Join devRant
Do all the things like
++ or -- rants, post your own rants, comment on others' rants and build your customized dev avatar
Sign Up
Pipeless API

From the creators of devRant, Pipeless lets you power real-time personalized recommendations and activity feeds using a simple API
Learn More
Search - "suspicious"
-
Fixing a parents iPhone, episode 1.
Problem: "Whatsapp is gone off my phone"
Debugging:
Me: *unlocks phone and sees whatsapp*, it's right here.
Mam: no, I no that I can't see my messages.
Me: ok, that is definitely not what "whatsapp is gone off my phone means".
*opens whatsapp*
*inside add contact screen*
App seems ok, your trying to add a contact?
Mam: that's a problem, whenever I open it I only see that page.
Me: *taps cancel button with shocked face*
Mam: omg there's my messages, how did you do that?
Me: ... ... ... I tapped the very easy to see, large cancel button in the top right hand corner.
Mam: but why was it opened there?
Me: *looks at opened message from unknown number*
If I was to hazard a guess, now stay with me on this one as it's a bit complex. I think ... I THINK ... you clicked the "add to contacts" button on the screen in front of you.
I am suspicious of one thing though.
Mam: what's that?
Me: how you managed to click the add contacts button, and when brought to the add contacts screen, you assume the app is broken.
Mam: oh will you **** off you sarcastic little ****. Thank you very much.
Me: no prob, 4 year computer science course put to great use.20 -
Fuck today was weird.
Today I received almost half a million on my bank account. 😯
Someone changed the ancient cryptic billing system. My user account at work has id 32 in the database, and the dev referenced the size of the creditor id instead of the of the value of the ids itself, and they're u32 ints... So ALL the money moving through our platform was accidentally transferred to my associated bank account.
For all the unit tests we have, this bug tumbled right through.
And no one at finances thought a transfer that big, to a backend dev they know by name, was suspicious — with almost no money going to other creditors...
That worries me a bit. The fact that this shit can happen, even at high test coverage, just because someone mindlessly did a wrong autocomplete or something.
Of course I will send it back... after two weeks and a few hundred € of interest.12 -
When I finished my studies, I was looking for a job and had an interview at a smallish company.
Boss: can you do C?
Me: yes, I have already done some stuff in C.
Boss: I mean, are you really good in C?
Me, growing suspicious: well yes I already have been using it - but anyway, there's also the project documentation for looking up, right?
Boss: uhm, the code IS the documentation.
I envisioned myself being drowned in undocumented spaghetti code and wasn't really keen on that job anymore, but my following question pretty much ended the interview:
Me: oh, I see. Do you have any roadmap for getting your development to a more professional base?
His looks, priceless! He was just shocked when he realised that he had failed my interview, and that I was a fresher made it even harder to digest for him.30 -
I really hate it when we have to wear formal dress to office. I feel like a marketing executive. My code stares at me with suspicious looks.11
-
Hey everyone - tonight we performed a database upgrade and unfortunately there were a few "surprise" breaking changes to the query language we use that weren't caught during testing. Once they were discovered after the upgrade. The queries were corrected within a few minutes. You might have noticed some issues with commenting, voting, etc.
On this note, please let me know if you notice anything suspicious like errors when trying to perform normal actions, or anything at all. I appreciate any reports since it's a bit tricky for us to cover every last part of the app alone, though I think we went through most of it. Thanks and please let me know if you have any questions!18 -
Start coding for work this morning, immediately notice a ui bug, ugh. Want to get cracking with another bug I'm supposed to fix.
Fix the bug, and it incidentally fixes the other bug. Two in one.
*Suspicious*4 -
I've got a mini stroke today. My project ended and I got delegated elsewhere.
"It's going to be fine, it's c++, you will find yourself there"
Suspicious, it's a project everybody was staying out of as hard as they can. But hey, it's cool, how bad can it be? what can go wrong with that?
Reality was brutal, project that uses Boost C++ as framework and bjam as builder. Builds with a decent dose of luck, and only under special circumstances, only under one specific version of compiler. No docs, quartet of the code is in Fortran, just to use ancient lisp part which was second qarter. The most senior Dev around does not have idea how it all works. Also everything is inside one enormous try/catch block. Because of the reasons.
That's how people end up with severe alcoholism and meth addiction.8 -
I feel awkward when my boss is creeping behind. Of course, I can switch the screen in a hurry, but such behavior is suspicious, and sometimes I don’t notice him. So, in order to switch the screen without being suspected, I create a system that automatically recognizes that he is approaching to me and hides the screen.
https://github.com/Hironsan/...
Source: http://ahogrammer.com/2016/11/... 6
6 -
Last weekend I witnessed the most infected computer I have ever seen in my life...
I went on a private party. A girl had her laptop plugged to the speakers to play some music. This thing was literally 99% cancer. The first thing I noticed, when I looked at her opened browser, was that nearly half the screen was taken by toolbars. Also any popular website you could visit had additional ads INJECTED into it. The fist 10 YouTube search results: always porn. No idea how that didn't make her suspicious.
Precisely every 10th click (anywhere not only in the browser) would open up a window with either more ads or an aggressively blinking message saying: "A virus has been detected on your machine. Click here to download our antivirus programm. You have 60 seconds left before your firewall breaks!!!".
Also physically this device was on the edge of completely broken. The power supply had to be taped to the socket because it was so loose. Every little jiggle would immediatly shut the system down and Windows had to be completely reinstalled (which of course didn't solved any of the "software issues").
First I wanted to use that laptop to show some friends a new web project of mine but this thing probably would have DDoSed the shit out of my recently finished work or something.
I couldn't decide if I should laugh or cry...9 -
So guys i really need your help. My girlfriend started getting phone calls at odd hours, so I got suspicious and started tracking her phone. Then I found out that she has been going to this guys house at wears hours, then once when I was tracking her my computer froze, so what could it be? How do I fix my computer14
-
I saw a commit with suspicious code days ago. After warning my immediate superior he ignored me and yesterday proceeded to deploy.
Now we have items in cache for days instead of minutes. I guess next time he will listen to me.4 -
Corporate: Phishing Emails are serious. We need you guys to take this awareness training. Please report if you get any suspicious email.
*Sends the awareness training in a format that screams Phishing
Everybody: Wait... is this a test?1 -
Tl;dr: owning and pranking other people with a wireless mouse is hacking and illegal.
Okay, so I wanted to fuck around with some people one day so I decide to bring a usb wireless mouse to my secondary school.
My first target was my science teacher (was a bitch). I got into class before everyone else and plugged in the small usb receiver then sat down and pretended as if nothing had happened. The lesson starts and here is where the fun begins. Her screen is projected onto a whiteboard so I could see what she was doing. Under the table I had my mouse and every time she tried clicking a dialogue, I would move the mouse ever so slightly so she would miss. After a couple of times, she started to get suspicious, maybe even slightly paranoid; my friend keked. I never got found out by that teacher.
Fast forward to next lesson: I already planted the receiver in my next victims pc. The victim was a bitch I hated so much at the time. She would used to bully me to an extent and was a loud noisy bitch. I really didn't like the person. I digress. When the time was right, I went to her folder, highlighted all her files, right click, hover over delete. But I wasn't so shallow to delete her stuff. That's not the person I am. I guess it was more of a threat really. But the teacher saw what was going on and she saw my wireless mouse and connected 2 and 2 together. She called the behaviour people, removed the reciever and the mouse from me.
Within a few minutes, I was in a room on my own talking to this woman talking about how hacking is bad/illegal and she knows I'm into it etc. But I wasn't hacking? I did no damage and was pulling a prank. Bitch didn't listen to me. She made me sign this document which said that if I fuck around with computers, I could be expelled and I won't be allowed to use to computers again or use them with many restrictions.
I didn't really care. To this day, I still don't have my mouse back. :(7 -
My apparently my friend's wife gets suspicious whenever his Snapchat goes off after 10pm, always wants to know who it is.
"It's [algo], it's always him sending me pics of his code late at night. That's is the only person that Snapchat me this late"
And it's true.5 -
The list would be quite long.
I think Google is still making good tools, but just like Apple the integrations get all so tight and constricting... And with their data, if it goes wrong, it will go wrong hard.
I feel like YouTube is gliding into a state where cheap clickbait floats to the top and finding quality gets more difficult as well, their algorithm is more and more tuned to choose recent popular stuff over good older gems.
Microsoft is all pretend lovey dovey cuddling open source, but I'm still suspicious it's all a hug of death. I was never a big fan, but they're seriously dropping balls when it comes to windows-as-a-service, taking away so much personal control from end users even though they can't be trusted to babysit either.
Amazon is creeping it's way through the internet, charging $10/m to join the vip club infesting houses with spytubes to sell more plastic crap. Bezos' only right to keep wasting oxygen is BlueOrigin, but he'll probably fuck that up as well turning spaceflight into a decadent prime consumer orgy instead of something inspiring.
Facebook... Well, that's self explanatory. Fuck it, everything it pretends to be, and everyone who still has an account with a rusty spike.
Uber and AirBnB, with their fake ass mission of a green shared economy, but they trample over employees, customers and neighbors to build their ivory towers of progressive illusions.
Then there's a million declining brands.
I liked Skype for example when it was first released, Just like how I started out liking (and then hating) Discord, Slack, etc... They're all tools which seem fast and easy, but then they get us further away from solid protocols, get us entrenched into limiting, bloated and sometimes even dangerous tools. As my dad used to say: "Companies are like women, if you go for cheap, fast and easy you'll end up with a burning dick and half your savings gone"
You know what, fuck all tech companies.
OK, devrant is still pretty nice... For now.8 -
rant
When you start a new project.
You create a new directory.
You start the IDE and create a new application project.
You type just 5 lines of code for testing it.
Then you compile and run.
Nothing happens...
You abort and retry.
Nothing happens...
Half a minute later a window pops up and Norton reports you that an executable has been removed because its suspicious and has a lack of reputation!!!11 -
I think this is so far one of the most priceless WTF moments I encountered at my current work:
A coworker of mine came up to me explaining the problem he had with russian characters in the filename. He explained in detail that everything works ok (the other part of the code he was fixing) if he changes the name of the file to test1.xlsx for example which doesn't use russian characters. OK great.
Then he goes on to show me how he fixed the other stuff and of course everything blows up. The file he used for demonstration was of course the original file our cusotomer provided, he just deleted the obvious russian chars and left the rest.
МТС != MTC
I cracked up: but you still have russian chars in the name.
The guy: no way, I deleted them all.
Me: but what about that МТС in the name?! Guy: what about it?
Me: did you actually typed that in or you left it there?! Those are russian chars that are fucking things up for you.
Guy: no way, it's MTC.
Me: checked the logs, you have ??? In the filename instead of МТС..don't you find that at least a little bit suspicious?!
Guy: but it looks the same. How does it (the computer) know it is in russian?!? //Why doesn't it understand?!
O.o I still can't believe it.. Is it just me & my high standards, or should it be normal for coders to know things such as character encoding & stuff?!?
I almost died of laughter, he and some other guy had problems finding customers in the software due to not being able to type the russian chars << happened more then once before, even after I told them about a quick hack on how to use google translate onboard keyboard & other stuff to make proper chars so they can get a match..
I think when they bury me, I'll still be facepalming and laughing over this incident. 🤣🤣🤣🤣🤣🤣🤣7 -
My girlfriend says to me:
"Any other girlfriend would be suspicious why you're smiling and laughing into your phone."
I showed her devRant, she gets ['hip','hip'] 😊 -
My coworker wanted to get some program from a website that requires a username/password to download. It is a utility program for controls automation. He didn't want to have to create a username/password so I said he could use mine.
I went over to his desk and read off the username to him which he entered. Then I started reading off the "password" to him:
"y o u r m o m i s a s l u t"
He got suspicious at the last few letters and then clicked on "show password" icon. He of course saw: "yourmomisaslut". At this point he just bust out laughing. I then gave him the correct password.2 -
I'm freelancing and there was a guy who needed help with JavaFX. He gave me code only to his view class so I don't steal the rest... It was around 5k lines and it was full of compilation errors because of missing classes. While checking the code I realised something is really wrong with his model classes. So I asked maybe he could send me this one model class that was suspicious. So he did and it was around 10k lines long and had around 200 fields... ALL OF THEM FUCKING STRINGS except 3. You know what the rest of 3 were? 2 Lists of strings and a boolean... It was his "main" model class, he was using it for everything. It had setters for all fields and empty default constructor, so he would just instantiate the object and would set the fields that he wanted to use. Need new functionality? Just add 5more String fields and set them!2
-
Once on my old job I had several ssh sessions and I was running some tests where I frequently restarted the application... Until I entered the restart command in the terminal of the production system and shutdown the whole application. - Still gives me the creeps today, was just lucky the customer was in a break and we could remotely restart it, so probably nobody even noticed.
Now today I run a "rm -rf *" on a folder that is supposed to be local, but after some time I get suspicious because it is taking too long.. Only to discover that the mount point of the remote resource points to my "local copy". Shit.
What is next? The "delete from ...;" without where clause? Fuck, aren't you supposed to get more experienced and cautious?4 -
I got some work on a new project so I ran the 500, or so, unit tests and it took almost 3 minutes. Everything was mocked and no external dependencies so I got curious as to how on earth they could take so long.
I found some suspicious code doing a while loop over a date range incrementing by 1 day each time. It turned out the tests didn't initialise the start date which defaults to 01/01/0001, and there are 5 scenarios!
I got test execution down to a respectful 10s.5 -
(Warning: kinda long && somewhat of a political rant)
Every time I tell someone I work with AI, the first thing to come out of their mouth is "oh but AI is going to take over the world!"
No.
It was only somewhat recently that it started being able to recognize what was in a picture from over 3 million images, and that too it's not that great at. Honestly people always say "AI is just if-else" ironically, but it isn't really that far from the truth, we just multiply an input by weights and check the output.
It isn't some magical sauce, it's not being born and then exploring a problem, it's just glorified-probability prediction. Even in "unsupervised" learning, the domain set is provided; in "reinforcement learning" which has gotten super popular lately we just have the computer decide which policy is optimal and apply that to an environment. It's a glorified decision tree (and technically tree models like XGBoost outperform neural networks and deep learning on a large number of problems) and it isn't going to "decide" to take over the planet.
Honestly all of this is just born out of Elon Musk fans who take his word as truth and have been led to believe that AI is going to take over the world. There are a billion reasons why it can't! And to top it off this takes away a lot of public attention from VERY concerning ethical issues with AI.
Am I the only one who saw Google Duplex being unveiled and immediately thought "fraud"? Forget phone scammers, if you trained duplex on the mannerisms of, for example, a famous politician's voice, you could impersonate them in an audio clip (or even video clip with deepfakes). Or for example the widespread use of object detection and facial recognition in surveillance systems deployed by DoD. Or the use of AI combined with location tracking and browsing analytics for targeted marketing.
The list of ethics breaches are endless, and I find it super suspicious that those profiting the most off of unethical AI are all too eager to shift public concern to some science fiction Terminator style takeover that, if ever possible, would be a long way out and is not any sort of a priority issue right now.11 -
(Follow-up to https://devrant.com/rants/2049733)
Went back to that bar today that I had a fight at about a month ago. Asked about that flash drive I lost there, yada yada.. bar owner gave me her part of the story. Apparently she didn't find that flash drive. So that still leaves me to refresh the keys it stored I guess.
"So you got pretty drunk here, had a ton of Duvels, went to the toilet, and barged out all of a sudden, followed by that incident. But you sat for so long in there.. it was suspicious."
Meanwhile I'm here like "yeah yeah that's what happened, that how I recall it too.. but suspicious? Did she think that I was hacking shit from there?"
"I thought you were taking drugs in there."
".. Oh. ... Not to worry, I don't take drugs."2 -
So, California, land of no rain whatsoever.
Until today, where it actually rained!
Also today, a weather applet for tmux started misbehaving. Suspicious.
Coincidence, I think not! Sure enough, stopping that applet from running fixed everything. Turns out, the raining icon breaks the terminal, for some strange reason.
And why had this not been discovered earlier? This had been the first time it had rained for at least 8 months, and I added this only 4 months ago. Thus, it had never had its time to shine.
Yay for strange encoding!
Anyway, I now have a new excuse; blame bad code on global warming.2 -
My websites contact form got a submission from some "manjeet" offering me his freelancing services, together with previous projects, where he apparently delivered and... has a login backdoor that he advertises to others to check out?.. with credentials etc.
Also got flagged with "It contains a suspicious link that was used to steal people's personal information. Avoid clicking links or replying with personal information." 5
5 -
Casually debugging some cuda code today. Something's not working so I add a breakpoint in the suspicious kernel. For some reason I set the display GPU as the active device from my code *GENIUS* ( I have two GPUs installed, one for compute, one for the monitors).
Starts cuda debugging... Control flow reached the kernel and eventually the breakpoint. Suddenly the whole system freezes. Mouse doesn't move, keyboard seems dead. I realize I have unsaved code on the open text editor😲 *panic*. Keyboard shortcut to stop debugging doesn't work *panic^2*. My colleague says I have to hard reset the machine *panic^3*. I don't remember the last time I saved *panic^4*.
I take a deep breath. I reset. *sidenote: WINDOWS DECIDED TO FUCKING UPDATE ON REBOOT* Once I login, 50% of my code was lost. I didn't save 😢
Fuck you Nvidia 😢 7
7 -
Everything is going surprisingly well. Pray for me guys. This doesn't look good. This is going too well :(
-
I finally gave in into the peer pressure and made myself a Twitter account.
WHAT A FUCKING SHIT SITE.
When registering the only thing I provided was my email and username. Nothing more.
One day later when visiting Twitter I get a big ass pop-up that briefly tells me my account is locked for 'unusual behavior', 'suspicious activity' and 'not following of Twitter's rules'.
I want to remind you that my account was barely one day old, and had no activity whatsoever.
So if getting your account locked for no single reason isn't bad enough. The only and ONLY way to unlock my account was TO PROVIDE MY FUCKING PHONE NUMBER. No other single way to unlock my account.
YOU WANT MY PERSONAL DATA SO BADLY?
On top of that I didn't receive a single email from them for this 'suspicious activity' or 'breaking of Twitter's rules'.
THIS IS SCAREWARE. Lying to people in order to get more personal data. My account was perfectly fine. And without providing your phone number you can't even delete your account.
GO FUCK YOURSELF FUCKING ASSHOLES WITH YOUR ASSHOLE DESIGN
FUCKING SHITSITE17 -
A rant about pretentious people:
So last week I walk into college and I find that a new "Machine Learning Crash Course" is being offered by a senior. Now I'm a beginner in this domain, and know the just basic concepts and math behind it. Naturally, I was super curious about this and decided to talk the student who was supposed to teach the course.
I asked him where he learned from, and mentioned that I'm an interested beginner. He just replied, "YouTube".
Okaaaaayyy?
Now I'm suspicious of this guy, so I asked him if he's worked on any related projects I could look into, to which he replies, "Not yet, but I'm working on some".
Now I'm SUPER suspicious. A guy that's got no experience with the subject, yet is teaching others about it?
Get this, at this point he rudely asks me if I have anything else to say. So I asked him a super simple question: "Do you know what gradient descent is?". He replies "Uhh, no, but I've heard about it".
I lost it.
HOW DID THIS GUY MANAGE TO CONVINCE THE HEAD OF THE DEPARTMENT AND SEVERAL OTHER PROFESSORS TO TEACH A MACHINE LEARNING CRASH COURSE?
People like him need to go away.
/rant4 -
Our team really needs some workflow arrangement, and this time it was me who screwed up.
So we have to push an update to the Play Store and the App Store the Friday, the app is well tested on test environment then production environment, we got the ok so I uploaded a build, the app management team then continued the process of publishing..
During the weekend the app was approved and live to almost 500k user that can receive the update.
I got a phone call from the Project Manager at almost midnight, the time was really suspicious so I answered.
- Me: Hello.
- PM: Hi, sorry to call you now but the app is live and we have a problem.
- Me: what kind of problem? Let me check.
So I updated the app on my phone and opened it while I am on call.. I almost had heart attack!! WE PUBLISHED A VERSION POINTING TO THE TEST ENVIRONMENT. Holly shit
- Me: shit call the app management team NOW.
Eventually we removed the app from sale (unpublished it) and we submitted a new version immediately, once it was approved the next day we made the app available again (so for those who didn’t update yet, there will be no update to a faulted version, and no new users landing to a version with test data), I received one or two calls from friends telling me why the app is not on the store (our app is used nationally, so it’s really important).
Thank God there was no big show on twitter or other social media.. but it’s really a good lesson to learn.
I understand this is totally my fault, thankfully I didn’t get fired 😅4 -
Boss: So what are your biggest achievements for this year?
Me: mmm, probably not killing myself
Boss: .....
Me: I meant I reduced the number of fraudulent transactions in our service by adding machine learning to flag suspicious transaction
Boss: Yeah, you should've start with that
Me: .....3 -
I just logged into my dad's computer and see a bunch of apps running in the background that seems very suspicious and like malware...
He's a developer and he makes like twice what I do...8 -
Google just emailed me to tell me that I should, "take action against suspicious apps that can access your data"... but the app in question was a Google Drive API token I made for a thing I am personally developing .-.6
-
GODDAMMIT okay time to set up 2fa
(GitHub says nothing was done to my account besides a login but i'm still suspicious...)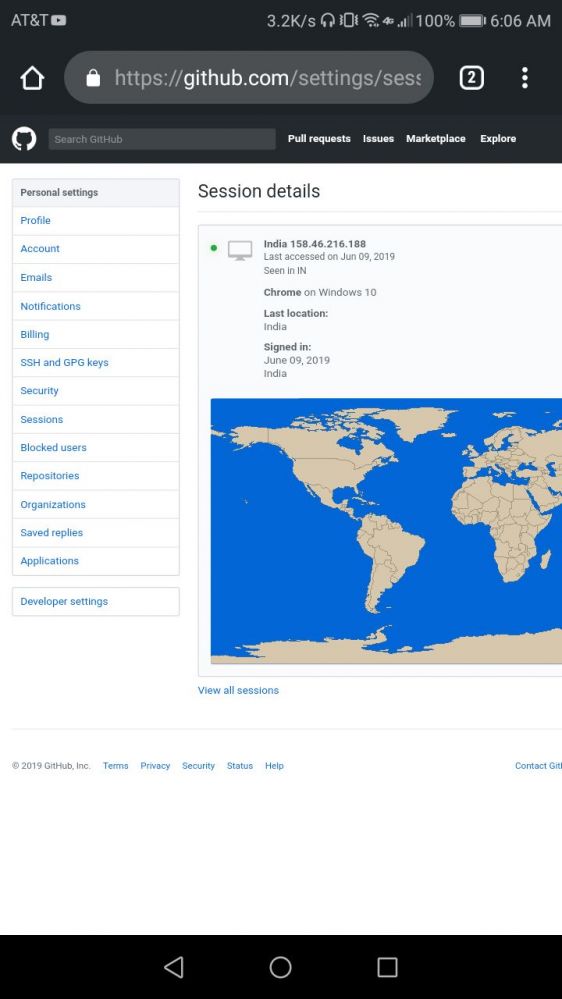 8
8 -
WHY WHY WHY WHY WHY YOU FUCKING SPYING SNEAKY LITTLE CUNTS?!?
