Join devRant
Do all the things like
++ or -- rants, post your own rants, comment on others' rants and build your customized dev avatar
Sign Up
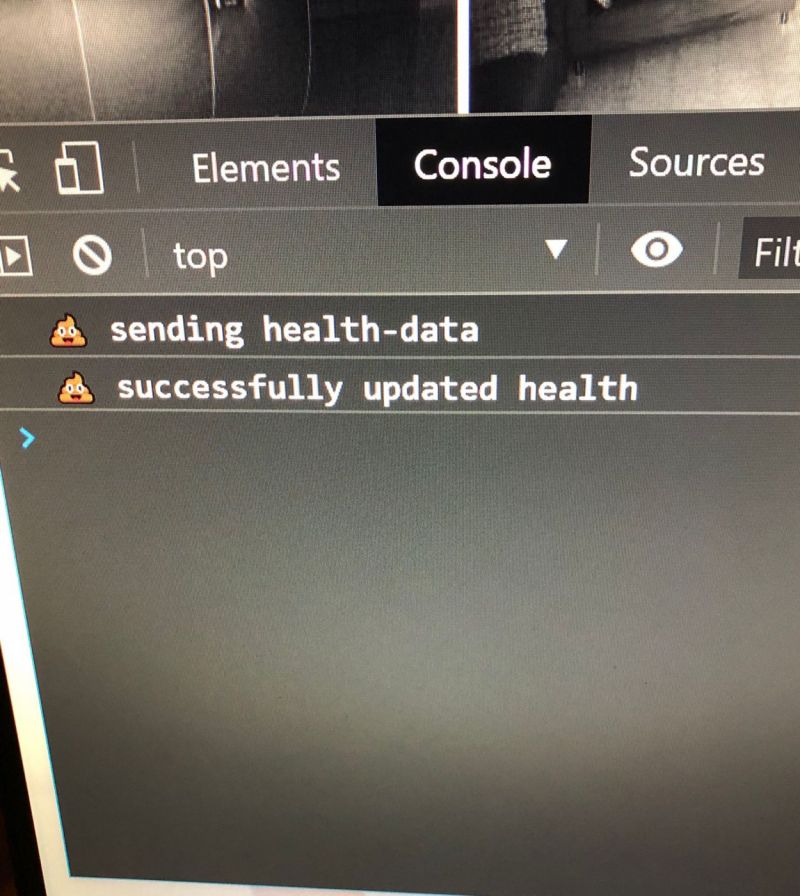
Pipeless API

From the creators of devRant, Pipeless lets you power real-time personalized recommendations and activity feeds using a simple API
Learn More
Search - "logging"
-
Hoorah! My code finally works! Now gotta remove those 1000 print statements I used to identify the bugs 😥11
-
** The most hilarious authentication implementation I've ever seen **
They stored password in cleartext, but never mind, this is sadly quite common.
For some reasons credentials were also case insensitive (maybe to avoid silly tickets from CAPS LOCK lovers?).
Then I had a look to the query executed during the login:
SELECT * FROM users WHERE username LIKE ? AND password LIKE ?;
So I tried logging in with user "admin" and password "%"... and it worked!
I laughed all the day.30 -
So my friend has two-step authentication for his smartphone.
Now he is not able to find his phone.
So, he tried to find his phone by logging into his google account via Android Device Manager.
Now, it is asking for the authentication pin which is in his phone.😂
He just got deadlocked.12 -
My classmate just fell for a phishing email from "PayPal."
She was talking about her payment being declined to her friend.
It peaked my attention when she said after logging in, she was lead to a blank page.
I asked if I could see it and it was definitely a phishing email
I will admit, it's one of the most professional phishing email I've ever seen, but the grammar wasn't very professional and the PayPal logo wasn't completely accurate.
Why do these idiots fall for everything?32 -
After several months of bug fixing, I can proudly say the application I inherited at work has gone a whole day in production without an unhandled exception (from a peak of above 1200 a few months ago).
Well, either that or I've broken the error logging and am now living in blissful ignorance.4 -
I'm logging my DevRant time as training ... I read all these dumb things that people do, and make mental notes so that I don't do the same thing. Best. Training. Ever.6
-
Worst thing you've seen another dev do? Long one, but has a happy ending.
Classic 'Dev deploys to production at 5:00PM on a Friday, and goes home.' story.
The web department was managed under the the Marketing department, so they were not required to adhere to any type of coding standards and for months we fought with them on logging. Pre-Splunk, we rolled our own logging/alerting solution and they hated being the #1 reason for phone calls/texts/emails every night.
Wanting to "get it done", 'Tony' decided to bypass the default logging and send himself an email if an exception occurred in his code.
At 5:00PM on a Friday, deploys, goes home.
Around 11:00AM on Sunday (a lot folks are still in church at this time), the VP of IS gets a call from the CEO (who does not go to church) about unable to log into his email. VP has to leave church..drive home and find out he cannot remote access the exchange server. He starts making other phone calls..forcing the entire networking department to drive in and get email back up (you can imagine not a group of happy people)
After some network-admin voodoo, by 12:00, they discover/fix the issue (know it was Tony's email that was the problem)
We find out Monday that not only did Tony deploy at 5:00 on a Friday, the deployment wasn't approved, had features no one asked for, wasn't checked into version control, and the exception during checkout cost the company over $50,000 in lost sales.
Was Tony fired? Noooo. The web is our cash cow and Tony was considered a top web developer (and he knew that), Tony decided to blame logging. While in the discovery meeting, Tony told the bosses that it wasn't his fault logging was so buggy and caused so many phone calls/texts/emails every night, if he had been trained properly, this problem could have been avoided.
Well, since I was responsible for logging, I was next in the hot seat.
For almost 30 minutes I listened to every terrible thing I had done to Tony ever since he started. I was a terrible mentor, I was mean, I was degrading, etc..etc.
Me: "Where is this coming from? I barely know Tony. We're not even in the same building. I met him once when he started, maybe saw him a couple of times in meetings."
Andrew: "Aren't you responsible for this logging fiasco?"
Me: "Good Lord no, why am I here?"
Andrew: "I'll rephrase so you'll understand, aren't you are responsible for the proper training of how developers log errors in their code? This disaster is clearly a consequence of your failure. What do you have to say for yourself?"
Me: "Nothing. Developers are responsible for their own choices. Tony made the choice to bypass our logging and send errors to himself, causing Exchange to lockup and losing sales."
Andrew: "A choice he made because he was not properly informed of the consequences? Again, that is a failure in the proper use of logging, and why you are here."
Me: "I'm done with this. Does John know I'm in here? How about you get John and you talk to him like that."
'John' was the department head at the time.
Andrew:"John, have you spoken to Tony?"
John: "Yes, and I'm very sorry and very disappointed. This won't happen again."
Me: "Um...What?"
John: "You know what. Did you even fucking talk to Tony? You just sit in your ivory tower and think your actions don't matter?"
Me: "Whoa!! What are you talking about!? My responsibility for logging stops with the work instructions. After that if Tony decides to do something else, that is on him."
John: "That is not how Tony tells it. He said he's been struggling with your logging system everyday since he's started and you've done nothing to help. This behavior ends today. We're a fucking team. Get off your damn high horse and help the little guy every once in a while."
Me: "I don't know what Tony has been telling you, but I barely know the guy. If he has been having trouble with the one line of code to log, this is the first I've heard of it."
John: "Like I said, this ends today. You are going to come up with a proper training class and learn to get out and talk to other people."
Over the next couple of weeks I become a powerpoint wizard and 'train' anyone/everyone on the proper use of logging. The one line of code to log. One line of code.
A friend 'Scott' sits close to Tony (I mean I do get out and know people) told me that Tony poured out the crocodile tears. Like cried and cried, apologizing, calling me everything but a kitchen sink,...etc. It was so bad, his manager 'Sally' was crying, her boss 'Andrew', was red in the face, when 'John' heard 'Sally' was crying, you can imagine the high levels of alpha-male 'gotta look like I'm protecting the females' hormones flowing.
Took almost another year, Tony released a change on a Friday, went home, web site crashed (losses were in the thousands of $ per minute this time), and Tony was not let back into the building on Monday (one of the best days of my life).10 -
So Nvidia doesn't let you use their GeForce Experience app anymore without logging in.
*Uninstalled*
Fuck that, I don't want to login so I can see an FPS counter in my ganes or record them to my local disk or something like that... Fuck you Nvidia and fuck whoever decided that would be a good idea.6 -
We're having an ongoing credential stuffing attack right now. Hackers hit us hard over the weekend and the web team sent out an email congratulating themselves that they stopped the threat.
I decided to look to see how they "fixed" the issue.
They modified their code to stop logging the errors to prevent Splunk from sending the automated emails to management (how we have been able to spot/monitor the attack).
They literally just put their heads in the sand, stapled a sign to their ass that reads "Meteor? We see no meteor approaching. Everything is fine."5 -
Fucking wix advertisements! Getting real tired of the "want a website? Why not make it yourself?" ads. You're already logging all my fucking google searches to display relevant ad info so maybe wrap your head around the fact that I'm a web dev and make my own fucking sites??6
-
I literally cringed today when my neighbor wanted help installing an app, she didn't tell me it was her banking app... And the thing I needed to help with was logging in... So she told me her bank details...
Even though I said (multiple times) it was dangerous to do so, and that she can't just trust people with this kind of information...
WHY ARE PEOPLE SO GOD DAMN STUPID WHEN IT COMES TO SECURITY!7 -
Boss: "Yeah we have a logging project coming up that has to be done in C" Me: "I know C, I can give some pointers on that"5
-
I now know another person's password without even wanting to.
He was sitting in the row in front of me, logging into our course page and then *brrrrraaaaapppp* - ran his index finger along the top number row and hit enter.
1234567890
I don't even know what to say.12 -
Yes, you fucking retards, I will read this article about logging in NodeJS when the cover photo
- Isn't JavaScript
- Isn't about logging
You really seem to know what you're talking about! 14
14 -
I used to work as an all-in-one IT guy in a company. One day I got a call from our HR team and the HR said "my Internet banking account has been hacked! It's logging in automatically!!" So I went to see the issue, and the so called "hack" was because she allowed Mozilla Firefox to save her login credentials, and because of that the login form was automatically filled. Such a stupid ass4
-
!rant
*me logging into the demo system*
Me: so what is the login data?
Boss: we are a security company, what do you think?
Me: admin admin?
Boss: admin admin.2 -
Yesterday the web site started logging an exception “A task was canceled” when making a http call using the .Net HTTPClient class (site calling a REST service).
Emails back n’ forth ..blaming the database…blaming the network..then a senior web developer blamed the logging (the system I’m responsible for).
Under the hood, the logger is sending the exception data to another REST service (which sends emails, generates reports etc.) which I had to quickly re-direct the discussion because if we’re seeing the exception email, the logging didn’t cause the exception, it’s just reporting it. Felt a little sad having to explain it to other IT professionals, but everyone seemed to agree and focused on the server resources.
Last night I get a call about the exceptions occurring again in much larger numbers (from 100 to over 5,000 within a few minutes). I log in, add myself to the large skype group chat going on just to catch the same senior web developer say …
“Here is the APM data that shows logging is causing the http tasks to get canceled.”
FRACK!
Me: “No, that data just shows the logging http traffic of the exception. The exception is occurring before any logging is executed. The task is either being canceled due to a network time out or IIS is running out of threads. The web site is failing to execute the http call to the REST service.”
Several other devs, DBAs, and network admins agree.
