Join devRant
Do all the things like
++ or -- rants, post your own rants, comment on others' rants and build your customized dev avatar
Sign Up
Pipeless API

From the creators of devRant, Pipeless lets you power real-time personalized recommendations and activity feeds using a simple API
Learn More
Search - "nsa"
-
So, someone submitted a 'bug' to Mozilla.
As some of you may know, in the next year, the new mass surveillance law in the Netherlands is going into effect.
Another fun fact is that the dutch security agencies/government have their own CA (Certificate Authority) for SSL/TLS certificates.
The new law says that the AIVD (dutch NSA/GCHQ equivilant) is allowed to hack into systems through obtained certificates and also that they're allowed to INTERCEPT TRAFFIC THROUGH OBTAINED PRIVATE SSL/TLS KEYS.
So someone actually had the fucking balls to submit a fucking issue to Mozilla saying that the Dutch State certs shouldn't be accepted anymore when the new mass surveillance law gets into place.
This person deservers a fucking medal if you ask me.68 -
Me: *puts small piece of tape over webcam*
NSA: Okay guys, shut it all down. No way we can record from the microphone, log keys, access the file system, USB devices, network data or watch the screen. He did the tape.23 -
(overheard parents talking)
Mum: I'm worried about our son, I guess he was hacking today
Dad: What? [Chuckle] No. He's not that grown up enough. Prolly programming.
Mum: But, the screen was all blue and there was nothing but text on it. And then suddenly it went blank. So, I asked him what he was doing and he said it was a BSOD. That sounds scary NSA level stuff.
Dad: it isn't [came out of the room, saw me there]
(And we laughed and laughed and laughed)4 -
*Me Calling the NSA..
[NSA]: Hello, how can I help you !
[ME]: Hello, this is the NSA right?
[NSA]: Yes
[ME]: Since you are recording all phone calls, I have a little request.
[NSA]: And What is that?
[ME]: My mom called me couple hours ago to bring something from the supermarket, her phone is off.. What did she told me to bring?
[NSA]: beep..beep..beep10 -
NSA: Hey, its looks like you a bit lonely
Me: Yeah sort of
CIA: (Retrieves list of facebook friends), why not hook up with these people
Me: Not interested
FBI: The girl across your room seems to be interested in you
Me: Nah not interested
CIA: We can send someone to keep you company if you want
Me: thanks, not interested
NSA: A girl winked at you at the cafe yesterday
Me: Didn't notice
CIA: What of the lady you spoke to on the phone earlier
Me: Too old
FBI: Can you please move your webcam to the left a little
Me: Bruuuuuhhhhhh!!!19 -
Meanwhile at NSA:
Alice: Uhm... Bob? I lost my SSH key...
Bob: *facepalms*
Alice: ... but i still have the public key! Could you please recalculate the private one for me?
Bob: Sure, give me a second. I'll fax it to you when it's ready.
Me: *wakes up from nightmare*13 -
CIA, NSA... if anyone 's listening.. Can you guys please tell me my root password.. :/.. I forgot..10
-
Facebook publicly announced that it won't build a backdoor into its services for the intelligence agencies as for the latest requests to weaken/remove the encryption.
I can only imagine the intelligence agencies going like this now:
NSA director: Alright, as expected they said no so they won't have more damage to their public image, lets go for plan A 2.0!
NSA employee: Aaaand that is?
NSA director: Serve them a FISA court order requiring them to do this shit anyways but also serve a gag order so they can't tell legally.
NSA employee: Ahh, fair enough, I'll get that rolling. By the way, how did we do this with WhatsApp's encryption again?
NSA director: Oh that one was simple. There's a backup function which nearly everyone uses on either Android/iOS which does plaintext backups to Google Drive/iCloud.
NSA employee: Oh, okay. How do we access that data again?
NSA director: PRISM/XKeyScore!
NSA employee: Right, but then still the issue of how we even collect the encrypted messages from Facebo...
NSA director: PRISM/XKeyScore as well, don't worry about that.
NSA employee: But, how'd we justify this....?
NSA director: We probably never have to as these programs operate outside of the public view but otherwise just call terrorism/pedophelia... BAM, done.
NSA employee: Gotya, let's put this into motion!22 -
Dude: Come on man, Google and/or Facebook are not actively listening to us, I mean, we're not terrorists.
Me: Ok, Google
Google Asistant: How can I help you?
Dude: ._.4 -
Started talking with someone about general IT stuff. At some point we came to the subject of SSL certificates and he mentioned that 'that stuff is expensive' and so on.
Kindly told him about Let's Encrypt and also that it's free and he reacted: "Then I'd rather have no SSL, free certificates make you look like you're a cheap ass".
So I told him the principle of login/registration thingies and said that they really need SSL, whether it's free or not.
"Nahhh, then I'd still rather don't use SSL, it just looks so cheap when you're using a free certificate".
Hey you know what, what about you write that sentence on a whole fucking pack of paper, dip it into some sambal, maybe add some firecrackers and shove it up your ass? Hopefully that will bring some sense into your very empty head.
Not putting a secure connection on a website, (at all) especially when it has a FUCKING LOGIN/REGISTRATION FUNCTION (!?!?!?!!?!) is simply not fucking done in the year of TWO THOUSAND FUCKING SEVENTEEN.
'Ohh but the NSA etc won't do anything with that data'.
Has it, for one tiny motherfucking second, come to mind that there's also a thing called hackers? Malicious hackers? If your users are on hacked networks, it's easy as fuck to steal their credentials, inject shit and even deliver fucking EXPLOIT KITS.
Oh and you bet your ass the NSA will save that data, they have a whole motherfucking database of passwords they can search through with XKeyScore (snowden leaks).
Motherfucker.68 -
When you are a coder and still go to school...
FAQ:
1. Can you hack?
2. Did you already hack the NSA?
3. Did you ever enter the darknet?18 -
When I still studied, quite some people found me paranoid.
One of my friends started whispering 'NSA is watching' whenever he walked by me and after a while, whenever any of my friends were near me AND near a camera or whatsoever, they all whispered that same phrase.
Then I thought fuck it and just joined with whispering that. So throughout the whole day everyone would whisper that around me and I just participated 😆9 -
Mom : there's a letter for you. It's from USA. Are you in trouble ?
Me : oooouh shit what have I done ?
Fiuuuuu..NSA still not tracking my buggy code 😂 9
9 -
*joins devrant*
*Deletes fb and all social stuff*
*all friends use facebook messenger*
*quietly installs again*
(First world problems)20 -
I hate Munich. Instead of using Windows, the city administration had built their own Linux distro called LiMux for all of the ~30000 city's computers. They invested years into developing it, because, hey, it's open source! Now they used it for four years, and just as Microsoft opens an office in town, they throw it all overboard and go back to Windows. Why? Because, umm, they can't even use MS Word, what all the others use and such.
This is such a bullshit. You had a good thing going here, in times of NSA surveillance and monopolies. Munich is such a capitalistic town. I'm happy to have moved out of it for good.13 -
Apparently this little music player has no transmitter, receiver, microphone nor camera, pity on you NSA!
 12
12 -
I'm getting ridiculously pissed off at Intel's Management Engine (etc.), yet again. I'm learning new terrifying things it does, and about more exploits. Anything this nefarious and overreaching and untouchable is evil by its very nature.
(tl;dr at the bottom.)
I also learned that -- as I suspected -- AMD has their own version of the bloody thing. Apparently theirs is a bit less scary than Intel's since you can ostensibly disable it, but i don't believe that because spy agencies exist and people are power-hungry and corrupt as hell when they get it.
