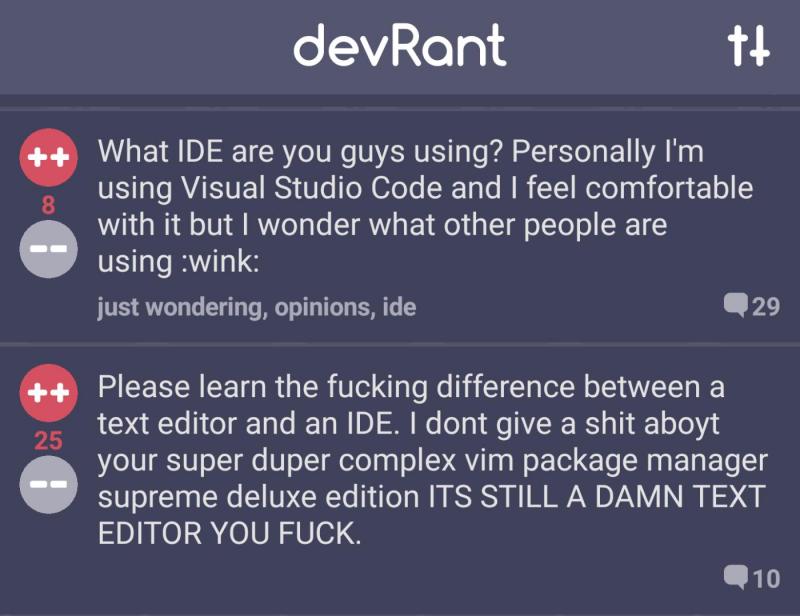
Join devRant
Do all the things like
++ or -- rants, post your own rants, comment on others' rants and build your customized dev avatar
Sign Up
Pipeless API

From the creators of devRant, Pipeless lets you power real-time personalized recommendations and activity feeds using a simple API
Learn More
Search - "algorithm"
-
Proud moment today when I actually made an hsv to rgb conversion algorithm by following a formula rather than copying code from stack overflow
 28
28 -
Algorithm: from the Greek "algos" (pain) and rhythmos (repetition), we derive the true meaning of this word: REPEATED PAIN.
:D5 -
A Machine Learning algorithm walks into a bar.
The bartender asks, "What'll you have?"
The algorithm says, "What's everyone else having?"1 -
Well apparently my compression algorithm actually made the file bigger. Back to the drawing board I guess?8
-
I spent three hours coding some algorithm and then looked it up on Stack Overflow out of curiosity. Big surprise. Someone did the exact same thing but more effeciently, and had all the code in his answer on SO.
Ughhhhhhhh 😓4 -
There is NOTHING more satisfying than having an algorithm suddenly click while you are in the shower.
I got a program for determining Prime Numbers using Extended Euclid Algorithm from ~2 to .28 seconds <35 -
I want to thank every Indian computer scientist on Youtube. Because of these guys I passed my Algorithms and Data Structures Exam.10
-
When you can code thousands of lines but is lost of words when trying to communicate to humans how you did it.4
-
This spring I was working on a library for an algorithm class at uni with some friends and one of the algorithm was extremely slow, we were using Python to study graphs of roads on a map and a medium example took about 6-7h of commission to finish (I never actually waited for so long, so maybe more).
I got so pissed of for that code that I left the lab and went to eat. Once I got back I rewrote just the god-damned data structure we were using and the time got down to 300ms. Milliseconds!
Lessons learned:
- If you're pissed go take a walk and when you'll come back it will be much easier;
- Don't generalize to much a library, the data structure I write before was optimized for a different kind of usage and complete garbage for that last one;
- Never fucking use frozen sets in Python unless you really need them, they're so fricking slow!3 -
I just experienced the opposite of rant.
I spent 1 entire day ranting about a algorithm I couldn't write with no issues, it occupied all my mind and got me pissed of.
And today, I rewrote it entirely, and it works perfectly everywhere.
I was like : "No it can't work here. Oh ok", "And here's the bug ! No ? Nice.", "Don't tell me it'll work here. I'm a God".