The errors only lasted a couple of minutes (exactly 2 minutes, which seemed odd), so everyone agrees to dig into the data further in the morning.
This morning I login to my computer to discover the error(s) occurred again at 6:20AM and an email from the senior web developer saying we (my mgr, her mgr, network admins, DBAs, etc) need to discuss changes to the logging system to prevent this problem from negatively affecting the customer experience...blah blah blah.
FRACKing female dog!
Good news is we never had the meeting. When the senior web dev manager came in, he cancelled the meeting.
Turned out to be a hiccup in a domain controller causing the servers to lose their connection to each other for 2 minutes (1-minute timeout, 1 minute to fully re-sync). The exact two-minute burst of errors explained (and proven via wireshark).
People and their petty office politics piss me off.2 -
My secret joy. Logging into our "automated email do not reply" mailbox and reading folks futile attempts to argue with an automated system4
-
My family hosts an 100 mile (160km) run once every year for ultra-runners. 11 hours in the first runner has done 105 km. And I'm sitting at this checkpoint logging their times and working on a project. But rain started pouring down and this not so waterproof tent has just become the worst developing workplace I have ever been in because the umbrella ain't big enough for me and the laptop. So I'm soaked and won't be relieved for another 8 hours. The things you do for family.
 8
8 -
I just finished setting up an instance of searx.me for the public to use.
You are free to use it at https://search.privacy-cloud.me
I can't prove it but I've disabled logging with searx and ip logging in the nginx access logs (catching ddos's another way). If you don't find that enough proof then I suggest you don't use it :)
Let's go to sleep now.13 -
So I thought I will set up a PIN to make logging into the corporate PC easier. Hm... based on these requirements I can probably stick with password.
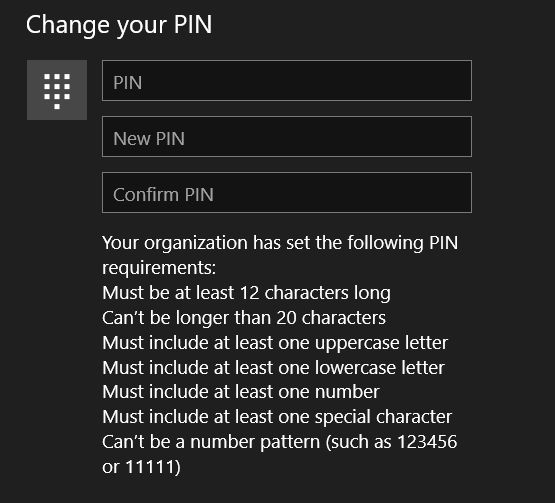 12
12 -
Sometimes the design decisions of big companies amazes me.
I wanted to contact support of Cloudflare. The only way to submit a new support query is by logging into the account first.
My problem is that I can not log into my account. What a bunch of retards.4 -
For my privacy advocate friends... They are logging keystrokes, clicks, and scrolls...
https://arstechnica.com/tech-policy...17 -
Every single fucking time:
Developers: Maybe we'll do something nice for the users, like signing in with Facebook account?
Business: Nah, nobody is gonna pay for that and it sounds useless. We're good with current solutions. Just do your job!
half a year later:
Business: Hey, I just came up with the idea that we could have logging in with Facebook.
Also business: Wow, great idea!
Management: Here's your bonus for a great idea!
Developers: ...5 -
Me: Hello. I'm from dept. ABC. My system isn't working.
IT: Have you tried logging OFF & ON again?
Me: (Let me rephrase) No the system isn't turning ON 😅
IT: Before I come over to your desk, can you try restarting once? 🤓
Me: (Motherfuck..) 🙂5 -
It fucking staggers me how many backend/devops-y people don't understand what a client side "request timeout" is, versus a server side one.
What does it mean:
The client was fed up with the servers bullshit, and decided to piss off and not wait around for the server to take forever to respond, because life's too short.
How not to solve/debug this issue:
- "I've checked the API request in tool xyz, and it works fine for me"
Congratulations, you've figured out how to call an API once, in isolation to the rest of the application, and without any excessive load. And using a different client to me, with a different configuration. Lets get back to actually looking at the issue shall we?
- "I only see HTTP 200's in the logs"
Yep, you probably will in most circumstances, because its the client complaining about it taking too long, not the server. If the server was telepathetic and knew what the client was thinking/doing at all times, we wouldn't have half of the errors we do.
- "Ah ok, I understand ... so how do I solve this?"
Your asking me? I don't fucking know, I didn't build the server! Put better logging in place and figure out why sometimes it takes forever.
Jesus fucking christ14 -
I GOT A PROPER DEV ROLE!!
The days of bemoaning the quality of devs on a product and logging tickets that never get addressed are coming to an end!
Edited: autocorrect changed it to "loving", somewhat optimistically6 -
In the old days switching accounts was as simple as logging out and logging in
Now, logging out redirects you to 20 different pages, doesn't redirect you to the original page, and sometimes it doesn't even log you out4 -
I came back here, after not logging in for about a year just to say that patents are fucking stupid. Thanks, see you in another year!5
-
I think I've got a working searx instance which I'd open up for the public.
NOTE: I cannot prove that I don't store anything because for that you'd need root access to the server which I won't give obviously. If you're not comfortable with that, just don't uses it.
I still have to do something for ip address logging anonymising or stripping, though. (nginx + CSF provided enough abuse prevention).
Tips on that?29 -
Client: “I’m sorry I just don’t understand the issue with the contract?
You said logging into Facebook was easy, what’s the issue with feature X (= complex graph API queries based on opinions and sentiment) and displaying images and videos, it’s the same thing!!!”
... no sir, it is NOT2 -
When a colleague left their computer without logging out, I created a shortcut to internet explorer, named it Google Chrome, and changed the icon to Chrome's icon. I couldn't remove Chrome's shortcut from the desktop or modify it because I didn't have permissions, so I turned of icon snapping and dragged it off the screen. I also replaced Chrome in the task bar with my fake icon. I then set the Internet Explorer to open a bunch of useless pages when it opens, set it to the default browser, and changed the search engine to Yahoo!18
-
CR: "Add x here (to y) so it fits our code standards"
> No other Y has an X. None.
CR: "Don't ever use .html_safe"
> ... Can't render html without it. Also, it's already been sanitized, literally by sanitize(), written by the security team.
CR: "Haven't seen the code yet; does X change when resetting the password?"
> The feature doesn't have or reference passwords. It doesn't touch anything even tangentially related to passwords.
> Also: GO READ THE CODE! THAT'S YOUR BLOODY JOB!
CR: "Add an 'expired?' method that returns '!active'?"
> Inactive doesn't mean expired. Yellow doesn't mean sour. There's already an 'is_expired?' method.
CR: "For logging, always use json so we can parse it. Doesn't matter if we can't read it; tools can."
CR: "For logging, never link log entries to user-readable code references; it's a security concern."
CR: "Make sure logging is human-readable and text-searchable and points back to the code."
> Confused asian guy, his hands raised.
CR: "Move this data formatting from the view into the model."
> No. Views are for formatting.
CR: "Use .html() here since you're working with html"
> .html() does not support html. It converts arrays into html.
NONE OF THIS IS USEFUL! WHY ARE YOU WASTING MY TIME IF YOU HAVEN'T EVEN READ MY CODE!?
dfjasklfagjklewrjakfljasdf4 -
"WTF? These records should have been inserted into the table!"
...Hours of checking code, trying to figure out how this is possible, can't find a way to have this scenario happen...
...Add additional debug and troubleshooting code, add more verbose logging, redeploy to all the containers, reset all the tables, many apologies to the boss for the delay....
...Co-worker comes in: "oh, hey, sorry, accidently deleted some stuff from the database last night before i left."1 -
Any bikers around here?
I recently bought my first motor bike ( super cheap ) and I'm excited to add some enhancements to it like GPS logging and collect relevant data about my bike.
Have you don't anything similar to your ride? I would like to put my Dev skills and improve my bike as a hobby. 17
17 -
So... I'm pretty much dead inside.
But today I laughed in a meeting.
Nearly died of laughter.
We're currently understaffed for various reasons, especially the ongoing migrations etc.
So a lot of projects are currently in "maintenance" mode (e.g. no new features) - cause we lack the necessary man power.
The meeting was more or less:
Team: We had an ongoing discussion in the team regarding logging and possibilities of tracing and XY suggested we implement OpenTelemetry in *all* projects in the next weeks, can we do that?"
Sometimes I'm not sure If I'm in a sitcom for torture experts.4 -
On a 5 hour bus ride for which the company advertised that they have WiFi. Technically they did, it just didn't seem to be connected to anything. (it was but it was unusable). I tried logging into the router as i always do and one default "admin" password later i was in.
I didn't want to mess up anything too badly, however i did change the wpa password to "YouShouldMakeThisABitMoreSecure"5 -
I like logging into public wireless networks where the admin credentials are the default and mess with their wireless settings...
Am I wrong?18 -
When I see two fields, one for username and one for password, I expect I can fill them out immediately subsequently with only a tab in between. While typing my password I DON'T want to get sent to a page where I can enter my password only: I was entering it already! Sometimes I even make it until I pressed the enter key that was supposed to log me in, but then I'm kindly requested to reenter my password. At that moment I not-so-kindly think: FUCK YOU Microsoft, you should know better. Even when logging into Visual Studio for fack sake3
-
Started part time job at a company, had to log my time on timesheets. Said fuck this and now the whole company logs their hours on a custom web based time logging system which I built.5
-
Introduced a ‘new’ logging framework for our web site. Web team is testing the integration and I get an email saying the logging wasn’t working. Instead of sending me how she is searching the logs, she sends me a screen shot of the code (which is ass-backwards of how I documented the logging library, but that’s another rant). OK, she wrote 5 lines of code that should be one line, but OK, the error still should have logged fine. I search the logs, and sure enough, there they are. Errors logged just as they should.
So I email back (with screenshot of the search query and results) asking how she searched for the errors.
Hour later she responds ..”I don’t know.”
That’s it.
WTF do you mean “I don’t know”?…WTF…you are a –bleep-ing developer too! This is not the first –bleep-ing splunk query you’ve written!
OK..I’m calm..feeling better. Wouldn’t be so bad if she emailed just me with the question (I’m not a splunk query expert either, we can figure it out together), but she was sure to cc 3 of the PMs involved in the integration, my boss, and other team members to make it sound like the problem was my code.3 -
They added a javascript that checks the login info. Worst part an if statement was the only thing keeping you from logging in without the correct password
-
during code review...
peer: "you should pass this variable, and extract the logger from it"
me: "why? it is a 3 line logging function. why not pass the logger instance?"
peer: "because that is our best practice. It is the way we do things"
me: "why is it a best practice?"
peer: "because it is. We use it everywhere!"
me: "No we don't. And I still don't understand why is this a best practice. can you explain?"
peer: gives ups, did not look at the mr, and was not going to.
mr stays open. probably forever.11 -
<just got out of this meeting>
Mgr: “Can we log the messages coming from the services?”
Me: “Absolutely, but it could be a lot of network traffic and create a lot of noise. I’m not sure if our current logging infrastructure is the right fit for this.”
Senior Dev: “We could use Log4Net. That will take care of the logging.”
Mgr: “Log4Net?…Yea…I’ve heard of it…Great, make it happen.”
Me: “Um…Log4Net is just the client library, I’m talking about the back-end, where the data is logged. For this issue, we want to make sure the data we’re logging is as concise as possible. We don’t want to cause a bottleneck inside the service logging informational messages.”