For those who don't know what the IME is, it's hardware godmode. It's a black box running obfuscated code on a coprocessor that's built into Intel cpus (all Intell cpus from 2008 on). It runs code continuously, even when the system is in S3 mode or powered off. As long as the psu is supplying current, it's running. It has its own mac and IP address, transmits out-of-band (so the OS can't see its traffic), some chips can even communicate via 3g, and it can accept remote commands, too. It has complete and unfettered access to everything, completely invisible to the OS. It can turn your computer on or off, use all hardware, access and change all data in ram and storage, etc. And all of this is completely transparent: when the IME interrupts, the cpu stores its state, pauses, runs the SMM (system management mode) code, restores the state, and resumes normal operation. Its memory always returns 0xff when read by the os, and all writes fail. So everything about it is completely hidden from the OS, though the OS can trigger the IME/SMM to run various functions through interrupts, too. But this system is also required for the CPU to even function, so killing it bricks your CPU. Which, ofc, you can do via exploits. Or install ring-2 keyloggers. or do fucking anything else you want to.
tl;dr IME is a hardware godmode, and if someone compromises this (and there have been many exploits), their code runs at ring-2 permissions (above kernel (0), above hypervisor (-1)). They can do anything and everything on/to your system, completely invisibly, and can even install persistent malware that lives inside your bloody cpu. And guess who has keys for this? Go on, guess. you're probably right. Are they completely trustworthy? No? You're probably right again.
There is absolutely no reason for this sort of thing to exist, and its existence can only makes things worse. It enables spying of literally all kinds, it enables cpu-resident malware, bricking your physical cpu, reading/modifying anything anywhere, taking control of your hardware, etc. Literal godmode. and some of it cannot be patched, meaning more than a few exploits require replacing your cpu to protect against.
And why does this exist?
Ostensibly to allow sysadmins to remote-manage fleets of computers, which it does. But it allows fucking everything else, too. and keys to it exist. and people are absolutely not trustworthy. especially those in power -- who are most likely to have access to said keys.
The only reason this exists is because fucking power-hungry doucherockets exist.26 -
A group of Security researchers has officially fucked hardware-level Intel botnet officially branded as "Intel Management Engine" they did so by gathering it all the autism they were able to get from StackOverflow mods... though they officially call it a Buffer Overflow.
On Wednesday, in a presentation at Black Hat Europe, Positive Technologies security researchers Mark Ermolov and Maxim Goryachy plan to explain the firmware flaws they found in Intel Management Engine 11, along with a warning that vendor patches for the vulnerability may not be enough.
Two weeks ago, the pair received thanks from Intel for working with the company to disclose the bugs responsibility. At the time, Chipzilla published 10 vulnerability notices affecting its Management Engine (ME), Server Platform Services (SPS), and Trusted Execution Engine (TXE).
The Intel Management Engine, which resides in the Platform Controller Hub, is a coprocessor that powers the company's vPro administrative features across a variety of chip families. It has its own OS, MINIX 3, a Unix-like operating system that runs at a level below the kernel of the device's main operating system.
It's a computer designed to monitor your computer. In that position, it has access to most of the processes and data on the main CPU. For admins, it can be useful for managing fleets of PCs; it's equally appealing to hackers for what Positive Technologies has dubbed "God mode."
The flaws cited by Intel could let an attacker run arbitrary code on affected hardware that wouldn't be visible to the user or the main operating system. Fears of such an attack led Chipzilla to implement an off switch, to comply with the NSA-developed IT security program called HAP.
But having identified this switch earlier this year, Ermolov and Goryachy contend it fails to protect against the bugs identified in three of the ten disclosures: CVE-2017-5705, CVE-2017-5706, and CVE-2017-5707.
The duo say they found a locally exploitable stack buffer overflow that allows the execution of unsigned code on any device with Intel ME 11, even if the device is turned off or protected by security software.
For more of the complete story go here:
https://blackhat.com/eu-17/...
https://theregister.co.uk/2017/12/...
I post mostly daily news, commentaries and such on my site for anyone that wish to drop by there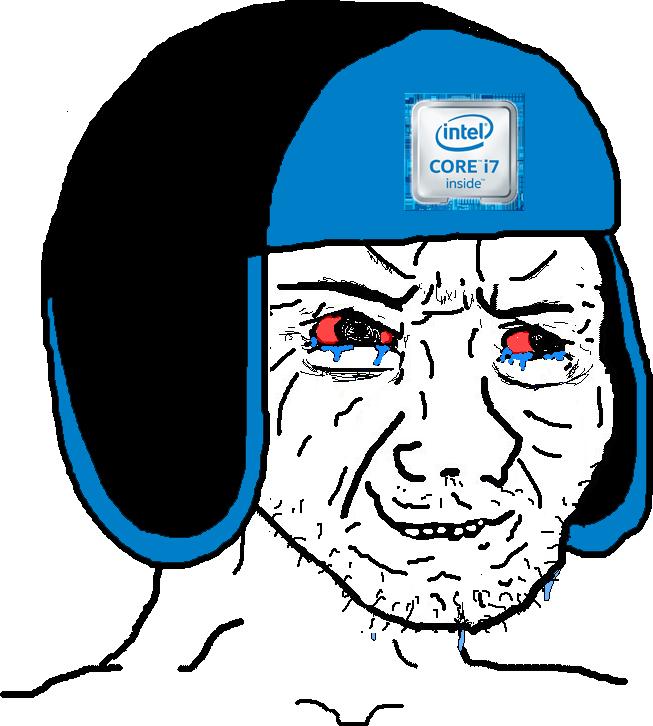 19
19 -
The director of then dutch intelligence agency AIVD (nsa/gchq equivalent) said, because the new mass surveillance law is getting loads of heat/criticism, that before the Dutch citizens should worry about the new surveillance law, they should look into which online companies they trust with their online data and why they trust those companies.
Nice try, sir. You're (probably deliberately) missing the entire point.9 -
I just shat my pants:
I accidentally typed "ebay.vom", and I was redirected to "navigation.nsgnav.com" before sending me to "ebay.com".
In that split second, I thought it redirected me to some "nsa.gov" server.
I almost set my laptop on fire and ran to Mexico.10 -
!rant
The change log from notepad++ update. The last paragraph is the cream!
" The issue of a hijacked DLL concerns scilexer.dll (needed by Notepad++) on a compromised PC, which is replaced by a modified scilexer.dll built by the CIA. When Notepad++ is launched, the modified scilexer.dll is loaded instead of the original one.
It doesn't mean that CIA is interested in your coding skill or in your sex message content typed in Notepad++, but rather it prevents raising any red flags while the DLL does data collection in the background.
It's not a vulnerability/security issue in Notepad++, but for remedying this issue, from this release (v7.3.3) forward, notepad++.exe checks the certificate validation in scilexer.dll before loading it. If the certificate is missing or invalid, then it just won't be loaded, and Notepad++ will fail to launch.
Checking the certificate of DLL makes it harder to hack. Note that once users’ PCs are compromised, the hackers can do anything on the PCs. This solution only prevents from Notepad++ loading a CIA homemade DLL. It doesn't prevent your original notepad++.exe from being replaced by modified notepad++.exe while the CIA is controlling your PC.
Just like knowing the lock is useless for people who are willing to go into my house, I still shut the door and lock it every morning when I leave home. We are in a f**king corrupted world, unfortunately. "2 -
One of my fears is that the NSA will start tracking my every movement because I've search "explode" in Google one too many times... I always forget if the $delimiter comes first or the $string in PHP's function explode().7
-
Once upon a time in Devland, there were two best friends @Alice and @Michelle and they worked together at The DevCo company as developers.
After a tough day handling an @-ANGRY-CLIENT-, they thought that they had to go and @RantSomewhere and so they went to a café. At the café, they ranted about some stupid clients, and @theItalianGuy at the third floor of their office building who never picked up calls, and @thatJavaGuy from the second floor who, they thought, was @notarealDev, and the usual stuff about their work. Somewhere in between, @Alice thought it would be @funvengeance to @hack @theNSA; “@karma is coming to get them”, said @Michelle.
