Join devRant
Do all the things like
++ or -- rants, post your own rants, comment on others' rants and build your customized dev avatar
Sign Up
Pipeless API

From the creators of devRant, Pipeless lets you power real-time personalized recommendations and activity feeds using a simple API
Learn More
Search - ""encryption""
-
What's wrong with WannaCry? All it does is secure you're system by encrypting your files for you.14
-
Fucking awesome. The 'encryption backdoor law' in Australia went through!
Now, whenever served with such warrants, companies which are active in Australia will have to pay hefty fines if they don't give encrypted messages to law enforcement in readable form. No matter whether this means just decrypting it with the keys they have or pushing backdoors/inject code into the messaging apps/services in order to extract the contents.
Now let's see how much the big companies really care about their users! (I'd expect them to pull out of Australia but the chance that this'll happen is as tiny as about nothing)34 -
Another attempt at trying to get support for weakening encryption recently.
An FBI spokesperson said something like 'we can put people on the moon, why can't we just create law enforcement-accessible encryption? i just don't buy it."
Fuck off and die.28 -
When I was in my second semester of college I was tasked with creating a file encrypt/decrypt program. Take in normal textfiles and spit out a new random text and symbols file. I worked on it for two weeks and read up on all different encryption types and stuff. I was so excited when it was done. After it was done compiling I tried it out on its own source code. Encrypto.c and named the output file Encrypto.c 😰 The next thing I did was google " best version control and how to use it."17
-
Holy fuck, muscle memory just saved my ass.
At a train station wanting to do some work on my mini laptop which has disk encryption (LUKS I think). Realised that I forgot the password partly 😬
Few tries.... incorrect. FUCK.
*hey, let's try to let my hands do the work based on muscle memory!*
*starts typing the password (its insanely long) and presses enter*
*succesfully unlocked, booting...*
😅25 -
Had three servers running in prod. For extra security all of them were encrypted (hdd encryption) just in case.
"mate, servers need a quick reboot, that alright?"
Me: yeah sure!
"oh hey they're encrypted, what's the password?"
Uhm.....
😐
😓
😨
😵😨😮😧😫
😲😶😭
Yeah, i also forgot to turn on the backup process...17 -
Me: "I'm a programmer"
Others: talks about linux
Others: search algorithms!
Others: service infrastructure
Others: memory optimization
Others: encryption
Me: "I'm a front end web developer"
Others: complex services
Others: strong user form validation
Others: lazy loading
Others: SEO
Me: "fucking, I make shit look pretty alright"11 -
Working with a radio chip we selected because it had built-in encryption. Cannot make the encryption work, thus in contact with the manufacturer:
"- I cannot make the encryption work, it's like the chip doesn't want to take a key.
- which key do you use?
- does it matter?
- well yes, you can't just use any key!
- why not?
- you need to get an approved key from us.
- why is that?
- so that your competitors can't read your data!
- ...
- ...
- so the way to get working keys is to get them from you?
- of course!
- keys are 256 bits. Can we potentially use all of them?
- OF COURSE NOT!
- how many can we get from you?
- one! We reserve it from your company.
- are you telling me that all units within a company will need to have the exact same encryption key?
- yes!
- so anyone with our product could eavesdrop another same product?
- well yes, but it's all within your own products.
- ...
- ...
- that's not how encryption is supposed to work.
- but it's safe, your competitors cannot eavesdrop!
- I'm out of here."
(We finally found a satisfactory work-around, but i am still pissed at them)9 -
We've password protected a file and forgot the password we need it cracking asap.
Sorry we can't crack passwords on files.
If we don't get access to the file it'll cost the company up to 250k.
Well you should've thought about that before encrypting the fucking file with 256 bit encryption.8 -
"could you please just use the standard messaging/social networking thingies? That way it'll be way easier to communicate!!"
Oh I don't mind using standard tools/services which everyone uses at all.
Just a few requirement: they don't save information that doesn't need to be saved, leave the users in control of their data (through end to end encryption for example) and aren't integrated in mass surveillance networks.
Aaaaaand all the standard options which everyone uses are gone 😩30 -
Manager: "The password must be encrypted to store it inside the database."
Me: "Great! No problem."
Manager: "Then it must have a copy of the unencrypted password to send it by email."
😐7 -
A US senator or judge or whatever his title is said today that he wants companies/governments to build a 'responsible encryption' system.
Preferably that would exist out of a big ass database which stores the private keys of citizens so in case a person loses their private key or the government needs access to encrypted content, that is possible.
NOO, WHAT COULD FUCKING POSSIBLY GO WRONG!?!?!
Seriously those kind of people should not be allowed to have the kind of positions they have.
This shit makes me so angry.45 -
So the new mass surveillance law will be going into effect from the 1st of January.
Of course, since I'm very keen on my security/privacy, I'm going to implement some precautions.
- A few vps's connecting to tor, i2p and VPN provider so that I can always use a secure connection.
- Setup anti tracker/ads/etc etc shit on the VPS's. Probably through DnsMasq and the hosts file.
- Use Tor browser by default. I've tried this for a while now and damn, the tor network has become way faster than only even a year ago! Some pages literally only take a few seconds to load.
- Wipe my laptop, encrypt the harddrive and at least put QubesOS on it together with probably a few other systems.
- Ungoogle my new phone, use it with VPN by default.
- Get rid of all non encrypted communication services. I think that only leaves me with a few account removals because I haven't chatted unencrypted for nearly a fucking year now.
If anyone has any more ideas, please share!42 -
Got some good news today, Australia's PM (Malcolm Turnbull) doesn't want a backdoor in encryption! All he just wants is "support" from companies to "access" their users encrypted data.
See the difference?
I don't 😒14 -
Project Manager: You used a hash/salt to encrypt the password in our customer database?
Me: Yes.
Project Manager: That's mean we will not be able to see the password?
Me: That's the whole point. Why would you want to see what password customer is choosing?
Project Manager: Change it. Use random encryption method.8 -
Citizens are advised not to use encryption as decrypting data takes too much time and is costly.
Please spread awareness and save money.
Thank you for Cooperating, have a nice day :)6 -
I've always wanted to experiment with encryption but never do. This weekend, I'm fucking doing it. Even if I'm just flipping a few bits around, I'm fucking gonna flip those bits like they've never been flipped before and they are gonna FUCKING LIKE IT.4
-
Dear Prof,
One does not simply encrypt the exam tips and give it to the students in a computer security introductory module.
Sincerely,
Disgruntled Undergraduate4 -
> be me
> install linux on encrypted drive
> takes 8 hours to fill the drive with fake data so theres no chance of data leakage
> save encryption password to phone
> phone doesnt actually save password
> realize you dont have access to pc anymore
> cry
> reinstall linux7 -
Senior C++ developer:
"Writing a custom encryption algorithm from scratch for our communications platform? Every developer knows that is an absolute no go, cryptography should be left to cryptography veterans!"
Same guy, year later:
"Blockchains? Hold my espresso, I can totally write a whitepaper on cryptography, write some shitty code with nice branding, and get millions from an ICO"1 -
"I should really make better offsite backups"
"Right, this service doesn't do client side encryption"
"Oh this one doesn't have a Linux client"
"OK this one only sets up a single directory you can dump shit into"
"Wtf this one charges more than a high class escort girl"
Whatever... I'm sure my house won't burn down.15 -
Had to give a 15 min presentation on web development. I somehow turned it into me giving a 1 hour lecture on ssl and end to end encryption to a bunch of accounting students 😅3
-
Me: *Has 3 difficult exams to study for and hours of work*
Also me: I should try my hand at encryption in Python.7 -
Gotta say, I find it awesome that I can connect with some devRanters through encrypted channels.
It's awesome to talk to devRanters with the same mindset through channels that offer a very high level of security/privacy.
Thanks!33 -
So... Facebook just stated that they plan on loosening up the End-to-end encryption in WhatsApp to analyze the messages and show user-specific advertisements.
Time to uninstall WhatsApp I guess!21 -
One of my favourite, encryption puzzles is this:
ITuyVT93oUZtLKWyVT5iqPO3nTS0VUEbMKxtp2IyoD==
Answer is plain text string in english. Good luck, post solution in the comments!19 -
Downloaded Kubuntu because i couldn't seen to be able to boot from a freshly created KDE Neon bootable usb.
Installed it onto my netbook (Lenovo Thinkpad X121E) and it worked great!
But just the fact that somehow the installer froze when trying to setup hdd encryption kept bugging me.
Took a random flash drive which was laying around and put it in to see what would happen. KDE Neon booted just like this and everything worked very well with hdd encryption.
I now have a very secure netbook 😊15 -
Setting up my new second hand thinkpad with Linux Mint KDE.
I just chose for harddisk encryption.
My password is so freaking long and complicated and I didn't write it down so let's start learning this fucker out of my head 😅11 -
Soooo my little encryption tool makes progress. <3
After a short break from development, we had our first successful loaded container yesterday!
This means:
- Protocoll is working
- We can create containers and store/copress files in it
- we're awesome
- I love it
- you are awesome, too!
(Loaded containers will be inaccessible for movement to different directories while our tool is open) 49
49 -
Boy, sure wish I knew about this before putting all of my passwords into lastpass. This looks way more secure. Handwriting in English is pretty much as good as encryption.
