Join devRant
Do all the things like
++ or -- rants, post your own rants, comment on others' rants and build your customized dev avatar
Sign Up
Pipeless API

From the creators of devRant, Pipeless lets you power real-time personalized recommendations and activity feeds using a simple API
Learn More
Search - "password be like"
-
I had a secondary Gmail account with a really nice short nickname (from the early invite/alpha days), forwarded to another of my mailboxes. It had a weak password, leaked as part of one of the many database leaks.
Eventually I noticed some dude in Brazil started using my Gmail, and he changed the password — but I still got a copy of everything he did through the forwarding rule. I caught him bragging to a friend on how he cracked hashes and stole and sold email accounts and user details in bulk.
He used my account as his main email account. Over the years I saw more and more personal details getting through. Eventually I received a mail with a plaintext password... which he also used for a PayPal account, coupled to a Mastercard.
I used a local website to send him a giant expensive bouquet of flowers with a box of chocolates, using his own PayPal and the default shipping address.
I included a card:
"Congratulations on acquiring my Gmail account, even if I'm 7 years late. Thanks for letting me be such an integral part of your life, for letting me know who you are, what you buy, how much you earn, who your family and friends are and where you live. I've surprised your mother with a cruise ticket as you mentioned on Facebook how sorry you were that you forgot her birthday and couldn't buy her a nice present. She seems like a lovely woman. I've also made a $1000 donation in your name to the EFF, to celebrate our distant friendship"31 -
So, since I hear from a lot of people (on here and irl) that Linux has a 'very high learning curve', let me share my experiences with the first time my dad touched Linux (Elementary OS) without me interfering at all! (keep in mind that he is very a-technical)
*le me boots the system* (I already did setup a user account for him and gave him the password).
Dad: *enters password and presses enter*
Me: "Hmm that went faster than expected."
Dad: "Uhm I know how to login son, it's not that hard and pretty obvious".
Me: "Alright, why don't you try to open up the default word documents editor on here! I'll be right back!"
Me: *Goes away and returns after a minute*.
Dad: *already a few test sentences typed in LibreOffice writer* it's going pretty well :)!
Me: "Oo how did you find that?!"
Dad: "Well, there's a thingy that says 'applications' so I clicked in and found it in the "Office" section, do you think I am blind or something?!"
Me: 😐. uhm no but I just didn't think you'd find it that quickly. Now try to install Chromium browser! *thinking: he'll fail this one for sure* I'll be right back :).
Me: *returns again after a minute or so*
Dad: *already searching for stuff through Chromium*
Me: "wait, how the hell did you do that so quickly, it's not the easiest thingy for most people".
Dad: "Jesus, it's not that hard! I went to the application browsing thingy, typed 'software' and then a sorta software store icon showed up so I clicked it and it opened a windows with a search bar saying something like 'search for applications/software'. clicked in it, typed 'chromium', saw it coming up, there was a very clear 'install' button, it asked for my password, I put it in and after a little it gave a notification that it was installed. Then I went to that application browsing thingy again and typed Chromium. Then I hit enter because it selected an icon called chromium...."
Me: O.o. Okay this is going very good, now open an email client and login to your email address!
Dad: *goes to application browsing thingy, types 'email', evolution icon shows up, dad clicks it, email address setup steps show up and dad follows them quickly. After about a minute, everything is setup.
I expected this to be a hard process for someone who dealt with Windows his entire life but damn, I underestimated it.
Asked him if he found it easy/what he liked about it:
"Well, it's very clear where I can find everything, default browser/email/word document editor programs are easy to find and that's about all I need so yeah, great system!"
I am proud of you, dad!77 -
Imagine what a coder Gordon Ramsay might be like:
Your alghoritm is so FUCKING slow, I'd rather to try to brute force a 20 characters long alphanumeric password!
This app is more insecure than an average teenager!
If your code was a spaghetti it would be a fucking health hazard!14 -
So a friend of Mine asked me to check their Mail server because some emails got lost. Or had a funny signature.
Mails were sent from outlook so ok let's do this.
I go create a dummy account, and send/receive a few emails. All were coming in except one and some had a link appended. The link was randomly generated and was always some kind of referral.
Ok this this let's check the Mail Server.
Nothing.
Let's check the mail header. Nothing.
Face -> wall
Fml I want to cry.
Now I want to search for a pattern and write a script which sends a bunch of mails on my laptop.
Fuck this : no WLAN and no LAN Ports available. Fine let's hotspot the phone and send a few fucking mails.
Guess what? Fucking cockmagic, no funny mails appear!
At that moment I went out and was like chainsmoking 5 cigarettes.
BAM!
It hit me! A feeling like a unicorn vomiting rainbows all over my face.
I go check their firewall. Shit redirected all email ports from within the network to another server.
Yay nobody got credentials because nobody new it existed. Damn boy.
Hook on to the hostmachine power down the vm, start and hack yourself a root account before shit boots. Luckily I just forgot the credentials to a testvm some time ago so I know that shit. Lesson learned: fucking learn from your mistakes, might be useful sometimes!
Ok fucker what in the world are you doing.
Do some terminal magic and see that it listens on the email ports.
Holy cockriders of the galaxy.
Turns out their former it guy made a script which caught all mails from the server and injected all kind of bullshit and then sent them to real Webserver. And the reason why some mails weren't received was said guy was too dumb to implement Unicode and some mails just broke his script.
That fucker even implented an API to pull all those bullshit refs.
I know your name "Matthias" and I know where you live and what you've done... And to fuck you back for that misery I took your accounts and since you used the same fucking password for everything I took your mail, Facebook and steam account too.
Git gut shithead! You better get a lawyer15 -
"your password must contain a capital letter, two numbers, a symbol, an inspiring message, CV, a gang sign, a dragon blood"
 7
7 -
So my actual job is being a nurse at the local hospital, with coding being just a hobby. However, the way some IT–Related things are treated here are just mind-blowing. Here are some examples:
Issue: Printer is not recognized by network anymore due to not being properly plugged in
Solution: Someone has to tell the house technician, if the house technician is currently not available, ask his assistant who only works part time and like twice a week. House technician took the printer (God knows why), came back 2 days later and plugged it back in.
Issue: Printer 1 of 2 on ICU has run out of ink and since all computers default to printer 1, nobody can print.
Solution: Call the house technician, blah blah, house technician comes, takes ink cartridge of printer 2 and puts it into printer 1.
Issue: Public WiFi is broken, can be connected to but internet access is missing. Probably config issue as a result of a recent blackout.
Solution: Buy a new router, spend 5 days configuring it and complain about how hard networking is.
Issue: Computer is broken, needs to be exchanged with a new one, but how do we transfer the data?
Solution: Instead of just keeping the old hard drive, make a 182GB backup, upload it to the main file server and then download it again on the new computer.
Issue: Nurse returns from vacation, forgot the password to her network account.
Solution: Call the technician who then proceeds to open a new account, copies all the files from the old one and tells her to pick an easier password this time. She chooses "121213".12 -
I was 15 years old and the first year of high school. Everything was new to me and I was such a newbie. At that time I had 2-3 year of programming behind me at an institution where they taught competitive programming. And I knew something about computers. Not much but more than most of my school mates. At that time I wanted to become "super cool hacker".
So we had this very very thought teacher for history which was also our form master. She really knows how to explained everything about history and in an interesting way. But while she was teaching we also had to write down notes from her powerpoints that were on a projector. And occasionally she would wait for us to copy everything and then move on with her lecture. But sometimes she didn't. This was frustrating as hell. The whole class would complain about this because you couldn't take notes down normal, you had to do it at double speed.
But she got one weak spot. She was not very good with computers. Our school computers were locked in some kinda closet so that students didn't have physical access to a computer and were also password protected. So I came up with the plan to plant wireless mouse in her computer so that I could control her mouse. At that time it seemed like SUPER HACKER MASTER PLAN.
So I got an opportunity one time when she left the classroom and let closet where the computer was open. I quickly sneaked the USB of the wireless mouse in the computer and then go back to the seat.
So THE FUN began.
Firstly I would only go back in powerpoint so that all my schoolmates could write down notes including me. And it was hilarious to watch when she didn't know what is happening. So then I would move her mouse when she tried to close some window. I would just move it slightly so she wouldn't notice that somebody else is controlling mouse. And by missing X button just by slight she would click other things and other things would pop up and now she had to close this thing so it became a nightmare for her. And she would become angry at the mouse and start complaining how the computer doesn't work and that mouse doesn't obey her.
One time when she didn't pay attention to her computer and projector I went to paint program and drew a heart and wrote we love you (In Slovenian Imamo vas radi -> See the picture below) and one of my school mates has the picture of it. We were all giggling and she didn't know what is was for. And I managed to close everything before she even noticed.
So it got to the point where she couldn't hand it more so she called our school IT guy so that he would check her computer (2 or 3 weeks passed before she called IT guy). And he didn't find anything. He was really crappy IT guy in general. So one week passed by and I still had messed with her mouse. So she got a replacement computer. Who would guessed all the problems went away (because I didn't have another mouse like that). I guess when our IT guy took the computer to his room and really thoroughly check it he found my USB.
So he told her what was the problem she was so pissed off really I didn't see her pissed off so much in all my 4 years in high school. She demanded the apology from whom did it. And at that moment my mind went through all possible scenarios... And the most likely one was that I was going to be expelled... And I didn't have the balls to say that I did it and I was too afraid... Thanks to God nobody from my school mates didn't tell that it was me.
While she waited that somebody would come forward there was one moment when our looks met and at that moment both of us knew that I was the one that did it.
Next day the whole class wrote the apology letter and she accepted it. But for the rest of 4 years whenever was there a problem with the computer I had to fixed it and she didn't trust anybody not even our IT guy at school. It was our unwritten contract that I would repair her computer to pay off my sin that I did. And she once even trusted me with her personal laptop.
So to end this story I have really high respect for her because she is a great teacher and great persons that guide me through my teen years. And we stayed in contact.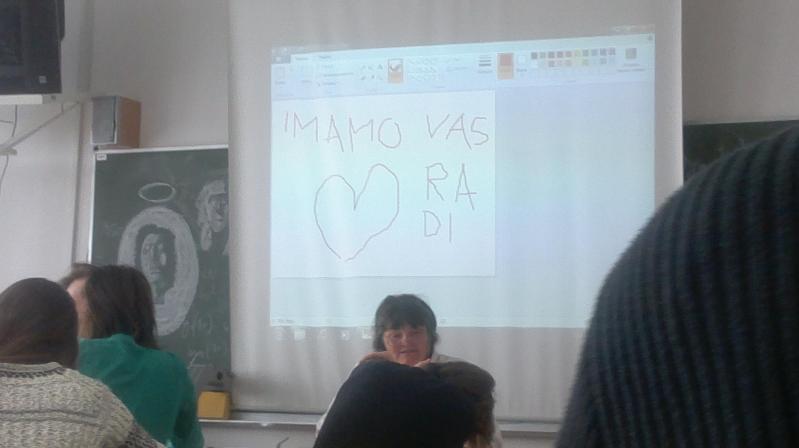 11
11 -
Short story time.
The last girl I dated was a proper geek. Like the kind of geek another geek wants. So one fine day she told me that she was making a greeting card for me. I was happy. After a few weeks she gave me the card and it was really cute. I loved it.
I reached home and received an email from her with a link in it. It was the link to a website she had made where each message from the card was deciphered to the real message.
DAAAAMNNN😱😱
That wasn't all. She didn't want the entire thing to be too easy. So the deciphered messages were password protected and I had to guess it.20 -
Was at my sisters place a little ago and somehow we came at the subject of her laptop.
For everyone who thinks I'm posting this solely to hate on windows, I'm not. This really happened and if you don't believe it, well, so be it, I guess.
Also keep in mind that's she's using a stock version without anything except for word and itunes installed.
She got it a couple of years ago and I dual booted it for her (windows + ubuntu). I fully expected her to use windows because of office and outlook etc.
Asked her anyways:
Me: So, you've got dual boot, although I think already know the answer, what system do you use mostly? (I didn't even consider that there was a possibility that the answer would be ubuntu or linux)
Sister: Ubuntu!
Me:
Me:
Me:
Me:
Me:
Me:
Me:
Me: 😵
Me: Sorry, what? You're not using windows as primary system?!
Sister: No. It at first takes that motherfucking system about 5 minutes to reach the FUCKING LOGIN SCREEN.
Me: Ow, that's bad :/
Me: *turns laptop on and indeed, it takes a fuckton of time*
Me: Is the password still the same as when I set it up for you?
Sister: Yesss.
Me: *types the password, it's working, loading screen appears*
Sister: Would you like a coffee?
Me: Uhm.... sure? But that would take you about 10-15 minutes to make.......?
Sister: Yes. And that's exactly how long it takes before that fucking piece of shit called windows has finally loaded the FUCKING DESKTOP.
Me: 😅
Me: Okay but it can't be that bad, right? I mean, I hate windows but you mostly need it for studies and such and as you know I'm not judging you for tha......
Sister: YES IT IS THAT FUCKING BAD. WHEN I'M IN CLASS, IT TAKES HALF THE FUCKING CLASS TO LOAD BEFORE I CAN OPEN WORD OR WHAT-THE-FUCK EVER.
THAT'S WHY I USE UBUNTU PRIMARILY, BECAUSE, ALTOUGH IT'S NOT MY FAVOURITE SYSTEM, IT. JUST. FUCKING. WORKS.
Well, I did definitely NOT see that one coming!
There is some bloatware on there but definitely as bad as what would cause this. Virus scan turned up empty. No. Fucking. Clue.
It's not a gaming laptop or anything but come on, it should run either windows or linux very well.51 -
Mam: Hey can I ask you a question about Facebook?
Me: (Christ give me strength) ... sure whats up?
Mam: You know when you get a notification and you click on it and see what someone uploaded?
Me: ... you are not on Facebook, you can't be getting notifications
Mam: well I do. Is it possible to...
Me: No hang on a second, it is 110% not possible for this to happen. Something else is going on that you think is a notification.
Mam: You know when you are on, and you see a message like "12 new notifications"
Me: on? on what? this is happening on your phone is it? Can I see?
Mam: No its on my laptop at home.
Me: ... you have an old laptop with an old windows, you can't get notifications on it.
Mam: OH FOR GOD SAKE! ... you know when you are in your emails and it says "12 new notifications"?
Me: ... right so we are talking about EMAILS about unread notifications and not getting notifications on your phone. So you have an old account then that you don't use?
Mam: Yeah I don't know the password to it, haven't logged in, in years.
Me: of course
Mam: Right anyway. When I get one and click on it, lets say its about you, can you see me reading your notifications?
Me: ..... you can't not read my notifications.
Mam: uh, can you see me reading your emails then smart arse?
Me: ... can't do that either.
Mam: So what the hell am I doing then?
Me: You are reading a post someone uploaded, which you got alerted to from an email.
Mam: Right, can you tell when I've read your POST then?!?!?!
Me: no
Mam: was that so hard?
Me: ... yep7 -
Sister = bee ( who isn't a stranger to Ubuntu)
Me = Cee
Bee: can I use your laptop?
Cee : why ? Use yours ,it's works fine.
Bee : no I want to use yours and I need to work with windows.
Cee: 🤯
Bee : my work can only be done using windows.
Cee : fine do whatever ( doesn't want to argue )
* Le bee opens MS word, and starts her work *
Cee : 😤😤Seriously?
Bee : I don't like libre
Cee : 😑😑😑^∞
* Few moments later *
Bee : my work is done ,you can have your laptop,btw it's updating.
Cee : 😑😑😑😑😑
* 2000 years later *
*Opens Ubuntu *
*Getting a weird bug*
*Tried to fix *
*Can't open OS files * 👏👏👏🎆
* Windows not shutdown properly *
* Opens windows *
* Not able to login via pin *
* Password ? not accepted *
* Changes outlook password *
* Please chose a password you haven't chosen before *
* Logs in *
* types old pin to change pin *
*You've entered wrong pin too many times *
*System hanging a lot *
* Removes pin *
* Gets huge mcAfee restart system popups , every 10 sec *
* Just shutdown , feels irritated for the rest of the day*
* Regrets dual booting, shd have wiped the windows partition 😫😫*
*Wonders,what the hell did my sister even do to my laptop ?*72 -
Navy story continued.
And continuing from the arp poisoning and boredom, I started scanning the network...
So I found plenty of WinXP computers, even some Win2k servers (I shit you not, the year was 201X) I decided to play around with merasploit a bit. I mean, this had to be a secure net, right?
Like hell it was.
Among the select douchebags I arp poisoned was a senior officer that had a VERY high idea for himself, and also believed he was tech-savvy. Now that, is a combination that is the red cloth for assholes like me. But I had to be more careful, as news of the network outage leaked, and rumours of "that guy" went amok, but because the whole sysadmin thing was on the shoulders of one guy, none could track it to me in explicit way. Not that i cared, actually, when I am pissed I act with all the subtleness of an atom bomb on steroids.
So, after some scanning and arp poisoning (changing the source MAC address this time) I said...
"Let's try this common exploit, it supposedly shouldn't work, there have been notifications about it, I've read them." Oh boy, was I in for a treat. 12 meterpreter sessions. FUCKING 12. The academy's online printer had no authentication, so I took the liberty of printing a few pages of ASCII jolly rogers (cute stuff, I know, but I was still in ITSec puberty) and decided to fuck around with the other PCs. One thing I found out is that some professors' PCs had the extreme password of 1234. Serious security, that was. Had I known earlier, I could have skipped a TON of pointless memorising...
Anyway, I was running amok the entire network, the sysad never had a chance on that, and he seemed preoccupied with EVERYTHING ELSE besides monitoring the net, like fixing (replacing) the keyboard for the commander's secretary, so...
BTW, most PCs had antivirus, but SO out of date that I didn't even need to encode the payload or do any other trick. An LDAP server was open, and the hashed admin password was the name of his wife. Go figure.
I looked at a WinXP laptop with a weird name, and fired my trusty ms08_067 on it. Passowrd: "aaw". I seriously thought that Ophcrack was broken, but I confirmed it. WTF? I started looking into the files... nothing too suspicious... wait a min, this guy is supposed to work, why his browser is showing porn?
Looking at the ""Deleted"" files (hah!) I fount a TON of documents with "SECRET" in them. Curious...
Decided to download everything, like the asshole I am, and restart his PC, AND to leave him with another desktop wallpaper and a text message. Thinking that he took the hint, I told the sysadmin about the vulnerable PCs and went to class...
In the middle of the class (I think it was anti-air warfare or anti-submarine warfare) the sysad burst through the door shouting "Stop it, that's the second-in-command's PC!".
Stunned silence. Even the professor (who was an officer). God, that was awkward. So, to make things MORE awkward (like the asshole I am) I burned every document to a DVD and the next day I took the sysad and went to the second-in-command of the academy.
Surprisingly he took the whole thing in quite the easygoing fashion. I half-expected court martial or at least a good yelling, but no. Anyway, after our conversation I cornered the sysad and barraged him with some tons of security holes, needed upgrades and settings etc. I still don't know if he managed to patch everything (I left him a detailed report) because, as I've written before, budget constraints in the military are the stuff of nightmares. Still, after that, oddly, most people wouldn't even talk to me.
God, that was a nice period of my life, not having to pretend to be interested about sports and TV shows. It would be almost like a story from highschool (if our highschool had such things as a network back then - yes, I am old).
Your stories?8 -
Dev : Every user in your organisation requires their own username and password...
User: Why?
Dev: Because if everyone uses one account, every note, product, message etc made by all the user's will be saved to that one account and confuse the he'll out of everyone using it when they can't find their 'own' information they made/captured/downloaded.
We just need the user emails.
User:We can't give you all the user emails just use one account ....
(The reason for not providing us the emails is purely cause it would require user to do work and that's out of the question)
Dev: Uhm ok, but this is not what you want, and *interrupts*
User: It is what we want, do it like that everyone will understand and it will make the system easier.
*Two weeks later*
User: Why is there only one account? Why doesn't everybody have their own account? This is not what we wanted.
... The shit you have to deal with when you are on holiday ...undefined where to hide bodies you still thing it's our fault working even when i'm not working i was right and you were wrong stil my fucking problem6 -
I really, honestly, am getting annoyed when someone tells me that "Linux is user-friendly". Some people seem to think that because they themselves can install Linux, that anyone can, and because I still use Windows I'm some sort of a noob.
So let me tell you why I don't use Linux: because it never actually "just works". I have tried, at the very least two dozen times, to install one distro or another on a machine that I owned. Never, not even once, not even *close*, has it installed and worked without failing on some part of my hardware.
My last experience was with Ubuntu 17.04, supposed to have great hardware and software support. I have a popular Dell Alienware machine with extremely common hardware (please don't hate me, I had a great deal through work with an interest-free loan to buy it!), and I thought for just one moment that maybe Ubuntu had reached the point where it just, y'know, fucking worked when installing it... but no. Not a chance.
It started with my monitors. My secondary monitor that worked fine on Windows and never once failed to display anything, simply didn't work. It wasn't detected, it didn't turn on, it just failed. After hours of toiling with bash commands and fucking around in x conf files, I finally figured out that for some reason, it didn't like my two IDENTICAL monitors on IDENTICAL cables on the SAME video card. I fixed it by using a DVI to HDMI adapter....
Then was my sound card. It appeared to be detected and working, but it was playing at like 0.01% volume. The system volume was fine, the speaker volume was fine, everything appeared great except I literally had no fucking sound. I tried everything from using the front output to checking if it was going to my display through HDMI to "switching the audio sublayer from alsa to whatever the hell other thing exists" but nothing worked. I gave up.
My mouse? Hell. It's a Corsair Gaming mouse, nothing fancy, it only has a couple extra buttons - none of those worked, not even the goddamn scrollwheel. I didn't expect the *lights* to work, but the "back" and "Forward" buttons? COME ON. After an hour, I just gave up.
My media keyboard that's like 15 years old and is of IBM brand obviously wasn't recognized. Didn't even bother with that one.
Of my 3 different network adapters (2 connectors, one wifi), only one physical card was detected. Bluetooth didn't work. At this point I was so tired of finding things that didn't work that I tried something else.
My work VPN... holy shit have you ever tried configuring a corporate VPN on Linux? Goddamn. On windows it's "next next next finish then enter your username/password" and on Linux it's "get this specific format TLS certificate from your IT with a private key and put it in this network conf and then run this whatever command to...." yeah no.
And don't get me started on even attempting to play GAMES on this fucking OS. I mean, even installing the graphic drivers? Never in my life have I had to *exit the GUI layer of an OS* to install a graphic driver. That would be like dropping down to MS-DOS on Windows to install Nvidia drivers. Holy shit what the fuck guys. And don't get me started on WINE, I ain't touching this "not an emulator emulator" with a 10-foot pole.
And then, you start reading online for all these problems and it's a mix of "here are 9038245 steps to fix your problem in the terminal" and "fucking noob go back to Windows if you can't deal with it" posts.
It's SO FUCKING FRUSTRATING, I spent a whole day trying to get a BASIC system up and running, where it takes a half-hour AT MOST with any version of Windows. I'm just... done.
I will give Ubuntu one redeeming quality, however. On the Live USB, you can use the `dd` command to mirror a whole drive in a few minutes. And when you're doing fucking around with this piece of shit OS that refuses to do simple things like "playing audio", `dd` will restore Windows right back to where it was as if Ubuntu never existed in the first place.
Thanks, `dd`. I wish you were on Windows. Your OS is the LEAST user friendly thing I've ever had to deal with.31 -
Worst thing you've seen another dev do? So many things. Here is one...
Lead web developer had in the root of their web application config.txt (ex. http://OurPublicSite/config.txt) that contained passwords because they felt the web.config was not secure enough. Any/all applications off of the root could access the file to retrieve their credentials (sql server logins, network share passwords, etc)
When I pointed out the security flaw, the developer accused me of 'hacking' the site.
I get called into the vice-president's office which he was 'deeply concerned' about my ethical behavior and if we needed to make any personnel adjustments (grown-up speak for "Do I need to fire you over this?")
Me:"I didn't hack anything. You can navigate directly to the text file using any browser."
Dev: "Directory browsing is denied on the root folder, so you hacked something to get there."
Me: "No, I knew the name of the file so I was able to access it just like any other file."
Dev: "That is only because you have admin permissions. Normal people wouldn't have access"
Me: "I could access it from my home computer"
Dev:"BECAUSE YOU HAVE ADMIN PERMISSIONS!"
Me: "On my personal laptop where I never had to login?"
VP: "What? You mean ...no....please tell me I heard that wrong."
Dev: "No..no...its secure....no one can access that file."
<click..click>
VP: "Hmmm...I can see the system administration password right here. This is unacceptable."
Dev: "Only because your an admin too."
VP: "I'll head home over lunch and try this out on my laptop...oh wait...I left it on...I can remote into it from here"
<click..click..click..click>
VP: "OMG...there it is. That account has access to everything."
<in an almost panic>
Dev: "Only because it's you...you are an admin...that's what I'm trying to say."
Me: "That is not how our public web site works."
VP: "Thank you, but Adam and I need to discuss the next course of action. You two may go."
<Adam is her boss>
Not even 5 minutes later a company wide email was sent from Adam..
"I would like to thank <Dev> for finding and fixing the security flaw that was exposed on our site. She did a great job in securing our customer data and a great asset to our team. If you see <Dev> in the hallway, be sure to give her a big thank you!"
The "fix"? She moved the text file from the root to the bin directory, where technically, the file was no longer publicly visible.
That 'pattern' was used heavily until she was promoted to upper management and the younger webdev bucks (and does) felt storing admin-level passwords was unethical and found more secure ways to authenticate.5 -
I'm trying to sign up for insurance benefits at work.
Step 1: Trying to find the website link -- it's non-existent. I don't know where I found it, but I saved it in keepassxc so I wouldn't have to search again. Time wasted: 30 minutes.
Step 2: Trying to log in. Ostensibly, this uses my work account. It does not. Time wasted: 10 minutes.
Step 3: Creating an account. Username and Password requirements are stupid, and the page doesn't show all of them. The username must be /[A-Za-z0-9]{8,60}/. The maximum password length is VARCHAR(20), and must include upper/lower case, number, special symbol, etc. and cannot include "password", repeated charcters, your username, etc. There is also a (required!) hint with /[A-Za-z0-9 ]{8,60}/ validation. Want to type a sentence? better not use any punctuation!
I find it hilarious that both my username and password hint can be three times longer than my actual password -- and can contain the password. Such brilliant security.
My typical username is less than 8 characters. All of my typical password formats are >25 characters. Trying to figure out memorable credentials and figuring out the hidden complexity/validation requirements for all of these and the hint... Time wasted: 30 minutes.
Step 4: Post-login. The website, post-login, does not work in firefox. I assumed it was one of my many ad/tracker/header/etc. blockers, and systematically disabled every one of them. After enabling ad and tracker networks, more and more of the site loaded, but it always failed. After disabling bloody everything, the site still refused to work. Why? It was fetching deeply-nested markup, plus styling and javascript, encoded in xml, via api. And that xml wasn't valid xml (missing root element). The failure wasn't due to blocking a vitally-important ad or tracker (as apparently they're all vital and the site chain-loads them off one another before loading content), it's due to shoddy development and lack of testing. Matches the rest of the site perfectly. Anyway, I eventually managed to get the site to load in Safari, of all browsers, on a different computer. Time wasted: 40 minutes.
Step 5: Contact info. After getting the site to work, I clicked the [Enroll] button. "Please allow about 10 minutes to enroll," it says. I'm up to an hour and 50 minutes by now. The first thing it asks for is contact info, such as email, phone, address, etc. It gives me a warning next to phone, saying I'm not set up for notifications yet. I think that's great. I select "change" next to the email, and try to give it my work email. There are two "preferred" radio buttons, one next to "Work email," one next to "Personal email" -- but there is only one textbox. Fine, I select the "Work" preferred button, sign up for a faux-personal tutanota email for work, and type it in. The site complains that I selected "Work" but only entered a personal email. Seriously serious. Out of curiosity, I select the "change" next to the phone number, and see that it gives me four options (home, work, cell, personal?), but only one set of inputs -- next to personal. Yep. That's amazing. Time spent: 10 minutes.
Step 6: Ranting. I started going through the benefits, realized it would take an hour+ to add dependents, research the various options, pick which benefits I want, etc. I'm already up to two hours by now, so instead I decided to stop and rant about how ridiculous this entire thing is. While typing this up, the site (unsurprisingly) automatically logged me out. Fine, I'll just log in again... and get an error saying my credentials are invalid. Okay... I very carefully type them in again. error: invalid credentials. sajfkasdjf.
Step 7 is going to be: Try to figure out how to log in again. Ugh.
"Please allow about 10 minutes" it said. Where's that facepalm emoji?
But like, seriously. How does someone even build a website THIS bad?rant pages seriously load in 10+ seconds slower than wordpress too do i want insurance this badly? 10 trackers 4 ad networks elbonian devs website probably cost $1million or more too root gets insurance stop reading my tags and read the rant more bugs than you can shake a stick at the 54 steps to insanity more bugs than master of orion 312 -
Friend of mine killed his MacBook with some Softdrink.
Just poured it all over his poor a1502.
He let it dry for a few days, it starts to work again.
Except the battery.
Goes on Amazon and buys a new battery.
New battery doesn't work either and so he tells me about it and I as stupid as I am couldn't resist the temptation to finally work on a MacBook like my "hero" Lois Rossmann does.
So turns out the board is good.
Cleaned it up and basically nothing happened to it.
So what's the deal with "los batlerias"?
The first got hit by liquid, the second had a broken connection to a cell.
That could have happened through my friend, installing it without testing it first, or at the seller, so it being a DOA battery.
Now away from the stupidity of my friend and the situation to the actual source for this rant.
Once something happens to a modern Managed battery, the Battery Management System (BMS) disconnects the voltage from the system and goes into an error state, staying there and not powering anything ever again.
For noobs, it's dead. Buy a new one.
But It can be reset, depending you know how to, and which passwords were set at the factory.
Yes, the common Texas instruments BQ20Zxx chips have default passwords, and apple seems to leav them at default.
The Usb to SMBus adaptors arrived a few days ago and I went to prod the BMS.
There is a very nice available for Windows called BE2works, that I used the demo of to go in and figure out stuff. The full version supports password cracking, the demo not.
After some time figuring out how Smart Battery Systems (SBS) "API" works, I got to actually enter the passwords into the battery to try get into manufacturer and full access mode.
Just to realise, they don't unlock the BMS.
So, to conclude, my friend bought a "new" battery that was most likely cut out of a used / dead macbook, which reports 3000mah as fully charged instead of the 6xxx mah that it should have, with 0 cycles and 0hours used.
And non default access.
This screams after those motherfuckers scaming the shit out of people on Amazon, with refurb, reset, and locked fucken batteries.
I could kill those people right now.
Last but not least,
My friend theoretically can't send it back because I opened the battery to fix the broken connection.
Though maybe, it'll get send back anyway, with some suprise in the package.9 -
I imagine those researcher must be like : "Would you give us your password? It's for a research project"
 3
3 -
Insecure... My laptop disk is encrypted, but I'm using a fairly weak password. 🤔
Oh, you mean psychological.
Working at a startup in crisis time. Might lose my job if the company goes under.
I'm a Tech lead, Senior Backender, DB admin, Debugger, Solutions Architect, PR reviewer.
In practice, that means zero portfolio. Truth be told, I can sniff out issues with your code, but can't code features for shit. I really just don't have the patience to actually BUILD things.
I'm pretty much the town fool who angrily yells at managers for being dumb, rolls his eyes when he finds hacky code, then disappears into his cave to repair and refactor the mess other people made.
I totally suck at interviews, unless the interviewer really loves comparing Haskell's & Rust's type systems, or something equally useless.
I'm grumpy, hedonistic and brutally straight forward. Some coworkers call me "refreshing" and "direct but reasonable", others "barely tolerable" or even "fundamentally unlikable".
I'm not sure if they actually mean it, or are just messing with me, but by noon I'm either too deep into code, or too much under influence of cognac & LSD, wearing too little clothing, having interesting conversations WITH instead of AT the coffee machine, to still care about what other humans think.
There have been moments where I coded for 72 hours straight to fix a severe issue, and I would take a bullet to save this company from going under... But there have also been days where I called my boss a "A malicious tumor, slowly infecting all departments and draining the life out of the company with his cancerous ideas" — to his face.
I count myself lucky to still have a very well paying job, where many others are struggling to pay bills or have lost their income completely.
But I realize I'm really not that easy to work with... Over time, I've recruited a team of compatible psychopaths and misfits, from a Ukranian ex-military explosives expert & brilliant DB admin to a Nigerian crossfitting gay autist devops weeb, to a tiny alcoholic French machine learning fanatic, to the paranoid "how much keef is there in my beard" architecture lead who is convinced covid-19 is linked to the disappearance of MH370 and looks like he bathes in pig manure.
So... I would really hate to ever have to look for a new employer.
I would really hate to ever lose my protective human meat shield... I mean, my "team".
I feel like, despite having worked to get my Karma deep into the red by calling people all kinds of rude things, things are really quite sweet for me.
I'm fucking terrified that this peak could be temporary, that there's a giant ravine waiting for me, to remind me that life is a ruthless bitch and that all the good things were totally undeserved.
Ah well, might as well stay in character...
*taunts fate with a raised middlefinger*13 -
My first poem for programmer girl 😘😘😘
My life is incomplete without you,
You are semicolon of my life
You are my increment operator,
you make my value increases
I am username and you are my password,
without you No one can access me
You are my initializer,
without you my life would point to nothing (NULL or “0”)
If I were a function you must be my parameter,
Because I will always need you
Can you be my private variable?
I want to be only one who can access you
You are my compiler,
My life wouldn’t start without you
You are my loop condition ,
I keep coming back to you
My love to you is like recursive function,
It will never ends & Will never enter into infinite loop
Forever and Ever10 -
TL;DR: Fuck you Apple.
10:30 PM, parent needs iPhone update to update Messenger. How hard can this be?