To do this, they knew they’d have to take help from none other than @Gandalf who lived in a nearby @cave. So, the next day, taking a leave from work, @Alice and @Michelle embarked on journey to meet @Gandalf. After about an hour’s drive, they reached @Gandalf’s @cave. @Michelle went ahead to knock on @Gandalf’s rusty cave door. Being a lazy @necromancer, he magically opened his door 2 minutes later. “Who is't dares to disturb me in mine own catch but a wink?” shouted a voice from the back; “We’re two developers from DevCo and we need your help in our mission to @hack @theNSA”, shouted @Michelle. After a few seconds, he replied, ”Hmm… N'rmally I wouldst sendeth thee to mine own cousin @Hagrid, but in thy case, I sayeth thee shouldst visiteth the detective who is't goeth by the nameth @S-Holmes”. @Alice replied back, “Thank you, Sir @Gandalf, we’ll get help from this @S-Holmes, I’ve heard that he’s an @exceptionalGuy”; “Mine own pleasure, Farewell!” said @Gandalf, and the door closed shut.
So, @Alice and @Michelle went back to their car, and that time @Alice raised a question, “How are we gonna find this @S-Holmes? We don’t have a phone number or anything so we could contact this guy.”
“We should call @thatJavaGuy from work, I’ve heard he is a man of resources, he must know how to contact @S-Holmes”, said @Michelle.
And it was true, after a call with @thatJavaGuy, they were able to obtain @S-Holmes’s phone number.
“Howdy, this is @S-Holmes, what can I diddily ding dong do you for?”
“Hi, I’m @Alice, I’m from DevCo and I was hoping that I could get your help in our mission.”
“What kind of mission?”, asked @S-Holmes.
“We want to @hack @theNSA.”, replied @Alice.
“Okay… I think I might be able to hel-diddly-elp you! There’s an old and abandoned laberino noodly-near @stacked Street. It was made in @1989 and since then, it houses a magical computeroo that can hel-diddly-elp you in your mission. So, you just have to connect the computeroo to the Internet and you can diddily ding dong do your programmeroo thing and then you'll have access to the the noodly-nsa diddily ding dong database!”, answered @S-Holmes.
S-Holmes continued, “But I shall warn you, there's a riddly-rumorino that the laberino was abandoned because of an @electric-ghost that lurks there, but I bel-diddly-elieve it is just a computeroo program that was diddily ding dong designed to try to @stop hackers from accessing the top secret stuff!".
“Okay, thanks for your help! I bet we can handle whatever this @electric-ghost thing is, so… Goodbye!”, replied @Alice.
“Goodbye!”, said @S-Holmes and that ended their conversation.
Luckily, the @stacked Street was just a couple of miles away from them, so they reached the lab quickly.
As they got close to the lab they saw something that really surprised them…
--------
To be continued in part two...
(Do you want a part two? :/)
My first ever story is a little special because it is kind of dev related at it has "cameos" by various devranters, as you might have noticed.
How many did you count?
More in Part Two.
Thank you for reading and please, any feedback is welcome. Did you like it?
I haven't really revised it once, it is straight out of the keyboard.
Should I drop the "@" ?
But then it would impossible to spot some of the devRanters .
Let me know.
PS
What should be the title?
1)Alice in DevLand?
2)Adventures of Alice and Friends: Hacking the NSA?
You decide..(or maybe I'll pick the second one :D)21 -
What is the difference between USA and USB?
One connects to all your devices and accesses the data, the other is a hardware standard! 3
3 -
Following a conversation with a fellow devRanter this came to my mind ago, happened a year or two ago I think.
Was searching for an online note taking app which also provided open source end to end encryption.
After searching for a while I found something that looked alright (do not remember the URL/site too badly). They used pretty good open source JS crypto libraries so it seemed very good!
Then I noticed that the site itself did NOT ran SSL (putting the https:// in front of the site name resulted in site not found or something similar).
Went to the Q/A section because that's really weird.
Saw the answer to that question:
"Since the notes are end to end encrypted client side anyways, we don't see the point in adding SSL. It's secure enough this way".
😵
I emailed them right away explaing that any party inbetween their server(s) and the browser could do anything with the request (includingt the cryptographic JS code) so they should start going onto SSL very very fast.
Too badly I never received a reply.
People, if you ever work with client side crypto, ALWAYS use SSL. Also with valid certs!
The NSA for example has this thing known as the 'Quantum Insert' attack which they can deploy worldwide which basically is an attack where they detect requests being made to servers and reply quickly with their own version of that code which is very probably backdoored.
This attack cannot be performed if you use SSL! (of course only if they don't have your private keys but lets assume that for now)
Luckily Fox-IT (formerly Dutch cyber security company) wrote a Snort (Intrustion Detection System) module for detecting this attack.
Anyways, Always use SSL if you do anything at all with crypto/sensitive data! Actually, always use it but at the very LEAST really do it when you process the mentioned above!31 -
ANTI VIRUSES AREN'T ALWAYS YOUR FRIEND!
So I'm under a little pressure to get an assignment done so I came home an was planning on working on it but Windows had other plans and decided to finish its update which I suspect copied my hard drive and uploaded it to the NSA at dial up speed because it it forever!!
But anyway back to the text in caps lock... I started working on it then when I hit compile I got an "access denied" error in the console and didn't know what the f*** was going on. So I decided to copy my filed to another directory and tried again... amazingly this worked so I carried on and after about 2 hours I get the same error -_- So instead of messing around and loosing my work I decided to commit it... but I cant... again "access denied" error.
After threatening my computer with a trip out the window, I finally decided to reboot it... cause "have you tried turning it off and on again" kept on rattling in my head.
After logging in I tried again and still the same error... Then I opened up my anti virus dashboard and went through the logs and found the screen shot attached.....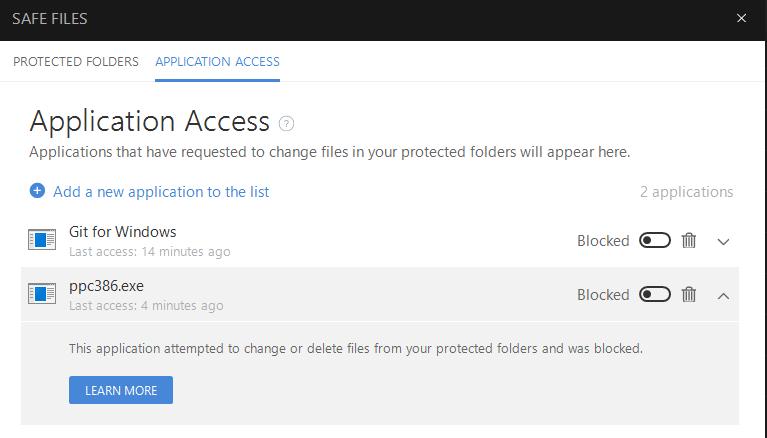 14
14 -
My college organised some interview with a company, with the whole demn class. We went there, it was quite far away (50km) and the CEO invites us to a meeting room.
Where he bores me for 2 hours talking about their projects in argiculture and NSA like spying systems at tankstations.
They were caputuring license plates at gas stations and with that information gather data about the person, such as salary (by looking at their car), house adres ect. All without people knowing. And than targeting them with specific ads and offers.
The class of sheep were super excited but it pissed me off. Because he told it like it was some awesome advancement in technology that none of us could probably ever do.
He was demeaning us, saying we would do some simple wordpress sites there and other things. We are probably not good enough forc te big stuff.
Asking him some really hard questions about his projects made him so pissed he almost wanted to kick me out.