That's why I love being a dev :D
Thank you, you freaking problem I had !7 -
!rant
After reading the wiki page over and over, I was finally able to implement Dijkstra's algorithm 😃4 -
Juste design a new algorithm to evaluate the chance of a project (any kind of project) will exceed the budget (time of cost). This algorithm been proven to be right almost all the time.

-
Is there a bug in the way it's decided which posts are displayed? This is on algorithm mode. There are a lot more 250++ posts below here with a couole of 1++ posts in between. And almost all of them I've seen before and ++d them
 23
23 -
Let's see the coder in you.
If I give input: 1 output: 2
If I give input: 2 output:1
Only these two test cases needed.
You should not use control structures such as if,else,for,while,switch etc. (The answer is simple) (Don't cheat)
int number;
cin>>number; //get number
cout<<??????; //Your code48 -
Spent two days debugging my algo to figure it was a problem with the colors they picked and my logic was fucking flawless!
Sweetest feeling ever :D
I'm sort of color blind so I never check colors and I'm really straight about it with everyone: I don't pick colors.
Its a rant with a happy ending :)6 -
Can anyone recommend good books for coding algorithms?
Any tips and tricks would also be helpful. Thanks.11 -
uhh interesting, bing search engine algorithm open sourced.
Will anybody have a look at it?
https://techcrunch.com/2019/05/...6 -
my Input: want from A -> B
The algorithm of my Public transport App result:
Walk from A to B, then take the tram from B to A. From there you walk to B.
Ooooookay. 2
2 -
An overflow in C, the program was writing 16 Bytes in an array of length 10 due to some mistake.
The problem was this ended up overwriting another place in the memory that was used by another algorithm to perform calculations... So we thought that the algorithm was buggy all along.2 -
For God sake tinder, fix your fucking algorithm.
Why are you showing my beautiful and out of my league girls. I don't want depression everytime I open tinder.
Please show me avarage looking girls.12 -
Developer: I created an algorithm that solves the issue.
Me: (to myself) ...algorithm huh? he must not want to talk about his cover up...2 -
Implementing a neural network trained with a genetic algorithm from scratch, no libs or frameworks. It was intense.4
-
That's an impressive algorithm there, cdkeys. You found nothing in 2ms.
Well done.
Well.
Done.
*slow clap* 2
2 -
Works as backend developer for 2 years now; Almost fails simple university algorithm course.
I'm contemplating my whole life and career choice right about now.2 -
And so I have ranted earlier about how a panelist during my thesis defense told me that my algorithm is not an algorithm because it needs mathematical equations to be called an algorithm. I also told you guys that I facepalmed during the course of the interrogation.
Now I failed my thesis because I facepalmed. I quit school because of that but now I'm a better career person than him. I already started my freelance team and earning more than double his salary and he's still suck at being a low quality professor.7 -
"Change your algorithm"
Answers like this are why Stack Overflow almost becomes worthless when asking questions. I asked for some clarification why my code, which reads some files and outputs another, was hitting System.OutOfMemory exceptions. And that was the response I got.
"Change your algorithm"
How? In what manner should I be seeking to change my algorithm? OBVIOUSLY I SHOULD CHANGE MY ALGORITHM YOU WASTE OF OXYGEN. That was a given by the exception my program threw!
I swear to god, SO has got to be one of the most unwelcoming, condescending sites on the internet.4 -
I finally finished my implementation of a suffix array construction algorithm! 😄
It takes about 30 mins to process 1GB of text and uses all available RAM, but it works! 🎉
Now I can optimize it, the original algorithm is 3x faster. 9
9 -
When you don't want to explain what you've done with application's code base so you play the "algorithm" card.
Boss: tell me about the new release.
Me: updated the search algorithms boss.
Boss: cool. Release!
Me: 😎 -
Caught a nice pair with the algorithm today...
Here's hoping your mornings were all something a little more in-between! 1
1 -
Does anyone know an extension or library that helps determine if a co-worker is into me?