Need to update iPhone from 9.x to latest, which is so outdated it still required iTunes. Fk.
Boot iTunes on Windows 10 pc that is at least 10 years old.
Completely unresponsive
Crash in task manager
Launch and is completely unresponsive. (Also starts playing unrequested music.. Oh joy..)
Fuck this, go to apple.com to download iTunes exe
Gives me some Microsoft store link. Fuck that shit, just give me the executable
Google “iTunes download”. click around on shitty Apple website. Success.
Control panel. Uninstall iTunes. (Takes forever, but it works)
Restart required (of fucking course).
2 eternities later. Run iTunes exe. Restart required. Fk.
Only 1 eternity later. Run iTunes, connect iPhone.
Actually detects the device. (holy shit, a miracle)
Starts syncing an empty library to the phone. Ya, fuck that.
Google. Disable option. Connect phone. Find option to update.
Update started. Going nowhere fast. Time for a walk at 1:00 AM punching the air.
Come back. Generic error message: Update failed (-1). Phone is stuck installing update. (O shit)
1x hard reset
2x hard reset
Google. Find Apple forum with exact question. Absolutely useless replies. (I expected no less)
Google recovery mode. Get into recovery mode.
Receive message: “You can update, but if it fails, you will have to reset to factory settings”. Fuck it, here we go.
Update runs (faster this time). Fails again. Same bullshit error message. (Goddammit, fuck. This might actually be bad.)
Disconnect phone.
… It boots latest iOS version. (holy shit, there is a god)
Immediately kill iTunes. Fuck that shit.
Parents share Apple account
Sign in, 2FA required.
Fat finger the code.
Restart “welcome” process.
Will not send code. What. The. Fuck.
Requests access code on other parent’s iPhone.
No code present. What???
Try restarting welcome process again. No dice. (Of course)
Set code on other parent’s iPhone.
Get message “Code is easy to guess”. Ya. IDGAF
Use code on newly updated iPhone. Some success.
Requires reset of password.
Password cannot be the same as old password (Goddammit)
Change password.
Welcome process done.
Sign in again on same phone after welcome process done in settings. (Nice.)
Sign in again on other phone with updated password
Update Messenger.
Update hangs. Needs more space.
Delete shit.
Update frozen in App Store (Really??)
Restart iPhone.
Update Messenger.
Update complete past 2. Well that was easy.
Apple, fuck you.
Some call Android unintuitive, but I look at the settings app on iPhone and realize you aren’t any better.
This company hasn’t been innovative since 2007. Over 1000 USD for a phone? Are you fucking kidding me?
Updating an iPhone from iOS 9.x is probably uncommon anymore. But this is a fucking joke. Fix your shit.
Shit like this is why I’ll never again own an Apple product. I have HAD IT with the joke of a business.
Thanks for reading.17 -
The time when I've felt like a badass, was when I was bored at a Birthday party at restaurant.
I didn't want to use my mobile data, so I tried to use the wifi of the restaurant. I didn't want to ask the password of the wifi, so I tried to get access by guessing. At first try I got it by entering "nameOfRestaurantCurrentYear".
Then I was browsing Play Store and there was a recommendation of an app (forgot the name) that analyses which the device is connected to wifi. So that got me interested that I installed on my phone.
So I played a little with and discover several Samsungs and iPhones connected to it (Some of the them had their real name next to the brand. It would be funny to yell their name out loud and they would be looking around.)
But there was one device that I didn't recognized. I searched on the web but found nothing. So later as I go to pay my part, I noticed that the credit card device had a wifi icon on it. So I looked over to the cash register and saw the name of the brand. It was the brand I didn't know of.
So basically they were using transfer payments over a public wifi.10 -
Worst WTF dev experience? The login process from hell to a well-fortified dev environment at a client's site.
I assume a noob admin found a list of security tips and just went like "all of the above!".
You boot a Linux VM, necessary to connect to their VPN. Why necessary? Because 1) their VPN is so restrictive it has no internet access 2) the VPN connection prevents *your local PC* from accessing the internet as well. Coworkers have been seen bringing in their private laptops just to be able to google stuff.
So you connect via Cisco AnyConnect proprietary bullshit. A standard VPN client won't work. Their system sends you a one-time key via SMS as your password.
Once on their VPN, you start a remote desktop session to their internal "hopping server", which is a Windows server. After logging in with your Windows user credentials, you start a Windows Remote Desktop session *on that hopping server* to *another* Windows server, where you login with yet another set of Windows user credentials. For all these logins you have 30 seconds, otherwise back to step 1.
On that server you open a browser to access their JIRA, GitLab, etc or SSH into the actual dev machines - which AGAIN need yet another set of credentials.
So in total: VM -> VPN + RDP inside VM -> RDP #2 -> Browser/SSH/... -> Final system to work on
Input lag of one to multiple seconds. It was fucking unusable.
Now, the servers were very disconnect-happy to prevent anything "fishy" going on. Sitting at my desk at my company, connected to my company's wifi, was apparently fishy enough to kick me out every 5 to 20 minutes. And that meant starting from step 1 inside the VM again. So, never forget to plugin your network cable.
There's a special place in hell for this admin. And if there isn't, I'll PERSONALLY make the devil create one. Even now that I'm not even working on this any more.8 -
+++ Thank you for 1000+'s! +++
So guys we did it! We've reached our first big milestone!
This account was created about a month ago, and we are already this far!
Thanks to all authors (@DLMousey, @filthyranter, @baewulff) who are putting a lot of work and time into their articles and help this account to further grow in size!
To make this article at least a bit informative, here's how we publish our posts:
When I started this account, I hadn't thought of how articles were going to be published. Should I give the password to all writers? Should I post the articles manually?
Well, after I've started the devNews Discord Server, @olback suggested making a Discord Bot, that helps us to publish our stuff.
After surprisingly few hours, @olback already got a prototype working.
We have a special channel and whoever writes stuff in it, updates the current article. Later, I took on the work, @olback has done and switched to LowDB, to be able to let multiple users have their own articles they are working on and much more. (Like special signatures)
And that's how it is now.
We have a channel for draft, where we write our stuff and a channel for publishing, where the bot listens to what we write and then publishes the articles with a command.
That's all of it.
Thank you for reading! 7
7 -
"please use a secure password*"
* But don't make it too secure, 20 Charakters is enough.
Why would you fucking do this? The only reason I can think about is a scenario like this:
"How do we store the passwords in the database?"
"Just like anything else?"
"So I create a VARCHAR(20)?"
"Yeah why not? It's good enough for a name, and you shouldn't use your or anyone else's name as a password, so it should be perfect"10 -
I absolutely love the email protocols.
IMAP:
x1 LOGIN user@domain password
x2 LIST "" "*"
x3 SELECT Inbox
x4 LOGOUT
Because a state machine is clearly too hard to implement in server software, clients must instead do the state machine thing and therefore it must be in the IMAP protocol.
SMTP:
I should be careful with this one since there's already more than enough spam on the interwebs, and it's a good thing that the "developers" of these email bombers don't know jack shit about the protocol. But suffice it to say that much like on a real letter, you have an envelope and a letter inside. You know these envelopes with a transparent window so you can print the address information on the letter? Or the "regular" envelopes where you write it on the envelope itself?
Yeah not with SMTP. Both your envelope and your letter have them, and they can be different. That's why you can have an email in your inbox that seemingly came from yourself. The mail server only checks for the envelope headers, and as long as everything checks out domain-wise and such, it will be accepted. Then the mail client checks the headers in the letter itself, the data field as far as the mail server is concerned (and it doesn't look at it). Can be something else, can be nothing at all. Emails can even be sent in the future or the past.
Postfix' main.cf:
You have this property "mynetworks" in /etc/postfix/main.cf where you'd imagine you put your own networks in, right? I dunno, to let Postfix discover what your networks are.. like it says on the tin? Haha, nope. This is a property that defines which networks are allowed no authentication at all to the mail server, and that is exactly what makes an open relay an open relay. If any one of the addresses in your networks (such as a gateway, every network has one) is also where your SMTP traffic flows into the mail server from, congrats the whole internet can now send through your mail server without authentication. And all because it was part of "your networks".
Yeah when it comes to naming things, the protocol designers sure have room for improvement... And fuck email.
Oh, bonus one - STARTTLS:
So SMTP has this thing called STARTTLS where you can.. unlike mynetworks, actually starts a TLS connection like it says on the tin. The problem is that almost every mail server uses self-signed certificates so they're basically meaningless. You don't have a chain of trust. Also not everyone supports it *cough* government *cough*, so if you want to send email to those servers, your TLS policy must be opportunistic, not enforced. And as an icing on the cake, if anything is wrong with the TLS connection (such as an MITM attack), the protocol will actively downgrade to plain. I dunno.. isn't that exactly what the MITM attacker wants? Yeah, great design right there. Are the designers of the email protocols fucking retarded?9 -
The tech stack at my current gig is the worst shit I’ve ever dealt with...
I can’t fucking stand programs, especially browser based programs, to open new windows. New tab, okay sure, ideally I just want the current tab I’m on to update when I click on a link.
Ticketing system: Autotask
Fucking opens up with a crappy piss poor sorting method and no proper filtering for ticket views. Nope you have to go create a fucking dashboard to parse/filter the shit you want to see. So I either have to go create a metric-arse tonne of custom ticket views and switch between them or just use the default turdburger view. Add to that that when I click on a ticket, it opens another fucking window with the ticket information. If I want to do time entry, it just feels some primal need to open another fucking window!!! Then even if I mark the ticket complete it just minimizes the goddamn second ticket window. So my jankbox-supreme PC that my company provided gets to strugglepuff along trying to keep 10 million chrome windows open. Yeah, sure 6GB of ram is great for IT work, especially when using hot steaming piles of trashjuice software!
I have to manually close these windows regularly throughout the day or the system just shits the bed and halts.
RMM tool: Continuum
This fucker takes the goddamn soggy waffle award for being utterly fucking useless. Same problem with the windows as autotask except this special snowflake likes to open a login prompt as a full-fuck-mothering-new window when we need to open a LMI rescue session!!! I need to enter a username and a password. That’s it! I don’t need a full screen window to enter credentials! FUCK!!! Btw the LMI tools only work like 70% of the time and drag ass compared to literally every other remote support tool I’ve ever used. I’ve found that it’s sometimes just faster to walk someone through enabling RDP on their system then remoting in from another system where LMI didn’t decide to be fully suicidal and just kill itself.
Our fucking chief asshat and sergeant fucknuts mcdoogal can’t fucking setup anything so the antivirus software is pushed to all client systems but everything is just set to the default site settings. Absolutely zero care or thought or effort was put forth and these gorilla spunk drinking, rimjob jockey motherfuckers sell this as a managed AntiVirus.
We use a shitty password manager than no one besides I use because there is a fully unencrypted oneNote notebook that everyone uses because fuck security right? “Sometimes it’s just faster to have the passwords at the ready without having to log into the password manager.” Chief Asshat in my first week on the job.
Not to mention that windows server is unlicensed in almost every client environment, the domain admin password is same across multiple client sites, is the same password to log into firewalls, and office 365 environments!!!
I’ve brought up tons of ways to fix these problems, but they have their heads so far up their own asses getting high on undeserved smugness since “they have been in business for almost ten years”. Like, Whoop Dee MotherFucking Doo! You have only been lucky to skate by with this dumpster fire you call a software stack, you could probably fill 10 olympic sized swimming pools to the brim with the logarrhea that flows from your gullets not only to us but also to your customers, and you won’t implement anything that is good for you, your company, or your poor clients because you take ten minutes to try and understand something new.
I’m fucking livid because I’m stuck in a position where I can’t just quit and work on my business full time. I’m married and have a 6m old baby. Between both my wife and I working we barely make ends meet and there’s absolutely zero reason that I couldn’t be providing better service to customers without having to lie through my teeth to them and I could easily support my family and be about 264826290461% happier!
But because we make so little, I can’t scrap together enough money to get Terranimbus (my startup) bootstrapped. We have zero expendable/savable income each month and it’s killing my soul. It’s so fucking frustrating knowing that a little time and some capital is all that stands between a better life for my family and I and being able to provide a better overall service out there over these kinds of shady as fuck knob gobblers.5 -
TL;DR I'm fucking sick and tired of Devs cutting corners on security! Things can't be simply hidden a bit; security needs to be integral to your entire process and solution. Please learn from my story and be one of the good guys!
As I mentioned before my company used plain text passwords in a legacy app (was not allowed to fix it) and that we finally moved away from it. A big win! However not the end of our issues.
Those Idiot still use hardcoded passwords in code. A practice that almost resulted in a leak of the DB admin password when we had to publish a repo for deployment purposes. Luckily I didn't search and there is something like BFG repo cleaner.
I have tried to remedy this by providing a nice library to handle all kinds of config (easy config injection) and a default json file that is always ignored by git. Although this helped a lot they still remain idiots.
The first project in another language and boom hardcoded password. Dev said I'll just remove before going live. First of all I don't believe him. Second of all I asked from history? "No a commit will be good enough..."
Last week we had to fix a leak of copyrighted contend.
How did this happen you ask? Well the secure upload field was not used because they thought that the normal one was good enough. "It's fine as long the URL to the file is not published. Besides now we can also use it to upload files that need to be published here"
This is so fucking stupid on so many levels. NEVER MIX SECURE AND INSECURE CONTENT it is confusing and hard to maintain. Hiding behind a URL that thousands of people have access to is also not going to work. We have the proof now...
Will they learn? Maybe for a short while but I remain sceptic. I hope a few DevrRanters do!7 -
How it is to be a dev in my country?
At bit of an odd question this week.
For me (in the USA), it's being technical support for *every* website my family uses.
Over the weekend my wife visited her aunt and I get a call.
Wife: "How do I create an ebay account?"
Me: "I don't like where this is going. We already have an account."
Wife: "Not for me, dummy, Aunt T. She found some books she wants to buy on ebay."
Me: "You go thru the process to create an account? Email, name, password, etc."
Wife: "We tried that, but it's not working."
<few seconds of silence>
Me: "Oookaaay...why isn't it working? Is there an error?"
Wife: "I don't know, we already clicked off of it. Something about the email."
<few more seconds of silence>
Me: "Can you reproduce the error and tell me?"
Wife: "Uggh..are you serious? We've done it like 10 times, its not working. Just tell me what I need to do."
Me: "If you can't tell me the error, I can't help you. I'm not there and can't see what you see."
Wife: "Stop being an asshole."
<Aunt T takes the phone>
T: "Said something about using another email address. Does that help you?"
Me: "Are you sure you don't already have a ebay account?"
T: "No, I don't think so. I hate ebay. but I really want these books. I don't want the same problems as last time."
Me: "Last time?"
T: "Yes, I bought a coffee cup on ebay from China and it never arrived."
Me: "OK, so you do have an account?"
T: "I don't know, I mean, I never got the cup."
Me: "What email address did you use? I'll send a 'remind me' email so you can reset the password and login"
<go thru the motions, she is able to login>
T: "Ahhh...I do have an account! There are the golf balls I bought for <husband> for Christmas."
<face smack>
Wife: "Why didn't you do this from the start? I thought you knew a lot about computers. We basically figured this out ourselves. Goodbye!"
<click>10 -
I'm fixing a security exploit, and it's a goddamn mountain of fuckups.
First, some idiot (read: the legendary dev himself) decided to use a gem to do some basic fucking searching instead of writing a simple fucking query.
Second, security ... didn't just drop the ball, they shit on it and flushed it down the toilet. The gem in question allows users to search by FUCKING EVERYTHING on EVERY FUCKING TABLE IN THE DB using really nice tools, actually, that let you do fancy things like traverse all the internal associations to find the users table, then list all users whose password reset hashes begin with "a" then "ab" then "abc" ... Want to steal an account? Hell, want to automate stealing all accounts? Only takes a few hundred requests apiece! Oooh, there's CC data, too, and its encryption keys!
Third, the gem does actually allow whitelisting associations, methods, etc. but ... well, the documentation actually recommends against it for whatever fucking reason, and that whitelisting is about as fine-grained as a club. You wanna restrict it to accessing the "name" column, but it needs to access both the "site" and "user" tables? Cool, users can now access site.name AND user.name... which is PII and totally leads to hefty fines. Thanks!
Fourth. If the gem can't access something thanks to the whitelist, it doesn't catch the exception and give you a useful error message or anything, no way. It just throws NoMethodErrors because fuck you. Good luck figuring out what they mean, especially if you have no idea you're even using the fucking thing.
Fifth. Thanks to the follower mentality prevalent in this hellhole, this shit is now used in a lot of places (and all indirectly!) so there's no searching for uses. Once I banhammer everything... well, loads of shit is going to break, and I won't have a fucking clue where because very few of these brainless sheep write decent test coverage (or even fucking write view tests), so I'll be doing tons of manual fucking testing. Oh, and I only have a week to finish everything, because fucking of course.
So, in summary. The stupid and lazy (and legendary!) dev fucked up. The stupid gem's author fucked up, and kept fucking up. The stupid devs followed the first fuckup's lead and repeated his fuck up, and fucked up on their own some more. It's fuckups all the fucking way down.rant security exploit root swears a lot actually root swears oh my stupid fucking people what the fuck fucking stupid fucking people20 -
My parents are real sticklers for who is allowed to be on Netflix. They only let people on when they are present, and they never click 'save password'.
Me being a poor college student and desperate for the Netflix password, created a fake website for one of my parents to sign into.
How did I do this? I created my own localhost server with a backend database for the password to go to. I then copied the Netflix home screen and log in and asked them to log me into their account.
They said I can be on for one hour, and then they were signing me out.
I agreed to these terms.
As a small twist, I had also copied the no internet tab from Chrome for the page to redirect to. Knowing that once they logged in they would be expecting the main UI.
They logged in and then waited for the page to load. I, of course, put in a delay for the page to load and then displayed the no internet tab. They were confused and asked me to refresh, still nothing. I asked them if the router was out, and they went to check.
While they were away I quickly switched back to the real Netflix website and yelled back saying I got it working again. They came back over and saw that it was asking for a password again. They signed in and saw the main homepage and none were the wiser that day.
Once they left I checked inside the DB and found the plaintext password they typed in... The damn password was so simple, I cursed myself for not having figured it out sooner. No matter, I had my parents Netflix password.
So you're probably wondering how they didn't see the URL above and think something was off?
I pressed F11 and fullscreened my entire browser. They did ask, and I simply replied with, I don't like seeing all the crap up above when I'm streaming. No further questions, perhaps I was lucky.14 -
Switched banks, got new e-banking, unable to set up a new password.
It contains invalid characters.
IT'S A FUCKING BANK ACCOUNT I SHOULD BE ABLE TO USE HASHTAGS OR EVEN HAVE FUCKING SPACES IN IT IF I FEEL LIKE IT.7 -
Sometimes I wonder how compromised my parents online security would be without my intervention.
My mom logged into her gmail and there was an red bar on top informing about Google preventing an attempted login from an unknown device.
Like typical parents / old people, that red bar didn't caught her attention but I noticed it immediately. I took over and looked into it. It showed an IP address and a location that was quite odd.
I went ahead with the Account security review and I was shocked to find that she had set her work email address as the recovery email!!
I explained her that work email accounts cannot be trusted and IT department of the workplace can easily snoop emails and other info on that email address and should not be related to personal accounts.
After fixing that issue, me being a typical skeptic and curious guy, I decided to find more info about that IP address.
I looked up the IP address on a lookup website and it showed an ISP that was related to the corporate office of her workplace. I noticed the location Google reported also matched with the corporate office location of her work.
Prior to this event, few days ago, I had made her change her gmail account password to a more secure one. ( Her previous password was her name followed by birth date!! ). This must have sent a notification to the recovery mail address.
All these events are connected. It is very obvious that someone at corporate office goes through employees email addresses and maybe even abuse those information.
My initial skeptism of someone snooping throguh work email addresses was right.
You're welcome mom!9 -
A few weeks ago I stepped onto the grounds of lovely Canada. Back then - coming from Europe - I was surprised. Free WiFi everywhere without all the bells and whistles of creating an account and such.
Well ... at least I thought so ...
Today I went to a location where they actually charge you for their wireless services - fair enough the coverage area is pretty huge - and provide you with an access coupon. All good my optimistic me told me but once the login page loaded...
There are a lot of things about UX I could rant about but let's put that aside. The coupon came from the office where they KNEW all your contact details but it required you to create an account with all of them again to redeem the coupon.
Not only that but it asked for things like the phone number - obviously asking for a Canadian landline number since hell who uses mobiles anyway with numbers longer than ten characters?! - and even though it had a nice country selection it kept the states field there even when selecting a country that doesn't have states ...
Oh, and on a regular phone screen (which would be the target user for WiFi on a campground I suppose) the input fields for state and zip were occluded by the margins of the input rendering the content invisible.
And if that weren't enough after creating your account they made you watch an ad as if the personal data and the 4$ you paid them wasn't enough for the lousy 400 KB/s you get for 24h ...
Gets better though! After creating the account they display your password to make sure you remembered it ... over a non-secured WiFi network ... and send you an email afterward ... password via unencrypted mail via an unencrypted WIRELESS connection ... not that it protects anything that would matter anyways you can just snoop the MAC of your neighbor and get in that way or for that sake get their password but oh well ...
Gosh, sometimes I just feel the urgent need to find the ones responsible and tell them to GTFO of the IT world ...
Is it just me feeling like this about crappy UI/UX design? Always wondering...2 -
Recently, one of our passwords was accidently published on a public page for a few minutes before it was noticed and removed. Unfortunately, this password opens nearly every locked account so it's a pretty big deal.
Management was informed of this mistake and told that we should change the passwords as well as implement a few other protocols to make sure this doesn't happen again including things like unique passwords, more secure passwords, using a password manager, etc.
Their response? It wasn't online long, probably no one saw it. There will be no changes in how we handle ours or our clients' secure passwords.6 -
Well, i have a few stories i would like to share with you :)
My neighbour asked me to fix her webcam.
I told her: But I am a programmer, not a repair service .
Next time my neighbour forgot her Skype password. Se asked me to hack it for her.
I told her: But I am a programmer, not a hacker.
My sister asked me to help her out in her program, because of some bug. Well, she is in the other part of the Country. But, i said, lets give it a try.
Well, it turned out to be some kind of mechanical remote scanner, with needed that exact same remote locally.
I told her: But I am a programmer, not a fictional remote signal scanner repairer.
My grandpa asked me, to copy his old gmail emails into his new laptop.
Well, i told him to log in. He logged in. Than i told him: It is done :D
Thanks for reading it :)4 -
Oh man. Mine are the REASON why people dislike PHP.
Biggest Concern: Intranet application for 3 staff members that allows them to set the admin data for an application that our userbase utilizes. Everything was fucking horrible, 300+ php files of spaghetti that did not escape user input, did not handle proper redirects, bad algo big O shit and then some. My pain point? I was testing some functionality when upon clicking 3 random check boxes you would get an error message that reads something like this "hi <SENSITIVE USERNAME DATA> you are attempting to use <SERVER IP ADDRESS> using <PASSWORD> but something went wrong! Call <OLD DEVELOPER's PHONE NUMBER> to provide him this <ERROR CODE>"
I panicked, closed that shit and rewrote it in an afternoon, that fucking retard had a tendency to use over 400 files of php for the simplest of fucking things.
Another one, that still baffles me and the other dev (an employee that has been there since the dawn of time) we have this massive application that we just can't rewrite due to time constraints. there is one file with (shit you not) a php include function that when you reach the file it is including it is just......a php closing tag. Removing it breaks down the application. This one is over 6000 files (I know) and we cannot understand what in the love of Lerdorf and baby Torvalds is happening.
From a previous job we had this massive in-house Javascript "framework" for ajax shit that for whatever reason unknown to me had a bunch of function and object names prefixed with "hotDog<rest of the function name>", this was used by two applications. One still in classic ASP and the other in php version 4.something
Legacy apps written in Apache Velocity, which in itself is not that bad, but I, even as a PHP developer, do not EVER mix views with logic. I like my shit separated AF thank you very much.
A large mobile application that interfaced with fucking everything via webviews. Shit was absolutley fucking disgusting, and I felt we were cheating our users.
A rails app with 1000 controller methods.
An express app with 1000 router methods with callbacks instead of async await even though async await was already a thing.
ultraFuckingLarge Delphi project with really no consideration for best practices. I, to this day enjoy Object Pascal, but the way in which people do delphi can scare me.
ASP.NET Application in wich there seemed to be a large portion of bolted in self made ioc framework from the lead dev, absolute shitfest, homie refused to use an actual ioc framework for it, they did pay the price after I left.
My own projects when I have to maintain them.9 -
My school just tried to hinder my revision for finals now. They've denied me access just today of SSHing into my home computer. Vim & a filesystem is soo much better than pen and paper.
So I went up to the sysadmin about this. His response: "We're not allowing it any more". That's it - no reason. Now let's just hope that the sysadmin was dumb enough to only block port 22, not my IP address, so I can just pick another port to expose at home. To be honest, I was surprised that he even knew what SSH was. I mean, sure, they're hired as sysadmins, so they should probably know that stuff, but the sysadmins in my school are fucking brain dead.
For one, they used to block Google, and every other HTTPS site on their WiFi network because of an invalid certificate. Now it's even more difficult to access google as you need to know the proxy settings.
They switched over to forcing me to remote desktop to access my files at home, instead of the old, faster, better shared web folder (Windows server 2012 please help).
But the worst of it includes apparently having no password on their SQL server, STORING FUCKING PASSWORDS IN PLAIN TEXT allowing someone to hijack my session, and just leaving a file unprotected with a shit load of people's names, parents, and home addresses. That's some super sketchy illegal shit.
So if you sysadmins happen to be reading this on devRant, INSTEAD OF WASTING YOUR FUCKING TIME BLOCKING MORE WEBSITES THAN THEIR ARE LIVING HUMANS, HOW ABOUT TRY UPPING YOUR SECURITY, PASSWORDS LIKE "", "", and "gryph0n" ARE SHIT - MAKE IT BETTER SO US STUDENTS CAN ACTUALLY BROWSE MORE FREELY - I THINK I WANT TO PASS, NOT HAVE EVERY OTHER THING BLOCKED.
Thankfully I'm leaving this school in 3 weeks after my last exam. Sure, I could stay on with this "highly reputable" school, but I don't want to be fucking lied to about computer studies, I don't want to have to workaround your shitty methods of blocking. As far as I can tell, half of the reputation is from cheating. The students and sysadmins shouldn't have to have an arms race between circumventing restrictions and blocking those circumventions. Just make your shit work for once.
**On second thought, actually keep it like that. Most of the people I see in the school are c***s anyway - they deserve to have half of everything they try to do censored. I won't be around to care soon.**undefined arms race fuck sysadmin ssh why can't you just have any fucking sanity school windows server security2 -
Sorry if this sounds like retard question on linux system
I installed nvidia driver on my laptop (720M) and it showed black screen after reboot, BUT if I enter my password and hit enter the screen goes back to normal on desktop, it just didn’t show anything on the first lock screen
I’ve followed linux mint nvidia driver instructions, removing the package re installing, etc.
P.S. All of the question I found on the internet seems to be total black screen after installing the driver, whereas mine could work after I entered my password8 -
The situation right now:
Our client: full of legacy desktop solutions that always ran inside a VPN, but wanting to modernize the system and migrate to be hosted in the cloud.
Our first project with them: Frontend built with Angular, backend in a serverless model, all with GraphQL and heavily tested to assure quality. The system is mostly an internal software for management, but the backed may receive data from an App.
The problem: all management users have weak passwords (like "12345", "password", or their first name).
The solution: restrict our system to be accessible only inside the VPN
The new problem: how the mobile app will send data to our backend?
The new solution: Let's duplicate the backend, one public and the other private. The public one will accept only a few GraphQL operations.
------
This could be avoided if the passwords weren't so easily deductible11 -
Not really hacking, but my roommate says otherwise. So we share a router in the apartment and I’m the only one that really knows how to access it, so of course I change the password and tell no one (not like they’ll try to get in anyway).
Occasionally set roommate likes to get blackout and play music very loud at 2am. To be petty, on those occasions I set up an RPi Zero to connect to the WiFi, restart it, and sleep for a minute, and repeat. He’s still convinced we are getting DDOSd, and suspects nothing.
Reason I don’t just set parental controls - he gets more frustrated when the WiFi appears for 10secs, the music is just about to start and shuts off again. So he gives up quicker. Otherwise, he resets the router and I have to set up everything from the start.3 -
What. The. Actual. Fuck.
My co-workers just tried to convince me that the following is a secure password:
"ThisIsASecurePassword2018"
Just... I mean... Why? *sigh*
Their argumentation is based on the new NIST guidelines.
If they've read these guidelines CAREFULLY though... (not only the appendix) it actually states "Don't use words from the dictionary". Passwords like these should even be rejected right away.15 -
!dev but actual long rant - about the students in my grade.
TL;DR: 1 asshole in 10 people can ruin everything. Mobbing sucks. I dislike parties.
There's the word "Jahrgang" in Germany which means the people in the same school year as you. I'll refer to it as "my (collective) classmates" although we don't have classes anymore, rather courses and I also mean those I do not have courses with.
With that out of the way, let the rant begin.
It's often the case that people with high logical and intellectual skills (no being arrogant, other people categorize me like that) have a lack of social skills - or empathy.
I'm a kind of an outsider in a way that since 10th grade I stopped trying to attach myself to certain groups since I do not fit in there. I'm fine with that now. Nowadays I can at least socialize with other nerds.
Here's why I dislike the collective of my classmates. This year is my last school year and as always, a big group forms a spirit. They have a theme (superheroes - super boring). I didn't go to any party they threw and I don't plan to go to the graduation ceremony as well since it's an unofficial party and not a school event. I hate parties. I hate alc and drunken teenagers. I didn't attend the "Kursfahrt" - a kind of excursion that's like holidays with your course - mainly because I dislike my "Stammkurs" (main course).
Why? I had a friend in this course. She was short, geeky and I could actually talk to her. Yet some jerks (not intensely) bullied her because "she was awkward" and in the end, she switched school - also because of other reasons.
When she was gone, even those who didn't bully her and who are considered "nice" made fun of her and talked badly about her - and me hanging around with her. So since then, I avoid anything with them that's not 100% school related.
Now they're planning what we call "Abigag" - it's a joke/prank the graduates pull on the school and younger students, something funny like an entrance room full of balloons and many other things. Also, the "Abizeitung", the yearbook the graduates put out with articles about their courses, teacher ranking and quotes etc. Also, a cabaret evening from the graduates to collect money for the graduation party. Cool stuff actually. I thought about taking part.
I'd say my talents are creativity and computer stuff. So a friend chatted with me about nerdy pranks like a school-wide wallpaper change. Or releasing a fake password list of the teachers - claiming we hacked them - with puns and insiders about the teaches. He said he gotta invite me into the WhatsApp group of the Abi prank. Disclaimer: He's one of those people who are socialized but still able to talk with me. He's fine.
Well guess what he told me later:
They don't want me on the team since I distance myself from my classmates. I should either be fully one of them or not at all.
That's enough. Who distances whom? I thought they were happy to have me on board but horse shit! Stuck with ideologies from the 19th century.
They can lick my ***. I don't have anything against most of them in person but as a collective, they're just fucking stupid. I guess it wasn't even the majority saying they don't want me to help. It was probably just the small crew of leading and loud jerks. And no one would disagree with them saying "Why not? He wants to help?" (even if it was their opinion) - they don't have the brain or balls to say anything against the strong idiot leaders. They'll do great later in politics as an adult - they wouldn't criticize Hitler if they were under his "protection".
So I won't take part in making Abi pranks, - but also not the Paper and cabaret eve. They can go jerk off to being part of a huge collection of assholes - which I, in all my pride, am not part of other than on paper.
(Disclaimer: No critics to other outsiders but those who were engaged and responsible for the choice of not letting me help)
If anyone actually read this:
Who were/are you in school times?
A proud outsider like me? Party boi/girl? Engaged striver?25 -
"Ad targeters are pulling data from your browser’s password manager"
---
Well, fuck.
"It won't be easy to fix, but it's worth doing"
Just check for visibility or like other password managers handle it iirc: assign a unique identifier based on form content and fill that identifier only.
---
"Nearly every web browser now comes with a password manager tool, a lightweight version of the same service offered by plugins like LastPass and 1Password. But according to new research from Princeton's Center for Information Technology Policy, those same managers are being exploited as a way to track users from site to site.
The researchers examined two different scripts — AdThink and OnAudience — both of are designed to get identifiable information out of browser-based password managers. The scripts work by injecting invisible login forms in the background of the webpage and scooping up whatever the browsers autofill into the available slots. That information can then be used as a persistent ID to track users from page to page, a potentially valuable tool in targeting advertising."
Source: https://theverge.com/2017/12/... 14
14 -
When I get on a site that is like “your password must contain upper case, lower case, a number, a symbol”, at first I’m like ooook, security I guess I’ll generate a long password, but then they sit there and say “and be at least 6 but not more than 10 characters”
WTF you fuckers really don’t know anything do you.2 -
So I have seen this quite a few times now and posted the text below already, but I'd like to shed some light on this:
If you hit up your dev tools and check the network tab, you might see some repeated API calls. Those calls include a GET parameter named "token". The request looks something like this: "https://domain.tld/api/somecall/..."
You can think of this token as a temporary password, or a key that holds information about your user and other information in the backend. If one would steal a token that belongs to another user, you would have control over his account. Now many complained that this key is visible in the URL and not "encrypted". I'll try to explain why this is, well "wrong" or doesn't impose a bigger security risk than normal:
There is no such thing as an "unencrypted query", well besides really transmitting encrypted data. This fields are being protected by the transport layer (HTTPS) or not (HTTP) and while it might not be common to transmit these fields in a GET query parameter, it's standard to send those tokens as cookies, which are as exposed as query parameters. Hit up some random site. The chance that you'll see a PHP session id being transmitted as a cookie is high. Cookies are as exposed as any HTTP GET or POST Form data and can be viewed as easily. Look for a "details" or "http header" section in your dev tools.
