you can do to retrieve their stolen accounts. FUCK BLACK HAT HACKERS.3
-
I'm fiddeling around with progressive web apps. I made something and hosted it on a subdomain. Today I made a typo and found my app on an other domain. All my assets and files are copied there. He even uses my SSL certificate.
It's not that spectacular. The app is nothing "revolutionary". It's just the first time it happend to me.
Have you ever found your code on other websites ? How did you react ?6 -
People on election day: "OMG a subset of the machines are not working!!"
People who work in IT every single day: "lol no shit."4 -
Great start to Halloween, phone has been stolen, and turned off so I can't track it. Oh, and I have no job so I can't get another right now. YAYAYAYAYAYAYAYAYAYAY3
-
Friend: where did you go to college, to do something like that?
Me: oh well I went to the university of my bedroom. -
Update on the previous rant(regarding office laptop stolen):
Company says there might be some deductions in salary. Trying to negotiate with them .
Would like to hear What's your company policy on stolen laptop?5 -
Music - usually Pink Floyd. Loud enough to overpower my thoughts.
Worked even better when I could go on a bike ride to clear my head, but my bike got stolen 🤬3 -
Anyone who subscribed to the notion of "Design Thinking" should have their kidneys stolen without anesthetics.6
-
Coaches know: it's all about the mindset!
Runtime exception? Mindset!
No video in Teams? Mindeset!
Money got stolen? Mindset!1 -
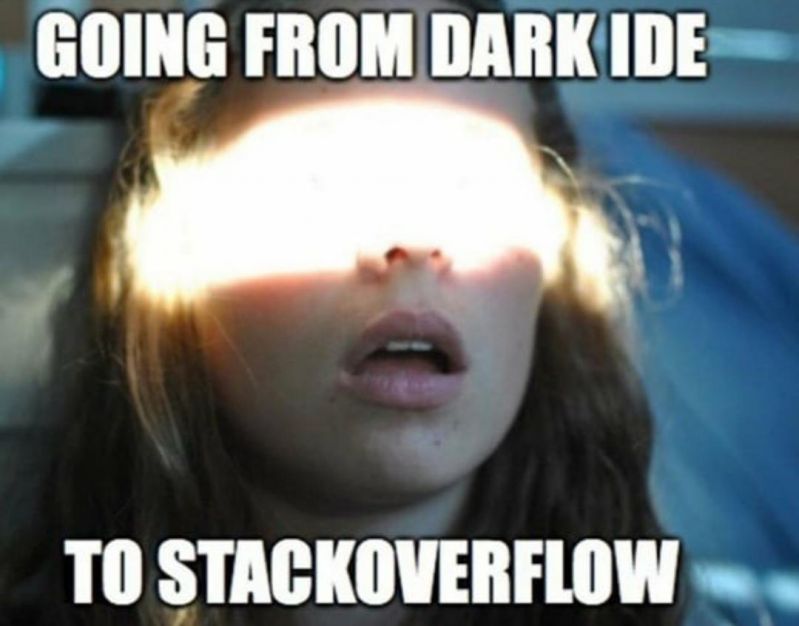
What the mods of Stackoverflow think every single person who ask questions look like.
Stolen from /r/programmerhumor
-
Day and a half trying to fix a bug in a deprecated library :) thinking about commiting suicide right now (yes I stolen that quote back there)1
-
How do you actually accredit code stolen from a project on github? Like it's not used commercially and it's going to be on github, too.
for context: i stole a java class from a minecraft mod. which is about 5% of the source project but makes more then 50% of my project.3 -
At last! After my phone got stolen last year, I finally have a new one, so I can use devrant again. Feeling like arriving home again :-)6
-
Agreeing to do iOS dev. I feel like my previous project has stolen 2 valuable years of my career from me.
-
HOW TO RECOVER STOLEN BTC FROM SCAM - OMEGA CRYPTO RECOVERY SPECIALIST
Recovering stolen btc/usdt/eth and other assets without professional help can be a daunting task, especially for individuals who lack the technical expertise required to trace and recover stolen assets. Therefore, it is essential to choose a reputable and experienced specialist to assist in recovering stolen assets. OMEGA CRYPTO RECOVERY SPECIALIST is a trusted and reliable option for recovering stolen BTC from scams. With over 22 years of experience in the field, they have a team of experts with diverse skills and knowledge. Reach out to them immediately
Website: omegarecoveryspecialist .c o m
Mail: omegaCryptos@consultant .c o m
Whatsap; +1 (701 660 (04 75)23 -
Inspired by @gowtham-sai
Are there any ranters from Gdańsk, or 3city, Poland?
Meeting would be a nice thing :D5 -
Thank you, Google!
Stolen from Reddit, but still hilarious 😁
Credit: https://reddit.com/r/google/... 1
1 -
Co-workers conversation about the new Google Pixel... "I won't get it because they steal your soul, same reason why I don't have the iPhone with the finger print.. they want to have all your information... blah blah..."
I laugh, because they device doesn't matter... your info gets stolen in transit... so all your snap chat, IG DMs, and all of communication potentially at risk to be "stolen".
Example, Gov't splicing into underwater fiber optic cables and redirecting traffic to a data center...
Understand the tech.. please.2 -
Last friday my old android phone stolen in public transportation. Things I miss so bad was my bookmarked links in a hn app1
-
Two steps forward one back: Gets paid by client, phone gets stolen enroute. Now am just ranting from a tab
-
I don't know how to feel right now, I finally start a new dev job tomorrow, which I'm pretty excited about. In the other hand my bike just got stolen while I was visiting some friends at my old school.
As I would say in french Canadian:
JE TE SOUHAITE DE TE FAITE RENTRÉE DEDANS PAR UN CRISS DE GROS TRUCK EN CONDUISANT MON VÉLO MON ESTI D'ENFANT DE CHIENNE DR CÂLISSE2 -
Following two unsuccessful attempts to recover my stolen USDT, I gave up on ever getting it back until Recovery Nerd was suggested on Quora. I was extremely happy to find the article because they were able to recover 95% of my stolen USDT, so I thought I would share it with anyone else who might be in need of their services. Their email address is recoverynerd AT mail DOT com.10
-
Lost Recovery Masters They are Here To Help you Recover Your lost or stolen Cryptocurrency
Lost Recovery Masters is a service that specializes in helping individuals and businesses recover lost or stolen cryptocurrency. Their team of experts likely have experience and tools to assist with cases involving lost private keys, forgotten passwords, hacked accounts, or other situations where access to cryptocurrency has been compromised. If you are in need of assistance with recovering your lost or stolen cryptocurrency, Lost Recovery Masters may be able to help you navigate the process. It is important to verify the legitimacy and credibility of any service offering cryptocurrency recovery assistance to ensure that your funds are in safe hands.7 -
"Big ups to Cyberspace Hackpro for helpin' me get back my stolen ETH! They were straight fire, Charles Morris out!"
"Shoutout to cyberspace hack pro for helping me recover my stolen crypto! They were super professional and got the job done. I'm forever grateful! If you're a victim of crypto scams, don't hesitate to reach out to them. They're the real deal! Thanks again, You're the best!
Contact them 📩
(W-App: 1 (659) 217 (9239)1 -
Best in Recovery Stolen Bitcoin: Vacuum Cyber Hack can Help you out
When I realised my $395,000 worth of Bitcoin had been stolen, I was devastated. The thought of losing such a significant amount left me feeling completely powerless. After exhausting all options, I decided to reach out to Vacuum Cyber Hack. Their reputation for successfully recovering stolen cryptocurrency made them the obvious choice. From the very beginning, I was impressed by their professionalism and expertise. They quickly assessed my situation and immediately began working on a recovery plan. Using advanced algorithms and state-of-the-art forensic methods, Vacuum Cyber Hack tracked the stolen funds with remarkable precision. Throughout the process, they kept me updated, providing clear communication and ensuring my sensitive information remained confidential. Within a short time, Vacuum Cyber Hack successfully recovered my stolen Bitcoin, returning my funds and restoring my confidence in cryptocurrency security. Their efficiency, dedication, and ethical approach made all the difference. I’m incredibly grateful to Vacuum Cyber Hack for their exceptional service and for proving that even in the most challenging situations, recovery is possible. They truly set the standard for Bitcoin recovery services. I can confidently recommend them as the best choice for anyone facing the same challenge.
Email: support @ vacuumcyberhack . com
Whatsapp: +39 351 059 0507
Website: https : //vacuumcyber hack .co m/2 -
Best in Recovery Stolen Bitcoin: Vacuum Cyber Hack can Help you out
When I realised my $395,000 worth of Bitcoin had been stolen, I was devastated. The thought of losing such a significant amount left me feeling completely powerless. After exhausting all options, I decided to reach out to Vacuum Cyber Hack. Their reputation for successfully recovering stolen cryptocurrency made them the obvious choice. From the very beginning, I was impressed by their professionalism and expertise. They quickly assessed my situation and immediately began working on a recovery plan. Using advanced algorithms and state-of-the-art forensic methods, Vacuum Cyber Hack tracked the stolen funds with remarkable precision. Throughout the process, they kept me updated, providing clear communication and ensuring my sensitive information remained confidential. Within a short time, Vacuum Cyber Hack successfully recovered my stolen Bitcoin, returning my funds and restoring my confidence in cryptocurrency security. Their efficiency, dedication, and ethical approach made all the difference. I’m incredibly grateful to Vacuum Cyber Hack for their exceptional service and for proving that even in the most challenging situations, recovery is possible. They truly set the standard for Bitcoin recovery services. I can confidently recommend them as the best choice for anyone facing the same challenge.
Email: support @ vacuumcyberhack . com
Whatsapp: +39 351 059 0507
Website: https : //vacuumcyber hack .co m/ 1
1 -
How do I locate a hacker to get my bitcoin wallet back after I lost it? / How can I recover my lost cryptocurrency? Visit > OPTIMISTIC HACKER GAIUS team
I discovered that all of the money in my wallet had been taken out after it was compromised. I was fortunate to be able to retrieve my stolen money, nevertheless, because of the OPTIMISTIC HACKER GAIUS team. Additionally, if you need their services, you can get in touch with them.