Or how to handle such inputs
I keep getting a fatal error: call to undefined function4 -
Writing some algorithm:
me: *codes for half an hour*
"hmm... isn't working... wait wtf this isn't right..."
me: *codes for an hour again*
"still not working hmmm... wait what no this isn't supposed to work..."
me: *codes for a few hours*
"still not working God damnit.... it's supposed to work now..."
me after another few hours: MOTHERFUCKER CAN YOU START FCKING WORKING FUUUUUUUUUUU1 -
I FUCKING HATE THE INSTAGRAM ALGORITHM FOR SUGGESTED POSTS TO EXPLORE.
You piece of shit; I have NEVER EVER looked at pictures of nature, but I get a shit load of suggested pictures of nature. Can't forget the time they spammed it with memes in a random language I can't read.
OH. AND LETS NOT FORGET YOUR TIMELINE ALGO. IT'S JUST AS SHITTY.
"Hmm. Let him see a picture posted a few minutes ago or one from a week ago? Fuck it, a week ago it is!"7 -
> my CS professor goes to conference
> meets an extremely intelligent scientist
> the said scientist names the algorithm he created by his own name
> my professor asks him why did you name the algorithm by yourself
> the scientist said "angels told me while i was sleeping"3 -
When you spend a couple of hours considering how to change your implementation of Dijkstra's algorithm to be directional only to realise it already was
Fuck!
Self.setIntelligence(-1)3 -
Hey Machine Learners and AI pips, whats the algorithm for detecting if a person is an asshole? :p10
-
It was my thesis defense and I've made a pretty complex algorithm of sorting out data to their respective tables. One panelist told me that it is not an algorithm but just a collection of for loops and if statements. An algorithm should contain mathematical equations he said. I facepalmed during the course of interrogation.
-
So during a test I was to write an algo of binary search tree traversal and I got a zero....Why? Cause I wrote a recursive algorithm and also because I wrote "English" instead of pseudocode, which she thought is called algorithm and on showing her the exact same recursive Algo on various websites and books, she just declared all of them wrong1
-
A funny story I just remember while my code is compiling :
Back in high school, in Math, we were taught how algorithm works, and we made some exercises with practical examples.
I didn't know anything about it back then, so was curious. Was pretty fun, but one day, my teacher said that a IF is a loop. I said "no, this is a test" but she keeps saying that it was a loop, ignoring me (I dunno if she actually heard me) and no one actually noticed it as she repeated it several times (while I was saying that it's not). I just gave up trying to say it's wrong.7 -
Hardest thing about software development to me is estimation of time needed to complete. There should be an algorithm that knows to estimate better than me, shouldn't it? Like google maps navigation knows precisely in advance when I will arrive somewhere taking a car or a train, perhaps they could do my development estimates for me?9
-
Just fixed an error that I seeked for a long time in my optimization algorithm.
Results are much worse now.
Feature it is.1 -
Facebook's algorithm is so bad that I can't believe that. In the past few days I marked ~20 posts from the same person with the same/similar content as "Hide post - see fewer posts like this". And now, not that I see fewer of these posts, they are literally throwing all such posts of that person to my feed. I know that I can unfollow this person but I don't want to. I just want to filter out these specific posts (they are all the same, some link, image of an old black and white photo and some description).5
-
Written coding test, first question :
Form the minimum spanning tree of the given graph using Kruskals algorithm.
Plot twist : No weights given. Assume unweighted graph4 -
One of my favorite things to do in Secondary School was to go around telling people I had written a program that uses the 'Doomsday Algorithm' which sounded really cool and always scared those who didn't understand it.
Truth is, the 'Doomsday Algorithm' is just an Algorithm that used to determine the Day of the Week of a given date.
I wrote this when I was 13/14 years old and I'm still super proud of it today.... well I mean I probably would be if I could read my own code.1 -
I think God is a developer. I have to say a most impressive feat, even for God, is the idiot algorithm. It has persisted through millennia of attempts to remove it, but it just keeps refining itself. While it's incredibly brief, its functions are yet to find an environment in which they cannot operate. It's full adaptable to any task, impressively modular, and self replicating.