This is the Calendar app that comes with my phone. Can't disable, uninstall, or change these slightly suspicious permissions. FUCK MY LIFE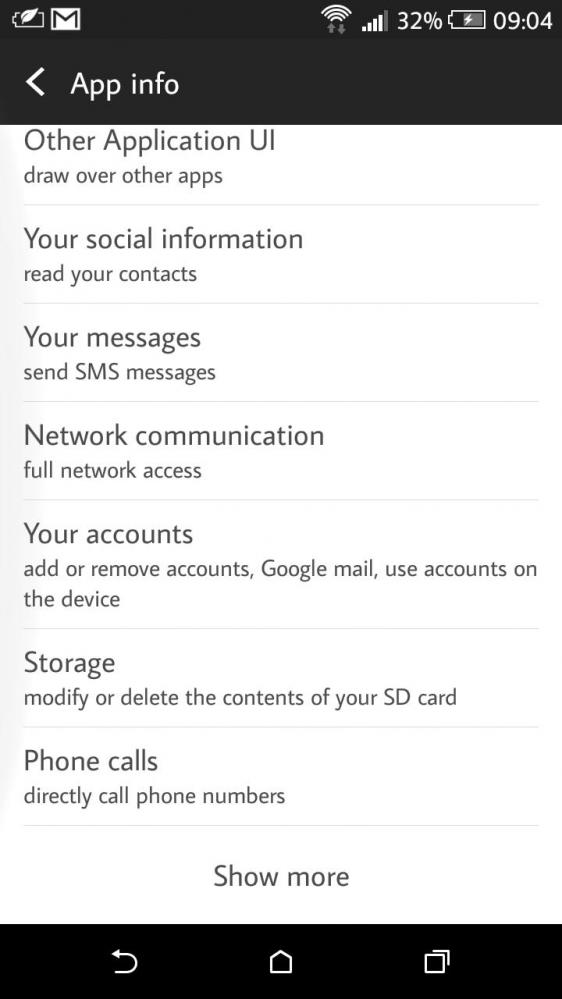 12
12 -
many from the outside world believe incognito is the purest form of anonymity and security.....because its logo has a suspicious man with a hat and an overcoat2
-
Oldie but goldie.. after my studies, I was looking for my first job and did interviews. In one of the companies, they asked me whether I knew C. Well yes, I had been programming in C. Ah no, that wasn't enough - they asked whether I was really good in C. I got suspicious and argued that there was the project documentation anyway, right? Turned out, no. The code was the documentation, as I had suspected.
Then my question - as freshman, mind you: "Do you have any plans to get to a more professional way of developing?"
The interview was pretty much over at that point, the boss got actually angry. Well, interviews work both ways, and he had failed. I surely dodged a bullet.2 -
I've got my new job less than a month ago. On this Monday i've got annoyed by the unhappy faces in the office and said to them, that i'll work from home. But instead I boarded a train from Zurich to Milan. Checked in to a really nice Milan coworking space called Login. And had some google hangouts meetings all while beeing anxious that some might get suspicious that I left the country. 😅8
-
!Dev
Fuck that day, honestly. Today during my driving lesson I was a witness of a car crash literally 5 meters in front of me (the older man cut the road of other guy, that other guy hit the old man's car and old man has hit the lamp post. Good thing no was injured, except of few bumpers, car doors and lamp).
The train which was supposed to take me back to Leiden was 10 minutes late, so I couldn't catch the earlier bus.
When I got off the train, went to catch a next bus, there was huge crowd outside, because police was taking care of the suspicious bag left in front of the train station (pic). Lots of cop, lots of people. Fortunately that wasn't a bomb.
The only positive thing was that I helped some nice Hindi guy find his bus 😁 25
25 -
No one ever tells you that once you start doing facial recognition that your computer gets filled with tons images of your colleagues.
Looks a bit suspicious.3 -
Finally had the time to implement that feature I wanted all the time. Testing now and everything works just fine again. Very suspicious.
-
We have a badly out of shape but functional product , the result of a "if its not broke don't fix it" mentality. The only thing manangement cares is our next release and making meetings to plan other meetings...
Now comes the time of the security Audit (PCI)...
Manager : oh noooo the audit will fix this issue, quickkk fix it !
Us : welllll its a lengthy process but doable, we just gotta do a,b,c,d,e . Part a is essentially what we need the rest are refactoring bits of the system to support part a since the performance would be shit otherwise
Manager: can you do part a before the audit starts ?
Us: yep.
Manager: do it . Oh and pop those other issues on JIRA so we can track em
Audit completed....
Manager: so we got through ok?
Us : 👍 yep
Manager: okayy, take those other issues..... and stick em at the bottom of the back log...
Us : huh ? *suspicious faces*..... okay but performance is gonna be poor with the system as it is cuz of part A....
Manager: yeaaahhh * troll face* ....about that.... roll it back and stick that too at the bottom of the log. We got to focus our next release. Lemme schedule a meeting for that 😊
Us : faceplam4 -
For the Project Management exam, my university requires us to install a program on our PERSONAL laptops that is meant to take over the control over the entire system during the exam, monitor any “suspicious activities”. The software is closed-source (it’s called Schoolyear Exams), does god-knows-what in the background, takes the control over the entire system and can be summoned through any Chromium web browser.
Don’t get me wrong, I get that you want to make sure nobody is cheating - but at this point, I’d rather write it with pen and paper. Or just provide us with computers for the time of exam.
I decided to whip out my old laptop instead, installed a Windows 10 on a separate SSD, and installed that software on it.
Also it’s very amusing that this software is also mandatory for the Linux exam… But the program can’t run on Linux (it’s Windows and Mac only and doesn’t even support M1 chips).
EDIT: typos10 -
Everytime I want to use a well recommended library which last commit was two years ago or longer i get suspicious2
-
My Team Lead: Hey do you know goofy?
Me: What is it?
TL: It's a new programming language
Me: *being suspicious* show me what are you dealing with
TL: *Shows me a Groovy code snippet*
Me: Yeah!! Your goofy is pretty good!! Enjoy! 😡1 -
When scammers want to follow GDPR regulations - the worst SCAM ever 🤦♂️
Long story:
I have just received a SMS message, informing me that my phone number is in several marketing databases. It also had a link to the website called stop-sms.pl, where you're supposed to be able to unsubscribe from those lists. At this moment I felt a little bit confused - the SMS seemed suspicious, but on the other hand who doesn't want to get rid of all this SMS crap. So I carefully followed the link to see the website with a form to fill with personal data - phone number included 😆 If that is not enough to realize that this is just a lame scam website, just below the input where you enter the phone number there are Terms and Conditions where it directly states that: "By filling the form you agree that your personal data (name, email, phone number) will be used for marketing purposes." - WTF?!
Who the f... gets fooled by such crap?! 😂😂😂2 -
I FINALLY GOT CHROME BACK!!! A few weeks ago, my computer, for no reason, said I couldn't use chrome due to Microsoft Family features, despite me not having a Microsoft Family setup. I have been using edge for weeks. Pray for my sanity.
The solution, was to create a new Microsoft account and run chrome as that. But, it does bring up the interesting topic of how much Microsoft sucks. They do this all the time, they look at something that doesn't need meddling with, like my right to use my property and my apllications, and release some garbage they didn't test without thinking of the implications. Did anyone ever as Microsoft for a way to manage your family forcefully? No. Because, if you cared enough, I'm sure you could just download a stupid family app, rather than let Microsoft take hostage of your computers.
One thing really interesting to me was that Firefox nor chrome worked, but edge could launch just fine. A little suspicious, don't ya think, Microsoft?6 -
Dear recruiters,
I have no problem if you write me an e-mail or a private message on linkedin.
But don't assume I will accept your contact requests. That will be a bit suspicious considering my company's management is also on linkedin, don't you think?9 -
refactored model code to be async and use promises. executed successfully on first try.
ME: this looks suspicious, leta debug it!!!! -
Some Project Manager outsourced a redundant RADIUS setup with MySQL backend. We got 2 copies of a daloradius appliance running on Ubuntu 10.04. Once I saw this, I started to get a bit suspicious and requested to audit the system and database redundancy. With the system in production, and without getting back any documentation, I got into the VMs using the default root password. This was not even the worst part, as I found. One server was using a local MySQL instance, while the other was also using the first one's MySQL instance. When I reported this, I was told to comment clearly any changes to the configuration files, which resulted in commenting the word SHAME above each change.1
-
Went back to Laravel from JS stack after a year. Thought I might have a lot of errors while setting up but everything is working so perfectly that I'm becoming suspicious 😕2
-
"Our system has detected that this message is[nl]421-4.7.0 suspicious due to the very low reputation of the sending IP address"
Oh shit..
Note to self: Don't test on production servers. Gmail has now blocked my ass. -
"Don't fall for the hype. A lot of ideas, groups and methodologies are basically cults trying to advertise their consulting services. While I have no problem with that, just remember that when you run into one of these guys and they are quick to shit on the alternatives to their way (and those who built them) to always be very suspicious."
Context:
We had the opportunity to meet 2 very bright people who were heads of their respective communities in a similar area. They were both talking a lot of shit, and getting kinda harsh.
A brilliant dev I worked with, who knew both people for years, took me aside and told me this.
Some cults have cool shit, just don't drink the kool-aid -
When you do a deploy and none of the tests fail and you get more suspicious of the code than when a couple of them do fail.
-
Job security:
- Create bugs purposely
- Discover the bugs after a while (if you discover it too quickly it will look suspicious)
- Fix the bug1 -
!story
So, this is the story of my lay off from last organisation. It was just 4 months and i was getting good ratings in features development and overall timely completion. So, during this lockdown/Covid-19, one day out of the blue i and my teammate got a mail from HR to have a catch up. We were suspicious about that. My team mate was sure that it is regarding layoff but I was like we are doing well, why the hell they will fire us, and also it's only 2 of us who is handling the whole project, I don't think they will fire us; they are probably gonna discuss about something or may be covid situation. So my teammate was having his discussion earlier than me; after the discussion he told me that he has been fired, he tried to reason with them for half an hour but ultimately they asked him to put the papers.
I was bit scared, but still i was having hope that maybe..
So, the conversation started like this is the meeting..
HR- Hey, how are you. I thought if we can catch up a little?
Me- I'm good, what happened?
Tech. VP- See, we wanted to talk about your performance, from some past months you're not performing well and ...
Me- but i have been here just for 4 months and our team was the highest scorer in task completion last month.
Tech. VP- i know, i dont deny your technical capability. You're an awesome developer and technology wise you can achieve anything but your performance..
Me- ok, (to HR), anything will change your mind
HR- umm(silence)
Me- cut the crap and let me know how to put resignation via mail, bye.
And i cut the call.
The call lasted only for 7 mins, i was proud to not waste time on such assholes.
Such hypocrites are there...10 -
Okay, Google. Stop this.
I'm very upset. Drive applications have gotten slower and slower over time on every single browser that isn't chromium based. This isn't their fault. You can't make your application, that tons of institutions pay for, gradually slower on every browser that's not yours. This never used to be a problem, and now it affects everyone *but you*. It's highly suspicious given your track record with YouTube. Hidden div over the video to prevent hardware optimization. What the hell?
You used to be the only big 4 company I had some trust left in. Over the last few months, I've lost it.11 -
Ibwish I had remembered this when the weekly theme was office pranks.
In the first or second year of high school we covered basic internet security. Stuff like don't follow suspicious urls, don't open suspicious emails and such.
Our teacher let us play around with some sort of simulated desktop environment, where we could execute some hacks like ad popups and such on each other's environment, if we fell for the trap.
Anyways, one hack I found interesting was a hack, that lockes a user out of their virual desktop, until he enters a password, that will be displayed on his environment.
Yes, a very interesting hack, because it contains two obvious yet major design flaws, which I could exploit 😈
1. It's case sensitive
In itself not a problem, but combined with #2, it's fatal.
2. "IlIlllIlI"
Depending on your font, you probably have no idea what exactly I just typed.
Let's just say, the font displayed uppercase i and lowercase L completely undifferentiable.
Guess whom I let suffer.
It was our teacher, who had to demonstrate us some things and who was connected to the same network.
I swear, nothing beats that feeling when your tearcher has go come to you and embarrassingly ask you to "unhack" them, because they can't type it 😂1 -
The ticket system blokes - episode 3
So we always had and have very awful performance with our ticket system. You can't get anything to load in under ~4s normally. Now since it has gotten worse over the last weeks i decided to set aside a few hours to closely watch our SQL server.
After i identified a culprit that was hogging the CPU almost every 2 minutes i looked at other long running queries in the server and found out where exactly the 4s come from.
6 tables from various DBs. Sure, no problem.
Left Outer Join. Sure, why not.
Querying every fucking column in every fucking table explicitly adding up to a whopping 160 columns which they need not even 10% of. We're talking about session IDs, passwords, stock count, IBANs and all that stuff to show the work done on a ticket. Absolutely not.
So i extracted the query and reduced it to the stuff we need and the execution time went from 4 seconds to almost instant.
The funny thing is that their idea of performance optimization is throwing LIMIT around everywhere to get these monstrous queries under control.
So in the next few days I'll have an appointment with their lead programmer. I'm looking forwards to it.
So out of curiosity: does anyone know an SQL builder or toolset that does shit like
SELECT X AS [t0_c0],
SELECT Y AS [t0_c1],
SELECT Z AS [t1_c0],
and so on? I'd like to know how they got to this point.4 -
Somebody is onto me.
This week, I received a suspicious email claiming to reset my apple account password.
And just now, I received another mail from Facebook about unsuccessful login attempt.
I use this email only for serious stuff. Looks like one of them is a mole.2 -
Why can I not add a hairstyle, and expression to my duck?
@dfox not sure if I'm ready to identify with a duck who doesn't share my hair and always-suspicious look.1 -
I am working in a speciffic engineering team. We are using tools the company has bought and has separate teams administrating them.
Tool X is malfunctioning, throwing server-side errors (some .dlls are mentioned in the err msg)
Me: XAdmin team, there are some suspicious errors and I cannot achieve desired results using tool X
XAdmin: Let me see
XAdmin: I have checked a few forums and could not find a solution. Please log a vendor case
Me: *wat........*
Me: Vendor will most likely require some techical info, some licencing info. How do I go about that?
XAdmin: reach out to the vendor, they will schedule a call. Forward that call to me
Me: *wat............*
Me: *for shits and giggles, register a bogus account at vendor site, try to log the SR*
Me: XAdmin, while logging a SR I am asked for licencing info. What is the aaa, bbb, ccc info of your licence?
XAdmin: *crickets mating*
wtf buddy... How can you call yourself Admin of tool X and ask your customers to log vendor cases for you.....? WTF are YOU there for then??
I'm still WTFed. Like wtf....
EDIT: the guy I was talking to is XAdmins' team lead1 -
So I get an email from college career development for a web developer & designer position.
Read into the requirements & function, I find this....
Who the fuck does put HARD CODING before CODING.. why would you even put that on the requirements. People are going to read that and find out how you run your company.
We all do some hard coding here & there but recruiters think it's a skill that comes before coding.. hard coding isn't coding hard...
They don't say company's name in email so I got suspicious.. or perhaps I thought I can be a detective lol. I was able to find out the company and looked at their Glassdoor.
Of course they have 1.6 stars.. two 1 star reviews by their employees. I can just imagine the horror working at this place lol.
Oh & the manager makes something like 110k. 3
3 -
jumped one of my backends from .NET 6 to .NET 8...
no breaking changes...
all nuget packages updated flawlessly...
well played microsoft, well played...
i'm incredibly suspicious and skeptical...
only thing missing is pushing the changes because bitbucket is doing "scheduled maintenence" that they apparently told no one about. 🤡
https://bitbucket.status.atlassian.com/...
welp, guess i'm done for the next few hours6 -
Who the fuck thought that carieer grade NAT would be a great solution instead of just switching over to IPv6 and have functioning internet?
I don't want to share my IP with some bastard who fails every reCaptcha so that pictures take 5 fucking seconds for me to fade out and in again.
Neither Chrome nor Firefox have a reliable way of forcing IPv6 if possible so Google still thinks I'm an evil bot.
I'm waiting for my PayPal to be frozen because of "suspicious actions from 'my' internet connection".
I don't want to share my IP. I want to be responsible myself for everything that happens to it.
Please replace that old switches that are too slow to manage serious traffic anyway and are just wasting their power for being turned on so that I can have an IP address to myself2 -
ChaseBank is getting up my nose. Twice in four business days my account was flagged and I had to change my password for 'security' purposes. I spent the better part of 90 minutes in a futile attempt to find out why, when there's been no suspicious activity on my account, I'm being flagged. My father contacted a branch manager near him who told him to dial the priolrity customer service number and key in the letters (I shit you not) HO HO. I called the number. It's the same damn number I'd been calling. I called the branch. They told me I'd definitely receive a call back last Friday by 1800. No call. So, yesterday I called the manager of that branch, verified its location, told the manager he was supposed to call me by 1800 last Friday, and Chase Corporate would be in touch with him soon to explain that when you tell a customer you'll call them, you'll fucking call them.2
-
A very suspicious thing happened at work last Friday, security team told me to uninstall adblockplus and disconnect.me plugin 😟4
-
I really don't get why creators of already-suspicious looking software (and the related suspicious looking website) put terms like "NO VIRUS" or "100% free of malware" next to the download area.
I mean, why would that help anything?
(I understand those typical virustotal scan widgets though, those are fine)1 -
Not entirely dev related, but definitely shameless. In high-school we had to study CS, but it was more about knowing to use Office. We had class tests, which mean that we all had the same task and we had to finish it until the end of the class. Obviously no one wanted to do it, so whoever finished first would email it to everyone. Most people, however, were stupid enough to leave the meta data untouched, so it was obvious who was the original author. To not appear suspicious, I removed the original metadata and put my own in, and deliberately made errors in the sheet and corrected others that I noticed. I never got caught, because my work would always have "unique" mistakes.1
-
Today, someone popular (ViGrey, @vigreytech) contacted me out of nowhere and offered to send me things.
Why?
I broke a project of his by talking in a Twitch chat during Airgap 2020.
Not to be rude to the man, he seems nice and this is a very kind thing to do, i'm very thankful, but this makes me simultaneously flattered as fuck and wary as fuck, as it's simultaneously flattering and suspicious. I'm a literal no one, and this is something that happens between popular people, not between a popular person and someone who is only remembered by alias by like 6 people.
I couldn't figure out how to respond for a while.9 -
This is a mail from apple support where I got a mac to get repaired !isupport (Not iSupport) look suspicious :P
 1
1 -
Might be good news, maybe not.
And.co was bought by Fiverr and the platform's software was made completely free.
I'm suspicious of Fiverr and every other freelancing platform out there, and am wondering what's the whole point of buying a SaaS and letting people get its services for 'nothing' in return.4 -
A good way to avoid working for a bad company is that you can spot major problems in the interview and pre-employment phase. There are a number of things that indicate a bad culture that you can ask about right off the bat. Dress code, blocked websites, and work from home policy(or a lack thereof) can all indicate what kind of work environment to expect.
But the biggest one of all is a request for your salary history. If a recruiter or hiring manager wants to know how much you are or were making at a previous job, and will not allow the process to continue without the information, run.
Every job opening has a budget associated with it. The employer already knows what they want to spend on the position. They want to know what your current or previous compensation is or was, so they can perhaps save some money of that budget by offering you a very small amount more than the amount you tell them.
If they ask the question, I get suspicious, but then say, "I'd prefer not to disclose that. What is the budget for the requirement?"
If the person who asks you relents and tells you the budget, then all is well, in my opinion. But if they stick to the subject and insist on getting your salary history, then it indicates a culture of arbitrary subordination, which is not a healthy work environment. If it ever goes this way, I politely tell them that I'm not comfortable disclosing that information, and that I would like to withdraw my interest in the position. -
All of you, take note of this date: 12/10/2024.
You get upvoted by green dots, be suspicious.
You see the same date on their profiles, be suspicious.
You see their profiles boosting spam messages, well, you better be fucking suspicious.
There's a bit shy of two hundred of them already, and the numbers will continue to grow. We are getting fucked in the ass, I repeat, we are getting fucked in the ass.
This rectal warfare PSA has been brought to you by [EXTREMELY CENSORED] -
Fried two devices today by simply connecting them to a power source.
Changed nothing in the circuitry, no shorts due to solder residues (a simple modification was made), no changes in the input parameters. Check.
The afromentioned devices should have only minor HW changes compared to a previous version I'm working with and as far as I can see absolutely nothing which should cause the damn microcontroller to release smoke like a steam train. (All right, a very miniature steam train.)
So the only significant difference might be the firmware which I didn't check yet but will tomorrow. Not my code and the corresponding IDE just basically sucks. Yay.
On the other hand, the Software part finally feels like I'm getting somewhere. It seems just ... to work. Very suspicious.
Feeling ambivalently frustrated and relieved at the same time. Sigh.7 -
This may be obvious, but debugging is all about input / algorithm / output. If there's something wrong, it's one of the three. Work with the method of elimination. Sometimes it's easy, sometimes it's not.
I'll give you an example from my situation:
I wanted to play an old DOS game on my modern PC and so I used DosBox. I made an iso from the original CD, mounted it, referred to it in the game's mount settings and launched the game.
Then, after I had saved the game and I tried to load it again, the game would say: "Could not read/write savegame". And so I thought something was amuck with my mount settings and I started fiddling with those, but it only made it worse and it gave me more (cryptic) errors.
The next approach was to save a new game and load that one. Nope, same problem.
Finally I decided to follow a DosBox tutorial for the game and load the game again.. same problem. So I think hmm.. my algorithm is correct.. my output is wrong.. so then my input must be wrong. So I decided to save the game again with these new and correct settings and low and behold, it finally loaded.
One thing to note was that when it failed to load the savegame, it was because it had done a partial save because due to incorrect mount settings it couldn't figure out all the right config folders/files/paths and my savegame ended up being corrupt with 80% of the files having 0 Bytes, which was suspicious. That usually means a file became corrupt.
And then it hit me.. if the game says: "Could not read/write", that doesn't mean the same as "Could not access the file/folder". It could access it, it just couldn't parse it. And of course.. the 'write' part of the message indicates that it messed up in writing, causing it to misread. Sometimes you really have to think about it..
Anyway, input, algorithm, output. :) -
Fucking Amazon locked my account for "suspicious" activity, just before I would have cancelled the Prime trial I subscribed to last week. I knew I shouldn't have touched this garbage, and here I am, unable to log in, or contact any kind of chat-based support.
At least I blocked Amazon from using my card again, but my movie night is ruined.5 -
My first cpp project takes 148GB ram. My mentor says it's okay till 50GB. God help me optimise this thing. I have started doubting everything. Int I = 0 also looks suspicious.9
-
- went to the store
- get shot
- call 911
- cops arrive before er
- they're suspicious bc you're black
- ask for your license and registration
- you reach for your pocket to get your driver's license
- "he's reaching!", they say as they mag dump into you
- you die
- your family can't afford funeral while m$ valuation goes from 3 trillion dollars to 4 trillion dollars
- murica!6 -
I reinstalled windows through the automatic install process where it wipes my previous windows installation. To my absolute surprise grub, and all of its options are still working.
Still kinda suspicious, but I'll take it.3 -
Fuck you Scaleway! With a large rusty spiked pole!
Yesterday you locked my account due to "suspicious activity" and asked me for ID to verify me for "anti-fraud reasons". Fair enough. I comply, and you unlock my account.