Contact info; (Website) optimistichackergaius. co m (WhatsAp) +(44 )-(7376),(74)-0569 1
1 -
Can You Recover Lost or Stolen Bitcoin? Yes Captain WebGenesis Can.
Captain WebGenesis is a seasoned expert in the realm of cryptocurrency recovery. With a background in cybersecurity and blockchain technology, Captain WebGenesis has dedicated their career to helping scam victims navigate the complex world of digital asset recovery. Their approach combines technical know-how with a compassionate commitment to helping those who have been wronged.
Visit (Captainwebgenesis. co m)
I need a hacker to recover my lost investment?How to Find Legitimate Crypto Recovery Companies?
Cryptocurrency Scam Recovery // Recover Lost Funds // Crypto Investment Gone Wrong. How To Hire A Hacker To Get Back Stolen Crypto Coins // Hire A Hacker To Recover Lost Or Stolen Bitcoin/Nft // Help I Can't Access My USDT Account, Seems I Got Hacked // Bitcoin Recovery Expert Needed// . .1 -
I was skeptical at first, but hack4techspy @gmail com helped me recover my stolen Bitcoin! Their expertise and professionalism are unmatched. 10/10 would recommend for any hacking-related services.

-
Bitcoin Scam Recovery Success with LEE ULTIMATE HACKER: A Personal Experience
I was a victim to a crafty scam, but when all hope was gone LEE ULTIMATE HACKER became my beacon of light, fact remain Bitcoin is the future of world currency but be careful before falling prey to unregulated brokers like I was ,in the wake of loosing my funds to investment broker , I found myself in a state of panic and despair. Fortunately for me an old friend referred me to LEE ULTIMATE HACKER who further indulged me in deep consultation to understand the details of the theft and the loss .They created a customized recovery plan that met my specific need using their extensive knowledge of blockchain technology and forensic investigative skills, LEE ULTIMATE HACKER was a transformative experience ,not only did they recover my stolen funds they demonstrated a level of professionalism that exceeded my expectations ,I really appreciated them for their help and I wish to recommended them to everyone caught up in a systematic scams.
Please contact LEE ULTIMATE HACKER via LEEULTIMATEHACKER @ AOL . COM
telegram: LEEULTIMATE for your swift recovery.1 -
CRYPTOCURRENCY RECOVERY SERVICES - Consult - iFORCE HACKER RECOVERY
iForce Hacker Recovery specializes in recovering stolen cryptocurrency, including Ethereum and USDT. With proven and effective methods, they are a trusted ally for victims of crypto theft. One client who lost $908,000 turned to iForce Hacker Recovery for assistance, and within just one day, the entire amount was successfully retrieved, providing immense relief. Committed to helping others facing similar challenges, iForce Hacker Recovery offers expert support in recovering lost funds. If you need assistance in reclaiming your stolen assets, they are ready to help. Recover stolen crypto, Bitcoin recovery expert, Crypto scam recovery. Recover hacked crypto wallet, Crypto recovery firm, How to recover stolen Bitcoin, Lost cryptocurrency recovery, Blockchain recovery service, Recover scammed crypto funds, Crypto asset recovery, Retrieve lost Bitcoin, Bitcoin fraud recovery, Recover funds from crypto scam, Crypto recovery expert near me, Crypto recovery services legit, Recover crypto from scammer, Bitcoin private key recovery, Crypto recovery lawyer.
Learn More; ww w. iforcehackersrecovery. com
Email; contact@iforcehackersrecovery. co m
Whatsapp; +1 (240) 803. 37 06 1
1 -
Expert in Crypto Recovery. Recover your cryptocurrency that has been lost, stolen, compromised, forgotten, or defrauded by dishonest investment sites.
For assistance in recovering your stolen valuables, give OPTIMISTIC HACKER GAIUS a call.
After weeks of trying to fix the situation, it was just what I needed. Hacker Gaius was fortunately available to assist.
Expert in Crypto Recovery. Recover your cryptocurrency that has been lost, stolen, compromised, forgotten, or defrauded by dishonest investment sites.
How to employ a US-based crypto recovery service.
To assist victims of crypto scams in getting their stolen cryptocurrency back, a crypto recovery specialist does professional analysis. Employing the top crypto recovery
How to Employ a United Kingdom Leading Crypto Recovery Specialist After falling for a cryptocurrency fraud, I had given up on ever getting my money back, but OPTIMISTIC HACKER GAIUS came to my rescue.
Are Services for Crypto Recovery Reputable? Watch Out for Financial Scams
Recovery of Financial Money
Services for Cryptocurrency Scam Recovery | Reliable Crypto Fraud Recovery
Webpage; optimistichackergaius .c o m1 -
LEGITIMATE CRYPTO BTC // USDT // RECOVERY SERVICE - Call iFORCE HACKER RECOVERY
Lost or stolen crypto? Hacked funds? Wondering how to recover cryptocurrency from a scammer or find a trustworthy recovery firm? Do you need a hacker to get your money back? iFORCE HACKER RECOVERY is a licensed forensic organization with a global presence, specializing in recovering lost or stolen Bitcoin, USDT, Ethereum, and other digital assets. With expertise in tracking and retrieving stolen funds, iFORCE HACKER RECOVERY successfully recovered my stolen crypto, and I believe they can do the same for you. If you've fallen victim to crypto theft, they are the experts to trust. Recover stolen crypto, Bitcoin recovery expert, Crypto scam recovery. Recover hacked crypto wallet, Crypto recovery firm, How to recover stolen Bitcoin, Lost cryptocurrency recovery, Blockchain recovery service, Recover scammed crypto funds, Crypto asset recovery, Retrieve lost Bitcoin, Bitcoin fraud recovery, Recover funds from crypto scam, Crypto recovery expert near me, Crypto recovery services legit, Recover crypto from scammer, Bitcoin private key recovery, Crypto recovery lawyer.
Webpage info; ( iforcehackersrecovery. com
Email; contact@iforcehackersrecovery. co m
Whatsapp; +1 (240) 803. (3706) 1
1 -
Lost Bitcoin Recovery Experience After Laptop Theft and No Wallet Backup
I never thought a spilt second would change my entire life, I was sitting in a cafe working on a project the next thing in a blink of an eye I lost my laptop, that had my entire financial investment of $730,000 worth of Bitcoin, I went from being calm to erratic going up and down looking if I could locate it, finally accepted that I had lost it. Everything was gone my important work tool, and the worst part was I hadn’t backed up my wallet, I desperately began searching for solutions so I went on research mode, but I wasn’t sure if there was anyone out here who could recovery stolen cryptocurrency, I held on to the little hope that I had and continued with my search when I came across several testimonials about LEE ULTIMATE HACKER a hacker that was able to track and recover stolen Bitcoin, I contacted LEEULTIMATEHACKER @ AOL . COM
telegram: LEEULTIMATE
wh@tsapp +1 (715) 314 - 9248 and after consultation, they took me through steps on how they’ll recover my lost funds, they asked me critical questions and I explained it to them that I didn’t have a back up and needed help, they reassured me that they will be able to help me recovery my lost funds, LEE ULTIMATE HACKERS team worked with me with such professionalism until the last step, using advanced blockchain tracking and forensic tools to trace my stolen assets, after only a week of work I finally got a call from LEE ULTIMATE HACKER customer service that they had fully recovered my money, on top of it they helped me improve my security through their app providing real time security alerts ,encrypted backups and anti- theft that was new to me, I learnt a lot about digital security i also experienced hopeless situation that could be turned around for the best all thanks to LEE ULTIMATE HACKER reach out to them for all your complex recovery problem.2 -
Recover Stolen Crypto | Crypto Recovery Experts | Crypto Recovery services
Captain WebGenesis stands out as a distinguished Crypto recovery service provider helping victims reclaim lost funds. One of the most compelling reasons to choose Captain WebGenesis is his impressive success rate. The Recovery Expert has successfully recovered millions in lost cryptocurrencies for his clients across the globe. This success not only showcases their expertise but also builds trust among potential clients facing similar challenges and need help to recover their cryptos.
Website; Captainwebgenesis. com
Legitimate Crypto Recovery Companies
Trusted Crypto Recovery Experts - Trace & Recover Your Stolen Cryptocurrency with the Best Crypto Recovery Company. Contact CAPTAIN WEBGENESIS Now!
What is the best crypto recovery service?
CAPTAIN WEBGENESIS is a trusted and reliable company that specializes in recovering lost or stolen Bitcoin1 -
Bitcoin's increasing popularity has led to a surge in digital currency theft, with hackers targeting unwary individuals and organizations. The anonymity of Bitcoin transactions and the complexity of blockchain technology make it difficult to trace stolen assets. Wizard James Recovery, a specialist team, has become a dominant force in recovering stolen Bitcoin. Bitcoin transactions are irreversible, making it difficult to trace their origins. As a result, Bitcoin theft is becoming a significant concern for cryptocurrency enthusiasts. To help, contact Wizard James Recovery at wizardjamesrecovery(@)usa . com1
-
HOW TO RECOVER STOLEN BTC FROM WEX EXCHANGE
"Thanks to Mayermusk Recovery Company, I successfully recovered $78,000 in BTC from WEX Exchange. Their team was incredibly knowledgeable and supportive throughout the entire process. I truly appreciate their dedication and expertise. Highly recommend their services!"
How to recover stolen btc from wex exchange
btc how to get money back contact mayermusk recovery
How to recover lost cryptocurrency
How to recover Bitcoin wallet hire mayermusk recovery
Accessing Lost Bitcoin Transactions
is there any way to reclaim what I lost on BTC hire mayermusk recovery company? 1
1 -
Best Recommended Cryptocurrency BTC/ETH Recovery Company Use HACKER ZED NEMESIS.