Mgr: “Oh, no, absolutely not, but I don’t know the right answer, which is why I’ll let you two figure it out.”
Senior Dev: “Log4Net will take care of any threading issues we have with logging. It’ll work.”
Me: “Um..I’m sure…but we need to figure out what we need to log before we decide how we’re logging it.”
Senior Dev: “Yea, but if we log to SQL database, it will scale just fine.”
Mgr: “A SQL database? For logging? That seems excessive.”
Senior Dev: “No, not really. Log4Net takes care of all the details.”
Me: “That’s not going to happen. We’re not going to set up an entire sql database infrastructure to log data.”
Senior Dev: “Yea…probably right. We could use ElasticSearch or even Redis. Those are lightweight.”
Mgr: “Oh..yea…I’ve heard good things about Redis.”
Senior Dev: “Yea, and it runs on Linux and Linux is free.”
Mgr: “I like free, but I’m late for another meeting…you guys figure it out and let me know.”
<mgr leaves>
Me: “So..Linux…um…know anything about administrating Redis on Linux?”
Senior Dev: ”Oh no…not a clue.”
It was all I could do from doing physical harm to another human being.
I really hate people playing buzzword bingo with projects I’m responsible for.
Only good piece is he’s not changing any of the code.3 -
What features would you want in a logger?
Here's what I'm planning so far:
- Tagged entries for easy scanning of log file
- Support for indenting to group similar sequential entries
- Multiple entry types (normal, info, event, warning, error, fatal, debug, verbose)
- Meta entries, so the logger logging about itself, e.g. disk i/o failures.
- Ability to add custom entry types, including tag, log-level, etc.
- Customizable timestamp function
- Support for JS's async nature -- this equates to passing a unique key per 'thread'; the logger will re-write all the parent blocks for context, if necessary. if that sounds confusing, it's okay; just trust that it makes sense.
- Caching, retries, etc. in the event of disk i/o issues.
- Support for custom writers, allowing you to e.g. write logs to an API rather than console or disk.
How about these features?
- Multiple (named) logs with separate writers (console, disk, etc.)
- Ability to individually enable/disable writing of specific entry types. (want verbose but not info? sure thing, weirdo!)
- Multiple writers per log. Combined with the above, this would allow you to write specific entry types (e.g. error, warning, fatal) to stderr instead of stdout, or to different apis.
- Ability to write the same log entry to multiple logs simultaneously
What do you think of these features?
What other features would you want?
I'm open to suggestions!17 -
Inmates are trying to take over the asylum again.
Got a message from the web team manager deeply concerned because since switching to the new logging framework, the site is significantly slower.
She provided no proof or any data to what 'significantly slower' means.
#1 The 'new logging' has been in place and logging for 5 years. We only recently depreciated the ILogger interface ('new' ILogger interface only has 1 method instead of 5)
#2 The 'old logging' was modified 5 years ago, so even if you were using the 'old' interface, the underlying implementation is still the same.
She tried to push the 'it wasn't this slow before' argument, so I decided to do some fact based analysis.
Knowing they deployed their logging changes couple of weeks ago, I opened up AppDynamics, looked at the average call time to Splunk (along with a few other http calls they are doing)
- caching services - 5ms
- splunk - 30ms
- Order Service - 350ms
- Product Data Service -525ms
Then I look at the data they are logging, for the month of June, over 5 million messages. At 30ms each, that's almost 42 hours spent logging errors...yes errors. Null reference exceptions, Argument exceptions, easily fixable stuff.
So far for the month of July (using the 'new' logging), almost 2.5 million errors. Pretty close so far with June's numbers.
My only suggestion was to fix the bugs in their code so they don't log so many errors.
Her response.."Can we have one of our developers review your logging code? We believe we can find ways to optimize the http requests"
Oh good Lord. I'm not a drinking man..but ...I might start.1 -
I created our login system to be secure and reliable.
One coworker hardcoded the roles a person who is logging in receives and built a backend to just assign roles you want. He pushed this to prod...
Yeah...2 -
My predecessor used auth as a bool. The only way he kept basic users from accessing admin functions was by including the word "admin" or "user" in the URL so any user could be the administrator by just changing the URL parameters after logging in
For example, mysite.com/admin/editorderdetails vs. mysite.com/user/editorderdetails -
So we have an API that my team is supposed send messages to in a fire and forget kind of style.
We are dependent on it. If it fails there is some annoying manual labor involved to clean that mess up. (If it even can be cleaned up, as sometimes it is also time-sensitive.)
Yet once in a while, that endpoint just crashes by letting the request vanish. No response, no error, nothing, it is just gone.
Digging through the log files of that API nothing pops up. Yet then I realize the size of the log files. About ~30GB on good old plain text log files.
It turns out that that API has taken the LOG EVERYTHING approach so much too heart that it logs to the point of its own death.
Is circular logging such a bleeding edge technology? It's not like there are external solutions for it like loggly or kibana. But oh, one might have to pay for them. Just dump it to the disk :/
This is again a combination of developers thinking "I don't need to care about space! It's cheap!" and managers thinking "100 GB should be enough for that server cluster. Let's restrict its HDD to 100GB, save some money!"
And then, here I stand trying to keep my sanity :/1 -
Is it just me, or does anyone miss logging into a Unix/Linux machine, doing a 'w' or 'who' and seeing a long list of folks all using the machine simultaneously? I still reflexively run 'who' as soon as I log into any real or virtual Unix or Linux machine and I am still slightly disappointed to find I'm all alone on it.3
-
When you take procrastination to another level... Adding Good looking table style output with emoji in a logging script which is only to be used once in a lifetime 😁
 2
2 -
X: Hi, regarding that ticket that you made...
You said "Implement logging to find out the culprit in site generation"...
What do you mean exactly?
Me: "Read the meeting notes, we had a full discussion on this 2 weeks ago".
X: "We don't understand it..."
Me: "As I said before, I have no experience in this tech stack... I'd expect bla to have a logging framework and I'd - for easier recognition - implement additional logging levels based on criteria <me just reading the meeting notes>"
X: But how do we do it?
...
I wish I had invented this discussion.
Because it hurts.
For the jolly of it, I had similar discussions today.
Three times to be exactly.
As I asked some dev what I should do next, put a foley catheter up his urethra or change the bed pan he wasn't amused.
Guess I'll get monday a call of HR.
So Monday I have less work to do, which is awesome.5 -
Having trouble logging into an app I am suppose to be working on with another dev. Debugging and found this:
// TODO: Temporary Optional because the API is not working properly
... i'm not happy for so many reasons -
So I was logging into google today and my password is very long so I often make mistakes while typing it so I went to inspect element to change input type to text so that I can check the password and I see that Firefox is storing my password already as plain text. Wtf Firefox???
 6
6 -
> worst coding procrastination story
worst and best at the same time:
If you wait long enough things might resolve themselves.
My team inherited an ancient site. Hosted on an old host that the org wanted to kill, using an old log service the org wanted to kill.
A ticket was written in 2021 to migrate that site's hosting and logging to the new services our org started using.
My team kept avoiding it since it was a cheap unimportant site.
in 2023 we were about to finally take action - then we hear "Turns out the new hosting platform and logging platform are way too expensive - I know all of you have migrated to these new services but you gotta revert and go back the old ones til we figure this out"
We didn't have to do squat.
Problem solved by procrastinating ✅1 -
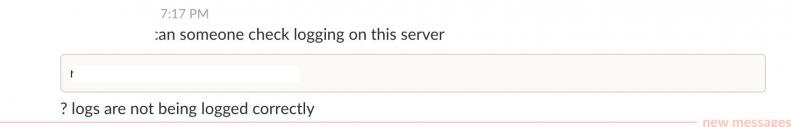
"Wait, we're logging all web traffic now?"
Me: You're the security engineer, you asked him to do it!
"I know but I didn't think he would actually do it!"
🙄😑 -
I'm planning on writing an open source (and much improved) version of my logger, but I'm stuck on picking a name :<
So, anyone have naming suggestions for a tagged and branching/nesting logging library? (ES6)
(I don't think "deforestation" is a good choice. sounds kinda bad.)19 -
I'm getting annoyed with the increasing number of platforms that implement the "Oops, something went wrong" vague error message.8
-
AI can take my job. I can't do this anymore.
Best of luck waking up 7 A.M on Mondays, logging in to work and telling in those 10 am scrum meetings “I’m still wOrking on the sAme tiCket as last friDay.”
Enjoy my job graybot.
I’m gonna go outside and remember what sunlight looks like. Maybe touch grass. Maybe grow crops. Maybe herd some cows. Idk. Might start a farm or might scream into the wind.2 -
Me: After 3 days of deliberation, I finally picked a framework, I can jump into the rewrite
*2 hours of inspired coding later
I finished the configuration validation and logging setup! What was that framework again?1 -
Putty, you son of a bitch. Why do you call the logging option "All session output" if you don't include binary zeros in the output? Zeros don't count as "all" or what?
Then call the option "All session output without zeros", that would have saved me some time and prevented handing out false data.6 -
Wow. Can't access a news article in an incognito tab without logging in or subscribing. This happened in Firefox and Chrome in mobile and desktop views on Android.
 5
5 -
We are required to use corporate SSO for any authenticated internal websites, and one of the features they require you to implement is a "logout" button.
They provide a whole slew of specifications, including size and placement/visibility, etc. They provide an SSO logout URL you must redirect to after you take care of your own application logout tasks.
Makes sense... except the logout URL they provide to serve the actual SSO logout function broke over 3 months ago, and remains non-functional to this day.
Apparently I'm the first person (and perhaps one of the only people) who reported it, and was told "just not to worry about it".
So, we have a standing feature request to provide a button... that doesn't actually work.
Corporate Security - Making your corporation _appear_ more secure every day...2 -
Client: "I cant logging me in"
Me: "Ok do you know your username? "
Client: "yes, off course"
Me:"ok, which password do you use?"
client: "I looked to my colleague... 5 stars"
Me: 🤐😣😯😭😭2 -
Following on from yesterday's catastrophe...
It happened again overnight!
And THEN another server failed when backing up the DBs...turns out 2 websites have activated logging .. each of around 20GB in the database!
So this morning both of our servers are down for different but similar reasons.
It's absolutely fine everybody.
I'm fine,
we're fine,
it's FINE!
-
Salesforce.
I mean I hate to be a predictable broken record, but it really is the biggest PITA thing I've come across. Proprietary stuff across the board, arbitrary limits, ridiculously tedious to get sane debug logging turned on and boy, if you've ever had to go through their process for listing an app...5 -
It was the first time I worked on a big project with a big team, I looked at the given code and copied their code style.
I finished very fast and everything was working fine, was really proud of myself. I'd like to add some logging though.
Programm failed it was heavily async and parallel so 2 days of debugging had past the whole team was on board nobody knew what went wrong there.
As I stared into the darkness of my code I suddenly saw what went wrong 😂
As I adopted no curly braces style of the Team for
If (condition)
Justine();
And I added logging above without braces everything broke 😂 it was indented properly so as a heavily python user everything looked fine2 -
So I have a script that runs every time I turn on my PC. The script copies a few files to a ftp server in my basement. Forgot to turn off logging....
Opend the file in Notepad, and would you look at that, 1 GB of ram..? WTF?
Edit: Managed to open the file, turns out that it's been exactly one year since I started using the script. 3
3 -
Still dealing with the web department and their finger pointing after several thousand errors logged.
SeniorWebDev: “Looks like there were 250 database timeout errors at 11:02AM. DBAs might want to take a look.”