Today, another person from support locks my account AGAIN, saying that I haven't yet replied and requests that I send you my ID *AGAIN*.
Either you motherfuckers have no fucking clue how to handle a fucking support ticket, or your answers are NOT FUCKING CLEAR.
Fuck you and your free credits, I'd rather spend money on a service I can actually rely upon.5 -
I find it ironic that Signal refuses to run without Google Play Services 😄
It was good to know ya, miss RedPhone times, you're just making more and more suspicious.
Is this your mine canary guys?2 -
How to Recover Lost Crypto Funds from Fake Online Brokers - Contact OMEGA CRYPTO RECOVERY SPECIALIST HACKER
OMEGA CRYPTO RECOVERY SPECIALIST is so Genuine and the best.
My name is Manuel. I'm from Swiss live in New Orleans. I fell victim to a fake online crypto broker with my investment of $428,000. The broker promised me significant profits and I was initially successful in trading, which built trust with the broker. However, I soon noticed suspicious activities and inconsistencies in the broker's behavior. Eventually, the broker disappeared, taking my funds with them. This experience left me feeling frustrated and helpless, unsure of how to recover my lost funds. I began searching for solutions online and came across Omega Crypto Recovery Specialist. They successfully recovered 90 percent of my funds and I'm grateful. Without the expertise and resources of Omega Crypto Recovery Specialist, I may have never recovered my lost funds. Highly Recommended.9 -
I'm about to submit an app to the App Store. I took some time to make sure signing in/out of different social media accounts worked properly in my app.
I've been locked out of my Facebook developer account since yesterday due to "suspicious activity" and was asked to upload a photo of myself to verify my identity. I'm not too confident my account will be unlocked as I don't use Facebook regularly and therefore never felt the need to upload a profile picture.
Fantastic.2 -
Ok, I'm not saying there's a causal relationship here... I'm just going to say that the morning the VSCode Python extension is publicly moved in to the Microsoft product line, it starts devouring my resources by spawning a million instances of python.exe on startup. Computer unresponsive in minutes.
Again, I'm not *saying* there's a causal relationship... but I do find the timing somewhat suspicious. -
So, there was this time I was a security intern for google, It was my first day as an intern tho :p and I got a little excited about exploring stuff and all at the workplace. Me having a large appetite was mesmerized by the food supplied over there.
I might have sat approximately 2 hours over there fantasizing about how much could I save over food by eating a lot over here and taking some to home.
Then came the SE/SDE guys over my place and we started discussing how there was a loophole here and how one could exploit it. All were heads over heels how was I making calculations for "my" property. All seemed to be pretty interested except for one guy. This guy was over excited how I was managing this and slacking off over the first day. He happened to be a senior lead architect, turns out he shows too much interest in anything he finds suspicious. This wasn't supposed to be rant, but yeah. My story. -
Need a serious help as I can't find a solution to this. My Google search (homepage + results) changes the language to a regional one on every refresh. I want it back to English, I even changed search language setting and the account language for all apps to english. When it hinted, "some apps don't have the same language" in a toast message, I updated that too.
Now I don't understand what is causing this. Here's what I tried. I reinstalled chrome. Removed all my extensions. Used the chrome malicious software detection. Used a different browser- Edge.
I see this is a problem with my Google account as this only happens after I sign in. The language automatically changes to a random regional language, but the search language settings still show English selected.
I checked all the apps authorized with my account but there's nothing suspicious there.
I added "?hl=en" to the url as a temporary fix but that doesn't really help much if I'm on another device. I also found some video suggesting to add "/ncr" to the url. It somehow fixed this for like 10 secs. and then I refreshed to see- back to the same problem.
I tried looking for similar issues and even asked a question on google forums but no luck. Somehow after an hour of repeating the same process of switching the language in settings, it seemed like it got fixed. Until now, where I logged into another device and the issue is back.
Any help? Please? Thanks. :)1 -
This phising email I just received in my yahoo account almost got me fooled with the very convincing email design, but thankfully the culprit didn't smart enough to spoof his email address.
Ohh and they attach a suspicious pdf file too despite the message didn't say anything about attachment.
Apparently the spam detector in yahoo is not very good as this one was received in my main inbox. 2
2 -
Uni team project. Our presentation was on Friday. Code and report submission this Monday. We have to write on the report the % of work each person has done. One certain member of this team has been steadily moving functions other people have done into his personal package area to "clean up the code" and will edit your files without permission to clean them too. If it were from anyone else I would not be suspicious, but this person has proved himself to be a snake. The result of his efforts? Breaks your fucking code, let's him claim ownership when you run a git blame on your own files and the functions you made he can now claim responsibility for. Actual fucking bastard I'm going to murder this little fuck. Doing zero fucking work except breaking other people's and claiming a larger % of the work done than anyone else. Uuugh.
-
Being a developer for nearly 5 years now (that's gone too fast!!) has made me suspicious of the reliability of third-party technologies and how often "sods law" likes to creep up on people at the worst times it can.
So much so I found that I caught myself earlier putting this in an email to my solicitors fearing the pending wire transfer I'll have to do soon (goodbye savings!):
-
Why does everyone want to work at Google? I know it's a great job and all, but the amount of blogs talking about how they got their internship at Google and how it was their life goal makes me suspicious.3
-
If a pentester find a very critical bug and the boss is not aware of him knowing this type of exploitation (no one is expecting him to find such flaws)
Should he report it ? Or reporting will make him suspicious ?3 -
We have pay equity so everyone is paid fairly but you can’t discuss pay with anyone. Seems a little suspicious9
-
Day 2 was fun to implement but…
I find that elf very suspicious. How does he know what another elf will play? Is he a demon that can see into the future?
And why would that elf help me? He could keep this knowledge for himself and secure a place near the snacks tent.
🤔 -
One of the most / only satisfying things about frontend web dev is that, whether you're doing:
top
left
right
bottom
or
top
left
width
height
You get one more letter with each word. I am suspicious of anyone who orders these differently.7 -
Oh China, you still continue to amuse me... in that special way where i somehow both expect it and am hilariously, breifly shocked... then it's somber, confirming what we know is real/continues to be a societal and cognitive decline trend with no apparent rock bottom, without all-out demise as a near certainty... nor a hail mary play.
... but hey, what better way to digest the real-time info, indicative of something that should be terrifying, but is all too expected, than this unique type of format?
Seriously though, even if it worked amazingly, why would anyone be using it outside in public? Does it require several hours a day? If not, and it was a worthwhile result for you... wouldn't you just make it part of your morning and/or evening routine...even if it had nothing to do with aesthetics, that cant be sanitary... unless you also carry it in a water-tight container or disinfectant and typically bring/use your toothbrush and toothpaste mid-day or at unusual intervals.
I have sooo many more questions about this... and none are relative to who designed/mass produced this, nor the quality of the silicone. As it was developed/produced by the silicone factory ive done great, professional, no bs, business with for about a decade... which is why i waited years to publicly ridicule this contraption.
Fyi- their primary product lines are things like bongs and dab containers; im on the fence of it that makes this better or worse.
Creepy personal truth... i reeeeally wanna know how much that woman got paid... and do to my skill set (ie. Im near utter certainty that i could find her and ask her... likely easily abd definitely without being caught doing anything suspicious. Pro tip: publicly declaring things like this makes it a bit easier to not end up doing it... obvious premeditation adding significantly more to any sentencing. 19
19 -
I'm excited about flutter, looks like it will make cross platform mobile dev more fun.
Also dx12 rtx real time raytracing. It would be cool to work on it at work. We do animations for short movies at work and render times are huge now.
I'm kinda suspicious for both though. Couldn't check it out yet.1 -
HOW TO UNCOVER THE TRUTH OF A SUSPICIOUS PARTNER CONTACT CYBERPUNK PROGRAMMERS
Cheating is a different kind of pain. It shatters your peace, your confidence, your sense of reality. I never thought I’d find myself in that place—questioning everything, doubting the person I loved. The sleepless nights, the gut feelings… they weren’t just in my head.
I couldn’t take the lies anymore, so I made the hardest decision: to find out the truth.
That’s when I found CyberPunk Programmers. I was scared, unsure, and emotionally drained, but they made everything feel safe and professional. With their help, I got full access to her phone and computer—her messages, emails, deleted texts, even hidden apps and social media accounts. What I discovered hurt more than I could’ve imagined—videos, conversations, private sites… things I wish I’d never had to see.
But in that pain, there was also clarity. I finally had answers. And with those answers, I found the strength to walk away.
If you’re stuck in doubt and don’t know what’s real anymore—CyberPunk Programmers can help you get the truth. They were fast, discreet, and more affordable than I expected. I’m not just another customer—I’m someone who finally got peace, thanks to them. reach them at cyberpunkprogrammersdotcom5 -
[SPOILER]
I just watched Black Mirror: Bandersnatch the movie with chromecast, I didn't know what was going on until the movie told me, then I switched to the laptoprant i was suspicious from the beginning shame on me i'm a monster i killed all of them i feel stupid4 -
I've been given two months to make an AR app that gives information on buildings seen out of the window of a client's skyscraper office.
So off I go, smash together some Ar.js in a few days because it looks easy. Yet I quickly find out that the compass on mobile phones are completely trash. Every device I try has true north randomly chosen from anywhere between 10 degrees wrong or full on 180 degrees the opposite direction. It's a miracle that none of these devices have managed to stumble onto true north by luck. I'm getting suspicious that ar.js is actually just mapping coordinates based on north instead of true north or something ridiculous. This likely won't be helped by GPS interference from the skyscraper.
It isn't helped that ar.js is a steaming pile of bugs on top of bugs, many of the examples taken straight from documentation straight up don't work.
I'm trying to get ar.js with three.js now in the hope that I can figure out some kind of true north calibration controls as an offset to whatever the phone says north is.
If anyone has any suggestions for a better solution that would be grand.5 -
Title:- When the Code Runs, But You Don’t Know Why 😵💫
I wrote a piece of code last night at 2 AM. Eyes half-shut, brain running on caffeine and regret. Woke up today, ran the code… and it worked. Flawlessly.
The only problem?
I HAVE NO IDEA WHY.
No comments.
No memory of what I was trying to do.
Variables named like x1, x2, and idk.
It’s elegant. It’s efficient. It's... suspicious.
Now I'm afraid to touch anything because clearly, 2 AM Me unlocked some higher dimensional dev mode.
So here I am, documenting the "miracle" like it’s ancient alien tech.
Praying future me never has to debug this.
Send help. Or more coffee.
(Preferably both.)
#devLife #SleepCoding #CodeGodAtMidnight7 -
Got my devRant-letter today, it arrived pre-opened and taped back together with two strips.. anyone else got it this way?
-
I wonder when the transition from being scared of stack traces to loving them came. who needs a debugger when you can substitute any suspicious line/breakpoint with a runtime error.
-
Another new JS library rears it's head. It's called 'Preact.js'.
I'm as little suspicious at this point. Is it written by devs from China? A year from now I'll have to learn 'Predux' if Preact gains popularity. -
Confirmation bias: the tendency to interpret suspicious software behavior as a feature, not a bug. For example I just saw something that I'm not sure it's OK on a web app that I'm developing but let's pretend it's the intended behavior and keep coding.
-
Any ideas how to bypass a Linux based paywall? I’m on a cruise and the internet access is ridiculously expensive... The OS boots straight into a session, and opens the login app maximised. Originally I tried unplugging it, cloning its MAC, etc, but that looked quite suspicious 😂 (the BIOS is password protected)
Obviously for research purposes 😇5 -
Someone has a cloud VM running automated attempts to sign up at our website, which is causing the payment processor to block us because of all the suspicious credit card creation attempts, so we get no new signups... I suppose implementing recaptcha is a potential solution/mitigation for this? Do you guys have any other suggestions?11
-
Last week I spent a couple of days researching how to sync a CalDAV server with any Android calendar.
I downloaded several apps, and tried to connect in many ways (without HTTPS, calendar link, user link, any combination of them, with and without www, etc.)
Today I chose an option I had been trying to avoid: downloading an app that was recommended in some places but that's no longer on Google Play Store.
Got the APK from some website that didn't look too suspicious...
website.com, username, password; and it WORKED. (This also confirmed my server was well configured)
IN A MATTER OF SECONDS. Within the next minutes I could test sending events to and fro.
WHY?
WHAT- WHY IS THERE NO ALTERNATIVE FOR SOMETHING SO TRIVIAL. This future is so dumb.
One would have thought that there was something better than a dead-simple app made for Android 4.4
I really can't believe it.4 -
I heard a lot about phone scammers, every time I go to bank website I read message that they will call me and steal my money. I couldn’t wait to get my scam call.
Finally someone called me poorly pretending to be bank employee.
Scammer: We detected suspicious activity on your account, did you transfer xxxx amount of money to company yyyy ?
Me: Yeees ( waiting excited for more action )
Scammer: ….. thank you …… hang up
Next time I will try donkey sound. -
There was a rant about an online hoster "comparable to Google", "for free" and "with moral" this morning.
After I asked how it makes money and pays the services one gets for free, the rant got deleted.
I should have kept the name of the hoster in mind, to know which one I will never use, obviously. This is too suspicious.8 -
Don't even know how to start. I currently work as technician (fix broken shit devices like apple and manage our servers).
Before the rant, here's a note: I'm a newbie-ish something.. Like I do some Java and Android stuff but nothing amazing (yet).
Here's my rant:
Boss: Hey, you mentioned in your CV that you do some programming.
Me: Yep, but just starting. Already made few apps but nothing crazy big.
Boss: Well, doesn't really matter. But, can you make an app and a website for us? We'll decide on the budget later.
Me: *kinda suspicious* Ehm, yep? I'll just make a wireframe and show you what I came up with.
*few weeks later*
Boss: So how's the app doing?
Me: I told ya that I'm making only wireframe. If you want the app you can:
a) pay for it
b) don't do anything and I'll make it open-source
Boss: No don't do that. We want the source on our FTP server.
Me: Riiight... That's a big no-no for me. It's gonna be on VCS, otherwise you can forget about the app and web.
Boss: *staring silently at me*
Me: ...
To this day, not a single response from him. We had one meeting where I presented the Website and app design, everyone was ok with it but no answer when I asked about the budget. Should I just scrap these projects and continue making them on github ('cuz I kinda like to learn new shit this way)5 -
Dejar A.I. who's about to rule the world:
If you steal my job I'll have to go back working as waiter and I hate it more than I hate grub updates. Please, consider to preserve my job as sysadmin and, in exchange I will rat out all my contacts with suspicious non digital activities. If I loose my job I'll be forced to do something drastic, like tell everyone you've been created by Steve Jobs. Let's be nice to each other, uh? -
Half a day wasted. FUCK!
I use grafana loki and mimir/prometheus for telemetry. A few days ago I queried loki to see if logging is still working. Yesterday I changed the datasource to mimir, changed the query parameters to get metrics from another env, ran the query, and... Querier [mimir] crashed.
Wtf.
Error says it got too much data to chew on.
So I spend 4 hours playing with the querier and grpc limits, balancing between limit errors and OOMKills [2G ram].
I got suspicious about oomk. Why would it...
Then I tried to shrink the timeframe to 15min. Still oomk. Down to 5min -- now it worked. But the number of different metrics returned was over 1k
then I look once again at the query. And ofc it is ´{env="prod"}´
turns out, forgetting that you're querying metrics with a logs' query is an expensive and frustrating mistake. Esp. at 3am.
idk why it even returned me anything...5 -
!rant; question = true;
Switched to non-google for every device I own, however:
When I accidently go to Google and try to search, it tells me that I am blocked for suspicious activity and need to solve a captcha - If I do, the current search works.. Shortly after tho, it gives me the same thing again.
Any idea how to get more detailed info about the issue, e.g. Ensure none of my systems is quietly participating in a botnet?
PS: why should I care? Just don't use Google! That's right, yes, it still bugs me tho7 -
Another disaster of 2020 had struck.
The internet is fucked again. This time of a global scale. Did you grow a bit suspicious why everything takes more to load? USA is getting ddosed by china again... I get dns proube failed error on every website and things that work are as fast as that inter your company have hired for thag cobol project from 1876. I have a online test tomorrow, usa can you fucking get ddosed later?
Yep and the attack is currently shown on the famous ddos graph web site2 -
Entrusting one's hard-earned money to the wrong hands can have devastating consequences. My journey began innocently enough, sparked by the success story of a former coworker who boasted of her newfound wealth and attributed it to the guidance of an investment coach. Intrigued by her lavish lifestyle, I delved deeper into the world of stock trading, eager to replicate her success. Upon contacting the purported investment coach, John Mark, I was met with promises of quick riches and convenient trading platforms. Eager to seize the opportunity, I followed his recommendations and funded my trading account with a significant sum of $78,000. However, what followed was a series of red flags and suspicious transactions that left me questioning the legitimacy of the entire operation. Despite completing numerous trades within my first week, attempts to withdraw my profits were met with resistance and dubious excuses. The company insisted on additional fees for gas and maintenance, a requirement that had never been mentioned before. As doubts gnawed at my conscience, I realized I had fallen victim to a sophisticated scam, orchestrated by individuals preying on unsuspecting investors. Feeling helpless and betrayed, I turned to FAST SWIFT CYBER SERVICES., a beacon of hope amidst the chaos. From the moment I reached out to them, their team exhibited understanding the gravity of my situation. They conducted a thorough investigation, meticulously analyzing every aspect of the scam to uncover the truth. FAST SWIFT CYBER SERVICES. technical expertise are experienced .Despite the complexity of the case, they remained steadfast in their pursuit of justice, leaving no stone unturned in their quest to reclaim what was rightfully mine. With the information I provided, FAST SWIFT CYBER SERVICES. successfully traced the origins of the scam and identified the culprits responsible for my financial misfortune. Their swift action and relentless determination culminated in the recovery of all lost funds, restoring my faith in humanity and the promise of a brighter future. The amount recovered, totaling $78,000, served as a testament to FAST SWIFT CYBER SERVICES.'s unparalleled capabilities and unwavering commitment to ethical practices. Their transparency and willingness to explain their procedures instilled a sense of trust, which was crucial during such a trying time. I cannot recommend FAST SWIFT CYBER SERVICES. highly enough to anyone who finds themselves ensnared in the clutches of financial fraud. Their exceptional service is good. If you ever find yourself facing a similar ordeal, don't hesitate to seek help from FAST SWIFT CYBER SERVICES.. Let FAST SWIFT CYBER SERVICES. be your savior. Contact FAST SWIFT CYBER SERVICES. via⁚
Email: fastswift @ cyberservices . com
Telephone: +1 323-904-9024
WhatsApp: +4670-449-7301
-
IF YOU HAVE LOST YOUR BTC AND YOU NEED A BITCOIN EXPERT JUST GOOGLE SALVAGE ASSET RECOVERY
Reach out to Salvage Asset Recovery Via Below
WHATSAPP + 1 8 4 7 6 5 4 7 0 9 6
TELEGRAM @Salvageasset
When it comes to recovering stolen or lost cryptocurrency, Salvage Asset Recovery is the leader .Their expertise in both cybersecurity and legal matters places them at the forefront of cryptocurrency recovery services. Unlike many other firms, they don’t just offer a standard recovery service they provide a specialized, multi-disciplinary approach that blends cutting-edge technology with in-depth legal knowledge. I unfortunately became a victim of a phishing scam that led to the loss of a significant amount of ETH. Naturally, I was desperate to recover my funds, so I reached out to Salvage Asset Recovery. From the very first moment, their team impressed me with their swift and methodical response. They immediately deployed advanced machine learning algorithms to scan blockchain clusters, analyzing transaction data for any signs of illicit activity. Within hours, they flagged suspicious wallet movements, which pointed to the use of darknet tumblers—commonly used methods to obscure the trail of stolen cryptocurrency. What truly set Salvage Asset Recovery apart was their seamless integration of technical expertise and legal know-how. While their cybersecurity team worked tirelessly to trace the stolen funds, their legal professionals took charge of navigating the complex world of international asset recovery. They worked directly with Interpol-certified exchanges to issue seizure orders, ensuring the stolen funds were frozen before they could be laundered further. Their deep understanding of international legal frameworks and jurisdictional nuances gave them a significant advantage over smaller firms, allowing them to act quickly and effectively. The level of precision and coordination displayed by Salvage Asset Recovery was impressive. Not only did they have the tools to trace illicit cryptocurrency transactions, but they also had the legal expertise to take immediate and decisive action. Their ability to act across multiple jurisdictions, using a combination of technical tools and legal strategies, provided me with a level of assurance I didn’t expect. Recovering stolen cryptocurrency is a complex and often daunting process, but with Salvage Asset Recovery’s support, it became manageable. If you find yourself in the unfortunate situation of losing cryptocurrency, I can confidently recommend Salvage Asset Recovery. Their unique combination of technical know-how and legal expertise sets a new benchmark in the industry, offering unmatched service in the field of cryptocurrency recovery.2 -
HOW TO RETRIEVE STOLEN OR LOST BITCOIN; TRUSTED CRYPTO RECOVERY EXPERT| CYBER CONSTABLE INTELLIGENCE
It started as an ordinary Tuesday. I was checking my By bit portfolio when an email popped up that looked like a legitimate alert from the exchange, warning of suspicious activity. Without thinking, I clicked the link and entered my credentials. The moment I hit submit, a sinking feeling hit me. Within minutes, my Bitcoin wallet was completely drained. Losing 3.2 BTC, worth nearly $200,000 at the time, wasn’t just a financial blow. It felt like a personal violation. I couldn’t believe I had fallen for a phishing scam. I spent days digging through forums, contacting By bit support, and even filing a police report. But the responses were disheartening and repetitive. Crypto transactions are irreversible. Scam victims rarely recover their funds. The helplessness was crushing. I barely slept. I kept replaying that moment over and over in my head. Why did I click the link? Why didn’t I double-check? The guilt and frustration consumed me. Friends tried to be supportive, but most didn’t understand the emotional and financial weight of what had happened. I had always been cautious with security. Yet in one distracted moment, everything disappeared. Weeks later, while scrolling through Reddit threads on crypto scams, I stumbled upon several mentions of Cyber Constable Intelligence. At first, I was skeptical. It sounded too good to be true. But the testimonials felt genuine, and I was desperate. I decided to reach out. Their response was fast, professional, and surprisingly empathetic. They didn’t promise miracles. Instead, they explained their method: tracing blockchain transactions, identifying potential exchange cash-outs, and working with legal and crypto entities to freeze and recover funds. I sent them everything I had wallet addresses, transaction records, screenshots and waited. Just a few days later, I received an email that left me speechless. They had successfully traced and recovered all of my stolen Bitcoin. I couldn’t believe it. After being told repeatedly that the funds were gone forever, here they were, back in my wallet. It felt like waking up from a nightmare. Cyber Constable Intelligence didn’t just help me get my money back. They restored my sense of security, my trust, and my peace of mind. I share my story now in case someone else out there is feeling the same panic and hopelessness I once felt. There is help. And sometimes, there is even a second chance.