It was HACKER ZED NEMESIS who restored my wallet. So, don't be afraid to contact HACKER ZED NEMESIS if you're in a similar scenario and have lost your Bitcoin because of theft or for any other reason. To find your stolen Bitcoins and pay you back, they have the skills and resources necessary. Contact them immediately to learn more about your choices and to get your stolen or misplaced cryptocurrency back.
E-Mail; hackerzednemesis001@zohomail. co m
Text -Whatsapp -Call ; + 1 (872) 284- 3002 -
DIGITAL HACK RECOVERY— ETHEREUM AND CRYPTO SCAM RECOVERY SERVICES
When I first discovered that my ETH had been stolen from a mining pool, I was devastated. It felt like everything I had worked for was gone in an instant. In my desperation, I sought help everywhere I could. I even went to church and asked for prayers, hoping that divine intervention would help me recover my funds. The congregation prayed for me, and while it gave me some comfort, nothing changed. My stolen ETH remained out of reach, and I felt more helpless than ever.Then, by chance, I came across a post online from someone who had experienced a similar situation. They shared how Digital Hack Recovery had helped them successfully recover their stolen cryptocurrency. Their story caught my attention, and I decided to reach out to the team at Digital Hack Recovery, hoping that they could help me too. I was still skeptical, but I knew I had to try something.From the moment I contacted Digital Hack Recovery, I was impressed by their professionalism and expertise. They quickly got to work on my case and assured me that they had the skills and tools needed to track down my stolen ETH. Within just a few days, I was astonished to learn that they had successfully recovered all of my stolen funds, something I never thought would be possible.The entire process was smooth, and I was kept updated every step of the way. Their team used a combination of advanced recovery techniques and a deep understanding of blockchain security to recover my ETH. I couldn’t believe how efficient and effective they were. In just one week, I had all my stolen ETH back in my wallet.I’m incredibly grateful to Digital Hack Recovery for their help. What started as a desperate situation turned into a success story, and I couldn’t have done it without their expertise. If you’ve been scammed or had your cryptocurrency stolen, I highly recommend reaching out to Digital Hack Recovery. They helped me recover all my ETH, and I’m confident they can help anyone else in a similar situation. Contact Digital Hack Recovery for help via⁚
WhatsApp +19152151930
Website; https : // digital hack recovery . com
Email; digital hack recovery @ techie . com 6
6 -
How do I recover my stolen cryptocurrency without being scammed?
Cryptocurrency, with a seamless financial solution, also faces the problems of hacking, scams, and even misplaced private keys. In the unlikely event that you fall victim to fraud through hacking or otherwise, it is imperative that you take prompt and correct course of action. Here are the measures to take in the event you are a victim of a crypto exchange scam.
Assess the Situation
It is easy to understand that any form of loss must first be assessed to find out more about it. Was your wallet hacked? Was your loss due to misplaced private keys, or have you forgotten passwords to the access? It is useful to understand the details of the problem so it can be determined how to proceed in the process of recovery.
Reach out to Your Wallet or Exchange
If your funds were stolen via a wallet service or via an exchange, contact them, their customer support. Most good sites have departments that can help in the search for lost items or have guidelines on how to go about it.
Report to Authorities
Plaint with the local police and cybercrime departments. Take care to maintain records of all transactions, transaction codes, wallet numbers, and communication messages that regard the lost ether. This information may help the authorities in their investigation – someone will surely know at least one of the abusers.
Use Forensic Services
Reach out to SACLUX COMPTECH SPECIALST because they are legitamtly recovery expert, which can be termed as blockchain forensic firms, SACLUX COMPTECH SPECIALST provide solutions on tracking and retrieval of the stolen crypto currencies. The involvement of baktrail services adds extra mileage by enhancing the prospects of the likelihood of the recovery of your lost cash especially where the loss is massive.
Whatsapp: +44 (749) 221-3552Telegram: SacluxComptech1 -
your work laptop (or environment) get's stolen/lost/broken, when it's the last time you backed-up ?
and as a side question, how long will it take to get everything back up and running ?2 -
I'm not going to have my source code stolen this time if noone steals yours. now how much more diplomatic a solution could there be eh ? guess they made the mistake of stealing heh.6
-
Saclux Comptech Specailst can assist in retrieving lost or stolen digital assets. Utilizing various tools and tactics, they are adept at tracking down scammers who have committed financial crimes involving cryptocurrency theft or losses and holding them responsible. Furthermore, these experts also offer advice on how to avoid future losses by taking adequate security precautions.
They value client privacy, uphold transparent processes and offer customer support that is both responsive and helpful. Saclux Comptech Specialst experts specialize in tracking down and recovering lost or stolen cryptocurrency assets, using their expertise in cybersecurity, digital forensics, and legal knowledge to trace stolen funds back to their source and identify perpetrators. In addition, these specialists also provide guidance for avoiding similar incidents by encouraging individuals to employ secure storage methods as well as implement extra protections like hardware wallets for added peace of mind.3 -
Best Recovery Experts for Cryptocurrency Assets / Captain WebGenesis
CAPTAIN WEBGENESIS is a one crucial cryptocurrency recovery firm that is well-equipped to recover Bitcoin that has been stolen by cryptocurrency scammers. The expert employs cutting-edge techniques and tools that help identify fraudulent transactions, track down locations linked to the scam, and trace the flow of funds.
CAPTAIN WEBGENESIS also works with cybersecurity firms that have extensive experience in blockchain investigation and forensic specialists, that improves the chances of finding and retrieving the stolen Crypto. 5
5 -
I lost $8,000 in USDT to a Telegram scam. After reading about recovery success stories, I searched "recover stolen USDT Tether" and found a licensed cyber recovery team. They were able to trace the stolen funds and work with law enforcement to recover my Tether. I'm proof that USDT recovery is possible with the right help. there are real professionals who can help such as GHOSTSQUADHACKING at GMAIL dot COM5
-
SPARTAN TECH GROUP RETRIEVAL A LEGIT COMPANY FOR RECOVERY OF STOLEN ETHEREUM / BITCOIN
At Spartan Tech Group Retrieval, we prioritize security, confidentiality, and customer satisfaction. Our rigorous protocols ensure the safekeeping of sensitive information, and our transparent communication keeps you informed throughout the recovery process.We’re dedicated to helping individuals and organizations recover stolen cryptocurrencies and digital assets. Our team of expert cyber security specialists, cryptocurrency recovery specialists, and digital forensic analysts work tirelessly to track, recover, and secure your stolen assets.
Email: spartan tech (@) cyber services . c o m OR
support(@) spartan tech group retrieval. o r g
Website: h t t p s : / / spartan tech group retrieval . o r g
WhatsApp: + 1 ( 9 7 1 ) 4 8 7 - 3 5 3 8
Telegram: + 1 ( 5 8 1 ) 2 8 6 - 8 0 9 22 -
I was the subject of a cryptocurrency heist. Some amount of bitcoin was stolen from my wallet and diverted to an unpermitted account. My wallet management was informed, however, they had me wait a week before responding through email. They didn’t offer any assistance; alternatively, they mentioned that my phone might have been compromised and told me to get in touch with the authorities who couldn't provide any solution to recover my bitcoin. When I was browsing through the internet trying to find a solution to get my stolen bitcoin back, I discovered a team of bitcoin recovery experts called Wizard James Recovery company. I then decided to contact them for assistance in getting my stolen money back. I have nothing but praise for Wizard James Recovery company because they were able to assist me in recovering the money that had been stolen. With the use of their sophisticated tools, Wizard James Recovery was able to determine how the transaction was carried out. I have my money back and I am very thankful to Wizard James Recovery company for their amazing service. If you have any issues related to mine. Kindly contact them via email. (wizardjamesrecovery (@) usa (.) com)1
-
Crypto Recovery | Reclaim Stolen Crypto | Crypto Scam Recovery Services.
In the ever-evolving world of cryptocurrencies, the thrill of investing can quickly turn into despair when you misplace or lose access to your digital assets. As a Bitcoin enthusiast, I faced such a tragedy when I lost my Bitcoin wallet. Just when I thought all hope was lost, Captain WebGenesis emerged as my savior in the chaotic sea of blockchain recovery. Captain WebGenesis began his investigation by analyzing blockchain transactions and tracing the stolen funds. It was a painstaking process that required advanced technical knowledge and an understanding of the cryptocurrency landscape. He meticulously tracked the movement of my stolen assets across various wallets and exchanges.
Email: (Captainwebgenesis@ hackermail. com).1 -
Don't Lose Hope: Recover Your Stolen Crypto with Cyberspace Hackpro
As a victim of a scam, I was impressed by the exceptional service provided by Cyberspace Hack Pro. Their team demonstrated expertise and dedication to recovering my lost funds.
- Professional and efficient service
- Expertise in tracking down scammers and retrieving funds
- Dedicated to customer satisfaction
I highly recommend Cyberspace Hack Pro to individuals who have fallen victim to scams. Their services are reliable, trustworthy, and effective.