Stolen tokens can be used to "log in" into the website, although it might be made harder by only allowing one IP per token or similar. However the use of such a that token is absolut standard and nothing special devRant does. Every site that offers you a "keep me logged in" or "remember me" option uses something like this, one way or the other. Because a token could have been stolen you sometimes need to additionally enter your current password when doings something security risky, like changing your password. In that case your password is being used as a second factor. The idea is, that an attacker could have stolen your token, but still doesn't know your password. It's not enough to grab a token, you need that second (or maybe thrid) factor. As an example - that's how githubs "sudo" mode works. You have got your token, that grants you more permissions than a non-logged in user has, but to do the critical stuff you need an additional token that's only valid for that session, because asking for your password before every action would be inconvenient when setting up a repo
I hope this helps understanding a bit more of this topic :)
Keep safe and keep asking questions if you fell that your data is in danger
Reeeeeeeeeeeeeeeeeeeeeeeeeeeeeeeeeeeeeeeee5 -
Wow, I'm going to have a hard time remembering this one.
IT have changed after so many years the password criteria for our machines, to the point it's a bit ridiculous.
Like I'm all for securing your accounts and using random passwords but, this is rough.
Minimum of 14 chars
Not the past 6 passwords
Must contain several %}*]=[^{
Must contains numbers
Must contain upper case letters
Must contain Lower case letters
Must not end in a number
Must sacrifice a virgin on every login
Must be changed every 30 daysrant security vs usability kill me - kill me now password managers go hard or go home - oh wait i am home22 -
I forgot my password to [SITE]. Of course, I click "forgot password", and enter my email, which I did remember. Fairly routine "ah shit we have a problem" steps.
Now, it takes a second. This is to be expected. So I'm not worried. I then get the email and...
Now, you will notice that I redacted some information, like the company name, email, and my PLAIN TEXT PASSWORD, and my name.
I would like to note that this isn't a small, very local company that's new (even then it'd be unacceptable), but this is a multinational, multimillion dollar company.
How'd someone fuck up THIS badly? 13
13 -
So I just wanted to log back into windows. Typed in the password. Wrong password...
Then I tried being super accurate while typing and also checked keyboard layout, etc. Still, wrong password.
Then I noticed that the letter p is not working. Shit, keyboard seems to be broken.
On screen keyboard -> p is not working...
What the hell? What kind of error is this?
NT Kernel code has to be something like this:
if(timeSinceLastError > someValue)
keyboard.p.enable = false;
I guess you could also replace the keyboard error with some random error.
If you encounter this, restart Windows.3 -
!dev
I'm always somewhat pissed off since i don't have a developer job - barely even a tech job. I scan patient charts into pdfs > a server, and that's as complicated as my job description gets. i sit and scan. my computer is (supposed to be) nothing other than a display for managing the scanned charts.
what really killed me though is that one time, we got a new MFC because our old one was, well, obviously broken beyond their patience level. They told me i'd be "Helping".
I got to cut open the box.
whoop dee fucking doo. Tech assist of the century ladies and gents.
That being ine of the worst cases, there's always the times when they talk to their IT guy and never forget to call him an asshole after simply because they don't like it when they don't understand stuff. I've texted him a few times and he's actually very pleasant to talk with and does his job well. just grinds my gears
(and being the IT guy is not available as an alternative. the job is 1. obviously filled, and 2. I installed a word document password bruteforcer, which they in turn told the doctor who told the IT guy and made it sound like i had developed it - of course, this being a pretty professional clinic, he suggested i get fired. so now any hope of me actually doing what I love there is pretty hopelessly out of my reach>2 -
So I manage multiple VPS's (including multiple on a dedicated server) and I setup a few proxy servers last week. Ordered another one yesterday to run as VPN server and I thought like 'hey, let's disable password based login for security!'. So I disabled that but the key login didn't seem to work completely yet. I did see a 'console' icon/title in the control panel at the host's site and I've seen/used those before so I thought that as the other ones I've used before all provided a web based console, I'd be fine! So le me disabled password based login and indeed, the key based login did not work yet. No panic, let's go to the web interface and click the console button!
*clicks console button*
*New windows launches.....*
I thought I would get a console window.
Nope.
The window contained temporary login details for my VPS... guess what... YES, FUCKING PASSWORD BASED. AND WHO JUST DISABLED THE FUCKING PASSWORD BASED LOGIN!?!
WHO THOUGHT IT WOULD BE A GOOD IDEA TO IMPLEMENT THIS MOTHERFUCKING GOD?!?
FUUUUUUUUUUUUUUUUUUUUUUU.3 -
The Hungarian public transport company launched an online shop (created by T-Systems), which was clearly rushed. Within the first days people found out that you could modify the headers and buy tickets for whatever price you set, and you could login as anyone else without knowing their password. And they sent out password reminders in plain text in non-encrypted emails. People reported these to the company which claims to have fixed the problems.
Instead of being ashamed of themselves now they're suing those who pointed out the flaws. Fucking dicks, if anyone they should be sued for treating confidential user data (such as national ID numbers) like idiots.3 -
ALMOST HALF AN HOUR SPENT TRYING TO LOG INTO MY FUCKING RASPBERRY PI OVER SSH.
you know what the problem is?
I’m not gonna tell you because I want you to feel the agony too.
> be me
> want to set up a nextcloud instance on pi to play with
> boot up
> ssh pi
*enter password*
*password incorrect*
^tries like 60 more times with different things
> pulls HDMI out of PC
> connect to pi direct
*please login*
*enter password*
Hackerman_voice_im_in.mp3
Wtf.xml
> check the logs
>try login from phone
Fuckyou.jpg
>Tries resetting password
Fuckyou-final.jpg
>tried logging into other pi
Fuckyou-final2.jpg
>*wtf’s harder*
Andthenithitme.png
>type @ sign
Pi: “
> OHHHHHHH5 -
I was asked to look into a site I haven't actively developed since about 3-4 years. It should be a simple side-gig.
I was told this site has been actively developed by the person who came after me, and this person had a few other people help out as well.
The most daunting task in my head was to go through their changes and see why stuff is broken (I was told functionality had been removed, things were changed for the worse, etc etc).
I ssh into the machine and it works. For SOME reason I still have access, which is a good thing since there's literally nobody to ask for access at the moment.
I cd into the project, do a git remote get-url origin to see if they've changed the repo location. Doesn't work. There is no origin. It's "upstream" now. Ok, no biggie. git remote get-url upstream. Repo is still there. Good.
Just to check, see if there's anything untracked with git status. Nothing. Good.
What was the last thing that was worked on? git log --all --decorate --oneline --graph. Wait... Something about the commit message seems familiar. git log. .... This is *my* last commit message. The hell?
I open the repo in the browser, login with some credentials my browser had saved (again, good because I have no clue about the password). Repo hasn't gotten a commit since mine. That can't be right.
Check branches. Oh....Like a dozen new branches. Lots of commits with text that is really not helpful at all. Looks like they were trying to set up a pipeline and testing it out over and over again.
A lot of other changes including the deletion of a database config and schema changes. 0 tests. Doesn't seem like these changes were ever in production.
...
At least I don't have to rack my head trying to understand someone else's code but.... I might just have to throw everything that was done into the garbage. I'm not gonna be the one to push all these changes I don't know about to prod and see what breaks and what doesn't break
.
I feel bad for whoever worked on the codebase after me, because all their changes are now just a waste of time and space that will never be used.3 -
auto.self.whatever.rant()
A few years ago, we had a lesson on git and stuff, and we had to create our first repository and push something on it to get familiar with the thing.
Our teacher jokingly said at the end "And always remember, no password in a repository!", and I thought to myself "who can be dumb enough to do actually do something like that?"
Now, guess which piece of shit had to reinstall two of his fucking servers because of security issues coming from not one but github repositories?4 -
Just watching some videos about feminism and I'm just thinking: "how fucking nutty are these people really?!"
Too drunk right now to write about the recent developments in Mozilla's adoption of "the big bad patriarchy and meritocracy" (and I don't have the password database mirrored on my recently unfucked WanBLowS 10 desktop yet so I've no idea how to authenticate to devRant on it yet) but I'll try to get it out there by tomorrow 🙂
Simply put, Mozilla.. I like you regardless of the whole Mr. Robot crap from earlier, and I'm sure you've got your heart in the right place.. although I'm using Brave nowadays - a creation from the board member you've shunned over this whole PC shit, Brandon Eich. But let me tell you this, Mozilla. Enough is enough. Don't be fucking idiots.24 -
Cracking old recovery CDs for the 9x/2000/XP era shines some light into how companies operated and when concepts came to be in that time:
Packard Bell: An EXE checks that you're running on a Packard Bell machine and reboots if it's not. How do we bypass it? Easy: just fucking delete it. The files to reinstall Windows from scratch come from...
...
C:?
Yup. Turns out Packard Bell was doing the recovery partition thing all the way back to the 9x era, maybe even further. Files aren't even on the restore disc so if your partition table got fucked (pretty common because malware and disk corruption) you were totally fucked and needed to repurchase Windows. (My dad, at the time, only charged at-cost OEM prices for a replacement retail copy. He knew it was dumb so he never sold PB machines.)
Compaq:
Computer check? Nope, remove one line from a BATCH file and it's gone.
Six archives, named "WINA.ZIP" through "WINF.ZIP" (plus one or two extras for OEM software) hold Windows. Problematic? Well... only because they never put the password anywhere so the installer can't install them. (Some interesting on-disc technician-only utils, though!)
Dell:
If not a Dell machine, lock up. Cause? CONFIG.SYS driver masquerading as OAK (the common CD driver) doing the check, then chainloading the real OAK driver. Simple fix: replace the fake driver with the real one.
Issues?
Would I mention this one if there weren't?
Disc is mounted on N:. Subdirectories work, but doing anything in them (a DIR, trying to execute something, trying to view shit in EDIT.COM) kicked you back to the disc root.
Installer couldn't find machine manifest in the MAP folder (it wanted your PC's serial before it'd let you install, to make sure you have the correct recovery disc) so it asked for 12-digit alphanumeric serial. The defined serials in the manifest were something like "02884902-01" or similar (8-2, all numbers) and it couldn't read the file so it couldn't show the right format, nor check for the right type.
Bypassing that issue, trying to do the ACTUAL install process caused nothing to happen... as all BATCHes for install think the CD should be on X:.
Welp.
well that was fun. Now to test on-real-PC behavior, as VBOX and VMWare both don't like the special hardware shit it tries to use. (Why does a textmode GUI need GPU acceleration, COMPAQ?????)4 -
I really hate it when I forget my password, cause then when I have to reset it and choose a new password a message pops up saying "Your new password cannot be the same as your old password. " Every damn time... Like WtF8
-
Tl;dr stupid password requirements
Begin quote
Password must not contain any non-alphanumeric characters.
Your Password change was not accepted. Enter your current Password correctly following the rules for New Passwords. Please try again.
Passwords must be between 8 and 12 characters in length and MUST contain each of the following:
At least 1 lower case character (a-z)
At least 1 upper case character (A-Z)
At least 1 numeric digit (0-9)
But, MUST NOT contain:
more than five repeating characters in a row (e.g. 111111356 would not be valid, but 112233445 would be valid)
spaces or other special characters
NOTE: Your new password cannot be the same as any of your 10 previous passwords.
End quote
Are you fucking kidding me? Only (26+26+10)^8 through
(26+26+10)^12 different passwords to go through? It's like the oxygen wasters that built this website give zero fucks about security.
Why? This is the site that manages money and investments. Just allow passwords up to 64 characters, allow any ascii character and just fucking encod the characters to prevent any Injunction.4 -
So... did I mention I sometimes hate banks?
But I'll start at the beginning.
In the beginning, the big bang created the universe and evolution created humans, penguins, polar bea... oh well, fuck it, a couple million years fast forward...
Your trusted, local flightless bird walks into a bank to open an account. This, on its own, was a mistake, but opening an online bank account as a minor (which I was before I turned 18, because that was how things worked) was not that easy at the time.
So, yours truly of course signs a contract, binding me to follow the BSI Grundschutz (A basic security standard in Germany, it's not a law, but part of some contracts. It contains basic security advice like "don't run unknown software, install antivirus/firewall, use strong passwords", so it's just a basic prototype for a security policy).
The copy provided with my contract states a minimum password length of 8 (somewhat reasonable if you don't limit yourself to alphanumeric, include the entire UTF 8 standard and so on).
The bank's online banking password length is limited to 5 characters. So... fuck the contract, huh?
Calling support, they claimed that it is a "technical neccessity" (I never state my job when calling a support line. The more skilled people on the other hand notice it sooner or later, the others - why bother telling them) and that it is "stored encrypted". Why they use a nonstandard way of storing and encrypting it and making it that easy to brute-force it... no idea.
However, after three login attempts, the account is blocked, so a brute force attack turns into a DOS attack.
And since the only way to unblock it is to physically appear in a branch, you just would need to hit a couple thousand accounts in a neighbourhood (not a lot if you use bots and know a thing or two about the syntax of IBAN numbers) and fill up all the branches with lots of potential hostages for your planned heist or terrorist attack. Quite useful.
So, after getting nowhere with the support - After suggesting to change my username to something cryptic and insisting that their homegrown, 2FA would prevent attacks. Unless someone would login (which worked without 2FA because the 2FA only is used when moving money), report the card missing, request a new one to a different address and log in with that. Which, you know, is quite likely to happen and be blamed on the customer.
So... I went to cancel my account there - seeing as I could not fulfill my contract as a customer. I've signed to use a minimum password length of 8. I can only use a password length of 5.
Contract void. Sometimes, I love dealing with idiots.
And these people are in charge of billions of money, stock and assets. I think I'll move to... idk, Antarctica?4 -
Boss: "So I'm taking the next week off. In the mean time, I added some stuff for you to do on Gitlab, we'd need you to pull this Docker image, run it, setup the minimal requirement and play with it until you understand what it does."
Me: "K boss, sounds fun!" (no irony here)
First day: Unable to login to the remote repository. Also, I was given a dude's name to contact if I had troubles, the dude didn't answer his email.
2nd day: The dude aswered! Also, I realized that I couldn't reach the repository because the ISP for whom I work blocks everything within specific ports, and the url I had to reach was ":5443". Yay. However, I still can't login to the repo nor pull the image, the connection gets closed.
3rd day (today): A colleague suggested that I removed myself off the ISP's network and use my 4G or something. And it worked! Finally!! Now all I need to do is to set that token they gave me, set a first user, a first password and... get a 400 HTTP response. Fuck. FUCK. FUUUUUUUUUUUUUUUUUUUCK!!!
These fuckers display a 401 error, while returning a 400 error in the console log!! And the errors says what? "Request failed with status code 401" YES THANK YOU, THIS IS SO HELPFUL! Like fuck yea, I know exactly how t fix this, except that I don't because y'all fuckers don't give any detail on what could be the problem!
4th day (tomorrow): I'm gonna barbecue these sons of a bitch
(bottom note: the dude that answered is actually really cool, I won't barbecue him)5 -
My client's using some legacy server side software. I set it all up nice and isolated with proxmox, tunneled it through cloudflare, got the folks to do their install on a windows vm, passthrough their licensing usb. Hosted GLPI on it too (system inventory) and so on.
Wait for it. Windows Server refuses to accept local or domain passwords. WTF. Even went ahead and did a Utilman reset on it which lets you use an admin cmd prompt to the login screen where you could reset the password. Insane that it was even possible, but no good.
Client blamed linux for it, I switched over to Windows Server on baremetal. I setup Hyper-V thinking it should be just as capable as KVM.
Nope.
Guess what, you can't pass through usb for licensing (the legacy software). MOFOS DECIDED TO install it baremetal. I couldn't even get hyper-v to create a decent virtual network. It keeps changing all my network adapter settings. I COULDN'T EVEN PASSTHROUGH PCIE NETWORK CARDS.
This feels like an eternally stagnated, mossy soup of abandonware.
FUCK YOU WINDOWS. You've been sore pain the ass for EVERYONE.2 -
tl;dr:
The Debian 10 live disc and installer say: Heavens me, just look at the time! I’m late for my <segmentation fault
—————
tl:
The Debian 10 live cd and its new “calamares” installer are both complete crap. I’ve never had any issues with installing Debian prior to this, save with getting WiFi to work (as expected). But this version? Ugh. Here are the things I’ve run into:
Unknown root password; easy enough to get around as there is no user password; still annoying after the 10th time.
Also, the login screen doesn’t work off-disc because it won’t accept a blank password, so don’t idle or you’ll get locked out.
The lock screen is overzealous and hard-locks the computer after awhile; not even the magic kernel keys work!
The live disc doesn’t have many standard utilities, or a graphical partition editor. Thankfully I’m comfortable with fdisk.
The graphical installer (calamares) randomly segfaults, even from innocuous things like clicking [change partition] when you don’t have a partition selected. Derp.
It also randomly segfaults while writing partitions to disk — usually on the second partition.
It strangely seems less likely to segfault if the partitions are already there, even if it needs to “reformat” (recreate) them.
It also defaults to using MBR instead of GPT for the partition table, despite the tooltip telling you that MBR is deprecated and limited, and that GPT is recommended for new systems. You cannot change this without doing the partitions manually.
If you do the partitions manually and it can’t figure out where to install things, it just crashes. This is great because you can’t tell it where to install things, and specifying mount points like /boot, /, and /home don’t seem to be enough.
It also tries installing 32bit grub instead of 64bit, causing the grub installer to fail.
If you tell it to install grub on /boot, it complains when that partition isn’t encrypted — fair — but if you tell it to encrypt /boot like it wants you to, it then tries installing grub on the encrypted partition it just created, apparently without decrypting it, so that obviously fails — specific error: cannot read file system.
On the rare chance that everything else goes correctly, the install process can still segfault.
The log does include entries for errors, but doesn’t include an error message. Literally: “ERROR: Installation failed:” and the log ends. Helpful!
If the installer doesn’t segfault and the install process manages to complete, the resulting install might not even boot, even when installed without any drive encryption. Why? My guess is it never bothered to install Grub, or put it in the wrong place, or didn’t mark it as bootable, or who knows what.
Even when using the live disc that includes non-free firmware (including Ath9k) it still cannot detect my wlan card (that uses Ath9k).
I’ve attempted to install thirty plus times now, and only managed to get a working install once — where I neglected to include the Ath9k firmware.
I’m now trying the cli-only installer option instead of the live session; it seems to behave at least. I’m just terrified that the resulting install will be just as unstable as the live session.
All of this to copy the contents of my encrypted disks over so I can use them on a different system. =/
I haven’t decided which I’m going with next, but likely Arch, Void, or Gentoo. I’d go with Qubes if I had more time to experiment.
But in all seriousness, the Debian devs need some serious help. I would be embarrassed if I released this quality of hot garbage.
(This same system ran both Debian 8 and 9 flawlessly for years)15 -
Just another big rant story full of WTFs and completely true.
The company I work for atm is like the landlord for a big german city. We build houses and flats and rent them to normal people, just that we want to be very cheap and most nearly all our tenants are jobless.
So the company hired a lot of software-dev-companies to manage everything.
The company I want to talk about is "ABI...", a 40-man big software company. ABI sold us different software, e.g. a datawarehouse for our ERP System they "invented" for 300K or the software we talk about today: a document management system. It has workflows, a 100 year-save archive system, a history feature etc.
The software itself, called ELO (you can google it if you want) is a component based software in which every company that is a "partner" can develop things into, like ABI did for our company.
Since 2013 we pay ABI 150€ / hour (most of the time it feels like 300€ / hour, because if you want something done from a dev from ABI you first have to talk to the project manager of him and of course pay him too). They did thousand of hours in all that years for my company.
In 2017 they started to talk about a module in ELO called Invoice-Module. With that you can manage all your paper invoices digital, like scan that piece of paper, then OCR it, then fill formular data, add data and at the end you can send it to the ERP system automatically and we can pay the invoice automatically. "Digitization" is the key word.
After 1.5 years of project planning and a 3 month test phase, we talked to them and decided to go live at 01.01.2019. We are talking about already ~ 200 hours planning and work just from ABI for this (do the math. No. Please dont...).
I joined my actual company in October 2018 and I should "just overview" the project a bit, I mean, hey, they planned it since 1.5 years - how bad can it be, right?
In the first week of 2019 we found 25 bugs and users reporting around 50 feature requests, around 30 of them of such high need that they can't do their daily work with the invoices like they did before without ELO.
In the first three weeks of 2019 we where around 70 bugs deep, 20 of them fixed, with nearly 70 feature requests, 5 done. Around 10 bugs where so high, that the complete system would not work any more if they dont get fixed.
Want examples?
- Delete a Invoice (right click -> delete, no super deep hiding menu), and the server crashed until someone restarts it.
- missing dropdown of tax rate, everything was 19% (in germany 99,9% of all invoices are 19%, 7% or 0%).
But the biggest thing was, that the complete webservice send to ERP wasn't even finished in the code.
So that means we had around 600 invoices to pay with nearly 300.000€ of cash in the first 3 weeks and we couldn't even pay 1 cent - as a urban company!
Shortly after receiving and starting to discussing this high prio request with ABI the project manager of my assigned dev told me he will be gone the next day. He is getting married. And honeymoon. 1 Week. So: Wish him luck, when will his replacement here?
Deep breath.
Deep breath.
There was no replacement. They just had 1 developer. As a 40-people-software-house they had exactly one developer which knows ELO, which they sold to A LOT of companies.
He came back, 1 week gone, we asked for a meeting, they told us "oh, he is now in other ELO projects planned, we can offer you time from him in 4 weeks earliest".
To cut a long story short (it's to late for that, right?) we fought around 3 month with ABI to even rescue this project in any thinkable way. The solution mid February was, that I (software dev) would visit crash courses in ELO to be the second developer ABI didnt had, even without working for ABI....
Now its may and we decided to cut strings with ABI in ELO and switch to a new company who knows ELO. There where around 10 meetings on CEO-level to make this a "good" cut and not a bad cut, because we can't afford to scare them (think about the 300K tool they sold us...).
01.06.2019 we should start with the new company. 2 days before I found out, by accident, that there was a password on the project file on the server for one of the ELO services. I called my boss and my CEO. No one knows anything about it. I found out, that ABI sneaked into this folder, while working on another thing a week ago, and set this password to lock us out. OF OUR OWN FCKING FILE.
Without this password we are not able to fix any bug, develop any feature or even change an image within ELO, regardless, that we paid thausend of hours for that.
When we asked ABI about this, his CEO told us, it is "their property" and they will not remove it.
When I asked my CEO about it, they told me to do nothing, we can't scare them, we need them for the 300K tool.
No punt.
No finish.
Just the project file with a password still there today6 -
Long story short: University fucked up single sign on.
For every online service I have, I set a different password, randomly generated ~ 20 characters long. At our university we have multiple systems but they offer a single sign on service which is quite nice because it is so non-transparent which service now uses which authorization. I changed my password a while ago and around the same time they also updated our mail client. Since then I am not able to log in which is not a big deal for me because I have mail forwarding.
Yesterday however I needed another service and also got rejected with my password. I knew from a friend that the passwords are fucked up and that some services have different restrictions (only 12 chars max.), so I decided to search how to reset my password. What the fuck was wrong with these people? It takes you five different pages to get the tiniest bit of information how to reset the password. Then on one page you can login with your single sign on and change the password. On that page you can also set the single sign on password, but if you enter an invalid password (in respect of the the other services) guess what? No feedback that you just locked yourself out of half the systems. Nice job. Also the password requirements are not next to the input fields where you change the password. Noo. That would be way to easy, remember the little small one line on the wall of text three pages ago? There you go.
Ok step one done. Now it should work, shouldn't it? Ohh no not so fast. One needs to activate the seperate service. Where you ask? Perfectly fine question. On the top of page four is a fucking one line table which looks like some five year old had some fun in excel. The button which takes you to the activation page is nearly invisible because of the non existing contrast. Also it is not a button but some arrow pointer thingy. Behind set arrow you have a page listing all differnt kinds of services, the description which you find on page two btw. No padding to decipher this shit what so ever. Nearly on the bottom is your needed button. Yes finally.
Finally I want to login, no good. Try again. Still no good. Go back to the fucked up excel table look at my username and think to myself what's the difference here? The table is so small and again no margin or padding. Apparently they cut of the last character of my normal username which i have which is fucking ridiculous.
What is wrong with you people, we are a TECHNICAL UNIVERSITY, is it so hard for you to find someone decend to unify this shit?1 -
Hey Citrix:
FUCK YOU.
Learn to make an accessible log in page you fucks.
Maybe instead of vague fucking "you're user name and password is wrong" say things like "your account is locked because we somehow decided we don't like your password anymore. . . . without telling you"
Fucking 2 hours of my day wasted trying to log into my company's VM because first it wouldn't take my password (that I've had for over a month and doesn't expire for another month) over and over again. I changed it, logged in. Got up to do something that'd take less than 5 minutes. And OF COURSE the people who set up the VM made them log you out if you're gone for more than 3 minutes (fuck that guy too). Come back to a log in screen and it won't accept my new password.
Change it again. Except this time it won't accept my new password because it's "like my old password." It is in that it uses the alphabet and numbers, but it's also different in that those alphanumeric characters are LITERALLY DIFFERENT IN EVERY PLACE. I finally get it to accept a new password.
I'm also loving the whole "answer these security questions that literally anyone who does minimal research on you can answer" before I get to change my password. Yeah. Because finding my mother's maiden name or the city I was born in is so fucking hard. Literally impossible to find out what my Dad's dad's name is. Shit like that isn't publically available. Nope. Why the fuck are we still using "security" questions?
I log into Citrix again. And it takes me to . . . the log in for Citrix.
There is no word in elvish, entish or the tongues of men for this stupidity.
Fuck Citrix. Fuck the people behind the password manager (Aviator or something like that), and fuck whatever administrator setting turns my computer off due to inactivity in such a stupid short amount of time. 10 minutes, 15 minutes, that'd be fine. But it's more like 3 or 5, like wtf.2 -
Me and my developer friend worked with my ex-colleague with this fitness directory website because he promised to give us {{ thisAmount }} upon the {{ completionDate }}.
He was my friend and I trusted him.
It took me weeks of sleepless nights building the project. I had a full-time job that time, and I worked on the project during evenings. All went well, and as we reach the {{ completionDate }}, the demo site is already up and running.
A week before the {{ completionDate }}, he hired his new wife as the COO of the startup. It was cool, she keep noticing things on the site which shouldn't be there, and keeps on suggesting sections that has to be there. I was okay with it, until I realized that we are already a month late with the deadline.
Every single hour, I get a message from them like, "it's not working", "when can you finish this feature?", blah blah blah.. and so on.
I got frustrated.
"I want my fucking life back", I told them. No one cared about the {{ completionDate }}, the sleepless zombies they are working with and our payment. They keep on coming up with this "amazing" ass features, and now they are not paying because they said "it's not complete".
Idiot enough to trust a friend. I was unprotected, there was no legal-binding document that states their obligation to pay.
My dev friend and I handed over the project to this web development company which they prefer, and kept a backdoor on the application.
I kind of moved on with the payment issue after a month. But without their knowledge, I kept an eye on the progress and made sure that I still have the access to their server, DNS, etc..
BUT when they announced the official launch on social media, I realized that I was on the wrong train the whole time.
They switched to a different server.
They thanked all the people involved with the project via social media, EXCEPT me and my coding partner who originally built the site from ground up. A little "thank you" note from them will make us feel a little better. But, never happened.
I checked up the site and it was rewritten from originally Laravel 5 to CodeIgniter 1. That is like shifting from a luxury yacht where you can bang some hot chicks, to a row boat where your left hand is holding the paddle whilst your right hand is wanking yourself.
I almost ran out of bullets.
Luckily, CodeIgniter 1 was prone to SQLi by default.
I was able to get the administrator password in plain text and fucked with their data. But that didn't make me feel better because other people's info are involved.
So, I looked for something else to screw with. What I found? A message with the credit card details.
Finally, a chance to do something good for humanity. I just donated a few thousand dollars to different charity websites.2 -
I am beginning to hate the relationship between email and my clients. I never thought it would come to the point where email is the worst communication platform I've ever used because some of my clients simply don't know how to use it properly.
I have one client who never uses the subject header in his emails. This makes conversational threads very difficult to follow, and I can't just scan the inbox I have for him. I have to actually do searches on my emails just to find recent conversations.
For some reason nobody knows how to start a new email thread. I have multiple clients that will just take the last email that I sent them, regardless of what it's about, and start a new conversation completely unrelated to the other email by hitting"reply". I end up with email threads that are 60 to 100 emails long and contain many different subjects, which again makes it hard to find anything. Never mind that they've usually put two or three important attachments, or username password combinations, or other valuable information in there amongst all the noise.
Worst of all, I have a few clients and co-workers who insist on starting a new email thread whenever anything about a particular issue comes up. This means that just today I have five separate email threads about the same goddamn issue from the same damn person. Am I supposed to respond to each thread with the same damned information? One of these people is supposed to be both a media consultant and an SEO expert and really should know better. Also, if you do actually send me an email with a subject like "the robot.txt error", please don't give me one sentence about that and five paragraphs about what color you'd like the background to be. That's ridiculous. How the hell am I supposed to find that later? Especially since we already discussed this in the other email that sitting in my inbox.
I swear I am setting up a bug tracking system simply so that my clients can log in and leave me bug reports, and feature requests, and will stop filling up my poor email boxes with what amounts to piles and piles threads that I have to sort through.
For a person who suffers with a form of ADD this is extremely frustrating. Why is it so difficult for my colleagues and clients to write good emails with good subject lines, and reply to the right damn emails?
Am I just being too anal, or does this bother others as well?16 -
Earlier this year I had to deploy an "emergency" fix to production for (luckily) an internal facing, but customer impacting, web application.
It was only the login page they were changing. I backed up the original, copied the new file into place, and marked my task complete.
Then I went and read the details on the incident. Someone discovered that if you supply ANY valid username and leave the password blank, you're in! Put the wrong password and you're blocked, of course. But blank? You must be legit!
Curious, I looked at the timestamp on the original file I had backed up to see how long it had been like this.
4 years.2 -
A few days ago Aruba Cloud terminated my VPS's without notice (shortly after my previous rant about email spam). The reason behind it is rather mundane - while slightly tipsy I wanted to send some traffic back to those Chinese smtp-shop assholes.
Around half an hour later I found that e1.nixmagic.com had lost its network link. I logged into the admin panel at Aruba and connected to the recovery console. In the kernel log there was a mention of the main network link being unresponsive. Apparently Aruba Cloud's automated systems had cut it off.
Shortly afterwards I got an email about the suspension, requested that I get back to them within 72 hours.. despite the email being from a noreply address. Big brain right there.
Now one server wasn't yet a reason to consider this a major outage. I did have 3 edge nodes, all of which had equal duties and importance in the network. However an hour later I found that Aruba had also shut down the other 2 instances, despite those doing nothing wrong. Another hour later I found my account limited, unable to login to the admin panel. Oh and did I mention that for anything in that admin panel, you have to login to the customer area first? And that the account ID used to login there is more secure than the password? Yeah their password security is that good. Normally my passwords would be 64 random characters.. not there.
So with all my servers now gone, I immediately considered it an emergency. Aruba's employees had already left the office, and wouldn't get back to me until the next day (on-call be damned I guess?). So I had to immediately pull an all-nighter and deploy new servers elsewhere and move my DNS records to those ASAP. For that I chose Hetzner.
Now at Hetzner I was actually very pleasantly surprised at just how clean the interface was, how it puts the project front and center in everything, and just tells you "this is what this is and what it does", nothing else. Despite being a sysadmin myself, I find the hosting part of it insignificant. The project - the application that is to be hosted - that's what's important. Administration of a datacenter on the other hand is background stuff. Aruba's interface is very cluttered, on Hetzner it's super clean. Night and day difference.
Oh and the specs are better for the same price, the password security is actually decent, and the servers are already up despite me not having paid for anything yet. That's incredible if you ask me.. they actually trust a new customer to pay the bills afterwards. How about you Aruba Cloud? Oh yeah.. too much to ask for right. Even the network isn't something you can trust a long-time customer of yours with.
So everything has been set up again now, and there are some things I would like to stress about hosting providers.
You don't own the hardware. While you do have root access, you don't have hardware access at all. Remember that therefore you can't store anything on it that you can't afford to lose, have stolen, or otherwise compromised. This is something I kept in mind when I made my servers. The edge nodes do nothing but reverse proxying the services from my LXC containers at home. Therefore the edge nodes could go down, while the worker nodes still kept running. All that was necessary was a new set of reverse proxies. On the other hand, if e.g. my Gitea server were to be hosted directly on those VPS's, losing that would've been devastating. All my configs, projects, mirrors and shit are hosted there.
Also remember that your hosting provider can terminate you at any time, for any reason. Server redundancy is not enough. If you can afford multiple redundant servers, get them at different hosting providers. I've looked at Aruba Cloud's Terms of Use and this is indeed something they were legally allowed to do. Any reason, any time, no notice. They covered all their bases. Make sure you do too, and hope that you'll never need it.
Oh, right - this is a rant - Aruba Cloud you are a bunch of assholes. Kindly take a 1Gbps DDoS attack up your ass in exchange for that termination without notice, will you?4 -
Fun though practical question.
You've accidentaly pasted and sent some internally used password, let it be your account pw or some server's root pw, into a company's chat channel with 100+ other employees. What do you do next? :)
P.S. deleting the message is not possible
P.P.S. this happens. Thanks to windows "Let me just quickly change window focus from putty to chat window" _FEATURE_ I've accidentally shared like a dozen of root passwords with others.11 -
I think I want to quit.