 9
9 -
On the presentation for my database project my team and I showed a NodeJS + Mongo + VueJS project with cloud storage capability, nothing fancy but did everything from scratch (from token auth and system encryption to the frontend CSS and the database) the teacher made some questions and meh'd at it.
Behold team two's project, WordPress with a standard template and phpMyAdmin, teacher loves it because "it's so beautiful"
Guess who just failed that class?
God I love college, it's the best time investment I've ever done and it'll surely pay out. 11
11 -
You've heard of ROT13, now get ready for ROT26. This new and improved algorithm is TWICE as secure as ROT13 due to letters being shifted /twice/ as much.
There's even an API for this encryption service, for all ease of programming integration needs!
http://api.rot26.org/encrypt/... to encrypt}2 -
Just saw this in the code I'm reviewing:
function encryptOTP(otp){
var enc = MD5(otp);
return enc;
}13 -
I found this in the code of a non-adult video portal...
Why would they need AES encryption for a pornhub grabber? 10
10 -
PM ordered me to not use encryption for customer authentication links because we want to be able so send same link if the user loose it. "we have to prioritize usability over security". At least I can tell future hackers it's not my fault..
 10
10 -
"Why are there so many programming languages? Why don't you guys all just program in binary?" A friend of mine some of you may remember, the same one who decided to select system32 when trying out some encryption software from the internet, and who put a shutdown script in the start up programs3
-
I love how the Keybase Linux client installs itself straight into /keybase. Unix directory structure guidelines? Oh no, those don't apply to us. And after uninstalling the application they don't even remove the directory. Leaving dirt and not even having the courtesy to clean it up. Their engineers sure are one of a kind.
Also, remember that EFAIL case? I received an email from them at the time, stating some stuff that was about as consistent as their respect for Unix directory structure guidelines. Overtyping straight from said email here:
[…] and our filesystem all do not use PGP.
> whatever that means.
The only time you'll ever use PGP encryption in Keybase is when you're sitting there thinking "Oh, I really want to use legacy PGP encryption."
> Legacy encryption.. yeah right. Just as legacy as Vim is, isn't it?
You have PGP as part of your cryptographic identity.
> OH REALLY?! NO SHIT!!! I ACTIVELY USED 3 OS'S AND FAILED ON 2 BECAUSE OF YOUR SHITTY CLIENT, JUST TO UPLOAD MY FUCKING PUBLIC KEY!!!
You'll want to remove your PGP key from your Keybase identity.
> Hmm, yeah you might want to do so. Not because EFAIL or anything, just because Keybase clearly is a total failure on all levels.
Written quickly,
the Keybase team
> Well that's fucking clear. Could've taken some time to think before hitting "Send" though.
Don't get me wrong, I love the initiatives like this with all my heart, and greatly encourage secure messaging that leverages PGP. But when the implementation sucks this much, I start to ask myself questions about whether I should really trust this thing with my private conversations. Luckily I refrained from uploading my private key to their servers, otherwise I would've been really fucked. -
It would seem that Australia just criminalized privacy. The world needs to watch, so this shit isn't repeated elsewhere.2
-
Australia passes anti-encryption law
More like "Have a backdoor" and please tell us about that. So that we can spy on people keeping on the stake of individual and national security
https://thehackernews.com/2018/12/...14 -
Friend,
I signed a petition on Action Network urging Congress to reject the dangerous EARN IT Act and protect our online free speech.
The Eliminating Abusive and Rampant Neglect of Interactive Technologies Act of 2019 — also known as the EARN IT Act — gives Attorney General Willliam Barr the power to demand that tech companies kill important encryption programs. That puts us all at risk of government censorship, cybersecurity breaches, and human rights abuses.
Don’t let Congress chip away at your essential freedoms online. Sign our petition now to tell your lawmakers to reject the dangerous EARN IT Act: https://actionnetwork.org/petitions...
Thanks!5 -
Discussed my Internet privacy campaign - Google-free, encryption where possible, didn't even mention VPNs - with 2 people and they've both asked, "why, what are you hiding?"15
-
"And there you have it folks. Open-source "many eyes have looked at it for years so it must be secure" crypto code."
🤘
https://threadreaderapp.com/thread/...21 -
Clicking "share" on directory in Windows Explorer, digging through config panel, fidgeting with network discovery options, toggling password protection, digging through account management, jumping over a chair 3 times to channel my inner Bill Gates, checking directory permissions, sacrificing 7 virgin unicorns, go into lusrmgr.msc, curse various gods, install CIFS1.0 protocol, reboot computer, disable encryption, checking registry, trying to summon Steve Ballmer using the blood of a bald goat and sweat-scented candles... 5 hours.
Install Ubuntu on spare SSD, mount Windows NTFS drive, start SMB daemon and set up samba users... 15 minutes.10 -
Today I was continuing my Ruby script for file encryption.
I added some features like Picture Encryption and Bookmarks.
Then I tried to start it to make sure it doesn't fuck up.
ruby PGCrypt.rb
No changes reflected.
w0t.jpg
Start debugging
Browses SO and DDG like a maniac
Reinstalls Ruby
Guess what happened.
My shell was in the wrong folder and I ran the old testing script.
GRAAAAAHHHH3 -
Continuation of https://devrant.com/rants/642962/...
You are the decryption key to my encryption,
No one can access my heart except you.
You are the loop in my life,
I always keep coming back to you.
You are my nodemon,
You are always watching over me.
You are the / to everything I do,
Am nothing without you and I will always preserve you.
You are my increment operator,
You add value to my life.
To be continued 😉3 -
After working for this company for only a couple years, I was tasked with designing and implementing the entire system for credit card encryption and storage and token management. I got it done, got it working, spent all day Sunday updating our system and updating the encryption on our existing data, then released it.
It wasn't long into Monday before we started getting calls from our clients not being able to void or credit payments once they had processed. Looking through the logs, I found the problem was tokens were getting crossed between companies, resulting in the wrong companies getting the wrong tokens. I was terrified. Fortunately I had including safe guards tying each token to a specific company, so they were not able to process the wrong cards. We fixed it that night.1 -
Should I actually look into getting a dev job..?
*I have a high school diploma (graduated three years early)
*College dropout (3-4 months, Computer Science - Personal Reasons)
*No prior work experience.
*Good textural communication skills, poor verbal communication skills.
*Currentally unemployed. (NEET :P)
*I have extensive personal experience with Java, and Python. Some Lua. Knowledge of data generation, parsing, Linux, Windows, Terminal(cmd & bash), & Encryption(Ciphers).
*Math, but very little algebra/geometry (though, could easily improve these).
*Work best under preasure.
Remote only.
Think anyone would hire me..?13 -
Not dev related but still a rant:
My company decided that all the network traffic should go throu a virus scanner. But they don't know what the fuck they are doing, so now EVERY valid SSL cert gets rejected by our browsers because the virus-scanner breaks the SSL encryption.
Anyone open for a pishing attack?8 -
Hello guys and girls!
My company tasked me to do something insane.
Little background info: I'm a trainee, in my first year (of three, even though I will shorten my apprenticeship to two years). I told my trainer that I like encryption in a somewhat private talk.
Now to the insane part. I got tasked to develop a whole security concept ~2 weeks ago to protect our products against industrial espionage. I feel in no way competent enough to achieve this especially because my concepts so far have been dismissed with a 'naaaah. Can't we just do X for now and add the other stuff later?' or 'we can't do that.'
I seriously don't want my name under a concept we would use world wide on our customers pcs which I know has serious flaws.
What should I do? What would you do?22 -
Was just thinking of building a command line tool's to ease development of some of my games assets (Just packing them all together) and seeing as I want to use gamemaker studio 2 thought that my obsession with JSON would be perfect for use with it's ds_map functions so lets start understanding the backend of these functions to tie them with my CL tool...
*See's ds_map_secure_save*
Oh this might be helpful, easily save a data structure with decent encryption...
*Looks at saved output and starts noticing some patterns*
Hmm, this looks kinda familiar... Hmmm using UTF-8, always ends with =, seems to always have 8 random numbers at the start.. almost like padding... Wait... this is just base64!
Now yoyogames, I understand encryption can be hard but calling base64 'secure' is like me flopping my knob on the table and calling it a subtle flirt...6 -
Embedding private encryption key in production javascript file and fetching third party session token client side.4
-
For anyone looking for a quick video conferencing solution, take a look at Jitsi Meet!
Although I'm still unsure about the levels of encryption, it works veeery well!8 -
"Ultron brings to you the best in security and encryption, directly taken from IE 5.5."
*screams internally*2 -
A Bank Account Number is like a public encryption key. Any random person needs it to send me money. Why does it seem like banks treat it as a secret or even use it to confirm my identity? It's literally printed in plain text on every check.2
-
"The laws of mathematics are very commendable but the only law that applies in Australia is the law of Australia", said Australian Prime Minister Malcolm Turnbull today.
Now what the fuck is this? Why would you propose a blanket ban on end-to-end encryption or force companies to build "secure" backdoors? At this rate retarded politicians would make our lives too difficult.
https://eff.org/deeplinks/2017/...3 -
One day, I spoke to my team which yubi or nitro key to get.
Senior (s) : but what do you need it for?
Me (m) : for encryption. And securing our password managers. Stuff, I guess.
S : encryption is not gonna be a thing. It hasn't and it won't.
M : *leaves*
I've been so baffled I couldn't cope with the situation.