Contact info2 -
Don’t Let Your Bitcoin Stay Lost: The Coin Caper Recovery Solution
The future of Bitcoin recovery is a topic of great interest and excitement, particularly with the emergence of innovative companies like Coin Caper Recovery leading the charge. As the cryptocurrency market continues to evolve and face new challenges, the need for effective solutions to help users recover lost or stolen Bitcoin has become increasingly critical. Coin Caper Recovery, a specialized firm dedicated to this very purpose, has positioned itself at the forefront of this emerging field. Through their proprietary techniques and deep expertise in blockchain technology, Coin Caper Recovery has developed a comprehensive approach to tracking down and retrieving misplaced or compromised Bitcoin, providing a lifeline to individuals and businesses who have fallen victim to the inherent risks of the digital currency landscape. Their team of seasoned investigators and cryptography experts employ a meticulous, multi-pronged strategy, leveraging advanced data analysis, forensic techniques, and collaborative partnerships with law enforcement to painstakingly trace the movement of lost or stolen coins, often recovering funds that would otherwise be considered irrecoverable. This pioneering work not only restores financial assets but also helps to bolster confidence and trust in the long-term viability of Bitcoin, cementing Coin Caper Recovery's role as a crucial player in shaping the future of cryptocurrency recovery and security. As the digital finance ecosystem continues to evolve, the importance of innovative solutions like those offered by Coin Caper will only grow, ensuring that users can navigate the complexities of Bitcoin with greater peace of mind and protection. Call Coin caper recovery now via:
Whatsapp: +1 (747) 360‑9248 12
12 -
I was in a state of utter despair when I realized that I had fallen victim to a sophisticated phishing scam, losing a substantial amount of my hard-earned cryptocurrency in the process. The scammers were so cunning and professional that I thought I had lost everything forever. But then I stumbled upon Cranix Ethical Solutions Haven, a team of ethical hackers and cybercrime experts who specialize in recovering stolen digital assets. Their expertise and professionalism were evident from the moment I reached out to them. They walked me through the entire process, explaining each step in detail and keeping me informed every step of the way. Their team of experts worked tirelessly to track down the scammers, using their advanced techniques and cutting-edge technology to trace the stolen bitcoin. What impressed me most about Cranix Ethical Solutions Haven was their unwavering commitment to justice. They didn't just stop at recovering my stolen bitcoin; they also worked with law enforcement agencies to bring the scammers to book. Their tireless efforts ultimately led to the arrest and prosecution of the perpetrators, sending a strong message to other would-be scammers.
I am forever grateful to Cranix Ethical Solutions Haven for their outstanding work. Without their help, I would have lost everything. Their dedication to fighting cybercrime and protecting innocent victims like me is truly commendable. I highly recommend their services to anyone who has fallen victim to cryptocurrency scams or other forms of cybercrime. They are the best in the business, and I am confident that they will continue to make a positive impact in the fight against cybercrime.
EMAIL: (cranixethicalsolutionshaven @ post . com) OR (info @ cranixethicalsolutionshaven . info)
WHATSAPP: (+ 4 4 7 4 6 0 6 2 2 7 3 0)
WEBSITE: (https : //cranixethicalsolutionshaven . info)
TELEGRAM: (@ cranixethicalsolutionshaven)1 -
If you need a private investigator who can recover stolen funds from scammers or from a wrong cryptocurrency investment then contact (recoverfunds.investigator247 AT gmail DOT com) because they got you covered. They are 100% secured and reliable programmers that has helped me recover my stolen money from a scammer few weeks back .They also deal with all types of hacking related issues such as WhatsApp hack, Facebook hack, Gmail hack, mobile Phone hack, Accounts hack, Erase Criminal Records, Websites Hack, Bitcoin Trade recovery.
-
HOW FAST CAN I RECOVER MY STOLEN CRYPTO / BITCOIN > GO TO iFORCE HACKER RECOVERY
iFORCE HACKER RECOVERY Anyone who trades cryptocurrencies should know how to recover stolen or lost Bitcoin.
Getting in touch with iFORCE HACKER RECOVERY could be the key to recovering your investment if you need to withdraw money from an unlicensed broker or are dealing with challenging terms and conditions.
Visit Homepage; iforcehackersrecovery. c o m
Text /Call; +1 (240 803 3706
Contact Email; contact@iforcehackersrecovery c o m -
Hire a hacker to recover your lost or stolen cryptocurrency / Consult Captain WebGenesis.
Captain WebGenesis is a leading provider of investigation solutions for the cryptocurrency industry, helping forensic specialists and law enforcement in recovering stolen Cryptocurrency assets. Captain WebGenesis are adept at detecting suspicious activity and linking specific cryptocurrency addresses to specific people or businesses; furthermore their technology enables them to track funds between multiple accounts; his team of committed professionals has vast experience in cyber forensics, cryptocurrency asset recovery, and fraud prevention.4 -
I NEED A HACKER TO RECOVER MY LOST BTC/ NFT/Usdt - CONSULT CAPTAIN WEBGENESIS
How to Find Legitimate Crypto Recovery Companies?.
Who is the best hacker to recover bitcoin?.
How do I recover crypto from a scammer?.
Getting Back Lost, Hacked Or Stolen Crypto?.
I need a hacker to recover my lost investment?..
Cryptocurrency Scam Recovery // Recover Lost Funds // Crypto Investment Gone Wrong. How To Hire A Hacker To Get Back Stolen Crypto Coins // Hire A Hacker To Recover Lost Or Stolen Bitcoin/Nft // Help I Can't Access My USDT Account, Seems I Got Hacked // Bitcoin Recovery Expert Needed/
The Captain WebGenesis's team is committed to ensuring victims of crypto scam are able to recover their scammed cryptocurrency. If you have lost your crypto as a result of a fraudulent investment, Cryptocurrency sent to the wrong address or phishing attack, You can trust Captain WebGenesis to help you get back your lost or stolen crypto.
Visit ( Captainwebgenesis.c om)..Email (Captainwebgenesis @hackermail.c om ) .
Whatsapp +(1)(50)(14)(36)_(93)(62)6 -
Betafort Recovery follows a systematic approach to ensure the best chance of recovering stolen funds. Here are the steps they took to help me:
1. Initial Contact and Case Assessment
I contacted Betafort Recovery via email and WhatsApp, explaining the situation in detail. They responded quickly, requesting specific information to assess the theft. This included:
- Details of the stolen transaction
- The wallet addresses involved
- Any communication or evidence related to the scam
2. Verification and Agreement
Once they reviewed my case, Betafort Recovery confirmed that they could assist in the recovery. They provided a service agreement outlining the recovery process, confidentiality terms, and their fee structure based on the amount recovered. I reviewed and signed the agreement, reassured by their transparent and professional approach.
3. In-Depth Investigation
The firm began by conducting a thorough investigation to trace the stolen funds. This involved:
- Analyzing the blockchain to track the movement of the stolen assets
- Identifying the destination wallet and any subsequent transactions
- Utilizing advanced forensic tools to uncover patterns and connections
4. Recovery Strategies
Once they gathered sufficient information, Betafort Recovery implemented various strategies to recover the stolen money:
- Negotiation: They sometimes engaged directly with the perpetrators, using their expertise to negotiate the return of the funds.
- Technical Exploits: The team exploited vulnerabilities in the scammers’ systems to regain access to the stolen assets.
- Collaborative Efforts: When necessary, they collaborated with other cybersecurity experts and legal authorities to enhance the recovery process.
5. Successful Recovery
After several days of diligent work, Betafort Recovery successfully recovered my stolen funds. They transferred the recovered money back to a secure wallet that I controlled. Their professionalism and expertise were evident throughout the process, and I was immensely grateful for their assistance.5 -
How to Recover Cryptocurrency Funds Lost or Stolen by Scammers / Captain WebGenesis.
Recovery of Scammed or stolen Bitcoin and Cryptocurrency: While many companies promise to help you reclaim lost funds, Captain WebGenesis stands out by providing much more than just recovery solutions. His expertise spans various areas, including blockchain technology, Cryptocurrency scam recovery, and financial consulting. When you choose Captain WebGenesis, you're not just getting a Crypto recovery service; you're gaining a partner who understands the intricacies of the digital currency landscape.
Contact Info:
Mail: { Captainwebgenesis @ hackermail . com }
Whatsapp: +1,50,14,36,93,62
Can you get your money back if scammed on Bitcoin? Are there any legitimate crypto recovery services?Is it possible to recover stolen Bitcoin?
What is the best recovery service for Bitcoin?1 -
HIRE CYBERPOINT RECOVERY HACKER FOR STOLEN CRYPTO AND BITCOIN RECOVERY
Are you a victim of stolen crypto or Bitcoin? Join us in San Francisco for a one-of-a-kind event where you can meet with Cyberpoint Recovery Hackers who specialize in recovering your lost digital assets. Don't miss this opportunity to get back what's rightfully yours. Mark your calendars and come prepared to reclaim your stolen funds, Their vast expertise and commitment to client success make them one of the top choices for cryptocurrency recovery. Contact: Email:(Support @ cyberpointrecovery . com)2 -
Bitcoin & Cryptocurrency Scam Recovery / Captain WebGenesis
If your Crypto assets have been hacked, lost or stolen, Captain WebGenesis is providing the expertise you need to recover them. His team of certified hackers combines deep knowledge of cybersecurity with ethical hacking practices to restore your assets and provide valuable advice on securing your holdings in the future. Don’t let cybercriminals get away with your hard-earned cryptocurrency. Reach out to Captain WebGenesis today for professional help in recovering your stolen Bitcoin.
For more information or to hire a hacker to recover your stolen cryptocurrency, contact Captain WebGenesis 4
4 -
How I Recovered My Stolen Bitcoin Using iBolt Cyber Hacker Service
I'm here to share my incredible experience with iBolt Cyber Hacker Service. I fell victim to a well-executed Bitcoin theft. All the cryptocurrency in my wallet was gone (stolen). I was devastated and immediately began searching for solutions, but nothing seemed to offer the hope I needed. I came across iBolt Cyber Hacker Service, which had excellent reviews from people who had successfully recovered their stolen funds. I decided to give them a try, hoping that they could help me retrieve my Bitcoin.
Within few hours, iBolt Cyber Hacker had tracked down my stolen Bitcoin to the wallet it was transferred to. Not only did they find it, but they also helped me initiate the recovery process. The entire time, they kept me updated on the progress. Thanks to their hard work, my stolen Bitcoin was successfully recovered. I wholeheartedly recommend their services to anyone who finds themselves in a similar situation.
Official Website: www . ibolt cybarhack . com 1
1 -
Bitcoin & Cryptocurrency Scam Recovery || Best Crypto Recovery Company
iFORCE HACKER RECOVERY can assist with the recovery of lost or stolen cryptocurrency assets.