I look at the actual exceptions being logged (bulk of the over 1,600 logged errors)..
“Object reference not set to an instance of an object.”
Then I looked the email timestamp…11:00AM. We received the email notification *before* the database timeout errors occurred.
I gather some facts…when the exceptions started, when they ended, and used the stack trace to find the code not checking for null (maybe 10 minutes of junior dev detective work). Send the data to the ‘powers that be’ and carried on with my daily tasks.
I attached what I found (not the actual code, it was changed to protect the innocent)
Couple of hours later another WebDev replied…
WebDev: “These errors look like a database connectivity issue between the web site and the saleitem data service. Appears the logging framework doesn’t allow us to log any information about the database connection.”
FRACK!!...that Fracking lying piece of frack! Our team is responsible for the logging framework. I was typing up my response (having to calm down) then about a minute later the head DBA replies …
DBA: “Do you have any evidence of this? Our logs show no connectivity issues. The logging framework does have the ability to log an extensive amount of data regarding the database transaction. Database name, server, login, command text, and parameter values. Everything we need to troubleshoot. This is the link to the documentation …. If you implement the one line of code to gather the data, it will go a long way in helping us debug performance and connectivity issue. Thank you.”
DBA sends me a skype message “You’re welcome :)”
Ahh..nice to see someone else fed up with their lying bull...stuff.
-
Had an internet/network outage and the web site started logging thousands of errors and I see they purposely created a custom exception class just to avoid/get around our standard logging+data gathering (on SqlExceptions, we gather+log all the necessary details to Splunk so our DBAs can troubleshoot the problem).
If we didn't already know what the problem was, WTF would anyone do with 'There was a SQL exception, Query'? OK, what was the exception? A timeout? A syntax error? Value out of range? What was the target server? Which database? Our web developers live in a different world. I don't understand em. 1
1 -
I can't believe I've just wasted 2 DAYS of my vacation to properly configure logging in my project...
2 fucking days!!! For something as trivial (yet vital) as logging!!!
FUCK3 -
I don't understand how people can write code, but be completely inept at developing software.
Take a zoom feature:
SOLUTION 0:
- Use 2 buttons
- Use 2 button listeners
- Use 2 float variables (for each button).
- Don't log anything.
- Use 3 crazy, hardcoded, constant, int literals like 66, 30...
- both buttons manipulate the same text field.
- no logging.
- Both listeners use if/else to check if the variable is within a range -- one if/else for each listener.
- Use crazy method calls to get text size.
SOLUTION 1:
- Use a slider.
- Use a single listener.
- No variables needed.
- Use a linear equation for zooming.
- has logging. 8
8 -
We found a binary string on our Loggly server. It's a PDF file .. the entire PDF file, being sent, to our logging service.3
-
Last year I planned to start a startup. I've started many good things but not the startup yet.
* A new data format
* A new data type
* A new web framework
* A new concept for logging
* And many other opensource tools and libraries2 -
Ok, so one of the oldest guy is leaving from my company (on a good note) and he was involved in multiple things in our organization. From having access to almost everything (AWS, Github and owning multiple projects and our legacy code). I am supposed to take KTof one project and man THE CODE IS MESS. YOU DONT PUT A RANDOM NUMBER WHILE CALLING A FUNCTION. You are supposed to define a constant and use that. I've told my manager that I need at least 1 week just to improve logging.2
-
I dont need DuckDuckGo,
I dont need any VPN
I dont need all of this "Internet Privacy Service" BULLSHIT which my ISP wants me to use,
I DONT NEED ANY OF THIS FUCKING SHIT!
AND I DONT WANT IT EITHER!
I HAVE MY OWN PI HOLE!
AND THATS FUCKING ENOUGH FOR WHAT I NEED! STOP TELLING ME ABOUT ALL THIS "We are clearly not logging your shit" WHILE YOU DO!!
Because I have my own shit!
Thx9 -
Goes back to high school.....
Me: This laptop is having issues logging into the network. I have tried restarting as well as restarting the WiFi. You probally should submit a ticket so IT knows it is broken.
Teacher: They would not fix it anyway.
Me: *facepalm*
TL;DR: Teacher thinks that telling IT to fix a computer would result in nothing happening.1 -
Yay! My first bash project :D
disclaimer - my bash is not pretty. yet.
Why I created it?
I encountered several footlong scripts in a new project at work. And they had no logging. And I am in charge of making it sing again. So here it is a tiny logging framework. 1
1 -
Supervisor: YOU NEED TO INCREASE THE COVERAGE OF YOUR UNIT TESTS! THE FILE logger.js DOESN'T HAVE >80% COVERAGE! IMAGINE PICKING THIS UP 6 MONTHS FROM NOW!
Bro. It's a Winston instance.
I am literally exporting a fucking Winston instance with 0 custom logic.
If 6 months from now I take a file and can't understand a Winston instance anymore, you're well within your right to fire me on the spot.2 -
Was logging in my student account to check whether the system actually registered my admission and here I go.
And this is not just some college. This is a website every engineering student shall use throughout the country.
Also this is not the first time this happened. 1
1 -
I hate:
- Enterprise patterns
- Enterprise type programming
- Dependency hell
- Logging hell
- Proxy hell
- Debugging hell
That will be all.7 -
A swedish insurance company has two different solution for logging in to their system.
1. An advanced high security single sign on solution involving active directory, verification of the network the request came from etc etc.
2. Using a link and passing your credentials in the query string!!! Like: insurancecompany.com?username=admin&password=password.
Solution 2 works with admin accounts from anywhere.4 -
Other staff: I’m having trouble logging in to website A. My password doesn’t work.
[Me thinking: That’s weird. When I set up your account, the password worked. I told you to change it. So maybe you forgot your new password. We haven’t changed anything to about the login process.]
Me: I reset your password. [sends new password]
Other Staff: The new password doesn’t work. But I can log in with Google.
Me: 😶 Website A does not have sign in with Google. What website are you actually on???10 -
They've been in a meeting with some clients the whole morning.
12PM, time for me to go. Say Happy New Year and am on my way home.
12:20 Got home, took shirt off, got something to eat from the fridge.
12:22 Bit the first slice of pizza. Phone rings.
- "Yo' we wanted to show them app 2 but I can't log in."
+ "I left the laptop (and the whole dev environment) there, and there's no PC on in my house (and no dev environment whatsoever)."
- "Well check with your phone. [SIC] Tell me when you fix it."
12:32 I had turned my personal computer on; checked the problem was what I imagined (unpkg lib with no version defined on the link had a new major/non-retrocompatible version); grabbed an online FTP tool; remembered IP, user & password; edited the single line that caused the problem; and checked it worked. Calling back.
+ "It's fixed."
- "Thanks!"
12:38 CEO sent me an image of the app not working, due to a known bug.
+ "That happens if you try to access app 1 having accessed app 2 and not logging off." (app 2 isn't being used / sold, as it's still in development) "Try logging off and logging in again from app 1."
- * radio silence *
+ * guess they could get in *
They had the whole freaking morning. 😠
I'm the hero CMMi's level one warns you about. But at what cost.
Happy early New Year's Eve everyone.2 -
Deleting debugging/logging lines instead of commenting them out, when there is 95% chance that I will need them again3
-
A service had/has been logging hundreds of errors in the development environment and I reached out to the owning process mgr that the error was occurring and perhaps a good opportunity to log additional data to help troubleshoot the issue if the problem ever made its way to production. He responded saying the error was related to a new feature they weren't going to implement in the backing dev database (TL;DR), and they know it works in production (my spidey sense goes off).
They deployed the changes to production this morning and immediately starting throwing errors (same error I sent)
Mgr messaged me a little while ago "Did you make any changes to the documentation service? We're getting this error .."
50% sure someone misspelled something in a config, but only thing they are logging is 'Unable to parse document'. Nothing that indicates an issue with the service they're using.2 -
Unreal Engine adventures:
me: So ok, I need a map from int to String
Unreal: ya but it's called TMap, FCompactPoseBoneIndex and FName.
me: ..uhhh ok whatever
...
me: ok for debugging, please print this
Unreal: FName is not a string
me: k. Fname.toString().
Unreal: ya but it aint a TChar array now
...
IT'S A FKING STRING JUST PRINT IT. And the other guy is still an int with extra steps! Come the fuck on now....
I mean, honestly, a logging function that cannot print a fking FString? sigh...
Man, I miss python and blender...8 -
You are a developer and you will only log time you're actually working. This means you will not be logging time spent in meetings, chasing for specs, requirement clarifications and similar. You must log 8 hours each day.
^^-- wtf?!? Is anyone else working in similar conditions?12 -
You know its a good end of the work week, when you feel compelled to mention the Geneva convention in your last PR before logging off :)2
-
I used to think that I had matured. That I should stop letting my emotions get the better of me. Turns out there's only so much one can bottle up before it snaps.
Allow me to introduce you folks to this wonderful piece of software: PaddleOCR (https://github.com/PaddlePaddle/...). At this time I'll gladly take any free OCR library that isn't Tesseract. I saw the thing, thought: "Heh. 3 lines quick start. Cool.", and the accuracy is decent. I thought it was a treasure trove that I could shill to other people. That was before I found out how shit of a package it is.
First test, I found out that logging is enabled by default. Sure, logging is good. But I was already rocking my own logger, and I wanted it to shut the fuck up about its log because it was noise to the stuffs I actually wanted to log. Could not intercept its logging events, and somehow just importing it set the global logging level from INFO to DEBUG. Maybe it's Python's quirk, who knows. Check the source code, ah, the constructors gaves `show_log` arg to control logging. The fuck? Why? Why not let the user opt into your logs? Why is the logging on by default?
But sure, it's just logging. Surely, no big deal. SURELY, it's got decent documentation that is easily searchable. Oh, oh sweet summer child, there ain't. Docs are just some loosely bundled together Markdowns chucked into /doc. Hey, docs at least. Surely, surely there's something somewhere about all the args to the OCRer constructor somewhere. NOPE! Turns out, all the args, you gotta reference its `--help` switch on the command line. And like all "good" software from academia, unless you're part of academia, it's obtuse as fuck. Fine, fuck it, back to /doc, and it took me 10 minutes of rummaging to find the correct Markdown file that describes the params. And good-fucking-luck to you trying to translate all them command line args into Python constructor params.
"But PTH, you're overreacting!". No, fuck you, I'm not. Guess whose code broke today because of a 4th number version bump. Yes, you are reading correctly: My code broke, because of a 4th number version bump, from 2.6.0.1, to 2.6.0.2, introducing a breaking change. Why? Because apparently, upstream decided to nest the OCR result in another layer. Fuck knows why. They did change the doc. Guess what they didn't do. PROVIDING, A DAMN, RELEASE NOTE. Checked their repo, checked their tags, nothing marking any releases from the 3rd number. All releases goes straight to PyPI, quietly, silently, like a moron. And bless you if you tell me "Well you should have reviewed the docs". If you do that for your project, for all of your dependencies, my condolences.
Could I just fix it? Yes. Without ranting? Yes. But for fuck sake if you're writing software for a wide audience you're kinda expected to be even more sane in your software's structure and release conventions. Not this. And note: The people writing this, aren't random people without coding expertise. But man they feel like they are.5 -
Spent hours troubleshooting an internal app that had zero logging today. It would just terminate, no exceptions, no feedback to the debugger, NOTHING.