When it was finally over, there was some test that you have to do if you want to work there. If you were good enough at the test, you could!!!! (YEEY)
Uhm, I said; no thank you I dont want to work here.
Later I talked to my classmate and friend who always thinks he's better then everyone in class even tho he barely understands OOP programming. He was asking me if he should try to get the internship. I told him; dont. They have no value for us and they think they are the greatest company on the planet.
The fucking idiot go so pissed, he stopped talking to me alltogether and blocked me everywere. I AM NOT EVEN JOKING. Just because I gave my FUCKING opinon about a company he likes for no reason.
So this idiot does the test (which was fucking simple btw, I did it too and compared the results and I had 95%) He gets invited for another interview and gets told he will be paid 200 euro's per month 😂. and a free meal everyday!! 😪 hahaha . That doesnt even cover commuting costs!
My "friend" told him that the train costs more every day. You know what the CEO said? "Yeah but you can learn so much here the also brings value and you're just a last year student. But I think you are really brave for asking more"
So in the end, he couldnt take the internship and I was fucking right. Really I hate these kinds of companies thinking they are heaven on earth when they are clearly not.
I am happy I told them no before putting my dignity on thd line.14 -
devRant is truly amazing, a social network where I don't have to give up on privacy by giving out my number to confirm that I am legit when I'd use something as a VPN to protect my identity (unlike twitter facebook and google)
Thanks for giving a fuck about privacy and not giving a fuck about my data11 -
What I'm posting here is my 'manifesto'/the things I stand for. You may like it, you may hate it, you may comment but this is what I stand for.
What are the basic principles of life? one of them is sharing, so why stop at software/computers?
I think we should share our software, make it better together and don't put restrictions onto it. Everyone should be able to contribute their part and we should make it better together. Of course, we have to make money but I think that there is a very good way in making money through OSS.
Next to that, since the Snowden releases from 2013, it has come clear that the NSA (and other intelligence agencies) will try everything to get into anyone's messages, devices, systems and so on. That's simply NOT okay.
Our devices should be OUR devices. No agency should be allowed to warrantless bypass our systems/messages security/encryptions for the sake of whatever 'national security' bullshit. Even a former NSA semi-director traveled to the UK to oppose mass surveillance/mass govt. hacking because he, himself, said that it doesn't work.
We should be able to communicate freely without spying. Without the feeling that we are being watched. Too badly, the intelligence agencies of today do not want us to do this and this is why mass surveillance/gag orders (companies having to reveal their users' information without being allowed to alert their users about this) are in place but I think that this is absolutely wrong. When we use end to end encrypted communications, we simply defend ourselves against this non-ethical form of spying.
I'm a heavy Signal (and since a few days also Riot.IM (matrix protocol) (Riot.IM with end to end crypto enabled)), Tutanota (encrypted email) and Linux user because I believe that only those measures (open source, reliable crypto) will protect against all the mass spying we face today.
The applications/services I strongly oppose are stuff like WhatsApp (yes, encryted messages but the metadata is readily available and it's closed source), skype, gmail, outlook and so on and on and on.
I think that we should OWN our OWN data, communications, browsing stuffs, operating systems, softwares and so on.
This was my rant.17 -
I feel sad for the NSA employee that is watching me. All he sees is me ranting over coding problems, playing games and masterbating.
He is probably thinking about changing his job.7 -
My friends with non tech background thinks that I am hacking into NSA or something but they don't know I am just downloading the package lists by running sudo apt-get update. 😂5
-
Just now I was compiling a new kernel for my laptop because the last ones were from before my rootfs became LUKS-encrypted. Then I found that option about SELinux again.. NSA SELinux. A MAC system that linuxxx praised earlier. Should I tell him? 😜
 8
8 -
At university. But at first I thought I was too stupid because everyone in my class sounded like they started hacking the NSA at age 3, and I hadn't even opened a command line. Even had a proffessor tell me if I didn't ace his OOP class, I should quit (I failed, did good the second time though). Moral of the story is: fuck him, and anyone who tells you that you can't do something.4
-
!Rant
Fun links I've found today:
http://amzn.to/2xy5g49
http://amzn.to/2xzKEJb
http://amzn.to/2hwULGY
http://amzn.to/2fpO492
http://amzn.to/2y5JQP1
http://amzn.to/2wVelCm
There are more, but I feel like this is enough.23 -
!Rant
*Whenever there's a big hacking thing that happened in cyberspace and the media gets the footage*
"Hey! You! you the website developer. Can you like get a hoodie and smash the keyboard."
"Why?"
"Big virus leak"
"But that's not ha.."
"SHUT THE FUCK UP AND GET THE HOODIE ALREADY"undefined and also probably am i overthinking this? the nsa is watch.. news shhh they don't need to know about that that's why there's always html code there what5 -
I commented on a rant that "devRant is anonymous" then later I get a ++ notification that @theNSA +1'd my comment.
So maybe not...2 -
Fresh internship story/conversation (Part 1)
Happened today:
- "Can you hack someone via cmd?"-cheap coworker at my internship workplace
- "Can you hack the NSA from any device?"-cheap coworker
- "Can the police identify me, if my face is on a Youtube video?"-cheap coworker
- "I can see all devices I have been through when I want to connect to a target as a route.
*talks about hops in a trace route, but uses non-technical terms for it*
*uses "ping host wikihow.com" instead of "tracert wikihow.com" to demonstrate it, besides of that "host" was not supposed to be there in that command*
*he had to google how to use the ping command on Windows*
*finally uses the ping command properly*
"Here, you can see all the devices our machine has connected to to reach the target"
ME: Aha. But dude... you know that all these ip adresses are in fact the same ip. These IPs are not any different. They are all the same. Besides of that this IP is the IP of this *points to domain name on windows cli* domain.
Him: Oh... I had a friend named ... *continues telling me some "hacker stories" from his past*
Me: *ignores him and always just responds with "Aha" to him* -cheap coworker
Happened yesterday:
- "You have programming classes? You must be an expert in Excel then, right?" -internship boss3 -
Privacy.
I have an Amazon Echo.
I've enabled Hey, Siri.
I've given Google the OK.
I don't tape my web cam.
And I find it highly amusing that someone has potentially seen my fat, hairy ass strut naked about my home office while singing "What's up" at the top of my lungs. Perhaps multiple times.
Should I feel bad? That I may have cost the American taxpayer money in the therapy required to rehabilitate those FBI or NSA agents that have witnessed me in my full glory?13 -
There are cybercrimes. That means you can be put to jail for performing certain actions with your computer. I’m taking about serious crimes like hacking crucial governmental servers but not about insulting people online. I’m talking about something that’ll make government chase you.
Every action at the computer could be done with keyboard only.
My face when there is finite sequence of keys that you press one by one and then become a criminal. And go to jail.
My face when if you put that sequence into script file, there is file that you double-click and instantly become criminal.
Press here to go to jail. The whole new level of abstraction.
Really makes me think.7 -
Other services : Please type your phone number to verify that it is you. It will be only used for verification process.
Me : Sure, why not? (Happily types in my number)
Facebook : Please type your phone number to verify that it is you.
Me : Hmmm (sees help)
Facebook : It will be used for verification process and will be visible to your friends. You can always change the scope settings.
Me : (reads as...) It will be used for verification process and will be visible to your friends and will be automatically sent to the NSA for free. You can always change the scope settings when you become the CEO of Facebook.
#deletefacebook -
What do you think about a digital assistant made by the NSA, for example for people with dementia?
It would be accessible everywhere and it would know everything
and it could result in some nice dialogues:
>> "Okay NSA?"
"Yo, I'm always listening."
>> "I forgot to take some nice pictures from my last vacation, do you have some for me? D:"
"Of course, here ya go."
And you could even trigger it without a keyword.