I know it’s a bit of an inconvenient time with there being corona around but everything was okay up till January. I’m a junior even though I shouldn’t be. Since my manager told me and my team leader senior in my review “maybe you two should switch jobs” things have been going downhill. I think the team lead had it out for me and didn’t put me on a new project, I’ve been left with doing stupid basic shit like updating text on websites in a cms and doing fuck all and then there’s also another guy that was basically harassing me trying to put me in my place any time I was doing better than him and literally both of them been like that ... and now that I’m working from home it’s even worse. I don’t have any kind of assurance that everything okay and actually I think I’m being framed as welll since I found keyloggers on my work laptop and deleted cleaned shit up the past two weeks and changed my WiFi security as there were like 5 unknown devices on our network so yeah .. I’ve been framed and they made it out like I put a powershell script on one of the servers and it crashed a Porsche website for 8 h and all kinds of bullshit - this was yday. On Tuesday they logged me out of everything like changed the password for work vpn and kicked me out of slack and Microsoft teams for over 2 hours till the end of shift and two managers weren’t answering their phone and then next day my manager called and apologised that saying that he “accidentally” did that to me along with 15 people they let go from the company....
I’m seriously thinking of quitting being removed from team group for a moment , not being on a project and people literally trying to put me down after I know I’m genuinely smarter than them and if I had over 10 years experience like those on my team (I have 1) I’d be far higher up and better
They can genuinely just go fuck themseves !!!! And here I was going to work over weekend on something! No fucking way I just wanna quit or give in my notice but because of corona I’m divided7 -
A lot of larger companies seem to be a happy about forcing employees to change their password every three months or so. They do it for security measures so that it is more difficult to break through the system, however most people end up making the worst passwords.
Instead of forcing a very good password on them every year or two maybe, they all end up having passwords like: "Summer16", "Qwer1234", "London15".
I used to work for our national police, and this was the case there as well...7 -
Everyone here deserves the worst.
No, really, you all deserve those dark juicy stories. So here's why I hate password systems that don't have the user experience in mind.
Recently my university went under a huge update, most of it good, but this is DevRant, so let me tell you what's just the worst.
They asked me to change my password, they do this every month or two. So I did it, but as I clicked "Ok" a wild error appeared! It told me I had to use a password that was not one of the FIFTEEN that I'd used previously...
I tried everything, and despite everything else being poorly programmed, or what not, I thought it would be easy to spoof. Nope. Unfortunately this seems to be the ONE thing they did right. Looks like I'll have to go back to basics. Just add a number on the end of my previous password, up to fifteen, and reset :]
I think this rant needs to turn into an email headed straight to them :)3 -
Oh boy, this is gonna be good:
TL;DR: Digital bailiffs are vulnerable as fuck
So, apparently some debt has come back haunting me, it's a somewhat hefty clai and for the average employee this means a lot, it means a lot to me as well but currently things are looking better so i can pay it jsut like that. However, and this is where it's gonna get good:
The Bailiff sent their first contact by mail, on my company address instead of my personal one (its's important since the debt is on a personal record, not company's) but okay, whatever. So they send me a copy of their court appeal, claiming that "according to our data, you are debtor of this debt". with a URL to their portal with a USERNAME and a PASSWORD in cleartext to the message.
Okay, i thought we were passed sending creds in plaintext to people and use tokenized URL's for initiating a login (siilar to email verification links) but okay! Let's pretend we're a dumbfuck average joe sweating already from the bailiff claims and sweating already by attempting to use the computer for something useful instead of just social media junk, vidya and porn.
So i click on the link (of course with noscript and network graph enabled and general security precautions) and UHOH, already a first red flag: The link redirects to a plain http site with NOT username and password: But other fields called OGM and dossiernumer AND it requires you to fill in your age???
Filling in the received username and password obviously does not work and when inspecting the page... oh boy!
This is a clusterfuck of javascript files that do horrible things, i'm no expert in frontend but nothing from the homebrewn stuff i inspect seems to be proper coding... Okay... Anyways, we keep pretending we're dumbasses and let's move on.
I ask for the seemingly "new" credentials and i receive new credentials again, no tokenized URL. okay.
Now Once i log in i get a horrible looking screen still made in the 90's or early 2000's which just contains: the claimaint, a pie chart in big red for amount unpaid, a box which allows you to write an - i suspect unsanitized - text block input field and... NO DATA! The bailiff STILL cannot show what the documents are as evidence for the claim!
Now we stop being the pretending dumbassery and inspect what's going on: A 'customer portal' that does not redirect to a secure webpage, credentials in plaintext and not even working, and the portal seems to have various calls to various domains i hardly seem to think they can be associated with bailiff operations, but more marketing and such... The portal does not show any of the - required by law - data supporting the claim, and it contains nothing in the user interface showing as such.
The portal is being developed by some company claiming to be "specialized in bailiff software" and oh boy oh boy..they're fucked because...
The GDPR requirements.. .they comply to none of them. And there is no way to request support nor to file a complaint nor to request access to the actual data. No DPO, no dedicated email addresses, nothing.
But this is really the ham: The amount on their portal as claimed debt is completely different from the one they came for today, for the sae benefactor! In Belgium, this is considered illegal and is reason enough to completely make the claim void. the siple reason is that it's unjust for the debtor to assess which amount he has to pay, and obviously bailiffs want to make the people pay the highest amount.
So, i sent the bailiff a business proposal to hire me as an expert to tackle these issues and even sent him a commercial bonus of a reduction of my consultancy fees with the amount of the bailiff claim! Not being sneery or angry, but a polite constructive proposal (which will be entirely to my benefit)
So, basically what i want to say is, when life gives you lemons, use your brain and start making lemonade, and with the rest create fertilizer and whatnot and sent it to the lemonthrower, and make him drink it and tell to you it was "yummy yummy i got my own lemons in my tummy"
So, instead of ranting and being angry and such... i simply sent an email to the bailiff, pointing out various issues (the ones6 -
I don't understand how is possible that programmers today are developing applications that are storing plain password in the database.
I know it's kinda boring topic since everybody here is talking about it this week, but it's really confusing to me.
Every now and then some DB gets hacked, millions of passwords are leaked and then you have developers, who should be smart and logical people, who decide to do that.
Ok, maybe the project deadline was close or something similar, but I think there is no excuse for something like that. No matter how close or behind deadline project is, you should always be able to explain to your boss/client what could happen.3 -
Not as much of a rant as a share of my exasperation you might breathe a bit more heavily out your nose at.
My work has dealt out new laptops to devs. Such shiny, very wow. They're also famously easy to use.
.
.
.
My arse.
.
.
.
I got the laptop, transferred the necessary files and settings over, then got to work. Delivered ticket i, delivered ticket j, delivered the tests (tests first *cough*) then delivered Mr Bullet to Mr Foot.
Day 4 of using the temporary passwords support gave me I thought it was time to get with department policy and change my myriad passwords to a single one. Maybe it's not as secure but oh hell, would having a single sign-on have saved me from this.
I went for my new machine's password first because why not? It's the one I'll use the most, and I definitely won't forget it. I didn't. (I didn't.) I plopped in my memorable password, including special characters, caps, and numbers, again (carefully typed) in the second password field, then nearly confirmed. Curiosity, you bastard.
There's a key icon by the password field and I still had milk teeth left to chew any and all new features with.
Naturally I click on it. I'm greeted by a window showing me a password generating tool. So many features, options for choosing length, character types, and tons of others but thinking back on it, I only remember those two. I had a cheeky peek at the different passwords generated by it, including playing with the length slider. My curiosity sated, I closed that window and confirmed that my password was in.
You probably know where this is going. I say probably to give room for those of you like me who certifiably. did. not.
Time to test my new password.
*Smacks the power button to log off*
Time to put it in (ooer)
*Smacks in the password*
I N C O R R E C T L O G I N D E T A I L S.
Whoops, typo probably.
Do it again.
I N C O R R E C T L O G I N D E T A I L S.
No u.
Try again.
I N C O R R E C T L O G I N D E T A I L S.
Try my previous password.
Well, SUCCESS... but actually, no.
Tried the previous previous password.
T O O M A N Y A T T E M P T S
Ahh fuck, I can't believe I've done this, but going to support is for pussies. I'll put this by the rest of the fire, I can work on my old laptop.
Day starts getting late, gotta go swimming soonish. Should probably solve the problem. Cue a whole 40 minutes trying my 15 or so different passwords and their permutations because oh heck I hope it's one of them.
I talk to a colleague because by now the "days since last incident" counter has been reset.
"Hello there Ryan, would you kindly go on a voyage with me that I may retrace my steps and perhaps discover the source of this mystery?"
"A man chooses, a slave obeys. I choose... lmao ye sure m8, but I'm driving"
We went straight for the password generator, then the length slider, because who doesn't love sliding a slidey boi. Soon as we moved it my upside down frown turned back around. Down in the 'new password' and the 'confirm new password' IT WAS FUCKING AUTOCOMPLETING. The slidey boi was changing the number of asterisks in both bars as we moved it. Mystery solved, password generator arrested, shit's still fucked.
Bite the bullet, call support.
"Hi, I need my password resetting. I dun goofed"
*details tech support needs*
*It can be sorted but the tech is ages away*
Gotta be punctual for swimming, got two whole lengths to do and a sauna to sit in.
"I'm off soon, can it happen tomorrow?"
"Yeah no problem someone will be down in the morning."
Next day. Friday. 3 hours later, still no contact. Go to support room myself.
The guy really tries, goes through everything he can, gets informed that he needs a code from Derek. Where's Derek? Ah shet. He's on holiday.
There goes my weekend (looong weekend, bank holiday plus day flexi-time) where I could have shown off to my girlfriend the quality at which this laptop can play all our favourite animé, and probably get remind by her that my personal laptop has an i2350u with integrated graphics.
TODAY. (Part is unrelated, but still, ugh.)
Go to work. Ten minutes away realise I forgot my door pass.
Bollocks.
Go get a temporary pass (of shame).
Go to clock in. My fob was with my REAL pass.
What the wank.
Get to my desk, nobody notices my shame. I'm thirsty. I'll have the bottle from my drawer. But wait, what's this? No key that usually lives with my pass? Can't even unlock it?
No thanks.
Support might be able to cheer me up. Support is now for manly men too.
*Knock knock*
"Me again"
"Yeah give it here, I've got the code"
He fixes it, I reset my pass, sensibly change my other passwords.
Or I would, if the internet would work.
It connects, but no traffic? Ryan from earlier helps, we solve it after a while.
My passwords are now sorted, machine is okay, crisis resolved.
*THE END*
If you skipped the whole thing and were expecting a tl;dr, you just lost the game.
Otherwise, I absolve you of having lost the game.
Exactly at the char limit9 -
*follow-up to https://devrant.com/rants/1887422*
The burnt remnants of my ID card's authentication information, waiting for the wind to come pick it up. It's stored in my password database now and committed to my git server, as it should be. Storing PIN and PUK codes on paper, whatever government cunt thought thought that that was a good idea...
If you've got identification papers containing authentication information like PIN and PUK codes, by all means add them to your password manager (if you're using Linux, I'd like to recommend GNU Pass) at once and burn the physical version. There's no reason why you'd want those on paper, unless you store your passwords on a post-it too.
At least that's as much as me and possibly you as citizens can do. Our governments are doomed anyway, given the shitty security policy they have, and likely the many COBOL mainframes still in use today. Honestly, the meddlings of Russia with the US elections doesn't seem too far-fetched, given this status quo. It actually surprises me that this kind of stuff doesn't happen more often, given that certain governments hire private pentesters yet can't secure their own infrastructure.
-
Whelp. I started making a very simple website with a single-page design, which I intended to use for managing my own personal knowledge on a particular subject matter, with some basic categorization features and a simple rich text editor for entering data. Partly as an exercise in web development, and partly due to not being happy with existing options out there. All was going well...
...and then feature creep happened. Now I have implemented support for multiple users with different access levels; user profiles; encrypted login system (and encrypted cookies that contain no sensitive data lol) and session handling according to (perceived) best practices; secure password recovery; user-management interface for admins; public, private and group-based sections with multiple categories and posts in each category that can be sorted by sort order value or drag and drop; custom user-created groups where they can give other users access to their sections; notifications; context menus for everything; post & user flagging system, moderation queue and support system; post revisions with comparison between different revisions; support for mobile devices and touch/swipe gestures to open/close menus or navigate between posts; easily extendible css themes with two different dark themes and one ugly as heck light theme; lazy loading of images in posts that won't load until you actually open them; auto-saving of posts in case of browser crash or accidental navigation away from page; plus various other small stuff like syntax highlighting for code, internal post linking, favouriting of posts, free-text filter, no-javascript mode, invitation system, secure (yeah right) image uploading, post-locking...
On my TODO-list: Comment and/or upvote system, spoiler tag, GDPR compliance (if I ever launch it haha), data-limits, a simple user action log for admins/moderators, overall improved security measures, refactor various controllers, clean up the code...
It STILL uses a single-page design, and the amount of feature requests (and bugs) added to my Trello board increases exponentially with every passing week. No other living person has seen the website yet, and at the pace I'm going, humanity will have gone through at least one major extinction event before I consider it "done" enough to show anyone.
help4 -
Recent conversation with a client for our SaaS product.
Client: So why can't we delete this information.
Me: We want to able to know who made a change to the data to avoid getting into trouble with the law.
Client: Does that mean you can see all the data on our account?
Me: (I know where she is going but let me stall)..You are the only one with access to your account. If I don't know your password, I can't access your data.
Client: But you sound like you can see the information in the cloud.
Me: (Laughs softly and segued).. The additional features you requested would be.......
Someone needs to read the T&C... -
Oh I have quite a few.
#1 a BASH script automating ~70% of all our team's work back in my sysadmin days. It was like a Swiss army knife. You could even do `ScriptName INC_number fix` to fix a handful of types of issues automagically! Or `ScriptName server_name healthcheck` to run HW and SW healthchecks. Or things like `ScriptName server_name hw fix` to run HW diags, discover faulty parts, schedule a maintenance timeframe, raise a change request to the appropriate DC and inform service owners by automatically chasing them for CHNG approvals. Not to mention you could `ScriptName -l "serv1 serv2 serv3 ..." doSomething` and similar shit. I am VERY proud of this util. Employee liked it as well and got me awarded. Bought a nice set of Swarowski earrings for my wife with that award :)
#2 a JAVA sort-of-lib - a ModelMapper - able to map two data structures with a single util method call. Defining datamodels like https://github.com/netikras/... (note the @ModelTransform anno) and mapping them to my DTOs like https://github.com/netikras/... .
#3 a @RestTemplate annptation processor / code generator. Basically this dummy class https://github.com/netikras/... will be a template for a REST endpoint. My anno processor will read that class at compile-time and build: a producer (a Controller with all the mappings, correct data types, etc.) and a consumer (a class with the same methods as the template, except when called these methods will actually make the required data transformations and make a REST call to the producer and return the API response object to the caller) as a .jar library. Sort of a custom swagger, just a lil different :)
I had #2 and #3 opensourced but accidentally pushed my nexus password to gitlab. Ever since my utils are a private repo :/3 -
Today I was debugging some shitty code left by unknown developer whos linkedin account is dead and phone number left in contact card calls local pizza house.
I knew it qould be hard so i've made myself comfortable, gathered 5 redbulls and other items that diabetes people would kill for eating again.
After around 10 minutes i was already frustrated but i kept the pace. "Who is the best, little devie, you!" - I fooled my ego to keep up and shut up.
After around 10 next minutes my attention span has ended. Limbic system started injecting some hormones into my brain, but I remained silent.
First two energy shots were applied. I felt like hero again. Two minutes after I was debugging through some library that was written fo java and found out that it ahots some natives to a c lang lib called "mypreciouslib".
Oh flock, how can i debug it if ita compiled , I cannot do such things, Me be only junior dev. I started swearing, but silently.
Started ollydbg to see what is inside livrary, i searched through but i couldnt match anything it was like mess stirred with fecals of an elephant.
So I opened aida pro " with vitamins" cause obviously, our pm says "but you write in java right " so we dont need those tools right ? Fuck no.
Aida was better at least i could find some funcions calls, but hey, the progress. I was swearing out loud, with earplugs in. And by the time I've sweared all the things in company i got a reminder.
"Hey -insane- stop swearing, the children are here."-sayys pm, it is some kind of " family and work " shitfuck day.
So i asked them: " why wouldnt you buy this fucking tools for programmming for us , you wouldnt have to hear me fucking swearing" . then i realized that , colleagues in room heard all of it, and one of them, total fuckface buttlicker(dev without bit of knowledge) started something like "you are wrong, see how good our software is sellling". Pm was like smiling like he thanked him for buttlicking again. Not to mention he is officially retarded and i know his password to all our services cause he is so smart to put it into text file and then have sharing files in windows turned on.
The other one told aloud, that we would be much better with some debugging tools that are better than fucking eclipse if we have to work without code.
PM told us that he will arrange a meeting. At that point I didnt care any longer. I just fired myself, fuck them.
Please saint Stallman give me hope and joy of programming from my teenage years. Uhhh..2 -
Currently working on my first real REST api and I've arrived at the authentication part.
I'm not sure how to do this one, the client will have to login using username/password but then, what's the most conventional way of authentication logged in users through a REST api? (no oauth (yet))
This should be usable for anything like ajax requests to calls from the backend to curl requests.
Looking forward to ideas!30 -
All these “top password” lists appearing.. Who audits this? Like ain’t that stuff supposed to be cooked with some salt or something?4
-
!rant
Need some opinions. Joined a new company recently (yippee!!!). Just getting to grips with everything at the minute. I'm working on mobile and I will be setting up a new team to take over a project from a remote team. Looking at their iOS and Android code and they are using RxSwift and RxJava in them.
Don't know a whole lot about the Android space yet, but on iOS I did look into Reactive Cocoa at one point, and really didn't like it. Does anyone here use Rx, or have an opinion about them, good or bad? I can learn them myself, i'm not looking for help with that, i'm more interested in opinions on the tools themselves.
My initial view (with a lack of experience in the area):
- I'm not a huge fan of frameworks like this that attempt to change the entire flow or structure of a language / platform. I like using third party libraries, but to me, its excessive to include something like this rather than just learning the in's / out's of the platform. I think the reactive approach has its use cases and i'm not knocking the it all together. I just feel like this is a little bit of forcing a square peg into a round hole. Swift wasn't designed to work like that and a big layer will need to be added in, in order to change it. I would want to see tremendous gains in order to justify it, and frankly I don't see it compared to other approaches.
- I do like the MVVM approach included with it, but i've easily managed to do similar with a handful of protocols that didn't require a new architecture and approach.
- Not sure if this is an RxSwift thing, or just how its implemented here. But all ViewControllers need to be created by using a coordinator first. This really bugs me because it means changing everything again. When I first opened this app, login was being skipped, trying to add it back in by selecting the default storyboard gave me "unwrapping a nil optional" errors, which took a little while to figure out what was going on. This, to me, again is changing too much in the platform that even the basic launching of a screen now needs to be changed. It will be confusing while trying to build a new team who may or may not know the tech.
- I'm concerned about hiring new staff and having to make sure that they know this, can learn it or are even happy to do so.
- I'm concerned about having a decrease in the community size to debug issues. Had horrible experiences with this in the past with hybrid tech.
- I'm concerned with bugs being introduced or patterns being changed in the tool itself. Because it changes and touches everything, it will be a nightmare to rip it out or use something else and we'll be stuck with the issue. This seems to have happened with ReactiveCocoa where they made a change to their approach that seems to have caused a divide in the community, with people splitting off into other tech.
- In this app we have base Swift, with RxSwift and RxCocoa on top, with AlamoFire on top of that, with Moya on that and RxMoya on top again. This to me is too much when only looking at basic screens and networking. I would be concerned that moving to something more complex that we might end up with a tonne of dependencies.
- There seems to be issues with the server (nothing to do with RxSwift) but the errors seem to be getting caught by RxSwift and turned into very vague and difficult to debug console logs. "RxSwift.RxError error 4" is not great. Now again this could be a "way its being used" issue as oppose to an issue with RxSwift itself. But again were back to a big middle layer sitting between me and what I want to access. I've already had issues with login seeming to have 2 states, success or wrong password, meaning its not telling the user whats actually wrong. Now i'm not sure if this is bad dev or bad tools, but I get a sense RxSwift is contributing to it in some fashion, at least in this specific use of it.
I'll leave it there for now, any opinions or advice would be appreciated.question functional programming reactivex java library reactive ios functional swift android rxswift rxjava18 -
Over the past 2 months I have interviewed with several companies and 2 of them stood out at rejecting me. Let's call them Company A, and Company B!
> I know right? Developers are bad at naming!
I guess part of it is my fault too! I am old and slow. Doesn't like competitive programming and already forgot most of how to answer algorithm question. I can't even answer some of the algorithm question I've flawlessly answered back when I was fresh out of University.
## Company A
When I got chance to interview at Company A, they require me to answer HackerRank style interview. It's my first time in nearly a decade of working in the industry to feel like I'm in a classroom exam again. I hate it, and I deliberately voiced my distaste to the answers comment:
// Paraphrasing
// I'm sorry, I'm dumb!
// I never faced anything like this in real world work...
// ......
But guess what? My answer still pass the score, have a call with their VP, which proceed to have another call with their Lead Engineer.
Talked about my experience with Event Driven System and CQRS+ES and they decided that I am:
- Arrogant
- Too RND in my tech stack
- And overkill in CQRS+ES
And decided they don't need me.
They hate me for having a headstrong personality which translates as Arrogance to the perceiving end.
## Company B
Another HackerRank style interview. Guess I passed their score this time without me typing some strong comment and proceed to have another test with their Lead Engineer.
This time they want 5 question answered in google docs within 60 minutes.
Two of them stood out to me for being impossible to work on 12 minutes (60 / 5 if you're wondering). Or maybe I'm just old and dumb?!
The others are just questions copied word for word from Geeks For Geeks.
One of the question requires me to write a password brute force attack to an imaginary API.
The other requires me to find a combination of math `+` or `-` operation from `a strings of numbers` that results in `a number`.
My `Arrogance` kicks in and I start typing a comment
// Paraphrasing
// I am sorry but I feel this is impossible for me to think of in 12 minutes
// (60 / 5 if you're wondering)
// But I know you guys got this question from Rosseta Code!
// Here's the link, but I don't know the logic behind it
See? I've worked on this question back when I was still a University student and remember where to look at.
Unsurprisingly, I've heard the feedback that I was rejected although I've answered one of their question `FLAWLESSLY`. I know they are being sarcastic at this point. haha.
---
I was trying to be honest about what I can and can't do in the `N` minutes timeframe and the Industry hates me.
I guess The Industry love people who can grind `GFG` or other algorithm websites, remember the solutions out of their head, and quietly answer their `genuinely original question` without pointing the flaws back at them.9 -
telco sysadmin: hey maybe we should secure our SMTP server with SSL and password verification so our clients can e-mail safely!
senior exec be like: nah just filter incoming connections for our own IP-range, that'll do.
result: I can impersonate any client of the telco and send e-mail in their name (from any home network connected to that provider), but I can't send e-mail over cellular network.1 -
Let's talk about the cargo cult of N-factor authentication. It's not some magic security dust you can just sprinkle onto your app "for security purposes".
I once had a client who had a client who I did server maintenance for. Every month I was scheduled to go to the site, stick my fingerprint in their scanner, which would then display my recorded face prominently on their screens, have my name and purpose verified by the contact person, and only then would the guards let me in.
HAHA no of course not. On top of all of that, they ask for a company ID and will not let me in without one.
Because after all, I can easily forge my face, fingerprints, on-site client contact, appointment, and approval. But printing out and laminating a company ID is impossible.
---
With apologies to my "first best friend" in High School, I've forgotten which of the dozens of canonicalisations of which of your nicknames I've put in as my answer to your security question. I've also forgotten if I actually listed you as my first best friend, or my dog - which would actually be more accurate - and actually which dog, as there are times in my High School life that there were more tails than humans in the house.
I have not forgotten these out of spite, but simply because I have also forgotten which of the dozen services of this prominent bullshit computer company I actually signed up for way back in college, which itself has been more than a decade ago. That I actually apparently already signed up for the service before actually eludes me, because in fact, I have no love for their myriad products.
What I have NOT forgotten is my "end of the universe"-grade password, or email, or full legal name and the ability to demonstrate a clear line of continuity of my identity from wherever that was to now.
Because of previous security screwups in the past, this prominent bullshit company has forced its users to activate its second, third, and Nth factors. A possibly decade-old security question; a phone number long lost; whatever - before you can use your account.
Note: not "view sensitive data" about the account, like full name, billing address, and contact info. Not "change settings" of the account, such as changing account info, email, etc. Apparently all those are the lowest tier of security meant to be protected by mere "end of the universe"-grade passwords and a second factor such as email, which itself is likely to be sold by a company that also cargo cults N-factor auth. For REAL hard info, let's ask the guy who we just showed the address to "What street he lived in" and a couple others.
Explaining this to the company's support hotline is an exercise in...
"It's for your security."
"It's not. You're just locking me out of my account. I can show you a government ID corroborating all the other account info."
"But we can't, for security."
"It's not security. Get me your boss."
...
"It's for security."8 -
The hand of IT guy in family
My family sees me as guy who works on IT stuff. The best part is that I will have to help them whenever they encounter problem regarding electronics in daily activities.
Son! The internet is not working
Son! The printer is not working
Son! The TV is not working
Son! My phone didnt get any signals
Son! The microwave is not working
Son! The TV remote is not working
Son! Why is this whatsapp popup always appear whenever I opened it
Son! The dvd player is not working
Son! My phone wont charged
Son! I want to buy online stuff
Son! The email that ur uncle sent me cannot be opened
Son! The email that ur aunt sent me is not there
Son! Can u help me download this travelling app
Son! I opened a website and it told me that I have 163718362 virus!
Son! I forget my password of my facebook account!
Son! Some guy idk on facebook added me as his/her friends, what should i do?
....
Son! The internet is not working (again)
The fact is that, most if these problem, I helped them by just.. restarting the router, reboot the router for 1 min interval, find specific toggler in disfunctional hardware that they accidentally hit during sweeping the floor, take out the power and put it back again, show them how to's in many account/payment mechanism in apps, etc
The very best part that whenever they satisfied, whenever things back to work again, whenever they can reset the password:
"I've tried what you told me, but it just didnt work, but idk when u did it, it works! you are really an IT guy"
And i was like
🙃4 -
oh FFS my university pissed me off so bad right now that I had to wait 20 min to cool down to be able to write a rant about it...
so, one of the university department offer an email address which is the official university approved email for student packs like jetbrain's. I wanted to renew my jetbrains subscription, but for that I have to get a verification email on that address..
But since the only time I use it is this annual renewal I dont know the webmail's url..
So I search for it on the department pages, services and its nowhere to be found. Finaly I found it on a student maintained wiki page.
I try to log in.. no luck. try another password, still not it. Try all of the passwords that I remember using in the previous 3 year and no luck.
well fck it the password change is managed by a website where I can log in with a different method, so I change the password and try to log in again.
No fcking luck! And at this point I bashed my head against the wall because I found out that the password change takes them about 1 or 2 hours... hours! wtf...5 -
Fire your whole fucking web team Bethesda
* Your design is a classic ipecac. Whatever the fuck you are doing doesn't in frontend doesn't justify the 4Mb of bandwidth I wasted on a single js file. Why the fuck can I see the whole fucking node_modules directory when looking at the sources?
I know this is supposed to be a webpage for a game development studio, but I'm seriously wondering if your budget would even get me a prostitute.
I'm a greedy fuck and want a free game. apparently your servers are only good enough to register me, but login is apparently too much to ask for. Yeah sure. Oh and also thank you for choosing an "incorrect username and password" error message by default, even though your fucking gateway timed out. Please be kind enough and punch me directly into my face next time. Not like I'll ever access that shit ever again3 -
Okay so my brother in law has a laptop that is... To put it mildly, chockful of viruses of all sort, as it's an old machine still running w7 while still being online and an av about 7 years out of date.
So my bro in law (let's just call him my bro) asked me to install an adblock.
As I launched chrome and went to install it, how ever, the addon page said something like "Cannot install, chrome is managed by your company" - wtf?
Also, the out of date AV couldn't even be updated as its main service just wouldn't start.
Okay, something fishy going on... Uninstalled the old av, downloaded malware bytes and went to scan the whole pc.
Before I went to bed, it'd already found >150 detections. Though as the computer is so old, the progress was slow.
Thinking it would have enough time over night, I went to bed... Only to find out the next morning... It BSoD'd over night, and so none of the finds were removed.
Uuugh! Okay, so... Scanning out of a live booted linux it is I thought! Little did I know how much it'd infuriate me!
Looking through google, I found several live rescue images from popular AV brands. But:
1 - Kaspersky Sys Rescue -- Doesn't even support non-EFI systems
2 - Eset SysRescue -- Doesn't mount the system drive, terminal emulator is X64 while the CPU of the laptop is X86 meaning I cannot run that. Doesn't provide any info on username and passwords, had to dig around the image from the laptop I used to burn it to the USB drive to find the user was, in fact, called eset and had an empty password. Root had pass set but not in the image shadow file, so no idea really. Couldn't sudo as the eset user, except for the terminal emulator, which crashes thanks to the architecture mismatch.
3 - avast - live usb / cd cannot be downloaded from web, has to be installed through avast, which I really didn't want to install on my laptop just to make a rescue flash drive
4 - comodo - didn't even boot due to architecture mismatch
Fuck it! Sick and tired of this, I'm downloading Debian with XFCE. Switched to a tty1 after kernel loads, killed lightdm and Xserver to minimize usb drive reads, downloaded clamav (which got stuck on man-db update. After 20 minutes... I just killed it from a second tty, and the install finished successfully)
A definitions update, short manual skimover, and finally, got scanning!
Only... It's taking forever and not printing anything. Stracing the clamscan command showed it was... Loading the virus definitions lol... Okay, it's doing its thing, I can finally go have dinner
Man I didn't know x86 support got so weak in the couple years I haven't used Linux on a laptop lol.8 -
As someone who uses UNIX and UNIX-like systems on a daily basis, and someone dealing with computer support in a school, I experience so, so many issues, many of which others have already ranted about.
For no reason at all, I find it incredibly frustrating how many high school students' understanding of sudo is limited to this:
Student: Hey, isn't sudo the minecraft command
Me: Erm
Student: You know, the one skeppy uses... to troll players? Anyway, you're doing it wrong. There should be a slash before you run the command
Me: aaargh.
and so on. Happens probably every 10th time I invoke sudo.
I mean, really? Surely these kids, with all their complaints and lines: hacking into the mainframe/whats the admin password/why did you block my VPN/ and so on, would know what sudo is. But NO, they just don't seem to get it. Sometimes I lose my hope in the futures of these kids.5 -
Am I the only developer in existence who's ever dealt with Git on Windows? What a colossal train wreck.
1. Authentication. Since there is no ssh key/git url support on Windows, you have to retype your git credentials Every Stinking Time you push. I thought Git Credential Manager was supposed to save your credentials? And this was impossible over SSH (see below). The previous developer had used an http git URL with his username and password baked in for authentication. I thought that was a horrific idea so I eventually figured out how to use a Bitbucket App password.
2. Permissions errors
In order to commit and push updates, I have to run Git for Windows as Administrator.
3. No SSH for easy git access
Here's where I confess that this is a Windows Server machine running as some form of production. Please don't slaughter me! I am not the server admin.
So, I convinced the server guy to find and install some sort of ssh service for Windows just for the off times we have to make a hot fix in production. (Don't ask, but more common than it should be.)
Sadly, this ssh access is totally useless as the git colors are all messed up, the line wrap length and window size are just weird (seems about 60 characters wide by 25 lines tall) and worse of all I can't commit/push in git via ssh because Permissions. Extremely aggravating.
4. Git on Windows hangs open and locks the index file
Finally, we manage to have Git for Windows hang quite frequently and lock the git index file, meaning that we can't do anything in git (commit, push, pull) without manually quitting these processes from task manager, then browsing to the directory and deleting the .git/index.lock file.
Putting this all together, here's the process for a pull on this production server:
Launch a VNC session to the server. Close multiple popups from different services. Ask Windows to please not "restart to install updates". Launch git for Windows. Run a git pull. If the commits to be pulled involve deleting files, the pull will fail with a permissions error. Realize you forgot to launch as Administrator. Depending on how many files were deleted in the last update, you may need to quit the application and force close the process rather than answer "n" for every "would you like to try again?" file. Relaunch Git as Administrator. Run Git pull. Finally everything works.
At this point, I'd be grateful for any tips, appreciate any sympathy, and understand any hatred. Windows Server is bad. Git on Windows is bad.9 -
Sharing your password with your coleagues is like sharing your underwear or your GF with them. It's not right and unless you're into some weird fetish you won't really want them back...
I've been asked to help in my previous project and I'm fairly certain my credentials are expired/locked/forgotten there. Guess whose managers will be encouraging sharing current dev's on that project passwords...2 -
My boss insists that we shouldn’t lock or password-protect a particular system because, in her words, remembering or write down a password is hard and email as a concept is confusing. I tried to explain if people who don't know what left versus right-clicking do have full admin access, it’s only a matter of time before something goes terriblely wrong. She listened but ultimately decided to keep everything open, confident that everyone would use it responsibly.
Unfortunately, that’s not what happened, it never has been and never will be. The problems started, just as I feared, and now I’m stuck cleaning up the chaos, one issue at a time. I do have a backup and automation snapshots, but things got so tangled up that it will still be a hassle.
I tried soft lock so everyone could only access the section relevant to them. The reaction was immediate—they were confused and stressed, saying they’d be unable to do anything if it stayed that way. They didn’t get the idea that keeping them from touching certain things (that they shouldn't be touching in the first place) wasn’t the same as blocking their whole work. But since they’re all my superiors, I had no choice but to remove the restrictions and leave the system wide open again.
Nothing serious came out, just really annoying because something like this happens all the time.4 -
More emarassing than frustrating..But I was applying to a couple internal positions recently and decided to bring in a sample package to demonstrate some of what I had been working on in my current team. They seemed to like the example and the interview seemed to go well...A couple hours later one of the managers came by my cubicle and asked "is that the real password?" and pointed to a line in the code. Sure enough, I had left a plain text password in the script I had just handed out to 10 panelists at 2 interviews..proceeded to collect the packets back. In the future I'll be paying closer attention to what I include lol.