Turned out to be the damn corporate virus scanner blocking "malicious" behaviour. Good thing my desk is so heavy or I woulda flipped it... -
Jeez maybe it's just me, not a very smart user, but after at least 6 years with iPhone5, just before changing it, I discovered how to raise the volume without logging in the phone first:
I press the home button, Siri show up, and THEN the fucking raise/lower audio buttons are working.
6 years typing the fucking pin just to raise the volume.
6 fucking years missing notifications and calls just because I forgot the fucking volume on the lower tone. Almost lost a girlfriend for that.3 -
Helpdesk: We can't figure out our own ambigious error message, you should solve it in another way...
Me: I see in the console that I get an execption response with an ID, you must be logging these exceptions, can't you check those?
Me thinking: you've just reduced yourself to desk without the help part -
Docker's encapsulation is amazing! I don't have to know anything about networking to get a swarm running with some demo services all talking to each other and central logging and... oh I fucked something up... better read about networking so I know what I broke1
-
At NYU doctor's office that forces me to register a temp account to use their WiFi.
I get an email saying my medical records have changed so I try logging into the site to check.
Site can't be accessed on the network..,1 -
!rant
Hello fellow devRanters, this weekend I've been working on devRant CLI client I want to share with you: https://github.com/stepnivlk/rrant
I'm using it as a fortune when logging into terminal and since it stores rants locally it is fast.
I spent only couple of hours developing it so there is some space for improvement :).
Enjoy it and feel free to comment/do codereview.1 -
I made Skype Bot which queries the data using wsdl authentication on our ticketing tool and send the data whoever has requested in skype itself(without logging or touching the ticketing tool).
Manager: Is that even possible?
Me: (In excitement) Everything is possible if you have the will.
Now, He wants me to work on his pet project. I dont know how to react!4 -
Spotted a new feature that had just recently being completed: "Disable all Logging due to noise". What.
Us on the Ops team just died a bit inside... -
I am building my portfolio website and added a contact section. In the API call to the backend, I am logging potential API failures to Firebase Analytics. Is it ethical to include the request data (content of the contact form) in log data?5
-
I spent 2 hours on Python logging system instead of doing real data science.
Really this module feels poorly designed. -
I needed to log in on a website in someone else's pc and didn't know the password by heart. I thought I'd log into chrome, if I log out later, what could go wrong right?
Apparently, a lot. It facking merged my bookmarks, history and passwords with hers! And she had shitloads of them! It took me facking hours to clean up the mess chrome created. I trust her, but I still didn't want her to have my passwords etc.
Omg I'm never logging into chrome again elsewhere, what a frustrating facking waste of time10 -
Once I implemented a giant ASCII skull for logging a fatal error in the company's app. Let's just say my feature did not get to production.4
-
Yesterday, I put the final touches on a massive system using hundreds of classes, with thousands of lines of code, all easily maintained because of the way I used abstract classes, and coding to an interface, stubs, etc. And all instantiated with a near english fluent api. With detailed logging and even contacts me when there's problems, result of a year's work. I felt like a genius
Today, this fucking simple contact form that won't do what I want it to for the past 4 hours...1 -
Presented my project at uni, teacher was pretty pleased and I'll get my grade some time next week, but for those that are interested, here's a small video of it in aciton:
https://youtu.be/LYV3bIC6QmU
Uses: Raspberry Pi 3B, Mifare RC522 RFID reader, a breadboard, ribbon cable, neopixel rgb led ring and a TowerPro sg90
For the ui I used PyQt5, almost got the threading completely working, there's only 1 blocking thing left, that's when the message for logging in doesn't disappear -
Microsoft and their dev tools...
> Trying to login to Azure VM
> Get an error, saying that password needs to be changed before logging in the first time
> Head over to Azure portal, try resetting password
> Password reset is not successful. Reason: Account already exists (???)
> Google the error message. Found solution (coming from a Microsoft employee!): Create a new user, login with that, fix the password for user #1 inside the VM, then delete the new user
What's wrong with these people? 😂3 -
I can't login ffs
I don't care that it shows an impossible number of characters honestly, but I don't get why that should prevent me from logging in to any of these servers
For that matter, why the fuck is number of characters a signed int? 2
2 -
2 hour meeting to brainstorm ideas to improve our system health monitoring (logging, alerting, monitoring, and metrics)
Never got past the alerting part. Piss poor excuses for human being managers kept 'blaming' our logging infrastructure for allowing them to log exceptions as 'Warnings', purposely by-passing the alerting system.
Then the d-head tried to 'educate' everyone the difference between error and exception …frack-wad…the difference isn't philosophical…shut up.
The B manager kept referring to our old logging system (like we stopped using it 5 years ago) and if it were written correctly, the legacy code would be easier to migrate. Fracking lying B….shut the frack up.
The fracking idiots then wanted to add direct-bypass of the alerting system (I purposely made the code to bypass alerting painful to write)
Mgr1: "The only way this will work is if you, by default, allow errors to bypass the alerting system. When all of our code is migrated, we'll change a config or something to enable alerting. That shouldn't be too hard."
Me: "Not going to happen. I made by-passing the alert system painful on purpose. If I make it easy, you'll never go back and change code."
Mgr2: "Oh, yes we will. Just mark that method as obsolete. That way, it will force us to fix the code."
Me: "The by-pass method is already obsolete and the teams are already ignoring the build warnings."
Mgr1: "No, that is not correct. We have a process to fix all build warnings related to obsolete methods."
Mgr2: "Yes. It won't be like the old system. We just never had time to go back and fix that code."
Me: "The method has been obsolete for almost a year. If your teams haven't fixed their code by now, it's not going to be fixed."
Mgr1: "You're expecting everything to be changed in one day. Our code base is way too big and there are too many changes to make. All we are asking for is a simple change that will give us the time we need to make the system better. We all want to make the system better…right?"
Me: "We made the changes to the core system over two years ago, and we had this same conversation, remember? If your team hasn't made any changes by now, they aren't going to. The only way they will change code to the new standard is if we make the old way painful. Sorry, that's the truth."
Mgr2: "Why did we make changes to the logging system? Why weren't any of us involved? If there were going to be all these changes, our team should have been part of the process."
Me: "You were and declined every meeting and every attempt to include your area. Considering the massive amount of infrastructure changes there was zero code changes required by your team. The new system simply worked. You can't take advantage of the new features which is why we're here today. I'm here to offer my help in any way I can with the transition."
Mgr1: "The new logging doesn't support logging of the different web page areas. Until you can make that change, we can't begin changing our code."
Me: "Logging properties is just a name+value pair dictionary. All you need to do is standardize on a name and how you add it to the collection."
Mgr2: "So, it's not a standard field? How difficult would it be to change the core assembly? This has to be standard across all our areas and shouldn't be up to the developers to type in anything they want."
- Frack wads smile and nod to each other like fracking chickens in a feeding frenzy
Me: "It can, but what will you call this property? What controls its value?"
- The look I got from both the d-bags I could tell a blood vessel popped.
Mgr1: "Oh…um….I don't know…Area? Yea … Area."
Mgr2: "Um…that's not specific enough. How about Page?"
Mgr1: "Well, pages can cross different areas, and areas cross different pages…what do you think?"
Me: "Don't know, don't care. It's up to you. I just need a name."
Mgr2: "Modules! Our MVC framework is broken up in Modules."
DevMgr: "We already have a field for Module. It's how we're segmenting the different business processes"
Mgr1: "Doesn't matter, we'll come up with a name later. Until then, we won't make any changes until there is a name."
DevMgr: "So what did we accomplish?"
Me: "That we need to review the web's logging and alerting process and make sure we're capturing errors being hidden as warnings."
Mgr1: "Nooo….we didn't accomplish anything. This meeting had no agenda and no purpose. We should have been included in the logging process changes from day one."
Mgr2: "I agree, I'm not sure why we're here"
Me: "This was a brainstorming meeting as listed in the agenda. We've accomplished 2 of the 4 items. I think we've established your commitment to making the system better. Thank you all for coming."
- Mgr1 and 2 left without looking at me or saying a word.1 -
They call it security questions.
I call it social engineering backdoor.
I'm supposed to enter those questions after logging into my account and I'm not able to skip it nor to set a proper two factor method.
Well, fuck you. Did you ever thought about dying by a two factor method? Ever watched a Saw movie? You got the idea. -
Why doesn't Twitter have a public API without authentication for simple stuff, such as reading tweets. One can do that without logging in on the website, why shouldn't code be able to do it.5
-
*Logging in my Google accout*
"Please set your phone number"
"Please set your home address"
Wow. Do you want my blood type too?8 -
Logging into my school website when... WHY DO YOU USE 🤬 FRNCH FOR BOOLEAN IN THE URL M🤬F
Ok, I know this is a francophone college, but come on! 4
4 -
Ran the build today 4:30 and found out our grunt file is missing some pretty critical error checks without even logging a warning. A dependency was unavailable and it was pushed to production. The site was down for 30+ minutes.1
-
If you think parametised queries will save the day think again.
I occasionally test sites I visit throwing a few quotes at inputs and query params.
I also always test logging in as % with user or pass.
Not only are plaintext passwords a thing but so is this:
WHERE username LIKE ? AND password LIKE ?.
Once I saw an OR.7 -
Bunyan
Bunyan is a simple and fast JSON logging library for node.js services
Server logs should be structured. JSON's a good format. Let's do that. A log record is one line of JSON.stringify'd output. Let's also specify some common names for the requisite and common fields for a log record.11 -
You know a server is having a jolly'ol time when, while logging through the serial console, it lags... Then, a few seconds later, you get a message
[time.seconds] Out of memory: Kill process PID (login) score 0 or sacrifice child
[time.seconds] Killed process PID (login) total-vm:65400kB, anon-rss:488kB, file-rss:0kB
10/10, only way to bring the server back to life was by a hard-reset :|3 -
Existing code:
Logger class would block the caller, lock a mutex, call CreateFile(), write a single line to the file, unlock the mutex and return.
Improvement:
Added two logging queues and created a thread that will periodically lock one queue and write it to the disk, around 500 entries at a time, while new entries are being inserted into the other queue. Kinda like a bed pan or urine bottle. While emptying one bottle, the logs go into the other one. Added fatal exception handlers so that the log queues are dumped when the application is crashing. When the exception handler is triggered, logging method does not return so that the application STOPS working to make sure there are no "not logged" activities.7 -
Just got handed a dozen servers. Documentation shows a (Linux) database cluster is using ldap authentication. I try logging in with my creds. No joy. I look up the root password and log in.
Not only is it not configured to use ldap, it's also not clustered.
I need more coffee. -
I dont understand the Log4j vulnerability.
Isnt the ability to execute code a feature they added so that you can add dynamic data to the logs?
If it is a feature then isnt it written in the documentation?
Is the problem that a lot of companies forgot to sanitize the input before logging it?23 -
Logging work in Jira, because it goes against the whole ethos of trusting people to get the work done when they have to log exactly how much time they spent on each individual story. It also doesnt account for pair programming. so 2 people log the same time and it looks like the story took twice as long. I’ll stop now because I’m precariously close to opening the “time based estimates” can of worms and thats for another rant.4
-
React Native developers:
Is it normal for the Expo app to suddenly go blank and stop working for no apparent reason, without showing any errors or logging anything? It happens all the time since I started using it and it's extremely frustrating2 -
Finally managed to get my CNN working with proper tensorboard logging. Think I'm starting to understand how it works.
But it got overfitted...4 -
At my last place we launched a new payment page and added logging.