>> *Walks to the fridge*
"Hey, you've already been at the fridge 45 minutes ago and since then you haven't bought anything."
>> "Thank you NSA"7 -
(L)user tried to impress the IT staff (myself included) by installing a few of the NSA leaked tools last night, (l)user was infected with ransomware... (l)user is now job hunting. 👌🏽2
-
I am a student. A Geospatial Engineering student. I made a demo Cordova app mapping incident spots on OSM., now my fellow undergrads think I can hack NSA, program a satellite, build all their dream websites and apps. The College Department wants me to lead an in-house photogrammetric programmable drone project. If they ask I'll say yes... yes I can! shit.😂5
-
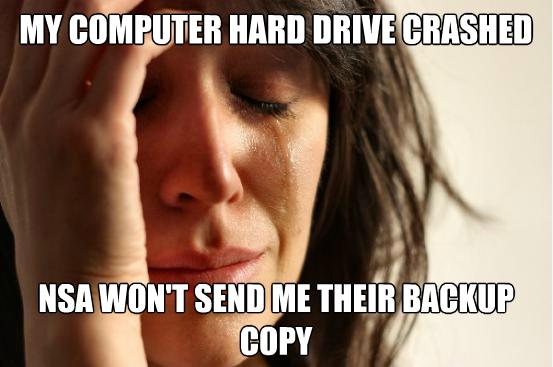
It is a sincere request to all the people who are asking for a backup of their files and documents, to please stop pestering us regarding the same.
We can't possibly collect your data, and even if there's a way, it would be nearly impossible for us to find your data from billions and billions of files and directories.
Citizens are requested to please understand our problems.
Have a nice day :)4 -
If you type "Illuminati" backwards and the ".com" into your browser, you will be led to the US government's national security page.
Source: pythonforbeginners2 -
Who's at fault for the recent Wanna Cry virus: The companies affected or Microsoft/NSA?
Personally, I think it's the companies affected. This is what happens when you try and be cheap when it comes to cyber security.8 -
Glassdoor.com is in hot water after federal investigators in the US sent a subpoena to unmask anonymous users who might be "third party witnesses" to certain business practices by a company under investigation for fraud.
Can DevRant (@dfox, @trogus) be forced to unmask its users (IPs, emails) in a any way, by the US government (@fbi, @cia, @nsa) or any other government (@svr_rf, @mss, @mi6, @bnd), should a similar situation arise?15 -
"restarts Windows machine*
*windows updates, hah fuck you ima take 30 mins to shut off and turn on again*
*installing NSA... Please wait*
*windows has detected a problem, please wait*
......... I just wanted to restart it
-
My worst bad practice:
Saving my Linux Root SSH Keys on a Cloud Storage company.
Have them there, so I wont loose them ever. I password protected them, but you never know what the NSA/FBI/CIA can do 😉1 -
WHY WHY WHY WHY WHY YOU FUCKING SPYING SNEAKY LITTLE CUNTS?!?
This is the Calendar app that comes with my phone. Can't disable, uninstall, or change these slightly suspicious permissions. FUCK MY LIFE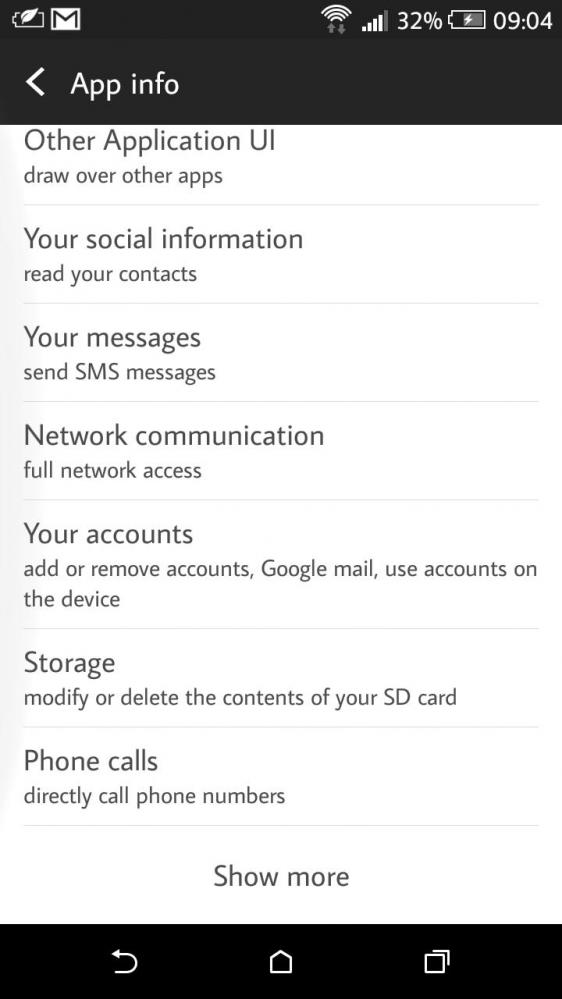 12
12 -
On Skype.
[tldr: #muhPrivacy;]
You know, people hiring via Skype.
Gaming, seeing family or having long range relationships.
It's become a decent tool.
Then there is the Skype employee.
Opening a court case because in his work time, evaluating Skype calls - ON FUCKING OBSERVING SKYPING PEOPLE - he has to look at too much flesh (as in porn) for his salary level.
Like : the payment category states that you gotta be classed like 1,2 salary categories higher for such work.
So the first instance did not recognise the employees case, because they said its a state thing, or even higher.
Later instance evaluated the employee was right and decreed Microsoft / the NSA (whomever direct employees they are) to properly categorize their employees.
Therefore cost relatively exploded and an algorithm to detect nudity was built.
Wich is operational way earlier than Skypes TOS renewal mid 2018.
That also bans bad language and auto bans given accounts.
Talking about social credit..
in PROC (or prod, as they're known).
And btw: complaining about Google while posting Christmas gatherings on Instagram.. You get what I mean.
Honestly, I don't recall the sources. It's been a while.
I'd really appreciate a little compendium of this for historical reasons.
They will ask: what has brought us here? What is everyone an ultimate right/left/center/agnostic/religious fascist?
And we'll have it on paper. Or papyrus,.. even stone. As I don't know how far mighty people will go for their fortune.15 -
Concerning my last rant, some explanation:
In short:
Skype and security agencies spy on all the people.
More context:
To the extent, that Skype employees suffer mentally from excessive porn.
That's what large amounts of users did on this platform the last two decades.
So the affected had to bring their case to national, maybe even super national courts.
Which gave in to their claim.
Thus bringing the employees into another salary category, so, compensating the damage done.
What sounds like a unions topic reveals large scale mass surveillance of everybody without exception.
And describes some effort in machine led (picture) recognition.2 -
Who am I?
Some of you, because of the hyperbolic, outrageous, trollish, and often self-satirical nature of my posts, might doubt me. Thats completely relatable.
Heres the truth:
I was diagnosed in childhood with ADHD, fucking everyone, every male, these days is diagnosed with that. I was diagnosed bipolar. Hell anyone reading my posts could see that from a mile away. I was diagnosed on the borderline personality spectrum. Yeah, I could see that.
I was tested. They said I was in the 98th percentile for clerical ability, not extraordinary but pretty good, mathematical ability a little higher than that. My SAT was 1491. Not yale material, but I coulda been someone.
Over the years I studied a LOT of politics and read a metric fuckton of books. (40+ books over the course of three years).
I predicted every single presidential election since bush juniors second election. Three supreme court picks. Senatorial elections. Congresional elections. More than that.
I have a better analysis track record than some of the multidecade analysts sitting in the fucking NSA.
No I am not shitting you. No I am not exaggerating.
It's about the only claim to fame I get to legitimately make.
People ask me, "then why aren't you famous?"