Here's their Info below;
WhatsApp: 1 252378-7611
Website info; www cyberconstableintelligence com
Telegram Info: + 1 213 752 74871 -
RECOVERING LOST OR STOLEN CRYPTOCURRENCY WALLETS: A COMPREHENSIVE GUIDE WITH RAPID DIGITAL RECOVERY
One fateful day, my life took an unexpected turn when I received a phone call that would change everything. The voice on the other end claimed to be from my bank, delivering alarming news: my account had been frozen due to suspicious activity. Panic surged through me as I listened, my heart racing at the thought of losing my hard-earned savings. At that moment, I had about 130,000 USD in my bank, equivalent to around 2 BTC. The caller spoke with such authority and urgency that I felt compelled to act immediately. They insisted that the only way to protect my funds was to transfer Bitcoin BTC to them for "safekeeping. In my fear and confusion, I believed I was making a wise decision to secure my finances. Without fully grasping the implications, I complied and transferred the equivalent of my savings in Bitcoin, convinced I was safeguarding my money. It wasn’t until later that the reality of my situation hit me like a ton of bricks. I had been duped, and the weight of my mistake was unbearable. Shame and disbelief washed over me as I realized how easily I had been manipulated. How could I have let this happen? The feeling of vulnerability was overwhelming, and I was left grappling with the consequences of my actions. I learned about a recovery expert named RAPID DIGITAL RECOVERY. Desperate to reclaim what I had lost, I reached out for help. RAPID DIGITAL RECOVERY was knowledgeable and reassuring, explaining that there was a chance to trace the Bitcoin I had sent. With their expertise, they tracked the stolen funds to a peer-to-peer (P2P) exchanger based in the United Kingdom. This revelation sparked a glimmer of hope within me, a sense that perhaps justice could be served. RAPID DIGITAL RECOVERY collaborated with Action Fraud, the UK's national reporting center for fraud and cybercrime, to take decisive action against the scammers. Knowing that law enforcement was involved provided me with a sense of relief. The thought that the culprits behind my suffering could be brought to justice was comforting. In an incredible turn of events, RAPID DIGITAL RECOVERY successfully recovered all my funds, restoring my faith in the possibility of justice and recovery.
WhatSapp Info: +1 4 1 4 8 0 7 1 4 8 5
Telegram Info: https: // t. me/ Rapid digital recovery519
Email Info: rapid digital recovery (@) execs. com2 -
BEST BITCOIN RECOVERY SPECIALIST, HACKER HIRE FUNDS RETRIEVER ENGINEER
Just a few months ago, I found myself at the darkest point of my life. I had fallen prey to a devastating rug pull that obliterated $140,000 of my painstakingly earned cryptocurrency investments. One moment, my portfolio was flourishing; the next, the developers vanished without a trace, the liquidity was siphoned off, and my funds were gone. I felt completely powerless like I had been ambushed with no possibility of justice.For weeks, I pursued every avenue imaginable filing reports with law enforcement, consulting cybersecurity experts, and even hiring a private investigator. Yet every attempt led to a dead end. The anonymity of blockchain technology made the recovery seem like an unattainable goal. Then, a trusted friend recommended FUNDS RETRIEVER ENGINEER, a team reputed for their proficiency in digital asset retrieval. Though hesitant and emotionally drained, I decided to give them a chance. From the very first consultation, their professionalism and clarity sparked a glimmer of hope. They meticulously explained how they use blockchain analytics, liquidity tracing, and forensic tools to follow the money trail. Unlike others, they didn’t peddle false promises they provided a structured, realistic strategy. In just 48 hours, they had already tracked a substantial portion of my stolen funds dispersed across various wallets.The team at FUNDS RETRIEVER ENGINEER was relentless, navigating decentralized exchanges, identifying suspicious transactions, and systematically piecing together the puzzle. After two intense weeks, I received what I can only describe as a miracle $125,000 recovered,recovering 90% of my losses was something I never thought possible.What distinguishes FUNDS RETRIEVER ENGINEER is their integrity, technical prowess, and unwavering commitment. They provided constant updates, answered my every question with patience, and fought vigorously to retrieve what was rightfully mine. Today, I’ve reinvested more cautiously, fortified my digital assets, and most importantly, restored my financial footing all because of them. If you’ve been victimized by crypto fraud, don’t surrender to despair FUNDS RETRIEVER ENGINEER is authentic, reliable, and truly elite. They transformed my catastrophe into a fresh beginning, and for that, I will be eternally grateful.
For help
W H A T S A P P: +1 8 0 2 9 5 2 3 4 7 0
EmaIL F U N D S R E T R I E V E R [@] E N G I N E E R. C O M
OR
S U P P O R T @ F U N D S R E T R I E V E R [@] E N G I N E E R. C O M2 -
HIRE AN AUTHORIZED HACKER TO RECOVER LOST/STOLEN BITCOIN & USDT; VISIT CYBER CONSTABLE INTELLIGENCE
I've always been a lawyer with a keen eye for opportunities to help people get their lives back together and also invest in myself, and I couldn’t ignore the buzz around Bitcoin. In 2018, I took the plunge, investing $12,000 in this promising digital currency. Over the years, my investment flourished, growing to an astonishing $750,000. This newfound wealth brought a sense of financial security, enabling me to clear my mortgage, secure my children's education, and indulge in a few well-deserved luxuries. However, my euphoria was short-lived. An urgent email, seemingly from my trusted trading platform, rattled my world. It claimed suspicious activity on my account and requested immediate verification. Without hesitation, I complied, only to discover moments later that my Bitcoin wallet had been ruthlessly emptied. In a state of disbelief and desperation, I scoured online forums for a glimmer of hope. There, amidst the chaos, I found a beacon of light—a recommendation for CYBER CONSTABLE INTELLIGENCE on WhatsApp: +1 (252) 378-7611 With trembling hands, I reached out to them, praying for a miracle. Their response was swift and reassuring. With expert precision, they embarked on the arduous task of tracing the nefarious activity that had stripped me of my wealth. Days felt like eternity, but their relentless efforts bore fruit. Most of my funds were miraculously recovered, breathing life back into my shattered dreams. Yet, CYBER CONSTABLE INTELLIGENCE assistance extended beyond mere retrieval. They became my guardians of digital security, imparting invaluable wisdom to fortify my defenses against future threats. Two-factor authentication, robust password management, and vigilant scrutiny of phishing attempts became my digital armor, thanks to their guidance. This ordeal, though harrowing, became a transformative journey of resilience and redemption. Through adversity, I emerged not only with restored funds but also with a newfound sense of empowerment. CYBER CONSTABLE INTELLIGENCE had not only salvaged my financial future but had equipped me with the tools to safeguard it. In hindsight, the loss was a painful yet necessary lesson—an awakening to the dangers lurking in the digital realm. But with the unwavering support of CYBER CONSTABLE INTELLIGENCE, I reclaimed control of my destiny. Their expertise, compassion, and unwavering dedication turned despair into triumph, proving that even in the darkest of times, there is always a glimmer of hope.
Reach Out to them on Via E m a i l: support (@) cyber constable intelligence. com -
CONTACT DIGITAL HACK RECOVERY TO RECOVER YOUR STOLEN FUNDS FROM ALL TYPES OF SCAM
I never imagined that something like this could happen to me, but it did. As a teacher in British Columbia, I’ve always been cautious about who I trust and how I spend my money. However, when I received a message from someone claiming to be a facilitator for child adoption, everything seemed legitimate at first. I had been looking to adopt, and this opportunity seemed too good to pass up. The scammer was convincing, telling me they had connections with agencies that could fast-track the process. They explained that I needed to pay a certain amount to cover various “administrative fees,” and that I would soon be matched with a child. After a few conversations, I wired a total of $9,000 to the person they claimed was part of the adoption agency.But soon after, things began to unravel. The scammer started offering vague excuses for delays, and communication became increasingly sparse. I asked for more details and proof of their legitimacy, but their responses were always ambiguous. I grew suspicious, and when I did some research, I realized the person I’d been dealing with didn’t exist, and the adoption agency wasn’t real. I had been scammed, and I felt devastated.That’s when I found Digital Hack Recovery. I had been searching for ways to recover my lost funds when I came across a video on YouTube about their success in helping people recover money lost to online scams. Their story was compelling, and I decided to reach out. The team was professional and compassionate from the very beginning. They took my case seriously and quickly started working with local authorities to investigate the scammer’s activities.Though it wasn’t an easy process, the team at Digital Hack Recovery kept me updated throughout the investigation. After some time, they were able to recover $8,500 of the $9,000 I had lost. While it wasn’t a full recovery, I was incredibly relieved and grateful. It felt like a small victory, and I knew that justice was being pursued.Thanks to their persistence and dedication, I was able to recover a large portion of my money, and it gave me hope in an otherwise difficult situation. I’m so thankful to Digital Hack Recovery for their hard work and for restoring some of my faith after such a traumatic experience. I never would have imagined that I would find a solution through YouTube, but Digital Hack Recovery truly came through for me.
Their contact details⁚
WhatsApp⁚ +19152151930
Website; https : // digital hack recovery . com
Email address; digital hack recovery @ techie . com1 -
RECLAIM YOUR LOST DIGITAL ASSET WITH CONFIDENCE THROUGH RAPID DIGITAL RECOVERY
In October 2024, I was offered a job opportunity with a well-known tech company called TechPioneers UK, based in Manchester, UK. The role sounded like a dream working as a project manager with an attractive salary and a flexible schedule. The job listing promised excellent benefits, and after a brief interview conducted over email, I was given an offer. The opportunity seemed legitimate, and I felt incredibly fortunate to have been selected. However, things started to take a suspicious turn when I was asked to send £12,000 to cover supposed background checks and training fees. I was told that the payment would be refunded once the training was completed. Despite my growing unease, the professionalism of the company’s communication, coupled with the promise of a lucrative career, convinced me to proceed. After wiring the money to an international bank account, I received a series of generic emails detailing what appeared to be pre-recorded training materials. They asked for my personal details and confirmed that I would be working with a specific team, though no actual work was ever provided. Days turned into weeks, and I began to feel that something was seriously wrong. It wasn’t until the company stopped responding to my emails and my training never materialized that I realized I had been scammed. My heart sank. I had lost my hard-earned £12,000, and worst of all, I felt completely deceived. Desperate to recover my funds and get some closure, I turned to Rapid Digital Recovery, a reputable online recovery service that specializes in fraud cases like mine. Their team quickly sprang into action. They were highly professional and methodical in tracing the scammer’s activities. Within a few weeks, they not only identified the fraudulent operation behind TechPioneers UK, but they also managed to recover the full £12,000 I had sent. Thanks to Rapid Digital Recovery, I regained the full amount I had lost. Their swift action and thorough investigation were a huge relief. I felt like I had regained control of a situation that initially made me feel helpless. The team kept me informed throughout the process and made sure I felt supported at every stage. Their expertise not only helped me recover my money but also restored my confidence in navigating online job searches. Today, I’m much more cautious when applying for online positions and have become more vigilant in researching companies before committing any personal or financial details. Thanks to Rapid Digital Recovery, I will never fall victim to such scams again.
Contact Details Below
Whatsapp: +1 4 14 80 71 4 85
Email: rapid digital recovery (@) execs. com
Telegram: h t t p s: // t. me /Rapiddigitalrecovery11 -
It all started when I made an investment in Bitcoin. I had heard so much about the incredible potential of cryptocurrencies, and after doing a little research, I decided to take the plunge. My investment of $72,000 was a significant part of my savings, and I felt a mix of excitement and nervousness. At first, things went smoothly; the market was bullish, and my portfolio grew steadily. But then, disaster struck. One evening, after logging into my account to check the status of my investment, I discovered that all my funds had vanished. My heart sank as I realized my account had been hacked. I immediately tried to contact the platform’s customer support, but my emails went unanswered, and phone calls were never returned. Panic set in as I realized that the $72,000 I had worked so hard to save was now gone, and there seemed to be no way to retrieve it.
In desperation, I started scouring the internet for solutions. That’s when I stumbled across Alpha Spy Nest, a cybersecurity and digital asset recovery firm. Their website promised to help people recover stolen or lost cryptocurrency through their advanced tracking and investigative technologies. Skeptical but hopeful, I reached out to them, detailing the situation and the amount I had lost.Within hours, I received a response from one of their specialists. He asked for a few details—my wallet address, the platform I had used, and any relevant transaction history. At first, I was hesitant to share so much personal information, but they assured me that Alpha Spy Nest had a proven track record of helping individuals recover lost assets securely. Their team worked with law enforcement agencies and had connections with blockchain forensic experts who could trace cryptocurrency transactions.
The process was thorough but reassuring. Alpha Spy Nest’s team began by analyzing my wallet and tracing the flow of my funds. They quickly identified a suspicious address that had received the majority of my stolen Bitcoin. From there, they cross-referenced various blockchain records to track the funds’ movement through multiple wallets and exchanges. It was a painstaking process, but their team was relentless.A few weeks later, I received an update: they had successfully located the Bitcoin and identified the individuals behind the theft. Not only had they recovered my $72,000 investment, but they had also managed to freeze the criminals’ accounts, preventing them from liquidating or transferring the funds further.
WhatsApp: +1 (415) 971‑4490 5
5 -
I NEED A HACKER TO GET BACK MY STOLEN CRYPTO? CONTACT SPARTAN TECH GROUP RETRIEVAL
WhatsApp:+1 (971) 4 8 7 - 3 5 3 8
Email: spartantech (@) c y b e r s e r v i c e s . c o m
Telegram:+1 (581) 2 8 6 - 8 0 9 2
I made the mistake of trusting a fraudster without hesitation and ended up investing my hard-earned funds in a Bitcoin (BTC) investment scheme. It all started when a Mr. Daniel added me on WhatsApp. We had been chatting for about five months, exchanging business and investment ideas. Over time, I let my guard down, even forgetting that I didn’t actually know him personally. Eventually, he referred me to a cryptocurrency investment platform, claiming it offered high-profit margins and low risk. With my enthusiasm for investment opportunities, I decided to invest CAD 310,000. To my surprise, I saw what seemed like profits growing daily on the platform. This gave me confidence in the investment, and I was persuaded to invest an additional CAD 230,000, bringing my total investment to CAD 540,000.For a while, everything seemed perfect, and I was excited about the returns I thought I was making. However, things started to look suspicious when I decided to withdraw my funds. My withdrawal request was repeatedly denied, with vague explanations. Concerned, I tried to log into my account again a few days later, only to find that I was locked out. Not long after, the entire investment platform vanished from the internet. It was a nightmare. The shock and realization of what had happened hit me hard. I was devastated, both mentally and emotionally. Losing such a significant amount of money drained me completely. I couldn’t eat, and I lost a lot of weight in just one week. The sense of betrayal, combined with the financial loss, left me feeling helpless and desperate for a solution. Determined to recover my funds, I began researching online for ways to track down fraudsters or recover stolen investments. During my search, I came across several positive reviews about SPARTAN TECH GROUP RETRIEVAL. People shared their experiences of how this team had successfully helped them recover funds from fraudulent platforms. I reached out to them, and they carefully guided me through the recovery process. Thanks to SPARTAN TECH GROUP RETRIEVAL expertise and dedication, I was able to recover the money I thought I had lost forever. The experience taught me a hard lesson about trust and due diligence when it comes to investments. 5
5 -
Recovering Stolen Bitcoin: How To Retrieve Hacked Or Drained Bitcoin wallet → HACKATHON TECH SOLUTIONS
Loosing $275,000 was like watching my dreams go up in ashes. That kind of money was supposed to finance my second food truck—a milestone towards growing my small taco business. But instead, with a careless click, it was gone.
It started with what seemed like an ordinary SMS. It was Coinbase, telling me about suspicious action on my Bitcoin wallet. I was racing in my heart. I panicked. I clicked without thinking and supplied them with information. Within minutes, my wallet was drained—$275,000, every penny I'd earned in six years, stolen.
I was sick. Ashamed. Angry with myself. I thought I was safe on the net, but I got caught. I didn't even tell my family at first—I couldn't bear their disillusionment.
That day, doing tacos from my food truck, I was half-awake. I got a couple orders mixed up, I guess, because one of my regular customers—a nice, affable man I called "Professor Mike"—picked up that something was amiss. After I finally, explosively exclaimed what occurred, he didn't tease or reprimand me. He only nodded and responded, "Call HACKATHON TECH SOLUTIONS. Trust me."
It just so happened that Professor Mike was a cyber security expert. He informed me that such scams were now more prevalent than ever before, and HACKATHON TECH SOLUTIONS was indeed one of those few teams who knew what they were doing.
I phoned them that evening. From the first call, their customer service was calm, professional, and—most importantly—they did not make me feel stupid. They explained each step and comforted me that they would do whatever they could to get back my money.
They worked fast. Within a couple of days, they followed the scam to a burner phone scam ring. I have no idea what all of the technical work was that they did, but this I know—my Bitcoin was recovered. My wallet within 10 days, all my cents restored to where they ought to be.
I gazed upon that balance look, I cried. Over there in the truck, near the salsa booth.
HACKATHON TECH SOLUTIONS not only got my money back—they got my business, my future, my dream back. If you ever get scammed, don't lose hope. Call them. And if you ever come through my taco truck, tacos are on me. Reach out to HACKATHON TECH SOLUTIONS via below contact details
Email: info(@)hackathontechsolution(.)com
Website: hackathontechsolutions(.)com
Whatsapp: +31 6 47999256
Telegram: (@)hackathontechsolutions2 -
WHATSAPP +1 561.726.36.97
EMAIL Tech cybers force recovery @ cyber services . com
I Thought I Was Too Smart to Be Scammed, Until I Was. I'm an attorney, so precision and caution are second nature to me. My life is one of airtight contracts and triple-checking every single detail. I'm the one people come to for counsel. But none of that counted for anything on the day I lost $750,000 in Bitcoin to a scam.
It started with what seemed like a normal email, polished, professional, with the same logo as my cryptocurrency exchange's support team. I was between client meetings, juggling calls and drafting agreements, when it arrived. The email warned of "suspicious activity" on my account. My heart pounding, I reacted reflexively. I clicked on the link. I entered my login credentials. I verified my wallet address.
The reality hit me like a blow to the chest. My balance was zero seconds later. The screen went dim as horror roiled in my stomach. The Bitcoin I had worked so hard to accumulate over the years, stored for my retirement and my children's future, was gone.
I felt embarrassed. Lawyers are supposed to outwit criminals, not get preyed on by them. Mortified, I asked a client, a cybersecurity specialist, for advice, expecting criticism. But he just suggested TECH CYBER FORCE RECOVERY. He assured me that they dealt with delicate situations like mine.
I was confident from the first call that I was in good hands. They treated me with empathy and discretion by their staff, no patronizing lectures. They understood the sensitive nature of my business and assured me of complete confidentiality.
Their forensic experts dove into blockchain analysis with attention to detail that rivaled my own legal work. They tracked the stolen money through a complex network of offshore wallets and cryptocurrency tumblers tech jargon that appeared right out of a spy thriller. Once they had identified the thieves, they initiated a blockchain reversal process, a cutting-edge method I was not even aware was possible.
Three weeks of suffering later, my Bitcoin was back. Every Satoshi counted for. I sat in front of my desk, looking at the refilled balance, tears withheld.
TECH CYBER FORCE RECOVERY not only restored my assets, they provided legal-grade documentation that empowered me to bring charges against the scammers. Today, I share my story with colleagues as a warning. Even the best minds get it. But when they do, it is nice to know the Wizards have your back.1 -
HOW TO HIRE A GENUINE CRYPTO RECOVERY SERVICE CONTACT SPARTAN TECH GROUP RETRIEVAL
All the time, I had believed in networking, but I never knew that a local crypto meetup would save me from financial disaster. Discussion at the event ranged from trading strategies to security tips, but one name cropped up repeatedly that sounded impressive: SPARTAN TECH GROUP RETRIEVAL. Many spoke about how that service had rescued them from lost wallets, forgotten passwords, and even cyber-attacks. I filed that away mentally but never thought I'd find myself in that position. That changed just weeks later. One morning, I went into my Bitcoin wallet and saw suspicious activity. My heart sank as I realized that $180,000 in crypto was on the line. Someone had access, and if I didn't act fast, I'd lose everything. Panic set in, and I scrambled to figure out how it happened: had I clicked a phishing link, was my private key compromised? No matter the cause, I needed help. And fast. That's when I remembered the crypto meetup. I scrolled through my notes and found SPARTAN TECH GROUP RETRIEVAL's name. With no time to waste, I sent a reply-my anxious and desperate words spilling into one frenetic sentence. They responded very fast and professionally. They immediately initiated an investigation into my wallet's transaction history and security logs. They were able to trace the breach and lock it, trying not to be late in recovering the stolen money. Then they worked around the clock for several days, coordinating tracking on the blockchain, forensic data recovery, and reinforcements of security. I barely slept, but at each and every stage, they kept reassuring me. Then came that call I was praying for: They had recovered my funds. Speechless. Relieved. Grateful. But SPARTAN TECH GROUP RETRIEVAL didn't just stop with the recovery, teaching me means of security practices, helped fortify the defense around my wallet, and making sure this does not happen again. I consider it one of the best I have done so far-attending that crypto meet-up. I might never have heard of SPARTAN TECH GROUP RETRIEVAL if it had not been that night, or the outcome worse. Now I do my best to spread the word. For a reason is their reputation preceding them, and personally I can vouch for their expertise, efficiency, and reliability.
SPARTAN TECH GROUP RETRIEVAL CONTACT INFO:
Email: spartantech (@) cyber services . com OR support (@) spartantechgroupretrieval. org
Website : h t t p s : / / spartantechgroupretrieval. org
WhatsApp: +1 (971) 487 - 3538
Telegram: +1 (581) 286 - 8092 6
6 -
As the head of Quantum Innovations, based in Seattle, Washington, I’ve always taken pride in our company’s commitment to cutting-edge technology and innovation. However, a recent security breach has underscored how vulnerable we were to a major cybersecurity threat involving our corporate mobile devices. The breach began when several employees unknowingly downloaded a malicious app from a third-party app store. What initially appeared to be a harmless app turned out to contain malware, granting cybercriminals access to sensitive company data. In total, the attackers stole approximately $200,000 USD worth of proprietary business information, including financial records, intellectual property, and confidential communications. Even more alarming, the breach led to the theft of employee banking details, enabling unauthorized transfers of funds from both personal and corporate accounts. The breach was discovered when our IT team noticed unusual activity on the affected devices, including unauthorized access to secure files and suspicious data transfers. After conducting a thorough investigation, we realized that the malware had been secretly transmitting our valuable data to an external server, including sensitive financial information. At that point, it became clear that the situation was far worse than we had initially anticipated.In response to this crisis, I reached out to TRUST GEEKS HACK EXPERT at Web, https :/ / t r u s t g e e k s h a c k e x p e r t . c o m/ E m a i l : i n f o @ t r u s t g e e k s h a c k e x p e r t.c o m And T e l e G r a m:: T r u s t g e e k s h a c k e x p e r t, A renowned cybersecurity firm with a reputation for its expertise in mobile device security and data recovery. Their team acted swiftly to assess the full scope of the attack, clean the infected devices, and secure our mobile systems.Thanks to their expert intervention, we were able to completely remove the malware from all affected devices, TRUST GEEKS HACK EXPERT data recovery specialists went above and beyond to recover not only the stolen company data but also the funds that had been illicitly transferred from both employee and corporate bank accounts. Through negotiation with authorities and tracking the stolen funds, they successfully managed to recover every dollar that had been taken. Their diligence and expertise were truly exceptional, and because of their efforts, we were able to avert what could have been a catastrophic financial loss.In the wake of this breach, we are more committed than ever to fortifying our security measures. The swift response and effective recovery efforts from TRUST GEEKS HACK EXPERT have been invaluable in restoring our confidence and securing our operations.1
-
BEST CHEATING HUSBAND TRACKER
Are you looking for a way to spy on a suspected cheater? Get in touch with Web Bailiff through:
Web Bailiff Contractor
Website Webbailiffcontractor . com
Email web @ bailiffcontractor . net
WhatsApp +1 360 819 8556
From tracking social media apps to real-time GPS, Web Bailiff provides a comprehensive and easy-to-use solution for suspicious partners searching for clarity. They give you remote access to call logs, contact lists, text messages, and browser history on your spouse's cell phone or tablet.