Who ever set the logging up didn't obfuscate the user card details and stored them in the db for anyone with access to see. :-O1 -
No your nested if statements dont make an ai the same way logging into a txt is not machine learning2
-
Developer just emailed our team a complaint that our logging assembly was resulting in their poor test coverage and they sent a change request to give them the ability to mock the underlying log provider (ex. from the event log to ‘something else’).
Looked at their tests, and they are testing whether or not the .Log was executed (on an exception, if the .Log method was not executed, the test failed), which seemed a bit worthless because we’ve already got coverage in our unit tests.
We had a meeting to discuss the issue.
Me: “I’m OK with changing the logging code if it’s necessary, but I want to understand why.”
DevA: “Logging errors is crucial to the database transaction. If someone removes the logging, the tests should fail.”
Me: “If someone removes the error logging on purpose, then they likely have an agenda and will remove the test validation too. It wouldn’t be an accident.”
DevA: “That’s not my problem. They will have to deal with HR.”
Me: “We purposely prevented someone from intercepting the logging just for that purpose. Your test code already covers the business rule, testing the logging seems out of place. That would like writing a test to make sure the System.IO.File.ReadAllText actually reads all the text from a file. You kinda assume a few smart Microsoft engineers already wrote tests for that.”
DevA: “Yea, I guess that would be silly.”
Got cc’ed an email a little bit ago from DevA to his boss..
“We’re not going to be able to change logging assembly. This may have some impact on our overall test coverage as those lines of code will not get testing coverage. You will have to let the DevMgr know we will not meet our test coverage goals.”
WTF!1 -
This rant is about myself and anyone whos like me: using logs over a debugger
So, sometimes when I wanna quick check something or make sure, if and when something get's executed or I've ran into a Problem, I add a few log/print statements to check in console.
But I don't think about proper and helpful messages, since they aren't supposed to stay in code. So I often type what comes in my mind, like memes or song lyrics.
The last time this became a huge act, was Code review/ Prototype demonstration with Clients (which I didn't knew about, otherwise I would have removed them, I swear) and Boss and my Code printed "show bob and va...", "send nudes" and stuff... in loop... to stdout2 -
Windows is so magical. I mean it doesn't support syslog which is in a way essential in large environments. Today my coworker told me about a tool named nxlog which has the function to send log messages from windows directly to a central syslog server. It can also read files... well theoretical because nxlog does not accept ":" as a valid character... cya C:\something2
-
In appraisal discussion,
Boss : Give me good reason why should we give you 30% appraisal!!!
Employee ( After logging into prod machine) : I am going to quit this job 😅😅 -
Logging literally everything from every service into one giant super log db for us to sift through.
It is expensive, it is stupid, and it is set to .info() level always forever no exceptions.2 -
"Let's just add a logging system to our dependency"
No. You fucking idiot. DON'T INCLUDE A CUSTOM LOGGING SYSTEM INTO A DEPENDENCY FOR IMAGE MANIPULATION. I DON'T WANT YOUR FUCKING BULLSHIT LOGGING WHEN I'M FUCKING HANDLING IT MYSELF FOR MY ALREADY EXISTING SOFTWARE!! HOW DUMB CAN YOU STUPID MOTHERFUCKER BE TO TELL ME TO JUST "IGNORE" THE MESSAGES IN THE CONSOLE WHEN I'M BUILDING A FUCKING CLI BASED SOFTWARE??!!1 -
I like my log messages to indicate automatically where in the code something happened, so that I can easily identify where a message originated from while tracking down problems.
In C/C++ this is nice and easy - write a logging routine, wrap it in macros for the different log levels and have that automatically output __FILE__, __LINE__ etc.
I wanted to do something similar in NodeJS, as I'd found myself manually writing the file name in the log message and then splitting functionality out into new files and it became a mess.
The only way I found to be able to do this was to create an "Error" object and access the "stack" member of it. This is a string containing a stack backtrace, suitable for writing to console/file. I just wanted the filename/line/routine.
So I ended up splitting the string into lines, then for each of the lines, trimming the surrounding spaces (or tabs?), and parsing them to see if the stack entry is inside my logger module. The first entry outside of that module must therefore be the thing that called it, so I then parse out the routine or object and method, filename and line number.
It's a lot of clumsy work but the output is pretty neat. I just wish it were simpler!2 -
One of my colleagues just tried to deny a buggy code change was his on the grounds that the new code contains logging and he never uses logging.2
-
Had Arduino for months, couldn't get MPU6050 working, because of a lack of time and other stuff. (Need it for long term college project, data logging blah blah)
Gave it to project teammate to figure it out, who hates even touching hardware, BTW.
He figures it out in an hour (adjusting baud rate for supply voltage)
I feel like a complete idiot.
🙁4 -
Boss: I don't want centralized error logging
Me: But we have 50+ client sites running the same web app, why the fuck wouldn't we?
Boss: What if the database is offline, then we wouldn't be able to log exceptions
Me: *beats head against desk*1 -
In my previous rant i complained about no irregular sprite collision detection libraries.
So after messing up with curves and line in p5.js I gave up on creating the fish like a complete caveman.
I wrote a simple vector paint program which can return the set of points on console logging, and here is the result 5
5 -
My companys custom logging library is not thread safe and has problems with multiple instances of the endproduct as well.1
-
The creator of this library logs error which makes me feel like a Shaolin Monk reading a scroll...
I shall now head towards that direction. Thank you master Shiva 🙏 1
1 -
The real life of me as a trainee developer:
New system works locally but fails to work in production and dev.
Proceeds at futile attempts to debug for hours to find out that my connection strings in the transforms were nested inside logging. -
Apple added medicine logging feature.
Do you know how they tell you you should take your medicine? It’s “It’s time to log in your medications”. It’s not “take your meds now”. Otherwise, imagine those lawsuits, ooga booga iphone told me to take meds and I died.5 -
Bruh, imagine paying taxes for a site that literally throws a cryptic error message, instead of telling you "Page not found", because those retards literally redirect to /Account/Login after successfully logging in.
Even better, most people here are don't understand English well enough to understand what is going on.
And I pretty much doubt an admin has been informed... 3
3 -
Spent hours trying to connect to a remote desktop using RDP, it was logging from win 7 but gives error with win 10.
Later, I discovered the solution was to add the computer name before the username!!!!
computername/username -
This morning, I was logging in on the site I was working on without problem.
After lunch, I couldn't log in. No reason why.
Then I found out why. Someone modified the login in database, and warned everyone.
Everyone except the ones that are working on the website (me and my team).1 -
Figured out the root cause of slow code by using a profiler in an afternoon (more like an hour but needed to confirm/investigate)...
Team spent over a week trying to figure it out using logging and debugging...
Even after I told them to use a profiler...
Guess now I've justified my position of being the highest paid dev on the team.
I just know how to use other tools besides a hammer.1 -
Client began micromanaging our project :/ . Now we have to log our hours on each task and then replicate that in another time tracking system. Double-accounting...
And we do not get the Jira's Tempo plugin to see a summary of what hours we've logged.
It's reached the point where now I have to create a task to cover for the hour spent for time logging alone :/
damn it. It was a fun project though.5 -
Super brilliant idea for Windows: when logging on with a password that is only slightly mistyped, or with the consecutively appended number from the previous month, it should still be accepted. So much more usability - Microsoft just cannot reject that!8
-
Main branch running locally - fine
Main branch locally connected to QA dB - fine
Main branch on QA server with QA dB - NOPE
OK - build main locally, push to QA server - fine
WTF.jpg
Main build by build server, push to QA - nope
Rebuild QA vm and dB - build main, push to QA - nope
Turn on full server logging - PASS.
MAXIMUM WHAT -
Spent the weekend geeking out getting my head around a proper Docker based environment for my development env at home and for the team... 90% done and I couldn't figure out why I couldn't start my Splunk instance up.... I'd set the default logging to Splunk.... Chicken & Egg probs!
But how awesome is docker with portainer and app templates eh?! -
Another day, another tragedy...
1,5 half year later 2 devs were able to deliver :
- custom authentication. Basically they did a very simple client credentials grant.
- a custom wrapper to manage windows services
- a custom job scheduling system
- a custom logging library to log everything to windows event viewer!!!!!!
- all csv reports are created using string interpolation WriteLine("'{varA}','{varB}'") like this...
There are a lot of defects in those functionalities and they delivered almost 0 business features.6 -
Don't you just love it when gitlab's ci pipelines crash for no apparent reason, causing tests which cannot fail to just magically break down, change logging levels to Just about anything and basically PMS for about 3 hours before it decides it needs to restart completely and when you return the same pipeline which you've been trying to fix for the better part of an entire evening, after regular work hours, it. Fucking. Works. With. No. Changes. To. The. Entire. FUCKING. System.
Waste of a day.3 -
One of our integration solutions (via Webservices) had some issues. I had to switch on http logging to see what might be the issue.
On average, those logs are around 20MB when there is a bunch of traffic. But the solution brought a heap pf traffic through, those logs shot up to 1GB in size.
Had to delete the logs, since they took a million years to open, and told our vendors that the logs are not showing us anything 😅 I told no lies -
A large pool of application instances' is writing logs to the same physical file. No way to distinguish which instance wrote which line.
Welcome to hell
We're being asked questions. We're replying that we cannot help unless logging is fixed. Noone's bothering to fix this mess and instead returns tickets with requests to investigate more.
F.U.N
/s3 -
Switching from Linux to Windows on my personal production server... because sometimes logging into RDP is so much easier than SSH.3
-
>closes laptop to let it cool down at 5:10PM
>5 minutes later, boots back up on its own and doesn't go back to sleep
>opening and logging back in
"We have an important update for you planned for 5:30PM"
OH NO YOU DON'T, you fucker!
Shit like this makes me wanna call Windows the McDonald's of operating systems.3 -
Why the FUCK is my VPN logging me out after a certain time. Its not like that I have to drive +4h to some remote location fix it when it cucks up at the wrong moment!
-
Adding noip.com to the list of services that accept more passwords for signup than for logging in. Damnit how does software even get to that point. Isn't it, like, more effort to get this wrong than to get it right?
-
Project managers moved all the tickets around and then got mad that we couldn't find them to log our time.
Mass mutiny about logging time in general and expected dev hours per week.
They returned the tickets to the old system at least -
Microsoft certsrv is returning UTF-8 on the authorization error page but UTF-16 when logging in via basic auth...
Debugged this for 2 hours today to parse the response correctly. Thanks Microsoft -
Boy I'm proud of myself! I just managed to produce a nice little awk script, which makes printing a file in a log look good!
https://gist.github.com/chabad360/...2 -
As a novice programmer, learning about the logging package in Python and how to utilize it is really exciting to me. It's basically what I've been working with recently (besides the script for macOS that won't fucking work).
-
anyone else get second thoughts about their bank when they see this kind of message after logging in?
"Online Banking is unavailable
We are really sorry we are preventing you from completing your banking today. Our technical teams are aware and actively investigating. Please know they are working hard to restore service as soon as possible.
Please call us at 123-456-7890 for banking assistance or information."
er... what?2 -
Trying to debug an app for twenty minutes, and wondering why it was crashing and not logging anything strange.
Realising only after some compulsive head scratching that logcat has been filtered the whole time -
Cognito is the dumbest piece of crap ever known to man. Markets itself as a great & easy auth solution to dumbass CTOs who then force the devs to implement it.
I spent a week or so trying to figure out why my token expires immediately after logging in only to find out that they issued me a token that is already revoked.