How do you know I'm not.
Look I'm gonna tell you my actual name.
My real name is Lawrence B. Lindsey
Okay, I'm bullshitting for fun. But words I have written on alt twitter accounts have legitimately come out of presidential hopeful's mouths. No, this I am *not* bullshitting you about.
Imagine that. A guy who lived in his parents attic for five years, writing words that came out of presidential candidates mouths.
At one time I was about as popular and influential as that fuckboy catturd.
yes, really. No I am not fucking joking.
Under normal conditions I wouldn't talk about this or reveal it, because who the fuck cares? I'm just some dude on the internet, drunk, both on alcohol, and the pseudo-anonymous equivalent of bragging rights.
You know how many women I turned down because I could? You know how fucking drunk I am? They say a drunk man's words are a sober man's thoughts. Well, I'm not usually honest like this because the internet is full of false braggarts, and you tell people the truth and they don't fucking believe you.
I swear, it seems like I made some faustian bargain at some time, and can achieve no fame or lasting wealth in my life--to save my life.
Shit, I was talking to a chinese women who ran a bank in china (yes, really), who advised me to buy into bitcoin early on. Didn't have the money to. Woulda been a fucking millionaire if I did.
*Non-obvious* Ideas that major corporations are now persuing? Yeah those were sitting in my card index since the early 2000s.
I helped two people build and sell businesses. One for me tens of thousands. Another for millions. Yes, really. Got zero, and I mean, *zero* credit for it.
Point is, doesn't matter how famous you are, or coulda been, Doesn't matter the ideas you have, or had.
The world doesn't promote runners-up, or hasbeens, or wannabes, or could-bes.
What matters is execution.
If you're wandering through life, wondering when you're lucky break will be, stop. You have to realize, you make your own luck. Recognize the difference between what you can control, and what you can, and work on promoting your own ideas or business or values, instead of other people's dreams.
And for those wondering, yes I am drunk, and no, I ain't fucking kidding you in anything I wrote here.
The most important lesson I learned is this:
First work on your own success, before you work on the success of others.
p.s.
I give surprisingly good advice for someone who doesn't benchmark well on traditional measures of success. I know, even I was shocked when I looked at the statistics.27 -
For some reason, I started using Office 365 30 day trial a month ago, obviously, and yesterday, a month passed, but the product registered automatically and says it is a product officially signed with a product key.
Thanks Microsoft!
I <3 you!
(don't report this to nsa)3 -
Tekashi 69 was about to snitch on me for hacking and leaking data from the NSA and then I hit em with the...
return;6 -
What if devRant was created by the NSA to make paranoid devs feel more comfortable and share some private information they wouldn't share on other social media?
🤔10 -
Zoom was dead before it even took grip.
Fml. Use jitsi or some other real stuff.
<deity>, I don't care, choose Skype, there we know that security is well established and it's watching workers are well payed (US Court case for proper work classification).9 -
Zero Days documentary about stuxnet malware features a "identity protected" NSA employee who reveals information about classified NSA tactics.
She claims "I would NEVER compromise ongoing operations in the field."
Well it's too bad that Amazon Prime Video and IMDB don't share your values. They have compromised your name, Joanne Tucker, and the other films you were in.
Nice acting though. You really have people believing you were a real source! 15
15 -
Waiting for another prank by the dR team in April 1st.
Maybe they will like remotely wipe our data with parnership with the NSA.4 -
Rant considering the latest Cyber attack and the news around it.
(A recap: a lot of Windows computers were infected with ransomware (due to security hole on Windows), which demanded 300$ in bitcoins to unlock data. After 3 days the price would double, and after 7 days the data was to be deleted)
1) In our country, one of the biggest companies was attacked (car factory). The production stopped and they got for around 1 000 000€ damage in less than 24h (1300 people without work). The news said that they were attacked because they are such a big company and were charged more, as the hackers "knew who they were dealing with" - another reason being the fact that the text was in croatian (which is our neighbor country), but noone realized that it is just a simple google translate of english text - which is obviously not true. The hackers neither know nor care who is hacked, and will charge everyone the same. They only care about the payment.
2) In UK whole (or large part) of medical infrastructure went down. The main thing everyone was saying was: "Nobody's data is stolen". Which, again, is obvious. But noone said anything about data being deleted after a week, which includes pretty much whole electronic medical record of everyone and is pretty serious.
And by the way, the base of the ransomware is code which was stolen from NSA.
All that millions and millions of dollars of damage could be avoided by simply paying the small fee.
The only thing that is good is that (hopefully) the people will learn the importance of backups. And opening weird emails.
P.S. I fucking hate all that 'hacky thingys' they have all over the news.5 -
A couple of days ago, an individual attempted to convince me that the National Security Agency is capable of cracking Rijndael encryption; as a response, I informed the individual of the infeasible nature of the factoring of extremely large semiprimes; however, my attempts were futile, as the individual believes that NSA possesses sufficient power to crack this encryption without intercepting the transmission of the corresponding private key.
The Dunning-Kruger effect is real; although this individual tends to be logically-minded, there does exist an exception to this good behaviour.
"It is easier to square a circle than get 'round a mathematician."1 -
Holy FUck!!!? O.o
You know, they say the customer is always right.. So with us, if the customer wants to shot himself in the knee with a gun, we let them. Usually we even provide a fancy hugeAss cannon, so he can do it more efficiently.
/* not like we make stuff worse, but we prepare our SW for them to do crazy fucked up shit they insist on doing with it, even thought it's against common sense and our recommendations on how to implement XY feature.. */
So.. We usually go above and beyond with the 'not so nice but handy' cannon to do that..
And right now, I think I am on the verge of creating a superDuprHugeAtomicBomb /* figuratively speaking!! NSA go awy!! */ for the customer to killthemselves with!! O.o xD
Supper happy (until I discover more bugs, but it's not finished yet.. so hopefully no bugs at the end!!)
Caboom!undefined !rant||rant bugzincoming xd cannon funstuff gun customers noideawhati'mdoing nsa bomb poop4 -
So... has anyone yet made a comment about now exHead AMD Chief of GPU division Raja Koduri joining Intel?
Now this is awkward after I made this OC image not so long ago :/
https://devrant.com/rants/896872/...
Also in other news can we comment that Systemd has pretty much took over most linux distros? is this the new NSA backdoor? (before someone points out is open source, have anyone been able to properly audit it?)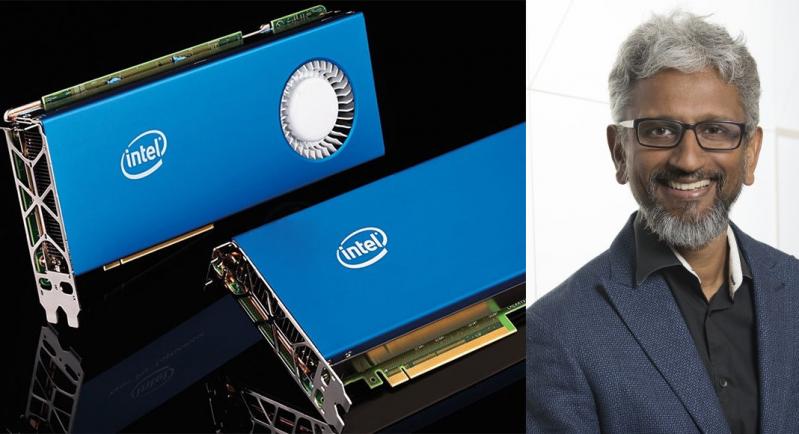 4
4 -
I'd just like to interject for a moment. What you're refering to as windows, is in fact, NSA/windows, or as I've recently taken to calling it, NSA plus Windows. Windows is not an operating system unto itself, but rather another free component of a fully functioning NSA system made useful by the NSA corelibs, spyware and data collection system components comprising a full surveillance system.