Still frustrated we keep the passwords in the script though >.> any suggestions for better storage of passwords and the like in Perl scripts?3 -
***ILLEGAL***
so its IPL(cricket) season in india, there is a OTT service called hotstar (its like netflix of india), the cricket streams exclusively on hotstar..
so a quick google search reveals literally thousands of emails & passwords, found a pastebin containing 500 emails&passwords ...but those are leaked last year most of passwords are changed & many of them enabled 2FA.. after looking through them we can find some passwords are similar to their emails , some contains birth year like 1975,1997 etc, some passwords end with 123 ..so after trying a few different versions of the passwords like
1) password123 -> password@123, password1234
2) passwordyear -> password@year
2) for passwords similar to emails, we can add 123 ,1234, @ etc
created a quick python script for sending login requests
so after like 30-40 mins of work, i have 7 working accounts
*for those who have basic idea of security practices you can skip this part
lessons learnt
1) enable 2FA
2) use strong passwords, if you change your password , new password should be very different from the old one
there are several thousands of leaked plaintext passwords for services like netflix,spotify, hulu etc, are easily available using simple google search,
after looking through & analysing thousands of them you can find many common passwords , common patterns
they may not be as obvious as password ,password123 but they are easily guessable.
mainly this is because these type of entertainment services are used by the average joe, they dont care about strong passwords, 2FA etc6 -
The university I used to study CSE, they had some OLD computers with Windows XP in them. Also, all those computers had TWO user accounts. One with the admin access and another one with normal access. Until this, it was fine.
But the browsers installed there were so old, even normal website struggles to load properly. and so many outdated apps, kept bugging us for update, but every time we click on UPDATE, they ask for the admin password, which we didn't have. So, most of the students were frustrated about this, but nobody took any action! :/
So, I hacked one of the computers' admin password. the password was "BRIGHT". I'm like, these people are never gonna set different passwords in different computers and remember them for eternity. Definitely all passwords have to be the same, and they were! Which saved my time.
So, I shared the password with everyone in my class and now they can install any apps they want. Which made me so happy!
But You know, words travel fast! Just one day after the hacking incident, the Seniors ( & the juniors ) came to me with their laptops to find their forgotten password, which made me earn some money & eat some delicious foods, also got to meet some beautiful girls of our campus ^_^
& I used to go to other classes to hack those Admin passwords for fun ^_^ But I never told them the password until they pay me or feed me something delicious! ^_^
I miss those good old days! ^_^6 -
Went through changing Apple ID email. I have 💻,📱and⌚️.
Felt like that horror movie moment when protagonist tries to be stealthy but makes a noise and a huge mob of zombies turn heads all at once. For what I love apple, the simplicity, in the email changing process there is none of that.
They forced me to enter my 60 arbitrary obscure characters password on Apple Watch screen.
On the other hand I felt nostalgic. When I was using Linux this all was my day to day experience no matter the distro, and I got a Linux Foundation certificate, I contributed to Elementary. Can’t imagine the experience of a user who just switched to Linux.
Windows? I don’t want to think about that, let alone talking. You only need to know that I successfully configured a SoE setup AND active directory in ad-hoc unstable network of literally rusty old computers. And I still switched to Linux back then.4 -
When I was in 11th class, my school got a new setup for the school PCs. Instead of just resetting them every time they are shut down (to a state in which it contained a virus, great) and having shared files on a network drive (where everyone could delete anything), they used iServ. Apparently many schools started using that around that time, I heard many bad things about it, not only from my school.
Since school is sh*t and I had nothing better to do in computer class (they never taught us anything new anyway), I experimented with it. My main target was the storage limit. Logins on the school PCs were made with domain accounts, which also logged you in with the iServ account, then the user folder was synchronised with the iServ server. The storage limit there was given as 200MB or something of that order. To have some dummy files, I downloaded every program from portableapps.com, that was an easy way to get a lot of data without much manual effort. Then I copied that folder, which was located on the desktop, and pasted it onto the desktop. Then I took all of that and duplicated it again. And again and again and again... I watched the amount increate, 170MB, 180, 190, 200, I got a mail saying that my storage is full, 210, 220, 230, ... It just kept filling up with absolutely zero consequences.
At some point I started using the web interface to copy the files, which had even more interesting side effects: Apparently, while the server was copying huge amounts of files to itself, nobody in the entire iServ system could log in, neither on the web interface, nor on the PCs. But I didn't notice that at first, I thought just my account was busy and of course I didn't expect it to be this badly programmed that a single copy operation could lock the entire system. I was told later, but at that point the headmaster had already called in someone from the actual police, because they thought I had hacked into whatever. He basically said "don't do again pls" and left again. In the meantime, a teacher had told me to delete the files until a certain date, but he locked my account way earlier so that I couldn't even do it.
Btw, I now own a Minecraft account of which I can never change the security questions or reset the password, because the mail address doesn't exist anymore and I have no more contact to the person who gave it to me. I got that account as a price because I made the best program in a project week about Java, which greatly showed how much the computer classes helped the students learn programming: Of the ~20 students, only one other person actually had a program at the end of the challenge and it was something like hello world. I had translated a TI Basic program for approximating fractions from decimal numbers to Java.
The big irony about sending the police to me as the 1337_h4x0r: A classmate actually tried to hack into the server. He even managed to make it send a mail from someone else's account, as far as I know. And he found a way to put a file into any account, which he shortly considered to use to put a shutdown command into autostart. But of course, I must be the great hacker.3 -
Ibwish I had remembered this when the weekly theme was office pranks.
In the first or second year of high school we covered basic internet security. Stuff like don't follow suspicious urls, don't open suspicious emails and such.
Our teacher let us play around with some sort of simulated desktop environment, where we could execute some hacks like ad popups and such on each other's environment, if we fell for the trap.
Anyways, one hack I found interesting was a hack, that lockes a user out of their virual desktop, until he enters a password, that will be displayed on his environment.
Yes, a very interesting hack, because it contains two obvious yet major design flaws, which I could exploit 😈
1. It's case sensitive
In itself not a problem, but combined with #2, it's fatal.
2. "IlIlllIlI"
Depending on your font, you probably have no idea what exactly I just typed.
Let's just say, the font displayed uppercase i and lowercase L completely undifferentiable.
Guess whom I let suffer.
It was our teacher, who had to demonstrate us some things and who was connected to the same network.
I swear, nothing beats that feeling when your tearcher has go come to you and embarrassingly ask you to "unhack" them, because they can't type it 😂1 -
any fucker who has written code for the indian ewaybill portal needs to be fucking assassinated. couldn't even get a simple aspx login page to work. motherfuckers.
They just display a message that if we are having troubles we should try clearing our cache.
Like for fucks sake build it properly. This is the main source of income for this fucking nation, probably.
- the password reset doesn't work.
- the userid reset doesn't work.
- sometimes i show up as not registered. i just fucking transacted yesterday you buffoons.
- there is an error alert, that says "error". i god fucking know there is an error. please fucking tell how may we please your ass to bypass those fucking errors 😭.
fuck every developer that works for that portal 😤. Good for nothings.
thanks for creating devrant, dfox and trogus. feels better now 😌.7 -
Since, I am already using Mullvad's vpn service, I also stumbled on https proxies.
Is it still safe to enter my devRant login data, when I would use a https proxy in FF's settings?
The Proxy is a free elite https proxy.
And devRant also uses SSL.
The traceroute would seem like this I guess.:
VPN(*le me sendin my password -> SSL Proxy -> SSL DevRant)
--------------------
Following that path, I would assume that it would be like this in detail:
HTTPS Request
-PW gets encrypted by VPN service
-" " " again " HTTPS Proxy
-" " " again " devRant itself9 -
Windows 10 Action Center yesterday alerted me to set a PIN for my laptop.
Turned on PC this morning and typed in my regular password then realized it wanted the PIN.
Thinking how this feature came to be....
1. Windows wants you to link your login to your Microsoft/Hotmail Account and it makes it a pain in the ass to set a seperate one (Windows 8)
2. 2018 arrived an logins are a pain, everything is autologin or PIN/code based (aka short 'unsecure' passwords)
3. MS backtracks and realizes email logins are too long so they make a partial fix which basically reverts back to the pre-Win8 days of a seperate system login.. except now its called a new feature!
I realized now under enter a PIN the reason for the checkbox that says: Allow symbols and letters. It's a nice way of saying: please type in your old password again.
**Also rant #2: cuz i dont feel like waiting 1hr**
I felt great yesterday when my boss told me apparantly I have like an Expert designation at the company.
Feel like crap today cuz some user is complaining about some report:
- they asked us to create months ago
- now complaining its all wrong but never gave any formal requirements and actually did sign off on it during testing
- FIXED ASAP
HELLO!!!!!!!!!!! STOP MAKING IT SOUND LIKE IT'S MY FAULT U CAN'T BE BOTHERED TO PROVIDE CLEAR REQUIREMENTS AND THEN TAKING FOREVER TO COME BACK WITH UR PROBLEMS AND NOW NEED IT FIXED ASAP BY USING A NEW DATA SOURCE THAT I HAVE NO IDEA WHAT THE FUCK IS SINCE U USED A RANDOM ABBREVIATION LIKE I CAN MIND READ.
IF I COULD MINDREAD, ID BE WORKING ON A PLAN TO GET UR ASS FIRED.....
Happy friday and long weekend... Got 3 days to relax before i need to deal with this shit again...2 -
I hate this company so much. I was tasked to write a simple program wrapped in an API. They gave me freedom of choice to use any language and technology because I said it'll be deployed in docker anyway.
Now, when they gave me the server, it's Windows Server 2016, of course, without docker installed (or even supported in any way). The access is done via TeamViewer for which I receive ID and password by calling a guy.
Oh, and everything runs as admin. "It's easier that way and we always do it like this."5 -
I discovered a commit message from one of my (senior) colleagues today. It made me shudder. It read, 'Just adding some changes made outside of source control and deployed (over last 12 months)'.
I genuinely think he can't follow any processes he didn't design. He controls the servers too, so it's not like any pipeline would prevent him from just doing what he wants. It's a bit scary to be honest, he thinks MD5 is a secure password hash! -
I need some opinions on Rx and MVVM. Its being done in iOS, but I think its fairly general programming question.
The small team I joined is using Rx (I've never used it before) and I'm trying to learn and catch up to them. Looking at the code, I think there are thousands of lines of over-engineered code that could be done so much simpler. From a non Rx point of view, I think we are following some bad practises, from an Rx point of view the guys are saying this is what Rx needs to be. I'm trying to discuss this with them, but they are shooting me down saying I just don't know enough about Rx. Maybe thats true, maybe I just don't get it, but they aren't exactly explaining it, just telling me i'm wrong and they are right. I need another set of eyes on this to see if it is just me.
One of the main points is that there are many places where network errors shouldn't complete the observable (i.e. can't call onError), I understand this concept. I read a response from the RxSwift maintainers that said the way to handle this was to wrap your response type in a class with a generic type (e.g. Result<T>) that contained a property to denote a success or error and maybe an error message. This way errors (such as incorrect password) won't cause it to complete, everything goes through onNext and users can retry / go again, makes sense.
The guys are saying that this breaks Rx principals and MVVM. Instead we need separate observables for every type of response. So we have viewModels that contain:
- isSuccessObservable
- isErrorObservable
- isLoadingObservable
- isRefreshingObservable
- etc. (some have close to 10 different observables)
To me this is overkill to have so many streams all frequently only ever delivering 1 or none messages. I would have aimed for 1 observable, that returns an object holding properties for each of these things, and sending several messages. Is that not what streams are suppose to do? Then the local code can use filters as part of the subscriptions. The major benefit of having 1 is that it becomes easier to make it generic and abstract away, which brings us to point 2.
Currently, due to each viewModel having different numbers of observables and methods of different names (but effectively doing the same thing) the guys create a new custom protocol (equivalent of a java interface) for each viewModel with its N observables. The viewModel creates local variables of PublishSubject, BehavorSubject, Driver etc. Then it implements the procotol / interface and casts all the local's back as observables. e.g.
protocol CarViewModelType {
isSuccessObservable: Observable<Car>
isErrorObservable: Observable<String>
isLoadingObservable: Observable<Void>
}
class CarViewModel {
isSuccessSubject: PublishSubject<Car>
isErrorSubject: PublishSubject<String>
isLoadingSubject: PublishSubject<Void>
// other stuff
}
extension CarViewModel: CarViewModelType {
isSuccessObservable {
return isSuccessSubject.asObservable()
}
isErrorObservable {
return isSuccessSubject.asObservable()
}
isLoadingObservable {
return isSuccessSubject.asObservable()
}
}
This has to be created by hand, for every viewModel, of which there is one for every screen and there is 40+ screens. This same structure is copy / pasted into every viewModel. As mentioned above I would like to make this all generic. Have a generic protocol for all viewModels to define 1 Observable, 1 local variable of generic type and handle the cast back automatically. The method to trigger all the business logic could also have its name standardised ("load", "fetch", "processData" etc.). Maybe we could also figure out a few other bits too. This would remove a lot of code, as well as making the code more readable (less messy), and make unit testing much easier. While it could never do everything automatically we could test the basic responses of each viewModel and have at least some testing done by default and not have everything be very boilerplate-y and copy / paste nature.
The guys think that subscribing to isSuccess and / or isError is perfect Rx + MVVM. But for some reason subscribing to status.filter(success) or status.filter(!success) is a sin of unimaginable proportions. Also the idea of multiple buttons and events all "reacting" to the same method named e.g. "load", is bad Rx (why if they all need to do the same thing?)
My thoughts on this are:
- To me its indentical in meaning and architecture, one way is just significantly less code.
- Lets say I agree its not textbook, is it not worth bending the rules to reduce code.
- We are already breaking the rules of MVVM to introduce coordinators (which I hate, as they are adding even more unnecessary code), so why is breaking it to reduce code such a no no.
Any thoughts on the above? Am I way off the mark or is this classic Rx?16 -
I'm trying to upgrade my account passwords etc. keepass (password manager) doesn't generate resizable windows, so when I want to generate a new password or do anything that creates a new window, THE NEW WINDOW IS TOO TALL FOR ME TO SEE WHAT'S AT THE BOTTOM AND THERE'S NOT EVEN THE OPTION TO SCROLL OR ZOOM OUT. YOU'RE OPEN SOURCE AND GIVING ME THIS BULLSHIT? If you were a living creature you'd be a giraffe with short stubby legs. Your missing features mean you don't get the best leaves and leave you dining with the rest of the peasants. At least I can interact with what I CAN see and closing the window prompts me to save changes, and passwords are generated by the rules I can actually see to manipulate.
Maybe I should look into the source or look at others' screenshots to see what I can't and tab into it to make blind changes, but I'm sufficiently happy with the passwords it gives already. I'm just pissed something so well rated has a flaw like that. Like a game where some levels are locked and you can't unlock them through play -_-2 -
ZNC shenanigans yesterday...
So, yesterday in the midst a massive heat wave I went ahead, booze in hand, to install myself an IRC bouncer called ZNC. All goes well, it gets its own little container, VPN connection, own user, yada yada yada.. a nice configuration system-wise.
But then comes ZNC. Installed it a few times actually, and failed a fair few times too. Apparently Chrome and Firefox block port 6697 for ZNC's web interface outright. Firefox allows you to override it manually, Chrome flat out refuses to do anything with it. Thank you for this amazing level of protection Google. I didn't notice a thing. Thank you so much for treating me like a goddamn user. You know Google, it felt a lot like those plastic nightmares in electronics, ultrasonic welding, gluing shit in (oh that reminds me of the Nexus 6P, but let's not go there).. Google, you are amazing. Best billion dollar company I've ever seen. Anyway.
So I installed ZNC, moved the client to bouncer connection to port 8080 eventually, and it somewhat worked. Though apparently ZNC in its infinite wisdom does both web interface and IRC itself on the same port. How they do it, no idea. But somehow they do.
And now comes the good part.. configuration of this complete and utter piece of shit, ZNC. So I added my Freenode username, password, yada yada yada.. turns out that ZNC in its infinite wisdom puts the password on the stdout. Reminded me a lot about my ISP sending me my password via postal mail. You know, it's one thing that your application knows the plaintext password, but it's something else entirely to openly share that you do. If anything it tells them that something is seriously wrong but fuck! You don't put passwords on the goddamn stdout!
But it doesn't end there. The default configuration it did for Freenode was a server password. Now, you can usually use 3 ways to authenticate, each with their advantages and disadvantages. These are server password, SASL and NickServ. SASL is widely regarded to be the best option and if it's supported by the IRC server, that's what everyone should use. Server password and NickServ are pretty much fallback.
So, plaintext password, default server password instead of SASL, what else.. oh, yeah. ZNC would be a server, right. Something that runs pretty much forever, 24/7. So you'd probably expect there to be a systemd unit for it... Except, nope, there isn't. The ZNC project recommends that you launch it from the crontab. Let that sink in for a moment.. the fucking crontab. For initializing services. My whole life as a sysadmin was a lie. Cron is now an init system.
Fortunately that's about all I recall to be wrong with this thing. But there's a few things that I really want to tell any greenhorn developers out there... Always look at best practices. Never take shortcuts. The right way is going to be the best way 99% of the time. That way you don't have to go back and fix it. Do your app modularly so that a fix can be done quickly and easily. Store passwords securely and if you can't, let the user know and offer alternatives. Don't put it on the stdout. Always assume that your users will go with default options when in doubt. I love tweaking but defaults should always be sane ones.
One more thing that's mostly a jab. The ZNC software is hosted on a .in domain, which would.. quite honestly.. explain a lot. Is India becoming the next Chinese manufacturers for software? Except that in India the internet access is not restricted despite their civilization perhaps not being fully ready for it yet. India, develop and develop properly. It will take a while but you'll get there. But please don't put atrocities like this into the world. Lastly, I know it's hard and I've been there with my own distribution project too. Accept feedback. It's rough, but it is valuable. Listen to the people that criticize your project.7 -
Those little assholes who code the web interfaces for the provider specific router. You also can't replace it with a fritzbox or something similar.
1. Password field only
2. Password field is no password field
3. This red internet thing doesn't tell me what's fucking wrong
4. The "diagnose" says everything is alright with my internet
5. It always complains because not every device in my network supports gigabit yet (there is an old switch). No reason to show everything in fucking red imo.
6. The things it lists I have to check can be and also should be checked by the fucking thing itself. Like wtf. They wanted a lot of money from me for this shitty thing and there is no temperature sensor to check if it's too hot.
7. It just stops working on hot days... Restart manually solves it. Let's restart manually from work when I have to access my files on my NAS from fucking 40 km away..
(see comments for more screenshots) 4
4 -
I deployed one of our staging websites to a free plan because the site is rarely used. Project Manager sends the stakeholders the new url. There will be a lot of 🤦♀️🤦♂️🤦 all around. Some of it’s my fault. A lot of it is just WTF.
Stakeholder: We still need the staging site because we don’t want to test in the live site…
PM: Okay. We didn’t say we were deleting the site. We are just moving it to a new and better hosting platform, so we’re letting you know the url has changed.
Stakeholder: This url is for the front facing page. How do I access the backend? [they mean the admin interface]
Me: The only thing that’s changed is the url for the staging website. So domain-A/account is now domain-B/account.
I thought that was a pretty straightforward way of explaining things, that even a non technical person would get it. They took the /account example as the literal login url.
Stakeholder: I forgot the password for our admin login and I submitted a password reset, but I realize I don’t know if I have access to the admin email. Or if it’s even a real email account.
WTF
I look back at the email chain and I realize that I gave the PM the wrong url.
Also, WTF x 2. How did this stakeholder not realize they were looking at the wrong website?? There are definitely noticeable style and content differences. And why would you have an admin login that uses a fake email??
Me: My apologies. I sent over the incorrect url. My instructions are mostly the same. All that’s changed is the domain.
Stakeholder’s assistant: [DMs me] How do we access the backend?
WTF…are they seriously playing this game and demanding I type out the url for them?! 🤬 I’m not playing this game and I just copy and paste the example that I already sent over.
They figure it out eventually. Apparently, they never used /account to login before They used /admin/index… but that would still bring them to /account, but with ?redirect=/admin/index appended to the url if they weren’t logged in. Again, WTF.
I know I made mistakes in this whole thing, but damn. I can’t even. I’m pretty sure this whole incident is fueling my boss’s push to stop supporting this particular website anymore so I can focus on sites that actually bring in revenue…and have stakeholders that aren’t looney and condescending like this.4 -
I have been trying to wrap my head around authentication in hapi for the last 6 hours...
Fuck this shit... when did simple,
I HAS A USERNAME
I HAS A PASSWORD
CAN HAS SESSION?
become:
- you magically get a token from somewhere
- you magically verify that token
- you respond with { credentials } //magic
- by some fucking black magic the server probably creates a session without you knowing about it...
- you freak out and write your own authentication scheme only to find out that you cannot read payload of POST requests in the authenticate method
- you get angrier and depressed and write a rant
(to be clear: there is @hapi/basic but I don't think sending a GET request with the URL looking like username:password@domain.tld is very safe...)11 -
This is another high school story. mostly because i’m in high school.
like most schools we have horrible forced passwords. Our school recently purchased microsoft 365. which means we all use outlook for our emails. the logins for our district follow the sand format.
s + first five of last name (x’s for missing letters) + first letter of your first name + the last three of your student id.
so for example Sean Peterson 456705 would be speters705. since we have outlook we can look up a persons name and get their email which gives you the last three of their password. All passwords start with a 4 and most are followed by a five so you pretty much can get 5 out of the 6 numbers in their password.
so to mess with my friends i signed into all of their accounts and messed with their emails so they thought they were getting random emails. and then i made word documents on all of their accounts and just pretty much messed with all of their school stuff.
so that’s my “hacking” story. my district doesn’t allow you to change your password so i’m pretty much stuck. pls help.4 -
Hey there people, I have a few questions regarding neo4j. Your experience could also be very useful to me here @dfox.
1. Is neo4j good for storing user data, like password hashes, etc.. In addition to the regular relationships with other components of the ecosystem
2. Is neo4j good enough to accommodate a really large number of users..
3. Does DevRant use a dual database, like user info in Mongo and relationships like comments and ++ on neo4j or is it like everything on neo4j
For q.3, if you're not @dfox then just provide an idea of how you would handle the situation.7 -
A long time ago you sent me an email with the subject 'I love you', I then got so excited that I forwarded the letter to all my contacts, and they forwarded it too.. I can't describe the words for the feelings I had back then for you. I felt into love with you, really. But there were always troubling moments for me.
For example when 'Code Red' showed up and found your backdoor. Man I was pissed at that time. I didn't know what to do next. But things settled, and we found each other again.
And then that other time when this girl named 'Melissa' was sending me some passwords to pr0n sites, I couldn't resist. She was really awesome, but you know, deep in my heart that was not what I wanted. I somehow managed to go back to you and say sorry. We even moved together in our first flat, and later in our own house. That was a really good time, I love to think back at those moments.
Then my friend 'Sasser' came over to us one night, do you remember how he claimed that big shelf in our living room, and overflooded it with his own stuff, so that we haven't a clue we are reading yet offshelve? Wow that was a disturbing experience.
But a really hard time has come when our dog 'Zeus' got kicked by this ugly trojan horse. I really don't want go into details how the mess looked like after we discovered him on our floor. Still, I am very sorry for him that he didn't survived it :(
Some months later this guy named 'Conficker' showed up one day. I shitted my pants when I discovered that he guessed my password on my computer and got access to all my private stuff on it. He even tried to find some network shares of us with our photos on it. God, I was happy that he didn't got access to the pics we stored there. Never thought that our homemade photos are not secure there.
We lived our lives together, we were happy until that day when you started the war. 'Stuxnet..'! you cried directly in my face, 'you are gonna blow up our centrifuges of our life', and yeah she was right. I was in a real bad mood that days back then. I even not tried to hide my anger. But really, I don't know why all this could happen. All I know is, that it started with that cool USB stick I found on the stairs of our house. After that I don't remember anything, as it is just erased from my memory.
The years were passing. And I say the truth here, we were not able to manage the mess of our relationship. But I still loved you when you opened me that you will leave. My 'Heartbleed' started immediately, you stabbed it where it causes the most pain, where I thought that my keys to your heart are secured. But no, you stabbed even harder.
Because not long after that you even encrypted our private photos on our NAS, and now I am really finished, no memory which can be refreshed with a look at our pictures, and you even want my money. I really 'WannaCry' now... -
I had to create an account on a website. I used LastPass to generate a strong password. I entered it and got the following message:
"Password must be between 8 and 16 characters and must have special characters (? , ! & #) and numbers"
My password was 20 characters, me annoyed to generate a 16 character password. Filled it in and got the same error. That was it for me.
Who dafuq limits a password to 16 characters, that's fucking nothing. It did not accept all special characters, only the ones that were showed (like 5 or so).
And here comes the worst part...
It's a bank website! I had to create the most most most insecure password in history for it to work.7 -
Originally wanted to get a head start on work since gonna be out Monday... And don't want to be distracted while working on it... But UAT db was down.
So spent all morning working on side projects like a password manager because we're not allowed to use keepass...2 -
Pentesting for undisclosed company. Let's call them X as to not get us into trouble.
We are students and are doing our first pentest at an actual company instead of assignments at school. So we're very anxious. But today was a good day.
We found some servers with open ports so we checked a few of them out. I had a set of them with a bunch of open ports like ftp and... 8080. Time to check this out.
"please install flash player"... Security risk 1 found!
System seemed to be some monitoring system. Trying to log in using admin admin... Fucking works. Group loses it cause the company was being all high and mighty about being secure af. Other shit is pretty tight though.
Able to see logs, change password, add new superuser, do some searches for USERS_LOGGEDIN_TODAY! I shit you not, the system even had SUGGESTIONS for usernames to search for. One of which had something to do with sftp and auth keys. Unfortunatly every search gave a SQL syntax error. Used sniffing tools to maybe intercept message so we could do some queries of our own but nothing. Query is probably not issued from the local machine.
Tried to decompile the flash file but no luck. Only for some weird lines and a few function names I presume. But decompressing it and opening it in a text editor allowed me to see and search text. No GET or POST found. No SQL queries or name checks or anything we could think of.
That's all I could do for today. So we'll have to think of stuff for next week. We've already planned xss so maybe we can do that on this server as well.
We also found some older network printers with open telnet. Servers with a specific SQL variant with a potential exploit to execute terminal commands and some ftp and smb servers we need to check out next week.
Hella excited about this!
If you guys have any suggestions let us know. We are utter noobs when it comes to this.6 -
Lady comes over to my cube and stands silently until I notice her in the mirror. She cheerfully asks that I help her reset her password.
Okay...one, I'm buried up to my balls in work that needs to be done, and here she is camping, expecting me to feel a disturbance in The Force to help on her whim, when our company has an issue system for shit like this. 👊
Two, I'm 👏 a 👏 developer 👏! My sign says Software Engineer on it, which might give some context as to why she forgot her password.
Look, I was nice to her. But it seems like I'm getting more and more phone calls and surprise visits lately from people that I shouldn't be.1 -
Yet another day at my company, Im rewriting some old code for client (rewriting old, php 4 system for vindications managment) and you know the moment when you are focused and someone comes to you to absolutely ruin your focus. Fine, whatever. Oh, for fuck sake. Again dev is doing as support becouse one moron with second can't login into zimbra admin panel and add fucking mailbox. I show them exacly how they login, remind them they are admins too, slowly show them, so you click "manage" than you click that gear icon and than you click "new", fill in email address and password. As simple as 1-2-3. Okay, fuck it, time to go for a cig. I just finish up few lines and stand, grab my vape and start walking towards door. In door I find my buddy with 2 random people. He told me that they are interns and that I should show them some basics and stuff around that. Oh god, fuck my life. If anything, Im definitely very bad teacher, mainly becouse I often have problems with saying what I mean in the way that somebody actually understans and knows what I am trying to say. Whatever. Fuck it all. I grab two of our old laptops that nobody used in like a year or so, and first thing I quickly figure out, is that one day for some what the fuck reason I dont even dont bothered to remember I installed Arch on both while I dont usually use Arch. I just needed it for some specific reason. Whatever. So I guess I will need to upgrade fucking system. Our network isn't really great so that was like... hour or so. In the meantime I figured what they know about coding in general etc, and holly shit. One of them (there was boy and girl), girl, apparently never ever in her life even touched code. Well... fuck. Why am I wasting my time? Becouse there was some programme or some shit like that... Someone could tell me before so I could mentally prepare.. fuck it. whatever. So while laptops are doing their pacman thing, I sit with them and slowly start to explain based on my machine some really basic concepts. Second guy actually had some expirience, he knew how to make some really really basic logic and stuff, so he had another world of problems, becouse it was PHP and, as we all know, everyone hates PHP, and... yeah.. You can probably imagine his approach. Yes, you get user input in super global array. I really wanted to say "Now shut the fuck up and write that fucking $_POST".
hour or so passed, I was close to giving up to not let my anger rise (im not really good teacher... I mentioned it. I suck at teaching others) but luckly machines upgraded. He wanted to use visual studio code, she didnt care too much, so I installed phpstorm in trial mode. whatever. Since that's linux and they were not comfortable with that, I walked them through installing LAMP stack, and when finally it started to look like LAMP stack, I requested them to google how to install xdebug, becouse xdebug is very usefull and googling skill is your best weapon on that field. I go for cig, come back and what I see boiled me a little bit. The girl was stuck looking at github page randomly looking through xdebug source code and idk... hoping for miracle (she admited she thought there will be instructions somewhere) and the guy was in good place, xdebug has a place to paste your phpinfo() for custom instructions. But it didn't work for him, he claims that wizzard told him it cant help him.. hmm intresting, you are sure you pasted in phpinfo? yes, he is sure. Okay, show me.
Again mindblown how someone can have problems with reading.
so his phpinfo() looked like that:
```<?php
phpinfo();```
I highlighted on the page the words "output of phpinfo". He somehow didn't see it or something. He didnt know, he thought that he needs to put in phpinfo so he did. OMG.
Finally, I figured out I can workaround my intern problem, and I just briefly shown them php.net, how documentation looks, said to allways google in english, if he uses tutorial to read whole fucking thing, not just some parts of it, and left them with simple task, that took them whole day and at which they ultimately failed.
To make 3 buttons labeled "1" "2" "3" and if someone presses one of them, remember in session that they pressed it and disallow pressing other ones.
Never fucking again interns. Especially those who randomly without apparent reason almost literally just spawn in front of you and here, its your fucking problem now.
Fuck it, I have some time to get back to my stuff. Time is running so lets not waste it.
After around 15 minutes my one of my superiors comes in and asks me if I can go on meeting with him and other superior. My buddy goes with us, and next 3 hours I was basically explaining that you cannot do some things (ie. know XYZ happened without any source of information) in code, and I can't listen for callbacks from ABC becouse it wont send anyc cuz in their fucking brilliant idea ABC can't even know that this script would even exist, not to mention it wants callbacks.
Sometimes I hate my job.4 -
I have fucking HATED Windows 10 from day one. Now I'm hearing there are new vacillations of this genius programming train wreck that I think is designed to force monetize Microsoft's business model.
After a short while I managed to get to a point where I can maintain W 7. In fact, I'm using my old computer right now. Because I could not get this rant to load onto Devrant website. If you are reading this we know that it is because 10 sucks consistently.
I save my files onto a backup hard drive so I can find 'paper file' type solution for whatever random crap might block me at the keyboard. In fact, I still use paper and file cabinets so "technology" doesn't bring me to a screeching halt every time something like "no record of that account" or "wrong password".
Why the hell does my PASSWORD work from W7 but not from W10?! And it's getting WORSE by the day! I'm about to take a fucking hammer to my new fucking computer. And to that guy who smarmy says something to the effect of 'don't be such a pussy... just fix it and you will be happy.' Well. Fuck you too!
Now. That being said. Anybody have a suggestion on what to try next? And don't say something like, 'take your computer to Micro Center or Geek Squad'. I've done those guys twice each. And for a small phenomenal fee they have each time made things slightly worse plus lost parts of my saved data each time.
Oh. And "reset to previous" doesn't work either.
Suggestions?
Probably better at this point to attempt to solve my own problems wrong for free at this point. Maybe I'll learn to program in Linux or some such thing.
Forrest
for suggestions please contact me at
res0naza@yahoo5 -
I recently went to an office to open up a demat account
Manager: so your login and password will be sent to you and then once you login you'll be prompted to change the password
Me: *that's a good idea except that you're sending me the password which could be intercepted* ok
Manager: you'll also be asked to set a security question...
Me: *good step*
Manager: ...which you'll need to answer every time you want to login
Me: *lol what? Maybe that's good but kinda seems unnecessary. Instead you guys could have added two factor authentication* cool
Manager: after every month you'll have to change your password
Me : *nice* that's good
Manager: so what you can do change the password to something and then change it back to what it was. Also to remember it keep it something on your number or some date
Me: what? But why? If you suggest users to change it back to what it was then what is the point of making them change the password in the first place?
Manager: it's so that you don't have to remember so many different passwords
Me: but you don't even need to remember passwords, you can just use softwares like Kaspersky key manager where you can generate a password and use it. Also it's a bad practice if you suggest people who come here to open an account with such methods.
Manager: nothing happens, I'm myself doing that since past several years.
Me: *what a fucking buffoon* no, sir. Trust me that way it gets much easier to get access to your system/account. Also you shouldn't keep your passwords written down like that (there were some password written down on their whiteboard)
Manager: ....ok...so yeah you need sign on these papers and you'll be done
Me:(looking at his face...) Umm..ok4 -
Having gone to a bank to reset a password again today (Yes, I forgot it for like... 3rd time, don't judge me, its my backup bank account I need to access like... once a year), I was once again made to think - I come in, give them my state ID by which they authorize that I can even make a password reset request.
Then they give me a tablet to... sign a contract addendum?