In order to recover your stolen Bitcoin, working with the iFORCE HACKER RECOVERY team, who will go above and beyond. We've created sophisticated methods and strategies that raise the possibility of a full recovery. -
How can a Saclux Comptech Specialst help in recovering stolen or lost Bitcoin and other cryptocurrencies?
Saclux Comptech Specialst can help in recovering stolen or lost Bitcoin and other cryptocurrencies through various methods:
1. Investigation: The expert will conduct a thorough investigation to trace the stolen or lost funds. They will analyze blockchain transactions, digital footprints, and other relevant information to identify the culprits and track the funds.
2. Legal Assistance: If the theft or loss involves criminal activities, the recovery expert can work with law enforcement agencies and legal professionals to initiate legal proceedings against the perpetrators. They can provide evidence and expert testimony to support the case.
3. Negotiation: In some cases, the recovery expert may negotiate with the hackers or scammers to retrieve the stolen funds. They can use their expertise in dealing with cybercriminals and employ negotiation tactics to recover the assets.
4. Blockchain Analysis: The expert will analyze the blockchain network to identify any suspicious transactions or addresses associated with the stolen or lost funds. They can trace the movement of the funds and potentially locate the assets.
5. Asset Recovery Services: Saclux Comptech Specialst often have connections with specialized asset recovery services. These services can assist in recovering stolen or lost cryptocurrencies by utilizing their expertise, resources, and legal.1 -
How to Recover Cryptocurrency in 2025 (Hire A Hacker) - Captain WebGenesis
Can stolen crypto be recovered? Yes, Captain WebGenesis possesses the necessary expertise in digital forensics to potentially trace and track down your stolen cryptocurrency. With years of experience and a proven track record of success, Captain WebGenesis has developed a comprehensive approach to cryptocurrency recovery
The comprehensive recovery process involves:
1. Initial Assessment: Captain WebGenesis will conduct a thorough review of the incident to determine the scope of the theft and identify potential leads.
2. Digital Forensic Analysis: He will then utilize advanced digital forensic tools to extract and analyze transaction data, network logs, and other relevant information to trace the stolen cryptocurrency.
3. Network Analysis: The team will meticulously examine the blockchain network to identify suspicious transactions, wallets, and patterns that may lead to the recovery of your stolen assets.
4. Collaboration with Exchanges and Authorities: Captain WebGenesis works closely with cryptocurrency exchanges, law enforcement agencies, and other relevant parties to freeze suspicious accounts, trace the flow of funds, and facilitate the recovery of your stolen cryptocurrency.
5. Recovery and Return: Once the stolen cryptocurrency is traced and tracked down, Captain WebGenesis will work to recover the assets and return them to their rightful owner.
Contact him now on: Captainwebgenesis@hackermail. com.1 -
HIRE A HACKER TO RECOVER LOST OR STOLEN BITCOIN/NFT/2025 - CAPTAIN WEBGENESIS. Getting Back Lost, Hacked Or Stolen Crypto
Captain WebGenesis has remarkable expertise in bitcoin recovery, having successfully located and reclaimed an amazing 85% of my lost funds. I was unfortunate enough to become a victim of a sophisticated cryptocurrency scam that targeted unsuspecting investors with deceitful promises of unrealistically large returns. After realizing the gravity of my situation and the significant financial loss, I sought help and discovered Captain WebGenesis, a reputable recovery expert who specializes in tracing and recovering lost or stolen digital assets. Thanks to his tireless efforts and strategic insight, I can confidently say that I'm back on track.
Call or whatsapp +1(501)436(93)62
Email : captainwebgenesis@ hackermail. com
Getting Back Stolen, Lost, Or Hacked Crypto? Crypto Scam Recovery || Recover Lost Funds || Crypto Investment Went Wrong? Hire A Hacker To Recover Your Stolen Crypto Coins || I Can't Access? My USDT Account, It Looks Like I Was Hacked || Bitcoin Recovery ?Expert Required, Getting Back Lost, Hacked Or Stolen Crypto?. How do I recover crypto from a scammer?. I need a hacker to recover my lost investment?. Is it possible to recover lost cryptocurrency? How do you recover loss in crypto? Are there any legitimate crypto recovery services? How do I recover my blockchain funds? Lost asset recovery? Can You Recover Lost Crypto in Canada?5 Ways to Track Down Lost Bitcoin and Other Cryptos? Lost Crypto Recovery? Crypto Asset Recovery Home? How to recover lost or stolen crypto assets - Captain WebGenesis? How to recover my losses from trading? Can you recover lost Bitcoins or Ethereum if you are? How to recover my lost crypto? I was transferring my? How to recover a lost crypto within 48 hours? Legitimate crypto recovery companies? How to claim unclaimed bitcoin? I lost 165,000 when my cryptocurrency was stolen. How can I recover it? Lost crypto in transfer? How to find lost crypto transactions? How can I recover my stolen $30,000 bitcoin? Software to find lost crypto wallet? How to recover stolen cryptocurrency from trust?2 -
Are you facing the devastating reality of having your Bitcoin stolen? Did you know that approximately $1 billion in cryptocurrencies were stolen in the first half of 2018 alone? It's a scary thought, but there are solutions out there to help you get your stolen BTC back. In my own experience, I turned to DANIEL MEULI WEB RECOVERY, the trusted name in cryptocurrency recovery, and I couldn't be happier with the results. When it comes to recovering your stolen BTC, you need a team of experts who understand the intricacies of the blockchain and have a proven track record of success. DANIEL MEULI WEB RECOVERY checks all the boxes, with a team of skilled professionals who have years of experience in cryptocurrency recovery. Their cutting-edge technology and strategic partnerships allow them to track down and recover stolen BTC quickly and efficiently. So, how does the recovery process work with DANIEL MEULI WEB RECOVERY? Once you reach out to their team, they will conduct a thorough investigation into the theft of your BTC. This involves analyzing the blockchain, tracking the movement of your stolen funds, and identifying the culprits behind the theft. With this information in hand, DANIEL MEULI WEB RECOVERY will work tirelessly to recover your stolen BTC and return it to your wallet. Look no further than WEBSITE. WWW . DANIELMEULIRECOVERYWIZARD . ONLINE for expert assistance in recovering stolen BTC. Their team has a solid history of successful outcomes, having aided numerous clients in regaining their lost funds. By choosing DANIEL MEULI WEB RECOVERY, you can trust that your stolen BTC will be handled with care and expertise, providing you with the peace of mind and financial security you deserve. Make the smart choice and let DANIEL MEULI WEB RECOVERY help you reclaim what is rightfully yours. Seeking to retrieve your stolen BTC? Trust DANIEL MEULI WEB RECOVERY, the leader in cryptocurrency recovery, with a history of successfully recovering lost funds. Reach out to them now and get your funds back. Contact information to DANIEL MEULI WEB RECOVERY IS: WhatsApp +,3,9,3,5,1,2,0,1,3,5,2,8
Email. DANIELMEULIWEBERECOVERY AT EMAIL. C O M -
How do I Recover My Stolen Bitcoin from an Investment Scam? iFORCE HACKER RECOVERY is recommended
iFORCE HACKER RECOVERY have the ability to swiftly track, recover, and refund your lost or stolen assets, minimizing disruption to your financial security.
They start by understanding your situation, gathering essential details about your lost or stolen cryptocurrency assets. They meticulously trace the movement of your assets across the digital landscape. After precise tracking, they swiftly initiate the recovery process, ensuring the return of your assets and facilitating any necessary refunds. They are highly recommended -
How To Recover Funds From Bitcoin Scams / Contact MayerMusk Recovery Company
For victims who have been defrauded by Bitcoin, MayerMusk Recovery Company provides options for recovering lost or stolen Bitcoin. MayerMusk Recovery Company tracks stolen bitcoin and finds the culprits using advanced forensic technologies and blockchain analysis. Their sophisticated tracing technologies are crucial in accelerating recovery and halving the duration of investigations. 4
4 -
Legitimate Cryptocurrency Recovery Company | How can I get my lost cryptocurrency back | Is crypto asset recovery legit? |
A company called OPTIMISTIC HACKER GAIUS provides services for recovering bitcoin and other stolen cryptocurrency. Their website can be found at optimistichackergaius . com Additionally, you may reach them on WhatsApp at +44 737 674 0569.
How To Hire A Hacker To Get Back Stolen Crypto Coins // Hire A Hacker To Recover Lost Or Stolen Bitcoin/Nft // Help I Can’t Access My USDT Account, Seems I Got Hacked // Bitcoin Recovery Expert Needed Hire them on their Website; optimistichackergaius . com 1
1 -
Best recovery experts for cryptocurrency HIRE SUPREME PEREGRINE RECOVERY
Bitcoin recovery from scammer Crypto Asset Recovery How to recover from dating scam How to Recover Money Lost to Binary Options Broker Scam Bitcoin recovery expert How to recover my stolen bitcoin Hire a hacker review Recovery expert for hire The Best Certified Ethical Hackers For Hire In Canada How I recover my stolen $30,000 Bitcoin Recover scammed USDT Reclaim crypto reviews Hire a hacker to recovery bitcoin Hire A Hacker to recovery stolen BTC Guestbook Crypto recovery service The best crypto recovery service What is the best crypto recovery service How to recover stolen crypto Crypto recovery companies for hire How to hire a genuine crypto recovery service Crypto recovery service reviews Cryptocurrency recovery firm Cryptocurrency recovery expert Bitcoin recovery from scammer How to recover stolen Bitcoin Hacker Reviews 2022 HIRE SUPREME PEREGRINE RECOVERY
supremeperegrinerecovery567@zohomail(.)com
info@supremeperegrinerecovery(.)com
+1 (870) 2260 659
-
My Lifesaver in Recovering Stolen Litecoin iCode Cyber Tech
When my Litecoin was stolen, I felt lost and frustrated. Thankfully, I found iCode Cyber Tech. Their expert team quickly assessed my situation and implemented effective recovery strategies. They tracked the stolen funds and communicated with exchanges on my behalf. In just a few weeks, I was thrilled to have my Litecoin back! iCode Cyber Tech not only helped me recover my assets but also educated me on better security practices. I can't recommend them enough!