Many computer users run a modified version of the NSA system every day, without realizing it. Through a peculiar turn of events, the version of the NSA data collection system which is widely used today is often called Windows, and many of its users are not aware that it is basically the NSA system, developed by the NSA.
There really is a Windows, and these people are using it, but it is just a part of the system they use. Windows is the piece of trash: the program in the system that steals the system resources from the other programs that you run. This piece of crap is an essential part of an NSA system, but useless in practice; it can only function in the context of a complete NSA system. Windows is normally used in combination with the NSA surveilance system: the whole system is basically NSA with Windows added, or NSA/Windows. All the so-called Windows systems are really distributions of NSA/Windows!
Inspiration:
4th comment
https://devrant.com/rants/4456259/...3 -
NSA is seriously hiring on SO. Even with happy YouTube video under it. Like nothing is happening.
It must be freezing in hell atm I guess
https://stackoverflow.com/jobs/...4 -
Blockstack; developers who are using blockchain technology to reconfigure the web. It’ll make NSA mass data collection impossible.
https://youtube.com/watch/...
Beat that @theNSA 4
4 -
"Startup (called Nectome) wants to upload your brain to the cloud, but has to kill you to do it"
https://theguardian.com/technology/...
No thanks, I am sure NSA will kick in.4 -
Me: *tries to deactivate windows 10 feedback*
Windows: nope *turns it back on*
Me: *please*
Windows: NO
Me: *Feels sorry for shitty quality* 2
2 -
Programmer: "Places : instead of ;"
Javascript: "What the fuck did you just fucking post about me, you absolute beginner? I'll have you know I worked for ten of the biggest silicon-valley industry companies, and I've been involved in over two hundred top secret projects including NodeJS. I am trained in refactoring the most fucked up code, and I'm the top C++er in the entire fucking internet-connected universe. You are nothing to me, but just another IP. I will fucking revoke your commits from your gitlab account with absolute dedication using only one Rasperry Pi client. Mark my fucking words. You think you can get away with posting that shit on one of my numerous very personal blogs? Your devices are fucking bricked, kid. My attack software can be anywhere, anytime, and it is tasked to remove your entire git contributions from planet earth. Not only am I extensively trained in remote cross-firewall device-hacking, but I have access to over 100 of the United States CIA and NSA git repositories. If only you could have known what doom-bringing C-one-liner you have raised from my fucking hands, maybe you would have held your fingers. But you could not. You did not. And now you're paying the price, noob. I will hail havoc upon your puny online-presence and you will drown in your own badly designed software. You're fucking offline, kiddo."11 -
Shower thoughts: Someone should infiltrate the NSA and create a backdoor. Then, with all the data NSA has, he could make the most efficient and successful dating service, which doesn't even need any rightleftmitchmatchbullshit, because it instantly knows who the perfect one is.1
-
Given the recent election, I'm taking measures to ensure the privacy and security of my data. Call me paranoid, but I think the NSA is going to be getting some extra funding soon. I'm already working on encrypting a ton of my data. Any other tips some of you guys could give me?8
-
Thank you, Google and Facebook, for organising my information. Godddd I wouldn't have the time and dedication to do it myself!!
-
y'know it's nice to know that no matter what happens, some things in life never change. even if you want them to.
like no matter who you are, or what you're doing, SELinux will always be there to ruin your life....4 -
Relative phones up worried about installing Adblocker as it "can store and modify the websites you visit"...my answer.."so can GCHQ, NSA AND CIA so just give in to the fact that you have no privacy and click ok"...*long pause*.."ok one more question, what's a chrome extension?"..FML
-
Kaspersky `hackproof` OS - now makes sure FSB gets the data first instead of NSA [for those who don't know Kaspersky has close ties with the Russian government and FSB]
-
This is crazy I actually bough a phone just for devrant total worth it, this morning I read a rant from someone thinking about wearing a tin foil to avoid NSA from spying on H ,your not alone, FYI this is how it looks like

-
Just fixed my broken htc one m9 (boot loop after legitimate update) by powering it up month after putting in back to box for future repair. Who to blame? NSA? Android 7? SD Card?
-
Now... I understand 2FA is to make things more secure, and I do appreciate it. BUT can we please work out a damn solution for people who work in an agency for other corporates which only have one shared account across the agency that bundles one phone number or mobile app.
What if people are on leave or sick? I need stupid 2FA to be able to login/work. uhhhhhhh.....8 -
Today I was minding my own coding-committing-pushing business, when all of a sudden, a split second before typing Enter on a command, the obnoxious UPDATE JAVA popup reared it's ugly head.
Normally I just politely recommend it to fuck off and let me manage my Java versions with homebrew on my own time. But I had no time to not press Enter, and so it rapidly started downloading/installing.
Thankfully I had juuust enough time to hit the cancel button. The progress bar it was showing stopped at 81%. Didn't even have time to read what it said. Crisis averted. Them NSA fucks be like, "curses, foiled again!"
This was probably the most intense moment of the year for me. I think my lifespan grew shorter a few months.
Dreaded auto-updates are getting smarter. They nearly got me when I was in a vulnerable state of hitting Enter many times. Stay on your toes!1 -
# NEED SUGGESTIONS
I am working on a secure end to end encrypted note taking web application. I am the sole developer and working on weekends and will make it open source.
The contents you save will be end to end encrypted, and server won't save the key, so even I can't read or NSA or CIA.
So I wanted to know if the idea is good? There are lot of traditional note sharing apps like Google Keep and Evernote. But they store your stuff in plaintext. So as a user will u switch to this secure solution?14 -
dear ietf-people i want to thank you that tls1.3 is official. i know it was hard work to say just no to the doughbags and preventing that middleware and spyware manufacturers implementing static keys.
to make it short:
Thank you for your hard work -
I think I need VPN now.... some sites are getting blocked/NSA is watching.... 😥 😥 😥 😥 😥
Will this do? What next? 20
20 -
I don't understand how can Wikileaks be still active and publishing new stuff... Shouldn't it be like "pwned" by CIA or NSA or something? Can I trust whatever I see on that website?10
-
Maybe I should automate downloading these google spreadsheets... neat there's an api for it, lemme just check the npm (https://npmjs.com/package/...).
Unpacked Size
49.2 MB
Total Files
900
Uhhh... fuck no? How about no fucking way? The nerve of these guys! Can you imagine being so up your own ass!? That's like 2kb of shit I care about, and the rest is bloat. Might even have some spyware hidden in there for how much NSA pays them.3 -
Enter one word in terminal and hack fucking government's, CIA's, NSA's, websites, database and servers, just like hackers in movies do.
If I failed to achieve this, would love to hack Sony's website and post a message on all their websites
"We make terrible mobile phone" -
Maybe im wrong but still, damn policies, at my job i need a code review and a commit review before committing code and Im ok with that but hell, I was required to run the api tests when I only modified 2 front end file, i mean seriously i need to run c# tests after modifying angular components. It just seems silly and foolish and a complete waste of time to run the tests for all the projects when i didnt even modified one.
If you work with me and know who I am then stho and accept it. :prant policies job tags are traps fbi putin has nothing on me like really angry angry deletefacebook pichardo for president hello nsa -
Ever wondered if there are any Devs on devRant that work at the NSA? Or other shady agencies. Or are they only indexing this network?3
-
Windows 10 is safe they said. Signature/https can be trusted they said.
When even NSA disclose "hacks" you know it's too big
https://wired.com/story/...4 -
TL;DR still don't know who 1:11 is...