A few weeks later I left the company. There were too many of such people and those products.3 -
Guys Quick Question 2 :
Should I Dance like no one is watching
and Encrypt like everyone is ?
Or do the opposite ?3 -
Today I continued working on my File Encryption Frontend, nothing functional, yet!
The icons are selfmade, I think at least the folder icon is pretty.
Our programm will have something like a Zip-Explorer feeling too it, but our aim is still encrypting files to the unbreakable point. 27
27 -
Fully Homomorphic Encryption (computing addition and multiplication of numbers WITHOUT decrypting) is fucking cool. That is all.
https://bit-ml.github.io/blog/post/...8 -
Let's teach the class about security. OK *spends 1.5 hr teaching about encryption and practices* OK now students make a login page and just store the passwords in a JavaScript array....... *Facepalm*7
-
Registered an account with a local pizza business and rated them 5* on Yell moments before checking my email and finding they had emailed me my unencrypted password, GREAT NOW I WON'T BE ABLE TO EAT3
-
Google researchers breaks SHA-1. Next 90 days they will release the code that was used to break this encryption.
Are we fucked?5 -
Today I started coding an encryption algorithm I'm calling Aepples (apples)!! I'll let all of you know how it goes!6
-
When I just started making things in PHP, I always taught that md5 encryption was the best thing out there.. Once I learned that it was the most easy way to break I changed to SHA1. What were I thinking? I now use a custom generated SALT for each user and encrypt with SHA512, should be safe for a while, right?
 7
7 -
Computer engineering : Insanity!!!
Today a friend of mine was assigned to make a Client-Server Encryption using Sockets. The guy did a great job applying BlowFish algorithm, but the teacher was disappointed because she couldnt map letters to the encrypted text and she declared the program to be wrong!!!2 -
Ever encrypt files on a USB drive before?
Ever do that then forget the password you used for the encryption?
Yep... 😭11 -
Apple drops plan for E2E encrypted backups after FBI pressure: https://reuters.com/article/...
And one step at a time, the world goes deeper and deeper into shit...8 -
I made a real working example of elliptic curve encryption without code examples in javascript. I really felt like a badass.2
-
I have a mate who downloaded encryption software that he somehow managed to use to encrypt almost every system file in windows, now the entire thing is fucked, like how can anyone be that stupid? Like before he even did that he tried encrypting the .exe of the encryption software and guess how that went6
-
In my ongoing quest to un-Google my life, I turned off the Whatsapp chat back up, which uses Google Drive. There's a message in that setting which says, "Media and messages you back up are not protected by Whatsapp end-to-end encryption while in Google drive".
Damn.
All my Whatsapp chats for years have been on Google servers in plaintext.
I assumed it uploaded one massive encrypted archive.13 -
Boss activates encryption on dashboard
we installed the software
2 machines get locked out coz drive got encrypted with bitlocker
No one received the 48 bit key from bitlocker
I loose all my work coz the only way to use my laptop was to format the drive
Me as the technical guy and knowing how encryption works i just formatted the drive
Boss blames me for the cluster fuck8 -
I just saw the equalizer 2 at the cinema and about half way through there is a phone with "military grade encryption" on it. We see the phone screen showing the encryption and what is it? Freaking JQuery!3
-
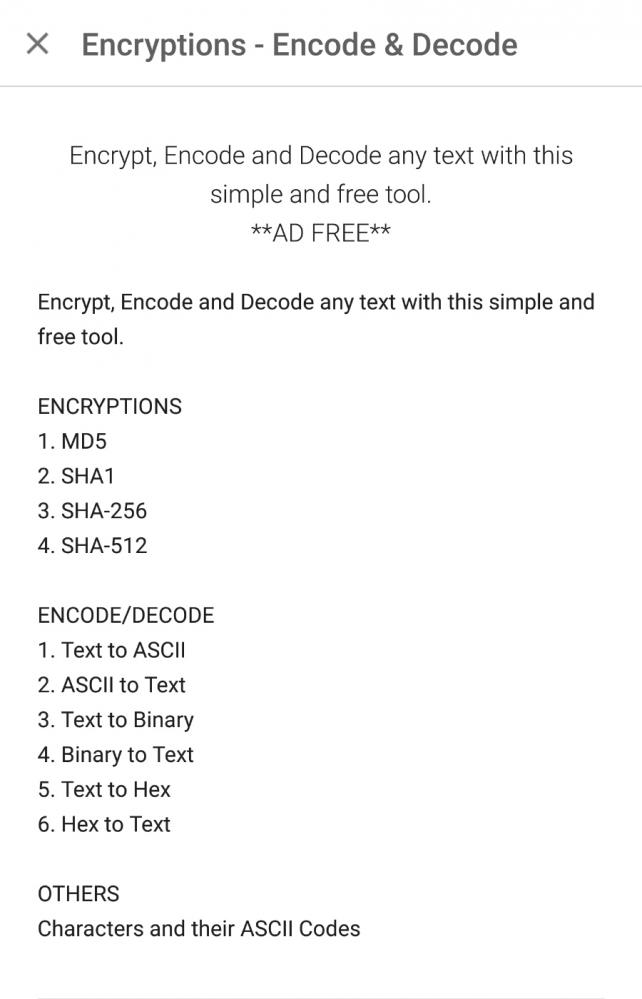
/* made a encryption app */
Developers and Designers and folks try it.. It's called Crypten
https://play.google.com/store/apps/...17 -
I saw this image on IBM's blog. The author was explaining how blockchain could be used to implement self sovereign identities. But, isn't the last step wrong? In order to decrypt Alice's message, Bob should use his private key instead of Alice's public key, right? Of course, while encryption Alice has to use Bob's public key.
 3
3 -
FUCK OPENSSL. I LOVE IT AND HATE IT SO FUCKING MUCH. WORK FASTER AND BE LESS CONFUSING SO I CAN BRAG ABOUT MY PRETTY ENCRYPTION CODE SOONER. FUCK20
-
A couple of days ago, an individual attempted to convince me that the National Security Agency is capable of cracking Rijndael encryption; as a response, I informed the individual of the infeasible nature of the factoring of extremely large semiprimes; however, my attempts were futile, as the individual believes that NSA possesses sufficient power to crack this encryption without intercepting the transmission of the corresponding private key.
The Dunning-Kruger effect is real; although this individual tends to be logically-minded, there does exist an exception to this good behaviour.
"It is easier to square a circle than get 'round a mathematician."1 -
Currently working with @Kreischo and another good friend to create a secured, encoded container to store files in it.
I am currently working on the frontend of things, thinking it's quite beautiful.. (Done with Electron)
Your opinion?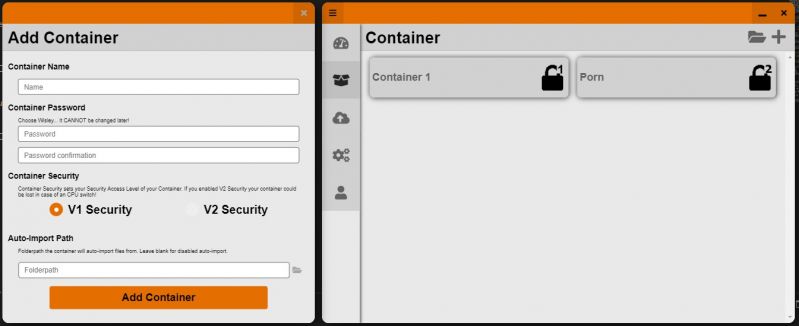 25
25 -
IPAY88 is the worst payment integration. They parse html data and encoded it into xml for return the data, it is not even singlet or server to server communication , tey called it the ADVANCED BACKEND SYSTEM (My arse!) For security, they ENCODE THE STRING into BASE64 and called it ENCRYPTION ! WHAT THE FUCK?
Encoding is not encryption! I qas expecting they used diffie hellman or AES or RSA etc. THEY TOLD BE ENCODING IS ENCRYPTION? WHAT THE FUCK?1 -
Many people / engineers around me talk about trendy stuff like Cybersecurity or AI and show off what great encryption and neuronal networks they 'have built' ( I would rather say 'using').
I kinda get the feeling of 'Everbody talks about it - no one really knows what's goin' on inside (especially those guys who hate math and even algorithms).'
Am I just stupid or does somebody else here feel the same way? I mean people have been doing serious research about this stuff for years. And currently many kids are coming up with it as if it is easy stuff like the bubble sort.4 -
TIL if you know the password for a WIFi SSID, you can replicate it with your hardware. All devices that have credentials for that SSID will connect to yours if your signal is stronger. The encryption just needs to be the same (wpa2/wep) The underlying UUID doesn’t matter.
Not bad for a quick and dirty man-in-the-middle attack. The WiFi spec needs a bit more work.
TLS all the things!4 -
When you spend 6 hours figuring out how to best encrypt/decrypt your unimportant website cookies just because you don't want people to see how bad you are at naming stuff :x
-
Me: "I'll use my old laptop as a server to access via SSH to do my Docker Tests. I don't wanna use Keyboard and Screen. So, I'll set up Debian Server"
Also me: "Oh, full disk encryption with a preboot Login required. That's such a GOOD idea"
Introducing: Stupid me 🤗 -
Someone fucking teach these so called devs the difference between HASHING and ENCRYPTION :/ They are not fucking same.4
-
Encryption, Data, Servers, Protection, Certificate
oOOO WEE, I use big ear old words so I must be a hacker.2 -
API Documentation: All API request should be made over https connections.