WHAT THE ACTUAL FUCK COGNITO???? -
Helping out a team, I was documenting some code/processes when I came across several classes that was logging a lot of, IMO, 'junk' that was unnecessary (and I knew wasn't being used in any Splunk alerts/reports)
I offer a refactoring suggestion, simplifying the data being logged, moving the duplicate code to a central location, maybe saving 10~20 lines of code. Didn't think it was a big deal because they were already actively working on the code and it was all new code (nothing deployed to production yet). Sent the suggestion to the lead developer and he responds:
Dev: "Yes, the changes looks fine, but not in scope of the project. Any out of scope work will need to be suggested at the end of the project, reviewed by the team, the project manager and approved by the vice president."
"Out of scope"? Logging data to Splunk needs a vice president's approval? WTF?
YOU PROBABLY HAVE THE PROJECT OPEN IN VISUAL STUDIO RIGHT NOW!!!
Along with the documentation the lead dev said they didn't have time to do, I send his boss and the dev team my suggested changes (before-after screen shots of the code) and offered to do the 2 minutes worth of work (again, this was new code, nothing in production and zero side affects to anything).
I even offered to create the splunk reporting/alerting against the data being logged (another item they said they would not have time to do)
About a minute later the lead dev responds..
Dev: "Those changes look good. I'll have Jake make those changes and we can test the logging when we deploy to dev on Monday. Thanks!"
Of course you will...fracking ass hat.
I'll bet my Battlestar Galactica DVD box set he was going to make the changes himself, brag to his boss how he refactored the code, saving X lines of code..blah blah blah to help *me* with documenting the logging portion. -
Trying to measue google one tap login failures in mobile app in app browsers. I can't even comprehend where to add logging or reproduce the fucking issue against a test environment. because I can't change the url in an in app browser2
-
Is there an SSH app like Putty that can login to multiple servers at a time and execute the same command?
We have multiple servers and trying to locate a request in the logs. The structure of all the machines are the same so I want to just toe each command like CD, grep, etc one time and see the output from all of them.
Rather then logging in one by one.21 -
Our company's first open source project: https://github.com/digineers/...
It's a Symfony bundle that enables logging changes to entities to allow simple mutation logging systems.
Would love to read some of your opinions :)1 -
Continuing to learn k8s ecosystem and to achieve acceptable level
With trying eventually Helm, Argo CD and even trying to use not managed setup for k8s.
Going though books to find out theory about being SRE.
And about data intensive apps.
Learning and trying Kafka
Learning and trying FastAPI and diving in generally to async python ecosystem
Learning Go.
Learning few more books to increase code quality and its compositioning.
Getting more practice in monitoring and logging systems with applicating them to k8s.3 -
Wanted to get to bed early tonight, but ended up wasting two hours after I moved code from my development machine over to a test system and it was failing. After adding all kinds of logging to figure out where it was failing on the test machine i realized i fixed am error in an input file on my dev machine, but that error in the input fine was still there on the test machine. Another night with little sleep and tomorrow is Monday. 😭
-
My brain hurts from trying to figure out this unit testing crap. Is it just me or is it really a struggle to test your front-end code? I'm using jest and enzyme to test our React app but complicated parts of code with multiple state changes or calling props is making my life a living hell. I mean I usually just debug by console logging everything and it works lol...but my fucking boss has forced me into writing this unit testing crap. FML.7
-
I'm so sick of devs not caring what happens after they push their code. A new feature was released on the front-end two weeks ago but the backend was never deployed. It's been logging errors for 2 weeks now.
I know I'm equally at fault for not noticing but I feel like the only person that ever notices things like this. I also discovered a data issue today by looking at the error logs.
How can I get my teammates to be more invested in how the service runs live?8 -
Log4j. My boss asked me to add it to a project. Had an issue with logging, went to docs. why do I need to read a whole fucking textbook to log messages to a file?3
-
Mini witch hunt going on with broken builds last couple of weeks. Change satellite assembly/project A, breaks random unit test that hasn’t been changed for months and the TFS nazi sends out emails demanding the “broken” projects be fixed. Doesn’t matter the unit/integration tests are likely out dated and team responsible for the tests needs to fix it.
Yesterday I deleted some logging code out of a security assembly, broke an integration test that hasn’t needed to be ran since January (test database didn’t exist anymore).
I would have had to re-create the database, re-import the test data (not trivial), re-deploy a service using the test database…blah. All because I removed some logging code.
I deleted the gated check-in TFS build definition. Code check in … no sirens …whew! I win! -
Logging into my schools blackboard using selenium is only redirected on school WiFi
Outside school WiFi I go directly to the site. But on the school WiFi it pauses on a redirect page with a link that loops back to the redirect when grabbed by selenium And selenium fails
Fucking hell2 -
When I run tests, I like to enable the debug logging. All the SQL queries and template tracing just flies by. Freaks the others out.
-
Fuck IIS
The documentation is crap. Most useful information is from forum posts from 2009. I just want a bit of customizable logging for fuck sake.5 -
Attendance logging software which integrates a website, physical devices and Android/iOS app.
I'm working on it right now. -
For fuck, fucking sake I literally spent 10 hours trying to setup Celery logging with Django but no, ohhh no Celery has some ninja handlers that don't even show up in logging_tree. If I try to change date format for Celery then I get big "fuck off" in my face. One more hour and I will explode.1
-
Thinking of logging into work to do a side project and learn some new tech.... bc I don't have time to work on it during the week...
And there's no personal use case to do this stuff...2 -
Just uploaded my latest project!
A logging library made in c#.
If anybody could take a look and let me know what you think I'd appreciate it.
https://github.com/Icecream-Burglar...9 -
Productivity Hack: I'm a java developer who decided to write a productivity app that integrates to-do, pomodoro and eisenhower matrix altogether with reports generation. this will also help me logging at work. I'm also using electron + angular2 + typescript, just because, well, I'm trying to learn new stuff.
Long story short, many many many many days later, i'm still waiting for that productivity boost. What is dis webpack? Wat u mean loaders? Wat promises? electron-prebuilt is now electron? Wat u mean npm and node should be updated? .....
Please send help1 -
We use celery at work, and one of the issues we face is that we use Django logging.
I'm not sure how it happened, however we only get 1 level of tracebacks from it now.
This has made debugging painstakingly difficult, since we have to manually traverse the code every time.
(we're in the process of moving to sentry, and we'll get our full logs back soon)1 -
I hate reading tons of informative logging lines that libraries and frameworks produce (Spring and NodeJS, for example).
npm install somelib
(depending on the software): 200 lines of text of information regarding the progress. This is the equivalent of displaying 200 alert boxes. lol.
Wait.. where was the error.. ah, there, that one relevant piece of text. I only had to visually scan 199 others..
Yeah, I know, I can configure them to only display a certain category (info, dev, etc) but it's annoying when that's not the case.4 -
So I've made the code public for a tool that I've made using React and Electron. This tool does periodic calls to CircleCI to get the builds that are running. I made this tool because at my job I have two circleci accounts, one via Bitbukkit and the other on GitHub. By running this tool I can get the previous build numbers in a pinch without needing to open up another tab or logging out and then back into another account to get the builds. None the less, Enjoy.
https://github.com/nhalstead/...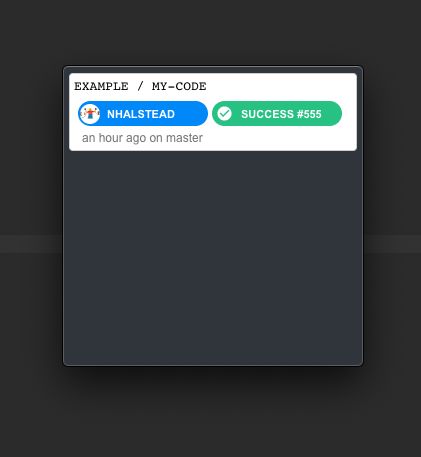 1
1 -
To be a Java (or other business popular language) developer
* Java 6, 8 and features up to 14
* SQL + nosql
* Caching
* Logging eg log4j2,
* Searching eg elastic stack
* Reactive
* Framework (at least 1, but hey, knowing 1 is lame..)
* Networking or at least base http knowledge
* Tomcat, jboss or other shit
* Aws, heroku, GCE or other SAAS/paas
* Rest, RPC, soap
* Business Hello World example
* Hexagonal Architecture
* TDD
* Ddd
* Cqrs
* 12 app factor
* Solid
* Patterns
* docket
* Kubernetes
* Microservices
* Security, oauth2
* concurrency
* AMPQ
* Cloud
* Eureka or consul as service Discovery
* Config server
* Hazel cast
*
*
* Endless story ...
Then we can start hello word app2 -
rant & question
What am I supposed to do to finally get log4j working?? It just doesn't want to log in my project. Or it simply hates me. However many tutorials and documentation I've followed, even copy pasting simplest examples with ConsoleAppendet, setting the xml config to classpath.
It starts with default fallback logging.
How do all the tutorials automagically work??1 -
So I'm looking for a tutorial somewhere to manage auth with react.
I have passport local setup with jwt in express, but looking to manage users in the front-end, managing the user state app wide, logging out, protected routes etc.
I've done some searching around but I can't see anything to concrete. Any pointers or articles would be great.
I was thinking of localStorage but not sure how to go about setting that up with react.3 -
not me, but my co-workers left del logging active for about 6 months, then one day it became severely slow for finding free filenames to save into.
mine is DROP DATABASE in prod, after that i have been like I will never keep open console to prod -
It be cool our if SVN got fixed so I could commit changes again. Or while it's down look at other vc options, maybe git?
Nudge, nudge wink, wink.
But in all seriousness wtf did the dba's do to break SVN? Logging my changes in a spreadsheet sucks raw balls. -
Django Logging im a nutshell:
Do something. Logging stops working. Revert. Loggin works now as wished.2 -
Name two production service, metrics and logging included, after a famous woman and an armored vehicle.
Dude, no. When those services go down in the middle of the night some poor soul on call duty will have to handle it without the faintest idea wtf is going on.1 -
🤬So I spent half an hour at my post office to pick up a certified letter. It turned out to be a paper version of „we have updated our privacy policy” from a company I last dealt with 5 years ago. 🤬🤬🤬
I want to thank my EU lawmakers for always thinking about our logging industry. I still don’t see why I need gdpr, though. I still dont know how the voters can stop this kind of non democratic nonsense in the future.
-
How to implement freakin OTPs ...
Loggin in ...
Click on Request OTP -> Not available
Click on Forgot password -> Send the OTP to both phone and Email.
The OTPs on phone and mail must not be the same.
So basically, user can't Login by entering OTP received on one of mail or phone.
Just ... fk the user while logging in already ... Entering the order entry in the database in twenty one minutes will do the rest. 😒
- Flipkart2 -
I always have multiple accounts thanks to Single-Sign-On, so I don't find my event tickets, logins, and contacts. To make it worse, those sites regularly log me out for no reason and some force logging in using my Google account although I have a main account with my business email address.
I suspect that's another deceptive pattern that they let happen on purpose so they can claim to have more users than they really have.1 -
Once again, the next build after hitting Ctrl + C while building a project surprised me with `java.lang.IllegalArgumentException: Malformed \uxxxx encoding`.
In which file? Is it so difficult to provide users with helpful information? Your `-X` option still does not show anything.
(Not to mention it must not corrupt ~/.m2/repository on SIGINT).1 -
When logging in, why is there no reminder like 'your password was at least 8 characters long with at least one digit'.8
-
Why does #Devrant (idk if #'s are a thing here) not have a confirm password field?