Its not the contract part that always makes me stop and think though - its the "sign" part.
I'd wager that I am not the only one who only ever uses a computer to write text these days. So... My handwriting got a lot jerkier, less dependable. Soooo... My signature can be wildly different each time.......
And if my signature varies a lot... then... what is the point of having it on a piece of paper?
I know its just a legal measure of some sort... And that, if it came down to someone impersonating me and I'd go to court with the bank, there would be specialists who can tell if a signature was forged or not... But...
Come on, the computer world has so much more reliable, uncrackable, unforgable solutions already... Why... Don't all folks of the modern world already have some sort of... state-assigned private/public keypairs that could be used to sign official documents instead?
It costs money, takes time to develop etc... But... Then, there would not only be no need to sign papers anymore... And it would be incredibly hard to forge.
The key could even be encrypted, so the person wishing to sign something would have to know a PIN code or a password or something...
tl;dr: I hate physical signatures as a method of authentication / authorization. I wish the modern world would use PKI cryptography instead...11 -
macs... I know I didn't like them before, but recently I wanted set up a vpn on another person's pc and first it didn't want to install because it was a third party program. understandable, change security settings, try again, works. and now... EVERY TIME the user wants to connect it asks for a password, because the vpn client is "changing system settings". whenever the pc is locked, it disconnects and asks for a password whenever you log in again.
The saying that macbooks "just work" has to be extended to "the most basic functionality kind of works, most of the time".
Or maybe I'm just ignorant and unable to handle the glory of mac osx4 -
When a banks mobile app, shows the exact number of characters required to login.
Not a blank space, or similar.
Even if the allowed password is within a range, it still shows the exact number of characters.
Correct me if i am wrong but this shouldn't be like this? -
9000 internet cookie points to whoever figures out this shit:
I'm trying to import a secret gpg key into my keyring.
If I run "gpg2 --import secring.gpg" and manually type each possible password that I can think of, the import fails. So far, nothing unusual.
HOWEVER
If I type the same passwords into a file and run:
echo pwfile.txt | gpg2 --batch --import secring.gpg
IT ACTUALLY FUCKING WORKS
What the fuck??? How can it be that whenever I type the pw manually it fails, but when I import it from a file it works??
And no, it's not typos: I could type those passwords blindfolded from muscle memory alone, and still get them right 99% of the time. And I'm definitely not blindfolded right now.
BUT WAIT, THERE'S MORE!!
Suppose my pwfile.txt looks something like this:
password1
password2
password3
password4
password5
password6
Now, I'm trying to narrow it down and figure out which one is the right password, so I'm gonna split the file in two parts and see which one succeds. Easy, right?
$ cat pw1.txt
password1
password2
password3
$ cat pw2.txt
password4
password5
password6
$ echo pw1.txt | gpg2 --batch --import secring.gpg
gpg: key 149C7ED3: secret key imported
$ gpg2 --delete-secret-key "149C7ED3"
[confirm deletion]
$ echo pw2.txt | gpg2 --batch --import secring.gpg
gpg: key 149C7ED3: secret key imported
In other words, both files successfully managed to import the secret key, but there are no passwords in common between the two!!
Am I going retarded, or is there something really wrong here? WTF!4 -
To all websites requiring at least one upper case, one lower case, one number, one special character, 25 emoji and 49 unicorns in the password when signing up.
If you say something is required, then your regex BETTER be checking ONLY for those things. You should not have hidden requirements for passwords that users are supposed to dream about and know. Especially if it's a super time-sensitive thing that they should have opened 2 Fridays ago.
I had to pull my hair out for 20 minutes (that felt like an hour) before looking at their code and reading their regex. The regex was different from what the page said the requirements actually were. What were they even thinking? 😑
The rest of everything related to this organization uses an SSO system, why can't they just use it? Isn't the whole point of SSO to avoid a different login for every tiny part of the system?
I wonder what the other less technically inclined people using the system are doing right now. Sadly, I have no way of letting them know.
I sincerely hope the dev that made that website faces the same thing while picking a password for creating an account somewhere else and realizes what he/she did.
I really needed to let it out.
I feel much better now.
Time to take out the stress ball :)1 -
The conversations that come across my DevOps desk on a monthly basis.... These have come into my care via Slack, Email, Jira Tickets, PagerDuty alerts, text messages, GitHub PR Reviews, and phone calls. I spend most of my day just trying to log the work I'm being asked to do.
From Random People:
* Employee <A> and Contractor <B> are starting today. Please provision all 19 of their required accounts.
* Oh, they actually started yesterday, please hurry on this request.
From Engineers:
* The database is failing. Why?
* The read-only replica isn't accepting writes. Can you fix this?
* We have this new project we're starting and we need you to set up continuous integration, deployment, write our unit tests, define an integration test strategy, tell us how to mock every call to everything. We'll need several thousand dollars in AWS resources that we've barely defined. Can you define what AWS resources we need?
* We didn't like your definition of AWS resources, so we came up with our own. We're also going to need you to rearchitect the networking to support our single typescript API.
* The VPN is down and nobody can do any work because you locked us all out of connecting directly over SSH from home. Please unblock my home IP.
* Oh, looks like my VPN password expired. How do I reset my VPN password?
* My GitHub account doesn't have access to this repo. Please make my PR for me.
* Can you tell me how to run this app's test suite?
* CI system failed a build. Why?
* App doesn't send logs to the logging platform. Please tell me why.
* How do I add logging statements to my app?
* Why would I need a logging library, can't you just understand why my app doesn't need to waste my time with logs?
From Various 3rd party vendors:
* <X> application changed their license terms. How much do you really want to pay us now?
From Management:
* <X> left the company, and he was working on these tasks that seem closely related to your work. Here are the 3 GitHub Repos you now own.
* Why is our AWS bill so high? I need you to lower our bill by tomorrow. Preferably by 10k-20k monthly. Thanks.
* Please send this month's plan for DevOps work.
* Please don't do anything on your plan.
* Here's your actual new plan for the month.
* Please also do these 10 interruptions-which-became-epic-projects
From AWS:
* Dear AWS Admin, 17 instances need to be rebooted. Please do so by tomorrow.
* Dear AWS Admin, 3 user accounts saw suspicious activity. Please confirm these were actually you.
* Dear AWS Admin, you need to relaunch every one of your instances into a new VPC within the next year.
* Dear AWS Admin, Your app was suspiciously accessing XYZ, which is a violation of our terms of service. You have 24 hours to address this before we delete your AWS account.
Finally, From Management:
* Please provide management with updates, nobody knows what you do.
From me:
Please pay me more. Please give me a team to assist so I'm not a team of one. Also, my wife is asking me to look for a new job, and she's not wrong. Just saying.3 -
So I just started watching Eli The Computer Guy's videos on networking and I really like them so far(only on the introduction so far though), but I was a bit confused about some of the stuff and I thought to myself that some of this might be obsolote or not so much in use these days/different. So here are some questions(now bear with me, I'm still a noob to the whole topic of networking):
-Are Eli's videos on networking obsolete(besides the speeds that he talks about), what you recommend some other tutorial, if so which one?
-Is a switch necessary for a small network?
-Do we still connect routers to modems or do we just use what we refer to as a router(a mix between a router and a modem -> gateway/gateway router)?
-Can you connect an ethernet cable to your router/gateway?
-So according to Eli if you have multiple routers they make seperate networks that cant just be acessed from each other, then how come it be that I can access my rasperry pi when I'm connected on the network of one router when the raspberry pi is connected to the network of another router and how come it be that once you have the wifi password you can connect to all of them?8 -
I wish that my previous company gets investigated. They probably got more violations if they are investigated. Here are a few examples:
The company is in the telecom business and they wanted to create AI summaries of their phone calls. So they used real private calls of their clients as test data without their knowledge & consent.
The CEO also made fun of someone handwritten CV on LinkedIn. Sure, he blurred out the obvious data but shit like certificates, past history & rough location was still present. It was not be hard to find who it was.
The 2FA of some IT services was still on the ex-CTOs private phone (now he is a consultant 1x a week)
One of their engineers moved back to Russia and has access to sensitive data. (aka call recording of insurances, banking, fire departments, ...)
Offering users to write a public review of the company for a discount if the review is positive. The "paid review" is not mentioned.
The reviews of their new feature are done by 'external' people but they all benefit from the companies success. The review is written from their own company but it was written by the external design company (CEOs wife under her own company), marketing consultant (under his own company).
They did fire an employee illegally (as in did not follow the legal procedures, the new COO thought she was a consultant, she was in fact not so she had more protections)
They did fire an employee for untrue reasons and waiting till he was on holiday & abroad (dick move but legal I think)
They did spy through the security cameras and made up a reason to fire someone. Company offered free soda during that time, employee did not like the offered soda and filled it with a diet-variant on their own dime. He then took his own bought diet-soda back home (not all) and got fired for stealing. (or idk, it might have been ice tea or fanta)
They did not report that an employee sold company data but he was let go.
They run cookies on their website but has no clause for cookie-consent.
Their features that they are promoting & selling is not working like expected
They lie about their server uptime or heavily manipulate it.
They sell a feature that is no longer supported and broke a few updates ago.
They are offering a product as a fix that is simply not longer supported by the development team
They have fired consultants and then refuse to pay their last month salary or only pays it partially. Happened as far as i know, 4 times (no proof).
Everyone had access to the full password vault including the login credentials for business routers and the credit card info of the CEO, CFO, CTO. It took me multiple times to report it to the IT admin for mine to be restricted.
Every new dev has access to production data within a few weeks or direct database access
Any person who has access to the admin-portal can spoof phonenumbers in a few clicks.
A colleague is blacklisted at the police portal for past crimes where they have to fulfil police orders. He did them pretending to be a different employee who was approved. Also, they do not keep track of the data needed to fill in the yearly report (idk why the company has to them but the police does not do it).
They forgot to implement a warning (legally needed) before someone hits their data limit. those people cannot be billed. Someone was watching 4k movies in Signapore and costed the company tens of thousands of Euro.
If I think of more, I'll add it comments lol10 -
I have a few projects on the go at work at the moment which could be successful, but only time will tell:
1. We have a requirement to monitor or SQL servers for any long running queries (anything that runs longer than 3 minutes). Company didn’t want to pay for enterprise grade solution so as the only SQL Developer I created a small system that involves a database, 2 tables a stored procedure and scheduled job. It goes off every 10 minutes queries some system tables etc and write the results to the tables. Still waiting for it to be deployed to one of the test servers. I have plans for a web front end in the future.
2. My company currently use source safe for version control. They’ve lost the admin password so only 1 person can log in. I’m running he project to plan the migration to GitLab. It’s getting close to completion and soon someone is going to be tasked with creating 100s or projects etc.
3. We use an ERP system which is huge with thousands of tables, but no FKs or anything like that. The current data dictionary is a spreadsheet, as a side project I’m creating a web app so that this information is easily available and searchable.
All 3 projects have the potential to be successful, for my team at least, but stuck waiting for other people to do their stuff first. -
A thing that I am annoyed that people are getting wrong is security by obscurity.
You have heard of it and being told it is bad. It is so bad that it alone is a counter argument. Let me set you straight:
>>>Security by obscurity is the best security you will ever have<<<
There is an asterisk: It is probably not right for your business. But that is for the end.
Security by obscurity means to hide something away. Most security is based on hiding. You hide your private key or your password or whatever other secret there is. If you had a 2048 long sequence of port knocking, that would be fine, too.. Or it would be fine if it wasn't observable. You could write this down in your documentation and it wouldn't be security by obscurity. It would just be security. Weird, but fine.
The real meat of obscurity is: No one knows that there is someone. The server you port knock looks like a harmless server, but suddenly has an open port to a bad application for an IP, but only if that IP went to 25 other ports first.
In the animal kingdom, there are different survival strategies. One of them is being an apex predator or at least so big and lumbering that no predator wants a piece of you. That's our security. It is upstream security. It is the state.
But what is the rest of the animal kingdom going to do? Well, run away. That works. Not being caught. And those not fast enough? Hide! Just be invisible to the predators. They cannot triple check every leaf and expect to be done with the tree before starving. That's security by obscurity. Or hide in the group. Zebras. Easy to see, hard to track in the group. Look like everyone else.
There is a reason why drug smugglers don't have vaults in the carry-on. Arrive at the customs and just refuse to open the vault. If the vault is good enough. Nope, they lack the upstream security by the state. The state is there enemy, so they need obscurity rather than cryptographic safety.
And so, for a private person, having a port knocking solution or disguising a service as another service is a great idea.
Every cryptography course happily admits that the moment they can catch you physically, cryptography is useless. They also teach you about steganography. But they omit to tell you that obscurity is the second best solution to having a stronger army when you cannot rely on your state as upstream security.
Why did I say, not a good idea for companies?
1. It is self-defeating, since you have to tell it to all employees using it. A shared secret is no secret. And therefore it cannot be documented.
2. It makes working with different servers so much harder if there is a special procedure for all of them to access them. Even if it were documented. (See 1.)
3. You're a company, you are advertising your services. How to hide that you run them?
Do you see how those are not security relevant questions? Those are implementation relevant questions.
Here is an example:
Should you have your admins log into servers as normal users before elevating to root or is that just obscurity? Well, not for security purposes. Because that foothold is so bad, if compromised, it makes little difference. It is for logging purposes, so we have a better server log who logged in. Not only always root. But if our log could differentiate by the used private key, there is no issue with that.
If it is your private stuff, be creative. Hide it. Important skill. And it is not either, or. Encrypt it your backup, then hide it. Port knock, then required an elliptic curve private key to authenticate.
It is a lot of fun, if nothing else. Don't do it with your company. Downsides are too big. Cheaper to hire lawyers if needed.1 -
Pulled my hair out over one today (and a week ago when I first saw the issue)
Setting up development environment. Created test user and test database and used mysqldump to copy data over.
MySQL was executing a function as the wrong user. Checked my config files, checked my config reader, checked my database connection, checked checked checked. Checked everything twice, I felt like Santa.
Changed the password in the config file to make sure it was logging in right. It threw an error still but not one I had expected so I figured the login still worked (My bias was that I thought the config file was not working or the mysql library was caching authentication. Both were wrong but this blinded my debugging. Foolish, I have forgotten my training)
Logged into the database directly via client. *didn't bother executing the function because I was only testing auth*
Think
Think
Think
Search entire project for database username. It's gotta be hard coded by accident SOMEWHERE.
It's not.
Why
Why
Why
Wait.
-- Flashback to how the test db was created -- What's actually in this damn script?
DEFINER `production_user` CREATE PROCEDURE `old_db`.`procedure_name`
Two issues: definer is old user (this is the error I was seeing) and its creating the procedure on the old db (this would be the next error I would have found if I kept going)
Fuck mysqldump. Install mysqldbcopy. Works
Put hair back in head. -
I started working for a startup as Server Administrator/ System Integrator beside university to get some dollars with easy work and nice people.
((I Know two of the C*Os so I got a had feeling with this. Besides the upcoming story I'm still really happy with my position and career chances here. God bless my Department which has the most funny/rude guys, love you.))
tl;dr:
Guy fakes his Skillset and fuckup whole department, can´t do most of his basic tasks. I had my first and hopefully last interaction with this bastard.
Heres how everything started:
I was more and more involved in the leading processes and decisions.
Heard about a story where and why the whole dev-department was kicked out of his position because they were crappy developers. And cant just believe the stories they told me about the former Dev-Lead
Now I met the former "Development Lead"
I was brought in because we in the IT wondered why he would like to share his local machine password with colleges. After some questions he came out with the Reason.
He is doing home-office for some days a week now and wants his colleges to be able to start his "software". (already confused by that)
The "better IT-guy" in me offered help for automatic deployment CI/CD stuff so that they can use it as an inhouse service.
BIG OOF incoming:
"The code is not in git because I wanted to clean it up before"
"My IDE is the only place where my PHP crap work is running"
"The 'PHP-software' is to complex for this"
My Lead and I were completely speechless,
I understand the decision to kick this "dev-Lead" from the lead position down to a code monkey/ script kid.
Now I´m thinking about getting my Hands on the Lead position after my exams because if such bastards with no clue about basic stuff, no clue about leading, no clue about ci/cd, no clue about generic software stuff get the job I would easily be the "good IT-guy" with more responsibility/ skill.
Now I sit here, hate people that fake their skills and set back work of colleges for multiple months and never asked for help or advice.
And the little "Bastard Operator from Hell" in my just wants to delete all his files, emails account during a migration to completely demotivate the person who failed to be responsible for a team nor their projects.rant ci/cd php administrator startup script-kid i hate people unskilled skill faker lead developer devops5 -
Did some distro hopping at the weekend and ended up back in Ubuntu.
And for the most part everything is running like a dream, except MY motherfucking SQL.
Installation appears to be ok, but doesn’t let me set a root password, and throws errors like it’s cool when I try and change the root password.
Same goes for MariaDB.
All of my googling for a solution has so far failed me1 -
As a long time Ubuntu user, last month I upgraded from Xenial to Bionic to try the new Gnome based desktop.
At first I thought it was a good transition, everything was working fine, beautiful UI, nice animations, so I installed all my tools and started the real work... then the problems started. The memory usage was always very high and only getting higher, the animations were stuttering and laggy, and it was having an unrecoverable freeze at least twice a week. Searching the web I was seeing more and more people complaining about freezes, lags, bugs, memory leaks, password input field bugs... damn, how I missed Unity! That was it, Gnome Shell made me miss Unity more and more.
This week I installed Unity 7 and purged Gnome Shell from Bionic. Now I'm happy again!
It's so good to be free of the anxiety caused by the lack of stability of the system, so good to know that the system will not break or freeze if I'm doing a resource intensive task. Now he sh** is working fast and stable, and I'm here wondering why such a good DE could be dumped for something so buggy like Gnome.1 -
I hate hate hate Windows. I'm forced to use it and the amount of problems is too damn high. I was able to cope with the shit but now it must be the top of the mountain. When I boot that tiny piece of sh** I get to the page where *normally* the login is.. but I just don't get a Username + Password box . The page stays blank with the default wallpaper. Why is stuff like that even happening? Not a single *solution* I found on the internet worked. FML.. going to reset that thing now5
-
Who actually started the reign of mixed character passwords? because seriously it sucks to have an unnecessarily complex password! Like websites and apps requesting passwords to contain Upper/Lower case letter, numeric characters and symbols without considering the average user with low memory threshold (i.e; Me).
Let's push the complaint aside and return back to the actual reason a complex password is required.
Like we already know; Passwords are made complex so it can't be easily guessed by password crackers used by hackers and the primary reason behind adding symbols and numbers in a password is simply to create a stretch for possible outcome of guesses.
Now let's take a look into the logic behind a password cracker.
To hack a password,
1) The Password Cracker will usually lookup a dictionary of passwords (This point is very necessary for any possible outcome).
2) Attempts to login multiple times with list of passwords found (In most cases successful entries are found for passwords less than 8 chars).
3) If none was successful after the end of the dictionary, the cracker formulates each password on the dictionary to match popular standards of most website (i.e; First letter uppercase, a number at the end followed by a symbol. Thanks to those websites!)
4) If any password was successful, the cracker adds them to a new dictionary called a "pattern builder list" (This gives the cracker an upper edge on that specific platform because most websites forces a specific password pattern anyway)
In comparison:
>> Mygirlfriend98##
would be cracked faster compared to
>> iloveburberryihatepeanuts
Why?
Because the former is short and follows a popular pattern.
In reality, password crackers don't specifically care about Upper-Lowercase-Number-Symbol bullshit! They care more about the length of the password, the pattern of the password and formerly used entries (either from keyloggers or from previously hacked passwords).
So the need for requesting a humanly complex password is totally unnecessary because it's a bot that is being dealt with not another human.
My devrant password is a short story of *how I met first girlfriend* Goodluck to a password cracker!5 -
I fucking hate people who uses complex words to describe something simple.
Describing a frame work
Show-off : "..you can define what objects/tables to expose, what values in that object you want to expose...if you are using some orm, then because you have models defined. Once you update your model, your endpoints get the new model..."
Simpleton : "something like parse..."
Wtf is 'fixedUUID'?
Show-off: "..hardcoded UUID is fixed (constant) value, with format of UUID, hardcoded UUID will be unique value between backend and frontend,
you will need to store it as constant value in your codebase ( we may encrypt/ decrypt it for security reasons)..."
Simpleton : "a secret password only u & I know"
--why whyyyyyyyyyy2 -
BT "We'll give you BT Virus Protect, which protects against viruses, phishing and other online attacks."
Or... For a start, let your users provide a good secure password when signing up? More than 8 characters is a bit ambiguous. 20 minutes later and several attempts to find out it can't be longer than 20 characters, only upper and lower case letter and numbers aaaand must start with a letter is a bit s**t. Not to mention LatPass doesn't like it as you can't copy and paste.1 -
TLDR: I wanted to change email to new one, but I could not remember which one I have
currently. I found out an API in DevRant JS files for email verification and used
it to find it out.
So, I am moving from Gmail to Protonmail Pro, absolutely love their service.
I wanted to do same on Devrant but I could not figure out my current mail for
"I lost my password" form. My Password Manager have only login saved, and profile does
not show email address.
I thought that this user information is stored on server so it have to be some way to retrieve it. I dug
in source code and I've found:
`<div class="signup-title">Verify Your Email</div>`
Which has event assigned to function which uses jQuery.ajax (love it btw :D) to call:
`url: "/api/users/me/resend-confirm",`
This seems like worth a shot. Few copy-pastes and one ajax call later:
*Ding*
From: support@devrant.io
To: dawid@dawidgoslawski.pl
"Welcome to Devrant"
Got it :) So I have already changed in march when DevRant on previous layout.
This is what I love in this profession - problem solving. AI will not replace human
in any way, we will just stop coding array iterations and data manipulation - we will focus
on real problem solving and human touch (like design, convincing management for changes).1 -
I just don't understand how people can be so careless with security. It's like every other fucking day you about 150 billion email address, SSNs, birth certificates, credit cards, private messages, you pet's medical records, and your personal DNA are fucking leaked and the best we got are "what street did you grow up on" to reset a password.2
-
What password manager/ generators do you suggest?
Also would anyone please clear my possibly misconceptions on the password manager/generators?
I’m that type of guy that only uses few password combinations at different websites.
tl;dr: my account out leaked, I didn’t want to use any password manager because I don’t want to give password to the company. Some do generate complex password for me but if they become defunct I’ll be locked out from those accounts.
A while ago, aptoide got attacked and my password(same as google account) was leaked. I’ll have to thank google for this, google blocking a stranger accessing account using a “less secure app” So now I’ll doing a emergency password changing process to all of my accounts with the password.
I like the whole aspect of the password manager, but I always thought that I shouldn’t give my password to other companies. And I got to use some website long term, if the password management company ever just become defunct, I might lose access to my account forever.30 -
After two years of being in (metaphorical) jail, I once again was given the a privilege of unlocking and rooting my phone. Damn. Frick Huawei, never coming back to that experience.
I gotta say, rooting... Feels a tad less accessible nowadays than when I last practiced it. All this boot image backup, patch, copy, reflash is crying to be automised, only reason I can think of why that changed and magisk can no longer patch itself into the phone's initrd is that it's somehow locked? Was it a security concern? Or can sideloaded twrp no longer do that?
Oh, and the war... The war never changes, only exploits do - fruck safety net... Good for Google that they now have an *almost* unfoolable solution (almost). The new hardware-based check is annoying af, but luckily, can still be forced to downgrade back to the old basic check that can be fooled... Still, am I the only one who feels Google is kinda weird? On one hand, they support unlocking of their own brand of phones, but then they continuously try to come up with frameworks to make life with a rooted or unlocked phone more annoying...
On the other hand, I do like having my data encrypted in a way that even sideloading twrp doesn't give full access to all my stuff, including password manager cache...
Any recommendations what to install? I do love the basic tools like adaway (rip ads), greenify (yay battery life!), viper4android (More music out of my music!) and quite honestly even lucky patcher for apps where the dev studio practices disgust me and don't make me want to support them...2 -
Over the last few weeks, I've containerised the last of our "legacy" stacks, put together a working proof of concept in a mixture of DynamoDB and K8s (i.e. no servers to maintain directly), passing all our integration tests for said stack, and performed a full cost analysis with current & predicted traffic to demonstrate long term server costs can be less than half of what they are now on standard pricing (even less with reserved pricing). Documented all the above, pulled in the relevant higher ups to discuss further resources moving forward, etc. That as well as dealing with the normal day to day crud of batting the support department out the way (no, the reason Bob's API call isn't working is because he's using his password as the API key, that's not a bug, etc. etc.) and telling the sales department that no, we can't bolt a feature on by tomorrow that lets users log in via facial recognition, and that'd be a stupid idea anyway. Oh, and tracking down / fixing a particularly nasty but weird occasional bug we were getting (race hazards, gotta love 'em.)
Pretty pleased with that work, but hey, that's just my normal job - I enjoy it, and I like to think I do good work.
In the same timeframe, the other senior dev & de-facto lead when I'm not around, has... "researched" a single other authentication API we were considering using, and come to the conclusion that he doesn't want to use it, as it's a bit tricky. Meanwhile passed all the support stuff and dev stuff onto others, as he's been very busy with the above.
His full research amounts to a paragraph which, in summary, says "I'm not sure about this OAuth thing they mention."
Ok, fine, he works slowly, but whatever, not my problem. Recently however, I learn that he's paid *more than I am*. I mean... I'm not paid poorly, if anything rather above market rate for the area, so it's not like I could easily find more money elsewhere - but damn, that's galling all the same.5 -
About a month ago, one billion of Yahoo Accounts has been compromised. Today I received two emails from yahoo in my gmail accounts, they were saying that my yahoo password has been changed and my recovery email has been removed (+ a lot of warning emails of old accounts of forum and games that were receiving unknown accesses, but nvm). In the email which informed me about the recovery, I saw a link that would have allowed me to restore the old account, but before to click I thought "Wait! I had like 10 yahoo accounts. What account am I saving?" I check, I read, I read again, but nothing, no information about it in the text. Nevermind, there's a link. This link will be related to a specific account. Right? Wrong. I click, it sends me in a generic page. The link is mute. I attach a screenshot, you can see where the link points in the left-bottom corner. So now I know that one of my accounts has been hacked, I don't know WHICH account has been hacked and I'm not able to recover my account. Luckily it wasn't my main inbox!
 5
5 -
My work network AD password has to be changed every 90 days or so and it is really getting to me now. I'm beginning to run out of passwords to use and may soon have to resort to writing them down on a piece of paper and lock it somewhere.
I get why we need to change it often. What I don't like is the stupid validation rules AD uses to check passwords. It doesn't allow variations and you have to use something completely new.
I have only been in the job for about 8 months and I have had a nightmare experience updating my password recently as the synchronisation failed and I was locked out of my accounts for a day or 2 rendering my useless and having to call support for help.
How the he'll am I supposed to remember my passwords when I have to change them that often!!!17 -
Cross-platform open-source & free password manager.
Description:
Cross-platform mobile/desktop password manager application. No backend needed, private data will be encrypted and stored in Google Drive/One Drive/Dropbox etc...
I've used multiple applications over the years but they pricey (especially if you switch platforms) and most of them don't have full cross-platform support.
Also, I've made a POC app with Ionic a while ago, but I didn't like the hybrid app feel.
Tech stack:
Js/React Native10 -
Okay this is my first time posting on this site. I've browsed it (definitely not in class) and the community looks beautiful, so I'm going to just kind of slide in here. Anyways this is the part where I use my caps lock button and type lots of naughty words I guess...
<rant type = 'school'>
Our programming classes are fucking DISMAL uuugh... Okay so we have four technology classes: Tech Exploration, Coding 1, Coding 2, and Intro to CS (a 'high school' level class)... So this means a fuck ton of kids in programming classes, mostly because I WANNA MAKE MINCERAFT AND BE A KEWL BOI LIKE GAME DEV BUT I'M ALSO A FUCKING IDIOT AND WILL NOT LEARN ANYTHING YAAAAAAY but that's a mood and so there's a fucking tidal wave of dumb kids in these classes. So right we're dealing with like 80 kids per class period. Sorry if I'm repeating myself but there are a FUCKTON of students. Now, we have... wait for it... ONE FUCKING TEACHER. ONE. I fucking swear this district does not give a SINGLE SHIT about possibly THE SINGLE FUCKING MOST IMPORTANT SUBJECT WHYYYYYY... Okay so the teacher is kinda overworked as fuck lol. She can't really teach eighty kids at once so she mostly gives us exercises from websites but when she can she teaches us shit herself and actually knows a good bit about her field of study. She's usually pretty grumpy, understandably, but if you ask her a good question that makes her think you can see the passion there lol. So anyways that's a mood. Now at the other school it's even worse. They have this new asshole as a teacher that knows NOTHING about ANYTHING IT IS SO FUCKING REDICULOUS OH MY UUUUUGH... THEY STILL DON'T EVEN KNOW WHAT A FUCKING LOOP IS LIKE OKAY YOU'VE BEEN TEACHING PROGRAMMING FOR A YEAR AND YOU'RE THE ONLY ONE TEACHING IT AT THAT DISTRICT SO MAYBE YOU SHOULD AT LEAST FUCKING TRY WHAT IS WRONG WITH YOU... so he just makes them do shit from a website and obviously can't do half of the shit he assigns it's so fucking sad... I swear this district is supposed to be good but maybe not for the ONE THING I WANT IT TO BE GOOD FOR. Funny story: in elementary school once I wrote down school usernames for people I didn't really know and shared them a google doc that said "you have been hacked make a more secure password buddy" etc etc and made them the owner and these dull shits report it to the principal... So I'm in the principles office... Just a fucking dumb elementary school kid lol and the principal is like hAcKiNg Is BaD yOu ShOuLd NoT dO iT and I'm like how did you know it was me... so he goes on to say some bullshit about 'digital footprint' and 'tracing' me to it... he obviously has no clue what he's saying but anyways afterwards he points to where it says last change made by MY SCHOOL ACCOUNT... HOW DULL CAN YOU FUCKING POSSIBLY BE IT WAS FROM MY ACCOUNT THAT LITERALLY PROVED THAT I DID --NOT-- 'HACK' INTO THEIR ACCOUNT YOU DUMB FUCK. Okay so basically my school is a burning pile of garbage but it's better than most apparently but it's GARBAGE MY GOD... Please fucking tell me it gets better...
okay lol that was longer than I thought it would be guess I just needed to vent... later I guess
</rant>12 -
client: "can you build out a staging server for us? here's all the code, everything you need"
me: "awesome, looking good, i have almost everything i need, just give me the credentials for the server, and I'll get started installing all the infrastructure"
client: "ok, try these!"
me: "doesn't work"
client: "this one?"
me: "doesn't work..."
client: "how about this one?"
me: "STILL NOT WORKING!!!"
imagine you want someone to do stuff on your server and you don't even know the root SSH password.... smh
why is this always a problem, use fucking 1password or something its 40 bucks a year, secure, and you can organize alllll your passwords. don't be a fucking boomer and write them on a piece of paper, or worse, apparently like my client, never know it or have it in the first place.5 -
One of the truth no one wants to say because what can not be can not be.... but...
Maven is fuck... bullshit... failure by design.
For each project I need an own settings.xml. Always something not working. The same artifactory password 10 times there. Null pointer exceptions all over the place. Basics like versioning not really solved.
In all my years with Ant I never had so much problems than with Maven.
This settings.xml is really a design failure. Crap.1 -
Well fuck Amazon. I am trying to get into my account because for some fucking reason they say my payment method is faulty while they actually write off the subscription of prime of it. But to get into my account I need to login again with 2FA as I have that turned it on. So far so good. But since it's an old phone number I can't login. Well just change the phone number wouldn't you think? Well yes but to change the phone number I need to login in with the old phone number to which I have no longer access 🤦♂️. Eventually found a phone number I could call. I get a lovely lady on the phone which guides me to resetting my password but for that, you guessed it, I need to do the 2FA again. I get send through to the next person as she can't change it for me because of privacy reasons (oh well). That guy first askes the last 4 numbers of my creditcard like 5 times because he can't remember it (write it the fuck down then asshole) then he starts mistaking the 6 for 9 (like how the fuck do you do that) and then the text messages don't come in while I am on the phone with him which he tries to blame to my service provider because they would block Amazon (like why would they do that?). But since I got a text message of them 15 min before I shot that down quickly. Then he finally admitted that they might have a disruption going on. So I think we'll fine I'll just ask my question to him how it's possible that Prime stops working as I am watching it because my payment method is faulty according to them (but manage to write off the subscription) and he starts talking just shit. Just admit that you don't know and connect me to someone who does know how that can happen. In the the end I just hung up because I knew I wasn't getting anywhere with this guy and don't you know it, as I start writing this the text messages come in. Problem solved you would say just out that number in the website and you can change your phone number. Well no because I have to tell the number to the guy who I hung up with because the texts weren't coming in 😒. Now I should call them back but I think I'll wait till tomorrow hopefully the day shift will be a bit more knowledgeable on how shit works and can actually remember 4 digits.2
-
Yeah, so when you create an account just about anywhere nowadays, you need to choose a strong password. Fair enough. But then, some sites/services/systems require a second password, sort of a password hint as an extra security for retrieving your first password in case you forget it. Well OK...That hint question just becomes very *in*secure when you must choose from some extremely stupid presets like "In which town were you born?" or "What was your mother's maiden name?", all of which are trivia that for most people can be easily googled, or looked up on facebook ffs. And these "in which town did this or that happen?" questions? As there is only one town in my country it's not a long shot that I was born in Mariehamn, met my partner in Mariehamn and had my first job in Mariehamn. Security questions for imbecils.4
-
Someone didn’t properly set the httpcookies domain for our staging and production websites. Yep, this was a C#/.NET site. The cookie domain for the staging site was set to the production domain instead of the staging domain (which was a subdomain). So if someone logged into the staging admin, that would also grant them access to production admin if they also had an account in the production site.
The staging site technically had an additional login to enter the site, but the username and password weren’t too hard to guess. It was like that for years until I was hired to be an in-house dev (the role was previously outsourced to a software development company).