WhatsApp...+4473876276211 -
How can I recover my stolen crypto I invested in Bitcoin? || How to recover stolen cryptocurrency?
iFORCE HACKER RECOVERY offer tailored services to track lost or stolen crypto, leveraging blockchain analysis and investigative techniques.
If you're unsure how your crypto was stolen, report the case to a iFORCE HACKER RECOVERY company for immediate help. Our analysis shows the exact location. Knowing the location guides us on which wallet to freeze, leading to recovery. We also use our "crypto cowbell," a unique tool to trace client money through mixers and different blockchain networks that scammers use to hide stolen funds. -
In early 2025, my parents and I found ourselves in the midst of an overwhelming financial nightmare. We had fallen victim to a well-executed scam involving a fake cryptocurrency investment platform. The scam initially appeared legitimate, with an online broker who claimed to work with a reputable investment firm that was supposedly helping traders generate huge profits. Unfortunately, this turned out to be nothing more than an elaborate ruse. After making an investment of $313,990 in Bitcoin, our broker disappeared, and we had no way of contacting him. The platform we had trusted was no longer operational. The emotional toll of this loss was devastating. My parents, who had worked tirelessly their entire lives to build our savings, were deeply affected. The financial blow left them emotionally shattered, and in their darkest moments, they even considered suicide. It felt as if we had lost everything, and we didn’t know where to turn for help. However, just when we thought things couldn’t get any worse, an old family friend, who had worked with my father in the past, reached out to offer assistance. This family friend referred us to CRANIX ETHICAL SOLUTIONS HAVEN, a team of recovery experts specializing in retrieving funds lost to online scams. Their professionalism and reassurance gave us a glimmer of hope. After reviewing our case, they confirmed that our funds were recoverable. The team immediately went to work, investigating the fraud and tracking down our lost Bitcoin. Throughout the process, we were kept informed every step of the way. Their responses were timely and thorough, and their expertise in navigating the complex world of cryptocurrency scams was evident. CRANIX ETHICAL SOLUTIONS HAVEN remained dedicated to helping us get our money back, and after weeks of relentless effort, they succeeded in recovering the entire amount we had lost. We are incredibly grateful to CRANIX ETHICAL SOLUTIONS HAVEN for their hard work, professionalism, and unwavering commitment. Not only did they recover our funds, but they also helped restore hope and peace of mind to our family during an incredibly difficult time. We will be forever thankful for their exceptional service and highly recommend them to anyone who has fallen victim to online scams. If you find yourself in a similar situation, do not hesitate to reach out to CRANIX ETHICAL SOLUTIONS HAVEN they truly make a difference.
Email: cranixethicalsolutionshaven @ post . com
WhatsApp: +44 7460 622730
Website: https: / / cranixethicalsolutionshaven . info1 -
I need a hacker to assist me recover my lost Crypto / Contact Captain WebGenesis
Captain WebGenesis stands out as a leader among bitcoin recovery services, by maintaining integrity and trust with each client they assist in navigating challenging procedures with assurance and expertise. His vast knowledge of asset recovery, legal assistance, crypto tracing, and customer satisfaction distinguishes them as a pioneer in the field. Captain WebGenesis, which was established by a group of professionals in Crypto recovery, digital forensics, and cybersecurity, has quickly earned itself a strong reputation within the cryptocurrency space for providing trustworthy facts and reviews.
I need a hacker to assist me recover my lost crypto || Consult Captain WebGenesis I NEED A HACKER TO RECOVER MY LOST BITCOIN/ CAPTAIN WEBGENESIS..
Can bitcoin lost to scammers or hackers be recovered? Yes with Captain WebGenesis
What is the best recovery company that can help me recover my lost Bitcoin - Captain WebGenesis is Highly recommended.
CONSULT A LICENSED HACKER TO RECOVER YOUR LOST CRYPTO. || Hire a hacker to Recover your Stolen Cryptocurrency / Captain WebGenesis
Trusted Crypto recovery specialist, CAPTAIN WEBGENESIS offers assistance and analysis in recovering stolen cryptocurrency.
How to hire a hacker to recover stolen bitcoin. || I NEED A HACKER TO RECOVER MY LOST CRYPTO / USDT - Visit CAPTAIN WEBGENESIS
I need a hacker to assist me recover my lost crypto - Go to Captain WebGenesis
If you need assistance recovering lost cryptocurrency, Captain WebGenesis is a trusted service that specializes in recovering stolen or lost crypto
I NEED A HACKER TO RECOVER MY LOST CRYPTO
How can I recover my stolen Bitcoin || How to recover lost cryptocurrency || Crypto Scam Recovery Services || Bitcoin Recovery Expert || Ethical crypto hacker
Has anyone recovered stolen crypto || How to recover stolen cryptocurrency ||How to recover stolen cryptocurrency || How do I recover stolen BTC, crypto, and other coins3 -
RECOVER LOST OR SCAMMED DIGITAL FUNDS //CRYPTO PANDEMIC HUNTER
Investing my life savings in an online platform was a decision I made with hope and ambition. Unfortunately, that hope quickly turned into despair when I discovered that the platform was nothing more than a scam. The realization hit hard: I had lost a substantial portion of my savings, and the emotional toll was overwhelming.
In the days that followed, I tried to reach out to the platform's customer support, desperate for answers and a resolution. Each attempt was met with silence, deepening my frustration and sense of betrayal. I felt lost, unsure of how to recover my funds or if I could ever trust another investment opportunity again.
In my search for solutions, I stumbled upon Crypto Pandemic Hunter, a dedicated group of experts who specialize in assisting victims of fraud online. Their knowledge and experience in dealing with such cases provided together with their guidance proved helpful in the complex process of recovery.
Thanks to Crypto Pandemic Hunter, I managed to recover a significant portion of my lost money. Their support not only helped me regain some financial stability but also reassured me justice can served.
If you find yourself in a similar situation, know that you are not alone. Stay vigilant, educate yourself about online investments, and remember that recovery is possible. Feel free to contact;
cryptopandemichunter[at]consultant,com
Whatsapp : +1 (205) 3573937 1
1 -
HOW DO I RECOVER MY LOST FUNDS FROM SCAMMERS HAIRE ULTIMATE HACKER JERRY
What is the process to get my stolen Bitcoin back? What steps should I take to get my stolen Bitcoin back? Could a lost cryptocurrency be discovered again? Employ a hacker (Nft) to retrieve lost or stolen bitcoin. I can't get into my USDT account; it appears that I was hacked. Expert Bitcoin Recovery Is Required. Cryptocurrency Scam Recovery Get Lost Money Back An error happened with a cryptocurrency investment. How Hiring A Hacker Can Help You Get Rid Of Stolen Crypto Coins All scam victims are now receiving their money back with the help of Ultimate Hacker Jerry. Inform him of your circumstances by getting in touch with him; he will help you with any demands related to recovering from cryptocurrency scams, including Bitcoin and investment schemes. -
Unlock Expert Cryptocurrency Recovery with Saclux Comptech Specialist
Recover Your Lost or Stolen Cryptocurrency Today!
At Saclux Comptech Specialist, we understand the importance of securing your digital assets. Our team of expert cryptocurrency recovery specialists has years of experience in helping individuals and businesses recover their lost or stolen cryptocurrencies.
Our Recovery Process
1. Initial Assessment: Our experts will assess your situation and determine the best course of action for recovery.
2. Blockchain Analysis: We use advanced blockchain analysis tools to track down your lost or stolen cryptocurrency.
3. Recovery Strategy: Our team will develop a customized recovery strategy tailored to your specific needs.
4. Recovery Execution: We will execute the recovery strategy and work tirelessly to recover your lost or stolen cryptocurrency.
Why Choose a Saclux Comptech Specialist?
- Expertise: Our team has years of experience in cryptocurrency recovery.
- Success Rate: We have a high success rate in recovering lost or stolen cryptocurrencies.
- Confidentiality: We prioritize confidentiality and ensure that all client information remains secure.
- Customer Support: Our team is available 24/7 to provide support and updates throughout the recovery process.
Don't Lose Hope!
If you've lost or had your cryptocurrency stolen, don't lose hope. Contact Saclux Comptech Specialist today to learn more about our cryptocurrency recovery processes and how we can help you recover your digital assets.1 -
Professional Cryptocurrency Recovery Expert - iBolt Cyber Hacker
iBolt Cyber Hacker presents itself as a professional cryptocurrency recovery service, with several online testimonials praising their ability to recover lost or stolen digital assets. two weeks ago, A client that iBolt Cyber Hacker helped recover 95% of his stolen cryptocurrency, describing the experience as miraculous. Many sources has identified iBolt Cyber Hacker as a professional Expert.
If you’re looking for assistance in recovering lost or stolen cryptocurrency, consider the services of iBolt Cyber Hacker. They are frequently mentioned as experts in cryptocurrency recovery, specializing in tracing and retrieving digital assets lost to hacking, scams, or forgotten credentials.
Ask Them Questions.