No matter how what problem you present it with the idiot algorithm can always find a solution. It never leaves well enough alone. It can even give you an answer before everything is fully processed!4 -
So in my last post I was angry that I didnt know many algorithms or how to make one, so you guys inspired me to learn about them and I found a course I'm gonna take about algorithms and such. I'm incorporating it into my learning schedule so let's hope this leads to me not being stupid.3
-
Anyone played Human Resource Machine yet? It's fun to solve and optimize these algorithm puzzles after a hard work day.
Does anyone know other games like this?5 -
Anyone else suddenly started seeing really old weekly rants? (Specifically for me, wk4, wk11) Has the algorithm changed?4
-
We had to implement our own sorting algorithm for a Linkedlist. My teammate was in charge of implementing this. I took a look at his algorithm when he pushed his changes. He was transforming the Linkedlist into an array, sorting it, then re-creating the linkedlist from the array.
-
Using a brute force dictionary algorithm to retrieve every employees password. Access got blocked for a day because they didn't know what my algorithm did, I deleted the main file moments ago. They only saw the curl scripts.3
-
Looks like I got dislike-banned as well... eventhough I only used it where appropriate.
I understand that our almighty gods dfox and trogus implemented this to fight bots and mischievous downvote cunts, but why not inform the user affected by it?
I fucking hate these silent bans, just like Twatter and YouTwat do it... you feel like you posted something but in reality it disappears and you're not even aware of it.
Man, nowadays a lot of people behave like bots thus I can't blame The Algorithm™...3 -
I've written an insertion sort algorithm in my own esoteric programming language!
I also like to call it 'San Francisco sort'.
Explanation: https://github.com/iamgio/pikt/... 8
8 -
which *git* diff algorithm is your default and why?
## default (myers)
The basic greedy diff algorithm. Currently, this is the default. if you don't know whart you are using, this is it (and it sucks)
## minimal
Spend extra time to make sure the smallest possible diff is produced.
##patience
Use "patience diff" algorithm when generating patches.
## histogram
This algorithm extends the patience algorithm to "support low-occurrence common elements".4 -
I’m really liking the Algorithm Design Manual so far, except for the fact that there’s not a glossary somewhere for “random mathematical symbols you have probably never had to deal with but we will use in psuedocode examples”1
-
We had to finish a student project, our project leader had done some work on the project before and his algorithm to detect an event was complete bullcrap.
I took it in my hands to rewrite the algorithm with the risk that it doesn‘t work and i hadn‘t done any work i could show, which would result in a bad grade.
Luckily my algorithm worked better in orders of magnitude and we managed to deliver on time -
Facebook don’t give a single fuck if you have a million years of experience, you’re going to fucking solve the “algorithm” shit —while they still admit you won’t remember much about it.
The HR guy was damn straight about it: you have to practice a lot.
Bitch, I’m out.10 -
FB post: I have a basic algorithm for detecting faces from webcam > What should I do to show respective names of persons when they show up in Webcam ?Please help !
Me : What's the output of your algorithm
Author : bounding box around the face.
*shoot myself in head* -
Few days back, I developed an app for a client where users can buy textile designs online.
The designs to be uploaded on the server must be square to display correctly on the app. so I had to make them square manually (by either pattern repetition or by filling extra space).
I was like "fuck me!", 800 design image to make it square and each takes like 1 and half minute. I did uploaded 30 to 40 images and then...
I got really frustrated and I was lazy to make more designs square anymore.. So I developed an algorithm that would identify the type of design and then it automatically makes it square by self decision.
so that was my little anti-laziness for my big laziness. -
Developed an app to display examination seats allocated by an algorithm developed by someone else.
The algorithm goes berserk and allocates randomly. Spectacular failure of the system follows.
Everyone blames me for all the trouble.
The algorithm developer smiles in the background. WTH! -
deep thoughts on algorithm design final exam ...