Me: Ok, (sees url bar), SECURE, good!
(sees curl code)
curl -X GET 'http://shittyapi.com/api/v2/users'
Me: (gasps) huh?
(heads to http://shittyapi.com/api/v2)
Me: Ok, (sees address bar) NOT SECURE
.
.
.
.
.
(long silence)5 -
One of our customers wants our mobile app to log out the user after 15 minutes of inactivity because of SeCuRiTy…
Why? The phones protect the apps with their hardware encryption from any malicious access.
And we are not dealing with super sensitive data here like some banking app or so.
Why do some people want to have bad UX for no reason?12 -
https://eff.org/deeplinks/2021/...
For fuck’s sake. Here we go again. The old, “...but think of the children...” argument.9 -
Tinfoil hat time!
So, for this scenario we assume a world war has is in full swing, and all communications are either completely out or extremely monitored.
Additionally, no servers can be trusted and no ISPs can be trusted. Even when downloading software you cannot know if the software you got is tampered or not.
You have to send a message to a recipient you cannot physically contact, and you have to make sure him and only him get the message, otherwise nukes are deployed and we all die. The message has to arrive within 3 months or else it's too late.
Is it possible? If yes, how?17 -
Problem:
some folks left the angular codebase full of ridicolous console.logs, client was upset as he noticed it during UAT
Solution:
1. add extra script in main template page
window.console.log = function(){};
2. translate it into JSFuck
3. if they ask, pretend it's a super-secret encryption algorithm to improve security5 -
It's been so long without an update on my little encryption project so...
We accomplished the following:
- big fixes and bug fixes
- drag and drop in files and folders
- screwed over many times
... And finally ...
- THEME SUPPORT!! WUHUUU
(Look attached screenshot)
Currently I just implemented two themes but a theme explorer will follow.
I'll create 3 themes for this project, normal, dark and Alice themed.
Stay tuned ✌️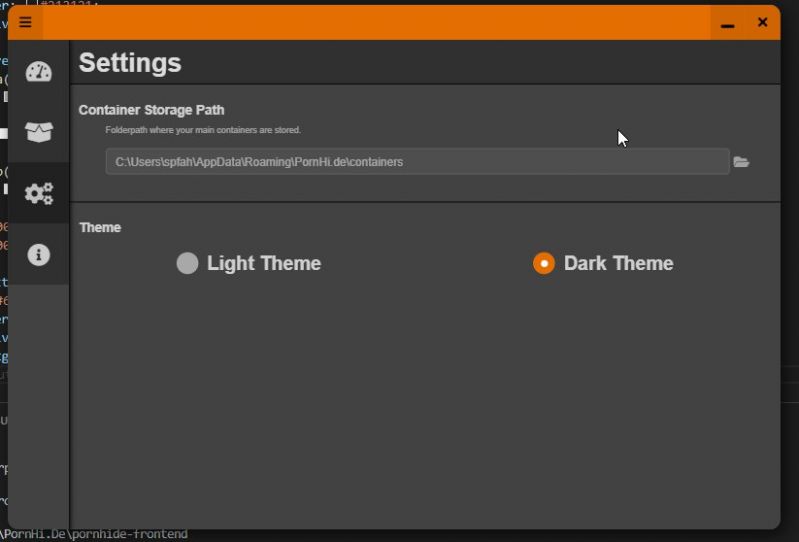 5
5 -
2nd year programming professionally I designed, coded, and released a PCI compliant credit card encryption system, including updating all 7 million records (at the time) in our existing database to utilize the new system. By some miracle, it worked with only one small hiccup (see previous rant).
-
I have a presentation which takes 10 min and must be about anything relative to computer .
Since the other students are very stupid , I might not choose a very advanced topic ( after thinking about encryption i realized this)
So i need help!
What is your recommandation for the subject?17 -
CS Teacher today:
"Transport Layer provides Security and Encryption to the communication" (TCP/IP stack)
me: WTF? Encryption is provided on the *top* of the transport layer (aka Application) ( and below [Network Layer] there is IPsec)
Teacher: no, it's wrong.
me: so Wikipedia it's wrong, RFC 5246 is wrong, and you have right?
Teacher: Yes.
me: Ok. (aka fuck you!)2 -
In an encryption-module, I had a bug, that caused my PC to crash, every time I tried to encrypt something.
Turns out, the loop, that appends
0-Bytes to the string, to make it Block-Cipher compatible,
Had an logical-bug in its exit-condition, that caused it to run infinitely and allocate an infinite amount of memory. -
An identity platform where you can find each other, get the other's public key and preferred contact method. And the entire key exchange and choice of contact method are negotiated automatically. No vendor lock in, encryption happens on your own device. Effortlessly and securely communicating, no searching for skype name, email, phone number, setting up shit. It would just work.7
-
Just finished a large write up on a security flaw I found and disclosed in an exam spyware vendor's "zero knowledge encryption" - derived keys that were generated from incrementing integers, discussion on obfuscation and more.
It was a hell of a time writing this up; not sure if linking my personal blog here would be bad practice, but here it is: https://proctor.ninja/wave-rake-pro...
It's been something else, but hopefully I can keep fighting against tech like this on school campuses.4 -
We can hide messages in images via steganography (or ZIP sewing), we can hide messages in sound via either sound-based transmission (like Morse) or waveform-based transmission (think oscilloscope art videos), we can transmit it in videos in like 300 different fucking combined forms...
Encryption isn't the ONLY way, yo. Social engineering and being a cheeky shithead can get it done too.2 -
What's wrong with the idea of having a huge computational network like in Watch Dogs to bruteforce encryption ?
I mean suppose having 500 or more million cores , how long does it actually take to bruteforce a 256 bit key ?11 -
Decrypt api responses in an iOS app which my “senior” dev thinks it is more secure to encrypt responses in stead of setting up a proper SSL cert (they use plain http to save money 🙄)
They disable the encryption since it does not function as we wanted and set up SSL instead🙄4 -
Remember kids when setting up data security, don't be an Equifax.
Since they can't honestly answer yes to the data at rest question, it probably means the resting data was not encrypted.
How did these guys get put in charge? This is a basic data security standard.
https://m.hardocp.com/news/2017/...1 -
This is my #wk110 about a project from when I was a real n00b. It can also be read as a rant about myself.
So I decided to code my own terminal based password manager. Because, you know, whom can you trust the most; yourself or some random password manager from the internet?
Obviously, encryption plays a major role when storing such sensitive information. So n00b me decided to go with Base64.
Base64.
I developed a password manager that stores your passwords in Base64 format.
What must I have thought?!
Perhaps the gibberish looks of Base64 encoded data made me think that this actually is encryption.
After having realized my stupidity, I quickly replaced Base64 with AES and more recently I completely rewrote the whole project which is now also available on gitlab: https://gitlab.com/bitteruhe/sesame
This act of stupidity still embarrasses me every time whenever I think about it, though. -
!rant
University assignment asks to create some encryption harder to break than Caesar Cypher. So I decided to go online and look for some tips on making a somewhat decent algorithm.
Universal answer: don't do it
😶
Well then, night off I guess 😎2 -
Firefox will be enabling dns over https by default in the near future for all its users
https://forbes.com/sites/...3 -
If you could choose one, what should happen in 2020 :
1. Apple let developer build iOS apps on non Apple machines
2. NPM/Maven/... run 10x faster
3. Javascript dies and gets replaced by a better language
4. Governments stop trying to ruin encryption
5. Facebook splits
6. Quantum computers are being sold for consumer use
7. We have our first high - level generic AI working17 -
techie 1 : hey, can you give me access to X?
techie 2 : the credentials should be in the password manager repository
t1 : oh, but I don't have access to the password manager
t2 : I see your key A1B2C3D4 listed in the recipients of the file
t1 : but I lost that key :(
t2 : okay, give me your new key then.
t1 : I have my personal key uploaded to my server
t1 : can you try fetching it?
t1 : it should work with web key directory ( WKD )
t2 : okay
t2 : no record according to https://keyserver.ubuntu.com
t1 : the keyserver is personal-domain.com
t1 : try this `gpg --no-default-keyring --keyring /tmp/gpg-$$ --auto-key-locate clear,wkd --locate-keys username@personal-domain.com`
t2 : that didn't work. apparently some problem with my dirmgr `Looking for drmgr ...` and it quit
t1 : do you have `dirmngr` installed?
t2 : I have it installed `dirmngr is already the newest version (2.2.27-2)`
t2 : `gpg: waiting for the dirmngr to come up ... (5)` . this is the problem. I guess
t1 : maybe your gpg agent is stuck between states.
t1 : I don't recall the command to restart the GPG agent, but restarting the agent should probably fix it.
t1 : `gpg-connect-agent reloadagent /bye`
source : https://superuser.com/a/1183544
t1 : *uploads ASCII-armored key file*
t1 : but please don't use this permanently; this is a temporary key
t2 : ok
t2 : *uploads signed password file*
t1 : thanks
t2 : cool
*5 minutes later*
t1 : hey, I have forgotten the password to the key I sent you :(
t2 : okay
...
t2 : fall back to SSH public key encryption?
t1 : is that even possible?
t2 : Stack Overflow says its possible
t1 : * does a web search too *
t1 : source?
t2 : https://superuser.com/questions/...
t2 : lets try it out
t1 : okay
t2 : is this your key? *sends link to gitlab.com/username.keys*
t1 : yes, please use the ED25519 key.
t1 : the second one is my old 4096-bit RSA key...
t1 : which I lost
...
t1 : wait, you can't use the ED25519 key
t2 : why not?
t1 : apparently, ED25519 key is not supported
t1 : I was trying out the steps from the answer and I hit this error :
`do_convert_to_pkcs8: unsupported key type ED25519`
t2 : :facepalm: now what
t1 : :shrug:
...
t1 : *uploads ASCII-armored key file*
t1 : I'm sure of the password for this key
t1 : I use it everyday
t2 : *uploads signed password file*
*1 minute later*
t1 : finally... I have decrypted the file and gotten the password.
t1 : now attempting to login
t1 : I'm in!