Come on... I doubt it annoys users and it saves people a lot of hassle, especially when we are logging in on multiple devices :/ I know lots of people who type their password wrong the first time and later on they can't login and get frustrated and confused then end up resetting via email.
Also why no login with Google etc~ that's kinda annoying too...3 -
Learning to use logging in Python for an existing application.
🙇Feeling enlightened looking at the first log file output.3 -
> totally disable logging on console
> logging is redirected instead on some 1200 separated files (no, not "log files rotated through 1200 days"; every part of the program has its own log file, and there's 1200 of them)
> still, in all those files, none of them contains MY log; somehow it disappeared
Why some people even chose to become developers will always elude me2 -
When u are traversing the logs to find how flow went...and find out the bastard who wrote it forgot to put in logs at all...1
-
If my manager asked for an update only on ONE report on projects, I think he'd be a perfect manager. Right now, I'm having to update FOUR different things for everything I work on: an institutional ticketing system, management's summary view page for the same ticketing system, weekly report, and my personal logging journal.
-
Was freaking out why my changes weren't being shown in development. Spent an hour console logging everywhere, trying to decipher bugs, and just generally worrying about "what the fuck did I do?"
I just forgot to merge my PR after it was approved.
Safe life. -
Imagine enabling verbose logging for a complex ETL process that typically takes 8 hours to run but has been failing for some reason after running for about 7 hours. Naturally, you want to check the log file to find out what went wrong.
Now imagine not having read access to the log file. -
Sigh :/ The npm default to print its own logging messages is so annoying I now do this:
alias npm='npm -s'
npm run my-script // only the output of my script
\npm run my-script // be annoyed by npm log messages1 -
So i'm trying to upload a file to an SSH server using node. First I try the obvious putFile method provided by the obvious node-ssh package. On any other server this would work fine but this server doesn't have sftp installed so that doesn't work.
OK, so next I learn how scp works (it runs the command "scp -t" on the remote server, and sends to stdin a command like "C0666 1234 file.txt" and then sends the contents of the file) and I write some javascript code to do this. It's pretty finicky, the first few tries I forget to close the stream right or detect the program finishing. I add some logging and that helps me figure out what the problem is, and finally I get it to not output any errors.
So I log into the server and check and the file isn't there. I try again several times, file still isn't there. I try running scp -t manually on the server, typing in exactly what my program is sending, and it works. This goes on for a while until I realize that I've been sending a file to one server and logging into a different server to check if the file was sent. grrr6 -
i am actually proud of my achievement of a scraping download-robot with decent logging, structured setup file, a small auto login to password protected areas and fancy cli options. because i am the only one on this sofa who can do this. :) this day has been kind to me.
-
Wanted to add a simple log entry when a model changes state in a certain way.
Unit tests pass, functional tests pass, manual tests through application GUI pass.
But for some fucking reason the single line logging call I added results in an error 500 when the application is accessed through a REST API.
Going to have a fun day tomorrow debugging this shit. -
When the services team asks the mobile team what the response on a request is... And then requests console logging on the app so that they can test their code.
-
> Error
> Error
> Adds "console.log(valueThatIsRelatedToError)"
> Smiles because I managed to not fuck up logging to the console1 -
I've just learned that our front-end application throws a simple 404 error when trying to retrieve an avatar that does not exists.
But our technicians/support use this error in the console to show the customers that there is indeed a problem with the application functionality but have unsufficient logging from the back-end to troubleshoot with their internal tools.
What a bunch of liars trying to keep the customer satisfied and it works relatively well :D2 -
I think I have a problem.
I remember when this platform used to have living people on it I didn't mind.
So i keep logging in curious what the dead fucking people said in response to me, knowing it will be the same anyway.
One day at a time... *deep breath*
Also fuck you, I wrote this before.2 -
So I wrote a while ago .ndjson shapes dataset player.
https://quickdraw.withgoogle.com/ this site contain peoples shitdrawings of particular object.
Grab dataset from here in .ndjson format logging into google account
https://console.cloud.google.com/st...
go to here
https://jsfiddle.net/ywmp6bju/
browse the file and press play when it's enabled.
Attached picture is a frog. 2
2 -
😂😂😂 mfw redid all my logging statements today to change sentences into keyvalue pairs (for log querying) and the script broke due to an invalid parameter reference in one of the debug statements.
Causing more errors trying to prevent errors smh -
Checking for root is maintaining a false façade of security. By the definition of root it can always be bypassed and we should be designing workflows to discourage logging in from an untrusted device unless you have 2fa.1
-
After attempting logging into FB Messenger with every browser I have, boy was I surprised when I found out Adblock was causing it to refuse to render with no errors displayed. Why would you block Adblock from an ad-free service !?1
-
What's your go-to logging word/message for when you just need to see if a function is executing/reaching a certain point?
I usually go with "dude"4 -
when the stack trace wasn't included in the error logging
fuck me, how the fuck am i supposed to know where the exception occurred
perhaps i've taken it all for granted thinking that the default toString implementation of an exception would've included that5 -
Working with Crystal reports, getting ready to deploy my changes. Guess what? My tiny changes to output has successfully broken 12 other fields, and 1 that is in absolutely no way related! Comes right from the database!
And it's crystal, so there's no debugger or logging. Plus, the report takes an hour to run! Today's gonna be a fun one!6 -
What is your favorite method of debugging?
Mine is a debug log. I like a key value setting for enabling/disabling, and logging most transactions, calculations, and variables, even if they seem trivial. I've been able to locate bugs much quicker with detailed logs while some coworkers are still stepping through the process line by line. I don't fault the step method as I use it when logging uncovers nothing (it usually means I didn't log something critical :p) or when logging is not possible.1 -
Saw my colleague debugging. He's got a try-catch, then I asked, "Why aren't you logging the stack trace?". He answered, "I don't cause it will be a security risk". So there he was having a hard time debugging.🤯
Can you guys confirm if what he said is true?4 -
Logging to the console in an aesthetically appealing manner makes the development experience 1000x better!2
-
The iteration order of some hashmap or some such keeps changing when I add or remove log lines. For a given source code the order is static, but I can't bisect errors by logging because when I add a probe arbitrary symptoms vanish or previously correct probes start printing bullshit.3
-
Does anyone use Winston JSON? or know what the perfomance impact is vs standard text logging? (serializing an object to JS)?6
-
At what point does it get easier to just log your errors than to add a to-do that this needs to be logged?
Asking for my boss who clearly prefers Todos to actual logging -
wait..... can you auto indent console logs depending on their nesting in functions?
I just realised it can be hard to read console logs because say you do
log('here 1')
callFunction()
log ('here 2')
But callFunction does a bunch of logging, then your here1 and here2 become separated !
But if you could make console log automatically add a couple spaces for every level of nesting/scoping that would be ideal .. ? 👀11 -
FUCK YOU GOLANG FOR LOGGING IN DUCKING BLOODY RED.rant logging is evil you don’t do that logging in red who the fuck even comes up with this shit who thinks this is a good idea9
-
Websites that use a snow effect in Winter, with many little snowflakes moving on screen, needlessly drain the battery of mobile devices. Since batteries in portable electronics are usually not replaceable as of 2022, it also shortens the overall useful life of mobile devices.
If web designers feel the need to appear creative, which the snowflake effect isn't since it apparently existed since the 2000s, they should at least give users an option to turn it off. And that option should be available without logging in. Perhaps this useless effect should be turned off by default for mobile users.6 -
Need complete control over information you're fetching while logging in via social site in Django
Check this out: https://prakhar.xyz/backend-control... -
What the hell, why is every damn article about nginx logging practically the same, I just want to see an example of an error log line and I guess I’ll have to actually go look at a running instance and produce errors
-
How do you seize crypto if it's anonymous? Secure?
Just need to catch someone logging in?
https://apnews.com/article/...14 -
I am trying to decompose a 3D matrix using python library scikit-tensor. I managed to decompose my Tensor (with dimensions 100x50x5) into three matrices. My question is how can I compose the initial matrix again using the decomposed matrix produced with Tensor factorization? I want to check if the decomposition has any meaning. My code is the following:
import logging
from scipy.io.matlab import loadmat
from sktensor import dtensor, cp_als
import numpy as np
//Set logging to DEBUG to see CP-ALS information
logging.basicConfig(level=logging.DEBUG)
T = np.ones((400, 50))
T = dtensor(T)
P, fit, itr, exectimes = cp_als(T, 10, init='random')
// how can I re-compose the Matrix T? TA = np.dot(P.U[0], P.U[1].T)
I am using the canonical decomposition as provided from the scikit-tensor library function cp_als. Also what is the expected dimensionality of the decomposed matrices.1 -
I want to keep 1 year of daily indexes but for the ones older than 30 days, unloaded from memory. But accessible when needed.
So like say there's a performance issue today and I want to compare all the activity against 2 months ago. I can open the old index and search it.
Can you do that, does closing remove it from memory? Otherwise how would you do that?6 -
Getting frustrated with errors I can't replicate or identify! After spending ages trying to find what's gone wrong and failing, its so embarrassing to suggest "try logging off and logging back in again"
-
Let’s hear the opinion of the public consensus. In a big system with many different things doing their own thing, should you expect the part which is responsible for logging / information purposes to book account payables in the ERP? Like, am I an idiot or should I start learning Chinese? Do I understand “send email” wrong?1
-
How do I deal with this;
Edge case hiccup on production, no errors in the available logs(very shallow logging), no access to the production server, issue unreproducable on staging and a manager that want me to fix it AFTER I already said that im kind of sailing blind and can't do much without logs or access, and already looked at it with another dev who also has no idea what is going on3 -
Backend development!
I love my little services like a cobweb with solid bases of communication, security, logging and measuring. It can't get more fulfilling to build a service that is used by just more than one frontend. -
We were on track to provision Cassandra for logging and elasticsearch for business data store.
Now we are on track to provision mongodb and elasticsearch. That's right, two document stores.
Things go to hell when management think they are capable of taking engineering decisions. -
Ok this is either my code, socket.io or China. So I wrote DApp for my crypto project but for some reason our Chinese users have problems using it... So i dig through our code for HOURS! and finally resort to making an AJAX call from the client to a hideous PHP script for logging and what do i find?
For some reason the WebSocket cannot connect. I haven't mapped this so it's only conjecture but I think the GFW is blocking my users connections? (Also using a VPN seems to fix it)
Anyone else had this issue?1 -
Any good recommendations on how to gather user metrics/instrumentation and visualize data?
The program is a WPF application with not internet connection so logging to file and get file is probably the only solution.
I've played a little with Serilog to file and trying to import the log into elastic search and visualize data with Kibana. -
I'm looking project for 6h Hackathon. We use Atlassian in our company, bitbucket and slack. Do you have some ideas? I'm thinking about desktop application in Vue + Electron to help logging time in Jira
-
The awesome thing about remote work is that you can be in a meeting for one team while working and logging hours for another team. Getting paid twice!
-
Can anyone recommend a good password manager that is 'in the cloud', can be used on my mobile and makes life easy for logging into apps on my phone that aren't logged in via a browser. Ideally something free but I'm willing to pay for something that is worth it8
-
Tracking/logging hours, how do you do it? Is there some decent software for Linux that does this?
I wanna start tracking my time doing specific tasks, so I'm just wondering what other ppl use, if at all hehe1 -
Logging a week of work on Redmine is taking me ages, I wonder if I'm retarded or Redmine UX is shitty. Likely both.1
-
Quick question. I'm currently working on a project that requires extensive activity logging. What do you recommend for some sort of monitoring and logging of user access on a Linux box?
Big thanks in advance. <34