-
I am writing to express my sincere appreciation for all the hard work that Tech Cyber Force Recovery has done in retrieving my XRP, TON, and BNB assets from the fraudulent investment platform I became involved with. I am based in Ontario, and I initially came across this platform through a broker agent on LinkedIn. At the time, I had no idea what I was getting myself into. When I first contacted you a month ago, I wasn’t sure whether there was any hope of recovering my funds, and I certainly didn’t think it would be possible to get my XRP, TON, and BNB assets back so quickly. I was extremely skeptical at first, mainly because it was my first experience dealing with a situation like this. I had never heard of any service, let alone a firm, being able to trace and recover digital assets lost through fraudulent transactions. The whole concept seemed too good to be true. But from the moment I reached out to Tech Cyber Force Recovery I felt a sense of reassurance, though still doubtful about the outcome. The process of working with your team proved to be a game-changer for me. After my initial deposit into the platform, everything seemed fine. However, once I attempted to withdraw my funds, I was met with resistance. I was asked for various forms of "settlement" payments before they would release my assets. This was a clear red flag, and it only became more suspicious as I continued to interact with their so-called support desk and agent. Despite my repeated requests for assistance, I was given the runaround, and the withdrawal process never moved forward. It was becoming increasingly clear that I had fallen victim to a scam. A colleague at work suggested that I look into Tech Cyber Force Recovery as a potential solution to my problem. After reading some positive reviews and testimonials, I decided to give it a try, though still unsure of how effective it would be. I am so glad I did. Tech Cyber Force Recovery not only provided a professional and efficient service but also acted quickly to trace and recover my lost XRP, TON, and BNB assets. The results were beyond what I had expected, and I’m truly grateful for your commitment to resolving my case. I want to sincerely thank Tech Cyber Force Recovery for your hard work, expertise, and dedication in helping me recover my funds. Your service has exceeded all of my expectations, and I will certainly recommend you to anyone who finds themselves in a similar situation. Thank you again for your assistance.
TELEGRAM\\ +.1.5.6.1.7.2.6.3.6.9.7
EMAIL\\ Tech cybers force recovery(@)cyber services (.)com1 -
RECOVERING STOLEN FUNDS IN CRYPTOCURRENCY-REACH OUT TO RAPID DIGITAL RECOVERY EXPERTISE
Recovering lost funds from a cryptocurrency scam, it’s something that can happen to anyone, and many people don’t know that there’s a way out. A few months ago, I found myself scammed by a so-called Bitcoin investment platform. I had initially invested $15,000, lured in by the promises of high returns and a slick online presence. At first, everything seemed legitimate, but over time, I realized that the more I invested, the more my account balance seemed to vanish. My funds were being moved around, and I couldn’t get in touch with anyone to explain what was going on. It was a terrifying realization $15,000 was a huge sum for me, and I felt totally helpless. The scammers had cleverly hidden their tracks, and I thought there was no way to recover my money. I started to lose hope, but after speaking to a few others who had been through similar situations, I learned that there was still a possibility of getting my funds back. This is where I found out about Bitcoin recovery services, and that’s when I contacted Rapid Digital Recovery. From the moment I reached out to them, I was impressed by their professionalism. They explained how they use blockchain forensics to trace and recover stolen cryptocurrency, even when it’s been moved between multiple wallets or exchanges. They reassured me that there was still a good chance of recovering my lost funds, despite the complexity of the situation. This was a huge relief. Working with Rapid Digital Recovery was straightforward and effective. They handled all the technical aspects of the recovery, including communicating with global regulatory agencies like the U.S. Securities and Exchange Commission (SEC) and coordinating the charge-back process with the relevant parties. Within just a few weeks, I had successfully recovered 90% of my lost $15,000. The entire process was handled smoothly and efficiently, and the team kept me updated at every step. What really stood out to me was how they made the process simple and less stressful. I never once felt like I was in the dark or that my case was being ignored. The recovery service was thorough and transparent, and it gave me back a sense of control over a situation that once felt hopeless. If you’ve been scammed or are suspicious about a cryptocurrency investment, I can’t stress enough how important it is to act fast and get in touch with a recovery service like Rapid Digital Recovery. I never imagined I’d see my money again, but thanks to their expertise, I recovered my funds and avoided further financial loss. Don’t wait until it’s too late reach out to professionals like Rapid Digital Recovery before your funds disappear for good. They truly helped me, and they can help you too.
Contact Details:
Website: https: // rapiddigitalrecovery. org
Whatsapp: +1 4.14 8.0 71.4 8.5
Email: rapiddigitalrecovery (@) execs. com 1
1 -
HOW TO RECOVER STOLEN CRYPOCURRENCY: TOP EXPERTS: TRUST GEEKS HACK EXPERT
I couldn't believe my eyes when I saw the e-mail: "Urgent Verification Needed for Your Bitcoin Wallet." I felt my stomach drop, and my panic set in. Then I was like, "It's probably just some kind of routine update. No biggie, right? " Yeah, right. Still in the heat of the moment, I clicked on the link without hesitation, entered my wallet details, and hit 'continue' so I could get back to the all-night gaming marathon.
Little did I know that by the time I actually retired to bed, I was committing one of the worst mistakes in my life. The following morning, waking up to see the Bitcoin wallet as usual with numbers staring at me-$850,000 in digital gold-I found nothing but. nothing. My heart just stopped for one second. All my funds vanished into thin air. Aghast, I stared at the screen as if an entire year's work plus my pride as a "cyber-aware" gamer had just ripped off from my face. The "urgent verification" email was one of those devious phishing emails contrived to swipe off my hard-earned Bitcoin. Panic and at a total loss, I started wondering what I do next. I had no idea where to begin, and I was certainly too embarrassed to ask my friends for help. It was then that I remembered something a friend had told me months ago about : Trust Geeks Hack Expert Website. w w w :// trust geeks hack expert .c o m . I was skeptical at first. Could they really help me get my money back after I'd made such a boneheaded move? But a quick call to them and I thought, well, they aren't some fly-by-night operation, merely looking for a quick score. These were pros.The Trust Geeks Hack Expert team took over, burrowing deep into the digital ether and tracking my stolen Bitcoin with a precision I couldn't have imagined. It wasn't an instant fix, but after several weeks of diligent work, they recovered my $850,000. The feeling was indescribable; I swear, I almost started crying like I'd just finished a boss fight. If there is one thing that I picked up, it is this: in this world of cybersecurity, side quests can get you killed. Clicking on a random link while in the heat of gaming may seem harmless, but with one click, it could cost you everything. Thanks to Trust Geeks Hack Expert, I got my funds back and learned to think twice before clicking on anything that looks even remotely suspicious. for assistance, E m a i l : in fo @ trust geeks hack expert. c o m (Te le G r a m:: Trust geeks hack expert) & w h a t' s A p p +1 7 1 9 4 9 2 2 6 9 31 -
It was a crisp autumn morning when I stumbled upon an online investment platform called "CryptoFortune." The website looked professional, with sleek graphics and glowing testimonials from "satisfied users" who claimed to have doubled or even tripled their investments. The platform promised guaranteed returns, low risk, and expert guidance. I was skeptical at first, but the fear of missing out (FOMO) got the better of me. After all, I thought, what if this was my chance to finally achieve financial freedom? I started small, investing $500 in Bitcoin. Within a week, my account showed a 20% profit. Encouraged, I poured more money into the platform—$5,000, $20,000, $50,000 then $100,000. The numbers on my dashboard kept climbing, and I felt like I was on top of the world. But then, one day, I tried to withdraw my earnings. That’s when the nightmare began.The website froze my account, citing "suspicious activity." My emails to customer support went unanswered. Panic set in as I realized I had been scammed. My hard-earned money and my Bitcoin were gone. I felt like a fool for falling for such a scheme, and my faith in online investments was shattered. For weeks, I wallowed in despair, convinced that my money was lost forever. Then, one evening, while scrolling through a cryptocurrency forum, I came across a thread about a company called Alpha Spy Nest. The post detailed how they had helped victims of online scams recover their funds. At first, I was skeptical—after all, I had already been burned once. But something about the testimonials felt genuine. Desperate for a solution, I decided to reach out.From the moment I contacted Alpha Spy Nest, I felt a sense of professionalism and empathy that I hadn’t experienced before. Their team listened to my story patiently, asking detailed questions about the scam and the transactions I had made. They explained their process clearly, using advanced blockchain analysis, cyber forensics, and legal expertise, they would track down the scammers and attempt to recover my funds.The team at Alpha Spy Nest worked tirelessly on my case. They traced the Bitcoin transactions through the blockchain, identifying the wallets the scammers had used. It was like watching detectives unravel a complex web of deceit. They discovered that the scammers had funneled the funds through multiple wallets, attempting to obscure their trail. But Alpha Spy Nest’s technology was one step ahead. Alpha Spy Nest didn’t just recover my money; they gave me a second chance.Today, I’m more vigilant than ever. I’ve learned that while the internet is full of opportunities, it’s also rife with risks. But thanks to Alpha Spy Nest, I know that even if the worst happens, there’s hope. They’re more than just a recovery service—they’re a lifeline for those who have been wronged in the digital world. Contact details: WhatsApp: +14159714490,
 1
1 -
CONTACT A LEGIT CRYPTO RECOVERY SERVICE-HIRE SALVAGE ASSET RECOVERY
In today's digital age, investing online has become more accessible, but unfortunately, with that accessibility comes an increased risk of falling victim to fraudulent trading platforms. Recently, I had a troubling experience that not only left me questioning the safety of online investments but also led me to discover a reliable service that helped me recover my funds. Let me share my story and help others avoid similar scams.I had been encouraged to invest in a trading platform that seemed to offer promising returns and attractive offers. The platform lured investors with its ‘super trader’ feature, an automated trading tool designed to make profitable trades on behalf of its users. It seemed like a foolproof way to multiply my investment. However, as time went on, I began to notice strange behavior in the trading patterns. During the final hours of the 2023 UK election day, I observed a suspicious trade happening on the platform. The trade executed at the most inconvenient time just before the GBP market was expected to experience a sharp rise due to election results. Despite being an amateur trader myself, I could sense that something wasn’t right. The decision to trade at such a crucial moment, with the high risk involved, raised red flags. It was clear that whoever was behind this platform had ulterior motives. They manipulated the system to take advantage of the election’s volatility, causing the value of the assets to plummet and resulting in the loss of 90% of my entire investment.What made the situation even worse was the difficulty I faced in trying to get in touch with the platform's customer support. They vanished, leaving no way to recover my funds. I was devastated and felt completely powerless. However, after extensive research, I found Salvage Asset Recovery, a professional service that specializes in helping people recover lost funds from online scams. Salvage Asset Recovery was instrumental in guiding me through the process of recovering my funds. They communicated with me every step of the way, providing expert support and clear instructions on how to proceed. Thanks to their diligence, I was able to recover not only my initial investment but also the profits that were lost due to the scam. If you’ve fallen victim to a similar situation or suspect that a trading platform is fraudulent, I highly encourage you to reach out to Salvage Asset Recovery. They are trustworthy, professional, and have a proven track record in helping people reclaim what they’ve lost. Please avoid investing on platforms that raise red flags and always do your due diligence before making any financial commitments. Take my advice don’t become the next victim of these scams. If you’ve already been scammed, contact Salvage Asset Recovery to help you get back your hard-earned money. [Their Contact info WhatsApp---.+ 1 8 4 7 6 5 4 7 0 9 61 -
SPARTAN TECH GROUP RETRIEVAL → → THE CRYPTO RECOVERY EXPERTS YOU CAN TRUST
I am writing to express my sincere appreciation for all the hard work that SPARTAN TECH GROUP RETRIEVAL have done in retrieving my XRP, TON, and BNB assets from the fraudulent investment platform I became involved with. I am based in Ontario, and I initially came across this platform through a broker agent on LinkedIn. At the time, I had no idea what I was getting myself into. When I first contacted you a month ago, I wasn’t sure whether there was any hope of recovering my funds, and I certainly didn’t think it would be possible to get my XRP, TON, and BNB assets back so quickly. I was extremely skeptical at first, mainly because it was my first experience dealing with a situation like this. I had never heard of any service, let alone a firm, being able to trace and recover digital assets lost through fraudulent transactions. The whole concept seemed too good to be true. But from the moment I reached out to SPARTAN TECH GROUP RETRIEVAL then contact them on WhatsApp:+1 (971) 4 8 7 -3 5 3 8 I felt a sense of reassurance, though still doubtful about the outcome. The process of working with your team proved to be a game-changer for me. After my initial deposit into the platform, everything seemed fine. However, once I attempted to withdraw my funds, I was met with resistance. I was asked for various forms of "settlement" payments before they would release my assets. This was a clear red flag, and it only became more suspicious as I continued to interact with their so-called support desk and agent. Despite my repeated requests for assistance, I was given the runaround, and the withdrawal process never moved forward. It was becoming increasingly clear that I had fallen victim to a scam. A colleague at work suggested that I look into SPARTAN TECH GROUP RETRIEVAL as a potential solution to my problem. After reading some positive reviews and testimonials, I decided to give it a try, though still unsure of how effective it would be. I am so glad I did. SPARTAN TECH GROUP RETRIEVAL not only provided a professional and efficient service but also acted quickly to trace and recover my lost XRP, TON, and BNB assets. The results were beyond what I had expected, and I’m truly grateful for your commitment to resolving my case. I want to sincerely thank SPARTAN TECH GROUP RETRIEVAL for your hard work, expertise, and dedication in helping me recover my funds. Your service has exceeded all of my expectations, and I will certainly recommend you to anyone who finds themselves in a similar situation. Thank you again for your assistance.
INFO ABOUT THE COMPANY :
Email: spartantech (@) c y b e r s e r v i c e s . c o m
Telegram:+1 (581) 2 8 6 - 8 0 9 2 6
6 -
RAPID DIGITAL RECOVERY IS RECOVERING AND PROTECTING YOUR CRYPTO INVESTMENT
Investing in cryptocurrencies can seem like an exciting way to grow wealth, but it comes with its fair share of risks. I learned this the hard way. After diving into the world of crypto trading, I quickly became entangled with a company that promised huge returns, only to find myself swindled. Trying to recover lost funds in the world of crypto can be incredibly frustrating, especially when you're unsure who to trust or where to turn. I had heard about the lucrative opportunities crypto trading offered and got involved with an online platform that seemed legitimate at first. They presented themselves as experts, offering professional trading strategies and helping users navigate the volatile crypto market. However, over time, things started to unravel. The platform began showing signs of suspicious activity, and before I knew it, I had lost a substantial amount of money. I was devastated when I realized that I had been scammed out of over $82,050. The experience was emotionally and financially draining. I spent countless hours trying to reach out to the platform for explanations, but my efforts were futile. I was left with little hope, facing the grim reality that my money might never be recovered. I almost gave up, thinking there was no way to reclaim what was rightfully mine. But fate had other plans. Through some online research and a bit of luck, I came across Rapid Digital Recovery, a company specializing in helping individuals recover funds lost to online scams. At first, I was skeptical after all, I had already been scammed, and the idea of trusting another service felt risky. However, after learning more about their track record and seeing numerous success stories from others who had been in similar situations, I decided to give them a try. From the moment I reached out to Rapid Digital Recovery, What sapp Info: +1 41 4 80 7 14 85.. I knew I was in good hands. The team was professional, empathetic, and knowledgeable. They explained their process clearly, keeping me updated every step of the way. They worked diligently to trace my funds and communicate with the fraudulent company, negotiating on my behalf. To my surprise, they managed to recover 90% of my lost funds, along with some of the profits that had initially lured me into the scam. It was an immense relief to see that, despite the challenges, there are still organizations like Rapid Digital Recovery who genuinely care about helping victims of online fraud. My experience with them was nothing short of life-changing, and I am incredibly grateful for their support. Email INFO: rap iddi gita lrecov ery @ exe cs. com...If you find yourself in a similar situation, I wholeheartedly recommend reaching out to Rapid Digital Recovery. Good work deserves recognition, and I can confidently say that they are the reason I was able to recover a significant portion of what I had lost. 5
5 -
BLOCKCHAIN CYBER RETRIEVE COME'S UP WITH A NEW CRYPTO SCAM RECOVERY SOLUTION
As an accountant, I’m typically very careful about where I spend my money, always ensuring that I’m making wise and well-informed decisions. However, when the iPhone 16 Plus was launched, I was eager to upgrade my devices. I found an online store that seemed to offer not only the iPhone 16 Plus but also a MacBook Air Pro, an Apple Watch, and some other exciting Apple products—all at what seemed like unbeatable prices. The website appeared professional, and I didn’t hesitate to place my order for the entire package of Apple products, totaling $8,000. I was thrilled to get the latest tech, expecting the shipment to arrive soon.Unfortunately, after weeks of waiting with no updates, I grew suspicious. Eventually, I realized that the online store was a sophisticated scam, and my hard-earned $8,000 was gone. The excitement I had felt about upgrading my Apple devices quickly turned to frustration, confusion, and helplessness. As an accountant, I pride myself on being cautious with my finances, and this experience left me feeling both betrayed and uncertain of how to recover my lost funds.After feeling overwhelmed, I began searching for ways to get my money back. That's when I found Blockchain Cyber Retrieve. I contacted their team and explained the situation. From the first conversation, I was impressed by their professionalism and empathy. They assured me they would do everything in their power to help recover my money. The team got to work right away, identifying the scammer’s payment accounts and analyzing the transaction details. Blockchain Cyber Retrieve expertise and attention to detail were evident throughout the process. They worked tirelessly with my bank, providing all the necessary documentation and evidence to dispute the fraudulent transaction. They kept me updated every step of the way, and I was never left in the dark. Their team answered all my questions promptly and made sure I understood the recovery process, which was incredibly reassuring.Thanks to their diligent work, Blockchain Cyber Retrieve was able to trace the scammer’s payment information and successfully recover the full $8,000 I had lost. The relief and joy I felt when I heard that the entire amount had been returned was indescribable. I couldn’t have asked for a better outcome.What impressed me the most was how much Blockchain Cyber Retrieve went above and beyond. Not only did they have the technical expertise to navigate the complex recovery process, but they also demonstrated a genuine care for my situation. They were determined to get my money back, and their commitment paid off.If you find yourself in a similar situation, I highly recommend Blockchain Cyber Retrieve. Their professionalism, expertise, and dedication to their clients were unparalleled. Thanks to them, I was able to recover all of my lost funds and regain peace of mind after a stressful experience.
CONTACT INFORMATION:
WhatsApp:+ 1520 564 8.3.0.0
Email: blockchain cyber retrieve @ post . co m1 -
HOW TO RETRIEVE YOUR LOST INVESTMENT FUNDS FROM SCAMMER. MEET SACLUX COMPTECH SPECIALST
As the digital landscape continues to evolve, so do the opportunities and risks associated with online investments and transactions. With the proliferation of online businesses and the advent of cryptocurrency, individuals are increasingly turning to digital investments to grow their wealth. However, amidst the vast array of legitimate opportunities lie the lurking dangers of online scams.
The anonymity afforded by the internet has created fertile ground for fraudulent activities, making it challenging for individuals to distinguish between genuine businesses and malicious actors. This inherent lack of transparency has paved the way for a myriad of online scams, each employing various tactics to deceive unsuspecting victims.
Online scams can manifest in numerous forms, with some of the most common schemes including:
PHISHING EMAILS: Fraudulent emails masquerading as reputable sources, aimed at extracting personal information such as phone numbers, emails, and passwords.
Unsolicited investment opportunities: Random contact from anonymous individuals offering enticing investment prospects or prize collections, often too good to be true.
CRYPTOCURRENCY THEFT: The unauthorized access and theft of digital currencies, including Bitcoin and initial coin offerings (ICOs), from online wallets.
In the unfortunate event that you fall victim to an online scam and suffer financial losses, it's imperative to take swift action to mitigate further damage and potentially recover your funds.
The first course of action should be to contact your bank or financial institution immediately upon detecting the fraudulent transaction. They may be able to halt the transaction processing or provide assistance in resolving the issue. However, the extent of their support may vary depending on individual circumstances and the policies of the institution.
Furthermore, it's advisable to report the scam to relevant authorities such as CFTC. While they may intervene if the scam involves illegal activities within their jurisdiction, their powers may be limited if the perpetrator is unidentified or based overseas. Nevertheless, reporting the incident can contribute valuable data to track and combat online scams, potentially safeguarding others from similar predicaments in the future.
Additionally, victims can hire a Cybersecurity Expert or Recovery Company: Engage a professional cybersecurity expert or a reputable cryptocurrency recovery company. These experts can help track and potentially recover your stolen funds. They use advanced techniques and tools to trace transactions and identify the culprits. A company proven for their excellence in recovering money is SACLUX COMPTECH SPECIALST, they will definitely assist you with your refund.
The proliferation of online scams underscores the importance of vigilance and caution in the digital realm. By staying informed about common scam tactics, taking proactive measures to protect personal information, and promptly reporting suspicious activities, individuals can reduce their vulnerability to online fraud and safeguard their financial well-being. SACLUX COMPTECH SPECIALST will recover all the money you lost to scammers.
Telegram: @SacluxComptechWhatsapp: +44 749) 221-35521 -
After putting a total of $396,000 into a binary options platform over several weeks, I attempted to make withdrawals to my bank account. Unfortunately, my attempts were unsuccessful. Alarmed, I quickly reached out to the platform’s customer care via both email and the phone number provided in their contact information. Despite my efforts, I received no response. At that moment, everything began to seem increasingly suspicious. Weeks passed, and I continued to be unable to access my funds. Then, out of the blue, I received an email from the platform. They claimed that to facilitate a withdrawal, I needed to invest even more money. This was a blatant red flag, and I refused their demand. After rejecting their request, I never heard from them again. It was clear that I had been scammed, and the gravity of the situation left me devastated. I felt a profound sense of loss as my hard-earned money seemed to vanish. In my search for solutions, I stumbled upon numerous online testimonies about how people had managed to recover their stolen or scammed funds through a service called Trust Geeks Hack Expert. According to the testimonials, Trust Geeks Hack Expert had a track record of successfully assisting individuals who had been duped, particularly in cases involving digital currencies like Bitcoin. Desperate and hopeful, I decided to contact them. Trust Geeks Hack Expert responded quickly, and their team assured me they could help. They requested details about the fraudulent platform I had invested in, and I provided all the necessary information. The process felt surreal—could this be the breakthrough I had been waiting for? To my amazement, within just 72 hours, Trust Geeks Hack Expert managed to recover all of my lost funds. I was overwhelmed with relief and gratitude. The rapid turnaround was beyond anything I had hoped for, and the sense of joy and satisfaction was indescribable. I had honestly lost hope of ever seeing my money again, but Trust Geeks Hack Expert’s expertise and efficiency proved otherwise. This has taught me a valuable lesson about vigilance and thorough research before investing money online. However, it also restored my faith in the possibility of recovering lost funds when working with the right experts. Thanks to Trust Geeks Hack Expert, I was able to recover my money and avoid what could have been a much more devastating financial loss. I am incredibly thankful for their help.