...
t2 : I think this should be in an XKCD joke
t2 : Two tech guys sharing password.
t1 : I know a better place for it - devRant.com
t1 : if you haven't been there before; don't go there now.
t1 : go on a Friday evening; by the time you get out of it, it'll be Monday.
t1 : and you'll thank me for a _weekend well spent_
t2 : hehe.. okay.8 -
Who would be interested in reviewing an old peice of Python code I wrote..? It's a few years old, and it uses basic procedual generation to cypher text (entry, or ASCII files) using a hashed password. It's a command line tool.
I used to brag about how "secure" it was, and now I'm curious if it is secure or not.
I plan on picking it back up and open-sourcing it, but I want to know what problems might be wrong with it now.9 -
I avoid websites that advertise with 256bit encryption and military grade stuff. This makes them kind of sketchy when they advertise this encryption that hopefully every normal website has today.1
-
Mozilla really knows how to nudge one to not use email encryption by default.
Since Thunderbird has native support for OpenPGP encryption, i can only chose to encrypt all or no messages by default. There is no opportunistic mode and there are no per-reciepient encryption preferences. The Enigmail addon had both.
So i obviously have gone for encrypt-by-default.
But since then, whenever i want to send a message to the majority of my contacts, i have to manually disable the encryption or get annoyed by the no-key-found dialog.
I thought, i would get the muscle memory to just disable encryption for recipients for wich i don't expect to have a key.
But they also made the GUI so i have to open a dropdown and then click on the right item to do that. All the items basically look the same, as there is no color coding or specific icon for them. The item labels are also too long for unconscious pattern recognition.
So i didn't got that muscle memory.
I now have turned off encryption by default and will probably forget to enable it for some emails wich i actually could send encrypted...4 -
Me: Ok, we'll implement that message tech. But since the clients are servers in that architecture and can't speak IPv6 we've to use a dedicated VPN so the endpoint is able to connect to the servers (clients). Since we have limited network resources we should use VPN cert-encryption and send the actual data plain to save at least some overhead.
Boss: Ok! Let's do it!
Next day.
Boss: Hey! I talked to a guy from that message tech. Their encryption is certified. We should use that instead and get rid of the VPN to save the overhead!
Me: *unable to say a word*
What in "VPN in that architecture is mandatory" is unclear?
Well, I assume we'll kill the architecture then... Fun Time! -
In the time I was attempting to learn C++ I was attempting to program an application that encrypted a file. Sounds cool but at the time I had no idea on how encryption worked and it didn’t go well. And didn’t work
-
A hidden page that you enter a user name and it displays the encrypted and unencrypted versions of their password... It was quickly deleted after I stumbled across it. I assume it was to test a homemade encryption algorithm that wasn't worth much anyway, passwords shouldn't be reversible
-
I think the fact that even Apple can't unlock your phone if you forget your passcode proves that they use very naive encryption method.
Suppose my data is "Hey This is Some Data" and Passcode is 1234, I could just Jumble this data using that passcode and It will be difficult to decrypt without Passcode. And If data is huge, it will be fairly impossible to do so. But that doesn't make it a good encryption method.
Such encryption, though safe is not practical, Imagine if there was no "Forget Password" Option on any account, I usually forgot my password very often when I was a child.
Apple has been doing such things for years, Using Bad things as a selling point. Apple users are dumb anyways because they don't want to control their phone.
Reset Password is a weak point which might be exploited but in such cases, usability is more important than security. Any service which doesn't allow resetting Password is a shitty service and I would never use such a service, They are too naive.678 -
A senior engineer, while talking about adding encryption to the application, mentioned using SHA256 for that purpose.13
-
I need to encrypt some large files at rest and then decrypt them immediately prior to processing.
App and files are on a Linux system (CentOS). App is in C. Machine is controlled by a third party.
What encryption libraries would you recommend? And, is there any clever way of managing the decryption key beyond compiling it in the code and doing some basic obfuscation?
Are they fancy obfuscation libraries out there, for example?
And, the reason I'm not going to SO (well, one reason) is that I don't want to have 50 answers that tell me that's it's impossible to 100% protect data on a machine you don't control. This I understand---just looking for "best effort" solution.7 -
In these dark times, it's inspiring to see that a country as insignificant as Australia can demonstrate to us how things can always get worse.
By passing a law mandating that encryption must be broken, in secret (like the US's National Security Letters), at the demand of the Government, the two biggest parties have colluded to destroy Australia's tech sector.
This is the same government that has been whining endlessly about using Huawei LTE equipment in Australian infrastructure "because it might be secretly compromised". Now the same is true of Australian equipment, by law.
My favourite part of all this is how there will be firmware updates for devices sold in Australia, in order to comply with the new law. How well do you think those backdoors will be secured? How thoroughly do you expect them to be tested, given Australia's population of only 25 million?
How can any Australian company expect customers to trust them now?3 -
They tell me to only review security in the security reviews I'm doing (and if I bring to attention that they're implementing a weak encryption so even though they're not using it at the moment it might cause issues so be careful with that they say to only review security 😵) and then I see this mssql in a where:
AND ISNULL(field, 0) IS NULL
And I think wtf, should I report that? I did and it's a bug and they're thanking me now....
God dammit it's hard to "review security" here...3 -
SecureMessengerAndroid
A chat app that uses AES encryption and doesn't require any personal information like phone number or email address.13 -
I just saw this on a website. Good to know that they use some kind of jQuery draggable plugin for encryption.
 2
2 -
We needed to generate secret tokens for the app, me being as curious as I am, asked what encryption algorithm they were using, little did I know the the answer would be a random string generator.
Every day further from god.9 -
Coolest bug is less of a bug and more of a feature. I've been working on a medical app and I used an open source backend which had almost everything I needed. To be hipaa compliant you have to encrypt all sensitive data - full db encryption was not something this backend was capable of.
So my solution was to encrypt the data on the client side and create a secondary server - that can only be accessed on my app server - to store and retrieve the keys.
If anyone's thinking of working on a HIPAA project - you're welcome -
Not a rant, just the completion of a very demanding and interesting task for this week.
Wrote a whole data scheme for this enterprise app my company is developing. Very proud of it, since it has a very restricted size, multiple layers of encryption and data verification, several user types with different requirements, and it all has to be rock solid in an offline environment.
The punchile is...I enjoyed writing the documentation for the whole package more than I should, I guess...spent the whole day being very thorough and documenting every member, function, constructor and exception.
Feelin fabulous.
-
My worst coding mistake
In my last project for the distributed application programming, I was working on encryption for messaging between two users, the mistake was after decrypting the message you should trim it, and I was trimming before which made the message corrupt, this mistake costed me 2 weeks of delay since I couldn't find the problem, the code was like this
Message=decrypt(message.trim());
Where it was supposed to be
Message=decrypt(message).trim(); -
1) Learning to make Android games with Godot3. Really awesome engine to do this. I was impressed when I found out it can use adb to deploy to my phone directly.
2) A sort of a modular multiplatform backup service with optional on the fly encryption/decryption and available for all devices -
So, my network security faculty thinks s/mime is secure multipurpose internet message encryption. And ssh is secure socket header.
Time to leave the class. 😭1 -
The fuck is this shit?
The upper link is the actual link to the exherbo-project, a new source-based linux-distro.
The lower link forwards to a broken site, largely copying text from the original, while adding certain paragraphs about easy encryption and data-wiping to hide incriminating material.
Did someone from Gentoo went mad, because someone's developing an actual alternative to their shitty distro and package manager or what is happening here? 5
5 -
If I made an app where you keep password hints so you can remember the password yourself, is it fair to say the encryption is your memory?1
-
# NEED SUGGESTIONS
I am working on a secure end to end encrypted note taking web application. I am the sole developer and working on weekends and will make it open source.
The contents you save will be end to end encrypted, and server won't save the key, so even I can't read or NSA or CIA.
So I wanted to know if the idea is good? There are lot of traditional note sharing apps like Google Keep and Evernote. But they store your stuff in plaintext. So as a user will u switch to this secure solution?14 -
If you're having a bad day, think about the fact that BuzzFeed reporters have PGP keys for confidential tips4
-
Still using a database from 90' - Enea Polyhedra:
- no decent visual sql client
- utterly limited scripting language
- weird communications protocol
- no redundancy beyond master-replica
- no encryption of communication protocols
- etc. -
At the time, I'm working on a simple RAT, for leaning purpose, written I'm Go.