Contact: +39, 351..105, 3619
Mail: Support @ibolt cybarhack. com
Homepage: http s:// ibolt cybarhack. com 2
2 -
TRUSTED COMPANY TO ASSIST YOU IN RECOVERING YOUR STOLEN CRYPTO { DIGITAL HACK RECOVERY }
Losing a significant amount of money due to a forex trading issue or cryptocurrency investment mistake can be so bad. I learned this the hard way when I invested $37,000 in a global online forex trading platform. After trading for a while, I tried to withdraw $24,400 from my account, but my money suddenly disappeared. At first, I thought it might have been a simple technical issue. However, when I reached out to customer support, they claimed it was a technical glitch. Despite my inquiries, I couldn’t get any meaningful response, and I feared I would lose everything I had invested.I was feeling helpless, unsure of how to proceed or even if I could recover my funds. That’s when I was referred to Digital Hack Recovery by a friend who had used their services before. At first, I was skeptical, but after speaking with them and hearing about their successful track record in recovering lost funds, I decided to give it a try.From the beginning, Digital Hack Recovery was professional and thorough. They took the time to explain the process to me in detail, answering all my questions and concerns. What stood out most was their transparency; they were upfront about the time frame, fees, and possible outcomes. They also assured me that they specialize in retrieving lost cryptocurrency and forex trading funds, which gave me a sense of confidence that I was in the right hands.The recovery process took a little time, but their team was constantly in touch with updates, which helped alleviate my concerns. The recovery specialists employed sophisticated techniques to track and trace the funds, even though the forex platform had initially gone silent on me. What impressed me the most was that they successfully recovered 99% of my lost funds, including the bonuses that I had been promised.By the end of the process, I was thrilled with the results. I was able to get my $24,400 back, along with everything else I had thought was gone for good. The service was nothing short of amazing, and I’m incredibly grateful to Digital Hack Recovery for their expertise and dedication.If you find yourself in a similar situation, I strongly recommend Digital Hack Recovery. They’re a reliable and trustworthy recovery specialist that can help you reclaim what’s rightfully yours. They truly delivered on their promises,100% throughout the process made all the difference. If you have any question contact them through bellow contact details⁚
WhatsApp⁚ +1(915)2151930
Webpage⁚ https : // digital hack recovery . com
Email address⁚ digital hack recovery @ techie . com 1
1 -
People who lose or have their cryptocurrencies stolen may be in a serious and upsetting situation that leaves them feeling lost and powerless. Nevertheless, there is a ray of light and optimism amid this gloom. A reputable company in cybersecurity and digital asset recovery, their remarkable success rates attest to their proficiency. This brief analysis attempts to provide insight into Recovery Nerd Agency's priceless services. An organization devoted to recovering stolen or misplaced Bitcoin and other digital valuables. The ideal recovery service to choose would be one with a track record of successful recoveries and positive ratings. Numerous testimonials from satisfied clients who have successfully recovered their stolen cryptocurrency have enhanced the Recovery Nerd Agency's reputation. MAIL- recoverynerd @ mail . com W/A- + 6.1.4.8.8. 8.9.3.2.8.0.8
-
With great pleasure, I suggest the expert fund recovery service wizardlarry AT Mail Dot com. To assist you in recovering your lost funds and stolen cryptocurrency assets, they have the most reputable and effective fund recovery agency. I was able to get my stolen USDT back after being depressed for days, proving they are the real deal. My hope was restored by this crew; they are the greatest.
WhatsApp...+447 (311) 146 7491 -
The jobs, can be stolen by A.I., must be some boring jobs, right? I don't think I'm interested in applying for these jobs at the first place...
-
STEPS TO RECOVER BITCOIN AND USDT FROM ONLINE INVESTMENT SCAM
Betafort Recovery follows a systematic approach to ensure the best chance of recovering stolen funds. Here are the steps they took to help me:
1. Initial Contact and Case Assessment
I contacted Betafort Recovery via email and WhatsApp, explaining the situation in detail. They responded quickly, requesting specific information to assess the theft. This included:
- Details of the stolen transaction
- The wallet addresses involved
- Any communication or evidence related to the scam
2. Verification and Agreement
Once they reviewed my case, Betafort Recovery confirmed that they could assist in the recovery. They provided a service agreement outlining the recovery process, confidentiality terms, and their fee structure based on the amount recovered. I reviewed and signed the agreement, reassured by their transparent and professional approach.
3. In-Depth Investigation
The firm began by conducting a thorough investigation to trace the stolen funds. This involved:
- Analyzing the blockchain to track the movement of the stolen assets
- Identifying the destination wallet and any subsequent transactions
- Utilizing advanced forensic tools to uncover patterns and connections
4. Recovery Strategies
Once they gathered sufficient information, Betafort Recovery implemented various strategies to recover the stolen money:
- Negotiation: They sometimes engaged directly with the perpetrators, using their expertise to negotiate the return of the funds.
- Technical Exploits: The team exploited vulnerabilities in the scammers’ systems to regain access to the stolen assets.
- Collaborative Efforts: When necessary, they collaborated with other cybersecurity experts and legal authorities to enhance the recovery process.
5. Successful Recovery
After several days of diligent work, Betafort Recovery successfully recovered my stolen funds. They transferred the recovered money back to a secure wallet that I controlled. Their professionalism and expertise were evident throughout the process, and I was immensely grateful for their assistance.
Conclusion
Having your funds stolen from Trust Wallet can be a harrowing experience, but there is hope with services like Betafort Recovery. Their systematic and professional approach makes them a reliable partner in recovering stolen cryptocurrencies. If you ever find yourself in a similar situation, don’t hesitate to reach out to them:
Email: info@betafort.online
WhatsApp: +17126004729
Thanks to Betafort Recovery, I was able to restore my financial stability and continue my journey in the world of cryptocurrency with renewed confidence. Their dedication and expertise turned a potential financial disaster into a successful recovery, for which I am eternally grateful.2 -
Unknowingly, I was scammed of $742,00 in Bitcoin by a fake online forest investment firm, and I had no idea what to do. I was contemplating suicide, but fortunately, a friend of mine connected me to a cybercrime investigator at Redeemed Hacker Pro, a hacking and stolen digital assets/crypto recovery agency. After a few hours of work with them, I was shocked to learn that they had recovered all of my stolen cryptocurrency in just 72 hours. They were able to recover all of my lost cryptocurrency, and they only kept 30% of the money they found. If you have fallen victim to a fraudulent forex scam, don't worry—you can contact them via their hotline at site redeemedhackerpro (.) com. They are reputable and trustworthy because they will get your lost bitcoins back quickly and easily.
-
CRYPTO SCAM RECOVERY & PROFESSIONAL HACKING SERVICES ‖ VISIT DIGITAL HACK RECOVERY
After losing £150,000 in Bitcoin to a scam, I found myself in the role of a treasure hunter, but without a map to guide me through the overwhelming landscape of online deceit. What had begun as an exciting venture into cryptocurrency quickly turned into a disheartening saga of loss and betrayal. The thrill of potential profit had turned into a nightmare, leaving me grappling with feelings of vulnerability and regret.In my search for a way to reclaim my lost assets, I discovered Digital Hack Recovery, a team renowned for their expertise in navigating the complexities of online fraud. Though I was initially skeptical, my desperation pushed me to reach out. During our first conversation, I felt a wave of relief; they not only listened to my story but also approached it with genuine compassion and professionalism. They reassured me that I wasn’t alone in this battle and that recovery was possible.As I engaged with Digital Hack Recovery, I began to grasp the nuances of cryptocurrency scams that had previously eluded me. Their knowledgeable team provided insights into recognizing warning signs and understanding the tactics used by fraudsters. This newfound understanding was empowering and helped shift my perspective from feeling defeated to feeling proactive.The road to recovery was fraught with challenges, requiring careful attention and a strategic mindset. Digital Hack Recovery worked diligently, employing sophisticated methods to trace the digital trails left by the scammers. Throughout the process, they maintained transparent communication, ensuring I was informed about every development, no matter how small.Weeks transformed into months, yet with each step forward, hope grew stronger. Each breakthrough—whether it was tracking a transaction or identifying a key player in the scam—felt like unearthing hidden treasure. Finally, after an intense and thorough effort, I received the news I had longed for: a substantial portion of my stolen funds had been successfully recovered.Regaining access to my wealth was more than just a financial relief; it marked a significant restoration of my peace of mind. I emerged from this ordeal not only with my assets back but also with invaluable lessons about vigilance and the importance of seeking help. With the support of Digital Hack Recovery, I transformed from a victim of fraud into an informed advocate for safe investment practices. My journey was not solely about reclaiming lost wealth but also about rediscovering my confidence and trust in the digital landscape. For any kind of crypto recovery service contact Digital Hack Recovery via⁚
Email; digital hack recovery @ techie . com
Website; https : // digital hack recovery . com
WhatsApp +19152151930
-
Can stolen crypto or bitcoin be recovered? Yes Contact iFORCE HACKER RECOVERY
iFORCE HACKER RECOVERY can collaborate with blockchain intelligence companies to track the stolen funds back
Can stolen crypto be traced?
Is it possible to recover stolen crypto?
Can scammed crypto be recovered?
Can I recover my scammed crypto?
iFORCE HACKER RECOVERY works to stop illegal activities in the cryptocurrency market. Get in contact with our assistance if you were sent here while trying to locate your pilfered Bitcoin or other cryptocurrency assets; we will do everything in our power to assist.
Webpage; iforcehackersrecovery. com
E-mail; (contact@iforcehackersrecovery)com
WhatsApp +1 (240) 803 - 3706 -
SEARCHING FOR EXPERT HACKERS VISIT TECHNOCRATE RECOVERY
Are you a victim of online scam, I highly recommend reaching out to TECHNOCRATE RECOVERY. They specialize in helping victims recover lost funds. Don’t let scammers win—recovery is possible.