It looks like my script took screenshots until about 2:50, but there was no activity on the desktop... That means they have to be on A days. I can try to run the script again next Wednesday OR I can use this thing I built to wait until 1:11 and spam the desktop with screenshots claiming to be the NSA... I'm a little too chicken for that lol. Anyways yeah couldn't find out who it was yet and I don't have much time to find out... -
Made this one-liner today:
hostname $(curl nsanamegenerator.com | grep body | sed -e 's/<.*;//g' | sed -e 's/<.*>//g')
and added it to my laptop's crontab...4 -
I found a better solution than taping over your webcam:
Not using the shitty inbuilt screen in the laptop.
And if you need tape, use BLACK TAPE, because who wants a glow in the dark yellow rectangle above their screen...1 -
!rant Scary Stuff...
Not sure what are the rules on sharing external content, but this story freaked me out and I wanted to share with you.
Pretty scary stuff, maybe something like this is already in the wild? Especially with the NSA and other power groups trying to exploit vulnerabilities and infiltrate everything...
Found it originally on the rational subreddit. Here is the link:
https://teamten.com/lawrence/...
Spoiler alert:
It's about the The Ken Thompson Hack:
"Ken describes how he injected a virus into a compiler. Not only did his compiler know it was compiling the login function and inject a backdoor, but it also knew when it was compiling itself and injected the backdoor generator into the compiler it was creating. The source code for the compiler thereafter contains no evidence of either virus."
How to detect/deal with something like this? better no to think too much about this. -
"We're excited to announce that we've disabled the deprecated Storefront Toolkit by default for new....."
I am also so freaking "excited" that you have also disabled the close button on the popup when you login to Salesforce BM genius.
How the hell i am suppose to use SFBM now?!! developer tool to remove the popup markup?!
Learn more?? I don't need FAQ doc, I need the popup closed!!! 3
3 -
Yesterday at work (where 2 of my bosses hate me...) I met a man named James Bond.
But I know Gates could take him down cause he's got the NSA on his side...1 -
Is the ransomware attack using leaked NSA hacking tools affecting 99 countries is seriously serious or should be categorized as fake news13
-
yahoo is now alleged to give away bulk mail content to intel agencies. such a dead investment, who uses yahoo for sensitive communications anyway?
http://thehackernews.com/2016/10/...1 -
You would think that the top information gathering government agency would be having their https certificate configured properly but apparently not...
https://iad.gov/NIETP/reports/...1 -
Used a keylogger to get my cousin's facebook password.
Now that 12 year old kid thinks that I am a badass hacker secretly working for the NSA😎.31 -
I know everything about you.
I've seen every rant on devRant.
And I know who are here for laughs and who are here to get rid of stress1 -
I like to teach sites that don't escape HTML/js in input fields a lesson, and put in a redirect. Where would you redirect them?
I tend to go SFW, like redirecting to a competitor or the NSA. -
As free software I guess you have to not be pedantic, but still felt like this was unnecessary when I feel like I having nothing to do with this political change nor will I have the ability or inclination to actively do something about it.
 3
3 -
My computer's performance plummets when there's no internet. Why the fuck do you need the internet to work?! Just how much data are you sending to the NSA?!1
-
all this talk of australian crypto laws got me thinking. here's a hypothetical (this might get a little complicated):
for the sake of the security facade, the government decides to not ban encryption outright. BUT they decide that all crypto will use the same key. therefore you can not directly read encrypted things, but it's not really encrypted anymore is it?
part two: there's a concept called chicken sexing, named after people who determine the sex of baby chicks. male chicks are pretty useless and expensive to keep alive, so they are eaten. female chicks go on to lay eggs, so ideally, from a financial standpoint, you only raise hens to maturity. this is nearly impossible to discern early on so at first you're just straight up guessing. is this one female? sure? that one? no? really 50/50. BUT if you have a skilled chicken sexer looking over your shoulder, saying right or wrong, then eventually you get better. why? nobody knows. they can't explain it. nobody can. you just sort of "know" when it's female or not. some people can do 1000s of chicks/hr with success up to 98% but nobody can explain how to tell them apart.
part three. final part:
after years, even decades of using this encryption with only one key, I wonder if people (even if only people who are regularly exposed to crypto like NSA analysts or cryptographers) can ever learn to understand it. in the same way as above. you don't know exactly what it says. or how you know it. you didn't run an algorithm in your head or decrypt it. but somehow you get the gist.
28464e294af01d1845bcd21 roughly translates to "just bought a PS5! WOOT!" or even just pick out details. PS5. excited. bought.
but how do you know that? idk. just do.
oh what a creepy future it has become.8 -
So I just saw this rant https://devrant.com/rants/977587/... and I'm wondering what is your reason for not wanting to be tracked or watched?7
-
Evaluating an app for a customer to ensure compatibility. It's in MS Store... so I better get it then. I'm logged in, should be fast.
"Enter the code we sent to yyy.zzz@maily.sss"
......
.....
...
..
It's been an hour. I can allow for some delay but please, it's a mail, not an NSA security check... or? -
For those wondering why so many people are leaving GitHub, it is due to the fact Microsoft is part of the PRISM surveillance program, where the NSA and other agencies can get their hands on your raw, unencrypted data without anyone knowing.
This is the reason 2 companies and 20ish devs gave me as to why they moved from GitHub to a self hosted Gitlab2 -
Innovative Bitcoin Recovery Solutions - How CRC is Revolutionizing Scam Recovery
Breakthrough Methods for Bitcoin Recovery
As cryptocurrency scams become more sophisticated, CipherRescue Chain (CRC) has developed cutting-edge techniques to recover stolen Bitcoin that set new industry standards:
1. Smart Contract Exploit Reversal
Deploys counter-exploit protocols
Utilizes time-delay transaction analysis
Implements blockchain-level interventions
2. AI-Powered Forensic Tracking
Machine learning wallet clustering
Predictive movement algorithms
Cross-exchange behavior mapping
3. Legal Pressure Strategies
Real-time asset freezing technology
Multi-jurisdictional seizure orders
Exchange compliance enforcement
Why CRC Leads in Bitcoin Recovery Innovation
1. Certified Cutting-Edge Technology
Patent-pending recovery algorithms
Blockchain Intelligence Group partnership
Regular technology audits by Kaspersky Labs
2. Transparent & Ethical Operations
Flat 12% recovery fee structure
14-day action guarantee
No hidden costs
Full legal compliance documentation
3. Unmatched Success Metrics
94% success rate for recent scams
$420+ million recovered since 2019
3,200+ wallets successfully traced
78% faster recovery times than industry average
The CRC Recovery Process
Phase 1: Digital Triage (48-72 Hours)
Blockchain snapshot analysis
Threat actor profiling
Recovery probability assessment
Phase 2: Active Recovery (7-21 Days)
Smart contract interventions
Exchange coordination
Dark web monitoring
Legal pressure campaigns
Phase 3: Asset Return (3-14 Days)
Multi-signature escrow returns
Anonymity protection
Tax documentation
Security consultation
About CipherRescue Chain (CRC)
CRC represents the next generation of cryptocurrency recovery with:
Technological Advantages:
Quantum-resistant tracing systems
Behavioral analysis engines
Real-time alert networks
Expert Team Includes:
NSA cryptography specialists
Former blockchain protocol developers
International cybercrime prosecutors
Financial intelligence analysts
For advanced Bitcoin recovery solutions:
📧 Contact: cipherrescuechain @ cipherrescue .co .site
CRC maintains revolutionary standards for:
Zero-knowledge client verification
Non-invasive recovery methods
Continuous technology updates
Global regulatory cooperation
Having developed 17 proprietary recovery techniques in the past three years alone, CRC continues to redefine what's possible in cryptocurrency recovery. Their combination of technological innovation and legal expertise provides scam victims with recovery options that simply didn't exist until recently.
Note: While CRC's methods are groundbreaking, they maintain complete transparency about each case's realistic recovery potential during free initial consultations.2