Now simple command-execution work's and I want to implement an encrypted connection between the client and the C&C-Server.
I know Go has some kind of TLS in its standard library, but is it really usable, or would it be easier to just implement my own simple encryption-module with some RSA and AES? -
I'm going through a KhanAcademy course learning about cryptography. I learn better by doing, so I wrote a script. It shifts bytes up depending on a random int produced by a high entropy pseudo random number generator using a sha256 hash as the seed. I'm trying to find information on the flaws with this method, that lead us to create DES, and then AES.
-
When you keep telling your boss that you remade one of their sites so that it has BCrypt(currently use SHA-512),CSRF checks, stricter Auth/Cookie encryption and that we should swap it and all he says we will get to it.
wot n tarnation-_-1 -
Trainee accidentally said md5 is an encryption... Gave him the "functional specification of OpenPGP on ISO Smartcards". He learns OpenPGP now, before he reads that I hope.
-
I want to use the DevRant community for a Unit test.
Inspired by Memento, I will make a tattoo ... but ... I want it encrypted. I know nothing about encryption.
I want to make some encrypted messages and I want you guys to decrypt them.
If I'm gonna put something on my wrist for life, it should be secure11 -
I am trying to "invent" secure client-side authentication where all data are stored in browser encrypted and only accessible with the correct password. My question is, what is your opinion about my idea. If you think it is not secure or there is possible backdoor, let me know.
// INPUT:
- test string (hidden, random, random length)
- password
- password again
// THEN:
- hash test string with sha-512
- encrypt test string with password
- save hash of test string
// AUTH:
- decrypt test string
- hash decrypted string with sha-512
- compare hashes
- create password hash sha-512 (and delete password from memory, so you cannot get it somehow - possible hole here because hash is reversible with brute force)
// DATA PROCESSING
- encrypt/decrypt with password hash as secret (AES-256)
Thanks!
EDIT: Maybe some salt for test string would be nice8 -
In university, I got really into cryptography. I wrote software that was testing the entropy of lots and lots of HTTPS encrypted packets, for sites that also supported HTTP. Meant that I had a pretty good idea what the plaintext was, and the quality of the encryption algorithms used. In the end, I got into lots of trouble with my university because apparently what I was doing could be deemed 'dangerous'! Never felt more like a hacker in my life.
-
How do you approach generating "random" unique numbers/strings ? Exactly, when you have to be sure the generated stuff is unique overtime? Eg. as few collisions in future as possible.
Now I don't mean UUIDs but when there is a functionality that needs some length defined, symbol specific and definitely unique data, every time it does it's stuff.
TLDR STORY: Generating 8 digits long numbers so they are (deterministically - wink wink) unique is hard but Format Preserving Encryption saves the day. (for me)
FULL STORY:
I had to deal with both strings and codes today.
One was to generate shortlink word for url, luckily found a library that does exactly this. (Hashids)
BUT generating 8 digits long, somewhat random number was harder then I thought, found out on SO something like "sha256(seed) => bytes => ascii/numbers mangling" but that had a lot of collisions because of how the hash got mangled to actually output numbers and also to fit the length.
After some hours I stumbled upon Format Preserving encryption (pyffx) and man it did what I wanted and it had max 2 collisions in 100k values. Still the solution with this feels hacky af. (encrypting straddled unix timestamp with lots of decimals)6 -
I'd like to locally encrypt files before syncing it with the cloud; what's the "best" software available for this?
I'm currently switching to STACK as my cloud service (it's a file hosting service for Dutch people that offers 1TB of free storage).
But I don't feel fully comfortable with them having access to all my personal data.
So I came to the conclusion that it would be best to locally encrypt files before syncing it with STACK. I DuckDuckGo'd but there seems to be a lot of software available for this so I'm not sure which one to use.
Which one could you recommend me? I'd prefer a free software but I'm okay with paying as long as it isn't too expensive.7 -
Isn’t it weird how a paper notebook is more private than anything you type on a computer, despite the complete lack of encryption? You don’t control what happens to your CPU under the hood, and you never had that control.13
-
Had to extend the platform of a customer. For one part of my task (generating an encrypted string) there already was a class with encryption and decryption methods. This class is used in a gazillion places all over the code, so I thought it might be a good idea to re-use already existing stuff... Until I saw that the encryption method using basic Java methods (all fine with that) wrapped in a try-catch block, 'cause the Java methods may throw, returning err.getMessage() in the catch block...
Yeah...sure...makes sense... Instead of throwing an error or returning null just remove the possibility to handle the error.
So I decided to basically copy the methods and return null so I can work with that.
Created a merge request and was told by another dev of that company to remove my own impelemtation of the encryption method and use the already existing. Arguing that I won't have a possibility to prevent my code, that returns an URI containing the encrypted string, from generating something like "http://..../Encryption failed because of null" without success.
So I had to use the already existing crappy code...5 -
Have you read about this yet ?
https://itnews.com.au/news/...
I don't live in a FVEY country , but it still terrifies me.6 -
Latest promoted thread on XDA to make the list:
"how to disable forced encryption".
This is from a place that tries to be innovative. I'm half expecting a thread get promoted with the title "how to give everyone your passwords/identity/credit cards".
https://forum.xda-developers.com/ma... 3
3 -
I had to choose a subject for a math project. So I selected encryption (elliptic curve). I decided to make an interactive demo website. First time working with node, websockets, large numbers and latex. Most fun project I ever did. I am still proud on the result and how fast I did it (~3 weeks)
-
Recently we started to encrypt all our PHP code.
To hide the code that we use to unauthorized people.
A new intern deleted ALL the encrypted and uncrypted files from all the servers (Also our backup server) saying
"I thought it was a Cryptolocker".
Now I can fucking start to find it all back and maybe even recreate our system and fucking crypt everything again.6 -
I sincerely hope the tragedy in Manchester won't be used as a pretext by our technically inept politicians to push through crackdowns on encryption and further surveillance.2
-
Why is Docker + SSL certificates so confusing? Or do I just have bad resources?
I just want to know how to compose an Docker, Nginx setup with encryption.11 -
Tomorrow I'll write an exam in programming. I code since I was 11 years old and as soon as I got to that stupid programming class in school I felt bored. My teacher is an former encryption expert and thinks I'm too good for that stupid school. Well at least I am ready for the exam... That shit is so boring in class 😂2
-
I just stumbled across this post about signed-only mails: https://k9mail.github.io/2016/11/... (TL;DR: Signed-only mails are not worth it).
So far, I've been signing all my mails (as not that many people I know use OpenPGP, so I'm far from encrypting everything). I've got a few replies like “I can't open that attachment” and “What is that .asc file?” but I have seen it as doing my part in motivating more people to use encrypted mail with little effort.
I DDW for a bit but couldn't find any other comments on the usefulness of signed-only mail per se. Consequently, I'd like to ask you: How do you use OpenPGP?6 -
Trying to get HIPPA compliance, and wet have to put full disk encryption and anti virus software on all our servers...
All of our servers are on aws ec2 / eks. The instances we do control aren't big enough for anti virus to be running...
God help me now5 -
Slight rant.
Guys which fucken anti-virus do you recommend for free, which doesn't throw around with ads like crazy?😵
I know this might kinda start a war and some of you want me to use linux.
Sadly, win10 is a must.😛
Girlfriend managed to catch some encryption fuck-up..
I made her use sophos home before, but it seems like sophos isn't self-acting enough..
I hope you have some ideas..25 -
So when it comes to password encryption in php, I've learned to use password_hash($password, PASSWORD_BCRYPT); // Blowfish
Anybody else use this? What do you php lovers like to use?3 -
So, in my second semester of CS I had a class about OS and the way they work. The professor made us do presentations every two weeks (we were basically giving the class...).
For full points we had to have the presentation, an example (video or pictures), and an activity.
My team was one of the last presentations of the first round (iirc there were 5 rounds). I was in charge of the activity, so I decided to create a program to make it fun (and leaned a new language in the way). Thanks to this the professor gave us extra credit because we were the first team that ever did that.
My classmates decided that it was a good idea to follow my idea and a couple of teams started to code their activities too. At the end of the semester almost every team had a program as their activity...
But the professor didn't gave them extra credit because it wasn't a novelty anymore. :D
In another round, my team got as a topic encryption. By the time I was already a Linux user and I knew a thing or two about encryption, so I decided to do the example in real time showing how to encrypt and decrypt using command line. Once again we received extra credit because of it. :D
At the end of the semester the professor offered me a job as a developer, but I couldn't take it since I moved out of the country the next month :( -
I started an e2e encrypted Dropbox clone, meaning file names and contents get encrypted client side prior to uploading. It also has a fairly advanced system for sharing links to files etc. But I got stuck at PDF previews which can't be generated on the server cause the file can't be decrypted there and I never finished it.2
-
In continuation with https://devrant.com/rants/1911995/...
Here it's worse than Australia
https://m.economictimes.com/news/... -
I know I'm probably the 1083742698574'th person to complain about this but what the hell? I'm building a Win 11 vm (to run a back-end service) and it _requires_ tpm, secureboot and drive encryption. Why?
Honestly, I don't like anything that going to make it harder for me to recover from a data emergency. Say what you have to about data security and whatnot, but I can't tell you how many grateful people have thanked me for taking the data off a drive from their dead pc. I saved their data from death - would not have been possible with drive encryption.