He wanted to make sure we fully understood the idea. :)
No idea about my score -
Maybe the twitter developers getting laid off should join spotify in their quest for a simple shuffle algorithm that they failed to develop or maybe just are not allowed to ship due to corrupt company politics?
As Spotify's algorithm sucks from a listener's perspective (major music industry might like it though), I have to rely 100% on curated playlists, and without shuffle, I have to listen in the exact order that they were made. Why not? We did the same when we put actual records on a record player. Who needs shuffle? Who needs streaming anyway? I'm gonna get a pair of turntables or just listen to MP3 files again!
There is a "new idea" thread in the spotify community forum started in 2020 (following up on an earlier 2012 suggestion), a feature request for the "option to have a true shuffle" that already has 70+ pages, tagged as trending in 2021 with the friendly stalling message:
As this idea has gathered a fair amount of votes, we've discussed it with the relevant team once again. We actually want to take a closer look at what you're experiencing and get some of you in touch with our devs.
Good luck everyone. If I still use Spotify in 2023, I can probably repost the very same status again one year later when the app will still lack a simple shuffle option, no?
https://community.spotify.com/t5/...3 -
I went to a machine learning meet up.. I asked every one over there to explain me K-means algorithm. I got K different answers, then I applied K-means algorithm on K different answers to form K clusters..1
-
The worst realtime coding you'll ever see.."Require efficient.... correction normal shipping/delivery algorithm"
 1
1 -
Teacher explained how genetic algorithm works by using us as a population. Best way to hear about GA for first time.2
-
Captain America: Winter Soldier
Thug officer: "Deploy Algorithm"
Me as random operator: "Like all of them? At once? There are tens of thousands running on this thing" -
Designed a person detection and tracking algorithm based on RCNN and lukas-kanade object tracking algorithm in openCV python.
Need help in cases of occlusion any suggestions? 4
4 -
anybody ever work with ProjectQ or QISKit? I'm doing a project for my algorithms class on Shor's algorithm, and I'm trying to find a guide for an implementation.
-
Trying to make my first genetic algorithm program "to be or not to be" in javascript.... (coming from java and experimenting a bit)
Can't even get past instantiating a function/class Gene.js file into the main.js file. -_-
I got a long way to go...1 -
Update to Doomsday !rant which can be found here: https://devrant.com/rants/1000628
Hey Everyone I'd like to let everyone know that I finally found the original file for my Doomsday Algorithm and thought it would be fun to show you the dirtiest code I've ever written (I was 12 when I wrote it).
here is the github link, https://github.com/LiamHolmesEPD/... , and I'll likely update it will more cleaner languages in the future.2 -
Does anyone know any algorithms for generating crop circles?
I would Google it but "crop circle codes" doesn't exactly give me what i want.9 -
There should be algorithm in DevRant to identify duplicate photos - same memes/photos posted in the last 48hours or less.
To stop seeing the same meme posted by 5 developers on the same day.
Thoughts?17 -
Whenever I had to pronounce Djikstra's Algorithm. My tongue be like - dijjuuksstrra... Fuck you I am commiting suicide between these teeth.8
-
Despair +
Craving sweet stuff +
Quarantine lead to a new interesting search algorithm.
I call it diabetes search.
It find's anything edible with enough sweetness or taste.
Current result is promising.
I found couverture chocolate, cocoa powder, maple syrup, vanilla sugar, crunched haselnuts...
I had some eggs, flour, and milk left.
The kitchen looks like in the movies.... When a martial arts battle took place inside a kitchen.
And I'm slightly comatose.
But: Pancakes with something Nutella like. Just more nutty.
Diabetes search very successful.3 -
That annoying moment when you took an algorithm test, you didn't even pass any test case or you passed just 3 🙂, doing that same algorithm again outside the time scope, then you killed it.
Moral lesson: you have to take your time to think properly even when time is running out. -
I posted a rant... on Quora: Why-do-most-software-developers-suck-at-algorithm-type-interview-questions
https://quora.com/Why-do-most-softw...