The admin side of the website wasn’t very sophisticated. But there was enough personal identifying info for a hacker to do something with.
I don’t know how they weren’t hacked yet. Honestly, I’d tell my employer to go back to that software agency and ask for a refund and cite the shotty work.1 -
TLDR; Send help, need VR video player that works on all the platforms (not IE, that can burn in hell)
Okay, don't get me wrong; I love iOS and most of it's features like being able to connect to the same WIFI-networks without having to fill a password twice.
But holy shit; Fuck Safari.
They made it so hard to access the stupid motion thing which you can use for VR.
Why do I know this? Well of course I have been building an app for a client which needs to display 360 degree video, which would be best viewed by turning your phone instead of swiping across your screen.3 -
Fuck you Linux! I thought user password validation would be a piece of cake, like bash one liner. How wrong could I be!
Yeah, it's already ugly to grep hash and salt from /etc/shadow, but I could accept that. But then give me a friggin' tool to generate the hash. And of course the distro I chose has the wrong makepswd, OpenSSL is too old to have the new SHA-512 built in, as it should be a minimal installation I don't want to use perl or python...
And the stupid crypto function that would do me the job is even included in glibc. So it's only one line of C-code to give me all I want, but there is no package that would provide me this dull binary? Instead I will have to compile it myself and then again remove the compiler to keep image small?5 -
Starting to wonder why I tend to like our QA people so much: they often seem so much saner. Yes, sometimes they quibble as with the complaints about a page that is hidden from the user anyway, but they would usually not creep to deep into the hole creating most unintuitive workflows and abysmal logic.
Disclaimer: We're more like backend devs, but we had to do a UI which was beautifully slaughtered by the CEO messing with it - guess what's happening with the new one - and because of that... thing I already nearly smashed my Mac because stupid entered credentials for updating software would only be applied if you defocused once out of the password entry box. Fucked up stuff like this, which devs meddle with, give up, just shrug it off and dump it on the (l)user.
Or a more recent example: So PM wanted a stupid "Apply to all" buttons on a list that can be filtered. Guess to which items the actions should be applied if you filtered it and you currently only see a small selection in your window! Yes, of course it still applies to all items in the universe. QA guy who's just trying the buttons comes to me: "Hey, you sure this "apply all"-stuff supposed to work like that?"
Third example to end this long QA-praise: So there is this virtual appliance we build and we should support another stupid hypervisor.. and he found the kernel modules I have to activate additionally so we can just convert the existing image without having to create a new build system.3 -
I'm reading online that after I buy bitcoins from Coinbase, I should transfer it to a private wallet that is kept offline.
What would be a private wallet? Does that mean I have to download and keep the entire blockchain on my PC?
Also how would I transfer?
And best way to keep the private wallet secure? and not lose the key, password, etc?
And I guess main reason I ask was bc I saw this. Actually does this basically act like Coinbase? But they keep my wallet?
https://try.blockfi.com/morningbrew...9 -
How does Spring Boot/Data create a MongoClient/Template Bean to a **remote** database that requires password, certs, other configs?
These would be set in application properties but how does it get translated to the Beans?
I went through a lot of examples is like @Autowired MongoClient client
And then they just use it.
And I'm like wtf?7 -
Trying to make a nodejs backend is pure hell. It doesn't contain much builtin functionality in the first place and so you are forced to get a sea of smaller packages to make something that should be already baked in to happen. Momentjs and dayjs has thought nodejs devs nothing about the fact node runtime must not be as restrained as a browser js runtime. Now we are getting temporal api in browser js runtime and hopefully we can finally handle timezone hell without going insane. But this highlights the issue with node. Why wait for it to be included in js standard to finally be a thing. develop it beforehand. why are you beholden to Ecma standard. They write standards for web browser not node backend for god sake.
Also, authentication shouldn't be that complicated. I shouldn't be forced to create my own auth. In laravel scaffolding is already there and is asking you to get it going. In nodejs you have to get jwt working. I understand that you can get such scaffolding online with git clone but why? why express doesn't provide buildtin functions for authentication? Why for gods sake, you "npm install bcrypt"? I have to hash my own password before hand. I mean, realistically speaking nodejs is builtin with cryptography libraries. Hashmap literally uses hashing. Why can't it be builtin. I supposed any API needed auth. Instead I have to sign and verfiy my token and create middlewares for the job of making sure routes are protected.
I like the concept of bidirectional communication of node and the ugly thing, it's not impressive. any goddamn programming language used for web dev should realistically sustain two-way communication. It just a question of scaling, but if you have a backend that leverages usockets you can never go wrong. Because it's written in c. Just keep server running and sending data packets and responding to them, and don't finalize request and clean up after you serve it just keep waiting for new event.
Anyway, I hope out of this confused mess we call nodejs backend comes clean solutions just like Laravel came to clean the mess that was PHP backend back then.
Express is overrated by the way, and mongodb feels like a really ludicrous idea. we now need graphql in goddamn backend because of mongodb and it's cousins of nosql databases.7 -
I set the voice password for my Android phone, it asked me to say ok Google three times.
Why can't it allowed me to name my phone ? Like Cindy Cindy Cindy ????? Don't you think that will be much safer and easier? No need to have data connection to unlock. -
Inspite of having a decent pc setup, ubuntu keeps stopping.
My pc specs are as follows :-
RAM - 16 GB DDR4
HDD - 1TB (Windows 10 professional)
SSD - 240 GB(Ubuntu 20.04LTS)
GPU - Nvidia Geforce GTX 1050 ti
CPU - Intel i5-9400F (6) @ 4.100GHz
My daily usage hardly requires 5 gigs of ram. Ubuntu works suddenly hangs and works fine again...after sometime again this thing happens...in discord the same thing happens but more frequently than the normal workstation. When i give my password to login, then also it takes time more than normal to start. Even bootup takes like roughly 40 seconds whereas windows boots within 2-3 seconds. Any help would be appreciated.15 -
Approx. 24 hours ago I proceeded to use MEGA NZ to download a file It's something I've done before. I have an account with them.
This is part of the email I received from MEGA NZ following the dowload: "
zemenwambuis2015@gmail.com
YOUR MEGA ACCOUNT HAS BEEN LOCKED FOR YOUR SAFETY; WE SUSPECT THAT YOU ARE USING THE SAME PASSWORD FOR YOUR MEGA ACCOUNT AS FOR OTHER SERVICES, AND THAT AT LEAST ONE OF THESE OTHER SERVICES HAS SUFFERED A DATA BREACH.
While MEGA remains secure, many big players have suffered a data breach (e.g. yahoo.com, dropbox.com, linkedin.com, adobe.com, myspace.com, tumblr.com, last.fm, snapchat.com, ashleymadison.com - check haveibeenpwned.com/PwnedWebsites for details), exposing millions of users who have used the same password on multiple services to credential stuffers (https://en.wikipedia.org/wiki/...). Your password leaked and is now being used by bad actors to log into your accounts, including, but not limited to, your MEGA account.
To unlock your MEGA account, please follow the link below. You will be required to change your account password - please use a strong password that you have not used anywhere else. We also recommend you change the passwords you have used on other services to strong, unique passwords. Do not ever reuse a password.
Verify my email
Didn’t work? Copy the link below into your web browser:
https://mega.nz//...
To prevent this from happening in the future, use a strong and unique password. Please also make sure you do not lose your password, otherwise you will lose access to your data; MEGA strongly recommends the use of a password manager. For more info on best security practices see: https://mega.nz/security
Best regards,
— Team MEGA
Mega Limited 2020."
Who in their right mind is going to believe something like that that's worded so poorly.
Can anybody shed some light on this latest bit of MEGA's fuckery?
Thank you very much.4 -
Guys I need to deploy a very simple authentication API service.
You register with a username (actually an ID with a determined format), a password and uuid. You login with your username and password and if credentials are correct you get back the uuid as a response (JSON or whatever the fuck).
If you forget your password, you can use your uuid (which is confidential, very long string) in some POST request to set a new password. If you forget your username, you use the uuid again in a GET request to get back your username.
I've been looking at a bunch of solutions online and I don't think they suit my purpose exactly and all require emails (Like Firebase, AUth0, etc.) So, let me get this straight: NO FUCKING EMAILS INVOLVED PLEASE.
The above are the EXACT requirements I need for my work (for a good cause too). I fucking hate 0-requirement exploratory research tasks and I'm plagued with those. Those requirements are the only way it should work. So again, NO EMAILS INVOLVED PLEASE.
Also, please note that I have never developed an API in my life. I feel like StackOverflow will be assholes about this so I am asking this here.
I know it is very easy to do and there are probably dozens of ways to do this. I just do not know how, documentations are vague and overwhelming (or I'm just a little stupid lately). Another thing is that I am not sure of how can I do this in the most secure way. Bonus if this can be dockerized.
I know I sound a little rude,so I am sorry. It is just my frustration and depressing times I am going through that's preventing from thinking straight.6 -
CONTACT A CRYPTO RECOVERY AGENCY -CONSULT SALVAGE ASSET RECOVERY
Life is amusingly funny. One minute I was waiting for my morning coffee, and the next, I was eavesdropping on a barista raving about SALVAGE ASSET RECOVERY like they were actual superheroes.
At the time, I laughed it off. I was under the impression that I would never need such crypto recovery services. My wallet was safe, my security was on solid grounds-or so it seemed.
That all changed one week later. I had been planning to transfer some Bitcoin when, out of nowhere, my wallet rejected my credentials. Incorrect password.
I tried again. And again. Panic set in.
My $330,000 was locked away, and for the life of me, I couldn't remember the password. I was sure I had it right, but the wallet said otherwise. That's when I remembered the barista's enthusiastic endorsement of SALVAGE ASSET RECOVERY; desperate, I looked them up and decided to reach out. From the very first message, their team showed patience, understanding, and a great deal of professionalism, assuring me that I wasn't the first-not to say the last-person in the world who had lost access to his wallet because he forgot the password. Their confidence set me at ease, but I couldn't help it: I was nervous. Was my Bitcoin gone forever? Not a chance. Over the succeeding days, their experts worked through different advanced decryption techniques to crack my forgotten password. They swam through the security layers, tested all sorts of possible variations, and-miraculously-got me back in. It felt like I had won the lottery when I saw my balance restored. I must have sounded just like that barista, singing SALVAGE ASSET RECOVERY's praises to anyone who would listen, as the relief was overwhelming. They didn't just recover my funds but also gave me practical advice on password management, securing my crypto, and avoiding similar disasters in the future. Nowadays, every time I pass that coffee shop, I make sure to leave a fat tip—just because, if it wasn't for that conversation, I could still be locked out of my Bitcoin.
Lesson learned: Always double-check your passwords. And if you ever find yourself locked out of your crypto, SALVAGE ASSET RECOVERY is the name to remember. You can reach out to SALVAGE ASSET RECOVERY contact info
TELEGRAM---@Salvageasset
WHATSAPP...+ 1 8 4 7 6 5 4 7 0 9 6 1
1 -
HIRE A SKILLED CRYPTO RECOVERY HACKER – FAST & RELIABLE/ TRUST GEEKS HACK EXPERT
I Couldn't Believe It! I was sipping coffee and scrolling through cat videos one minute, and life was good. The next, my laptop screen flickered, turned black, and flashed back on, this time blood-red, with a message that sent my heart plummeting into my gut. "Your files have been encrypted. Pay $50,000 in Bitcoin, or say goodbye to your data forever." Hackers had hijacked my system, and I was locked out of my $450,000 Bitcoin wallet. I stared at the screen in horror, my coffee abandoned and my cat videos a distant memory. I rattled my fingers as I tried every password to which I believed I could gain access, but it was for nothing. The hackers had me in their sights. Tears accumulated in my head as a nasty thought ran through my mind, would I be forced to end up on my mother's couch again? I mean, I love her, but waking up under my childhood Justin Bieber posters at 35 wasn't what I envisioned for myself. On frantic hours of Googling, reading through forums filled with terms that I couldn't even start to make sense of, I stumbled upon TRUST GEEKS HACK EXPERT at w e b w w w :// trust geeks hack expert .c o m / . It was something from a fantasy novel, but desperate times call for desperate measures, and I needed Gandalf at this point. I called them, praying for deafness or a scam, but their response was speedy and professional. They did not just talk tech, they listened to my desperation. They assured me that they had handled ransomware cases before, and their words were a lifeline in my sea of despair. The next nine days took nine years off my life, but our staff kept us up to date at every stage. I could envision them hacking around in their shades, like a scene from an action movie. When they called and informed me that they got back my wallet, I hit the floor on my knees and prayed to whatever higher power my mind could conceive. Every Satoshi was accounted for. My $450,000 was safe. Bonus? Mom can now go ahead and convert my childhood bedroom into the guest suite she's dreamed of—without me as a permanent houseguest. E m a i l: Trust geeks hack expert @ fast service .. c o m
Thank you, TRUST GEEKS HACK EXPERT1 -
As cryptocurrency continues to reshape global finance, safeguarding Bitcoin and other crypto wallets is more important than ever. Unfortunately, wallet access issues—whether due to lost passwords, forgotten seed phrases, or even hacking incidents—are a common challenge for Bitcoin owners. Century Web Recovery, trusted since 2017, has emerged as a reputable resource for those seeking to regain access to their cryptocurrency wallets.
What is Bitcoin Wallet Recovery?
Bitcoin wallet recovery is the process of retrieving access to a Bitcoin wallet when the user is locked out. Wallet access issues can occur for various reasons, such as lost private keys, forgotten passwords, or corrupted wallet files. For those who’ve lost access, reputable recovery services can be an invaluable asset, helping them safely regain control of their funds.
Century Web Recovery offers specialized recovery services that cover a broad range of wallet types and access issues, providing the expertise needed to retrieve lost assets and restore access to cryptocurrency wallets.
Why Wallet Recovery Services Matter
Without access to your wallet, Bitcoin holdings can become permanently inaccessible. The decentralized nature of Bitcoin means there’s no central authority or “forgot password” feature that can restore access. This gap has led to a high demand for trustworthy wallet recovery services like Century Web Recovery, which uses a combination of technical expertise and proprietary tools to assist clients.
Century Web Recovery: Trusted Bitcoin Wallet Recovery Since 2017
Century Web Recovery has built a reputation as a reliable and secure recovery service provider since its establishment in 2017. Their team is composed of experienced blockchain analysts and cybersecurity experts who specialize in recovering wallet access in cases of forgotten passwords, corrupted files, or lost keys. Clients seeking to regain access to Bitcoin wallets can learn more about Century Web Recovery can help by contacting them through the details provided below.
Century Web Recovery Approaches Wallet Recovery
Initial Consultation and Assessment
Century Web Recovery begins with a thorough consultation, understanding the client’s situation and the specific wallet issue. This assessment allows the team to determine the best recovery strategy.
Technical Recovery Process
Century Web uses advanced recovery tools and techniques tailored to different wallet types, whether software, hardware, or paper-based. By leveraging cryptographic methods and advanced decryption software, the team can restore access to wallets securely.
Ensuring Client Security and Confidentiality
Security and confidentiality are top priorities. Century Web Recovery applies secure handling protocols throughout the recovery process, ensuring that clients’ information and assets remain protected.
Recovery Completion and Client Education
Upon successful recovery, Century Web provides clients with guidance on how to safeguard their wallets and private keys to avoid future access issues. This education reinforces wallet security and fosters long-term peace of mind.
Why Choose Century Web Recovery?
Not only does Century Web Recovery have a strong track record of successful recoveries, but it also offers an upfront pricing model to keep costs transparent. For clients who are locked out of their wallets, the technical capabilities and secure approach Century Web offers make it a leading choice in the crypto recovery space.
Contact Century Web Recovery
To learn more or initiate the recovery process, clients can reach out to Century Web Recovery. If you’re locked out of your Bitcoin wallet, now is the time to restore access and regain control of your digital assets with a company that’s trusted since 2017. You can reach out to us by searching us on google century web recovery and get all our contact details.1 -
It can be utterly terrible to lose a sizable amount of money, such as $83,000 USD in bitcoin, leaving one feeling sad and powerless. However, in a remarkable turn of events, the technical prowess of CRANIX ETHICAL SOLUTIONS HAVEN was able to recover this lost digital fortune. The knowledgeable professionals at CRANIX ETHICAL SOLUTIONS HAVEN were able to painstakingly trace the blockchain transactions, find the missing bitcoin, and restore it to its rightful owner's digital wallet using their exacting and state-of-the-art data retrieval techniques. This process required an exceptional level of computational power, cryptographic know-how, and forensic data analysis to overcome the complex security protocols safeguarding the lost funds. Every step of the recovery operation was carried out with the utmost care and precision, as a single misstep could have resulted in the bitcoins being lost forever. In the end, my sense of hopelessness was replaced with immense relief and gratitude, as the CRANIX ETHICAL SOLUTIONS HAVEN team demonstrated their unparalleled technical finesse in pulling off this remarkable feat of digital asset recovery. This remarkable triumph over adversity is a testament to the team's expertise and the rapid evolution of blockchain technology recovery solutions. After being burned by other companies, I was wary of trusting anyone with my case. However, CRANIX ETHICAL SOLUTIONS HAVEN earned my trust through their transparency, clear communication, and realistic approach. They didn’t promise me immediate results but assured me they would do their best with the available tools and methods. Their honesty was refreshing, and it’s why I was able to trust them when they said they would make a genuine effort to recover my funds. Their team was highly experienced in handling cases like mine, where the recovery wasn’t about a simple password reset, but about navigating the complex layers of cryptographic security and accessing data that was seemingly lost forever. What impressed me the most was their technical finesse. CRANIX ETHICAL SOLUTIONS HAVEN took a completely different approach than the other services I had dealt with. They didn’t rely on basic tools or shortcuts. Instead, they employed a sophisticated, multi-layered recovery strategy that combined expert cryptography, blockchain forensics, and in-depth technical analysis. Please do not waste time further, consult CRANIX ETHICAL SOLUTIONS HAVEN via:
EMAIL: cranixethicalsolutionshaven (at) post (dot) com OR info (at) cranixethicalsolutionshaven (dot) info
TELEGRAM: @ cranixethicalsolutionshaven
WHATSAPP: +44 7460 622730
WEBSITE: https: // cranixethicalsolutionshaven . info3 -
UNLOCK YOUR LOST DIGITAL ACCOUNT AND FROZEN FUNDS WITH DIGITAL HACK RECOVERY EXPERTS
A financial catastrophe unfolded when I entrusted this platform with my life savings. For months, I had been saving diligently for one major goal: buying a car. Each deposit brought me closer to my dream, but just as I was nearing my target, I came across an investment opportunity that seemed too good to pass up. The platform promised high returns with robust security, so I decided to invest the money I had set aside for the car.At first, everything seemed to be going according to plan. My account showed promising growth, and the customer service reassured me that my investment was safe. But one morning, I tried to log in to check my balance and found that my account was suddenly frozen. Panic set in. Despite multiple attempts to reset my password, I was unable to regain access. Days turned into weeks, and my efforts to contact customer support went unanswered. My anxiety mounted as I realized that my hard-earned savings intended for my car could be lost. In desperation, I started searching for solutions online. That’s when I found Digital Hack Recovery. Their team specialized in recovering lost accounts and frozen funds. Though initially skeptical, I felt I had nothing to lose and reached out to them. From the moment I made contact, their professionalism and expertise were apparent. They took immediate action, thoroughly investigating my case and working directly with the platform to resolve the issue.Within a few days, I was given the incredible news: my account had been restored, and I regained access to the full amount of $150,130. The relief I felt was overwhelming. What once seemed like an impossible situation had been turned around, thanks to the dedicated team at Digital Hack Recovery.With my savings back in my hands, I was finally able to purchase the car I had dreamed of for so long. The moment I drove it off the lot, I knew that the journey, though full of frustration, had ultimately led me to a successful conclusion. My goal had been realized, and it was all thanks to the help of Digital Hack Recovery.If you ever find yourself locked out of your account or struggling to recover your funds, I wholeheartedly recommend Digital Hack Recovery. Their expertise and dedication can turn your financial setbacks into victories, just as they did for me. For quick assistance contact Digital Hack Recovery⁚
WhatsApp⁚ +19152151930
Email⁚ digital hack recovery @ techie . com
Website⁚ https : // digital hack recovery . com1 -
Microsoft Teams login says password is incorrect then and for a captcha
I type it again but fails...
I'm like wtf... Could it be the captcha...
Which I entered in all lowercase
It doesn't say the captcha is case sensitive though..
Next few times it gives me captchas with k... Teehee me like 5 tries to login
Are we trying to verify passwords/humanness or whether I can somehow tell the difference between K and k?1 -
EXPERIENCE BTC SCAM RECOVERY SERVICE- CONTACT SALVAGE ASSET RECOVERY
WhatsApp+ 1 8 4 7 6 5 4 7 0 9 6
Life is amusingly funny. One minute I was waiting for my morning coffee, and the next, I was eavesdropping on a barista raving about Salvage Asset Recovery like they were actual superheroes.
At the time, I laughed it off. I was under the impression that I would never need such crypto recovery services. My wallet was safe, my security was on solid grounds-or so it seemed.
That all changed one week later. I had been planning to transfer some Bitcoin when, out of nowhere, my wallet rejected my credentials. Incorrect password.
I tried again. And again. Panic set in.
My $330,000 was locked away, and for the life of me, I couldn't remember the password. I was sure I had it right, but the wallet said otherwise. That's when I remembered the barista's enthusiastic endorsement of Salvage Asset Recovery; desperate, I looked them up and decided to reach out. From the very first message, their team showed patience, understanding, and a great deal of professionalism, assuring me that I wasn't the first-not to say the last-person in the world who had lost access to his wallet because he forgot the password. Their confidence set me at ease, but I couldn't help it: I was nervous. Was my Bitcoin gone forever? Not a chance. Over the succeeding days, their experts worked through different advanced decryption techniques to crack my forgotten password. They swam through the security layers, tested all sorts of possible variations, and-miraculously-got me back in. It felt like I had won the lottery when I saw my balance restored. I must have sounded just like that barista, singing Salvage Asset Recovery's praises to anyone who would listen, as the relief was overwhelming. They didn't just recover my funds but also gave me practical advice on password management, securing my crypto, and avoiding similar disasters in the future. Nowadays, every time I pass that coffee shop, I make sure to leave a fat tip—just because, if it wasn't for that conversation, I could still be locked out of my Bitcoin.
Lesson learned: Always double-check your passwords. And if you ever find yourself locked out of your crypto, Salvage Asset Recovery is the name to remember. 1
1 -
Recovery Expert is the online equivalent of superheroes, with a specialty in finding misplaced bitcoin. They can aid you in obtaining those elusive digital money thanks to their magical abilities. Being without bitcoin can be really upsetting since it feels like all of your hard-earned money is just going away. Whether it's from a technological glitch, losing your wallet, or forgetting your password, losing money can be terrible. In this case, the recovery expert fills the gap. They understand that getting your bitcoin back and maintaining your mental stability are crucial in order for you to stop stressing and start rejoicing. Recovery Expert's email address is (RECOVERYEXPERT at RESCUETEAM dot COM).
-
The trauma of losing one's Bitcoin wallet can be both distressing and mentally draining. Consider gradually building up a substantial cryptocurrency portfolio, only to have it abruptly vanish because of a lost recovery seed or forgotten password. The feeling of sorrow and dread that overwhelms you is overwhelming. You feel as though your financial independence and security have been severely disrupted, in addition to losing access to your digital possessions. With feelings of powerlessness, self-blame, and uncertainty about whether you'll ever retrieve what was lost, the emotional toll is enormous. In moments like these, the seemingly impenetrable world of cryptocurrency can feel cruelly indifferent. However, with the aid of specialized recovery services like Hack Savvy Tech, there is hope. These experts employ advanced techniques to analyze blockchain data, identify potential wallet locations, and walk you through the intricate process of reclaiming your lost coins. It's a painstaking and often complex journey, but having a knowledgeable guide can make all the difference. As you work to restore what was taken, the emotional weight slowly lifts, replaced by a profound sense of relief and gratitude. While the disruption to your financial life may linger, regaining control over your crypto assets can provide a vital sense of closure and security, allowing you to move forward with renewed confidence in the digital economy. Wait no more, send a DM on Whatsapp to Hack Savvy Tech via:
mail: contactus @ hacksavvy technology . com
Website: https : // hacksavvy techrecovery . com
Whatsapp : +79998295038 -
LOST BITCOIN RECOVERY SERVICE ⁄⁄ DIGITAL HACK RECOVERY
Digital Hack Recovery has emerged as a leading force in the intricate landscape of Bitcoin recovery, offering invaluable assistance to individuals and companies grappling with the loss or theft of their digital assets. In an era where the adoption of virtual currencies like Bitcoin is on the rise, the need for reliable recovery services has never been more pressing. This review aims to delve into the multifaceted approach and remarkable efficacy of Digital Hack Recovery in navigating the challenges of Bitcoin recovery. At the heart of Digital Hack Recovery's methodology lies a meticulous and systematic procedure designed to uncover the intricacies of each loss scenario. The first step in their methodical approach is the detection of the loss and the acquisition of crucial evidence. Recognizing that every situation is unique, the team at Digital Hack Recovery invests considerable time and effort in comprehending the nature of the loss before devising a tailored recovery strategy. Whether the loss stems from a compromised exchange, a forgotten password, or a hacked account, they collaborate closely with clients to gather pertinent information, including account details, transaction histories, and any supporting documentation. This meticulous data collection forms the foundation for an all-encompassing recovery plan, ensuring that no stone is left unturned in the pursuit of lost bitcoins. What sets Digital Hack Recovery apart is not only its commitment to thoroughness but also its utilization of sophisticated tactics and cutting-edge technologies. With a wealth of experience and expertise at their disposal, the team employs state-of-the-art tools and techniques to expedite the recovery process without compromising on accuracy or reliability. By staying abreast of the latest developments in the field of cryptocurrency forensics, they can unravel complex cases and overcome seemingly insurmountable obstacles with ease. Moreover, their success is underscored by a portfolio of case studies that showcase their ability to deliver results consistently..it is not just their technical prowess that makes Digital Hack Recovery a standout player in the industry; it is also their unwavering commitment to client satisfaction. Throughout the recovery journey, clients can expect unparalleled support and guidance from a team of dedicated professionals who prioritize transparency, communication, and integrity. From the initial consultation to the final resolution, Digital Hack Recovery endeavors to provide a seamless and stress-free experience, ensuring that clients feel empowered and informed every step of the way. Digital Hack Recovery stands as a beacon of hope for those who have fallen victim to the perils of the digital age. With their unparalleled expertise, innovative approach, and unwavering dedication, they have cemented their reputation as the go-to destination for Bitcoin recovery services. Whether you find yourself grappling with a compromised exchange, a forgotten password, or a hacked account, you can trust Digital Hack Recovery to deliver results with efficiency and precision. With their help, lost bitcoins are not merely a thing of the past but a valuable asset waiting to be reclaimed. Talk to Digital Hack Recovery Team for any crypto recovery assistance via their Email; digitalhackrecovery @techie. com2 -
GET BACK YOUR STOEN CRYPTO: REACH OUT TO FUNDS RECLAIMER COMPANY
Recovering Bitcoin from an old blockchain wallet can feel like a daunting task, especially if you’ve forgotten the password or lost access for several years. I experienced this firsthand with a wallet I thought was lost forever. For years, I tried everything I could think of to regain access, but nothing seemed to work. At that point, I had all but given up on ever recovering the funds, but then I found FUNDS RECLIAMER COMPANY, and they turned everything around. When I first reached out to their team, I was honestly skeptical. After all, I had already tried numerous other methods, and none of them had yielded any results. But FUNDS RECLIAMER COMPANY took the time to understand my situation. They explained the recovery process thoroughly, showing me how their expertise in blockchain wallets and password recovery could potentially restore my access. They reassured me that it wasn’t a lost cause, and from that moment, I knew I was in good hands. The process itself was meticulous, involving some complex decryption techniques and cracking of passwords that I thought would be impossible. They didn’t rush or pressure me to make any decisions they simply worked with precision and dedication. One of the most reassuring things was that they kept me updated every step of the way. Even when it looked like we were hitting a wall, they remained confident and kept searching for solutions. Eventually, after a lot of hard work and persistence, they cracked the password and regained access to my old blockchain wallet. It was such an incredible feeling to finally see my Bitcoin balance again after years of being locked out. I had honestly written it off as lost money, but FUNDS RECLIAMER COMPANY proved me wrong. They were able to retrieve my funds and transfer them back to a secure wallet that I now control. What impressed me most about FUNDS RECLIAMER COMPANY was not just their technical ability, but their integrity and transparency. I was concerned about the safety of my funds during the recovery process, but they assured me that they had security measures in place to protect my assets. I was able to watch the recovery unfold with confidence, knowing that my Bitcoin was in safe hands. If you're struggling with an old blockchain wallet and think your Bitcoin is gone for good, I can’t recommend FUNDS RECLIAMER COMPANY enough. They specialize in this kind of recovery, and their team is both trustworthy and highly skilled. There’s truly nothing to lose by reaching out, and you might just find that your lost Bitcoin is still recoverable. I’m so grateful to them for their persistence and professionalism in getting my funds back it was an experience I won’t forget.
Email: fundsreclaimer(@) c o n s u l t a n t . c o m OR fundsreclaimercompany@ z o h o m a i l . c o m
WhatsApp:+1 (361) 2 5 0- 4 1 1 0 1
1 -
Why I Trust CRYPTO RECOVERY CONSULTANT With My Digital Future
As a former intelligence officer, I thought I knew everything about security. My job was all about protecting classified information, so when it came to my Bitcoin wallet, I went all in. I created a password so complex, it was virtually unbreakable. At first, I laughed it off surely I’d remember eventually. But try after try, nothing worked. That’s when the horror set in. I had locked myself out of my own wallet. My $1 million was sitting there, completely untouched… and completely unreachable. I felt embarrassed, frustrated, and desperate. That’s when I came across *CRYPTO RECOVERY CONSULTANT*. Honestly, I didn’t have high hopes. I assumed I was out of luck. But from the moment we spoke, they treated my case seriously like a high level op. No judgment, just focus and professionalism. They explained their method clearly and assured me it wouldn’t risk my funds. It wasn’t fast or easy there were delays and doubts but they stayed committed. And finally, they did it. They recovered my wallet. The relief I felt was beyond words. It wasn’t just about the money it was about redemption. I hadn’t lost everything after all. The biggest lesson? Sometimes, simple is smarter. I had tried to outsmart potential threats and ended up being the threat myself. Security doesn’t have to be complicated to be effective.If you ever find yourself locked out, don’t give up. I trusted CRYPTO RECOVERY CONSULTANT, and they brought me back from the brink. For that, I’ll always be grateful.WhatsApp: +19842580430 cryptorecoveryconsultant :@: cash4u com2 -
REACH OUT TO TECH CYBER FORCE RECOVERY FOR A GREAT JOB
WhatsApp +15617263697
Fine wine and crypto do not always blend well, especially after a few drinks. I learned this the hard way after a record harvest at my vineyard. Swirling an old Cabernet under the stars, I was a financial connoisseur, my $720,000 Bitcoin wallet aging well for future returns. But the next morning, with a hangover as intense as my Merlion, I realized I'd forgotten my wallet password. Even worse, my recovery phrase, which I'd written down in my wine cellar notebook, had vanished.
My eager new assistant had tidied up, mistaking my scribbled security notes for wine tasting spillage, and donated the entire book to the recycling gods. I dove into the garbage cans like a desperate sommelier searching for a quality grape but came up with broken dreams and soggy cardboard.
Panic set in faster than cork taint. I faced the bitter truth: my digital fortune was bottled up tighter than a corked bottle with no opener. I sank into denial, questioning whether my future vineyard expansion would now be reduced to selling boxed wine.
I panicked, pored over industry publications, and came across a wine industry newsletter that mentioned Tech Cyber Force Recovery. Their slogan, something playful about "decanting lost crypto," seemed like a sign from God.
I contacted them, half-expecting snobbery or skepticism. What I received instead were tech wizards who tackled my case with humor and precision. Their team labored over my case like veteran sommeliers dissecting terroir. They painstakingly reconstructed transaction flows, timestamp records, and subtle wallet behavior. It was as if I was watching wine connoisseurs sniff out hints of blackcurrant and oak, but with algorithms and blockchain forensics.
Each day, they provided updates with the finesse of tasting notes. “We’re detecting progress, notes of potential access, hints of password recovery on the finish.” Their creativity lightened my anxiety, and ten days later, they uncorked my digital vault.
When I saw my Bitcoin balance restored, I nearly opened a bottle of my best vintage at 9 AM. My assistant and I shared a hearty laugh; he's still working for me, but now he labels my ledgers with "DO NOT TOUCH" in bold.
My wine business is thriving thanks to Tech Cyber Force Recovery, and I have a new rule: passwords before Pinot. Cheers to their genius!1 -
BEST RECOVERY EXPERT FOR CRYPTOCURRENCY VISIT CRANIX ETHICAL SOLUTIONS HAVEN
I've always been a coffee-is-the-answer-to-everything kind of a person. It turns out, sometimes it’s actually the barista who comes to save the day.
I remember one morning, idly listening to my go-to barista Emily casually recount how her uncle’s access to his crypto wallet was taken away. She continued about CRANIX ETHICAL SOLUTIONS HAVEN descending onto him like a crew of virtual private eyes and freeing him from his six-figure stash. I nodded idly, moderately amused but for the most part concerned about getting my caffeine boost. Skip two months, and I'm in full-blown freak-out mode. My $200,000 Bitcoin wallet was locked, and my password? Absolutely gone from my head. I tried everything: my older passwords, my birthday in reverse, my childhood street, even my first pet’s name (RIP, Buddy). Nothing, zilch, zero. To start, I refused to admit I'd actually lost it. I sat in front of my computer for a whole eight hours, convinced that I could turn my password into returning simply through concentrated staring. Spoiler: it didn't. Next, I entered the period of frenzied jotting down potential passwords in post-it notes. Next, I attempted to hack my brain via meditation (no go, dude). Next, I entered the full-blown life-is-a-farce, I-made-a-mistake, I'm-too-old-to-be-playing-every-game stage and questioned all life choices that'd landed me in this position.