If I want my data safe, I'll just keep my computer with me.3 -
Rewrite my entire side-project from scratch using Kotlin and AndroidX. While doing so I want to learn about state of the art encryption and key derivation functions (especially Argon2).
Oh yeah, and finish my PhD... -
I just got the dna test.
I am the father. My daughter is now 3 weeks old.
No surprise there. I expected to be the father. I had no reason to distrust my wife. But, after all, I know my IT security.
The relationship I had with my daughter was transitive. I trusted my wife and my wife had my daughter, ergo I had a connection with my daughter. Or in clearer terms: from a => b and b => c follows a => c.
The problem I was thinking about: What if I will stop trusting my wife in the future. At some point in the future... Something might happen. And I would stand there and wonder how long it went on. Maybe a month? Or before my daughter's birth? Maybe more than 9 month before my daughter. Would I be able to hide it from my daughter or would she notice...
If anything ever happens now, I know it has nothing to do with my daughter...
That's the same reason why we use end2end encryption. Sure, we have to trust that the application provided is not manipulated. But we only have to trust today. If it lands on their severs, we have to trust until the end of eternity.
I don't need any trust right now. And I am fucking happy about it.3 -
That short moment of fear when Windows restarts during boot without appearant reason and you think the last Windows update messed with the hard drive encryption1
-
Oh dear Amber Rudd has encyrption in her sights again. And still doesn't seem to understand what it is.
-
I have being working on a project with server side using PHP. My dev environment is XAMPP on Debian. PHP is 7.3.10. So.... no MCrypt. Documents said that a new kid called Sodium is in town but php said he doesn’t know this guy...
I have no encryption library...14 -
Is there any note taking, or password vault app which can work offline, cross platform, sync data with online storage services, like Dropbox, Google drive etc., and do encryption?6
-
I want to switch over to Linux again, Windows just annoys me a lot lately. Thing is, I don't know what distro I wanna use yet.
I want one that is:
0. Security focused, so encryption, VPN and so on. (I know software could do the job, but would be nice if it comes with the OS)
1. Not hard to configure, but I should be able to configure it more when I want to.
2. Not too ulgy looking.
I have a little bit of experience with Linux, but I'm not even close a professional.
Looking forward to your suggestions!11 -
That dude that doesn't really understand the concept of cariables and hardcodes a caesar encryption/decryption.
I have no words for this. 1000+ lines of code -
What are the thoughts of privacy conscious people about quantum computers? As far as I understand current TLS version encryption method is vulnerable to quantum computers, thus if your ISP or other agencies store all your traffic data right now, they'll be able to decrypt it after gaining access to quantum computers.
One way to secure your privacy would be to use your own VPN that uses encryption method that is quantum-resistant, but again the VPN would be using TLS to connect to the Internet.6 -
When you wake up on a sat, log in to your emails to share with your bosses a new hacking framework just out that can decode encrypted strings, and no one replies because it's the weekend
-
When someone tells you there app is 100% secure just because they use E2E encryption but using the Authorization header is too complex..2
-
What makes WhatsApp not privacy friendly? They don't state that they share contact information and only statistical stuff (App last opened, etc.) Which is marketing, but not really bad. And they use end to end encryption.
By the way, this here is there Whitepaper on end to end encryption. But haven't read through it yet. https://whatsapp.com/security/...15 -
What local database you guys use??
I am searching for local db that also provide encryption for windows desktop application.
* found sqlite but most add-on that provide encryption are not free *11 -
What do you windows users out there use for full disk encryption? Anyone using anything else than bitlocker?
Asking for a friend or some silly excuse like that.10 -
I tried ProtonMail after a user here got creeped out after watching snowden. And I like it. Sick of gmails intrusion to what I buy, where I go and yes the need of phone number. Why tho?
I think we as a developer community should educate the need of such encrypted non-intrusive services not necessarily proton to common people. Privacy is a right.
*doesnt apply to insta models though, lulz* -
FUCK YOU hash_hmac and your stupid fucking $raw_output = false default...UGHHHHHHHHHHHHHHHH
http://php.net/manual/en/...4 -
Interesting past of American + Germany worldwide espionage through a company in Switzerland.
https://washingtonpost.com/graphics... -
Guys, I need some advice. I finally got a customer, and I'm trying to convince them to let me add SSL encryption, but they don't want the extra costs involved, that hosting providers tend to charge.
I don't really know of many hosting providers, as I run my own server, so I was wondering if people could recommend anyone that can let me run a nodejs backend, using mongodb?8 -
I've implemented Chat function for my app. Since I'm a security noob what is the preferred way of encrypting the messages End-to-end maybe?
I'm definitely not leaving them as plain text :)4 -
Nothing like changing state contract ws-security polices to make your eyes bleed and your brain melt with symmetric encryption binding in WCF services
-
is it possible to find a password/note manager that is also:
has a user and permission manager;
free/open source;
local (lan only, no cloud);
web based (local web server);
encrypted;
secure;
????8 -
Try to enter a new password limited to 16character ... Why ... Password is use to be secure with encryption. Someone can explain!2
-
1, someone breaks public/private key encryption
2, watch the world burn
3, people will understand that this rant is just a joke1 -
Why you should use sketchware and not use it at the same time regarding: encryption
sketchware the app is known to build apps by dragging elements to the screen then coding them with blocks or even write your code with the built in ide but there is one thing every developer fears. ah yes. the reverse engineers (or modders)
random guy [rates: X]: sketchware encryption is trash! are you serious?! string fog?! class rename?! i decrypted this whole app with the software i made >:D
sketchware dev wrote back to random guy: string fog isn't working because you decrypted sir! there is nothing we can do sir but email to our email and we will get back to you in a few and fix the problem
i have to say this is why i stick to android studio too many skids decrypt the C++ files or the mod menu just to edit stuff :) i also build some games im learning android studio game development but at the time lets have fun and mod other peoples games1 -
This shithead continuously wasted 2 lectures of CNS(Cryptography and Network Security) on debating: in a link to link encrytion if encryption and decryption takes place on every node, what if attacker attacks the node while the data is decrypted.
Though I couldn't care less about the lecture but this guy brings the same issue in every lecture
Do anyone have any idea about the link to link encryption?
I know already it encrypts the whole packet with header and on each hop the data is decrypted and the destination ip address is fetched and encrypted again, but i don't know if it's possible to perform an attack on the decrypted data.3 -
Fuck. I don't think any conventional encryption stands a chance against this monster...
https://nextbigfuture.com/2019/09/...3 -
Anybody that uses GPG for email encryption might want to read this:
https://lists.gnupg.org/pipermail/...
This sheds a bit more light on what's actually going on.
TLDR:
It's not really GPG that's affected but the E-mail client plugins.3 -
Let's see:
No archival of data on a database server with over 5000 high profile customers using no encryption whatsoever with telnet open on LAN, every user on the same account in the office using the companies name as the password... But hey there are security cameras! -
I need a new professional email address and i was thinking of going with an encrypted email service, do you guys have any recommendations on what to use?
My only requirement is that it needs to work with desktop email clients like Thunderbird, i am too lazy to use a web browser :)11 -
!rant
Wanakiwi can be used to possibly decrypt wanna cry encrypted files and computers. https://github.com/gentilkiwi/... -
So I apparently forgot to encrypt some parameters when sending error reports from our app to the server.
Which means the server tried to decrypt them but couldn´t and just threw an error...
No error logs for the app this week I guess. Yay!
I need "git reset --hard head~1" for my brain this weekend, to get rid of this week... -
Okay I'm probably going to get flak for this but...
WhatsApp chats are apparently e2e secure. Except when you back them up, right? Why not, when you create a backup (iCloud, google drive, whatever), have the app generate a password protected key pair and use that to encrypt/decrypt the backup?
When restoring the backup, use the password you set for the key et voila! While at rest, that backup is still encrypted.
Or have I missed something completely?2 -
https://accessurl.com
[...] All session data is encrypted using (salted) AES-256, the same encryption algorithm used by the U.S. Government to protect TOP SECRET data. [...]
FUCK!! But perfect for Netflix!! ;)4 -
So, are we gonna ignore the fact that Pied Piper could have been successful, had they used if else on the encryption to block the AI from tampering with an encrypted data?3
-
Which encryption library do you people use with c/c++? I'm trying to use openssl but well there is more documentation about how to replace my own heart in the dark than on that. Also most of the structs have missing declarations hell yeah its nice to have a EVP_PKEY but what's that? Oh I know it's a evp_pkey_t and what's that? Nothing apparently. Comments? You kidding??? A proper library doesn't have them...3
-
If anyone in this wonderful community wants to help with my encryption project contact me VIDNIC@protonmail.com
Thank You18 -
Ah the permanent role joblisting converted into a year contract proposal ... They must have used the wrong encryption type :/
-
So when I started at my current company, I was the second developer in the company. My job is to handle the embedded development side of our product. The existing code base? Made in fucking China. All of the comments were in Chinese too. They had implemented Huffman compression incorrectly and AES CBC encryption incorrectly as well. It was seriously some of the worst code I've ever seen. I remember one gem I found:
Int header = *(*int) "MGIK";
😫1 -
Been wondering about something and can't figure out if I am a retard or a genius 😂.