Thoughts?9 -
Yesterday my lead architect told me that the bin packing problem is easy and all I have to do is add up the volume of each boxes to calculate the number of containers needed.
Fuck this man.4 -
How to deduce the time complexity of any algorithm faster?
And is there any software that calculates it and suggest another optimal algorithm instead?1 -
I need to compare the JSON results of an API before and after a code change. But it was also moved to another API.
However some fields are auto-generated like timestamp or derived off the url (resource links).
Also if a JSON list is returned it maybe in different order...
Wondering is there a quick way to test text likeness?
I've done it before but just used matching status code and maybe measuring the diff in response size7 -
What is the best string comparison algorithm ?
Example Use case: group messages from your telco into groups of related messages.
I have gone through the various algos and implanted them. I just want your opinion if you have experience on this.15 -
I got one task left... One algorithm to solve... That's the second day I'm on it... And I need to sleep so much... Fix yourself please, let me write random lines and please work...1
-
I am a cs student at first class. Obviously we take an algorithm lesson. However, despite we have learned all things related to OOP , we didn't even learn switch case statement not even bubble sort algorithm or anything related to the algorithms. Because of that in my free time I learn this stuff individually. I know we will learn these things in the second class but it doesn't make sense to program anything without knowing them because you need to use them. You can use standard library but that doesn't mean you don't need to know how that works.
-
#include <stdio.h>
/*
* Windows Update Algorithm
*/
int main()
{
int percent = 1;
while (percent <= 100) {
printf("Working on updates\n");
printf("%i %% complete\n", percent);
printf("Don't turn off your computer\n\n");
if (percent == 30) {
printf("Restarting\n");
break;
}
percent++;
}
return 0;
} -
Damn those homework are pretty over my head and I’m not sure if I’m overthinking it all… Basically the assignment was, that we program a tool that fills as less LEGO base plates with a given number of LEGOs as possible.
For example you’ve got 10x20 base plates, and 30 2x4, 10 6x4, … LEGO blocks and now need to fill those base plates.
I’m now looking into rotatable rectangle bin packing but as said it could easily be that there is an simpler solution to that.
Any suggestions?3 -
Yeah it's just me.
*when your recursion function suddenly worked and you still can't figure out why it worked...*
Guess I need to improve on my algorithms more. Just can't wrap my head around even a quite simple recursion. I'm certain this won't last long. -
The Devrant Algorithm not only reads everything and then sort by sarcasm but sees everything and then sort by sarcasm.
Even puts Google's cloud vision to shame.
-
Apple watch 6
We use advanced algorithm to calculate your blood O2
Boohoo!! It’s a 2 line formula not a advanced algorithm
What a piece of shit
I might buy one though 🤓4 -
Anybody here implemented Dynamic Time Warping (DTW) algorithm? I need to implement it for a school project. Its basically an android application and want to authenticate users using this algorithm.
Will appreciate any help possible.2 -
Do all devs know how to write these Goolgle/Amazonesq algorithms off the top of their heads? ex: build singly linked list from scratch / pre or post binary tree traversals etc..5
-
I have a question
Given an irregular area which is created by combining triangles from Delaunay triangulation, and a box with fixed ratio, how to decide where to put the box so that it has maximum area (box only has fixed ratio no fixed edge length)
I can only think of something maybe just a bit better than brute force but cannot think of anything else10 -
Hi.
I know python and javascript and I'm interested in solving algorithms. But I have a problem, that is I don't the algorithm that I have designed is optimum. I mean it has lower order complexity. I want to know if I want to improve my skills, I should solve programming challenges or, start to read data structures and algorithm design?
I should add my ultimate goal is machine learning.5 -
If you wanted to conquer the world using ninja kittens, which positions of power would you occupy first?
I need advice on programming the mental conditioning algorithm. 1
1 -
Word used by the programmer when he does not want to explain what he did??
:
:
:
:
:
Answer - Algorithm.........7 -
It all started with Yeonmi Parks video. And now YouTube’s algorithm has decided to teach me all about North Korea.3