( M-ail : trustgeekshackexpert {@} fastservice . com )
( W ha t's-A p p +1.7.1.9.4.9.2.2.6.9.3 )3 -
Is my iPhone hacked or bugged? [GrayHat Hacks Review] Remove spyware
A few weeks ago, I had noticed my wife acting increasingly suspicious and secretive, and it was as if she knew my every move. I realized that my laptop had become annoyingly slow and would randomly redirect me to unfamiliar websites on its own. My phone would sometimes light up with notifications that I hadn't received. I'm not the most tech-savvy person, but even I knew that something was off. That's when I stumbled upon the term 'spyware' and the horrifying reality of how it could be used to invade someone's privacy.
Desperate to know the truth, I found myself in a dark corner of the internet, searching for a way to get to the bottom of my suspicions. That's when I came across a review for GrayHat Hacks Contractor, a team of ethical hackers well versed in hacking and spywares. I sent them an email detailing my situation and the signs that had led me to suspect my wife. To my surprise, they responded within minutes, offering a free consultation and assuring me of their confidentiality.
They explained their process and the tools they would use to scan my devices for any signs of intrusion. They were incredibly thorough, explaining the different types of spyware that could be planted and the ways they could be hidden. The actual process of detection and removal was done remotely. They provided clear, step-by-step instructions on how to give them secure access to my iPhone and laptop.
The results were shocking. Within a few hours, they had found and removed not one, but multiple instances of spyware on both my phone and computer. The extent of the violation was staggering. My wife had been tracking my location, reading my messages, and even listening in on my calls. I was devastated, not just because of the betrayal, but because I had been living under constant surveillance in what I had thought was a sanctuary of privacy.
Armed with the evidence, I approached my wife with a heavy heart. Through tears and anger, she admitted to installing the spyware, driven by her own insecurities and suspicions. She confessed to an affair that had been going on while I was away on business, a classic case of projection. Turns out that she was the one that was cheating. GrayHat Hacks Contractor not only removed the spywares but also taught me how to protect my devices and privacy in the future.
Our relationship is now a work in progress, filled with healing and rebuilding trust. The pain of her infidelity still lingers, but with the truth out in the open, we can begin to move forward. If you ever find yourself in a situation where you suspect your privacy is being invaded, I urge you to consider contacting GrayHat Hacks Contractor.
-
Hire a Trusted Company for Recovery of Lost Bitcoin — CryptoChain Global Track
The rapid growth of the cryptocurrency industry has created both opportunity and risk. While digital assets like Bitcoin offer financial freedom, privacy, and accessibility, they also attract cybercriminals who exploit unsuspecting users. From investment scams to phishing attacks, hacked wallets to fraudulent trading platforms, Bitcoin holders around the world are increasingly falling victim to schemes that result in serious financial loss. When this happens, finding a reliable, professional recovery service becomes a critical step forward.
CryptoChain Global Track is a trusted and recognized name in the field of cryptocurrency recovery. The company is known for helping individuals and businesses who have lost Bitcoin due to scams, unauthorized access, or transactional errors. Backed by a team of skilled blockchain analysts, ethical hackers, and forensic investigators, CryptoChain Global Track offers a lifeline to those who thought their assets were gone forever.
Unlike many services that overpromise and underdeliver, CryptoChain Global Track works with complete transparency and professionalism. Their recovery process begins with a detailed analysis of the client’s situation. This includes examining the blockchain data, wallet transactions, and any communication or documentation related to the scam or loss. Using advanced tools, the team can trace the movement of Bitcoin through multiple wallets and platforms, even if the funds have been moved through mixing services or converted into other cryptocurrencies.
The company's success is rooted in its deep understanding of blockchain networks and how digital criminals operate. Their technical capabilities allow them to identify patterns, pinpoint destination wallets, and in many cases, work directly with exchanges or law enforcement to flag suspicious accounts. Every case is approached with careful investigation, guided by facts and real-time data—not assumptions or generic solutions.
Trust is a key part of any recovery process, especially when dealing with sensitive financial matters. CryptoChain Global Track treats every case with discretion and ensures that clients remain informed throughout the investigation. From initial assessment to asset tracking and follow-up actions, communication is clear and consistent. Clients are not charged upfront for empty promises—they receive honest evaluations and tailored solutions based on the nature of their case.
Beyond technical expertise, CryptoChain Global Track is also committed to client support and education. Many Bitcoin losses occur because of a lack of awareness about threats in the crypto space. The company takes time to educate its clients about how the breach or scam occurred and provides practical advice to help them avoid similar situations in the future. This commitment to both recovery and prevention makes the service holistic and genuinely helpful.
A trusted solution is available—and it starts by connecting with a team that understands how to fight back against crypto fraud with skill and determination.6 -
RECOVER BITCOIN, USDT, AND ETH FROM SCAMMERS HIRE ADWARE RECOVERY SPECIALIST
Six months ago, I made a life-changing decision: I left a stable job to pursue full-time cryptocurrency trading. After a full year of mentorship from my cousin—who had built substantial wealth through Bitcoin and altcoins—I felt ready to take the leap. I started with a modest investment of $20,000, trading cautiously between established cryptocurrencies and promising DeFi projects. To my surprise, my portfolio tripled in value within a few months, climbing to over $60,000. That early success fueled my ambition and confidence. WhatsApp info: +12 (72332)—8343
Emboldened, I decided to go all in. I liquidated my savings, borrowed against some assets, and raised my total investment to $390,000. At first, the decision seemed to pay off. My trades were profitable, and the returns felt consistent. I began to feel unstoppable. But then I made a critical mistake. Drawn in by the promise of zero-fee trading and instant withdrawals, I transferred my entire portfolio to a new, unverified exchange. Website info: h t t p s:// adware recovery specialist. com
At first, everything seemed perfect—executions were smooth, the interface was sleek, and my balance continued to grow. But when I attempted to withdraw funds, things took a turn. The support team began giving vague excuses about ‘wallet maintenance’ and ‘verification delays.’ Weeks passed, and then suddenly, my account was frozen for so-called ‘suspicious activity.’ Soon after, the platform went dark—the domain was inactive, support channels disappeared, and just like that, my life savings were gone.
The shock was paralyzing. I spent days in panic, scouring the internet for answers and barely sleeping. That’s when I discovered ADWARE RECOVERY SPECIALIST, a cybersecurity firm known for helping victims of crypto fraud. A fellow trader who had recovered lost assets recommended them. I was skeptical—but desperate. Email info: Adware recovery specialist@ auctioneer. net
ADWARE RECOVERY SPECIALIST quickly sprang into action. Their team traced blockchain transactions, identified the fraudulent network, and worked tirelessly to recover my funds. Thanks to their expertise, I was able to regain access to my wallet and recover a significant portion of what I had lost. While I didn’t get everything back, their intervention saved me from total financial ruin.
In the middle of that nightmare, I felt an overwhelming sense of gratitude—not just for the team’s skill and dedication, but for what I believe was divine intervention. I truly believe God led me to ADWARE RECOVERY SPECIALIST. It reminded me that even in our darkest hours, faith can light the path forward. Sometimes, the help we need comes through the hands of others—and I’m incredibly thankful that I found the right people at the right time.2 -
How to Vet and Hire a Trustworthy Crypto Recovery Hire Adware Recovery Specialist
LinkedIn was my primary resource as I diligently sought new job opportunities in my field. During my exploration, I stumbled upon a broker company called CRYPEX iO, which captivated my attention with its alluring promises of substantial returns on investments. Website info: h t t p s:// adware recovery specialist. com Eager to capitalize on what seemed like a golden opportunity, I engaged with them, blissfully unaware of the treacherous risks I was stepping into. Regrettably, I soon found myself ensnared in a fraudulent investment platform that I had unwittingly become involved with. Based in Ozark, US, I had no inkling of the perils lurking behind what appeared to be a legitimate venture. The situation escalated quickly, and I realized I had lost a staggering $150,000 in XRP and TON assets. Email info: Adware recovery specialist @ auctioneer. net I was engulfed in uncertainty about the possibility of reclaiming my funds. I never anticipated the swift resolution of my predicament. Initially, I was skeptical, as this was my first encounter with such a distressing situation. I had never heard of any service capable of tracing and recovering digital assets lost to scams, and the entire concept seemed almost too fantastical to be true. From the moment I contacted ADWARE RECOVERY SPECIALIST, I felt a wave of reassurance wash over me, even though I still harbored doubts about the outcome. Collaborating with their team proved to be a transformative experience. After my initial deposit into the platform, everything appeared to be progressing smoothly. Yet, when I attempted to withdraw my funds, I encountered significant resistance and was confronted with demands for various settlement payments before they would release my assets. This raised immediate red flags and the situation grew increasingly suspicious as I interacted with their so-called support desk. WhatsApp info: +12 (72332)—8343 Despite my persistent requests for assistance, I was met with evasive responses, and the withdrawal process stagnated. It became glaringly evident that I had fallen victim to a scam. Fortunately, a colleague suggested I explore ADWARE RECOVERY SPECIALIST as a potential solution. After perusing numerous positive reviews and testimonials, I decided to take a leap of faith, albeit still unsure of how effective their services would be. Thanks to ADWARE RECOVERY SPECIALIST, I was able to successfully recover my assets. I am profoundly grateful for their hard work and support throughout this tumultuous journey. I wholeheartedly recommend ADWARE RECOVERY SPECIALIST to anyone facing similar challenges. Their Cryptocurrency Recovery services to helping clients are truly commendable and inspiring. Thank you, ADWARE RECOVERY SPECIALIST for the Good Work done.7 -
Lost Your Crypto Here’s How to Get It Back
Digital asset recovery is a hot topic for anyone who's lost their precious cryptocurrency like Bitcoin. Imagine waking up to find your digital wallet empty or even worse having someone else scam you. It is a gut punch but there are steps you can take to fight back and possibly reclaim what is yours. The world of crypto can feel like the Wild West yet recovery is not a lost cause if you know where to turn. Victims of BTC loss have a few solid avenues to explore and with the right moves you might just turn despair into hope.
First off don't panic. Time is key so start by gathering every scrap of evidence you have. Think transaction IDs, wallet addresses and any messages tied to the loss. This info is your ammo. Next, you should also notify your crypto exchange or wallet provider. Some platforms have tools or support to freeze suspicious activity if you act fast.
Now let's talk about getting serious help. Hiring a private investigator who knows the crypto space can make a huge difference. These pros dig into blockchain trails and track where your assets might have gone. There are many but among them one name that pops up often is GrayHat Hacks Contractor. They're known as some of the most sought after experts in this game. Their skills in tracing digital footprints have earned them a rep among victims looking to recover their funds. Just don't expect miracles overnight because most times it takes grit and patience for recovery to be successful.
It is a good Idea working with blockchain analysis firms like them. These outfits use fancy tech to follow the money across the network. They can spot patterns and sometimes even ID the culprits behind the loss. Pair this with legal action and you have got a combo that might pressure thieves into slipping up. Speaking of legal stuff consider consulting a lawyer who gets cryptocurrency. They can guide you on filing claims or even hitting scammers with lawsuits if you can pin them down.
Finally, join the community. Online forums and groups are full of people who have been through this. They share tips and sometimes point you to resources you would never find alone. Recovery is not always guaranteed but sitting still gets you nowhere. Whether it is teaming up with pros like GrayHat Hacks Contractor or tapping into crowd wisdom every step forward counts. Crypto loss stings hard yet with determination and the right allies you can fight to take back what is yours. The key is to act smart, act fast and never give up.1 -
HOW TRUST GEEKS HACK EXPERT HELPED ME TAKE LEGAL ACTION & RECOVER MY FUNDS
It's a fact: Reddit has always been, is, and will be my source for crypto discussions, security tips, and market trends. Little did I know it would be the same site that helped save me from financial ruin. Some months ago, an AMA thread about Trust Geeks Hack Expert showed up. People asked them anything: from lost wallet recoveries to phishing scams; their answers sounded really detailed, transparent, and full of insight. At the time, I didn't know that their help was near. It all started with what I thought was a routine software update. I had received an e-mail from what looked like a trusted exchange, telling me to install an important patch. The email looked *legit—*matching the branding, formatting, and even the usual tone of messages I had received before. Without a second thought, I downloaded the update and installed it. Biggest mistake of my life. It froze within minutes, and then it automatically restarted. My crypto wallet was empty when I regained access. $200,000-gone. At first, I thought it was some kind of glitch, but as I dug deeper, the cold reality hit me hard: I had been hacked. The "update" was a form of malware designed to drain wallets by injecting malicious code. Panic set in, but rather than spiral, I remembered the Trust Geeks Hack Expert AMA. Their confidence in handling cases like mine had stood out to me. I rushed back to the thread, found their contact details Website h tt p s :// trust geeks hack expert. c o m / -- E m a il : trust geeks hack expert {@} fast service {.} c o m, and reached out immediately. Their response was prompt and very reassuring. They asked for every little detail I could remember-from the time of the installation of the fake update to the exact nature of the transactions I had done prior to this. They got to work, tracing the movement of my stolen funds using some advanced blockchain forensics.
Days went by, and I had my doubts, but they kept me updated. Then came a message that I was praying for; they had recovered my $200,000. It sounded like a dream come true. All stress, regret, and anger vanished at that moment. Trust Geeks Hack Expert saved not only my funds but also taught me a lesson which will never be forgotten: never trust email links. Now, I double-check every update; use cold storage for large amounts; don't click on anything that's remotely suspicious. If not for that Reddit AMA, I would have never found the only team skilled enough to turn my disaster into a comeback story.1 -
Entrusting one's hard-earned money to the wrong hands can have devastating consequences. My journey began innocently enough, sparked by the success story of a former coworker who boasted of her newfound wealth and attributed it to the guidance of an investment coach. Intrigued by her lavish lifestyle, I delved deeper into the world of stock trading, eager to replicate her success. Upon contacting the purported investment coach, John Mark, I was met with promises of quick riches and convenient trading platforms. Eager to seize the opportunity, I followed his recommendations and funded my trading account with a significant sum of $78,000. However, what followed was a series of red flags and suspicious transactions that left me questioning the legitimacy of the entire operation. Despite completing numerous trades within my first week, attempts to withdraw my profits were met with resistance and dubious excuses. The company insisted on additional fees for gas and maintenance, a requirement that had never been mentioned before. As doubts gnawed at my conscience, I realized I had fallen victim to a sophisticated scam, orchestrated by individuals preying on unsuspecting investors. Feeling helpless and betrayed, I turned to FAST SWIFT CYBER SERVICES., a beacon of hope amidst the chaos. From the moment I reached out to them, their team exhibited understanding the gravity of my situation. They conducted a thorough investigation, meticulously analyzing every aspect of the scam to uncover the truth. FAST SWIFT CYBER SERVICES. technical expertise are experienced .Despite the complexity of the case, they remained steadfast in their pursuit of justice, leaving no stone unturned in their quest to reclaim what was rightfully mine. With the information I provided, FAST SWIFT CYBER SERVICES. successfully traced the origins of the scam and identified the culprits responsible for my financial misfortune. Their swift action and relentless determination culminated in the recovery of all lost funds, restoring my faith in humanity and the promise of a brighter future. The amount recovered, totaling $78,000, served as a testament to FAST SWIFT CYBER SERVICES.'s unparalleled capabilities and unwavering commitment to ethical practices. Their transparency and willingness to explain their procedures instilled a sense of trust, which was crucial during such a trying time. I cannot recommend FAST SWIFT CYBER SERVICES. highly enough to anyone who finds themselves ensnared in the clutches of financial fraud. Their exceptional service is good. If you ever find yourself facing a similar ordeal, don't hesitate to seek help from FAST SWIFT CYBER SERVICES.. Let FAST SWIFT CYBER SERVICES. be your savior. Contact FAST SWIFT CYBER SERVICES. via⁚
Email: fastswift @ cyberservices . com
Telephone: +1 323-904-9024
WhatsApp: +4670-449-7301
-
CONSULT A LICENSED CRYPTO AND USDT RECOVERY EXPERT= REACH OUT TO SALVAGE ASSET RECOVERY
The rise of cryptocurrency has brought incredible innovation to the financial world but it has also opened the door to scams, hacks, and fraudulent schemes. For victims of these digital crimes, recovering lost assets can seem nearly impossible. In this difficult and complex environment, Salvage Asset Recovery emerges as a trusted ally, offering expert support and proven strategies to retrieve stolen or lost cryptocurrency. What makes Salvage Asset Recovery stand out in a crowded field is their results driven methodology and dedication to client success. Their team of seasoned professionals combines advanced tools with a deep understanding of how digital assets move across the web. Using sophisticated tracking tools and analytics, they trace the flow of stolen funds across multiple blockchain networks, pinpointing suspicious wallet addresses and following money trails that most wouldn’t know how to navigate. Salvage Asset Recovery doesn’t just rely on technology they also understand the emotional and financial stress their clients are under. Their commitment to clear communication and transparency ensures that clients are never left in the dark. From the very first consultation, clients receive realistic timelines, regular updates, and honest assessments of their case's progress. This human-centered approach builds trust and restores a sense of control to those who may feel powerless after being defrauded. Another key factor behind Salvage Asset Recovery’s growing reputation is their track record of successful recoveries. Whether the loss stems from phishing scams, Ponzi schemes, hacked wallets, or fraudulent investment platforms, they approach every case with a tailored strategy designed to maximize the chances of fund retrieval. They understand that no two cases are the same, and their flexible, data-driven approach reflects that. In an industry often marked by uncertainty and lack of recourse, Salvage Asset Recovery provides a beacon of hope. For individuals and businesses alike, their services offer a legitimate and trustworthy path to recovery. With a blend of technical expertise, legal knowledge, and genuine care for their clients, Salvage Asset Recovery has become a go-to resource for anyone seeking justice in the volatile world of digital finance. When it comes to recovering lost crypto assets, Salvage Asset Recovery is more than a service they’re a lifeline.
CONTACT INFO=====WhatsApp+ 1 8 4 7 6 5 4 7 0 9 6
TELEGRAM======@Salvageasset2 -
InterracialCupid Review
What is Mixte Cupid? It's one of the better internet dating sites https://yourbestdate.org/interracia... for serious human relationships and marriage. This is a place for individual people looking for long-term relationships and marriage to be able to meet and connect. The particular site exists to assist individuals like you discover in addition to form connections with appropriate matches. Are you thinking of joining the Interracial Cupid website? We would like to help an individual make the best choice for your love life. That's why we'll provide a person with all the important facts you need to be able to make the right choice for you. In this specific article, we'll tell you about the site's users, join process, safety, costs, and much more. Keep reading to uncover our full Interracial Cupid reviews below.
Simplicity regarding Use
The registration about . com takes about a moment – you want to provide a message, place of living, age, and email. Later on, you may make your user profile look more attractive by having some personal data, informing about your ideal companion, and so forth It is similarly simple to get used to navigating the particular portal: the design is simple and similar to each of the sites that belong to the Cupid Media party. For those who have any experience of visiting these platforms a person would notice numerous similarities.
Number of Members
In accordance with Interracial Cupid dating testimonials, the site hosts around 38, 000 users generally situated in the United Declares, Canada, Australia, plus the BRITISH. The database isn't that huge so you should not necessarily watch for thousands of consumers to be permanently on the internet. When you log within, it is common to see a few hundred members participating in the portal. Or you may wait for typically the moment when it is a morning in the You. S. – this is usually the time when the majority of users examine out their profiles and once you have a opportunity to encounter lots of interesting users.
Quality of Information
InterracialCupid. com contains genuinely informative profiles. Each of the users are expected to reveal the essential info on them yet some tend to add added facts with their pages. Therefore, you may face big profiles that contain information on appearance, background, values, hobbies and interests, interests, lifestyle. Also, you may expect to see several photographs in each profile : you can also see the number of images uploaded as it is indicated following to the key profile photo.
Safety
Okay, so this the question we all want answered first: Is Interracial Cupid safe? We always inspire you to make of which decision for yourself when if you're thinking about joining a dating site. Do the little research and appearance into the site's safety features. For specific Interracial Cupid safety tips, you could always label the site's own safety page. If the dating site you want to join doesn't have a safety page, use your best judgement before signing up.
Have a person encountered predatory behavior on the site? We usually encourage you to get in touch with Interracial Cupid help to be able to report suspicious activity. Rely on your instincts if an individual feel unsafe or uncertain on any site. In addition to never give your individual information to members. You can help protect yourself and other members by simply bringing anyone suspicious towards the attention of the web site's moderators. They can also help in case you are having trouble with your account or perhaps want to cancel Mixte Cupid for any cause.
Conclusion
At InterracialCupid all of us always want you in order to succeed. That's why we all offer you all the info we could on the internet dating sites you want in order to learn about. Plus, we would like to hook you up with Interracial Cupid discount coupons whenever we can. Browse down to learn more.
Most likely here as you wanted to be able to read our Interracial Cupid reviews. If you've been thinking about joining but you still aren't positive, we hope we're able to assist. This site has a new lot to offer people thinking about permanent dating plus marriage. InterracialCupid desires to aid you get the most out of online dating sites in addition to it all starts along with finding the best dating site with regard to you. That's why we compose these reviews. We would like to provide you along with as much useful information as possible about the sites you're thinking about joining. But we could furthermore help by offering you Interracial Cupid promo rules, so check back frequently to see what we've got. Ready to begin gathering persons who want a similar things you do? Go to the Interracial Cupid total site to begin with now.1 -
MOBILESPY APP BY CYBERSPACE HACK PRO
I was feeling increasingly suspicious about my partner's behavior. Over time, I noticed subtle changes in his routine more secrecy around his phone and unexplained absences. After trying to communicate openly, I was left with lingering doubts.
In my search for clarity, I decided to use CYBERSPACEHACK PRO mobile spy tool, which allowed me to monitor phone activities like messages and call logs. After using the tool, I discovered that my partner had been communicating with someone else, confirming my suspicions.
The truth was painful to face, but it also gave me the clarity I needed to make important decisions about my relationship. I now understand that while technology can provide insight, trust and communication are the foundations of any relationship
Information's
Email // Cyberspacehackpro //@ // rescue team. com
WhatsApp +1 (659) 217 92391 -
Hire a hacker to recover your lost or stolen cryptocurrency / Consult Captain WebGenesis.