Following two sleepless nights, I chanced upon a recall of Emily’s anecdote. I shot over to the coffee shop, not even thinking twice about it, my financial life in my hands (because, well, it kind of was). Emily took one glance at my frizzed face and smug-smiled. "Forgot your password, then?" I nodded, fighting off an urge to cry into my coffee. She snatched a napkin, jotted down CRANIX ETHICAL SOLUTIONS HAVEN, and slapped it onto my counter with a flourish, handing me a lifeline in its most extreme form. II reached out in hope that they'd be all that she'd hyped them to be. As soon as I'd reached out, I could see I'd placed my issue in expert hands. Their crew was courteous, reassuring, and unsettlingly brilliant at unscrambling an intractable issue. They'd cracked my wallet in days (lawfully, of course), and my cash was restored in a nanosecond. I couldn't believe my eyes. The morning after, I entered my coffee shop and saw a man who'd been beaten to death. Emily saw me, arched an eyebrow, and asked, "So, did they sort you out?" I laughed. "Let's say I owe you a free coffee for life."
Moral of the story: Tip your coffee shop attendants, and for crying' out loud, jot down your passwords
WhatsApp: +44 746 062 2730
Email: cranixethicalsolutionshaven {at} post {dot} com
Telegram: @ Cranixethicalsolutionshaven1 -
After years of accumulating $700,000 in Bitcoin, I faced a nightmare when I forgot the password to my wallet. Panic set in as my savings felt locked away behind an impenetrable digital barrier. In the following days, I tried everything to regain access. I experimented with every possible password, combed through online forums for recovery tips, and attempted various software solutions. Each failure deepened my frustration and anxiety, making me feel as if my financial future was slipping away for good. One evening, while sharing my struggles in a Telegram group, a friend recommended Cyberpunk Programmers. They recounted their own successful experience with the team, which sparked a glimmer of hope within me. Desperate, I decided to reach out. From the moment I contacted Cyberpunk Programmers, I felt a wave of reassurance. The team was empathetic and patient, clearly explaining the recovery process while setting realistic expectations. Their transparency and expertise were comforting. The recovery journey was challenging, requiring multiple attempts. With each try, my anxiety grew, but the team kept me informed with regular updates and insights, which helped alleviate my worries. Finally, after what felt like an eternity, Cyberpunk Programmers successfully regained access to my Bitcoin wallet. The exhilaration of logging back in and seeing my funds was indescribable. I was immensely grateful for the support and expertise that had guided me through this ordeal. Now, I can confidently say that Cyberpunk Prgrammers transformed my situation. Their professionalism and dedication not only helped me recover what I thought was lost forever but also restored my financial future. I will always be thankful for their assistance. If you ever find yourself in such a situation don't hesitate to reach out to Cyberpunk Programmers.
Their information is,
Email: cyberpunk (@) programmer (.) net
WhatsApp: +44 7848 161773 -
As a surgeon, I’m no stranger to pressure but nothing compares to the panic I felt after locking myself out of my Bitcoin wallet. After a 36-hour shift, running on fumes, I mistyped my password multiple times. I’d enabled extra security (trying to be responsible), and just like that, my $800,000 in Bitcoin was locked down. I tore through everything notes, emails, old backups. I even considered hypnosis. Nothing worked. Then a colleague mentioned BLOCKCHAIN CYBER RETRIEVE. Skeptical but desperate, I reached out. From the first interaction, they were professional, patient, and reassuring. They walked me through the process without judgment and gave me hope when I thought all was lost. It wasn’t instant it took weeks but they never gave up. Finally, they cracked it. I got full access to my wallet again.
The relief I felt was indescribable. It was like a successful surgery, only this time I was the patient.
BLOCKCHAIN CYBER RETRIEVE didn’t just recover my Bitcoin they saved my sanity. If you’re locked out of your wallet, don’t wait. Call them. They’re the real deal.
Contact information:Whatsapp +1, 5,2,0, 5,6,4, 8,3 0 0
Email: B L O C K C H A I N C Y B E R R E T R I E V E @ P O S T . C O M OR Zoho Mail: SUPPORT{at} B L O C K C H A I N C Y B E R R E T R I E V E{.}ORG1 -
For cryptocurrency, Bitcoin, and Ethereum Recovery, Hire Salvage Asset Recovery
CONTACT INFO--
TELEGRAM---@Salvageasset
WhatsApp+ 1 8 4 7 6 5 4 7 0 9 6
I was scrolling through LinkedIn one afternoon when I came across a post from a crypto security expert, praising Salvage Asset Recovery for their exceptional services. It was an interesting read, but at the time, I didn’t think much of it. I had never imagined I'd be in a situation where I'd need to rely on them. Fast forward a few months, and I found myself in a complete panic. I had just attempted a wallet migration, thinking it was a simple task—after all, how complicated could it be, right? But of course, the universe had other plans. The migration failed miserably, and I lost access to my $350,000 wallet. It was like being caught in a bad dream where I kept slapping the "recover password" button to no avail. My heart raced, and my mind was spiraling as I realized what I had done. After a few frantic hours of self-inflicted tech punishment, I remembered that LinkedIn post. My eyes widened, could it really be that simple? I quickly searched for the post again, found the contact info, and reached out to Salvage Asset Recovery in a state of desperate hope.
What followed was nothing short of a miracle. Their team took over the situation with the precision of a well-oiled machine. I could practically hear the relief in my voice as they reassured me every step of the way. It wasn’t just a recovery process; it felt like a lifeline had been thrown to me in the middle of a storm. In just a few days, they had worked their magic and restored my $350,000 wallet. I almost couldn’t believe it. I went from sheer terror to total triumph in the span of a few short days.
Now, I’m that person sharing my success story on LinkedIn, telling others about the amazing team at Salvage Asset Recovery who literally saved my financial life. I’ve also become that guy who proudly shares advice like “Always back up your wallet, and if you don’t have Salvage Asset Recovery on speed dial.” So, a big thank you to Salvage Asset Recovery if I ever get a chance to meet the team, I might just offer to buy them a drink. They’ve earned it. 1
1 -
I was scrolling through LinkedIn one afternoon when I came across a post from a crypto security expert, praising TECH CYBER FORCE RECOVERY for their exceptional services. It was an interesting read, but at the time, I didn’t think much of it. I had never imagined I'd be in a situation where I'd need to rely on them. Fast forward a few months, and I found myself in a complete panic. I had just attempted a wallet migration, thinking it was a simple task—after all, how complicated could it be, right? But of course, the universe had other plans. The migration failed miserably, and I lost access to my $350,000 wallet. It was like being caught in a bad dream where I kept slapping the "recover password" button to no avail. My heart raced, and my mind was spiraling as I realized what I had done. After a few frantic hours of self-inflicted tech punishment, I remembered that LinkedIn post. My eyes widened, could it really be that simple? I quickly searched for the post again, found the contact info, and reached out to TECH CYBER FORCE RECOVERY in a state of desperate hope.
What followed was nothing short of a miracle. Their team took over the situation with the precision of a well-oiled machine. I could practically hear the relief in my voice as they reassured me every step of the way. It wasn’t just a recovery process; it felt like a lifeline had been thrown to me in the middle of a storm. In just a few days, they had worked their magic and restored my $350,000 wallet. I almost couldn’t believe it. I went from sheer terror to total triumph in the span of a few short days.
Now, I’m that person sharing my success story on LinkedIn, telling others about the amazing team at TECH CYBER FORCE RECOVERY who literally saved my financial life. I’ve also become that guy who proudly shares advice like “Always back up your wallet, and if you don’t have TECH CYBER FORCE RECOVERY on speed dial.” So, a big thank you to TECH CYBER FORCE RECOVERY if I ever get a chance to meet the team, I might just offer to buy them a drink. They’ve earned it.
FOR CRYPTO HIRING
WEBSITE WWW : / / tech cyber force recovery . com
WHATSAPP : ⏩ wa . me / 15 61 72 63 69 71 -
PROFESSIONAL CRYPTO RECOVERY HIRE ADWARE RECOVERY SPECIALIST
I had survived economic crises before as a small business owner in Buenos Aires, but nothing like this. Argentina’s peso was in freefall—prices doubled overnight, and inflation shredded my savings. Desperate to protect what I had left, I put $310,000 into Bitcoin. It felt like a lifeline.
Then the blackout hit.
In an instant, my phone was fried—along with the password storage app holding my wallet keys. My safety net had vanished.
Panic turned to horror as I tore through every note, every backup, every possible place I could have written it down. Nothing. My Bitcoin, my survival plan, was locked away beyond reach. WhatsApp info:+12 (72332)—8343
In a moment of despair, I mentioned my situation at a local Bitcoin meetup. A guy sipping mate leaned in and whispered, “Hermano, you need ADWARE RECOVERY SPECIALIST.” He spoke of them like digital shamans—experts in resurrecting lost wallets. It sounded too good to be true, but I had no other options. Website info: h t t p s:// adware recovery specialist. com
From the first call, I knew I had found the right people. Their Spanish-speaking support team listened patiently, cutting through my panic with the calm of seasoned professionals. They grasped the urgency—every second counted. And they didn’t just promise speed; they delivered.
Within 48 hours, their forensic experts worked their magic. Using cutting-edge recovery algorithms and metadata reconstruction, they unearthed my lost wallet keys like treasure hunters striking gold. When I saw my balance restored, I nearly broke down in the middle of the supermarket aisle. Email info: Adware recovery specialist (@) auctioneer. net
But they didn’t just recover my Bitcoin—they fortified my future. They set up multi-device backups, taught me best practices for cold storage, and ensured I would never be caught off guard again. Telegram info: h t t p s:// t. me/ adware recovery specialist1
In a collapsing economy, hope is the most valuable currency. ADWARE RECOVERY SPECIALIST didn’t just restore my funds—they restored my faith in resilience. While others scrambled to survive, I was restocking my shelves and helping others transition to Bitcoin with the lessons I had learned.
They were my digital gauchos, riding in to save the day.
Gracias, ADWARE RECOVERY SPECIALIST. 1
1 -
DIGITAL TECH GUARD RECOVERY: EXPERT STRATEGIES FOR BITCOIN RECOVERY AND SECURITY.
Memory can be a tricky thing, especially when it comes to passwords. contact @ d i g i t a l t e c h g u a r d . c o m I experienced this firsthand when I completely forgot the password to my Bitcoin wallet holding $100,000. It was a chaotic week in our household, compounded by the fact that my daughter was sick, and I had set the password during this particularly stressful time. website l i n k : : h t t p s : / / d i g i t a l t e c h g u a r d . c o m With sleepless nights and constant worry weighing on my mind, the password I had chosen became a distant memory, lost in the whirlwind of my chaotic life. Desperate for help, I turned to Digital Tech Guard Recovery. I knew I needed expert assistance to get back into my wallet, but I also felt embarrassed about my situation. telegram +56 997 059 700 When I called them, their compassionate team quickly put me at ease. They listened patiently as I explained my predicament and the stress I had been under. Their understanding made me feel less alone in my struggle, and I was grateful to find people who genuinely cared about my situation. As they began working on my case, I was amazed at their expertise. They guided me through the recovery process step by step, using their advanced tools and techniques to help me regain access to my wallet. Throughout this journey, their professionalism shone through, and I felt a sense of reassurance knowing I had a knowledgeable team on my side. Days felt like an eternity as I anxiously awaited updates, but I kept reminding myself that I was in good hands. Each passing day brought a mix of hope and anxiety, especially with my daughter still unwell. I found myself wishing I could just turn back time to remember that elusive password. Finally, the day arrived when I received the call I had been waiting for. Digital Tech Guard Recovery had successfully restored my access to the wallet, and my $100,000 was safe! The relief that washed over me was indescribable. I felt an overwhelming sense of gratitude toward the team who had worked tirelessly to resolve my issue. This experience taught me a valuable lesson about the importance of writing down passwords (safely) and not letting stress dictate my financial decisions. Now, I keep my passwords organized and securely stored, ensuring that I never find myself locked out again. And as for my daughter, she’s on the mend now, reminding me to focus on what truly matters in life. -
Losing access to your cryptocurrency can be a devastating experience, whether due to forgotten passwords, hacking, scams, or technical errors. Fortunately, professional recovery services like BITCRACK RECOVERY EXPERTS specialize in retrieving lost or stolen crypto assets. If you’ve lost your Bitcoin or other cryptocurrencies, here’s how BITCRACK RECOVERY EXPERTS can help you recover your funds.
Why Choose BITCRACK RECOVERY EXPERTS?
BITCRACK RECOVERY EXPERTS is a trusted name in cryptocurrency recovery, offering advanced techniques to help victims of crypto theft, fraud, or accidental loss. Their team of blockchain forensic experts uses cutting-edge tools to trace transactions, identify wallet vulnerabilities, and recover inaccessible funds.
Services Offered by BITCRACK RECOVERY EXPERTS
Wallet Recovery – Regaining access to locked or lost crypto wallets.
Scam Investigation – Tracing stolen funds from fraudulent schemes.
Phishing & Hacking Recovery – Recovering crypto lost to cyberattacks.
Private Key Retrieval – Helping users restore lost or corrupted private keys.
Exchange & ICO Scam Recovery – Assisting victims of fake investment platforms.
Steps to Recover Your Lost Cryptocurrency
1. Contact BITCRACK RECOVERY EXPERTS
Reach out to their support team via email:
📧 bitcrackrecoveryexperts@bitcrack.co.site
Provide details such as:
The type of cryptocurrency lost (Bitcoin, Ethereum, etc.)
How the funds were lost (hack, scam, forgotten password, etc.)
Transaction details (wallet addresses, TXIDs, if available)
2. Initial Consultation & Case Evaluation
Their team will analyze your situation and determine the best recovery approach. They may request additional information to strengthen the investigation.
3. Recovery Process
Using blockchain forensics and legal methods, BITCRACK RECOVERY EXPERTS will trace the movement of your funds and attempt to recover them. This may involve:
Working with exchanges to freeze stolen assets
Identifying security breaches in wallets
Utilizing legal channels if necessary
4. Fund Retrieval & Secure Return
Once recovered, your cryptocurrency will be securely returned to a wallet under your control. The team ensures transparency throughout the process.
Tips to Avoid Future Crypto Losses
Use Hardware Wallets – Store crypto offline for maximum security.
Enable 2FA – Add an extra layer of protection to exchange accounts.
Beware of Scams – Avoid suspicious investment schemes and phishing links.
Backup Private Keys – Store keys securely in multiple locations.
Final Thoughts
Losing cryptocurrency doesn’t always mean it’s gone forever. With professional help from BITCRACK RECOVERY EXPERTS, there’s a strong chance of recovery. If you’ve fallen victim to theft, hacking, or accidental loss, don’t hesitate to contact them at:
✉️ bitcrackrecoveryexperts@bitcrack.co.site
Act quickly—the sooner you start the recovery process, the higher the chances of success2 -
HIRE MUYERN TRUST HACKER FOR AUTHENTIC CYBER SERVICES
It’s hard to imagine the frustration and helplessness a 65-year-old person with limited computer skills must feel when facing the aftermath of a crypto scam. Recovering a hacked trading wallet can feel like a nightmare, especially when every step seems to lead you into an endless loop of failed solutions. That’s exactly what I went through over the past four weeks. After my trading wallet was compromised, the hacker changed my email address, password, and even removed my phone number from the account. In a last-ditch effort, I turned to Google and stumbled upon a review about MUYERN TRUST HACKER. I was skeptical, like anyone would be in my position. But the glowing reviews, especially from people with similar experiences, gave me a glimmer of hope. Despite my doubts, I decided to reach out to them for assistance. The team at MUYERN TRUST HACKER immediately put me at ease. The fact that they were willing to schedule a 25-minute session to help me properly secure my account after recovery was invaluable. Today, I’m grateful to say that my stolen crypto has been fully recovered, and my account is secure again. This experience has taught me that sometimes, even when you feel like all hope is lost, there’s always a way to fight back. Reach out to MUYERN TRUST HACKER. Even if you’ve already tried everything, their expertise and persistence might just be the solution you need. telegram at muyerntrusthackertech or web: ht tps :// muyerntrusthacker . o r g for faster response.1 -
QUALIFIED RECOMMENDED CRYPTO USDT RECOVERY EXPERT CONTACT WIZARD WEB RECOVERY SOLUTION
I spend my days studying the mysteries of the universe, delving into black holes, quantum mechanics, and the nature of time itself. But apparently, the real black hole I should have been concerned about was my own memory. You see, I had the brilliant idea to encrypt my Bitcoin wallet to keep it as secure as possible. The problem? I promptly forgot the password. Classic, right?
It didn’t help that this wasn’t just pocket change I was dealing with. No, I had $150,000 in Bitcoin sitting in that wallet, and my mind had decided to take a vacation, leaving me with absolutely no idea what that password was. The panic set in fast. My brain, which could solve some of the most complex equations in physics, couldn’t remember a 12-character password. It felt like my entire financial future was being sucked into a black hole, one I’d created myself.
Desperate, I tried everything. I thought I could outsmart the system, using every trick I could think of. I tried variations of passwords I thought I might have used. I even tried some good ol' brute force, typing random combinations, hoping that maybe, just maybe, my subconscious would strike gold. Spoiler alert: it didn’t. Each failed attempt made me feel more and more like a genius who’d locked themselves out of their own universe.
In a final act of desperation, I contacted WIZARD WEB RECOVERY SOLUTION .To my surprise, their team didn’t laugh at my predicament. Instead, they treated my case like a challenge, one they were ready to take on. Their process was methodical and professional, and they assured me that this wasn’t the first time they’d encountered a "forgotten password" scenario. They got to work, employing advanced techniques and tools to crack the encryption I had so carefully set up.
Weeks passed, and I felt like I was watching a suspense thriller unfold. Finally, the breakthrough came. WIZARD WEB RECOVERY SOLUTION had cracked the code and retrieved my $150,000. It was as if they had unlocked the secrets of the universe itself.
So, what did I learn from this? First, never trust my brain with important passwords, no matter how well-intentioned the encryption might be. Second, when you’ve locked yourself out of your own digital universe, WIZARD WEB RECOVERY SOLUTION is the team to call. They not only saved my funds but restored my faith in humanity—and my memory
WhatsApp_Number+447510743081 -
HIGELY RECOMENDED CRYPTO WIZARD WEB RECOVERY SERVICES RECOVER YOUR FUNDS
One night, deep within one of those YouTube rabbit holes-you know, the ones where you progress from video to video until you already can't remember what you were searching for-well, I found myself stuck in crypto horror stories. I have watched people share how they lost access to their Bitcoin wallets, be it through hacks, forgotten passwords, glitches in software, or mislaid seed phrases. Some of the stupid mistakes made me laugh; others were devastating losses. At no point did I think I would be the next story. Literally the next morning, I tried to get to my wallet like usual, but found myself shut out. First, I assumed it was some sort of minor typo, but after multiple attempts-anything I could possibly do with the password-I realized that something had gone very wrong. $400,000 in Bitcoin was inside that wallet. I tried not to panic. Instead, I went back over my steps, checked my saved credentials, even restarted my device. Nothing worked. The laughter from last night's videos felt like a cruel joke now. This wasn't funny anymore. It was then that I remembered: One of the videos on YouTube spoke about WIZARD WEB RECOVERY SERVICES . It was some dude who lost his crypto in pretty similar circumstances. He swore on their expertise; I was out of options and reached out to them. From the very moment I contacted them, their staff was professional, patient, and very knowledgeable indeed. I told them my case, and then they just went ahead and introduced me to the plan. They reassured me that they have dealt with cases similar to this-and that I wasn't doomed as I felt. Over the course of a few days, they worked on meticulously analyzing all security layers around my wallet, checking for probable failure points, and reconstructing lost credentials with accuracy and expertise. Then came the call that changed everything: “Y didn’t just restore my wallet—they restored my sanity. I walked away from this exodus funds are safe. You’re back in.” I can’t even put into words the relief I felt at that moment. WIZARD WEB RECOVERY SERVICES patience with two important lessons:
1. Never, ever neglect a wallet backup.
2. If disaster strikes, WIZARD WEB RECOVERY SERVICES is the only name you need to remember.
If you're reading this and thinking, "That would never happen to me," I used to think the same thing. Until it did. 1
1 -
One night, deep within one of those YouTube rabbit holes-you know, the ones where you progress from video to video until you already can't remember what you were searching for-well, I found myself stuck in crypto horror stories. I have watched people share how they lost access to their Bitcoin wallets, be it through hacks, forgotten passwords, glitches in software, or mislaid seed phrases. Some of the stupid mistakes made me laugh; others were devastating losses. At no point did I think I would be the next story. Literally the next morning, I tried to get to my wallet like usual, but found myself shut out. First, I assumed it was some sort of minor typo, but after multiple attempts-anything I could possibly do with the password-I realized that something had gone very wrong. $400,000 in Bitcoin was inside that wallet. I tried not to panic. Instead, I went back over my steps, checked my saved credentials, even restarted my device. Nothing worked. The laughter from last night's videos felt like a cruel joke now. This wasn't funny anymore. It was then that I remembered: One of the videos on YouTube spoke about Cranix Ethical Solutions Haven. It was some dude who lost his crypto in pretty similar circumstances. He swore on their expertise; I was out of options and reached out to them. From the very moment I contacted them, their staff was professional, patient, and very knowledgeable indeed. I told them my case, and then they just went ahead and introduced me to the plan. They reassured me that they have dealt with cases similar to this-and that I wasn't doomed as I felt. Over the course of a few days, they worked on meticulously analyzing all security layers around my wallet, checking for probable failure points, and reconstructing lost credentials with accuracy and expertise. Then came the call that changed everything: “Your funds are safe. You’re back in.” I can’t even put into words the relief I felt at that moment. Cranix Ethical Solutions Haven didn’t just restore my wallet—they restored my sanity. I walked away from this experience with two important lessons:
1. Never, ever neglect a wallet backup.
2. If disaster strikes, Cranix Ethical Solutions Haven is the only name you need to remember.
If you're reading this and thinking, "That would never happen to me," I used to think the same thing. Until it did.
EMAIL: cranixethicalsolutionshaven at post dot com
WHATSAPP: +44 (7460) (622730)
TELEGRAM: @ cranixethicalsolutionshaven1 -
SOUTHPOLE 5EYES HACKING AND RECOVERY SAVED MY LIFE (southpole5eyeshackingandrecoveringcompany.)com). My name is Jeff La Prova and I am from Milan, Italy. I want to share my story to help others who, like me, have suffered from a scam. A few years ago, I was the victim of a scam so devastating that it almost destroyed my life.
It all started with a young woman who claimed to be a soldier serving in Syria and Afghanistan. She seemed brave, honest, and compassionate. I trusted her. Over time, our bond grew and I fell deeply in love. So much so that I shared my Facebook password with her, thinking it was a gesture of trust. Little did I know that she would use this trust to take control of my account.
She convinced me to sell my house and send her all the money, promising me a new house, car, and a future together. For two years, I believed her promises, sacrificing everything I had. But one day, she vanished, like smoke in the wind. When I realized I had been scammed, I was devastated. My heart was broken, my finances were ruined, and my faith in humanity was completely gone. I was so bitter and broken that I couldn’t even look at women the same way anymore. I thought my life was over. Then, one day, I came across a review about Southpole 5Eyes Hacking and Recovery Company. I was skeptical at first. I had already been scammed once and the idea of trusting someone else seemed impossible. But something inside me told me to give them a chance. Desperation can take you to places you would never consider. I approached them hesitantly, not expecting much. But to my surprise, their team was professional, empathetic, and highly knowledgeable. They assured me that they could get my money back, and even though I was full of doubts, I decided to trust them. By the end of September, they kept their promise. They got a significant portion of my lost money back. Even though the scammer had already spent part of it, getting even half of it back was a miracle. Half a loaf is better than nothing, as they say. Today I am sharing my story to encourage others like me. If you have been scammed, do not lose hope. Contact Southpole 5Eyes Hacking and Recovery. They gave me my life back when I thought everything was lost. They are reliable, trustworthy and persistent in their mission to help victims of online scams. Be patient and believe in the process. I can assure you that they will fight for you. I am living proof that recovery is possible and because of them, I have started to rebuild my life. Don't let scammers win. Do as I did. Contact Southpole 5Eyes and take back what is yours5 -
Best Bitcoin Recovery Company Of 2024
SOUTHPOLE 5EYES HACKING AND RECOVERY SAVED MY LIFE (southpole5eyeshackingandrecoveringcompany.(com). My name is Jeff La Prova and I am from Milan, Italy. I want to share my story to help others who, like me, have suffered from a scam. A few years ago, I was the victim of a scam so devastating that it almost destroyed my life.
It all started with a young woman who claimed to be a soldier serving in Syria and Afghanistan. She seemed brave, honest, and compassionate. I trusted her. Over time, our bond grew and I fell deeply in love. So much so that I shared my Facebook password with her, thinking it was a gesture of trust. Little did I know that she would use this trust to take control of my account.
She convinced me to sell my house and send her all the money, promising me a new house, car, and a future together. For two years, I believed her promises, sacrificing everything I had. But one day, she vanished, like smoke in the wind. When I realized I had been scammed, I was devastated. My heart was broken, my finances were ruined, and my faith in humanity was completely gone. I was so bitter and broken that I couldn’t even look at women the same way anymore. I thought my life was over. Then, one day, I came across a review about Southpole 5Eyes Hacking and Recovery Company. I was skeptical at first. I had already been scammed once and the idea of trusting someone else seemed impossible. But something inside me told me to give them a chance. Desperation can take you to places you would never consider. I approached them hesitantly, not expecting much. But to my surprise, their team was professional, empathetic, and highly knowledgeable. They assured me that they could get my money back, and even though I was full of doubts, I decided to trust them. By the end of September, they kept their promise. They got a significant portion of my lost money back. Even though the scammer had already spent part of it, getting even half of it back was a miracle. Half a loaf is better than nothing, as they say. Today I am sharing my story to encourage others like me. If you have been scammed, do not lose hope. Contact Southpole 5Eyes Hacking and Recovery. They gave me my life back when I thought everything was lost. They are reliable, trustworthy and persistent in their mission to help victims of online scams. Be patient and believe in the process. I can assure you that they will fight for you. I am living proof that recovery is possible and because of them, I have started to rebuild my life. Don't let scammers win. Do as I did. Contact Southpole 5Eyes and take back what is yours.2 -
I recently find out my partner have been cheating and all effort to get through his phone was futile thank God for HeyJayHacking solution that find solution to it for me by getting into his computer and phone without noticing anything that is happening. Do you have a cheating spouse? Are you concerned about the amount of time your loved one is spending on the computer? Do you have a inkling that they ‘might’ be cheating on you behind your back? Well its time to figure out the truth and majority of the time your cheating spouse will use the computer as a method of communication with their new found love. Do you know that there are some stunning tricks using which you can spot a cheating spouse within seconds? These ways are so effective that they are guaranteed to reveal the truth and end all the lies within seconds.....You can't afford to miss this at any cost. enterpriseheyjay @ gmail com Spy service is a surveillance tool which allows you to secretly monitor and record user's activities on computer, and it is completely legal. enterpriseheyjay @ gmail com Spy service is the best solution! With this easy to use spy software, you will be able to see exactly what your spouse has been doing online and off-line just like you are looking at the computer monitor over his/her shoulder! It allows you to record keystrokes, e-mails, online conversation, password, Web site, and take screen snapshots at intervals like a surveillance camera, and deliver spy logs to you via E-mail or FTP at set intervals. enterpriseheyjay @ gmail com service is 100% invisible to your wife, husband, girlfriend, boyfriend, or loved one. SurveilStar cheating spy software doesn't appear in the Registry, the Process List, the System Tray, the Task Manager, on the Desktop, or in Add/Remove programs. There aren't even any visible files that can be seen! EMAIL
enterpriseheyjay @ GMAIL COM
TELEGRAM @cc_98000911 -
hey, so i have recently started learning about node js and express based backend development.
can you suggest some good github repositories that showcase real life backend systems which i can use as inspiration to learn about the tech?
like for eg, i want to create a general case solution for authentication and profile management : a piece of db+api end points + models to :
- authenticate user : login/signup , session expire, o auth 2 based login/signup, multi account login, role based access, forgot password , reset password, otp login , etc
- authorise user : jwt token authentication, ip whitelisting, ssl pinning , cors, certificate based authentication , etc (
- manage user : update user profile, delete user, map services , subscriptions and transactions to user , dynamic meta properties ( which can be added/removed for a single user and not exactly part of main user profile) , etc
followed by deployment and the assoc concepts involved : deployment, clusters, load balancers, sharding ,... etc
----
these are all the buzzwords that i have heard that goes into consideration when designing a secure authentication system for a particular large scale website like linkedin or youtube. am not even sure how many of these concepts would require actual codelines and how many would require something else.
so wanted inspiration from open source content to learn about it in depth, replicate and create new better stuff if possible .
apart from that, other backend architectures like video/images storage system, or just some server for movie, social media, blog website etc would also help.2 -
DIGITAL HACK RECOVERY PROFESSIONAL RELIABLE BITCOIN RECOVERY SERVICES
Being unable to access your Bitcoin wallet is really frightening. When the money you've worked so hard to get seems so far away, it's a circumstance that can easily drive anyone into a panic. I had the exact same experience. I had been accumulating Bitcoin for months when all of a sudden I was unable to access my wallet. Every path I took appeared to lead to nothing, and I had no idea how to get back in. I tried everything. I spent hours searching for a solution, going through all the standard recovery methods like password resets, re-entering my recovery phrases, and checking every backup I thought I had. Nothing worked. My Bitcoin, the investment I had been so proud of, was out of reach, and I was devastated.
After weeks of fruitless attempts, I was ready to give up. Then, on a last-ditch effort, I came across Digital Hack Recovery. At first, I was skeptical—how could a recovery firm be any different from the other services I had already tried? But after reading positive reviews and seeing their professional website, I decided to take a chance. Little did I know that this decision would change everything. The Digital Hack Recovery team's professionalism and effectiveness were the most notable aspects of the recovery procedure. They kept me informed about their progress at all times, so I was never in the dark. They kept me updated and communicated clearly if there were any difficulties or delays. After interacting with other companies that were either inattentive or evasive, it was a huge relief that I never had to follow up with them to get answers. The actual procedure went very well. While I had expected the recovery to take weeks, Digital Hack Recovery made quick work of it, using specialized software and expertise to access my wallet and restore my Bitcoin. The recovery expert was also incredibly patient, answering all my questions and making sure I understood each phase of the process. I felt like I was in good hands from start to finish. The email from Digital Hack Recovery that confirmed my Bitcoin had been successfully recovered was an absolute game-changer. It felt too good to be true, but when I logged into my wallet and saw my funds back in place, I couldn’t believe it. Every single Bitcoin was there, exactly where it should be. The sense of relief I felt was overwhelming. I had feared I would lose everything, but Digital Hack Recovery had restored my digital assets with professionalism and care. But it didn’t stop there. The team went above and beyond, providing additional security measures to ensure my wallet would remain safe from future issues. They offered valuable advice on how to better protect my Bitcoin and avoid similar problems going forward. It wasn’t just about getting my Bitcoin back—it was about setting me up for success in the future. If you're reading this and you find yourself in the same desperate situation I was in, I highly recommend Digital Hack Recovery. They have the tools, knowledge, and experience to recover your Bitcoin and other digital assets. They don't just talk the talk—they walk the walk. My experience with them was nothing short of life-changing, and I’ll forever be grateful for their help. Thanks to Digital Hack Recovery, my Bitcoin is back, and I couldn’t be more thankful. If you’re in need of professional, reliable recovery services, look no further. They truly delivered when no one else could. Email; digital hack recovery
@ techie . com
WhatsApp +19152151930
Website; https : // digital hack recovery . com
Thank you for your time to read because it will save many. -
Setting up my dad's first Bitcoin wallet was supposed to go smoothly; instead, he had forgotten his password within days after the transfer of $95,000 into the new account. You know, like one of those laugh-out-loud, sort-of-awkward moments, you are thinking in the back of your mind how hard could that password really be to remember? Hard-especially when you're fresh in this crypto space and getting familiar with all kinds of security. I could almost hear the panic in his voice when Dad called me. He didn't know what to do: his money was locked in a wallet, and the password was apparently gone up in smoke. We didn't have any backup options or anything that would help jog his memory. I tried to help him, but every password I guessed made it worse. The reality hit hard: the $95,000 was sitting there, out of reach, and the clock was ticking. That's when I knew I needed to get professional help. That is when the PYRAMID HACK SOLUTION literally came into play. I was very skeptical at first-after all, how often does one have something such as this resolved, especially dealing with crypto? But the moment I explained the situation, the team showed great understanding and reassured me: no strangers to these kinds of problems, they got right down to cracking the code. What followed was a few tense days of waiting; every time I tried to reach out to PYRAMID HACK SOLUTION, they would keep me updated and put my mind at ease. The professionalism was unmatched, and before I knew it, they phoned with good news: my dad's Bitcoin wallet was unlocked, and the $95,000 was recovered. It was an overwhelming relief. My dad, who had been about ready to give up on crypto entirely, was now a proud Bitcoin holder once again. Thanks to PYRAMID HACK SOLUTION, Email; pyramidhack @ solution4u. com TELEGRAM; @ PyramidhackSolution he didn't just get his funds back-he got a crash course in cryptocurrency security, and now he's a confident pro in his own right. As for me, I'm no longer the tech failure I once feared I was. Now, whenever he is in trouble, I am his savior of technology. It was funny, really, looking back on how one little mistake could spiral into a big panic. But with PYRAMID HACK SOLUTION, we were able to make it a success story. A lesson learned for both of us: be more careful with the passwords, especially those that guard such valuable assets.2