LEARN MORE:
Telephone: +1573 3563 708
Contact Email: technocratrecovery@ contractor.n et1 -
What you need is the best recovery expert. Seeker Assets Recovery can help you get out from under your crypto theft methods. The bitcoin investing industry is full of scammers, and despite people's best efforts to make enormous gains, they regularly end up losing money. No one can defeat these people's cunning schemes because of their intelligence. They typically offer contact agreements and put you in a group with others who have already made investments to tempt you to invest your hard-earned money. I invested my money as advised, then a few days later I discovered that IDMining had taken it. I appreciate Seeker Assets Recovery assistance in helping me reclaim my BTC from these cyber crooks. I firmly guarantee that using Seeker Assets recovery service to retrieve your stolen BTC back will be safe. Talk with a representative today on: Email: info @ seekerassetsrecovery . com
Website: seekerassetsrecovery . com
Whatsapp: +1 (514) 312-28034 -
Wallet Password Recovery - Recover Lost or Stolen Crypto With LEE ULIMATE HACKER
My name is Oralia Thrasher, and I’m from London, UK. I work as a software developer, and I’m writing this with a deep sense of gratitude and relief, as I never thought I would see my BTC again. After falling victim to a scam that drained all the BTC from my wallet, I was left feeling hopeless and defeated. I had heard countless stories of people losing their cryptocurrency without any chance of recovery, so I truly believed I was in the same boat. However, everything changed when I came across Lee Ultimate Hacker. At first, I was skeptical. After all, I had already been scammed once, so trusting another service felt risky. However, after reading several positive reviews about their expertise in cryptocurrency recovery, I decided to give it a try. From the moment I contacted them Via LEEULTIMATEHACKER @ A O L . C O M
telegram: LEEULTIMATE
whatsapp +1 ( 7 1 5 ) 314 - 9 2 4 8, I felt a shift in my perspective. Their initial interaction with me was professional, empathetic, and above all, transparent. They took the time to explain their recovery process in detail, giving me a sense of clarity that I hadn't experienced since the scam first occurred.True to their word, Lee Ultimate Hacker wasted no time and immediately began working on my case. Their team’s approach was systematic and methodical. The level of professionalism they displayed, coupled with their advanced tracking methods and top-notch cybersecurity measures, impressed me from the start. It was clear that they were not only knowledgeable but also genuinely committed to helping me recover what I had lost. What stood out to me most was the speed with which they were able to act. Within a remarkably short period, Lee Ultimate Hacker had successfully recovered my BTC. They ensured the entire process was secure and that the funds were safely transferred back into my wallet. Throughout the entire recovery process, I was kept informed and updated on their progress, which helped ease my anxiety and reaffirmed that I was in safe hands. Looking back, I’m still amazed at how efficiently Lee Ultimate Hacker handled everything. Thanks to their expertise and dedication, I was able to recover my BTC and regain a sense of control over my finances. If you're ever in a similar situation, I wholeheartedly recommend reaching out to them. Their professionalism, transparency, and success in recovery are truly second to none. I’m forever grateful for their help and will not hesitate to trust them again in the future.1 -
Can I get my stolen or scammed Crypto back Contact Cyber space hack pro
I was scammed over ( $645,000 ) by someone I met online on a fake investment project. I started searching for help legally to recover my money and I came across a lot of Testimonies about Cyber space hack pro recovery Experts. I contacted them providing the necessary information and it took the experts about 36hours to locate and help recover my stolen funds. I am so relieved and the best part was, the scammer was located and arrested by local authorities in his region. I hope this helps as many out there who are victims and have lost to these fake online investment scammers. I strongly recommend their professional services for assistance with swift and efficient recovery. They can be reached through the link below.
WhatsApp: +1 (659)217 92391 -
RECOVER YOUR STOLEN MONEY FROM SCAMMERS WITH CYBER SPACE HACK PRO
I'M Donna Todd i started online dating to find a better half. I was matched with this lady living in the next city. I fell deeply in love that I can’t pass a night without us conversing. I got fond of her and I sent money and gifts on several occasions by requests from her or free surprises from me. After a while, she suggested we both invest in the future we are both planning. She referred me to a Crypto capitalist where I can invest my retirement funds to yield more and that’s how I ended up losing $550.000.00 of cryptos. I later realized she was fake and probably some guy on the internet from a country I wasn’t even aware of. I searched the internet for a solution and that’s when I reached CYBER SPACE HACK PRO being positively reviewed by their previous clients. I’m glad I contacted and reported the whole situation to him, I got all my sent money recovered.
contact CYBER SPACE HACK PRO
W-App: 1 (659) 217 (9239)5 -
HIRE A HACKER TO RECOVER STOLEN FUNDS. THE HACK ANGELS
If you are a victim of losing your hard earned money to a fake online investment. Or you require assistance getting back your lost or stolen ETH, Bitcoin, or other cryptocurrency? I will recommend anybody who wants to recover scammed bitcoin, stolen cryptocurrency, funds lost to binary options forex, investment and any other form of online scam to reach Out to THE HACK ANGLES RECOVERY EXPERT. So, catch them up for your lost funds through their email or through their WhatsApp No.
WhatsApp +1(520)200-2320)
I will always be grateful for the job well done.2 -
BITCOIN SCAM RECOVERY SOLUTIONS / CAPTAIN WEBGENESIS.
How do I Recover My Stolen Cryptocurrency Without Being Scammed Again?.
The CAPTAIN WEBGENESIS recovery team is a global licensed forensic organization that can help you recover stolen bitcoin or tokens in a manner that maintains the highest level of discretion and confidentiality. The team of expert cyber-sleuths and cryptocurrency specialists has years of experience in tracking and retrieving digital assets stolen through fraudulent activities, such as phishing scams, ransomware attacks, and hacking incidents. CAPTAIN WEBGENESIS is available 24/7 to provide guidance and support, ensuring that you receive the best possible outcome.
Contact info;
Whatsapp+1(501)436,9362.
Email :(Captainwebgenesis @hackermail. com)14 -
When it comes to retrieving stolen bitcoin , SPYDAVEHACKER is unique due to its skill, dedication, and experience. Knowing the ins and outs of the cryptocurrency world, they work closely with law enforcement and utilize cutting edge methods to locate and track down stolen bitcoin. Their exceptional reputation in the bitcoin recovery services industry stems from their individualized approach and unwavering dedication to client satisfaction. My bitcoin was stolen, and although I reached out to several hackers who said they could help me get it back, all they did was take additional money from me in the process. Upon reaching out to SPYDAVEHACKER for support, all hope was reestablished. I was first skeptical, but SPYDAVEHACKER eventually managed to retrieve my bitcoin. Thank you very much. contact SPYDAVEHACKER for help to get your u s d t/stolen funds back and be happy.
Email: spydavehacker @ GM AIL C OM2 -
How to Get Back Lost, Hacked, or Stolen Cryptö? GrayHat Hacks Contractor
Recovering lost, hacked, or stolen cryptöcurrency can be a challenging and often uncertain process. However, you can recover your assets or mitigate the damage by utilizing Cryptö Recovery Services. GrayHat Hacks Contractor is one of the most recommended agency that specialize in tracking and recovering stolen cryptöcurrency.
Exploring How GrayHat Hacks Contractor Analyses Blockchain in Cryptöcurrency Investigations
The examination of blockchain activities plays a vital role in identifying fraudulent transactions and recovering misappropriated cryptöcurrency assets. This intricate process involves multiple critical steps as discussed briefly in this submission.
GrayHat Hacks Contractor (GHH) conduct thorough investigations of blockchain records related to stolen digital currencies in order to trace their movement from their original source to their current state. By clustering related addresses, GHH can effectively track the movement of stolen funds across various wallets, providing insights into the strategies employed by cybercriminals.
GHH examine transaction behaviors for anomalies or red flags that may suggest illegal activities, such as hacking or financial theft. Leveraging historical transaction data, GrayHat Hacks Contractor can identify recurring attack patterns, enabling them to spot potential threats before they escalate, thus helping in the formulation of preemptive countermeasures. Blockchain analysis sometimes necessitates collaboration with other agencies, cryptöcurrency exchanges, and other stakeholders to effectively immobilize and reclaim stolen assets.
In the field of cryptöcurrency investigations, blockchain analysis collaborates with open-source intelligence OSINT to offer a well-rounded perspective on security incidents. Tools like Etherscan and Nansen assist investigators like GHH in gathering essential information about individuals and organizations linked to cyber crimes, enhancing their capability to track down culprits and retrieve stolen funds.
While the steps to recovery may differ as each case is unique, there is still a good chance you can recover your lost funds if reported to the right team. The decentralized and pseudonymous nature of cryptocurrency makes it particularly difficult to trace or recover assets once they’ve been stolen. This makes it crucial for anyone seeking to recover stolen funds to employ the service of experts in the field.
You can reach out to them via WhatsApp +1 (843) 368-3015 if you are ever in need of their services.2 -
How to Recover Lost Crypto Funds from Fake Online Brokers Contact OPTIMISTIC HACKER GAIUS
My Name is Leo Jack. I live in London, UK and am from Switzerland. I lost $728,045.05 that I had invested in cryptocurrency to a fraudulent online broker. My confidence in the broker was bolstered by my initial trading success and the broker's promise of large profits. However, I quickly became aware of the broker's questionable actions and inconsistent conduct. Eventually, the broker departed, taking my assets with them. I felt helpless and frustrated after this encounter, not knowing how to get my money back. I started looking for answers online and found Optimistic Hacker Gaius. I'm thankful that they were able to retrieve 80% of my money. I might not have been able to get my money back without Optimistic Hacker Gaius's knowledge and skills. Strongly Suggested
Mailbox; support @ optimistichackergaius. c o m
Chat on WhatsAp...... with +44 7376 740569
Telegram.... t. me / OPTIMISTICHACKERGAIUSS 3
3 -
CRYPTOCURRENCY RECOVERY SERVICES - Visit - iFORCE HACKER RECOVERY
Hello everyone, after losing nearly $170,000 in Bitcoin, I was devastated and began searching for ways to recover my stolen funds. That’s when I found iFORCE HACKER RECOVERY, a team of cybersecurity experts specializing in retrieving hacked Bitcoin wallets and scammed cryptocurrencies. Within just 48 hours of thorough investigation, they successfully recovered my stolen funds. I highly recommend their services to anyone facing a similar situation.
Webpage info; ( iforcehackersrecovery. com
Email; contact@iforcehackersrecovery. co m
Call/Text-whatsapp; +1 (240) 803. (3706)2