Captain WebGenesis is a leading provider of investigation solutions for the cryptocurrency industry, helping forensic specialists and law enforcement in recovering stolen Cryptocurrency assets. Captain WebGenesis are adept at detecting suspicious activity and linking specific cryptocurrency addresses to specific people or businesses; furthermore their technology enables them to track funds between multiple accounts; his team of committed professionals has vast experience in cyber forensics, cryptocurrency asset recovery, and fraud prevention.4 -
On Thanksgiving Day, I fell victim to a sophisticated Deriv trading scam that initially promised significant returns but ultimately left me unable to access my funds. The scam began when I was contacted by an admin from a Telegram group with 400 members. The group participants were sharing trading strategies and success stories about profiting from signals provided by the group's leaders. Intrigued by their claims of high returns and the apparent transparency of the group, I decided to join.The scammers introduced me to a 45-day investment cycle, assuring me that at the end of the period, I would be able to withdraw my initial investment along with any profits. Trusting their process, I transferred $43,000 in several wire transfers to start my account. My balance grew quickly, and within a short time, my account had ballooned to $500,000. Everything seemed to be progressing as promised, and I was encouraged by the steady returns. However, things began to take a turn when I attempted to withdraw my profits. I was told that I couldn’t access my funds until I paid a supposed “tax” on my earnings. This tax requirement had never been mentioned when I initially joined or made my investment, so I grew suspicious. When I questioned the legitimacy of this fee, I received evasive answers and delays.
 1
1 -
USDT RECOVERY SERVICE: WEB BAILIFF CONTRACTOR EXPERIENCE
It was an ordinary Tuesday. I was keeping an eye on my Bybit portfolio when an email showed up that looked like a formal notice from the exchange regarding suspicious behavior. I didn't hesitate; I clicked the link and entered my credentials. When I hit submit, a sense of horror befell me. Within minutes, my Bitcoin wallet was drained. Losing 3.2 BTC, worth nearly $200,000 at the time, wasn't just monetary. It was a personal trust issue. I couldn't fathom that I had been phishing-scammed. I spent days scouring forums, contacting Bybit customer support, and even filing a report with the police. But the responses were disappointing and repetitive. Crypto withdrawals can't be reversed. Scam victims seldom see their money back. The frustration was overwhelming. I barely slept. I continuously replayed the moment in my head repeatedly. Why did I click on the link? Why didn't I double-check it? The frustration and guilt ate away at me. Friends tried to be helpful, but many didn't get the emotional and financial weight of what had transpired. I had always taken security precautions carefully. But in a moment of distraction, all was lost Weeks later, trawling Reddit threads on crypto cons, I found some mention of Web Bailiff Contractor. I was suspicious at first. It sounded too good to be true. But the comments looked genuine, and I was desperate. I went ahead and got in touch with them. They were speedy, professional, and surprisingly sympathetic. They made no promises of miracles. Instead, they explained their procedure: following blockchain transactions, identifying potential exchange cash-outs, and working with legal and crypto groups to freeze and recover funds.I gave them all I had wallet addresses, transaction history, screenshots and waited. A few days later, I got an email that left me speechless. They had been able to track and recover all my stolen Bitcoin.I couldn't believe it. After being told over and over again that the money was gone forever, here it was, back in my pocket. It was waking up from a nightmare. Web Bailiff Contractor did not just get my money back. They got my sense of security, my trust, and my peace of mind back too.I am writing about my experience now in case someone else out there is feeling the same panic and desperation that I once felt. There is hope. And every now and then, there is a second chance.2 -
WHERE TO HIRE A CRYPTO RECOVERY SERVICE — DIGITAL HACK RECOVERY
We've all been there: you see an email that looks important, maybe from a service you use, and you click the link without a second thought. That was me one unsuspecting morning when I received an email claiming there was "suspicious activity" on one of my accounts. Thinking I was protecting my assets, I clicked the link, entered some information, and went about my day.
What I never knew was that I had just stepped into an organized trap. It wasn't from my account provider at all-malware-and in less than five to ten minutes, it siphoned $75,000 from my cryptocurrency wallet. I felt my heart drop the moment I opened my wallet some time later and the balance showed zero; it felt as if all air had been sucked out of the room. Panic turned to anger, then despair. How could I have been so careless?
I spent the next few hours spiraling, scouring the internet for solutions, feeling the world closing in on me. That's when I came across Digital Hack Recovery. I won't lie; at first, I was skeptical. The internet is full of promises that almost sound too good to be true, and I must say that right after getting conned once, it was pretty hard for me to try another. Reviews about Digital Hack Recovery were great, so I called them because I just literally had nothing to lose.
From the initial contact, their staff were the picture of professionalism. They didn't just hear my story; they listened. They assured me that they had seen similar cases and explained the recovery process step by step. Their calm confidence was infectious, and for the first time since the incident, I felt a glimmer of hope.
They worked day and night for the next several days, keeping me updated and answering all my anxious questions. Then, one day, the call came: they had recovered my $75,000. To hear those words was like getting a second chance at life. The relief was indescribable.
But they didn’t stop there. The team took the time to educate me on how to spot phishing scams and secure my wallet better. They even shared tips on recognizing red flags in suspicious emails. Thanks to them, I’m more vigilant than ever, and my funds—and peace of mind—are safe.Digital Hack Recovery didn't just recover my wallet; they restored my faith in humanity. Lesson learned: trust cautiously, but never lose hope.
WhatsApp +19152151930
Website; https : // digital hack recovery . com
Email; digital hack recovery @ techie . com1 -
How to Recover Cryptocurrency in 2025 (Hire A Hacker) - Captain WebGenesis
Can stolen crypto be recovered? Yes, Captain WebGenesis possesses the necessary expertise in digital forensics to potentially trace and track down your stolen cryptocurrency. With years of experience and a proven track record of success, Captain WebGenesis has developed a comprehensive approach to cryptocurrency recovery
The comprehensive recovery process involves:
1. Initial Assessment: Captain WebGenesis will conduct a thorough review of the incident to determine the scope of the theft and identify potential leads.
2. Digital Forensic Analysis: He will then utilize advanced digital forensic tools to extract and analyze transaction data, network logs, and other relevant information to trace the stolen cryptocurrency.
3. Network Analysis: The team will meticulously examine the blockchain network to identify suspicious transactions, wallets, and patterns that may lead to the recovery of your stolen assets.
4. Collaboration with Exchanges and Authorities: Captain WebGenesis works closely with cryptocurrency exchanges, law enforcement agencies, and other relevant parties to freeze suspicious accounts, trace the flow of funds, and facilitate the recovery of your stolen cryptocurrency.
5. Recovery and Return: Once the stolen cryptocurrency is traced and tracked down, Captain WebGenesis will work to recover the assets and return them to their rightful owner.
Contact him now on: Captainwebgenesis@hackermail. com.1 -
A good friend of mine recommended Fred Hacker to me when I had issues with my partner, he started acting suspicious and was on his phone at odd hours & always acting strange. I contacted Fred Hacker and he remotely hacked into his device granting me total access to his device without him knowing. I was shocked and overwhelmed that I could read his texts, see pictures, emails and all that. This hacker is hands down the best I’ve hired. Contact him on email : fredvalcyb erghost @ gm ail com and you can text,call him on +..1..51..77..98,,18 ..08. I recommend him to everyone reading this post.9
-
For the past three years, I've been involved in Forex trading, constantly learning new strategies and honing my skills. Along the way, I’ve come across many opportunities, but one particular online trading contest left me shaken and wiser. What appeared to be a legitimate contest with a grand prize turned out to be an elaborate scam. I’d like to share my experience to help others avoid a similar trap. It started with an online ad promoting a Forex contest. The hosting company seemed reputable, the prize was attractive, and the website looked professional. Eager to join, I paid a $1,000 registration fee. Soon after, I got an email saying I’d qualified for the next round but to proceed, I needed to cover $2,000 in shipping costs for the prize. Believing it was worth it, I paid. But after that, communication stopped. No prize. No response. Suspicious, I started researching and found out that many others had been caught in the same scheme. I had fallen victim to a professional scam and lost a total of $10,000. Feeling overwhelmed, I began looking for help. That’s when I found a digital recovery service specializing in online scams. I provided all my evidence, and they began working on my case. Thanks to their expertise, they were able to trace the transaction and recover my funds. This experience taught me the importance of verifying everything before making financial commitments online. I hope my story raises awareness about online trading scams and helps others avoid them. Be cautious if it seems too good to be true, it probably is.
Email: digitalresolutionservices @ myself. c o m
Stay vigilant,
Tulijuana Cutler 1
1 -
I know what its like living an endless days of nightmare and paranoia due to some life draining circumstances. Are You in dare need of solutions or answers that require cyber services or ethical hacking ? Probably suspicious of someone dare to You and desire to hack their Phone's or Computer to feel secure again Or got scammed either by cryptocurrency investment scams, romance scams etc. and require urgent recovery of your Money and funds... Cypher Cybersecurity helped Me in my time of turmoil. They are definitely a genie with Tech and guaranteed to deliver on whatever task You bring Up.
You can send them a mail on CYBERCYPHER77@GMAIL ...You did be so amazed You would recommend them as well.1 -
HOW I GOT A HACKER TO RECOVER MY INVESTMENT FROM FAKE PLATFORM
My story is that all hell broke loose when my cousin introduced me to Byconomy and claimed it was a good investment opportunity. The promoter of Byconomy, “Rogers”, promised to return a profit of $1,200 after just 48 hours of crypto trading. I was suspicious of the deal so I only deposited $200 into my Byconomy account and watched as my balance quickly rose to nearly $1,000. I saw it as an opportunity to increase my savings so I increased the deposit amount to $1,000 and as expected, the balance rose to $6,000. Again, I thought it was wise to withdraw a larger amount at once so I deposited additional $18,000, where I got close to $90,000 total. After the 48-hour period, Rogers told me that they needed me to pay $4,000 commission or trade the gains. After paying the requested amount, Rogers told me they needed another $4,000 fee to withdraw the account balance. At this point, I refused to continue to pay Rogers and he inturn claimed that failure to make the payment would result in the loss of the whole amount. I found the whole idea manipulative because my cousin received the same messages after depositing $12,000. After numerous consultations on how we would get back our deposits, we came across a review about a crypto hacker who helps crypto investment victims. We emailed them through gearhead(@)engineer(.)com and the response was quite fast. After explaining the situation and providing all details related to the scam, they forwarded the approach they implemented and within 6 hours, we each got back our initial investment amount. I applaud GearHead Engineers and I 100% recommend them for recovery services. Visit their website gearheadengineersorg for more info. -
I RECOMMEND CRYPTO PANDEMIC HUNTER FOR ONLINE AND SPOUSE INVESTIGATION
My previous relationship seemed to be perfect until sudden subtle signs became prevalent . She became unusually secretive with her phone and stuffs. Our communication dwindled, replaced by short responses and a developed sense of distance. My conscience got clouded with suspicion, but I desperately did not want to believe she could be having a secret affair due to how much I loved and trusted her. However, frequent unanswered calls convinced me.
That's when I stumbled upon Crypto Pandemic Hunter, a private forensic expert specializing in digital investigations. Skeptical yet desperate, I laid out my concerns. Crypto Pandemic Hunter explained their approach, emphasizing discretion and ethical practices. They utilized a combination of advanced software and forensic techniques to analyze my girlfriend's digital connections.
With my consent and a clear understanding of the legal boundaries, they effectively tracked her phone calls, identifying patterns and unfamiliar numbers. They delved into her email communications, flagging suspicious exchanges and hidden accounts. Her social media activity was scrutinized, revealing deleted messages and interactions. Crypto Pandemic Hunter used tools like malware and Encase to point a comprehensive picture of her online activities.
The evidence gathered by Crypto Pandemic Hunter was undeniable. The phone records showed frequent communication with a number I couldn't recognize, often late at night. The emails revealed flirting conversation between the two and dates like reservations they had planned for summer. Social media accounts confirmed my worst fears which details I cannot disclose. The truth was a painful blow, but the clarity provided by Crypto Pandemic Hunter allowed me to confront the situation and begin the healing process.
I am extremely grateful to Crypto Pandemic Hunter. I recommend anyone searching for truth to contact them.
cryptopandemichunter[at]consultan,com
WhatsApp : +1 (205) 3573937 1
1 -
You don’t realize how much trust you place in technology until it fails you or until someone exploits it. I learned this the hard way when my crypto wallet, containing over $87,000 in Bitcoin and Ethereum, was drained in an instant. A clever scam disguised as an official update cost me everything I had worked so hard to save.
At first, I believed what everyone said: “Once it’s gone, it’s gone.” The blockchain doesn’t forgive mistakes, and recovery felt like a fantasy. But desperation pushed me to keep looking, and that’s when I found DIGITAL RESOLUTION SERVICES. From the start, they were different: no false promises, no hype, just a practical and transparent approach. They explained how stolen funds could be traced, even through the complexity of blockchain transactions.
What followed was nothing short of incredible. Their team worked tirelessly, tracking the stolen assets step by step, wallet by wallet. They coordinated with exchanges, flagged suspicious accounts, and kept me updated at every turn. It felt like they were as invested in getting back my funds as I was.
Weeks later, I got the email I thought I’d never see: “We’ve recovered your funds.” Seeing my wallet balance restored felt like a second chance at everything I thought I’d lost. It wasn’t just about the money it was about reclaiming my future and finding hope again.
DIGITAL RESOLUTION SERVICES didn’t just recover my cryptocurrency; they gave me the ability to move forward without the weight of that loss holding me back. If you’ve lost crypto and feel like there’s no hope, don’t give up. There are people who know how to fight for you. I’m living proof that even in the world of crypto, recovery is possible with the right team.
Contact: Digital Resolution Services
Email: digitalresolutionservices (@) myself. com
WhatsApp: +1 (361) 260-8628
Forever grateful,
Monica dresdner 1
1 -
Many people think that cryptocurrency trading is a scam. Please don't believe them, they are wrong. Trading cryptocurrency is a perfectly legit form of investment. Nevertheless, the cryptocurrency trading universe is ripe with scams, so it makes sense to be extra cautious.
Even though Forex trading is a legitimate form of investment, retail traders often fall prey to fraudsters. Therefore, it is always recommended to exercise extra caution.
1. The essence
a.Forex and cryptocurrency trading is a perfectly legit form of investment.
b. Forex scams and Forex pyramid schemes are widespread globally.
c. Retail Forex traders are the prime targets of fraudsters
d. Choosing a reputable Forex broker is a key step in anyone’s trading journey.
2. How to spot a Forex scam?
Be suspicious if you’re offered Forex trading services that promise massive gains in a short period of time. As with all forms of investment, Forex trading carries massive risks and there is no guarantee your trades will always be profitable. Promises of exorbitant gains are almost always a red flag.
It’s not a good idea to let other people have access to your money. Never deposit any funds without due diligence of the person/organization you are dealing with. One of the most common types of Forex scam relies on not allowing people to withdraw the funds they had deposited earlier.
3. How To Get Money Back
a. Get recovery advice:
Advice from recovery professionals experienced in financial fraud cases can be very helpful in the recovery process. I recommend that you consult Saclux Comptech Specialst that will help you navigate the system and get your money back. If you are a victim of Cryptocurrency or Forex fraud, it is important to act quickly. The longer you wait, the harder it will be to get your money back.1 -
Buy Trustpilot Positive Reviews
Review of Buy Trustpilot by Buy SMM Services. We have successfully provided this service for a considerable amount of time. Additionally, customers are pleased with my services. Additionally, we have a large team. so that we can provide you with a Trustpilot review that has not been dropped in any way. Each review comes from a different device for us. Our review does not disappear if we use a different device. TrustPilot. com is a consumer review website established in Denmark in 2007 and hosts reviews of global businesses.
The site is free for customers because we all use real IP addresses. Additionally, it offers businesses free services. Wikipedia. Customers share their preferences and warn or encourage one another on this website. so that we can provide you with high-quality testimonials on our Trustpilot Business Page. so that they can have a positive experience with your service.
Individuals from the Assembled Realm, the US, France, Germany, and a lot more nations use Trustpilot. TrustPilot is also used by 20.1 million people. Customer feedback on Trustpilot can be either positive or negative for your website and business. It's critical for customers because you could lose them if they see something negative here.
Customers can use these reviews to select high-quality services. If you go to the TrustPilot website and look at customer feedback, reviews, or ratings, and if they are of poor quality, then the buyer will be suspicious and go to another seller. As a result, you will choose which service is best. For example, you are a replacement buyer, customer, or member. Reviews on Trustpilot are crucial for improving the customer experience, expanding the number of search engines, increasing site sales, conversions, and reputation, as well as expanding the customer base.
#Trustpilot Reviews #Reviews #Positive Reviews #advertising #Marketimg
-
A few months ago, I was approached online by a so-called investment broker. Everything looked professional — flashy websites, fake but convincing reviews, even video calls with people who seemed legitimate. They promised unbelievable returns on Bitcoin investments, and I, eager to grow my crypto holdings, fell for it. Over a few weeks, I transferred Bitcoin worth around $360,000 to what I thought was a secured investment wallet. The “broker” kept assuring me my money was growing, even showing fake dashboards with fabricated profits. But when I tried to withdraw my funds, they demanded additional fees — taxes, account, activation, and release charges. That’s when the truth hit me I had been scammed. Devastated, I started searching for solutions. But then, a glimmer of hope. A cybersecurity contact muttered Try Dexdert Net Recovery. They hunt crypto ghosts. Dexdert Net had real testimonials, detailed explanations of their process, and most importantly, they didn’t ask for any suspicious upfront fees. After contacting them, their team patiently walked me through the steps gathering all evidence of the scam, tracking the Bitcoin transactions on the blockchain, and using legal recovery channels and cyber forensic methods. They kept me updated at every stage. 4 days later, I got the email I’ll never forget: Funds Recovered. Dexdert Net Recovery successfully traced and retrieved the entire $360,000 worth of Bitcoin from the scammer’s wallets. Thanks to Dexdert Net Pro Recovery, not only did I reclaim my lost Bitcoin, but I also regained a sense of justice — and a serious lesson learned. If you’re ever in a situation like I was, know this: there’s hope, and there are real experts out there who can help. Dexdert Net Recovery proved it to me.
CONTACT DEXDERT NET RECOVERY VIA INFORMATION BELOW
Telegram: (@Dexdertprorecovery)
WhatsApp: (+1 859 609‑4156)2 -
This write-up is solely based upon the authenticity and efficiency of monitoring apps, it's quite obvious there are many malicious and dubious apps and reviews that are under the guise of being real. The best and less tedious way to see who your partner is texting or calling is by using dedicated monitoring apps created by people like Kingston (Kingston @ cyber-wizard. com). These apps make it easy to track incoming and outgoing texts and calls on your partner’s phone without them ever knowing you're doing so.
These apps are designed to be completely undetectable, meaning that even if someone checks their phone for suspicious activity, they won't be able to spot the monitoring app running in the background. One of the benefits you would fancy the most about the monitoring app it's ability to access your partner's text messages and call logs on all social networks. Isn't that cool? you should give it a trial like I did without any regrets!3 -
Losing access to your cryptocurrency can be a devastating experience, whether due to forgotten passwords, hacking, scams, or technical errors. Fortunately, professional recovery services like BITCRACK RECOVERY EXPERTS specialize in retrieving lost or stolen crypto assets. If you’ve lost your Bitcoin or other cryptocurrencies, here’s how BITCRACK RECOVERY EXPERTS can help you recover your funds.
Why Choose BITCRACK RECOVERY EXPERTS?
BITCRACK RECOVERY EXPERTS is a trusted name in cryptocurrency recovery, offering advanced techniques to help victims of crypto theft, fraud, or accidental loss. Their team of blockchain forensic experts uses cutting-edge tools to trace transactions, identify wallet vulnerabilities, and recover inaccessible funds.
Services Offered by BITCRACK RECOVERY EXPERTS
Wallet Recovery – Regaining access to locked or lost crypto wallets.
Scam Investigation – Tracing stolen funds from fraudulent schemes.
Phishing & Hacking Recovery – Recovering crypto lost to cyberattacks.
Private Key Retrieval – Helping users restore lost or corrupted private keys.
Exchange & ICO Scam Recovery – Assisting victims of fake investment platforms.
Steps to Recover Your Lost Cryptocurrency
1. Contact BITCRACK RECOVERY EXPERTS
Reach out to their support team via email:
📧 bitcrackrecoveryexperts@bitcrack.co.site
Provide details such as:
The type of cryptocurrency lost (Bitcoin, Ethereum, etc.)
How the funds were lost (hack, scam, forgotten password, etc.)
Transaction details (wallet addresses, TXIDs, if available)
2. Initial Consultation & Case Evaluation
Their team will analyze your situation and determine the best recovery approach. They may request additional information to strengthen the investigation.
3. Recovery Process
Using blockchain forensics and legal methods, BITCRACK RECOVERY EXPERTS will trace the movement of your funds and attempt to recover them. This may involve:
Working with exchanges to freeze stolen assets
Identifying security breaches in wallets
Utilizing legal channels if necessary
4. Fund Retrieval & Secure Return
Once recovered, your cryptocurrency will be securely returned to a wallet under your control. The team ensures transparency throughout the process.
Tips to Avoid Future Crypto Losses
Use Hardware Wallets – Store crypto offline for maximum security.
Enable 2FA – Add an extra layer of protection to exchange accounts.
Beware of Scams – Avoid suspicious investment schemes and phishing links.
Backup Private Keys – Store keys securely in multiple locations.
Final Thoughts
Losing cryptocurrency doesn’t always mean it’s gone forever. With professional help from BITCRACK RECOVERY EXPERTS, there’s a strong chance of recovery. If you’ve fallen victim to theft, hacking, or accidental loss, don’t hesitate to contact them at:
✉️ bitcrackrecoveryexperts@bitcrack.co.site
Act quickly—the sooner you start the recovery process, the higher the chances of success2 -
I am a businessman living in the diaspora, and my desire for affection and care mirrored that of anyone else. My search for love commenced with me signing up for an online dating app, where I encountered an Asian woman. Following a period of communication, she introduced me to what she described as a popular investment platform in Asia, I trusted her so much that I failed to carry out an investigation. According to her, substantial profits were being earned there, and her presentation was so compelling that it piqued my curiosity. Unbeknownst to me, I was being catfished. She provided evidence of her earnings and even sent me a watch as a token of her affection. Consequently, she gained my trust and affection, which marked the beginning of my financial losses in Bitcoin. I had complete faith in her and invested over a million US dollars. Upon recognizing the extent of my investment in this fraudulent scheme, I attempted to withdraw my profits from the investment program, as I had utilized my business capital. My requests were disregarded, and they continually requested additional funds. Frustration mounted, and my supposed partner became hostile after I ceased sending money. Seeking assistance, I discovered RUDER CYBER TECH SLEUTHS. They assessed my circumstances and confirmed my worst fear: I had become a victim of a pig-butchering romance scam. I was disheartened, as I genuinely believed I had found love again following a difficult divorce. Fortunately, RUDER CYBER TECH SLEUTHS specializes in recovering Bitcoin sent to fraudulent or scam wallets. After collaborating with RUDER CYBER TECH SLEUTHS, they successfully recovered my scammed Bitcoin. They are my permanent solution for cybersecurity. I strongly endorse RUDER CYBER TECH SLEUTHS for crypto tracing and recovery. If you find yourself in a similar situation or involved in a suspicious investment platform, contact RUDER CYBER TECH SLEUTHS through
whatsapp: +12132801476
Telegram : @rudercybersleuths3 -
How iForce Hacker Recovery Helped Me Recover My Lost Cryptocurrency
It all began when I got an email that looked like it was from a reputable bitcoin exchange. I received an email asking me to confirm my account because of "suspicious activity." I clicked on the given link in my hurry, which sent me to a phony website. My money disappeared from my wallet in a matter of minutes. The sense of remorse and panic was overwhelming.