If MD5 is so outdated and should not be used to store password hashes (let's say for whatever reason you cannot effectively switch to another algorithm) wouldn't it just be easier and more secure to just re-encrypt the hash again, so just MD5 the MD5 hash... in theory, wouldn't that make the hash virtually uncrackable because instead of trying to brute force actual real words, you now have a hash of essentially random characters which have no relation to the others, and even then, suppose you manage to crack the hash, you will get another hash to crack before getting to the password?5 -
Does anyone want to help me with the project I am working on It is to improve the disappointment of the encryption program1
-
As V1.0 I found Allo quite fine. Google assistant is so cool answering a lot of questions that you would rather switch to chrome and browse Google search results etc.. About encryption issues, I'm not a CIA agent and I have no problem if they use my data to improve the app utility. That's what AI and machine learning are all about. And please, don't tell me that Facebook or other services don't store your conversations. What is missing is SMS/MMS support and a Desktop client, that's it.1
-
I have been working on idea similar to pastebin for mobile platform currently available on Android. The main concept is the easy share of Note in any language that is encrypted and the notes get deleted as soon as other party reads it. Plus you can encrypt it further by adding your own password and then share that password with others. This is useful when we are sharing our card details and other secret stuff with friends or family. The problem is that if you use mail or messaging stuff it gets stored in other party device and it can be exploited in future in case of theft or mobile loss. Here is my application for Android.
Please comment your reviews.,comments and suggestions here.
If you want to fork the code of both server and client comment that also.
https://play.google.com/store/apps/...7 -
story time
today I learned how to license a git hub project have I finally made it to intermediate developer?
------if Ur interested in a little something I did just for fun--------
https://github.com/vindicit/...12 -
"We'll publish critical vulnerabilities in PGP/GPG and S/MIME email encryption on 2018-05-15 07:00 UTC. They might reveal the plaintext of encrypted emails, including encrypted emails sent in the past. #efail 1/4"
https://twitter.com/seecurity/...
Let's see how this unfolds. While there is chaos I trink some tea and laugh, because I never send critical information over e-mail. 🧐🍵4 -
Is there an encryption/decryption algorithm that's guaranteed to have an output of less than 100 chars? Say to encrypt messages less than 50 chars in length4
-
Welp, how much longer till someone building some magic to crack any modern encryption in blink of an eye.
...
tl;dr Google claimed it has managed to cut calculation time to 200 seconds from what it says would take a traditional computer 10,000 years to complete.
https://nydailynews.com/news/...18 -
hey I just finished on taking criticism sorry for not fixing the one security issue tho but evreything else has been fully implemented
https://github.com/vindicit/...4 -
How should I start off with end to end encrypted applications for the web.
Anybody has any known examples or starter repos I could start off with :)
Preferably nodejs10 -
Only last month I removed a file called 'statuspage.aspx', this file has been sat there for years on our customer sites.
The file did one simple query on the database to ensure connectivity, this query dumped the admin username and password to the page, no encryption.
Needless to say we rolled out ab emergency update... Not quite sure how that made it through QA! -
me Looks at beta 1.0 of encoding/encryption program
program Looks back
me :>
announcement bet1.0 is here -
These past few days were the first days in ages that I actually had time to work on a project. It is also the first time in ages that I pulled all nighters to code. Being reminded of the feeling of putting on some headphones and hacking away on this project was the best feeling I've ever had in so damn long. God I love programming.
If you wanted to know what the project is:
We got an end of year project in comp sci at school and we got a lot of freedom for what we were required to do so I got the idea of creating bank management software cause it seemed pretty simple. But then I started the project and realized how much more I could do with this. So I've been working on an entire bank management program including account creation, database creation, file encryption, payment options, and credit/debit card attaching. It is currently text based but I'd like to create a gui in the time we have left to finish. I'd also like to incorporate more features that come to mind. -
Anyone else get the mind of a angsty college student without coffee?
I just had trouble describing asynchronous encryption -
One of our partners sent me a Key Injection Tool to inject encryption keys into a PINPAD with. Looks like they were short on developers and had to hire Python typists who have made a mess of a simple AES encryption/decryption. When do these companies learn that writing a security related software in Python is not really secure? I had to read the rubbish in Python and read it from scratch in C++ to get it to work, and am now contemplating whether to provide that company with my version of their Key Injection Tool or not...1
-
I need some help here. I'm working on a my app, and one of the components is a chat. Now, for video and audio calls I am using WebRTC, but what about texts? Is there a way to use WebRTC there, preferably with E2E encryption?1
-
Can anyone explain indepth details about ransomware like it is just a normal encryption one or it is affecting the windows kernel ?
-
Have been searching on this topic alot lately, but I cant find any good solution, in my opinion.
I have a system where I want to encrypt some data in the database, so it isn't in plain text, but how would you do it properly?
It has to be decrypted to view the data in the system, but how to manage it?
How can I store the keys in the right way? In my current trial, I have a encryption key and an iv, but wouldn't it be wrong to store the encryption key in the config file?
Can't really see how to grasp this the right way and in the same way have it as secure as possible.
Is it just stupid in general? -
Hey, anyone have experience with email with encryption?
I need to setup TLS for emails for all devices on premises. The printer and other devices does not support TLS.
I'm thinking i could use local exchange server that forwards to our office 365, as we use outlook for the domain. But i would rather use some linux solution.
We have multiple ip's we might send from.1 -
I'm kinda looking for a new phone, should be super cheap (so a used one would do), I wanna modify it to be secure (proper encryption, VPN, etc.), very good battery time and not very big (more like 4"). I have been looking at the Lenovo P2 a lot, but I'm afraid my current phone will die before I have enough money for that one (I'm a broke trainee yay).
So what do y'all have or can recommend?3 -
Reversed network protocol didn't work, the sent messages weren't acknowledged or denied... basically no response from the server at all.
Turned out, after weeks of cluelessness, that I forgot to append PKCS#7 padding... -
Vivaldi browser is shit.
Simple isntructions on how to make most shitty browser ever:
1. Force users to use "really-fucking-long" password that will not match to any of their existing ones.
2. Invent some useless stupid "encryption password" (why does any normal browser work fine without that shit) and most ridiculous - automatically set it to be the same as the main password.
3. Of course you forget the pass you set because you dont remember what symbol you added 5 times in the end of your normal pass to fit their stupid rules.
4. You have to reset it
5. "Encryption password" does not reset with it, so you still dont remember it
6. Sync is not working!
7. If you think this is shitty enought, you are not right - they went futher. To reset that fucking "encryption password" you have to... ERASE ALL YOUR CLOUD DATA.
Fucking retarded piece of shit - never, never trust those morons who made this shit browser to sync any of your sensitive information.17 -
I am so done for today. I was trying to get this encryption work in Rust, but no fucking way. If I encrypt data in PHP, it is just impossible to decrypt them in Rust. If I encrypt something in Rust, I can decrypt it anywhere, but not the other way around.
I checked the data hundred times and they are exactly the same in both programs. Also OpenSSL library in Rust is so helpful, that it won't show any error details except that there is an error.
Fuck my life!4 -
Last employer -- a major health care insurance carrier -- had over a million current and former subscribers data in SQL database with no encryption on SSN or other personally identifiable information. I reported this as an issue, and was told that since they had intrusion detection, etc. they don't need to encrypt the data. Guess they have never heard of zero day vulnerabilities or disgruntled employees?
-
I'm planning to do an app with some personal data for a small community (Verein). I want to save the data somehow encrypted so not all people can just access them. There will be just 4 persons who need to access this data. I'm think about PGP/GPG, with encrypting the data for these 4 people with their different keys, but I am not sure about that. So every person would have its own keypair. This is just the first idea. So if you have any hints/links on some ideas/blog posts how to do this or do it another way, I'd be glad about a comment. Thanks ;)
Tech stack: I'm planning to create a Webapp, using Python and Flask... -
Crypto Scam Recovery Services || Bitcoin Recovery Expert || by Captain WebGenesis
The Captain WebGenesis Recovery Specialists is a trusted and reliable solution for individuals seeking to recover lost or inaccessible cryptocurrency assets. With his expertise in cutting-edge encryption technology, intuitive user interface, prompt customer service and strong security measures, Captain WebGenesis Recovery Specialists guarantees a safe and easy recovery process for each and every one of his clients
Contact Captain WebGenesis today! He’ll help you recover your stolen Crypto funds.
Contact; Call or Text - +1 501,436,9362 -
Captain WebGenesis Crypto Asset Recovery Company.
Captain WebGenesis is a trusted and reliable solution for individuals seeking to recover lost or inaccessible cryptocurrency assets. With his expertise in cutting-edge encryption technology, intuitive user interface, prompt customer service and strong security measures, Captain WebGenesis Recovery Specialists guarantees a safe and easy recovery process for each and every one of his clients
Contact Captain WebGenesis today! He’ll help you recover your stolen Crypto funds -
I'm implementing 2FA supporting TOTP, SMS and backup codes. To store the backup codes I've issued in my app's database, what should I do re hashing/encryption?5
-
Basic advantages of using PayPal accounts-
PayPal shields users with top-notch security protocols. Two-factor authentication and data encryption secure accounts. Transactions are monitored round-the-clock against fraud. So, we suggest you to buy verified PayPal accounts at usasmmzillow
Using PayPal means swift and simple online payments. Users enjoy seamless checkout experiences. Send and receive money effortlessly across diverse platforms.1