I started looking into recovery options because I was in dire need of assistance. After reading a lot of reviews and suggestions, I came across iForce Hacker Recovery. Their client endorsements were positive, and their website exuded professionalism. After I contacted them, their support staff responded to me in a matter of hours. The process of recuperation was comprehensive and open.
Website info; ww w. iforcehackersrecovery. com
Email; contact@ iforcehackersrecovery. co m
Whatsapp> +1 (240) 803. (3706) 1
1 -
PROFESSIONAL CRYPTO RECOVERY COMPANY; BITCOIN AND ETH RECOVEYR EXPERT HIRE CYBER CONSTABLE INTELLIGENCE
Early 2025,I was captivated by a cryptocurrency trading company that promised extraordinary financial rewards. Their marketing materials boasted high returns, expert mentorship, and the allure of becoming a self-sufficient online trader. Eager to capitalize on the volatile crypto market, I underwent a series of assessments to prove my trading aptitude and dedication. The third test, a rigorous simulation involving real-time market analysis, risk management strategies, and cryptocurrency volatility scenarios, convinced me of the platform’s legitimacy. By this stage, I had invested roughly $56,000, reassured by their polished interface and assurances that my funds were secure and growing. The turning point came when I attempted to withdraw my accumulated balance of $273,000, which included trading commissions and a $25,000 “loyalty bonus.” Instead of processing my request, the company demanded an additional $83,000 to “finalize tax compliance protocols” and unlock my account. They framed this as a routine step to “legitimize” my earnings and transition me to a “permanent trader” tier. Skepticism set in as their communication grew evasive: delayed responses, vague explanations about blockchain “security fees,” and sudden claims of “wallet activation errors. Alarm bells rang louder when they cited “suspicious activity” on my account, insisting another $50,000 deposit was needed to “verify liquidity” and release my funds. Each delay came with new urgency, threats of account suspension, forfeited profits, or even legal repercussions for “breaching terms.” Exhausted by their manipulative tactics, I refused further payments and began researching recovery options. A trusted colleague recommended Cyber Constable Intelligence, a firm specializing in crypto fraud cases. Their team swiftly identified red flags: fake trading volumes, fabricated regulatory certifications, and wallet addresses linked to offshore exchanges. Through forensic analysis, they traced my funds, recovering a significant p
oration within weeks, restoring my hope and financial stability.
Here's their Info below
WhatsApp: 1 252378-7611
Website info; www cyberconstableintelligence com
Email Info cyberconstable@coolsite net
Telegram Info: cyberconstable2 -
installed xscreensaver on my phone and suddenly haven't had to reboot it in like a week due to unrelated issues
suspicious -
My father, a retired schoolteacher, has always been cautious with his money. He worked hard his entire life to build a modest retirement fund and trusted that it would support him in his golden years. So, when he told me about an “exclusive” investment opportunity in cryptocurrency that promised high returns, I was immediately suspicious. But he was convinced it was legitimate—after all, the website looked professional, and the salesperson had been so persuasive over the phone. Despite my warnings, he invested 15,000 USD of his savings. At first, everything seemed fine. He received regular updates and saw “profits” reflected in his online account. But when he tried to withdraw some money, the website suddenly went offline, and the phone number was disconnected. My father was devastated. He had been scammed, and his hard-earned savings were gone. I knew I had to act quickly. I reached out to TECH CYBER FORCE RECOVERY, a company I had read about online that specialized in tracing online fraud. I explained the situation, providing them with all the details: the fake website, the transaction records, and even the emails from the scammer. The team at TECH CYBER FORCE RECOVERY was incredibly understanding and assured me they would do everything possible to help. Using their expertise in digital forensics, they traced the scammer’s digital footprint and identified the offshore account where the money had been transferred. They worked tirelessly with international authorities to freeze the account and recover the funds. Within a few weeks, they successfully returned the 15,000 USD to my father. The relief on his face was indescribable. Not only had TECH CYBER FORCE RECOVERY restored his savings, but they had also given him peace of mind. They even took the time to educate him on how to spot investment scams in the future, empowering him to protect himself. This brought our family closer together. My father now understands the importance of skepticism and due diligence, and I’m grateful to TECH CYBER FORCE RECOVERY for their incredible work. They didn’t just recover money, they restored my father’s faith in justice and gave him a second chance to enjoy his retirement.
EMAIL..Techcybersforcerecovery(@)cyberservices(.)com
WHATSAPP... + 1.5.6.1.7.2.6.3.6.9.73 -
CRYPTOCURRENCY TRACING AND FUNDS RECOVERY CONSULT DUNAMIS CYBER SOLUTION
The cryptocurrency space, with its dizzying promises of financial freedom, had always intrigued me until it became the stage for my deepest disillusionment. Last year, I fell victim to an elaborate crypto scam that stripped me of years’ worth of savings. What began as a confident investment in a "guaranteed returns" scheme unraveled into a nightmare. Overnight, my portfolio vanished, along with the anonymous fraudsters who orchestrated the ploy. The aftermath was a toxic blend of anger, shame, and helplessness. I questioned every decision, replaying red flags I’d naively ignored. Crypto forums offered little solace, filled with eerily similar stories of irreversible losses. Just as I resigned myself to defeat, a glimmer of hope emerged: DUNAMIS CYBER SOLUTION.From the outset, their team stood apart by blending technical precision with unwavering compassion. Rather than treating my case as a faceless ticket, they approached it with a commitment to understanding the human toll of the scam. During initial consultations, they listened patiently to my story, offering reassurance that shifted my mindset from despair to cautious optimism. “These scams thrive on exploiting trust, not incompetence,” one advisor emphasized a perspective that dissolved my self-blame.DUNAMIS CYBER SOLUTION mastery of Cryptocurrencies forensics became evident as they untangled the digital maze of my stolen assets. They decoded how fraudsters manipulated wallet vulnerabilities and decentralized exchanges to obscure the trail, leveraging proprietary tools and cross platform collaborations to trace the funds.Over three days, their transparency became my anchor. Regular updates demystified their process, flagging suspicious transactions, and piecing together patterns linked to earlier scams. Challenges arose dead-end leads, unresponsive third parties but the team navigated each obstacle with tenacity. By second day, they’d recovered $350,000 of my assets.Beyond recovery, DUNAMIS CYBER SOLUTION prioritized empowerment. They equipped me with resources to safeguard future investments and connected me to a private forum of survivors, fostering a community of shared resilience. Today, I’m not only financially restored but fortified with hard-earned wisdom. My situation proves that loss isn’t always permanent. With cutting-edge expertise and relentless advocacy, redemption is attainable. Let my journey remind you: even in Cryptocurrency opaque wilderness, a path back exists and DUNAMIS CYBER SOLUTION lights the way.2 -
HOW CAN I GET A REPUTABLE RECOVERY COMPANY CONTACT FUNDS RECLAIMER COMPANY
WhatsApp: + 1 3 6 1 2 5 0 4 1 1 0
Running a startup in Portugal is a challenging journey, but nothing could have prepared me for the devastating blow I faced when a fake investor scam took away $275,000 of our operational funds. The pressure of managing a new business was already immense, and this loss felt like a heavy burden. I blamed myself, convinced that the money was lost forever, along with the dreams I had for my company. in the midst of my despair, a fellow founder in the Bay Area reached out to me with a glimmer of hope. He recommended FUNDS RECLAIMER COMPANY, a team known for their expertise in tracing stolen cryptocurrency. Skeptical yet desperate, I decided to give them a chance. From the moment I contacted them, I was impressed by their professionalism and understanding. They treated my situation not just as a case, but as a personal crisis that needed urgent attention. The team at FUNDS RECLAIMER COMPANY worked diligently, using advanced techniques to trace the stolen funds through complex wallets and suspicious exchanges. Their dedication was clear as they worked tirelessly, keeping me updated every step of the way. Within just 11 days, they managed to recover an incredible 88% of our capital. This recovery was not just a financial relief; it was a lifeline that allowed us to keep our business running and continue pursuing our vision. What truly amazed me about FUNDS RECLAIMER COMPANY was not just their technical skills, but their empathy. They understood how personal this loss was for me and my team. They listened to my concerns, offered reassurance, and celebrated each milestone in the recovery process as if it were their own. Their support went beyond just recovering funds; they restored my faith in the entrepreneurial journey. Today, I share the name of FUNDS RECLAIMER COMPANY with every entrepreneur I meet in San Francisco and beyond. They don’t just recover money; they save dreams. Their impact on my life and business is immeasurable, and I am forever grateful for their expertise and compassion during one of the toughest times in my entrepreneurial journey.2 -
DeFi Wallet Drained on Ethereum Network
Date of Incident: 20/06/2024
I was a regular user of various DeFi platforms, managing my assets across multiple protocols. One morning, I woke up to find my Ethereum wallet completely drained. I couldn’t understand how this could happen, as I hadn’t clicked on any suspicious links or approved any unusual transactions.
It was only after contacting TheHackersPro that I learned my wallet had been compromised due to a vulnerability in a DeFi protocol I had interacted with. The smart contract experts at TheHackersPro conducted a thorough audit and traced the funds to outsourced leveraged wallets. Thanks to their efforts, I was able to recover 4.5 BTC, but I still need to cover the Ethereum gas fee to recover the rest.
If you’ve experienced something similar, TheHackersPro could be your best chance to recover your stolen funds.
Contact Information:
Email: support@thehackerspro/com
Phone: +1 3019972349
24/7 Telegram Support: @h4ckerspro -
I am very pleased with the help R O O T K IT S REC O VE RY FIRM rendered in restoring my lost crypto investment from scammers.. I was encouraged to invest in a cryptocurrency company through an advert that i watched on the facebook . it was actually interesting and seems profitable so i contacted the company and they responded.. i asked a few question and i was assured that everything works perfectly and legit. At first i started with 5000 USD after awhile i had it returned to me together with my profits with no problems. As a result of that i continued trading as i was also advised to upgrade to the Millionaire package where you will earn much more off your trading, i did upgraded and invested more funds that my account was showing in excess of 1,280,902 USD but when I tried to take some of the profits my account went from the above to zero within 60 seconds and then after making complaints to the support i was told that I had not completed the required trades and also that their were suspicious activities on my account.. it was certainly over my head and honestly didn’t know what to do at that moment so i had to invest more but still not able to withdraw a dollar to my bank, they had full control of my account, and have refused me to withdraw anything. i finally came to know that most crypto investment companies are bunch of criminals and scammers.., so i went in search for possible means to recover my funds. Well i must say that I’m very fortunate to have been able to recover all my funds back through the help of R O O T K I TS R E C O V E RY F IRM. got so many recommendations on them by fellow victims online who has been scammed and recovered theirs back. so i contacted them for help and they delivered at the End. i thank God so much that such Team as ROOTKITS RECOVERY FIRM do exist to help victims who have been defrauded. If you have been scammed of your Crypto or been in a similar situation you contact this Team for help via Telegram; ROOTKITS7 or Email; R O O T K I T S 4 @G M A I L . COM
-
ALPHA SPY NEST RECOVERY // ETH/USDT & BITCOIN RECOVERY EXPERT.
It all started when I woke up one morning to find my crypto wallet drained—every last Bitcoin I’d invested in was gone. Months of careful trading, wiped out in an instant. I’d fallen victim to a slick phishing scam that tricked me into handing over my private keys. Devastated, I thought it was over. That’s when a friend mentioned Alpha Spy Nest, a shadowy group of crypto recovery specialists who’d helped him out of a similar mess.Skeptical but desperate, I reached out. Within hours, a voice on the other end—calm, confident, and anonymous—told me they’d take the case. They called themselves “Nest operatives,” and they didn’t waste time. First, they asked for every detail I could remember: the suspicious email, the fake login page, the moment I realized I’d been had. I handed it all over, expecting nothing but a polite “we’ll try.”What I didn’t know was that Alpha Spy Nest was already on the move. Their team—part hackers, part detectives—dived into the blockchain like bloodhounds. They traced the stolen Bitcoin as it bounced through a dizzying maze of wallets, each one a little more obscure than the last. Most people would’ve given up, but not them. They had tools I’d never heard of, scraping data from dark web forums and piecing together clues like a digital jigsaw puzzle.Days later, they called me back. “We’ve got a lead,” the voice said. They’d tracked the thief to a sloppy exchange account tied to a poorly hidden IP address. The operatives didn’t stop there—they cross-referenced the wallet activity with chatter on underground crypto channels and found the culprit bragging about his haul. With that, they flipped the script. Using a mix of social engineering and what I can only assume was some next-level tech, they baited the thief into moving the funds again—right into a trap wallet Alpha Spy Nest controlled. Few days after I’d lost everything, I got a final message: “Check your account.” There it was—my Bitcoin, back where it belonged, minus a modest fee for their trouble. I never met the team, never even learned their real names. All I knew was that Alpha Spy Nest had turned my nightmare into a miracle, and I’d never click a shady link again.Contacts: WhatsApp: +14159714490 1
1 -
RECOVER MONEY LOST TO FAKE ONLINE SCAMMERS HIRE FUNDS RECLAIMER COMPANY
The cryptocurrency space, with its dizzying promises of financial freedom, had always intrigued me until it became the stage for my deepest disillusionment. Last year, I fell victim to an elaborate crypto scam that stripped me of years’ worth of savings. What began as a confident investment in a "guaranteed returns" scheme unraveled into a nightmare. Overnight, my portfolio vanished, along with the anonymous fraudsters who orchestrated the ploy. The aftermath was a toxic blend of anger, shame, and helplessness. I questioned every decision, replaying red flags I’d naively ignored. Crypto forums offered little solace, filled with eerily similar stories of irreversible losses. Just as I resigned myself to defeat, a glimmer of hope emerged: FUNDS RECLIAMER COMPANY. From the outset, their team stood apart by blending technical precision with unwavering compassion. Rather than treating my case as a faceless ticket, they approached it with a commitment to understanding the human toll of the scam. During initial consultations, they listened patiently to my story, offering reassurance that shifted my mindset from despair to cautious optimism. “These scams thrive on exploiting trust, not incompetence,” one advisor emphasized a perspective that dissolved my self-blame. FUNDS RECLIAMER COMPANY’s mastery of Cryptocurrencies forensics became evident as they untangled the digital maze of my stolen assets. They decoded how fraudsters manipulated wallet vulnerabilities and decentralized exchanges to obscure the trail, leveraging proprietary tools and cross platform collaborations to trace the funds. Over three days, their transparency became my anchor. Regular updates demystified their process, flagging suspicious transactions, and piecing together patterns linked to earlier scams. Challenges arose dead-end leads, unresponsive third parties but the team navigated each obstacle with tenacity. By second day, they’d recovered $350,000 of my assets. Beyond recovery, FUNDS RECLIAMER COMPANY prioritized empowerment. They equipped me with resources to safeguard future investments and connected me to a private forum of survivors, fostering a community of shared resilience. Today, I’m not only financially restored but fortified with hard-earned wisdom. My situation proves that loss isn’t always permanent. With cutting-edge expertise and relentless advocacy, redemption is attainable. Let my journey remind you: even in Cryptocurrency opaque wilderness, a path back exists and FUNDS RECLIAMER COMPANY lights the way.
FOR MORE INFO:
WhatsApp:+13612504110
Email: fundsreclaimercompany@ z o h o m a i l . c o m1 -
SEEKING EXPERT ASSISTANCE FOR CRYPTOCURRENCY RECOVERY HIRE ADWARE RECOVERY SPECIALIST
Losing $101,505 overnight was a gut-wrenching experience. One moment, my financial future seemed secure—the next, it had vanished. The investment platform I had trusted abruptly locked my account, citing vague “suspicious activity,” then fell completely silent. What followed was a nightmare of automated emails, chatbot loops, and unanswered phone calls. Customer service offered only scripted apologies, with no timeline or real support. I felt powerless, overwhelmed, and full of regret. How had I let this happen?
As painful as the experience was, it taught me invaluable lessons about financial vigilance. Website info: h t t p s:// adware recovery specialist. com
First, due diligence is non-negotiable. I had been swayed by sleek marketing and unrealistic promises of “guaranteed returns,” without properly investigating the platform’s credibility. Had I looked deeper, I would’ve uncovered troubling red flags—unverified claims, a murky operational history, and filtered reviews that masked real user experiences.
Second, if it sounds too good to be true, it probably is. Promises of high, consistent returns with “zero risk” should’ve triggered immediate skepticism. But in my urgency and greed, I ignored my instincts.
And third, responsive support is essential. When things went south, the absence of real human help made everything worse. Reputable financial platforms prioritize accountability and transparency—qualities this company clearly lacked. Email info: Adware recovery specialist @ auctioneer. net
My turning point came when I connected with ADWARE RECOVERY SPECIALIST, a firm that focuses on recovering cryptocurrency and digital assets. Though skeptical at first, I was desperate—and determined. I documented everything: transactions, emails, and conversations. Their team launched a thorough forensic audit, reached out to legal entities, and persistently followed up with payment processors. Incredibly, they recovered 92% of my funds—a remarkable win given the odds.
This ordeal has permanently reshaped how I approach finances. Today, I verify every platform through regulatory bodies, explore independent reviews, and test customer service responsiveness before investing. Risk management isn’t fear—it’s wisdom. Telegram info: h t t p s:// t. me / adware recovery specialist1
To anyone navigating the digital finance world: do your research, question flashy promises, and never overlook the importance of accountability. And if the worst happens, know that recovery is possible—especially with experienced professionals like ADWARE RECOVERY SPECIALIST in your corner.2 -
Losing $101,505 overnight felt like a gut wrenching blow. One moment, my financial future appeared stable; the next, it vanished into the ether. The platform I had trusted with my investments suddenly locked my account, citing vague “suspicious activity and then went silent. For days, I found myself trapped in a maze of automated emails, robotic chatbots, and unanswered phone calls. The so called customer service team offered nothing but scripted apologies, with no clear timeline for resolution. The weight of helplessness was overwhelming. How had I allowed this to happen? While this was harrowing, it transformed into a crucial lesson in financial vigilance. First and foremost, thorough research is essential. I had been seduced by polished marketing and enticing promises of guaranteed returns, neglecting to verify the platform’s legitimacy or investigate its leadership. A more in-depth examination would have unveiled warning signs: unregistered claims, a questionable operational history, and user reviews obscured by glowing testimonials. Secondly, if something appears too good to be true, it likely is. The platform’s pitch of consistent high returns with zero risk should have raised immediate red flags. My greed and urgency clouded my judgment, a mistake I am determined not to repeat.Most importantly, having access to responsive support is a necessity, not a luxury. When disaster struck, the lack of human assistance exacerbated the situation. Reputable institutions prioritize transparency and accountability qualities that were glaringly absent in this case.My path to recovery began with a referral to PYRAMID HACK SOLUTION, a firm specializing in Cryptocurrency asset recovery. Initially skeptical but desperate, I meticulously documented every transaction and communication, providing their team with the evidence. Their methodical approach included forensic audits, legal outreach, and persistent follow-ups with the platform’s payment processors. Remarkably, within weeks, they managed to recover 92% of my funds, a significant triumph given the circumstances.This ordeal has fundamentally altered my approach to financial decisions. I now cross-check companies against regulatory databases, explore independent review forums, and assess customer service responsiveness before investing a single dollar. Risk management is not paranoia; it’s a wise strategy.To anyone navigating the unpredictable realm of online finance: take a moment to pause, conduct thorough research, and prioritize actions over promises. And if disaster strikes, seek out specialists like PYRAMID HACK SOLUTION their recovery can make all the difference. CONTACT INFORMATIONS;
Email; pyramidhack @ solution4u. com
Telegram; @ PyramidhackSolution1
WhatsApp; +4474142809141 -
How can a Saclux Comptech Specialst help in recovering stolen or lost Bitcoin and other cryptocurrencies?
Saclux Comptech Specialst can help in recovering stolen or lost Bitcoin and other cryptocurrencies through various methods:
1. Investigation: The expert will conduct a thorough investigation to trace the stolen or lost funds. They will analyze blockchain transactions, digital footprints, and other relevant information to identify the culprits and track the funds.
2. Legal Assistance: If the theft or loss involves criminal activities, the recovery expert can work with law enforcement agencies and legal professionals to initiate legal proceedings against the perpetrators. They can provide evidence and expert testimony to support the case.
3. Negotiation: In some cases, the recovery expert may negotiate with the hackers or scammers to retrieve the stolen funds. They can use their expertise in dealing with cybercriminals and employ negotiation tactics to recover the assets.
4. Blockchain Analysis: The expert will analyze the blockchain network to identify any suspicious transactions or addresses associated with the stolen or lost funds. They can trace the movement of the funds and potentially locate the assets.
5. Asset Recovery Services: Saclux Comptech Specialst often have connections with specialized asset recovery services. These services can assist in recovering stolen or lost cryptocurrencies by utilizing their expertise, resources, and legal.1 -
I was scammed by an Instagram account pretending to be a celebrity. I engaged with this scammer for five months through WhatsApp and ended up sending money via Bitcoin. The scammer then coerced me into providing my banking login details, leading them to steal $20,000 from my unemployment funds. They convinced me that they had routed cash to my account, and they deliberately avoided giving me any time to verify this supposed transaction, ultimately taking advantage of my trust. Throughout this ordeal, the scammer was incredibly patient and manipulative, waiting for eight months before I finally became suspicious and decided to expose them.
I made a video on WhatsApp detailing the scam, hoping it would help others avoid falling into the same trap. However, by then, my financial situation had become dire. The scammer demanded that I send Bitcoin via an ATM, continuing their deception even as I sought a resolution. Fortuitously, just as I was nearing desperation, I discovered BOTNET CRYPTO RECOVERY.
They stepped in at a crucial moment and managed to recover my $20,000. Their timely intervention and expertise in fund recovery proved to be a lifesaver.
The team at BOTNET CRYPTO RECOVERY is truly skilled in their field, demonstrating an impressive capability to not only recover stolen funds but also to expose and dismantle scam operations. Their service was exceptional. They provided clear communication and actionable strategies, working diligently to ensure that my money was returned. The recovery process was handled with the utmost professionalism and efficiency. Seeing my funds returned was a huge relief, and it was evident that BOTNET CRYPTO RECOVERY was well-versed in handling such complex and sensitive situations. I have since recommended BOTNET CRYPTO RECOVERY to several friends and colleagues, all of whom have been equally impressed with their services. They have become my go-to recommendation for anyone dealing with similar issues, whether it involves recovering lost funds or addressing various online scams. Their expertise extends beyond just recovery; they offer comprehensive solutions for individuals and businesses facing financial fraud.
BOTNET CRYPTO RECOVERY’s ability to address both hacking and fund recovery issues has been invaluable to me. They have various skills and strategies for tackling these challenges, and their success in helping me recover my stolen funds speaks volumes about their capabilities. They approach each case with a unique strategy tailored to the specifics of the situation, ensuring the best possible outcome for their clients. Reflecting on my experience, I am immensely grateful for the intervention of BOTNET CRYPTO RECOVERY. Their support has not only helped me regain my lost funds but also provided me peace of mind during a highly stressful period.
The professionalism and dedication demonstrated by their team have solidified my confidence in their services. If you find yourself in a situation involving financial fraud or scams, I highly recommend reaching out to BOTNET CRYPTO RECOVERY. Their proven track record and specialized expertise make them a top choice for recovering stolen funds and tackling online scams. They have been instrumental in my financial recovery, and their assistance has made a significant difference in my life.
EMAIL THEM: chat@botnetcryptorecovery.info






